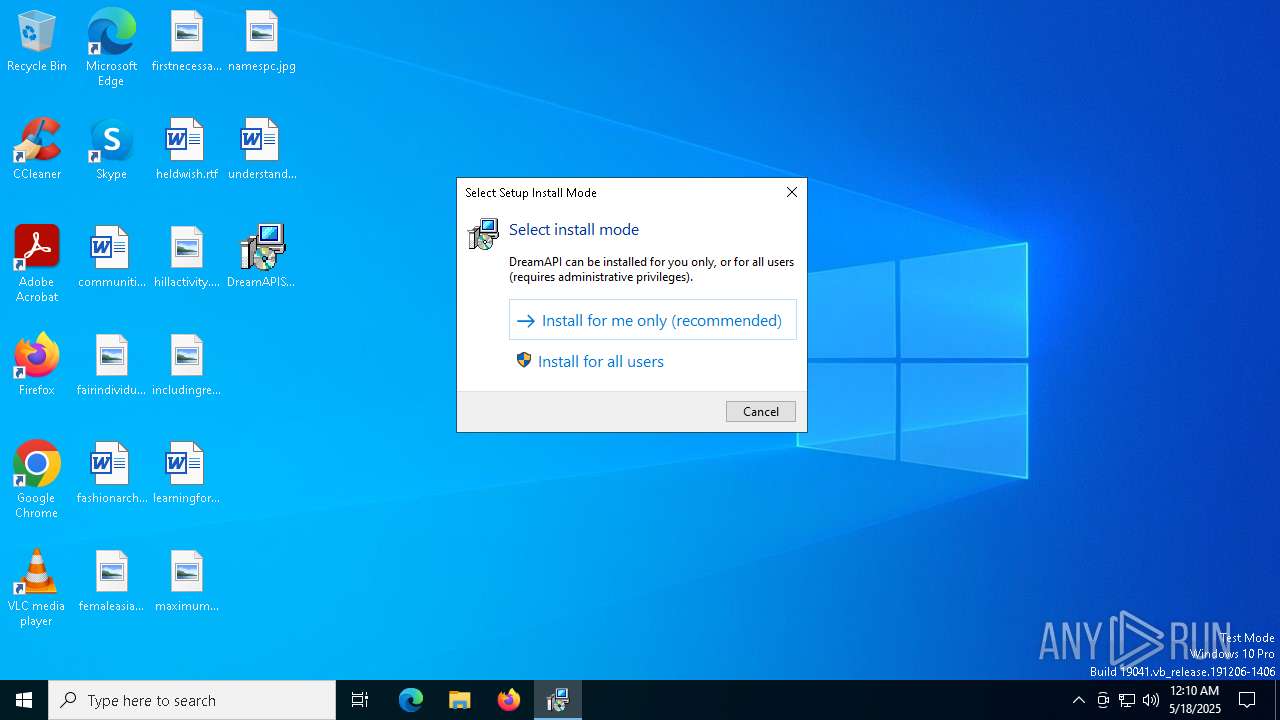
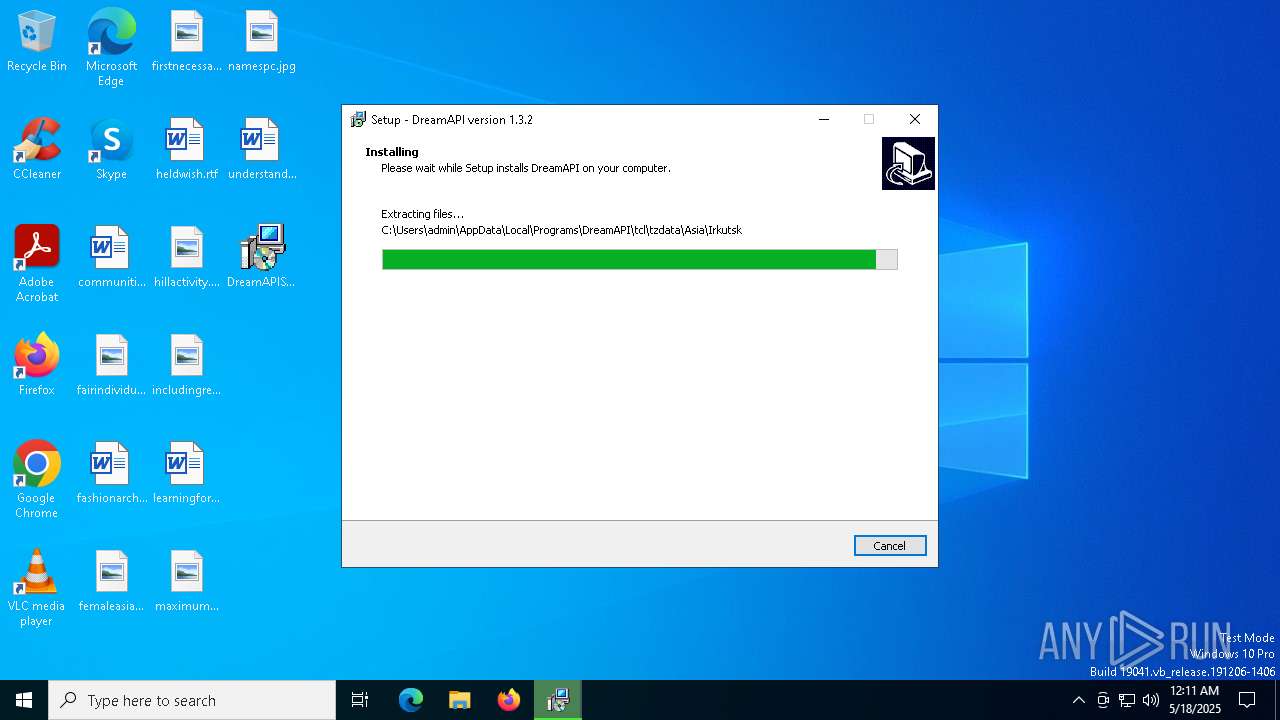
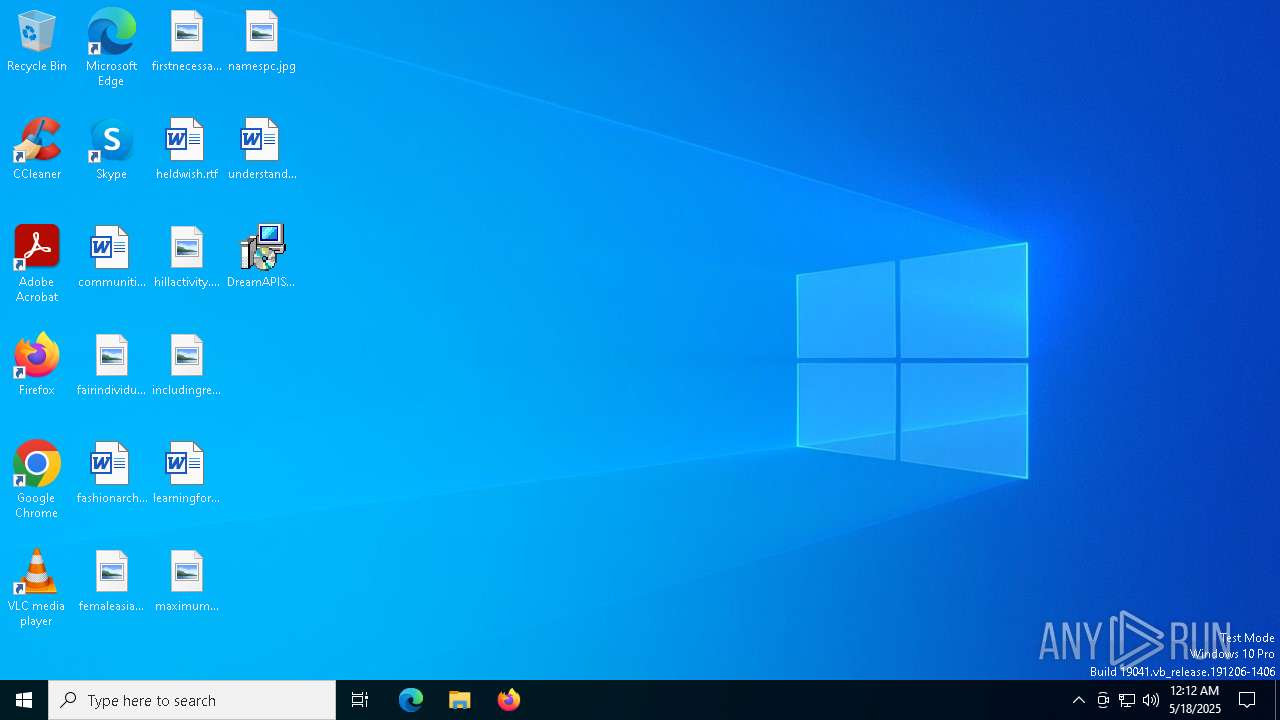
| File name: | DreamAPISetup.exe |
| Full analysis: | https://app.any.run/tasks/3798a815-508c-45b6-a5bd-48866a365198 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 00:10:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | D52F6460FF887D6999A061A4E0849338 |
| SHA1: | BEA4672A5F662FF0DACA69ECE68B420627F553E7 |
| SHA256: | A3166EAFEE99F6C911ADB0F9B0610A8EFB27B9FA879EBF7BE735F872523146D6 |
| SSDEEP: | 196608:C9KIBc/vQOwjjGBEv7KcXEMt+05cWZWWvCY9ZYS0xWQL48:C9xc/onwK3rVdXZYSN78 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- DreamAPISetup.exe (PID: 7388)
- DreamAPISetup.tmp (PID: 7408)
Reads the Windows owner or organization settings
- DreamAPISetup.tmp (PID: 7408)
Process drops legitimate windows executable
- DreamAPISetup.tmp (PID: 7408)
Drops a system driver (possible attempt to evade defenses)
- DreamAPISetup.tmp (PID: 7408)
Process drops python dynamic module
- DreamAPISetup.tmp (PID: 7408)
The process drops C-runtime libraries
- DreamAPISetup.tmp (PID: 7408)
INFO
Checks supported languages
- DreamAPISetup.exe (PID: 7388)
- DreamAPISetup.tmp (PID: 7408)
Reads the computer name
- DreamAPISetup.tmp (PID: 7408)
Create files in a temporary directory
- DreamAPISetup.exe (PID: 7388)
- DreamAPISetup.tmp (PID: 7408)
Detects InnoSetup installer (YARA)
- DreamAPISetup.exe (PID: 7388)
- DreamAPISetup.tmp (PID: 7408)
Compiled with Borland Delphi (YARA)
- DreamAPISetup.exe (PID: 7388)
- DreamAPISetup.tmp (PID: 7408)
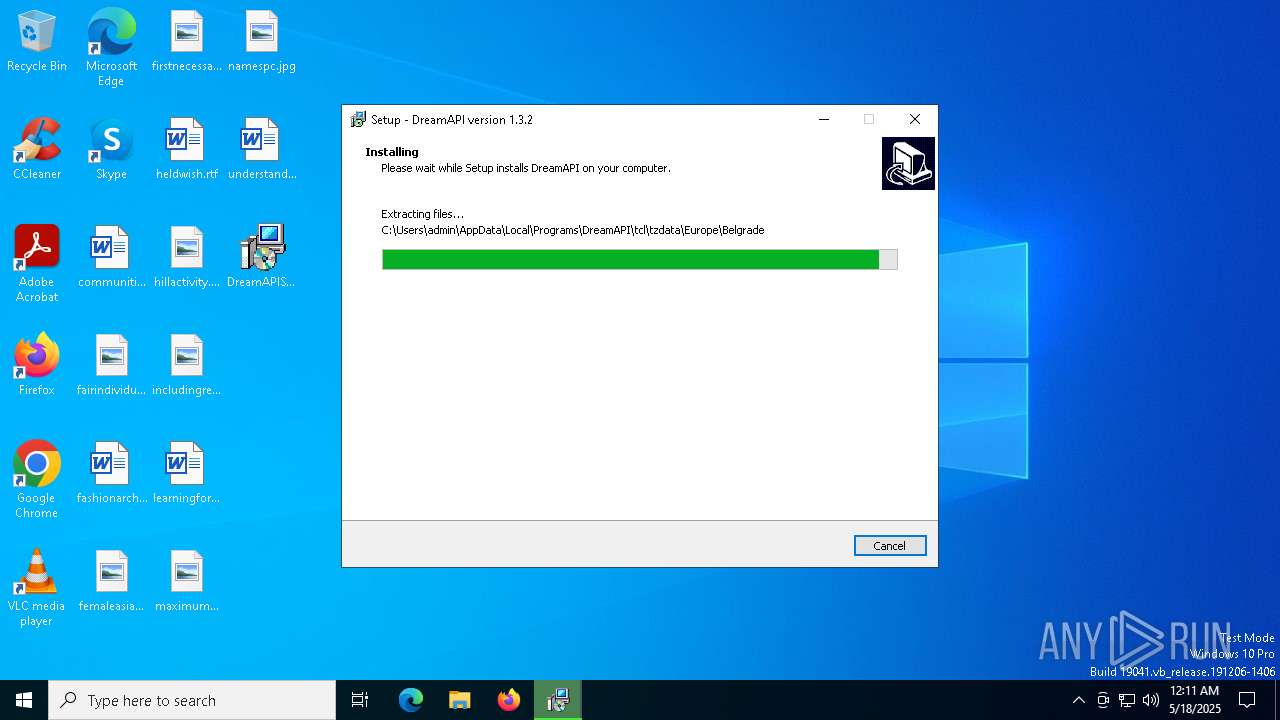
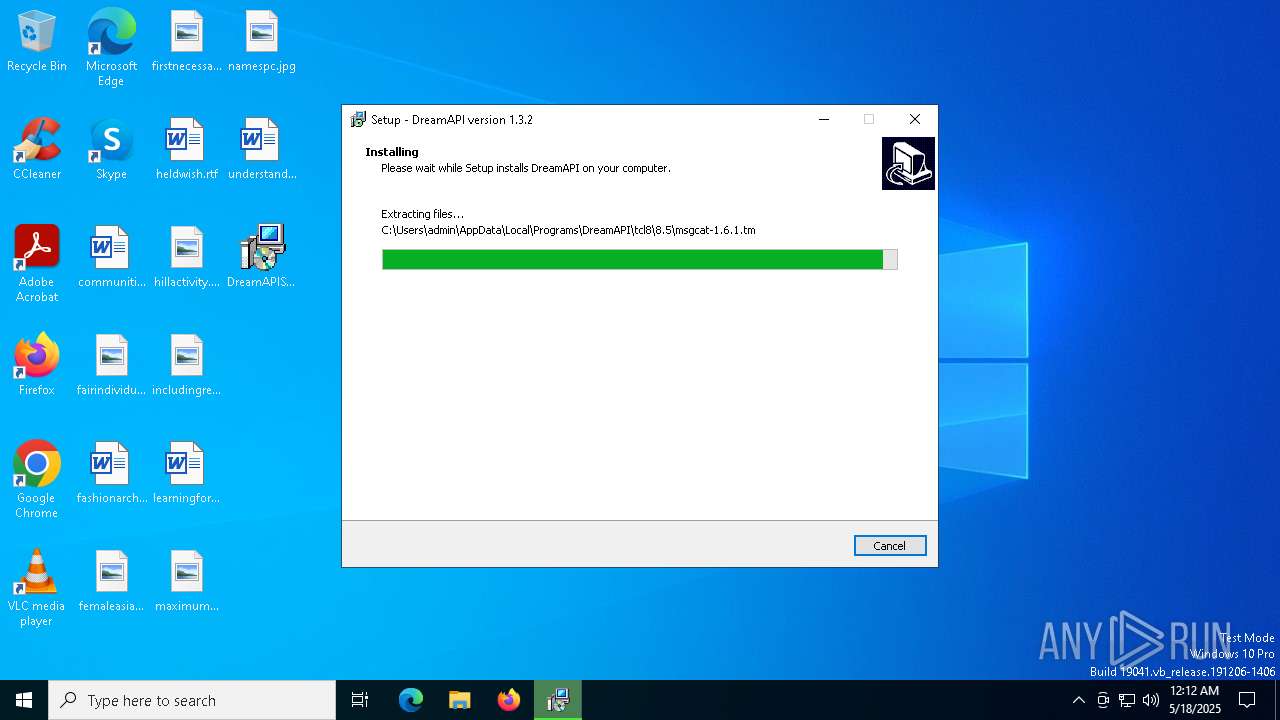
Creates files or folders in the user directory
- DreamAPISetup.tmp (PID: 7408)
The sample compiled with english language support
- DreamAPISetup.tmp (PID: 7408)
Checks proxy server information
- slui.exe (PID: 7812)
Reads the software policy settings
- slui.exe (PID: 7812)
Creates a software uninstall entry
- DreamAPISetup.tmp (PID: 7408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 09:48:30+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.2.0 |
| ProductVersionNumber: | 1.3.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | acidicoala |
| FileDescription: | DreamAPI Setup |
| FileVersion: | 1.3.2.0 |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | DreamAPI Setup |
| ProductVersion: | 1.3.2.0 |
Total processes
125
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7388 | "C:\Users\admin\Desktop\DreamAPISetup.exe" | C:\Users\admin\Desktop\DreamAPISetup.exe | explorer.exe | ||||||||||||
User: admin Company: acidicoala Integrity Level: MEDIUM Description: DreamAPI Setup Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 7408 | "C:\Users\admin\AppData\Local\Temp\is-BOE1B.tmp\DreamAPISetup.tmp" /SL5="$802AA,17703683,780800,C:\Users\admin\Desktop\DreamAPISetup.exe" | C:\Users\admin\AppData\Local\Temp\is-BOE1B.tmp\DreamAPISetup.tmp | DreamAPISetup.exe | ||||||||||||
User: admin Company: acidicoala Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 7812 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 655
Read events
3 630
Write events
25
Delete events
0
Modification events
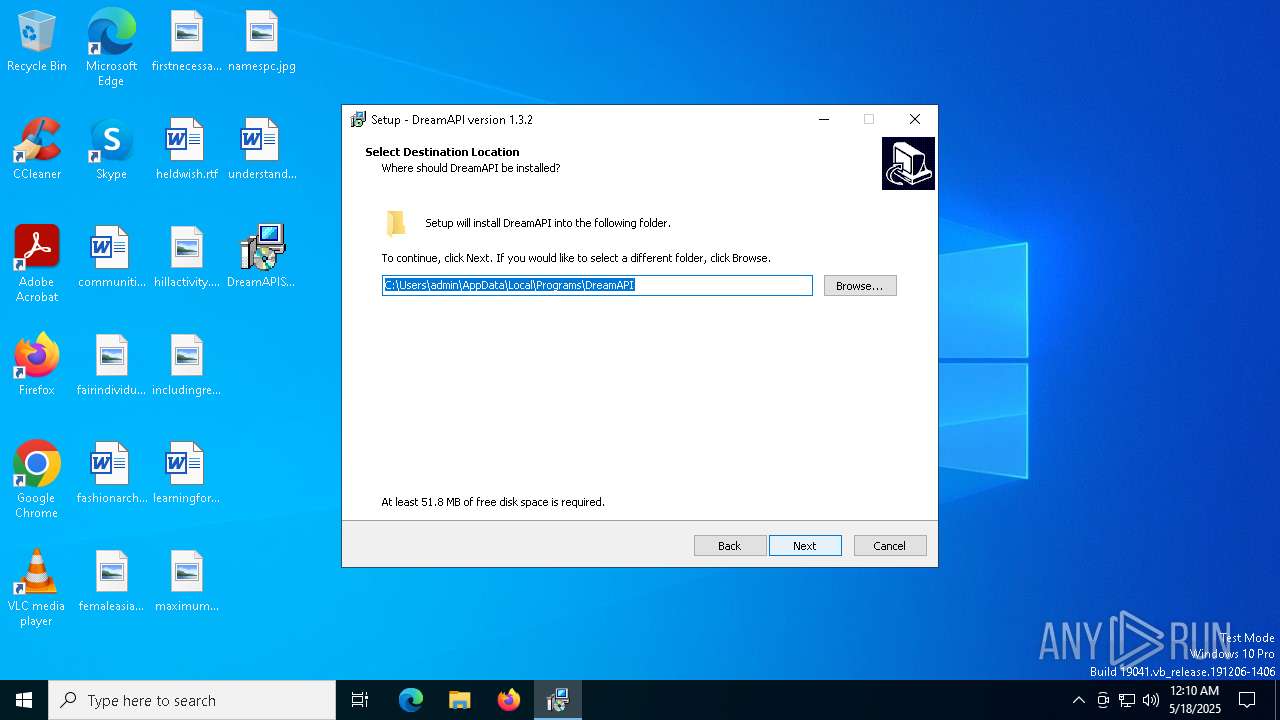
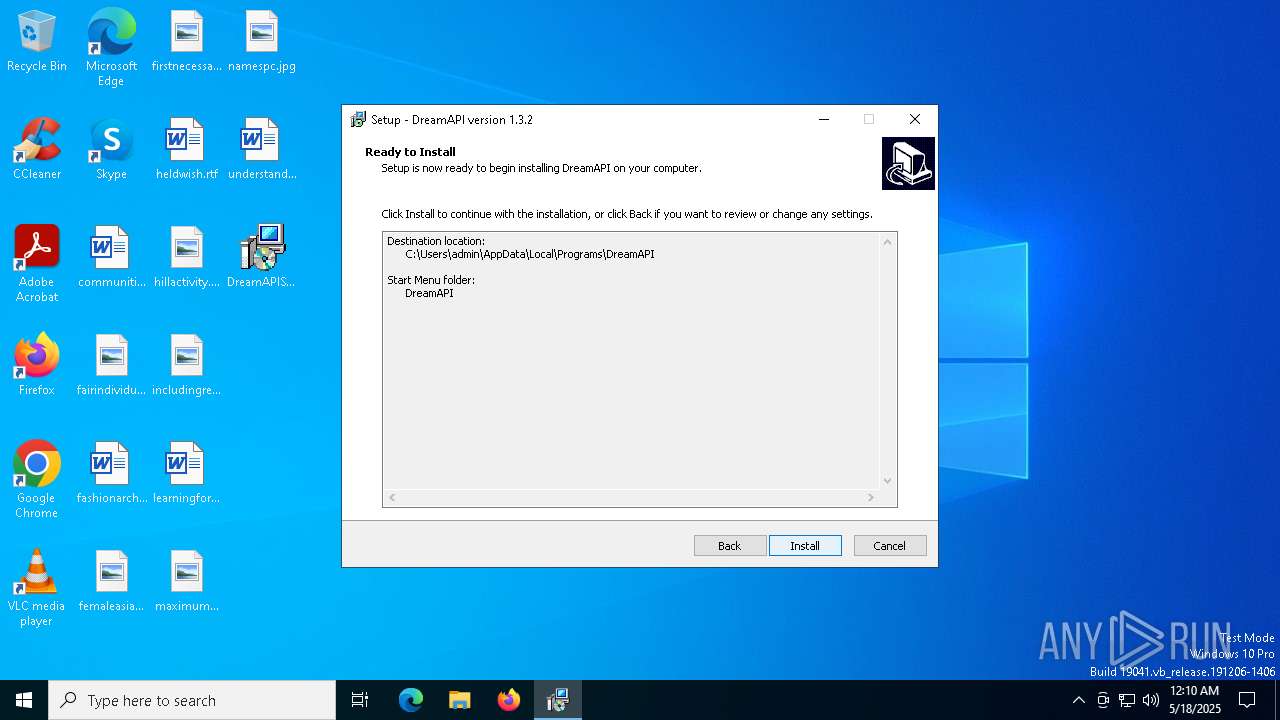
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.1.2 | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local\Programs\DreamAPI | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\DreamAPI\ | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: DreamAPI | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: desktopicon | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | DisplayName |
Value: DreamAPI version 1.3.2 | |||
| (PID) Process: | (7408) DreamAPISetup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{FF9B6947-9E8A-4075-83F6-F231A6F3DB07}_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Programs\DreamAPI\DreamAPI.exe | |||
Executable files
187
Suspicious files
11
Text files
1 856
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Temp\is-E6LM8.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7388 | DreamAPISetup.exe | C:\Users\admin\AppData\Local\Temp\is-BOE1B.tmp\DreamAPISetup.tmp | executable | |
MD5:40880CD1F35490C0F3E1F2AC444AF3F3 | SHA256:67480B5C917D7E95072F9F2F6452DCBE6B4F312CDEA2938B817C20554829561F | |||
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Programs\DreamAPI\is-IQR67.tmp | executable | |
MD5:FB08E4BC9CD4E441D9B3F9995B18C7CA | SHA256:09A6F1F11D16960C124F9CE700A6B5D9EC1947D2ABD9C64B3683BAFAB4821A6D | |||
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Programs\DreamAPI\unins000.exe | executable | |
MD5:FB08E4BC9CD4E441D9B3F9995B18C7CA | SHA256:09A6F1F11D16960C124F9CE700A6B5D9EC1947D2ABD9C64B3683BAFAB4821A6D | |||
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Programs\DreamAPI\DreamAPI.exe | executable | |
MD5:A6A01A58F50DFF2C0A2ADD88B7AF4F6C | SHA256:F8702A617B109040B9773AA22CDD8450D1F38185FD52782B9BE9914A40A8CC84 | |||
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Programs\DreamAPI\is-FSLQA.tmp | executable | |
MD5:A6A01A58F50DFF2C0A2ADD88B7AF4F6C | SHA256:F8702A617B109040B9773AA22CDD8450D1F38185FD52782B9BE9914A40A8CC84 | |||
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Programs\DreamAPI\is-4KG5G.tmp | executable | |
MD5:B65D571875079332C81963FF98E62AB3 | SHA256:B83A794600A47BE935CC562ACE7A4D531083C76FCC8AC6424D008F1034EEDF96 | |||
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Programs\DreamAPI\is-QH4UA.tmp | executable | |
MD5:B7300D7A31BC0C3ABB631F1951CC103A | SHA256:A580C502170462431A197954EADA3A2B92CDDDA8E77D489475A8FA6DA0000349 | |||
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Programs\DreamAPI\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:B7300D7A31BC0C3ABB631F1951CC103A | SHA256:A580C502170462431A197954EADA3A2B92CDDDA8E77D489475A8FA6DA0000349 | |||
| 7408 | DreamAPISetup.tmp | C:\Users\admin\AppData\Local\Programs\DreamAPI\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:5A75A7940BC8762E41DAFCCE9C07628B | SHA256:4AAF273C4CB1D93B8C8686843FFBC577D31E1C010E02AE8E72478C5B52DDA06D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
53
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7612 | SIHClient.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7612 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7612 | SIHClient.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7612 | SIHClient.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7612 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7612 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7612 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7612 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7612 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7612 | SIHClient.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |