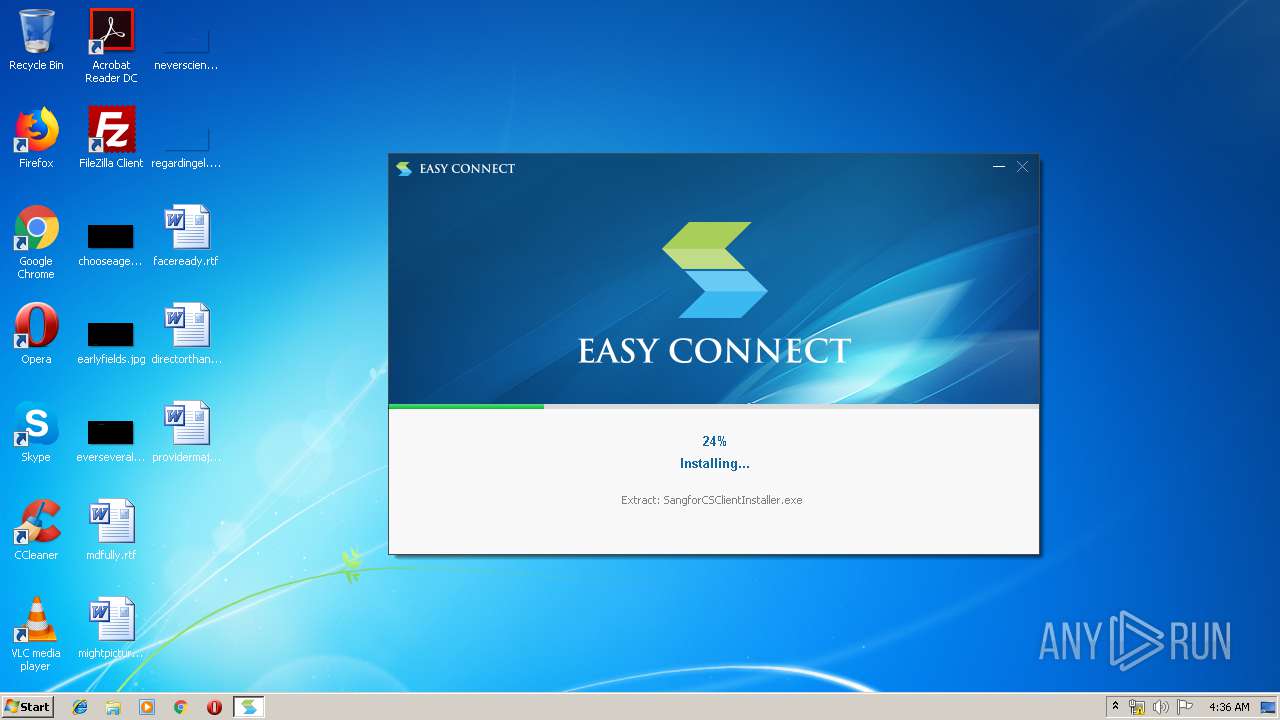
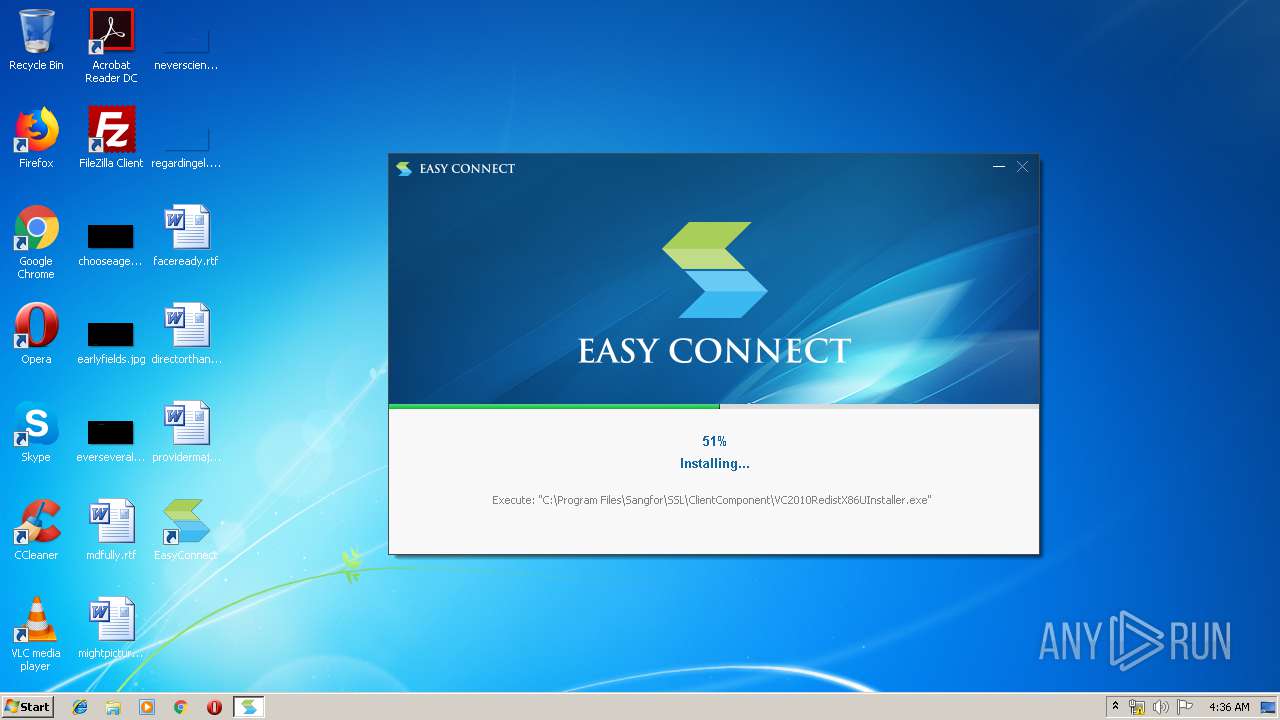
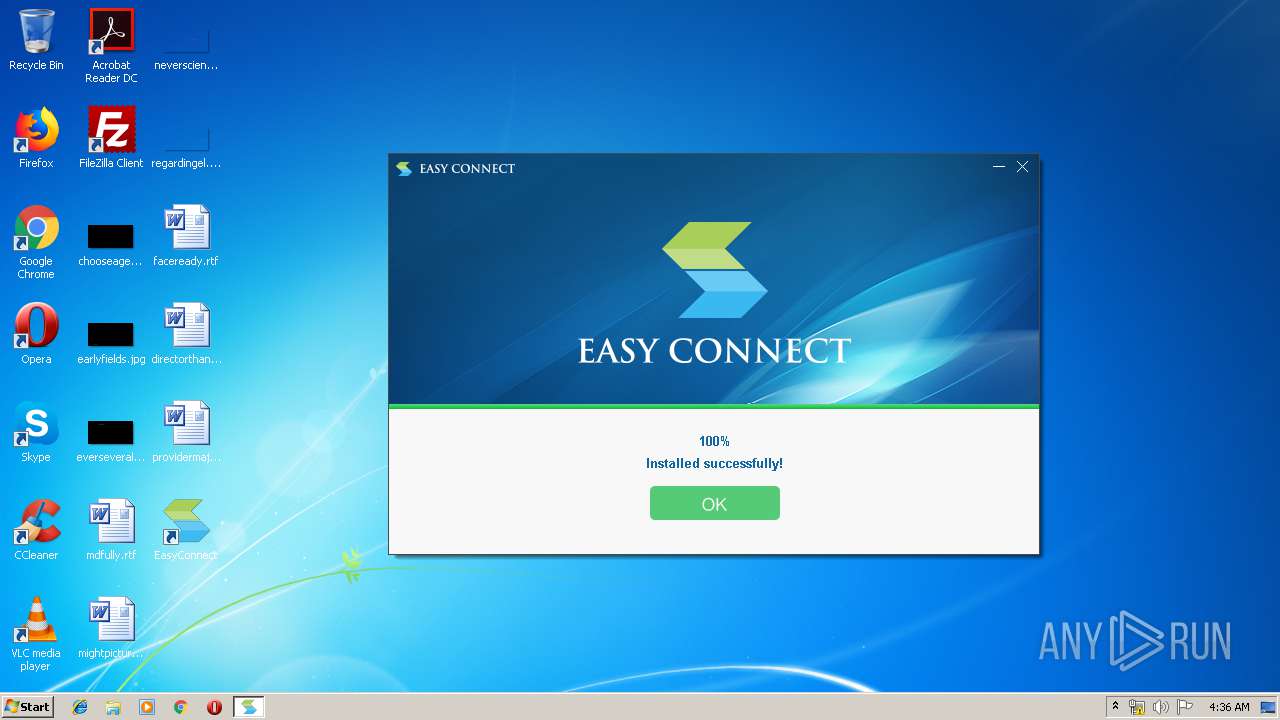
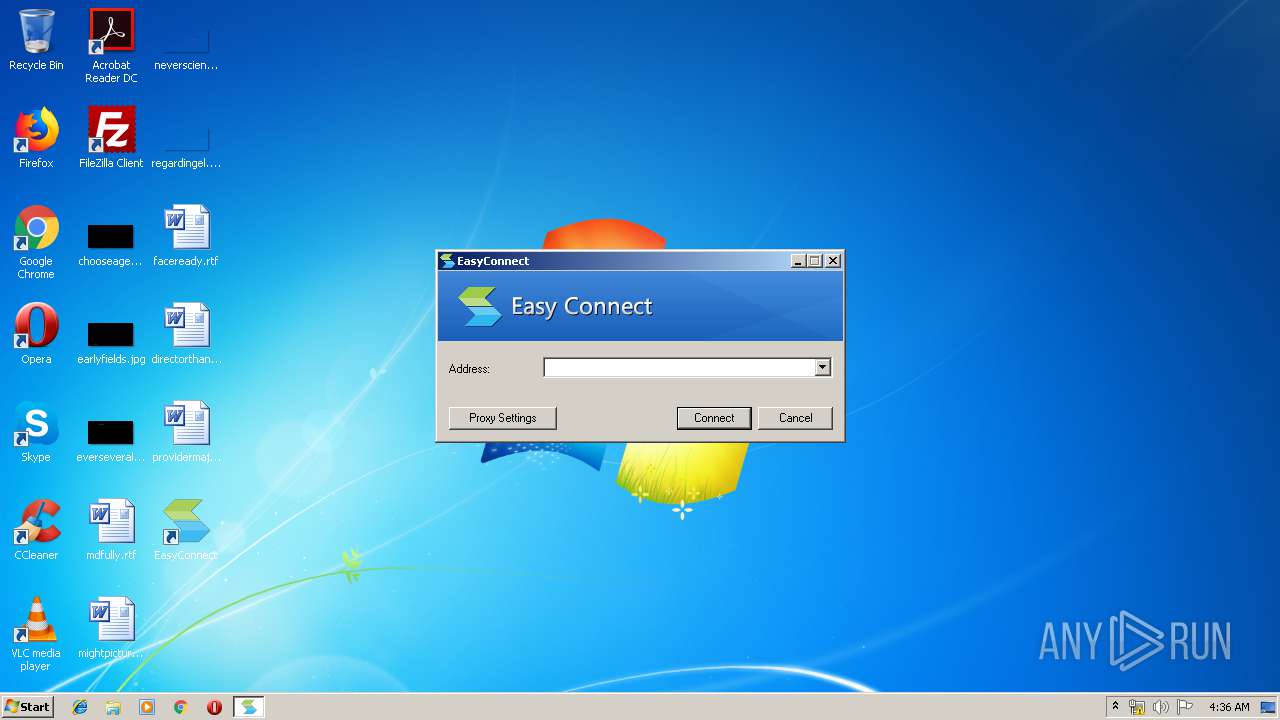
| File name: | EasyConnectInstaller.exe |
| Full analysis: | https://app.any.run/tasks/23dc7684-31dc-4e52-885b-87a4c222f6ab |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2019, 03:35:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | BB5226DB0EB0A8F0519E5A6FE231899A |
| SHA1: | 212DBB39003BBF212CC17E65A0ACD5B6D05E6929 |
| SHA256: | A3118352E8D490D4E6C25F24DEE7C4F490291870D18FB8176462B1188C74E1FA |
| SSDEEP: | 393216:/6nU9lqD55eRMIaJghtV7xyaaEh/xRoSHE4s:CI2uGZQRxyAvoIE |
MALICIOUS
Loads dropped or rewritten executable
- EasyConnectInstaller.exe (PID: 916)
- SangforCSClientInstaller.exe (PID: 3664)
- TcpDriverInstaller.exe (PID: 3276)
- SuperExeInstaller.exe (PID: 1424)
- SangforServiceClientInstaller.exe (PID: 3988)
- InstallControl.exe (PID: 2084)
- ECAgent.exe (PID: 2364)
- SangforPromoteService.exe (PID: 2428)
- ECBaseInstaller.exe (PID: 3380)
- ECAgent.exe (PID: 3004)
- ECAgent.exe (PID: 1712)
- SangforCSClient.exe (PID: 2552)
- SangforPromote.exe (PID: 3348)
- SangforPromote.exe (PID: 952)
- SangforUD.exe (PID: 3688)
Application was dropped or rewritten from another process
- Uninstall.exe (PID: 3176)
- SangforCSClientInstaller.exe (PID: 3664)
- TcpDriverInstaller.exe (PID: 3276)
- Remove.exe (PID: 4028)
- DnsDriverInstaller.exe (PID: 1672)
- Install.exe (PID: 2704)
- Remove.exe (PID: 3908)
- SuperExeInstaller.exe (PID: 1424)
- Install.exe (PID: 2460)
- ns5177.tmp (PID: 3604)
- SangforServiceClientInstaller.exe (PID: 3988)
- VC2010RedistX86UInstaller.exe (PID: 3044)
- InstallControl.exe (PID: 2084)
- SJobberInstaller.exe (PID: 968)
- SangforUpdateInstaller.exe (PID: 3856)
- SangforRAppInstaller.exe (PID: 3364)
- ns5445.tmp (PID: 3168)
- ECBaseInstaller.exe (PID: 3380)
- ECAgentInstaller.exe (PID: 3524)
- SuperServiceInstaller.exe (PID: 2244)
- ECAgent.exe (PID: 2364)
- SangforPromoteService.exe (PID: 3228)
- ECAgent.exe (PID: 3004)
- ECAgent.exe (PID: 1712)
- SangforPromoteService.exe (PID: 2428)
- SangforPromote.exe (PID: 3348)
- SangforCSClient.exe (PID: 2552)
- SangforPromoteService.exe (PID: 2104)
- SangforPromote.exe (PID: 952)
- SangforUD.exe (PID: 3688)
Changes settings of System certificates
- SangforPromoteService.exe (PID: 2428)
- ECAgent.exe (PID: 3004)
SUSPICIOUS
Creates files in the program directory
- EasyConnectInstaller.exe (PID: 916)
- SangforCSClientInstaller.exe (PID: 3664)
- TcpDriverInstaller.exe (PID: 3276)
- SuperExeInstaller.exe (PID: 1424)
- DnsDriverInstaller.exe (PID: 1672)
- expand.exe (PID: 2076)
- SangforServiceClientInstaller.exe (PID: 3988)
- SJobberInstaller.exe (PID: 968)
- SangforUpdateInstaller.exe (PID: 3856)
- SangforRAppInstaller.exe (PID: 3364)
- InstallControl.exe (PID: 2084)
- expand.exe (PID: 1868)
- ECBaseInstaller.exe (PID: 3380)
- ECAgentInstaller.exe (PID: 3524)
- SuperServiceInstaller.exe (PID: 2244)
Executable content was dropped or overwritten
- EasyConnectInstaller.exe (PID: 916)
- SangforCSClientInstaller.exe (PID: 3664)
- TcpDriverInstaller.exe (PID: 3276)
- DnsDriverInstaller.exe (PID: 1672)
- SuperExeInstaller.exe (PID: 1424)
- expand.exe (PID: 2076)
- SangforUpdateInstaller.exe (PID: 3856)
- SJobberInstaller.exe (PID: 968)
- SangforRAppInstaller.exe (PID: 3364)
- InstallControl.exe (PID: 2084)
- expand.exe (PID: 1868)
- SangforServiceClientInstaller.exe (PID: 3988)
- VC2010RedistX86UInstaller.exe (PID: 3044)
- ECBaseInstaller.exe (PID: 3380)
- ECAgentInstaller.exe (PID: 3524)
- SuperServiceInstaller.exe (PID: 2244)
Creates COM task schedule object
- EasyConnectInstaller.exe (PID: 916)
- InstallControl.exe (PID: 2084)
Creates files in the Windows directory
- EasyConnectInstaller.exe (PID: 916)
- SangforCSClientInstaller.exe (PID: 3664)
- expand.exe (PID: 2076)
- ECAgent.exe (PID: 3004)
Creates a software uninstall entry
- SangforCSClientInstaller.exe (PID: 3664)
Modifies the open verb of a shell class
- SangforCSClientInstaller.exe (PID: 3664)
Starts application with an unusual extension
- SuperExeInstaller.exe (PID: 1424)
- SangforServiceClientInstaller.exe (PID: 3988)
Creates files in the user directory
- ECAgent.exe (PID: 2364)
- ECAgent.exe (PID: 1712)
- SangforCSClient.exe (PID: 2552)
Removes files from Windows directory
- EasyConnectInstaller.exe (PID: 916)
- ECAgent.exe (PID: 3004)
Adds / modifies Windows certificates
- SangforPromoteService.exe (PID: 2428)
INFO
Dropped object may contain Bitcoin addresses
- SangforCSClient.exe (PID: 2552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:53:18+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 124928 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x36a0 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.6.6.1 |
| ProductVersionNumber: | 7.6.6.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Chinese (Simplified) |
| FileDescription: | EasyConnect |
| FileVersion: | 7.6.6.1 |
| LegalCopyright: | Copyright (C) 2018 |
| LegalTrademarks: | SANGFOR, Inc. |
| ProductName: | EasyConnect |
| ProductVersion: | 7,6,6,1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:53:18 |
| Detected languages: |
|
| FileDescription: | EasyConnect |
| FileVersion: | 7.6.6.1 |
| LegalCopyright: | Copyright (C) 2018 |
| LegalTrademarks: | SANGFOR, Inc. |
| ProductName: | EasyConnect |
| ProductVersion: | 7,6,6,1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:53:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000061A4 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44297 |
.rdata | 0x00008000 | 0x000011E0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.3067 |
.data | 0x0000A000 | 0x0001C3F8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.1303 |
.ndata | 0x00027000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00035000 | 0x0001A480 | 0x0001A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.89081 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.87125 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 4.32403 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.57732 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 4.76878 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 5.09933 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.93166 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73119 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.74597 | 408 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
70
Monitored processes
34
Malicious processes
13
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Users\admin\AppData\Local\Temp\EasyConnectInstaller.exe" | C:\Users\admin\AppData\Local\Temp\EasyConnectInstaller.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: EasyConnect Exit code: 0 Version: 7.6.6.1 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Sangfor\SSL\Promote\SangforPromote.exe" | C:\Program Files\Sangfor\SSL\Promote\SangforPromote.exe | SangforPromoteService.exe | ||||||||||||
User: SYSTEM Company: Sangfor Technologies Inc. Integrity Level: SYSTEM Description: SangforPromote Exit code: 0 Version: 7, 6, 3, 0 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Sangfor\SSL\ClientComponent\SJobberInstaller.exe" -SessionId=-1 | C:\Program Files\Sangfor\SSL\ClientComponent\SJobberInstaller.exe | EasyConnectInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Sangfor\SSL\ClientComponent\SuperExeInstaller.exe" -SessionId=-1 | C:\Program Files\Sangfor\SSL\ClientComponent\SuperExeInstaller.exe | EasyConnectInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Sangfor\SSL\ClientComponent\DnsDriverInstaller.exe" -SessionId=-1 | C:\Program Files\Sangfor\SSL\ClientComponent\DnsDriverInstaller.exe | EasyConnectInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Sangfor\SSL\ECAgent\ECAgent.exe" --from-sp | C:\Program Files\Sangfor\SSL\ECAgent\ECAgent.exe | SangforPromoteService.exe | ||||||||||||
User: admin Company: Sangfor Technologies Inc. Integrity Level: MEDIUM Description: Agent for EasyConnect Exit code: 0 Version: 7,6,6,1 Modules
| |||||||||||||||
| 1868 | "expand.exe" -r "C:\Program Files\Sangfor\SSL\SangforServiceClient\SangforServiceClient.CAB" "C:\Program Files\Sangfor\SSL\SangforServiceClient" | C:\Windows\system32\expand.exe | ns5445.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | "expand.exe" -r "C:\Program Files\Sangfor\SSL\Promote\SangforPromote.CAB" "C:\Program Files\Sangfor\SSL\Promote" | C:\Windows\system32\expand.exe | ns5177.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Sangfor\SSL\ClientComponent\InstallControl.exe" -SessionId=-1 | C:\Program Files\Sangfor\SSL\ClientComponent\InstallControl.exe | EasyConnectInstaller.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Sangfor\SSL\Promote\SangforPromoteService.exe" -/StartServer | C:\Program Files\Sangfor\SSL\Promote\SangforPromoteService.exe | SuperServiceInstaller.exe | ||||||||||||
User: admin Company: Sangfor Technologies Inc. Integrity Level: HIGH Description: Promote Service Exit code: 1 Version: 7, 6, 3, 0 Modules
| |||||||||||||||
Total events
1 831
Read events
839
Write events
826
Delete events
166
Modification events
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CSClientManagerPrj.CSClientManager |
| Operation: | write | Name: | |
Value: CSClientManager Class | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CSClientManagerPrj.CSClientManager\CLSID |
| Operation: | write | Name: | |
Value: {F257CF85-8E97-4C9B-8407-459B28007631} | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CSClientManagerPrj.CSClientManager\CurVer |
| Operation: | write | Name: | |
Value: CSClientManagerPrj.CSClientManager.1 | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CSClientManagerPrj.CSClientManager.1 |
| Operation: | write | Name: | |
Value: CSClientManager Class | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CSClientManagerPrj.CSClientManager.1\CLSID |
| Operation: | write | Name: | |
Value: {F257CF85-8E97-4C9B-8407-459B28007631} | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F257CF85-8E97-4C9B-8407-459B28007631} |
| Operation: | write | Name: | |
Value: CSClientManager Class | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F257CF85-8E97-4C9B-8407-459B28007631}\ProgID |
| Operation: | write | Name: | |
Value: CSClientManagerPrj.CSClientManager.1 | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F257CF85-8E97-4C9B-8407-459B28007631}\VersionIndependentProgID |
| Operation: | write | Name: | |
Value: CSClientManagerPrj.CSClientManager | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F257CF85-8E97-4C9B-8407-459B28007631}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Program Files\Sangfor\SSL\ClientComponent\CSClientManagerPrj.dll | |||
| (PID) Process: | (916) EasyConnectInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F257CF85-8E97-4C9B-8407-459B28007631}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
Executable files
108
Suspicious files
5
Text files
21
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | EasyConnectInstaller.exe | C:\Windows\system32\SangforInstallHelper.dll | executable | |
MD5:— | SHA256:— | |||
| 916 | EasyConnectInstaller.exe | C:\Program Files\Sangfor\SSL\ClientComponent\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 916 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse18B2.tmp\btn_finish_en.bmp | image | |
MD5:C0F1CB5CA40A8A2AD4844644655CB0D4 | SHA256:8D7E8A02CE5580D19B6CA75A23B72BC426F0A0CADFD521B1716CCF63F5C00971 | |||
| 916 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse18B2.tmp\System.dll | executable | |
MD5:315ACA574311D0622D91D498BFE1AE66 | SHA256:B03832D636CC508D7C8DFCCEEF29454D786E4AE3EFABFB7BB5D49B84E049EF33 | |||
| 916 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse18B2.tmp\bg.bmp | image | |
MD5:F194D602F7CD5810D0F7C221C5359586 | SHA256:35E80485E17C3C6EF779FF8197F066E7AE0E8AFF87149A37A32AE264CF0AF7DD | |||
| 916 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse18B2.tmp\btn_finish_cn.bmp | image | |
MD5:71607B1DD8E735196DBED039BDBAEAF5 | SHA256:5E36F3A5686695A302F2B1066069119C0374DE7D31093153F716DD40EE18BD48 | |||
| 916 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse18B2.tmp\btn_mini.bmp | image | |
MD5:89F661E7046201913DCA29B752148B70 | SHA256:08A09B319267BB46BCD9A25D9F154A9F4285CFF781D196D88CC77609E685B554 | |||
| 916 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse18B2.tmp\progress_h.bmp | image | |
MD5:7A8B397B96244D5E95352E8F5C44A6B7 | SHA256:82A6721F4BD377B8A57C59928F120CB36C622378D2E808A4CBB9F8407999FA73 | |||
| 916 | EasyConnectInstaller.exe | C:\Users\admin\AppData\Local\Temp\nse18B2.tmp\btn_close.bmp | image | |
MD5:4BC3A7F6B8FDCEAAD9AC67A966273219 | SHA256:15BA4F22EB3B1866A93A6CEDAC016BF67BF3576AF2DF64A03B64253C4CF99BF0 | |||
| 916 | EasyConnectInstaller.exe | C:\Program Files\Sangfor\SSL\ClientComponent\nd_dkey_v2.CAB | compressed | |
MD5:9671E3D4DBAB15EB26205FC523BD481D | SHA256:A93E69EAFF8DC3532872464C11A70B5D1691C1299CDABD82E86790895DA7A3F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2552 | SangforCSClient.exe | GET | 200 | 61.175.193.50:80 | http://rvpn.zju.edu.cn/ | CN | html | 8.00 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2552 | SangforCSClient.exe | 61.175.193.50:80 | rvpn.zju.edu.cn | No.31,Jin-rong Street | CN | unknown |
2552 | SangforCSClient.exe | 61.175.193.50:443 | rvpn.zju.edu.cn | No.31,Jin-rong Street | CN | unknown |
2552 | SangforCSClient.exe | 210.32.174.2:443 | edurvpn.zju.edu.cn | China Education and Research Network Center | CN | unknown |
2552 | SangforCSClient.exe | 218.108.88.254:443 | cncrvpn.zju.edu.cn | Huashu media&Network Limited | CN | unknown |
2552 | SangforCSClient.exe | 124.160.105.200:443 | curvpn.zju.edu.cn | CHINA UNICOM China169 Backbone | CN | unknown |
3688 | SangforUD.exe | 218.108.88.254:443 | cncrvpn.zju.edu.cn | Huashu media&Network Limited | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rvpn.zju.edu.cn |
| unknown |
cncrvpn.zju.edu.cn |
| unknown |
curvpn.zju.edu.cn |
| unknown |
edurvpn.zju.edu.cn |
| unknown |
Threats
Process | Message |
|---|---|
EasyConnectInstaller.exe | open registry(SOFTWARE\Sangfor\SSL\VPN\Sessions\IDTable) failed, errcode = 2 |
EasyConnectInstaller.exe | open registry(SOFTWARE\Sangfor\SSL\VPN\Sessions\IDTable) failed, errcode = 2 |
EasyConnectInstaller.exe | registry(SOFTWARE\Sangfor\SSL\VPN\Sessions\IDTable) not found |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is HTHMAC.HTHMACCtrl.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is FT_ND_SC.ePsM8SC.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is CSClientManagerPrj.CSClientManager.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is SangforBHO.SangforIEBHO.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is SangforBHO.SangforHelper.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is ProxyIE.CSProxy.1 |
Uninstall.exe | [Uninstall]Deal_Com the ProgId is ProxyIE_X64.CSProxy.1 |