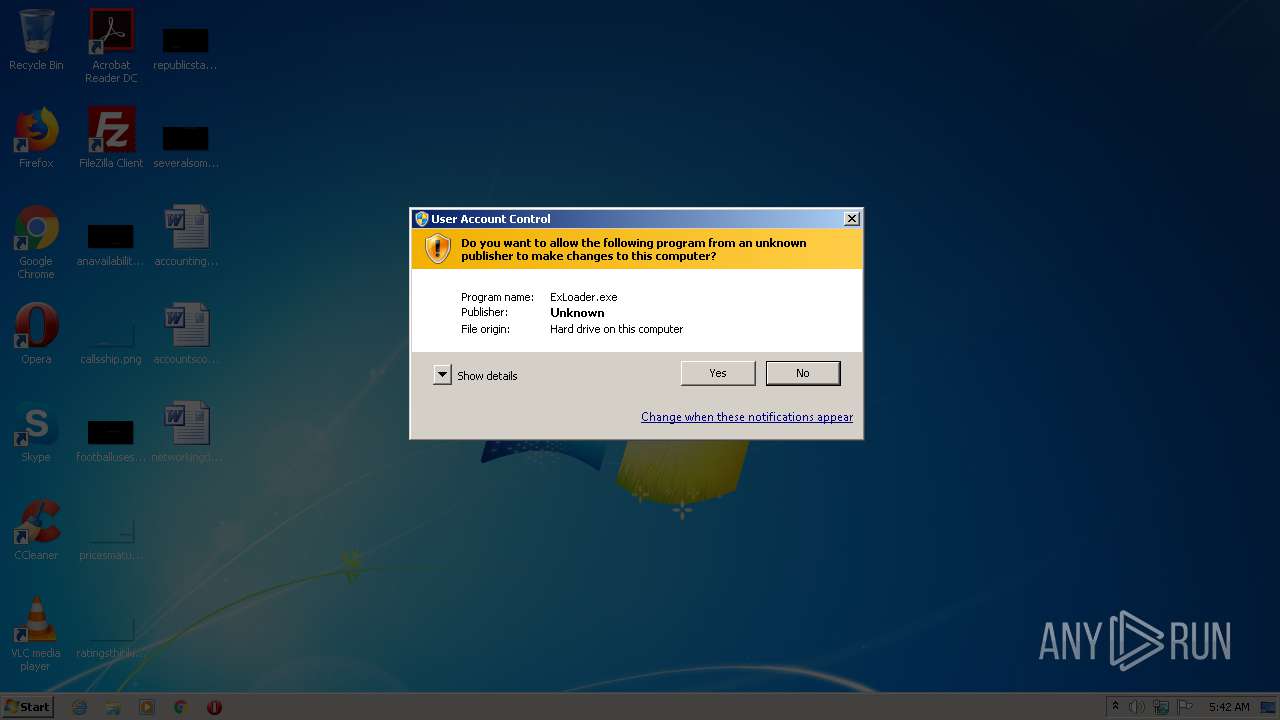
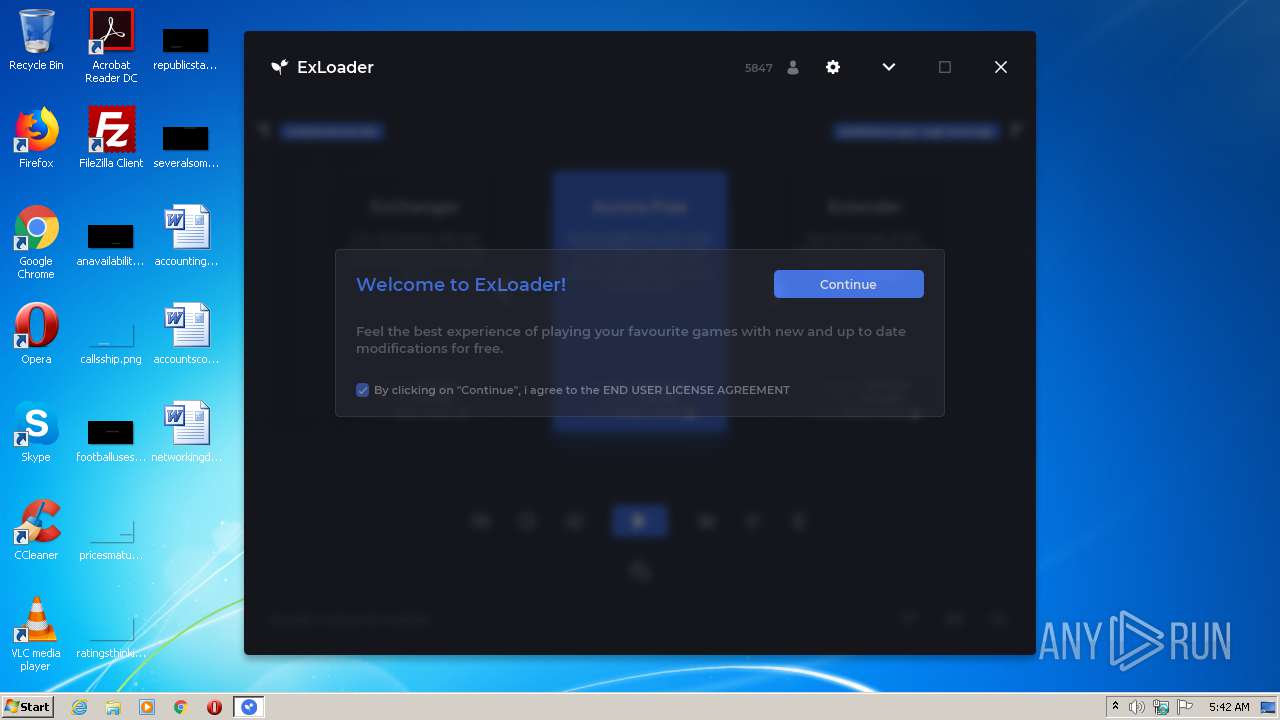
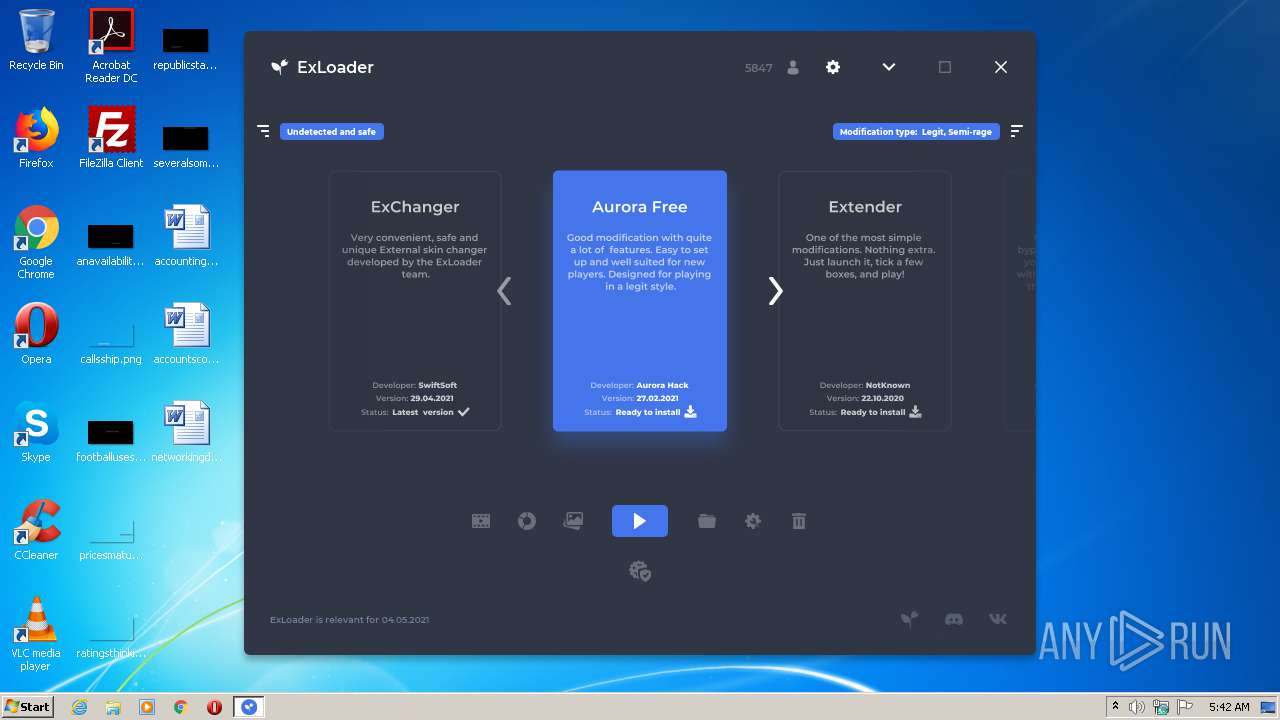
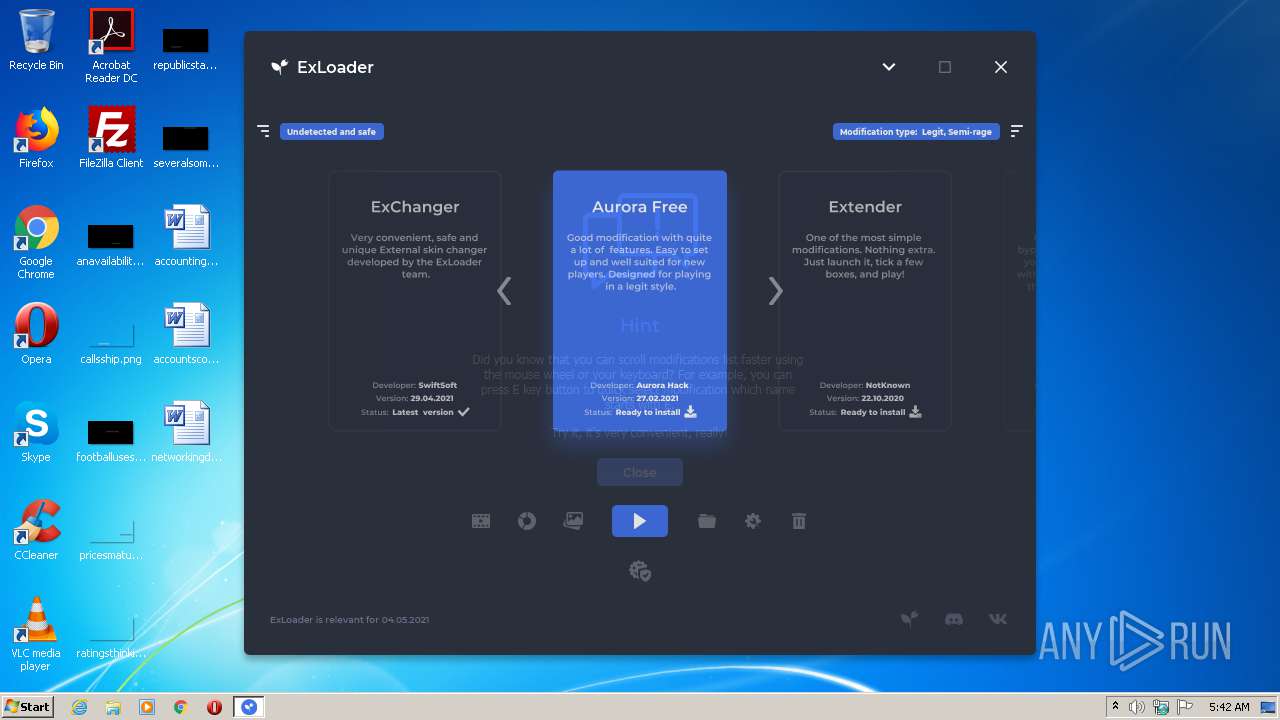
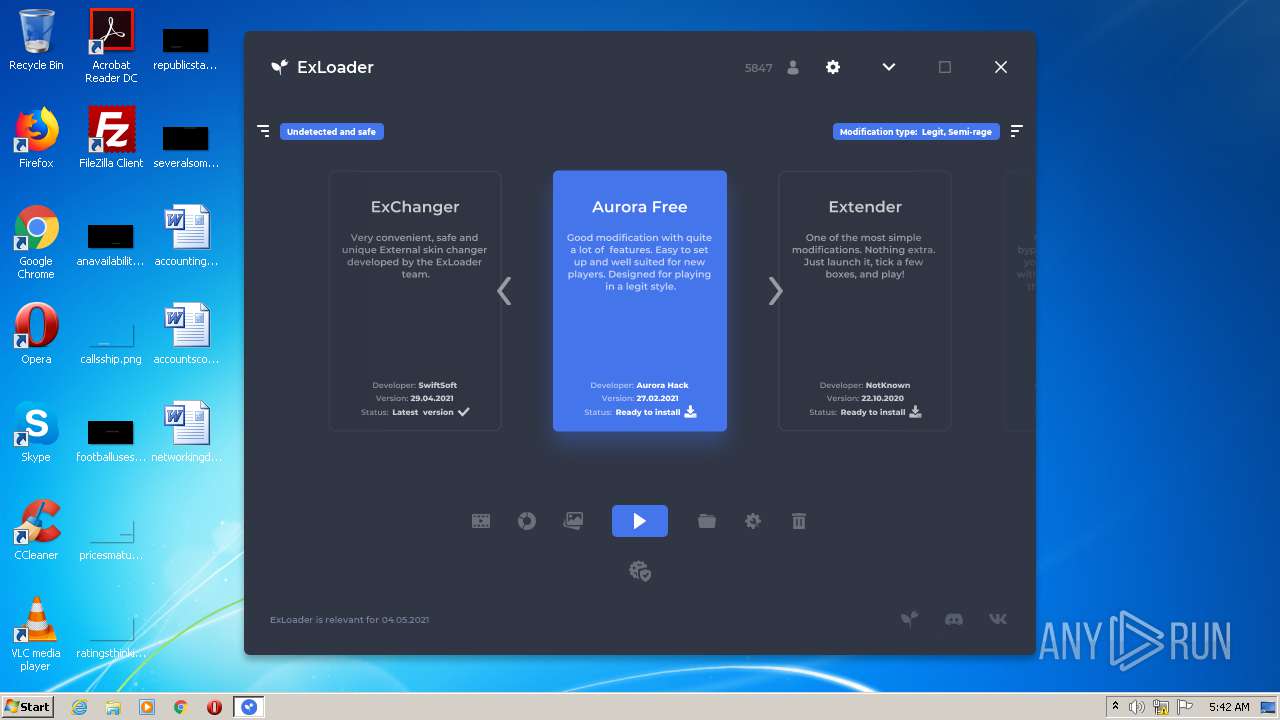
| File name: | ExLoader.exe |
| Full analysis: | https://app.any.run/tasks/bd5e6122-d216-4a84-963e-1bbf622eaf69 |
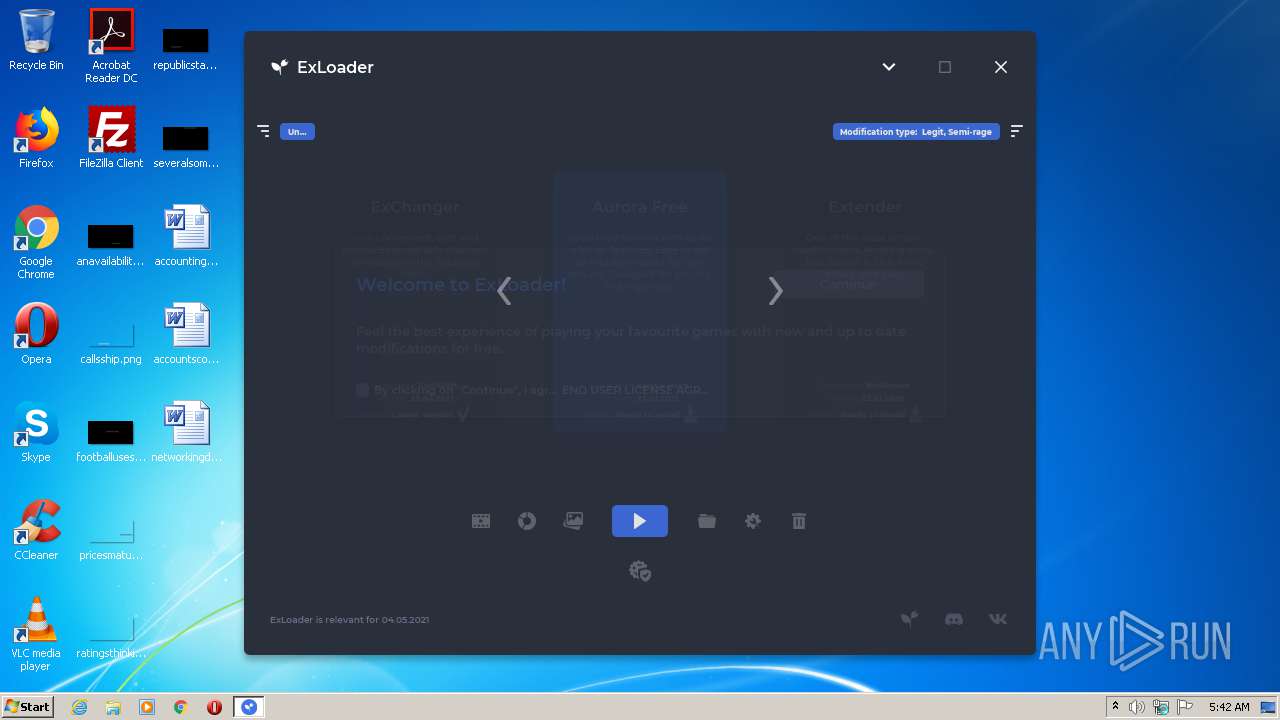
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2021, 04:41:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 270D9ADBE1F297DC654CC8DB4127785D |
| SHA1: | 55542D95F37C71112DB8AD2B51E2E1877B596D75 |
| SHA256: | A3030DFC7D019654CB7CE04C711F343E0B4E8EFB6914BFC8912EC7C828189092 |
| SSDEEP: | 196608:RIfZlqv+JHZXo/Bhf7h07ByJ6XFBhriiXXK2oPjY6oNUUPXPs:ef0c5Xo/vfF07QJ6XJrBHXo7eNU1 |
MALICIOUS
Loads dropped or rewritten executable
- javaw.exe (PID: 1816)
SUSPICIOUS
Creates files in the user directory
- javaw.exe (PID: 1816)
- powershell.exe (PID: 2072)
Creates files in the program directory
- javaw.exe (PID: 1816)
- javaw.exe (PID: 2952)
Starts application with an unusual extension
- cmd.exe (PID: 1856)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 3524)
- cmd.exe (PID: 1916)
- cmd.exe (PID: 972)
Executes JAVA applets
- ExLoader.exe (PID: 2712)
- ExLoader.exe (PID: 2372)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 1816)
- javaw.exe (PID: 2952)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 972)
- cmd.exe (PID: 3524)
- cmd.exe (PID: 1856)
- cmd.exe (PID: 1916)
- cmd.exe (PID: 2132)
Checks Windows language
- reg.exe (PID: 3248)
- reg.exe (PID: 1824)
Executes PowerShell scripts
- javaw.exe (PID: 1816)
Uses TASKKILL.EXE to kill process
- javaw.exe (PID: 1816)
Executable content was dropped or overwritten
- javaw.exe (PID: 1816)
INFO
Checks supported languages
- reg.exe (PID: 3248)
- reg.exe (PID: 1824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
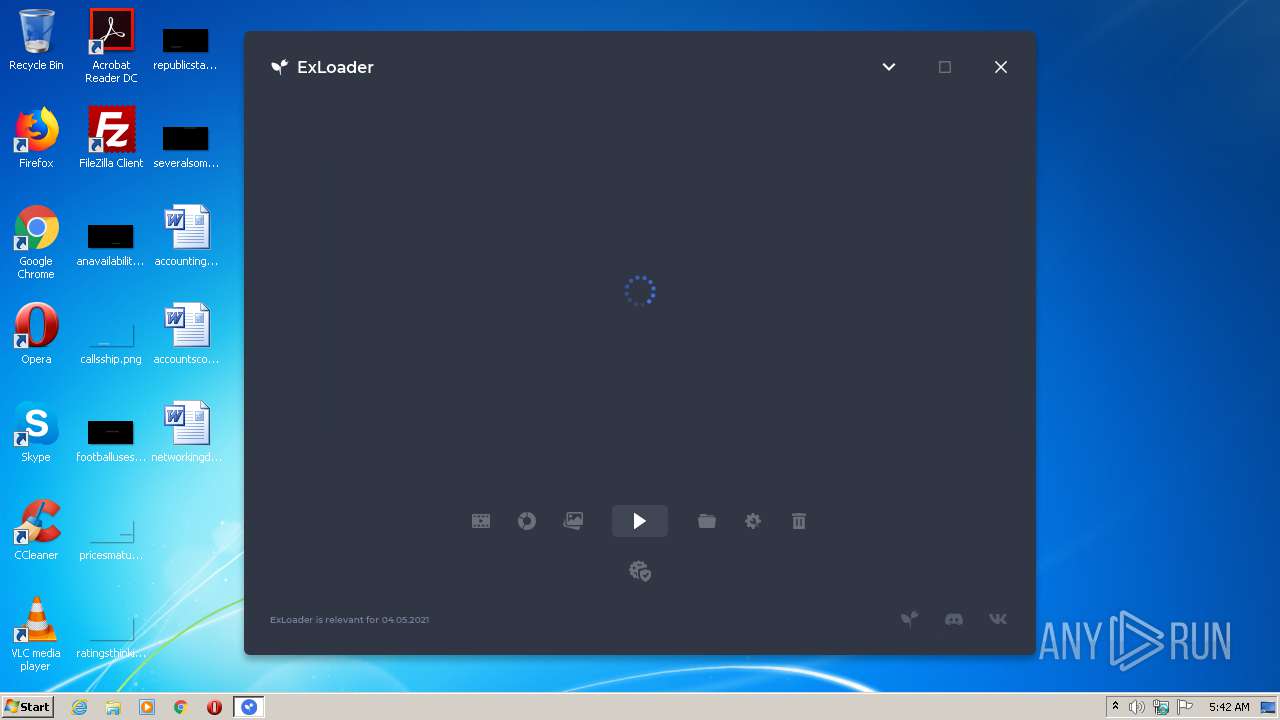
| ProductVersion: | 2.5.24.0 |
|---|---|
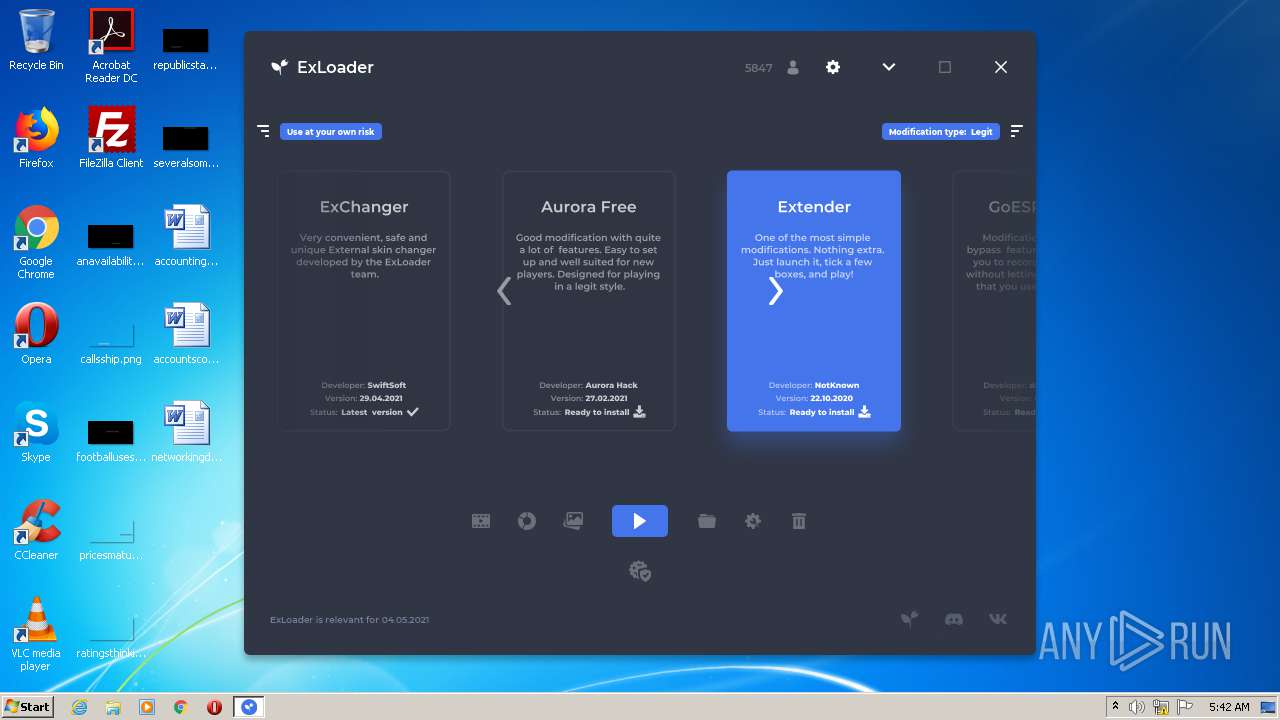
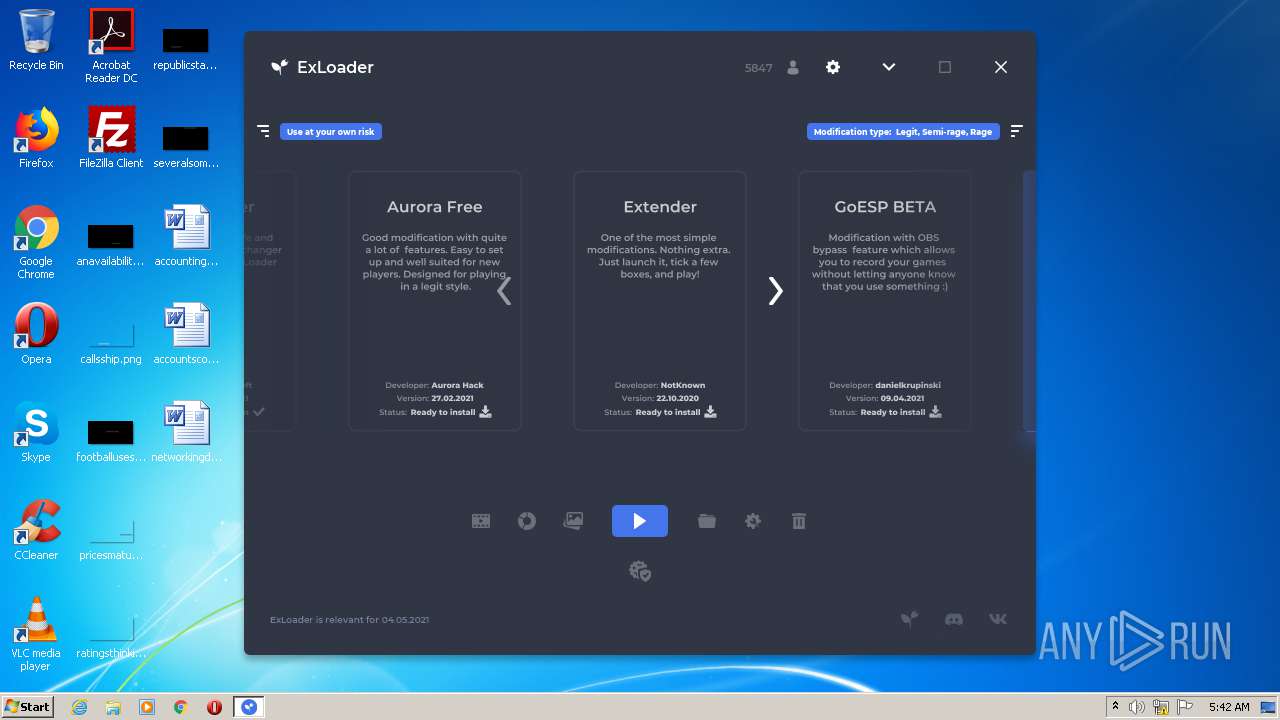
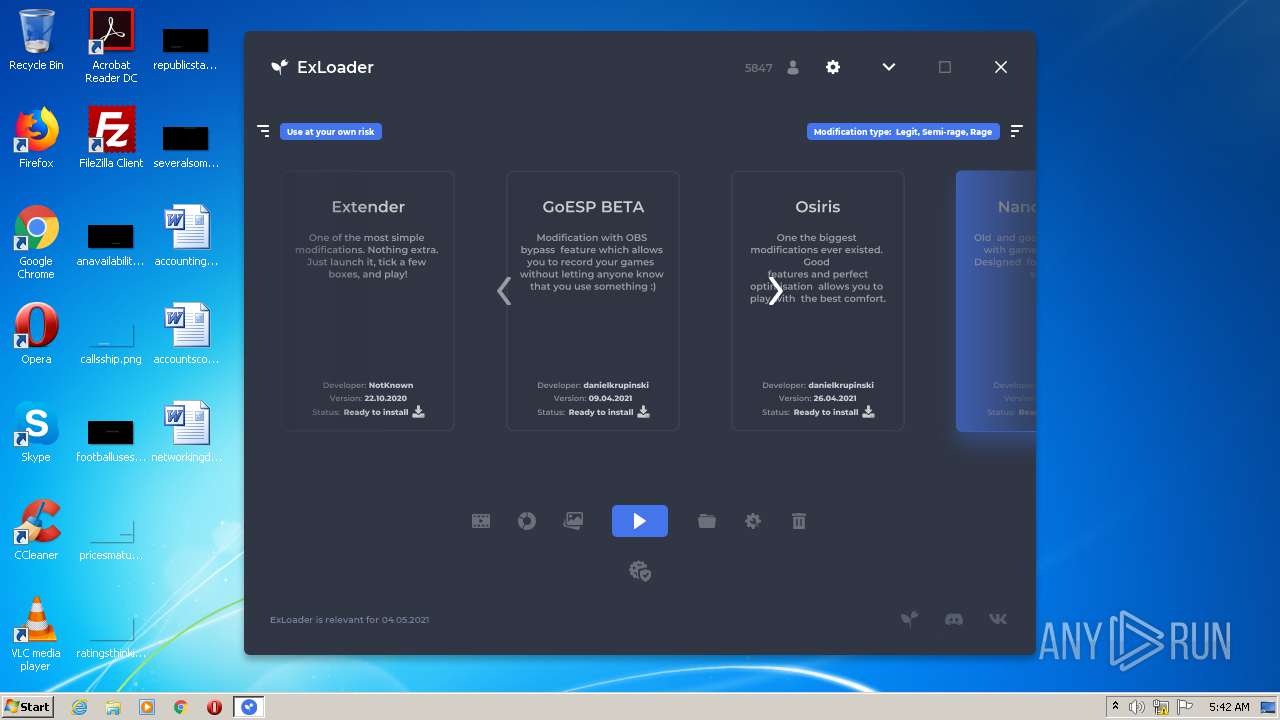
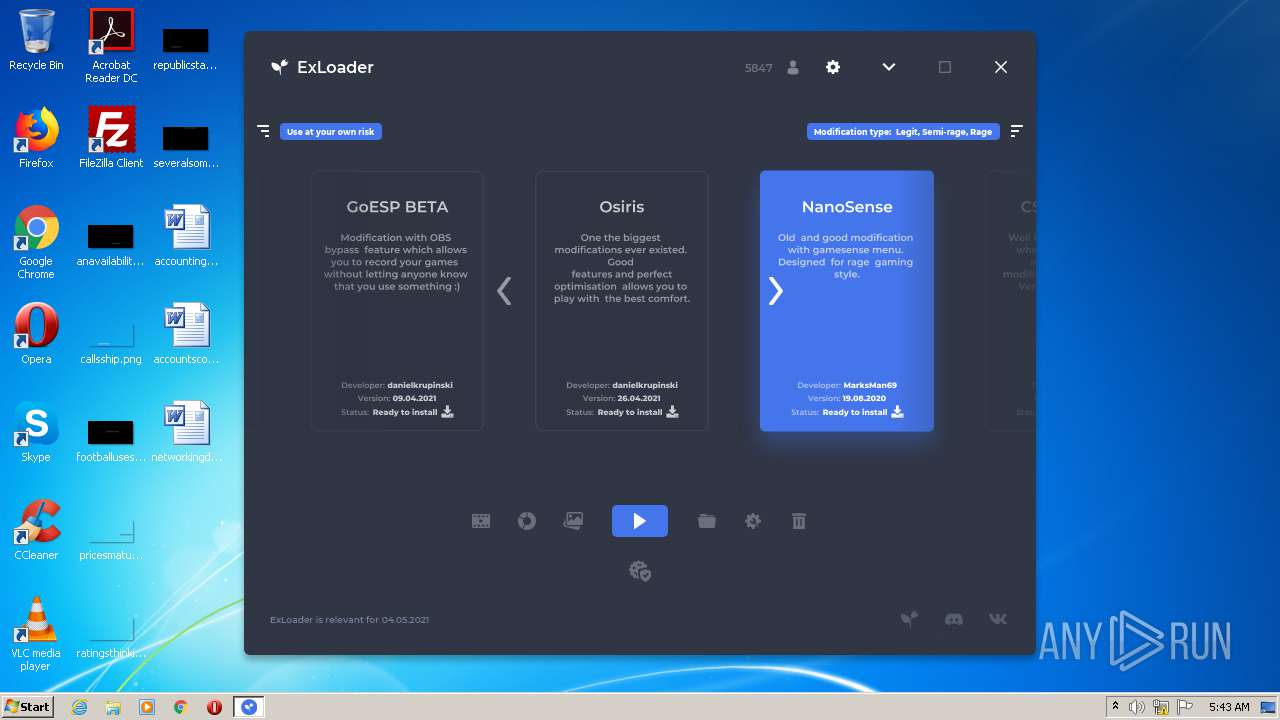
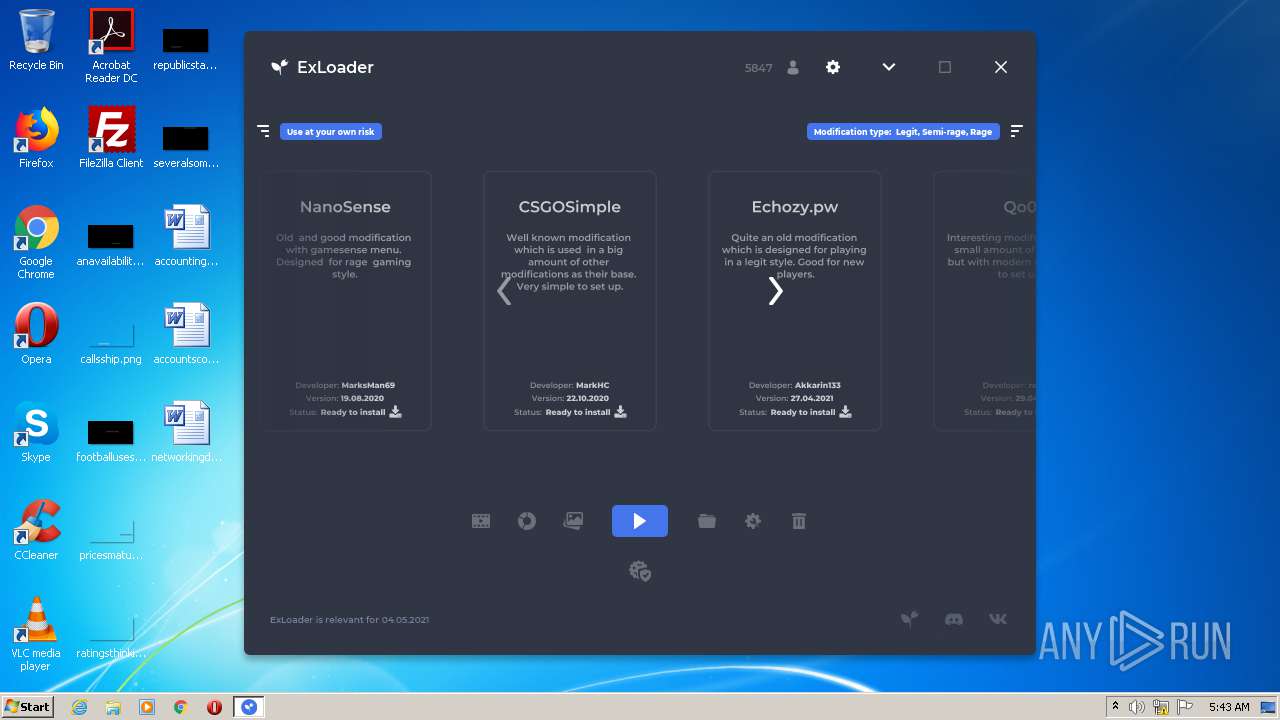
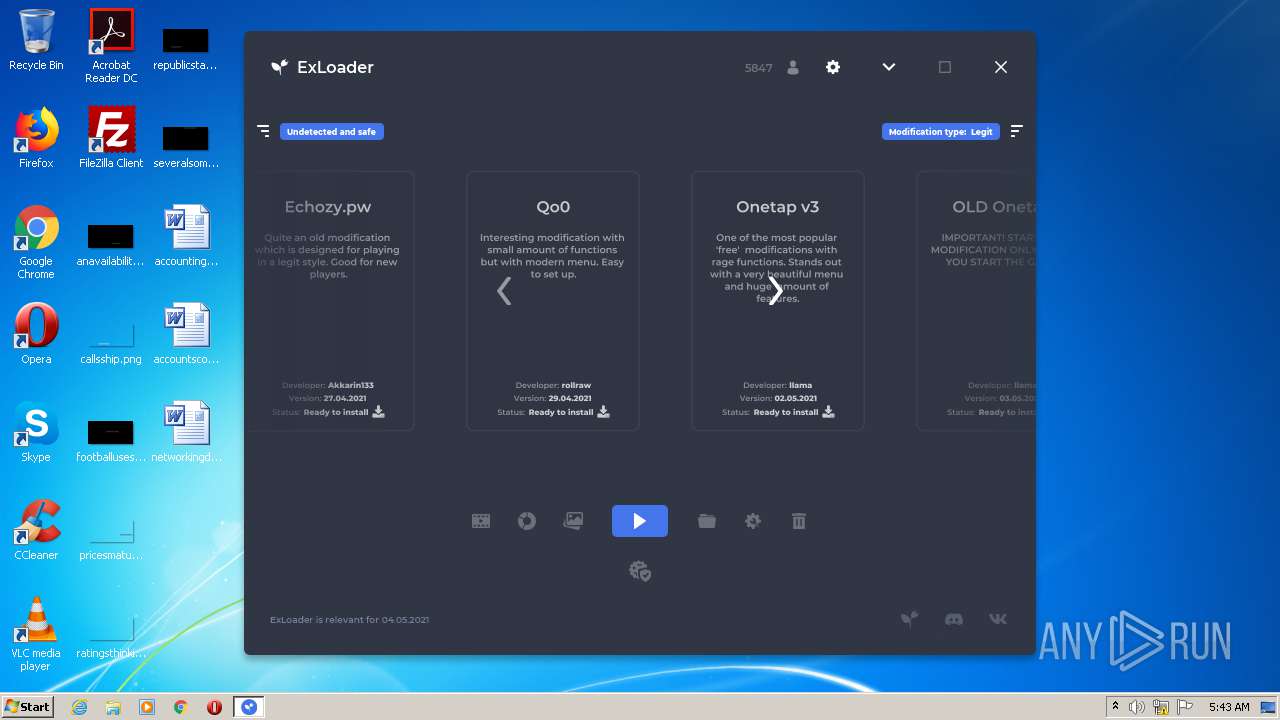
| ProductName: | ExLoader |
| OriginalFileName: | ExLoader.exe |
| LegalTrademarks: | ExLoader |
| LegalCopyright: | SwiftSoft LLC |
| InternalName: | ExLoader |
| FileVersion: | 2.5.24.0 |
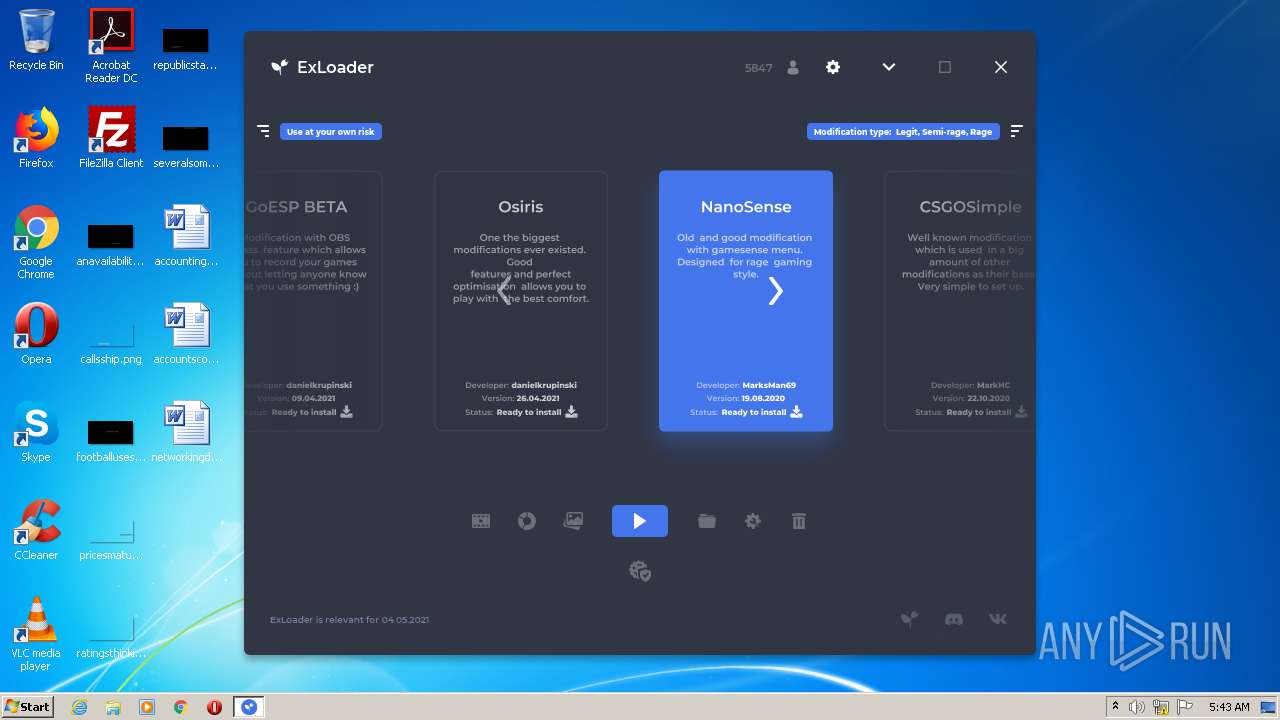
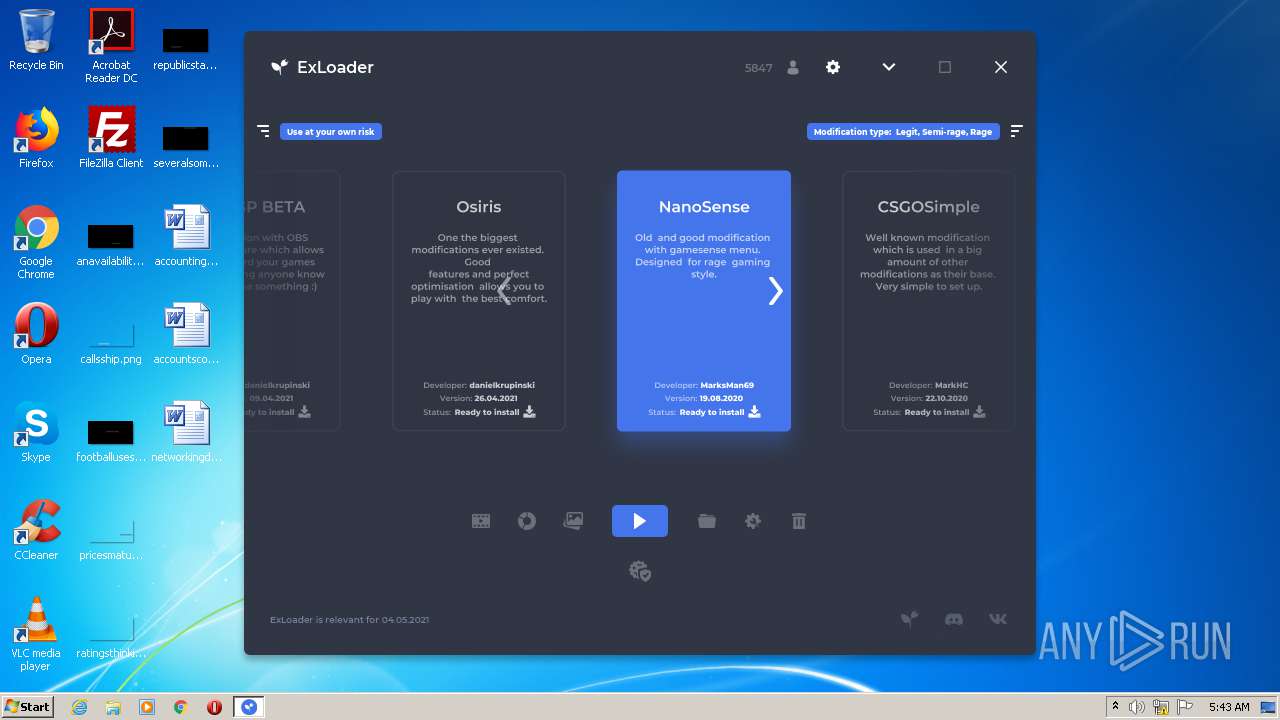
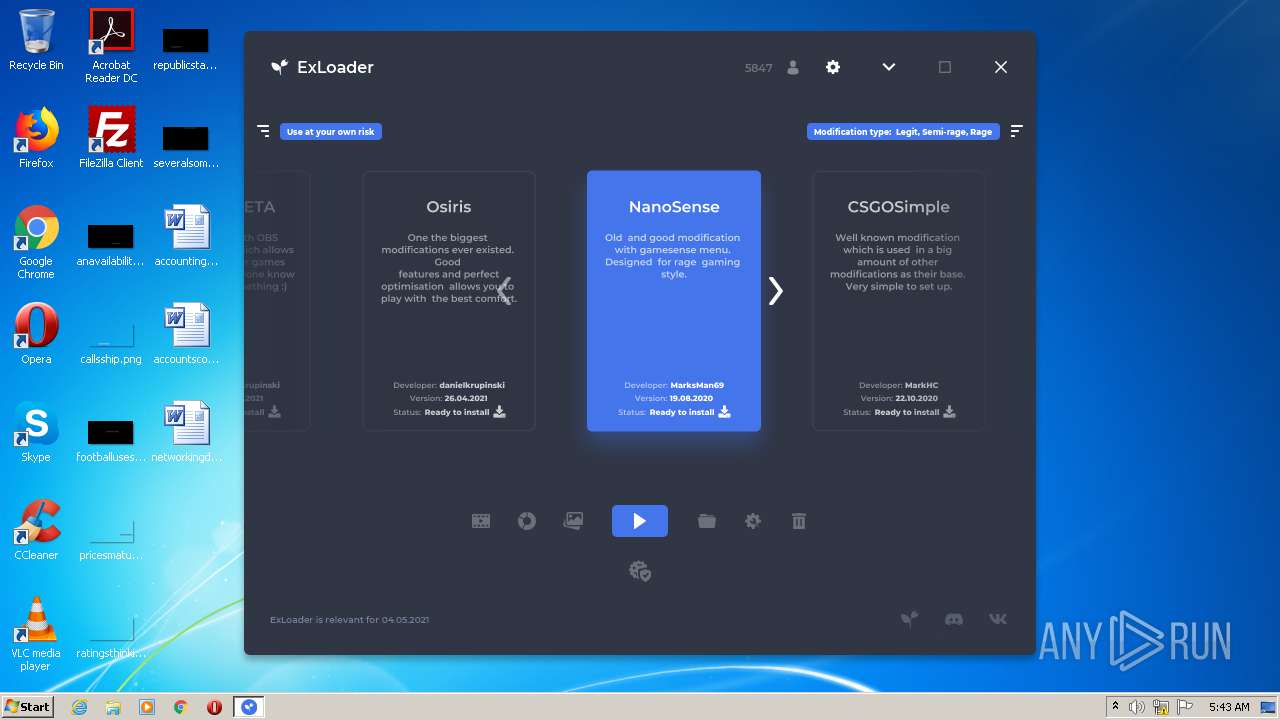
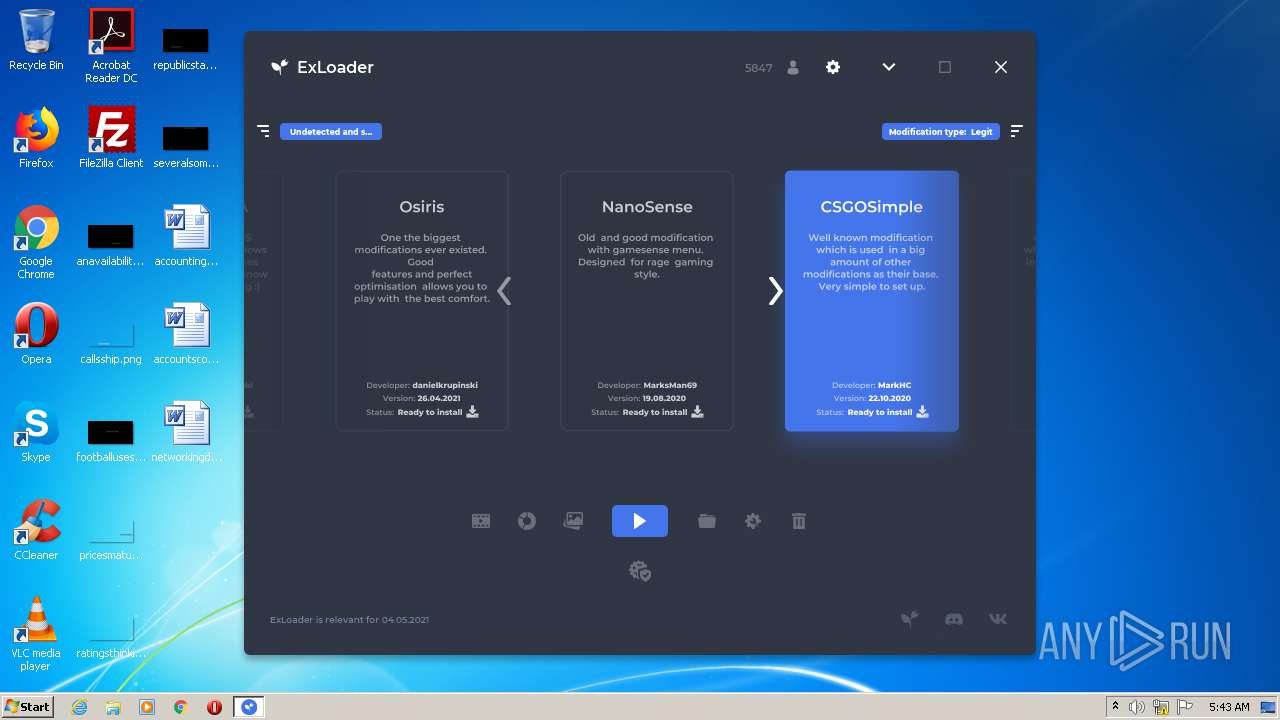
| FileDescription: | Unified library of game modifications |
| CompanyName: | SwiftSoft LLC |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 2.5.24.0 |
| FileVersionNumber: | 2.5.24.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1290 |
| UninitializedDataSize: | 36864 |
| InitializedDataSize: | 16384 |
| CodeSize: | 19968 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| TimeStamp: | 2021:05:02 15:27:00+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-May-2021 13:27:00 |
| Detected languages: |
|
| CompanyName: | SwiftSoft LLC |
| FileDescription: | Unified library of game modifications |
| FileVersion: | 2.5.24.0 |
| InternalName: | ExLoader |
| LegalCopyright: | SwiftSoft LLC |
| LegalTrademarks: | ExLoader |
| OriginalFilename: | ExLoader.exe |
| ProductName: | ExLoader |
| ProductVersion: | 2.5.24.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 02-May-2021 13:27:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004CE0 | 0x00004E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03278 |
.data | 0x00006000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00007000 | 0x00000680 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92317 |
.bss | 0x00008000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65099 |
.rsrc | 0x00012000 | 0x00002820 | 0x00002A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.2553 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.32451 | 800 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
10 | 4.2515 | 57 | UNKNOWN | Process Default Language | RT_RCDATA |
13 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 2 | 4 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 5.36446 | 74 | UNKNOWN | Process Default Language | RT_RCDATA |
22 | 4.10539 | 24 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
68
Monitored processes
21
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | C:\Windows\System32\reg.exe query "HKU\S-1-5-19" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | C:\Windows\System32\chcp.com 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 972 | C:\Windows\System32\cmd.exe /c "C:\Windows\System32\chcp.com 65001>nul & C:\Windows\System32\reg.exe query "HKU\S-1-5-19"" | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1468 | taskkill /f /pid 1816 | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\ExLoader.exe" %* | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | ExLoader.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1824 | C:\Windows\System32\reg.exe query "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Nls\Language" /v "InstallLanguage" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | C:\Windows\System32\reg.exe query "HKEY_LOCAL_MACHINE\SOFTWARE\Valve\Steam" /v "InstallPath" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1856 | C:\Windows\System32\cmd.exe /c "C:\Windows\System32\chcp.com 65001>nul & C:\Windows\System32\reg.exe query "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Nls\Language" /v "InstallLanguage"" | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1916 | C:\Windows\System32\cmd.exe /c "C:\Windows\System32\chcp.com 65001>nul & C:\Windows\System32\reg.exe query "HKEY_LOCAL_MACHINE\SOFTWARE\Valve\Steam" /v "InstallPath"" | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2072 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -inputformat none -command "Invoke-Expression ([System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String('W0NvbnNvbGVdOjpPdXRwdXRFbmNvZGluZyA9IFtTeXN0ZW0uVGV4dC5FbmNvZGluZ106OlVURjgKU3RhcnQtUHJvY2VzcyAtVmVyYiBydW5BcyAiQzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXEV4TG9hZGVyLmV4ZSIgLUFyZ3VtZW50TGlzdCAnLVJlc3RhcnRlZFdpdGhBZG1pblJpZ2h0cyc=')))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
579
Read events
518
Write events
61
Delete events
0
Modification events
| (PID) Process: | (1816) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2072) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2072) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2072) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2952) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
1
Suspicious files
2
Text files
21
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JM3WPJL3HENHLWPOU8MZ.temp | — | |
MD5:— | SHA256:— | |||
| 2072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1816 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12ec2d.TMP | binary | |
MD5:— | SHA256:— | |||
| 1816 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 2952 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2952 | javaw.exe | C:\ProgramData\ExLoader\config.json | text | |
MD5:— | SHA256:— | |||
| 1816 | javaw.exe | C:\Users\admin\AppData\Local\Temp\jna-92668751\jna5240830191594488421.dll | executable | |
MD5:28D895A3CB7E9A0B6A5AE5ED6A62B254 | SHA256:04C9A8AB43D1EB616B84D0686C8AE1D881EF03FE4F3AA26511E5B19D35EF16AF | |||
| 2952 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF1731428441178834571.tmp | ttf | |
MD5:6D1796A9F798CED8961BAF3C79F894B6 | SHA256:DA0B09317F1CEFFB9767876579B15DC4DC9F75784E678404AA80632B6771207D | |||
| 2952 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF1942811950282762867.tmp | ttf | |
MD5:C88CECBFFAD6D8E731FD95DE49561EBD | SHA256:BAB583D38D105DAC9141B287FB2B7763B6D8B0BAE97E745FAACCEDB40A579C29 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | javaw.exe | 172.67.157.20:443 | exloader.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
exloader.net |
| unknown |