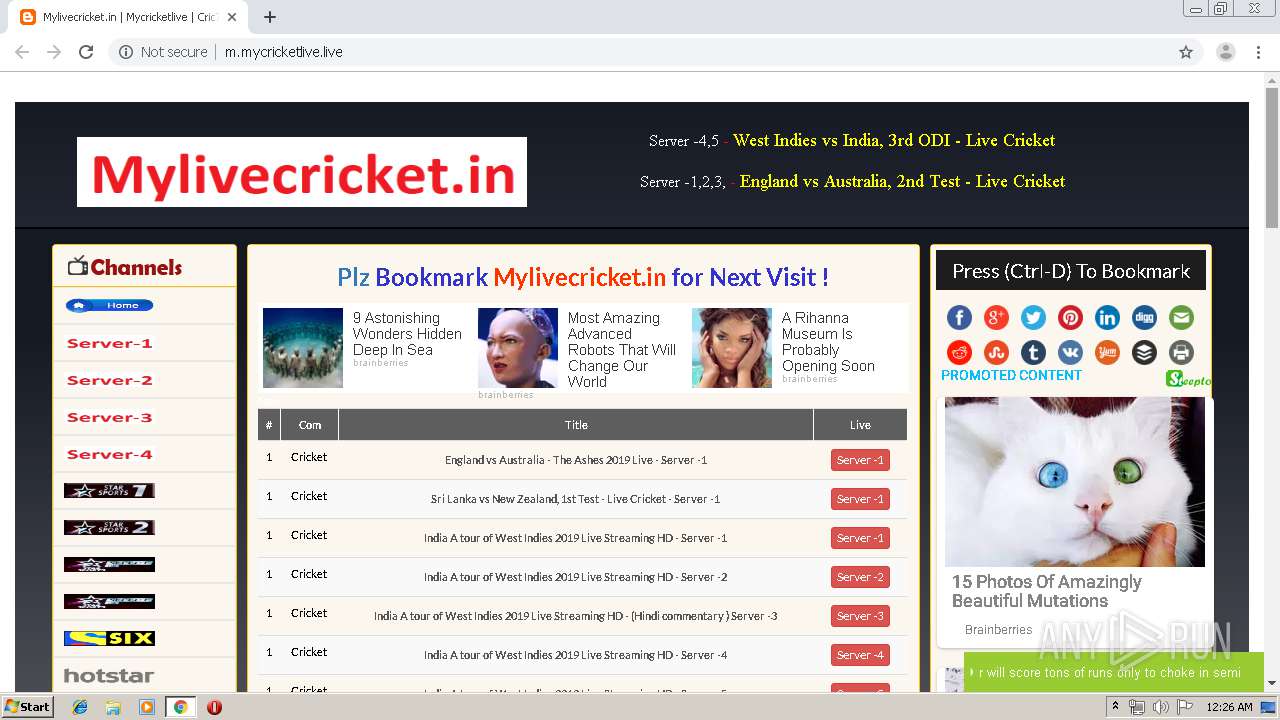
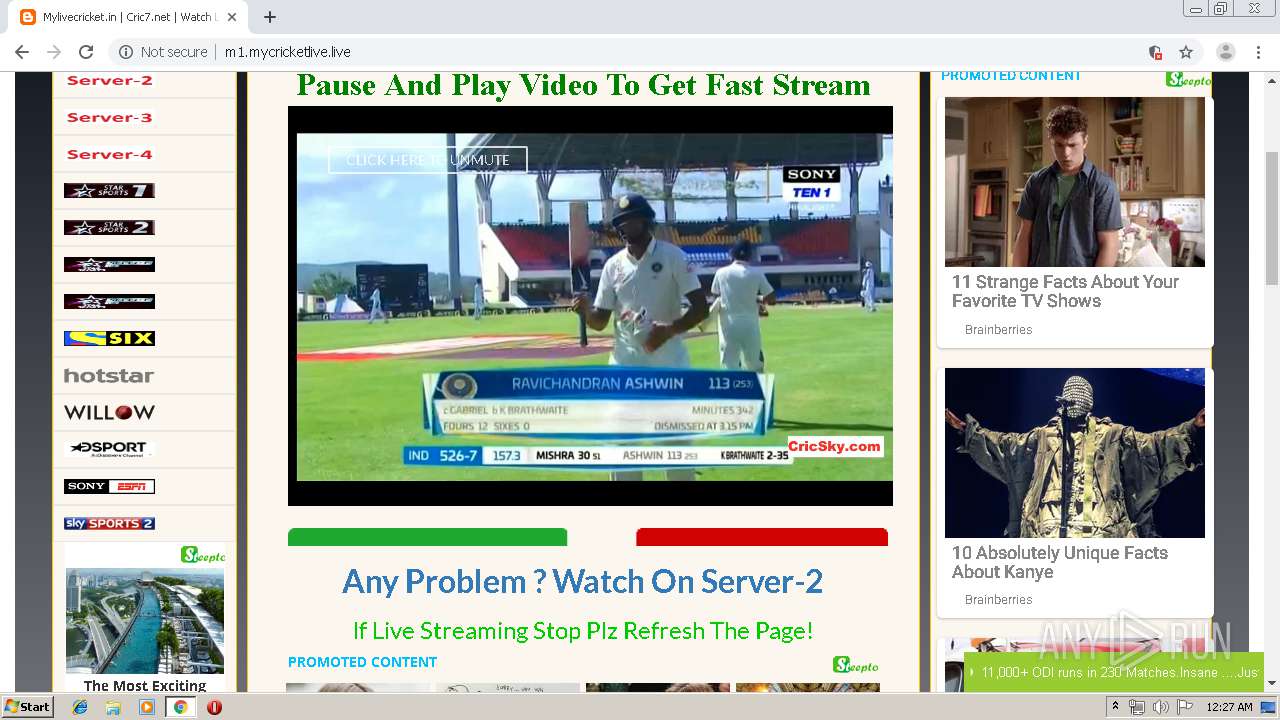
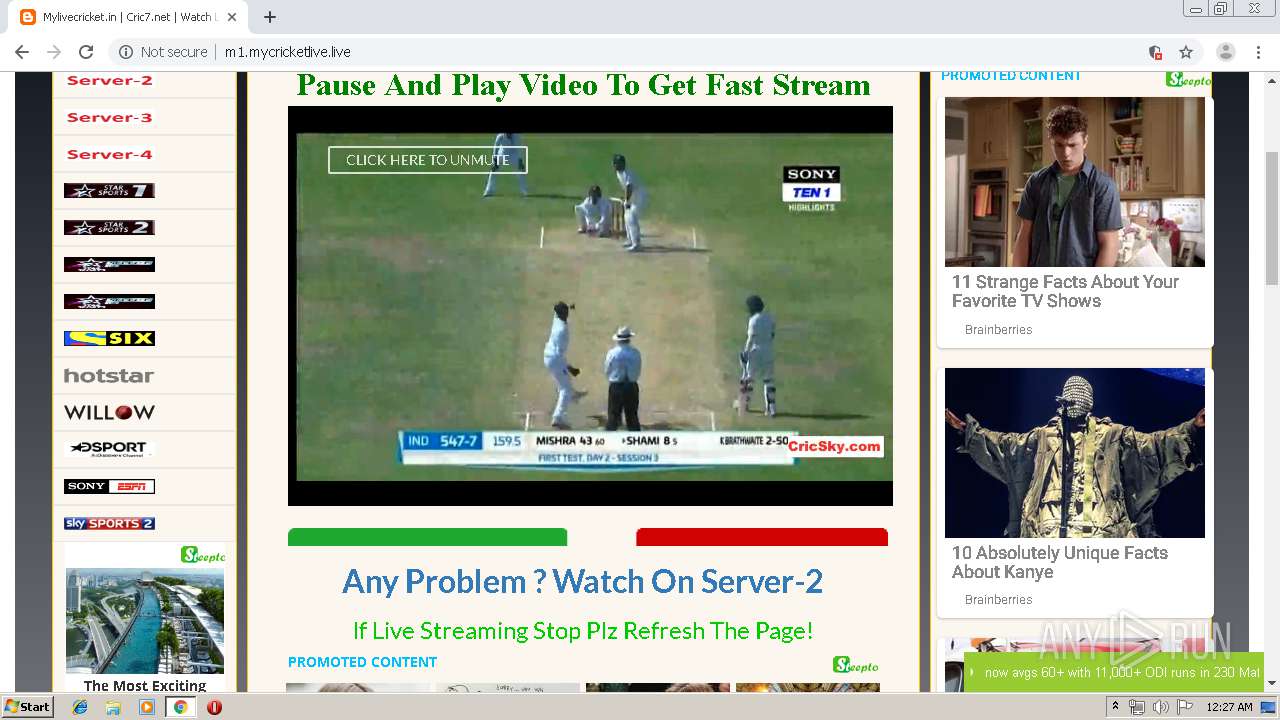
| URL: | https://mycricketlive.live/ |
| Full analysis: | https://app.any.run/tasks/95ba0887-fba9-4121-abf9-85bd65b74328 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2019, 23:26:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF9D835D58C4FC62E7DA911CDE1FD0AD |
| SHA1: | 398857ADD562A64AC8A23D18EDABEEDE84044E92 |
| SHA256: | A2F9B44BA94FD70AD55496DB1F47A09B2D975B6D4B9F2602620217A32BFB3923 |
| SSDEEP: | 3:N8ovnJSv:2Rv |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3604)
INFO
Changes settings of System certificates
- chrome.exe (PID: 1596)
Connects to unusual port
- chrome.exe (PID: 1596)
Application launched itself
- chrome.exe (PID: 3604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
39
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17983955145284036706 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8922185687861587111 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16618557536672194144 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2745535883784399440 --mojo-platform-channel-handle=4104 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12102011962304562667 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10378676014566265838 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6354741160467782039 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7569755996282043837 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17591269277149298837 --mojo-platform-channel-handle=3816 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,4741187733243192186,4744935793779468934,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14563525766962973279 --mojo-platform-channel-handle=3528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
648
Read events
542
Write events
101
Delete events
5
Modification events
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3604-13210298782628750 |
Value: 259 | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3604-13210298782628750 |
Value: 259 | |||
Executable files
0
Suspicious files
79
Text files
182
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\219ec89e-57d6-46b3-8b5e-05863e589f2b.tmp | — | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF37a0b9.TMP | text | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
80
TCP/UDP connections
263
DNS requests
122
Threats
796
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
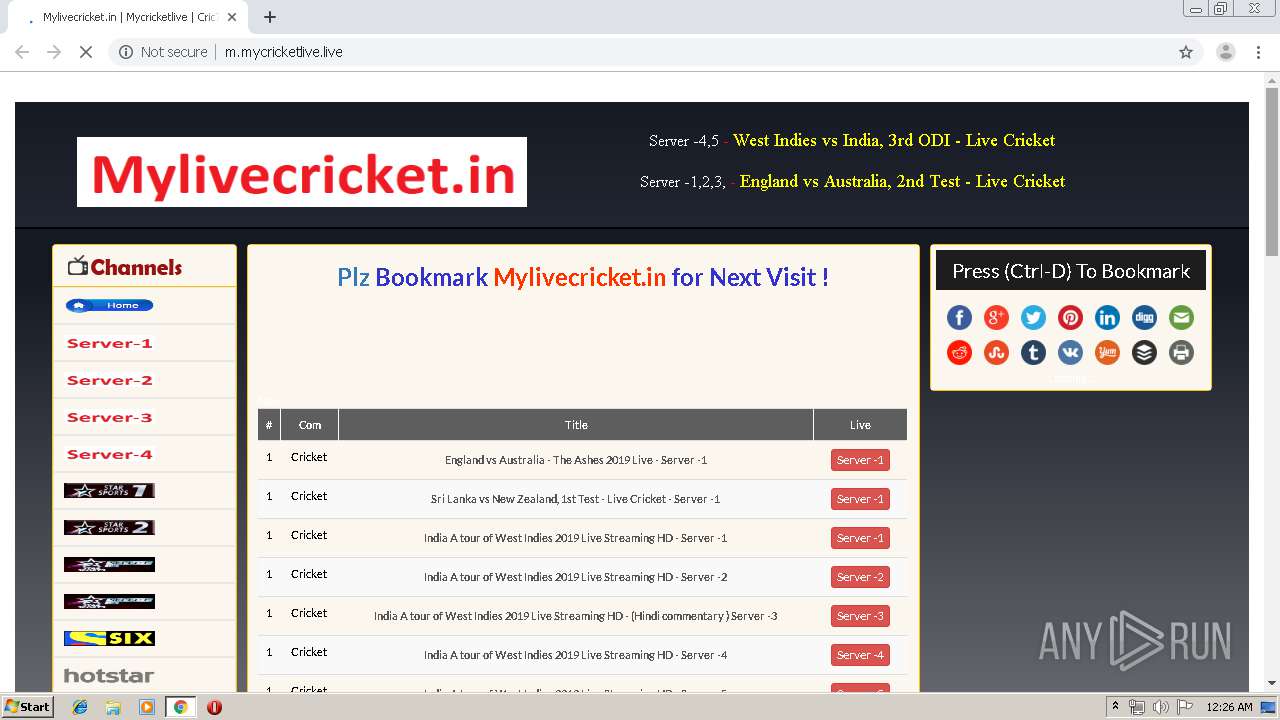
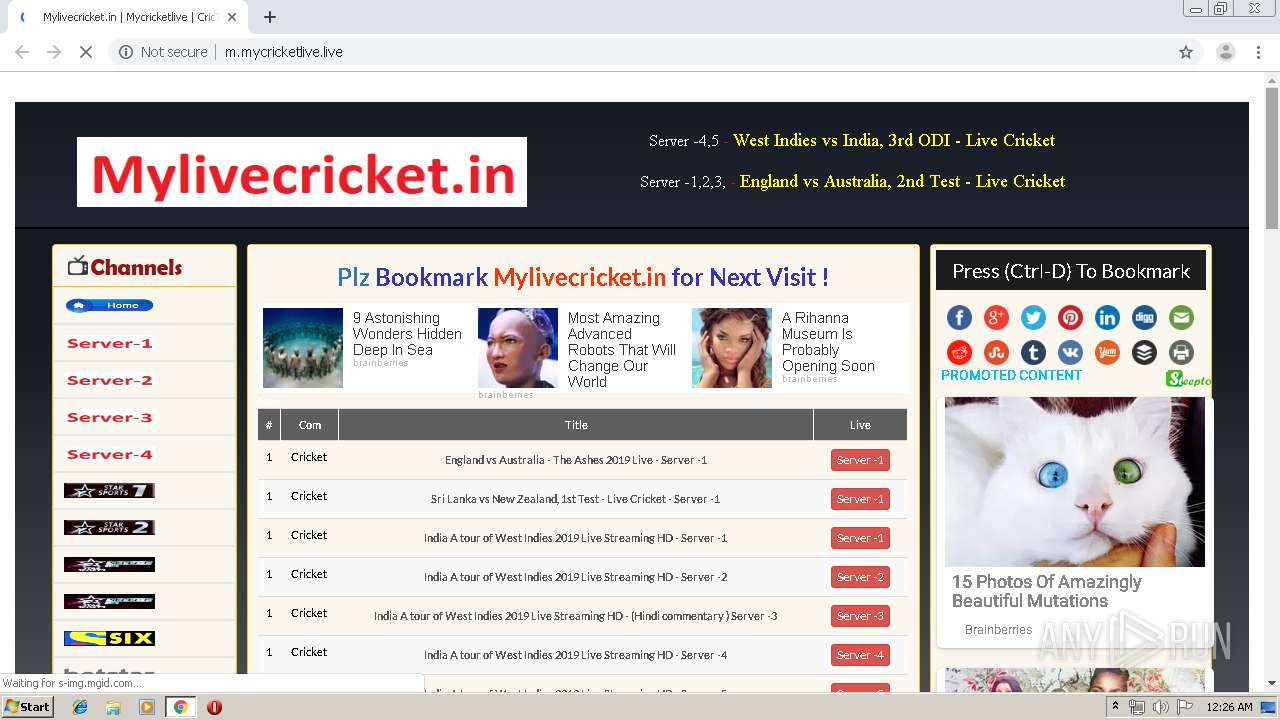
1596 | chrome.exe | GET | 403 | 198.134.112.241:80 | http://newthuads.com/46/86/b8/4686b8551c3a7a7b923be037a54fc470.js | US | — | — | malicious |
1596 | chrome.exe | GET | 307 | 67.202.94.86:80 | http://whos.amung.us/widget/3uo57t29tekf.png | US | — | — | whitelisted |
1596 | chrome.exe | GET | 200 | 216.58.205.243:80 | http://m.mycricketlive.live/ | US | html | 10.1 Kb | malicious |
1596 | chrome.exe | GET | 301 | 162.255.119.173:80 | http://mycricketlive.live/ | US | html | 63 b | suspicious |
1596 | chrome.exe | GET | 200 | 172.217.16.193:80 | http://4.bp.blogspot.com/-4HFPIDzMzzM/WR7efCF8gPI/AAAAAAAAAD0/BoFXeKBnVlkY3CNiRktPZnf9zHy06kL4wCLcB/s320/star2.png | US | image | 20.2 Kb | whitelisted |
1596 | chrome.exe | GET | 200 | 216.58.205.225:80 | http://2.bp.blogspot.com/-kwAER8qXGWY/WSa_nS-di8I/AAAAAAAAAGE/aIT-HL5SHi4gHdjoGGkVfilQdOiMAc78QCLcB/s320/home_button.png | US | image | 23.8 Kb | whitelisted |
1596 | chrome.exe | GET | 200 | 172.217.22.65:80 | http://1.bp.blogspot.com/-KX5lvpQ_f7c/WUT-g5qilcI/AAAAAAAAAJY/Cc9pZ1k2iy8nump40syJ5QZQczYlq7d1ACLcBGAs/s1600/mylive.png | US | image | 7.36 Kb | whitelisted |
1596 | chrome.exe | GET | 200 | 172.217.23.129:80 | http://3.bp.blogspot.com/-x3R--bo1dnI/WR7ecyVlJgI/AAAAAAAAADM/AHWLYNZb4LUDjb5i9qPdCbgMB9SSTW24QCLcB/s1600/schedule.png | US | image | 1.96 Kb | whitelisted |
1596 | chrome.exe | GET | 200 | 208.93.230.16:80 | http://st.chatango.com/js/gz/emb.js | US | text | 24.0 Kb | whitelisted |
1596 | chrome.exe | GET | 200 | 172.217.18.115:80 | http://a.cric7.live/ | US | html | 2.70 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1596 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 162.255.119.173:443 | mycricketlive.live | Namecheap, Inc. | US | suspicious |
1596 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 162.255.119.173:80 | mycricketlive.live | Namecheap, Inc. | US | suspicious |
1596 | chrome.exe | 216.58.205.243:80 | m.mycricketlive.live | Google Inc. | US | whitelisted |
1596 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 216.58.206.9:443 | www.blogger.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 185.199.109.153:80 | mylivecricket.github.io | GitHub, Inc. | NL | shared |
1596 | chrome.exe | 172.217.22.65:80 | 1.bp.blogspot.com | Google Inc. | US | whitelisted |
1596 | chrome.exe | 172.217.22.65:443 | 1.bp.blogspot.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mycricketlive.live |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
m.mycricketlive.live |
| malicious |
www.blogger.com |
| shared |
fonts.googleapis.com |
| whitelisted |
mylivecricket.github.io |
| malicious |
1.bp.blogspot.com |
| whitelisted |
3.bp.blogspot.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1596 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1596 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1596 | chrome.exe | Potential Corporate Privacy Violation | ET INFO Suspicious Darkwave Popads Pop Under Redirect |
1596 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1596 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |