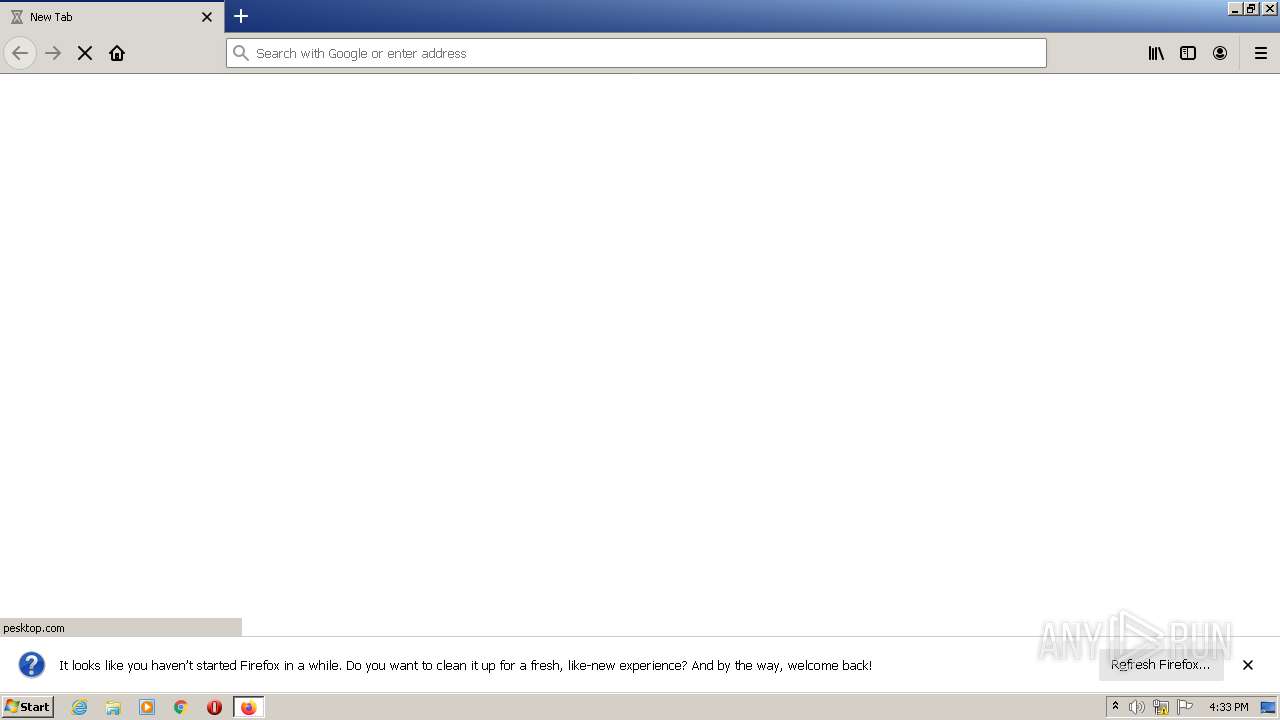
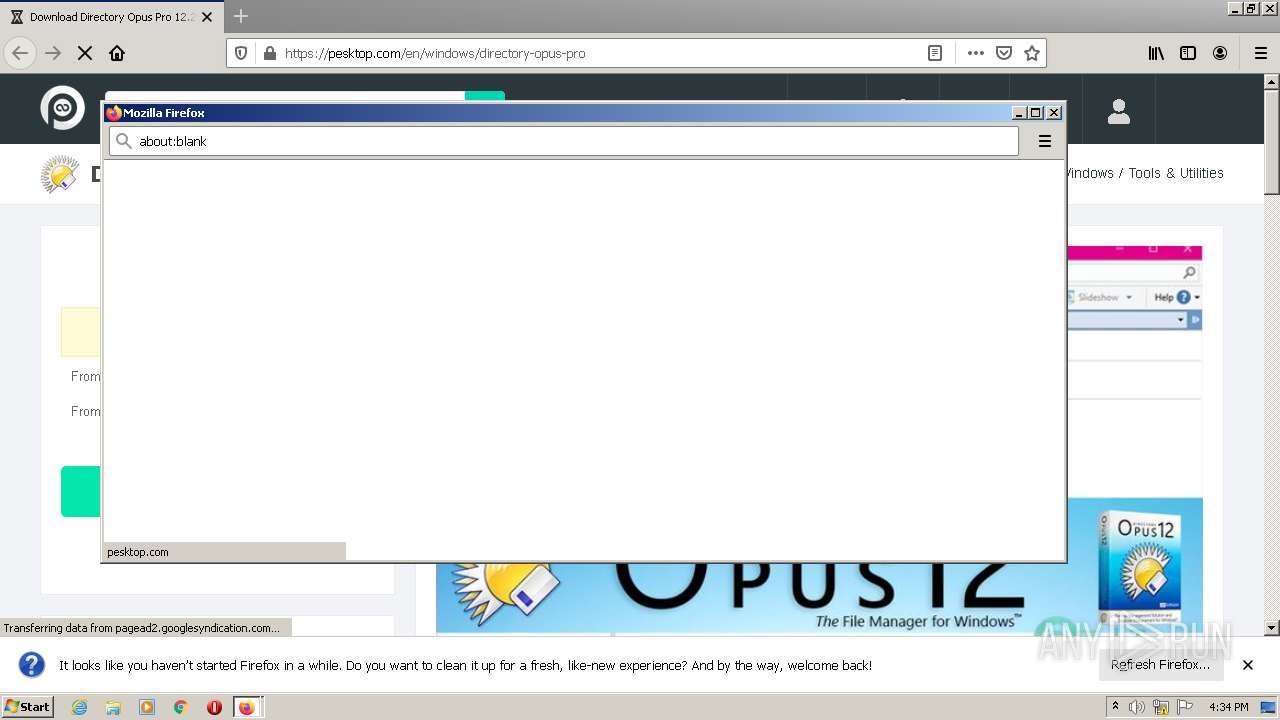
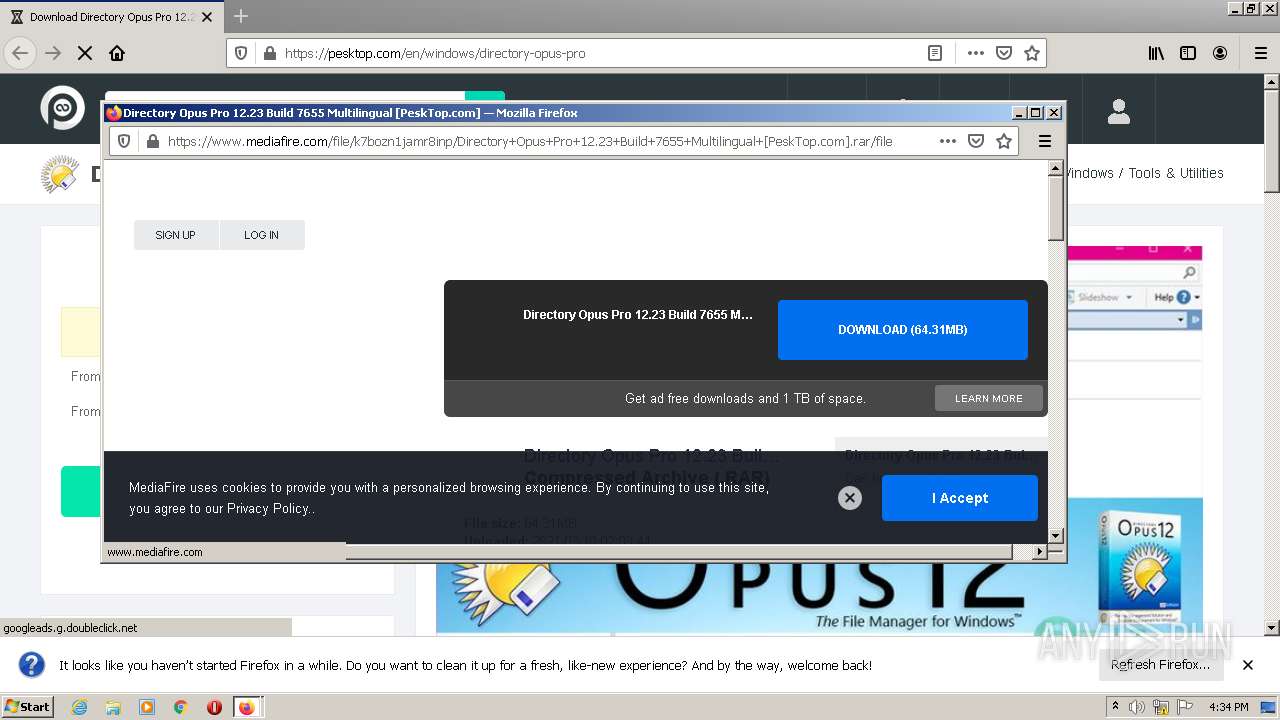
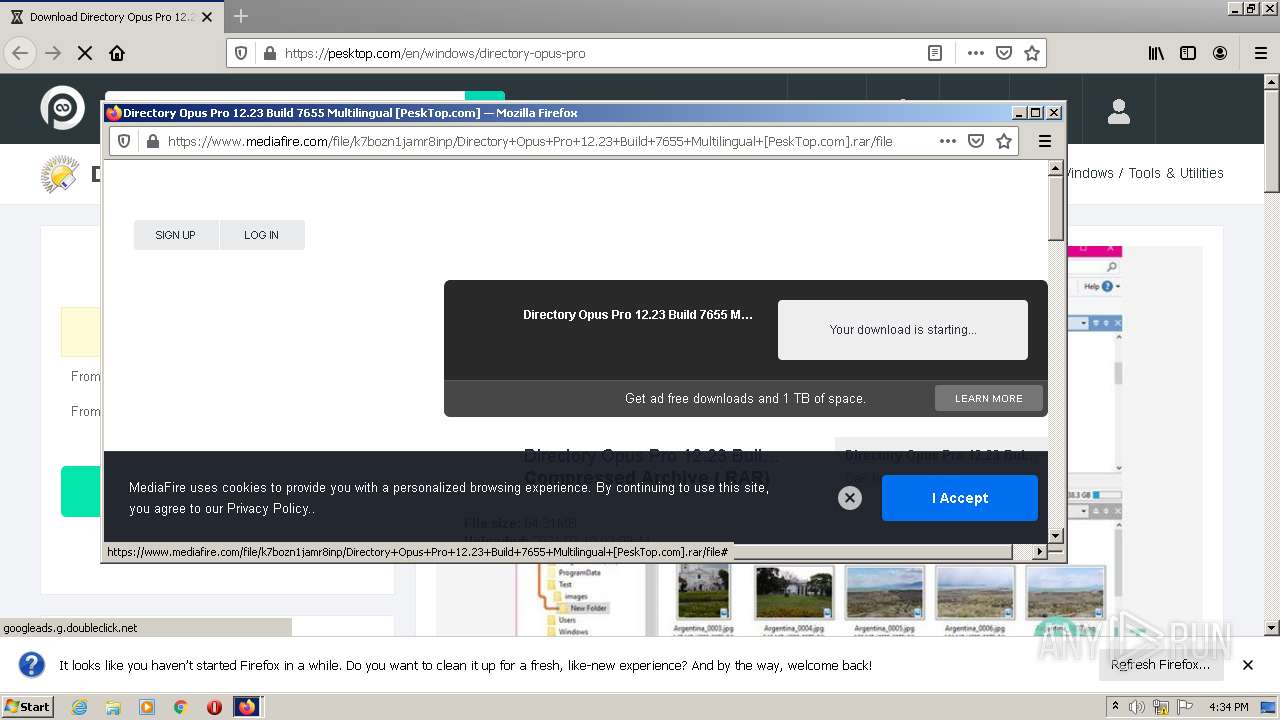
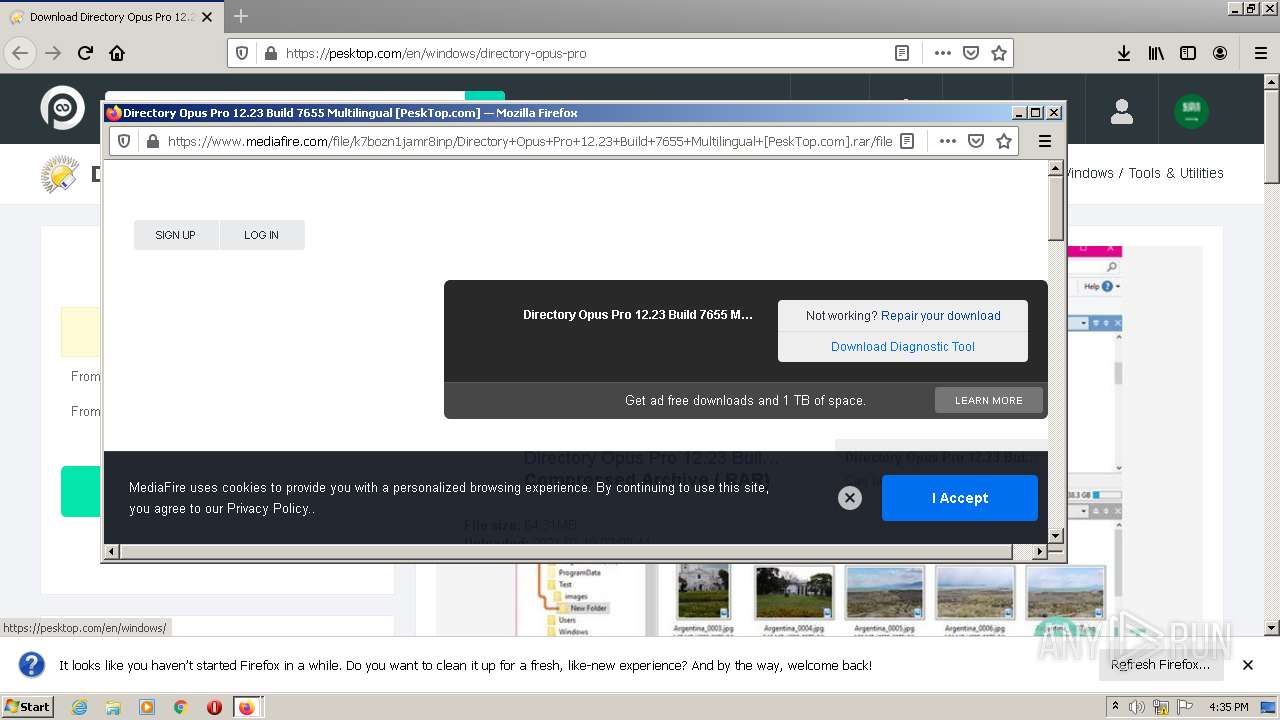
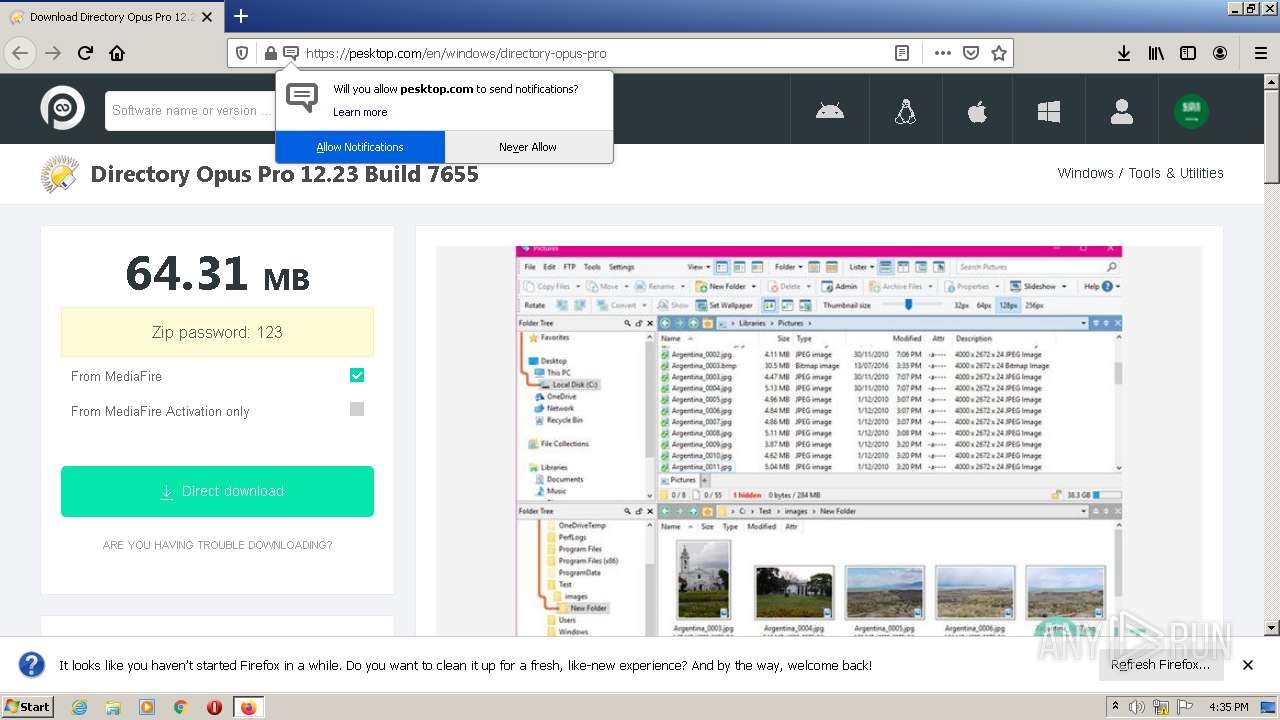
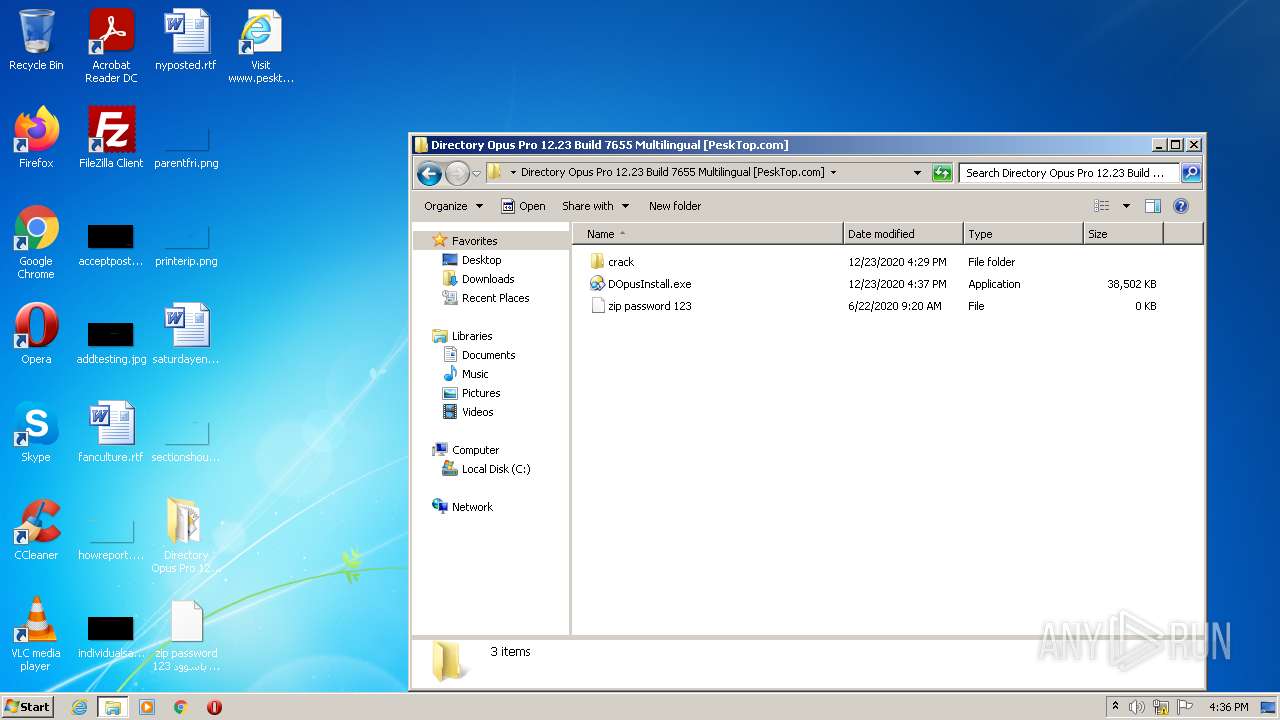
| URL: | https://pesktop.com/en/windows/directory-opus-pro |
| Full analysis: | https://app.any.run/tasks/b4e00102-819e-4ddf-84a8-1f3c053c1bad |
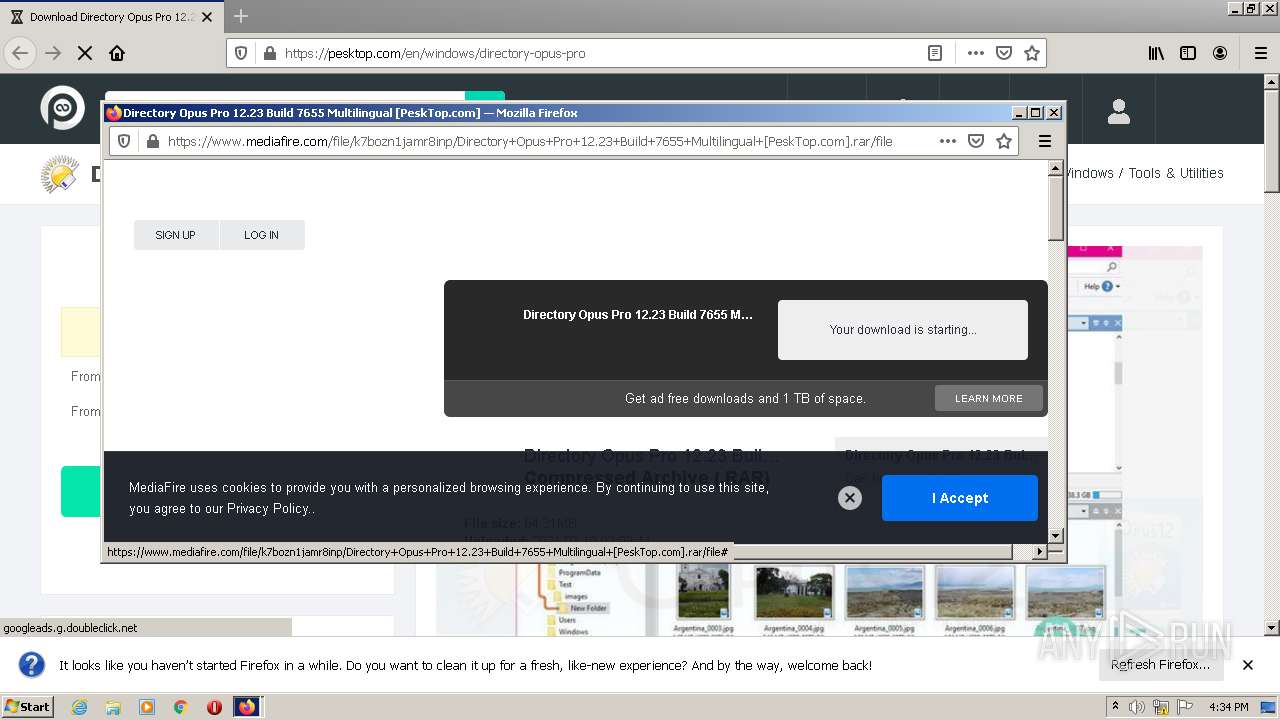
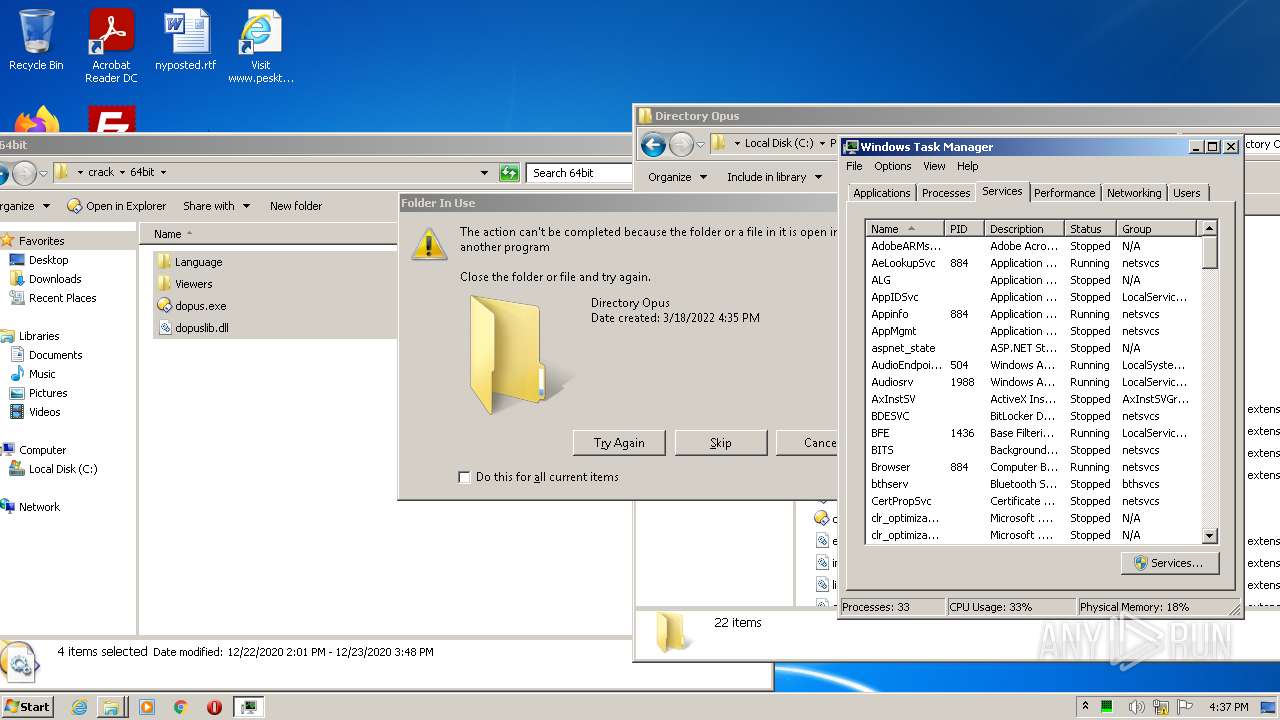
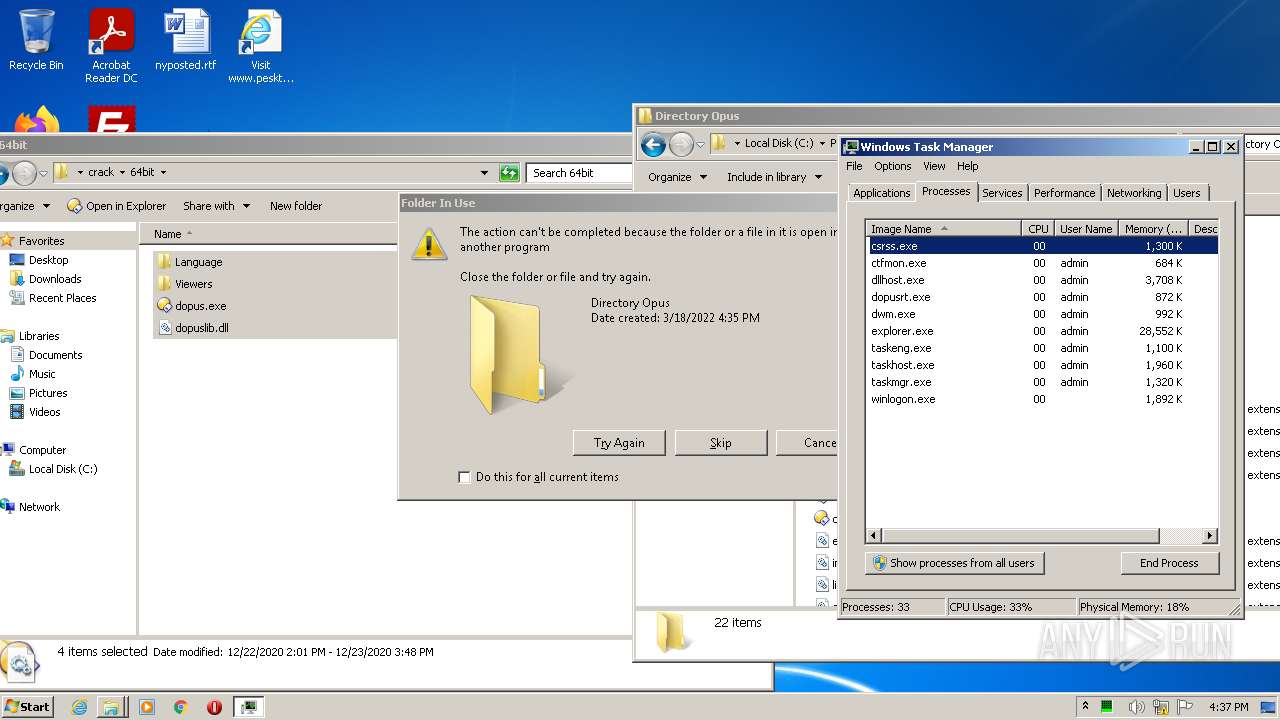
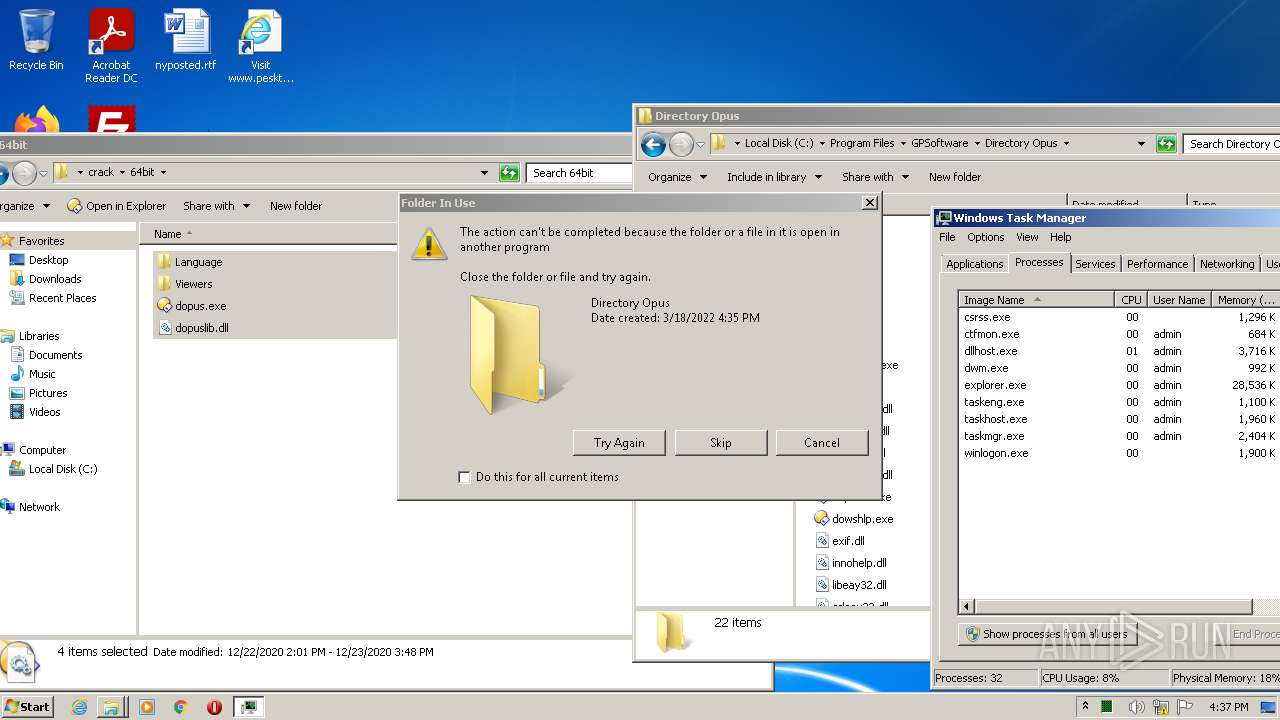
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2022, 16:33:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C3A690DF1059261E3D326BA1F6E794CE |
| SHA1: | AB62F58C80EBE6CB6B549A7A4009D9E4E9DC3DA3 |
| SHA256: | A2F1D9D942D8F171E20199821D537A6A6702DF370E75B101F798B303A1F40D2B |
| SSDEEP: | 3:N8EiVLKKFSML8UMdK4n:2E2LKKF/L8Vdxn |
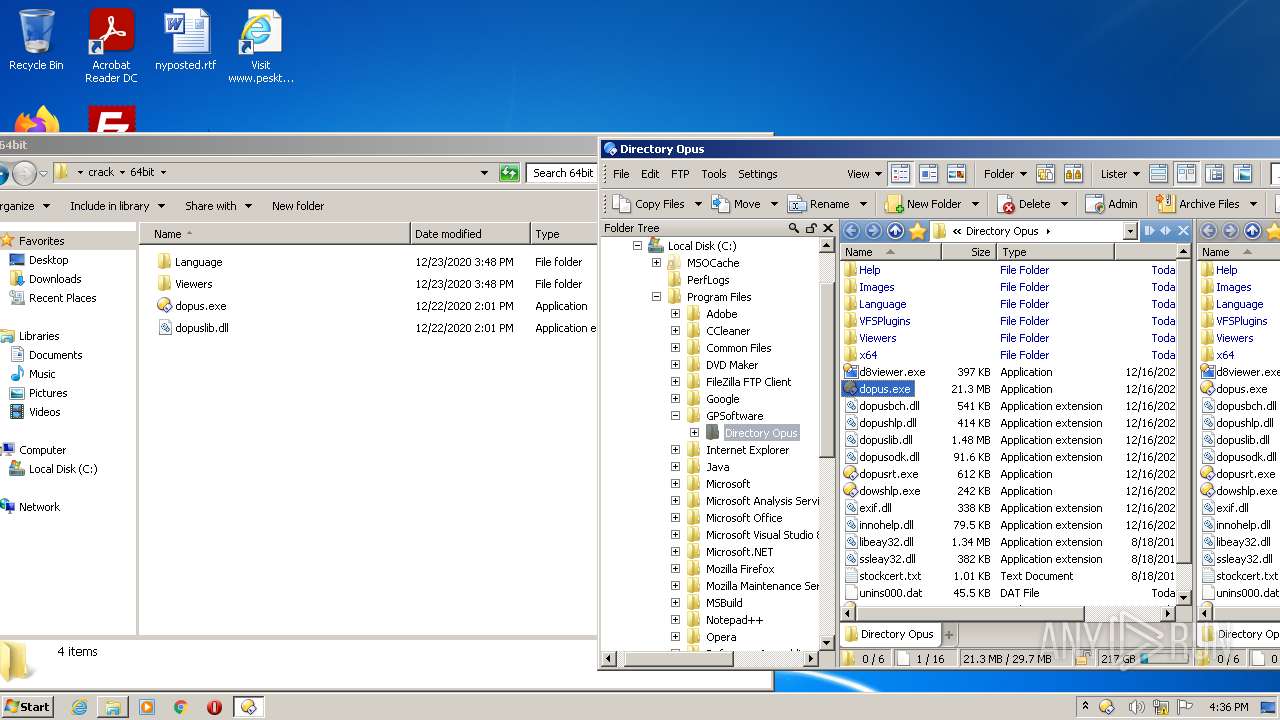
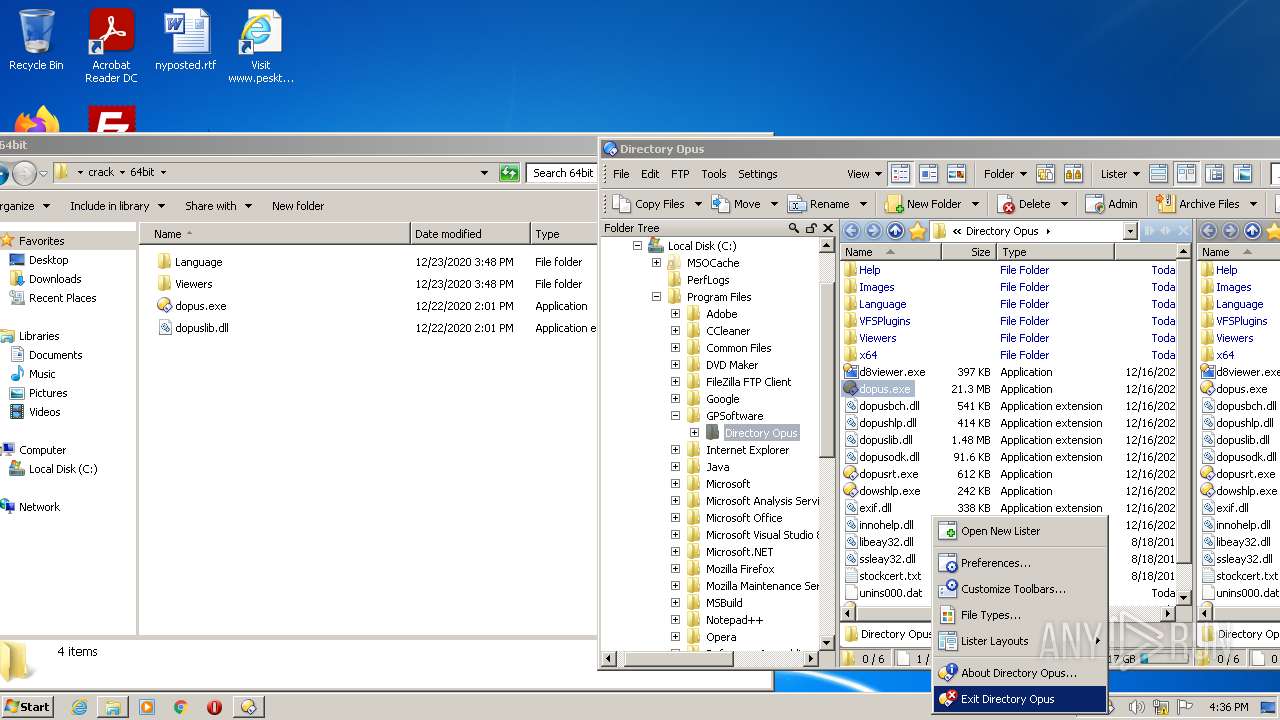
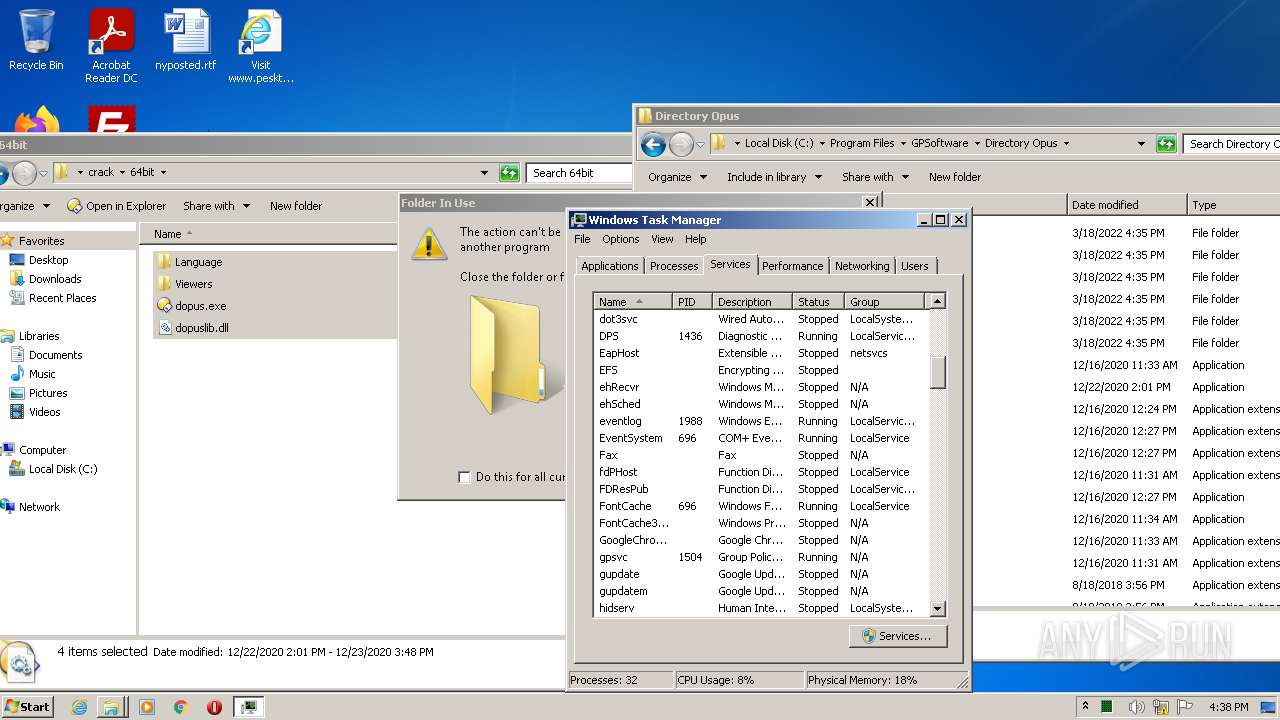
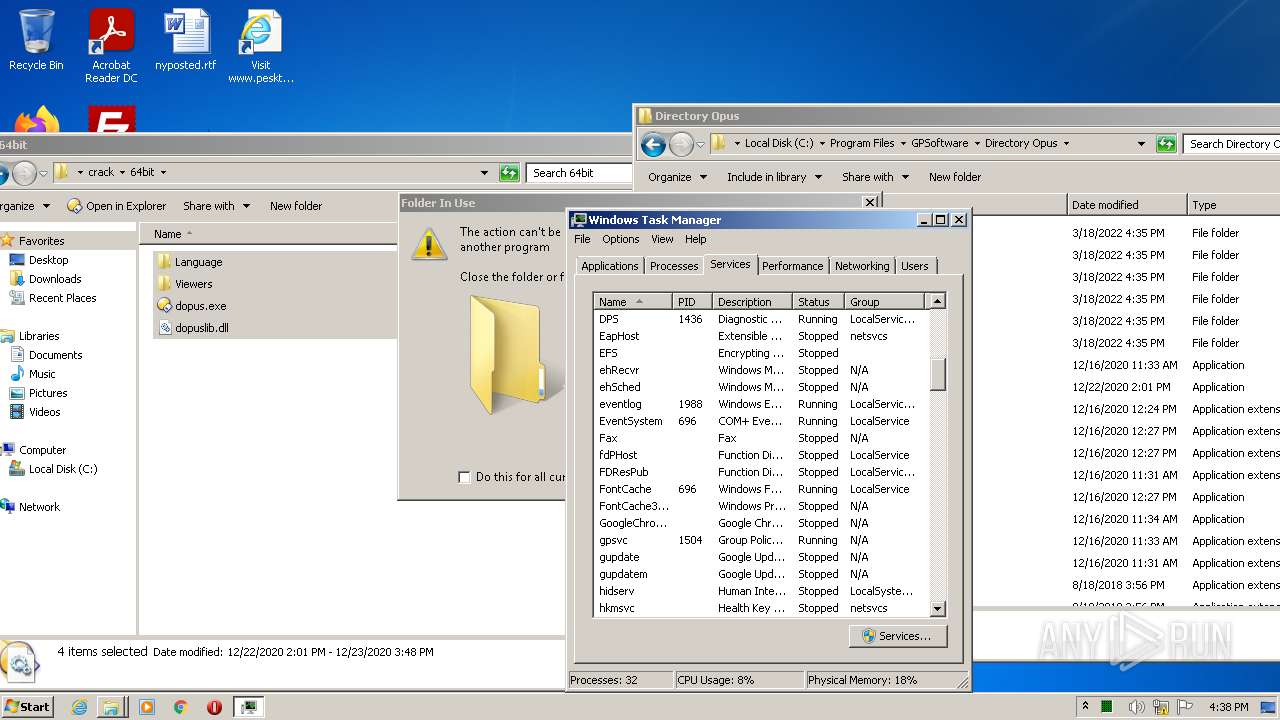
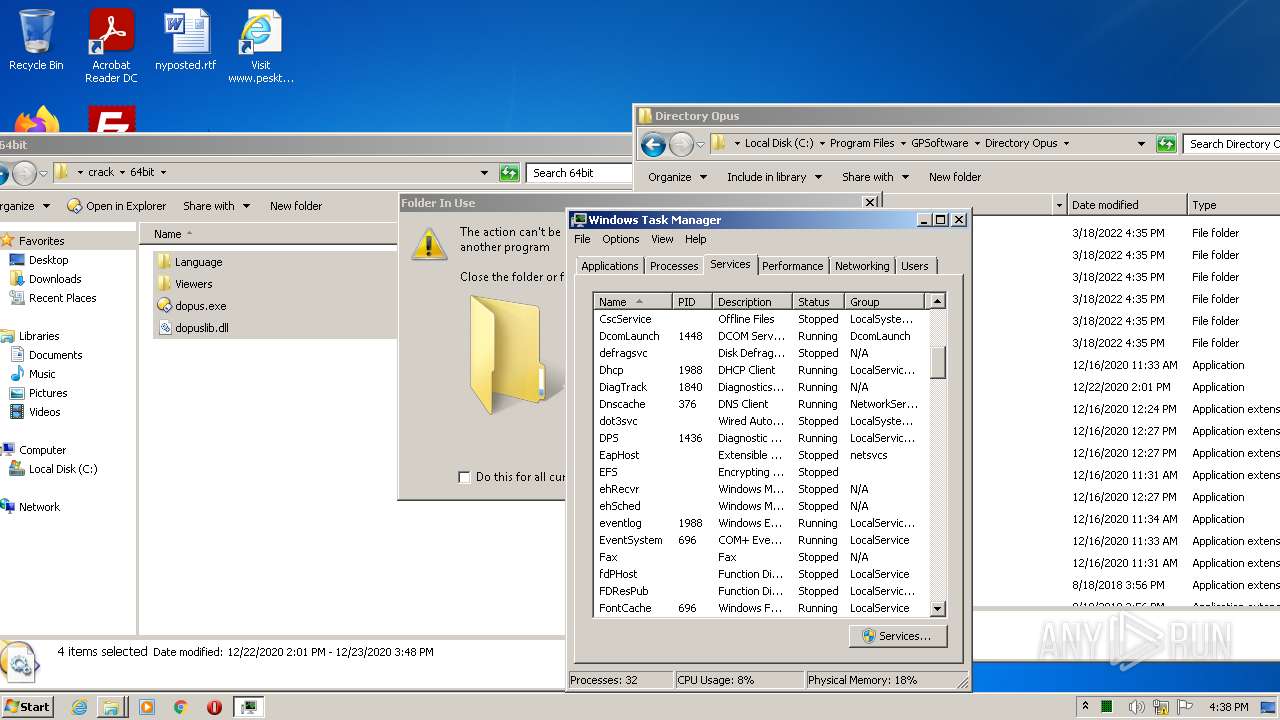
MALICIOUS
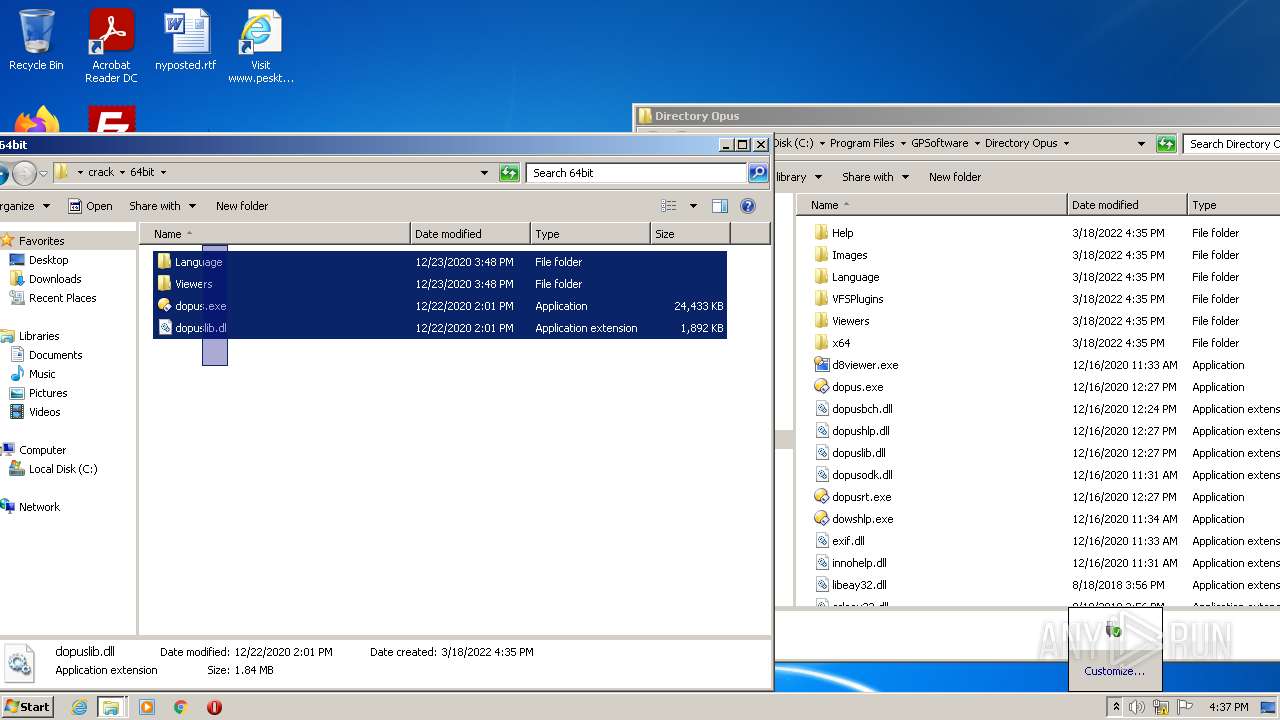
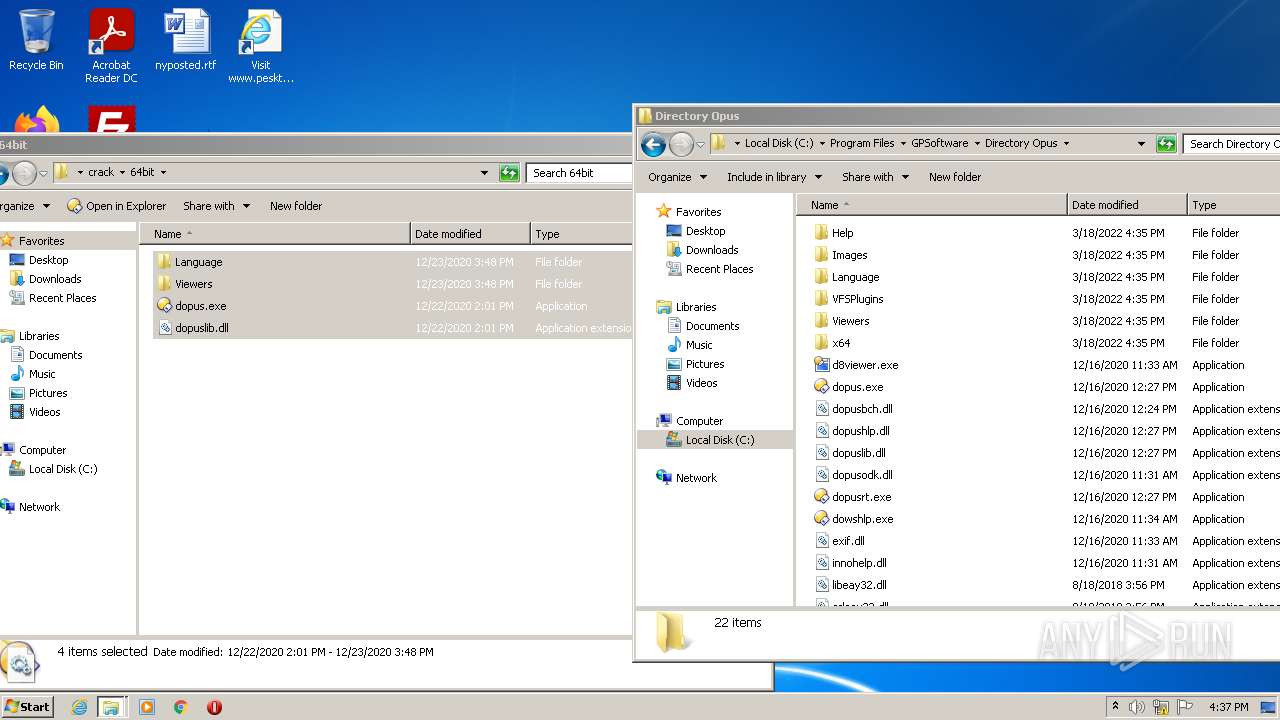
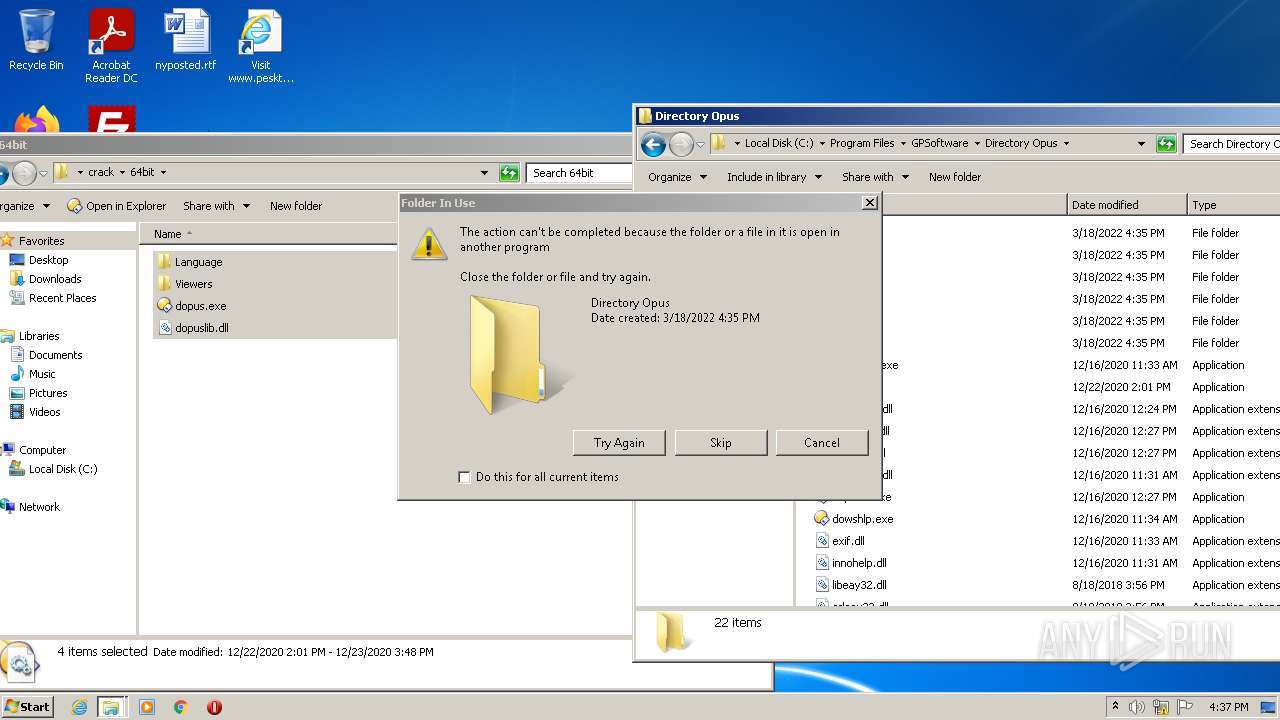
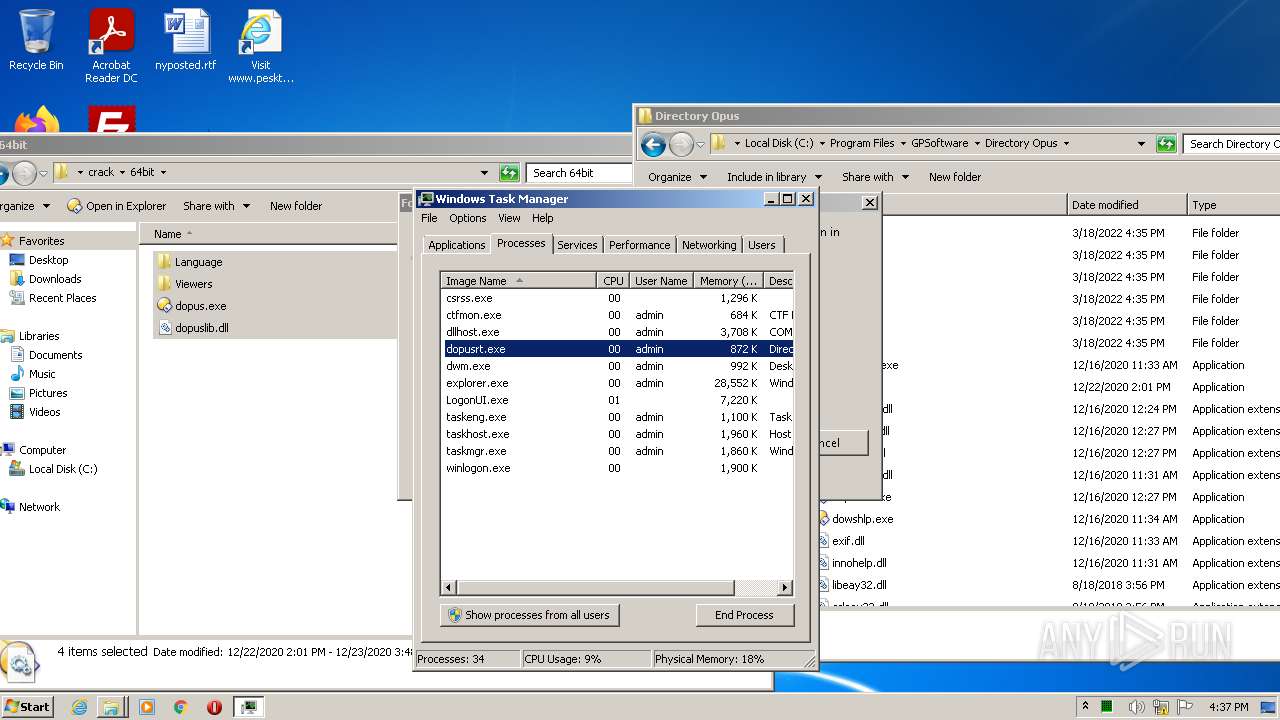
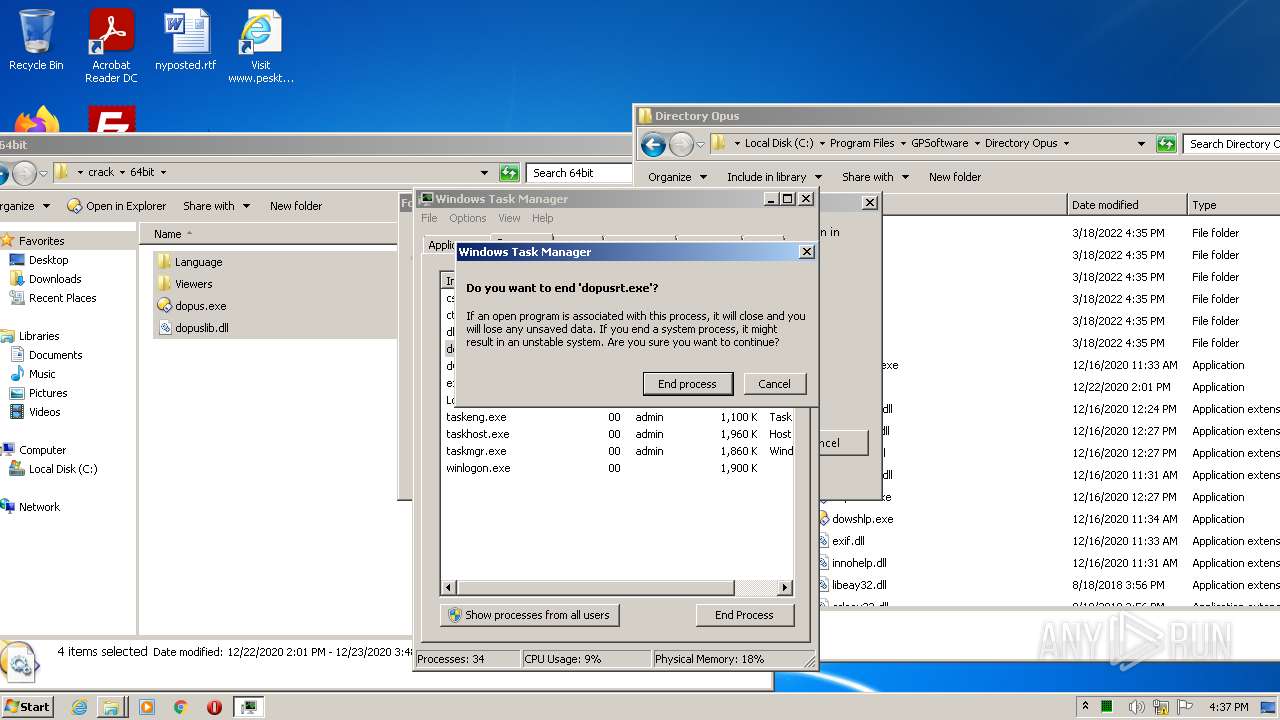
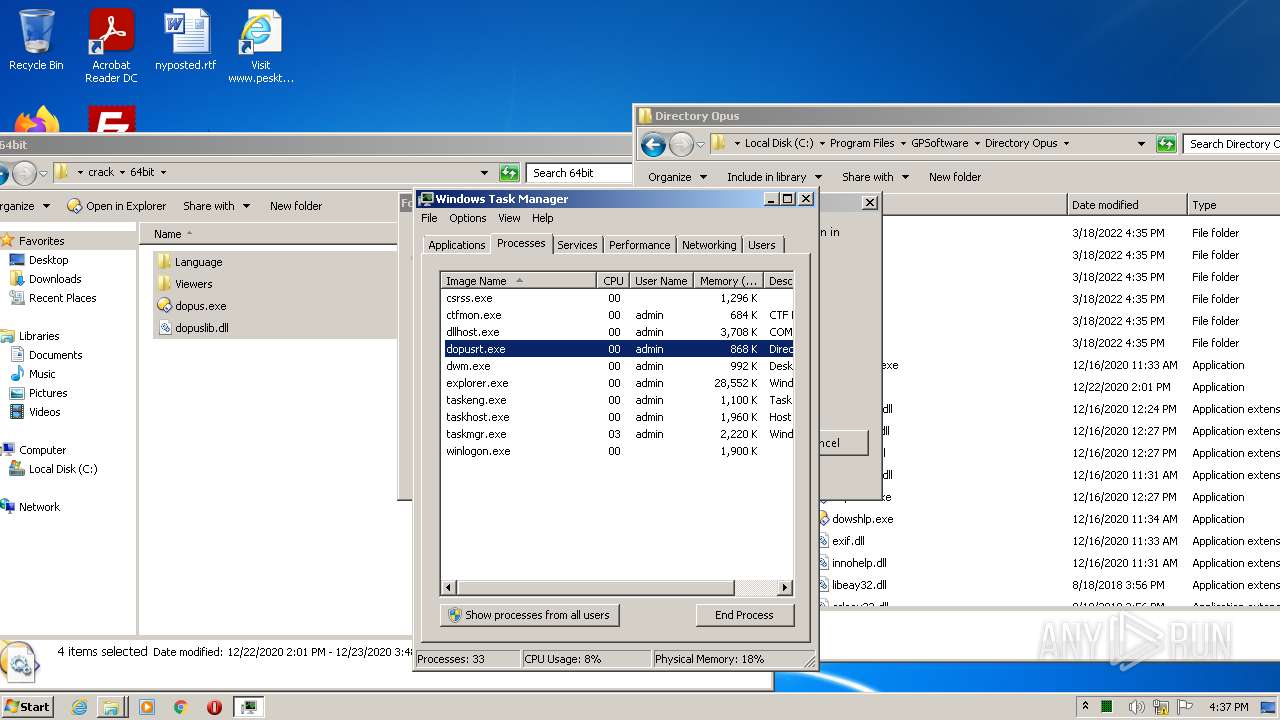
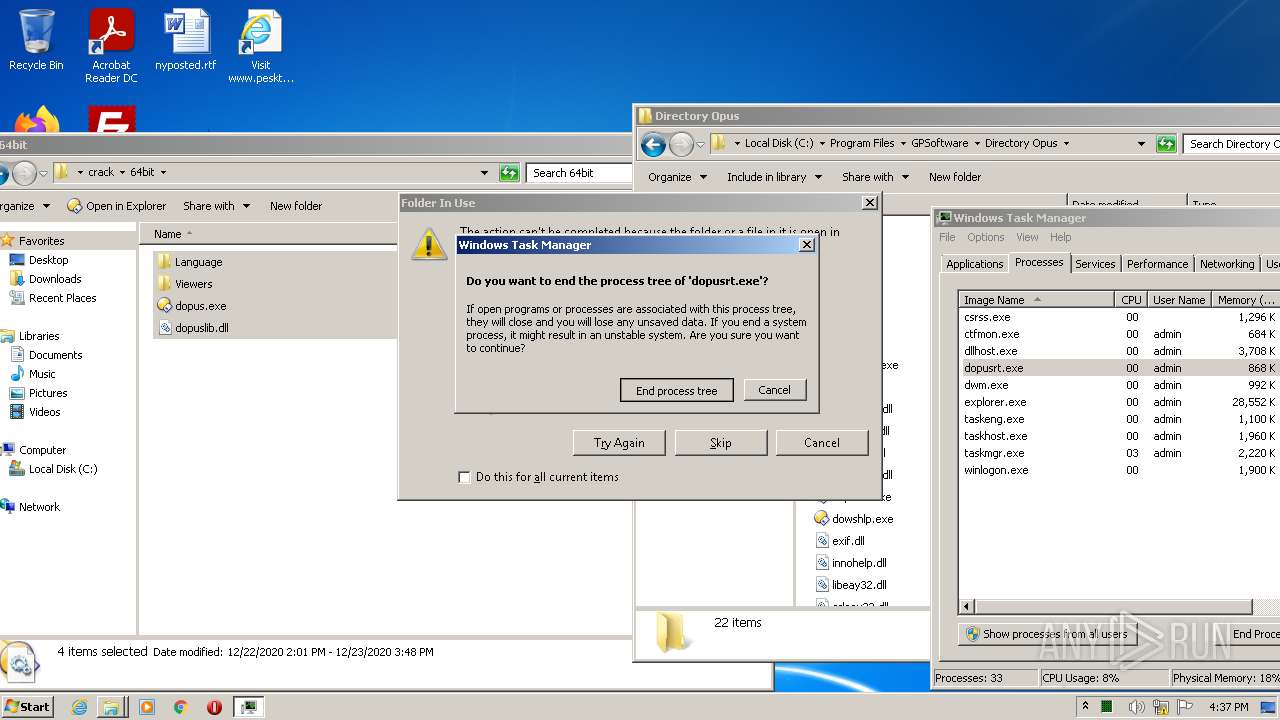
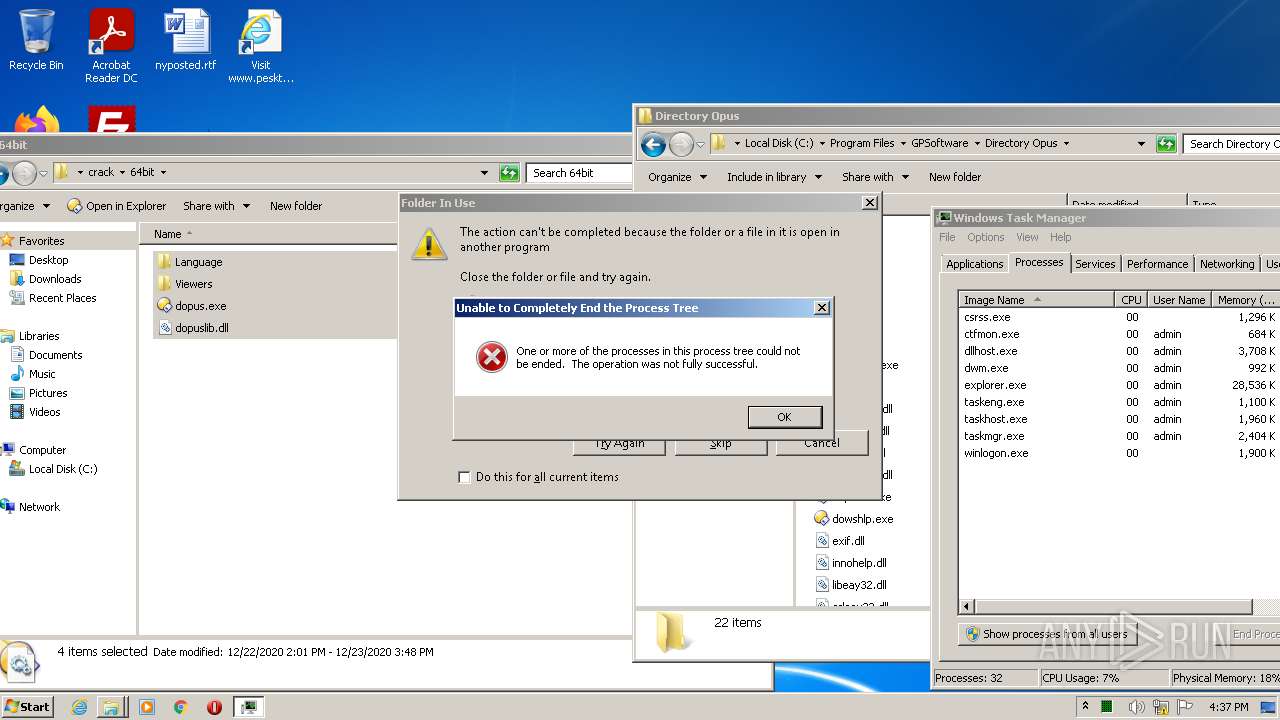
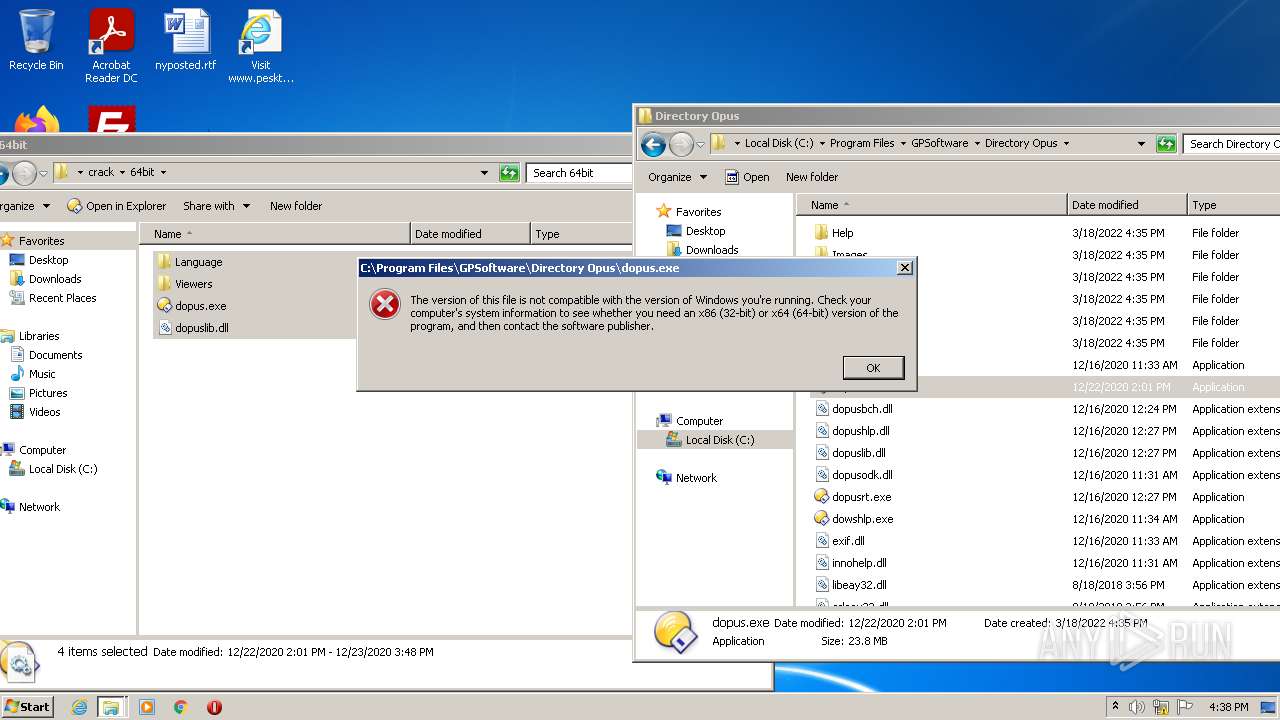
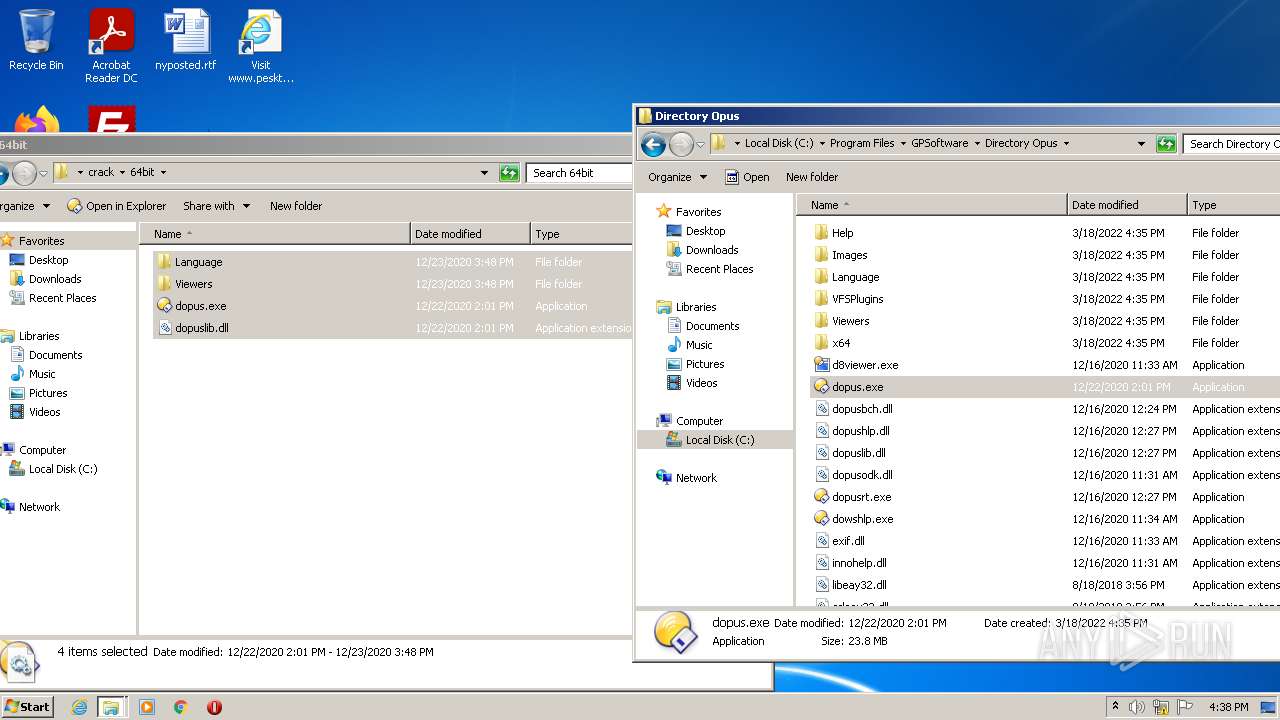
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3080)
- regsvr32.exe (PID: 2380)
- regsvr32.exe (PID: 3484)
- svchost.exe (PID: 884)
- dopusrt.exe (PID: 3616)
- dopus.exe (PID: 908)
- dopusrt.exe (PID: 1432)
- Explorer.EXE (PID: 584)
- explorer.exe (PID: 2508)
- dopusrt.exe (PID: 3672)
- dopusrt.exe (PID: 2840)
- dopus.exe (PID: 1560)
- taskmgr.exe (PID: 2564)
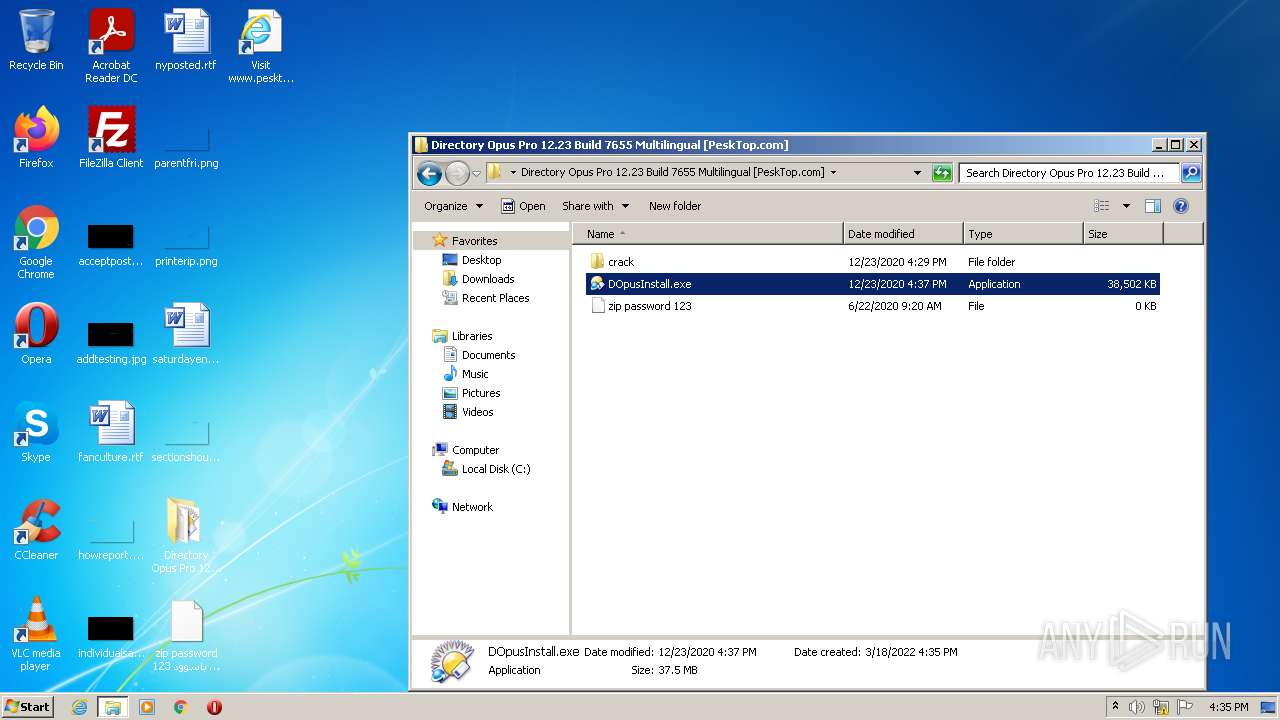
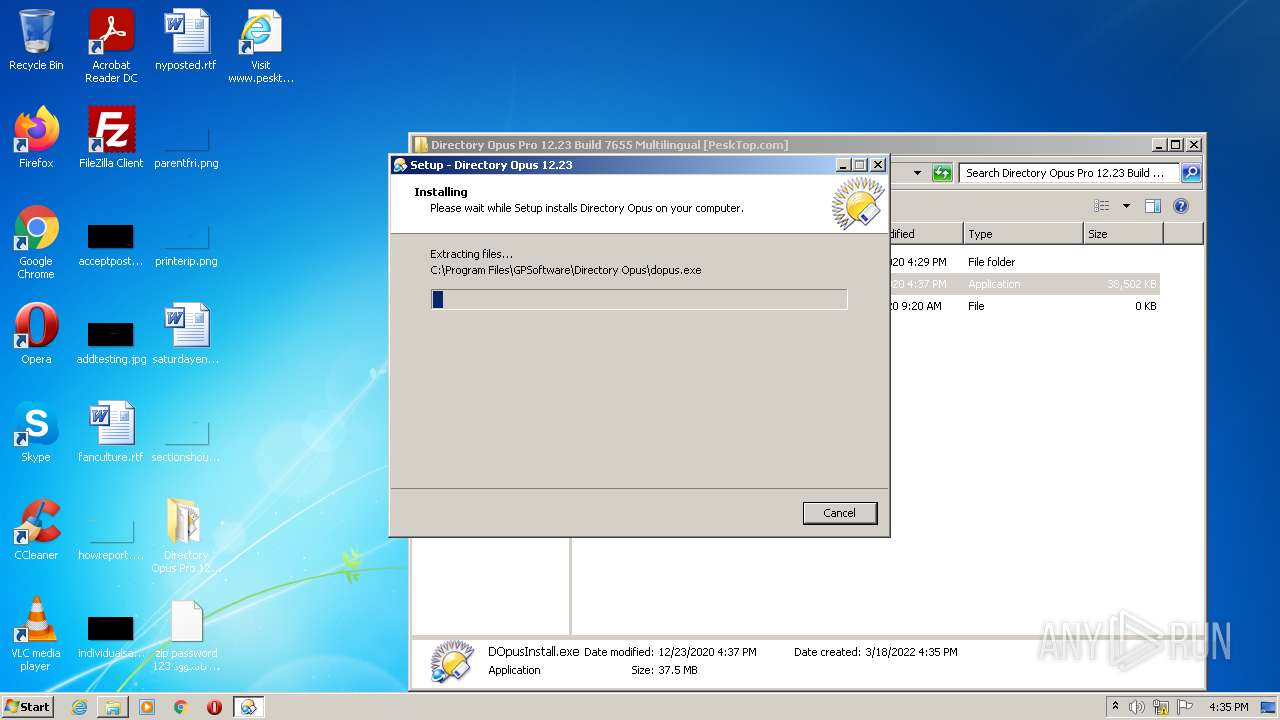
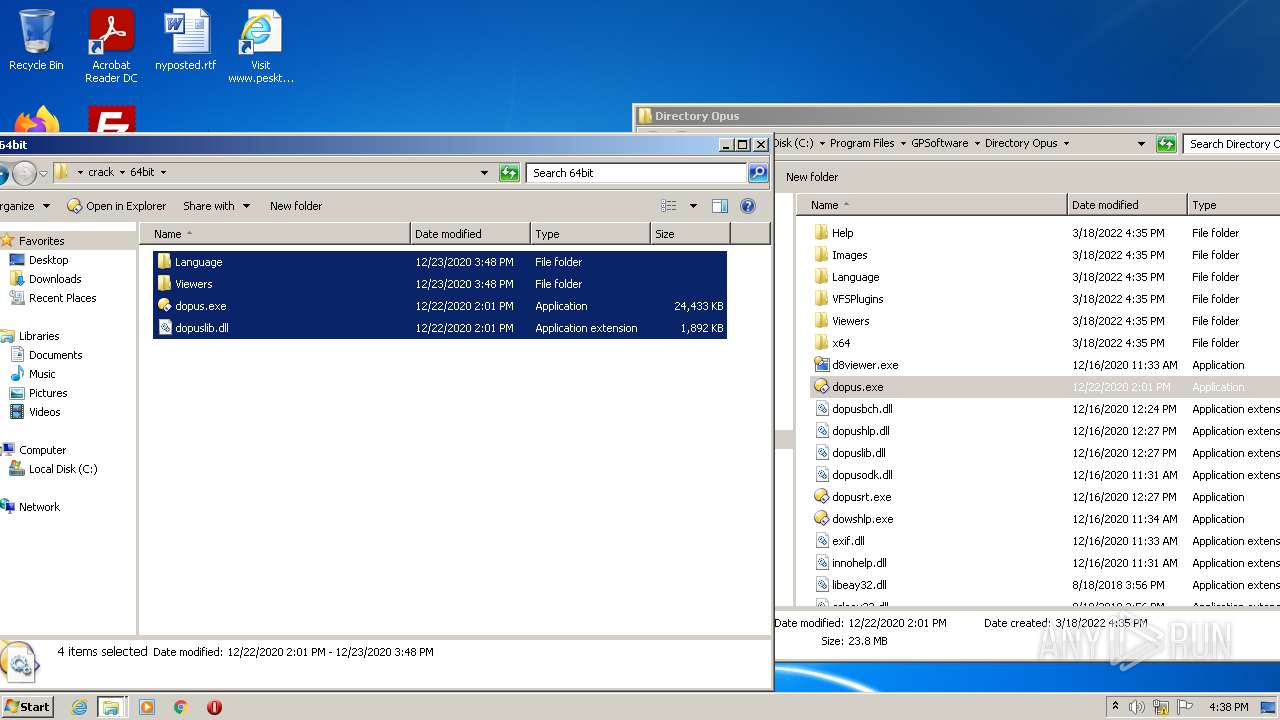
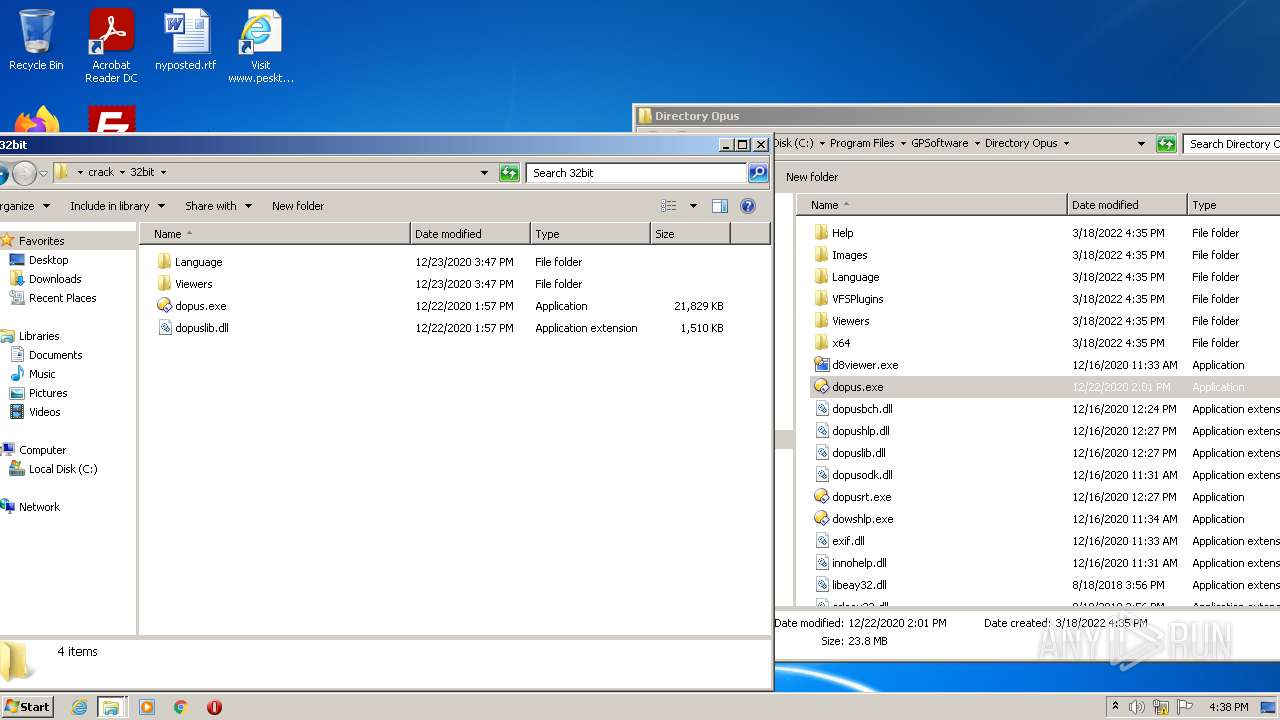
Drops executable file immediately after starts
- DOpusInstall.exe (PID: 3596)
- DOpusInstall.tmp (PID: 2016)
- DOpusInstall.exe (PID: 896)
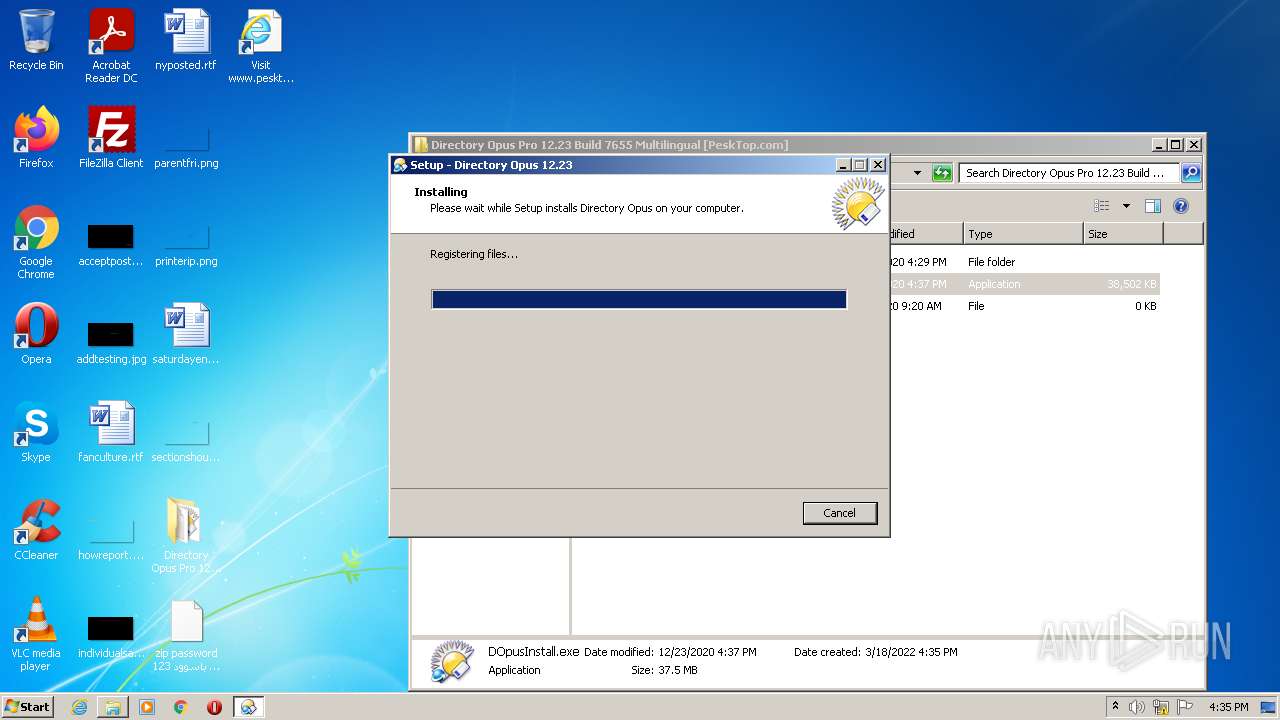
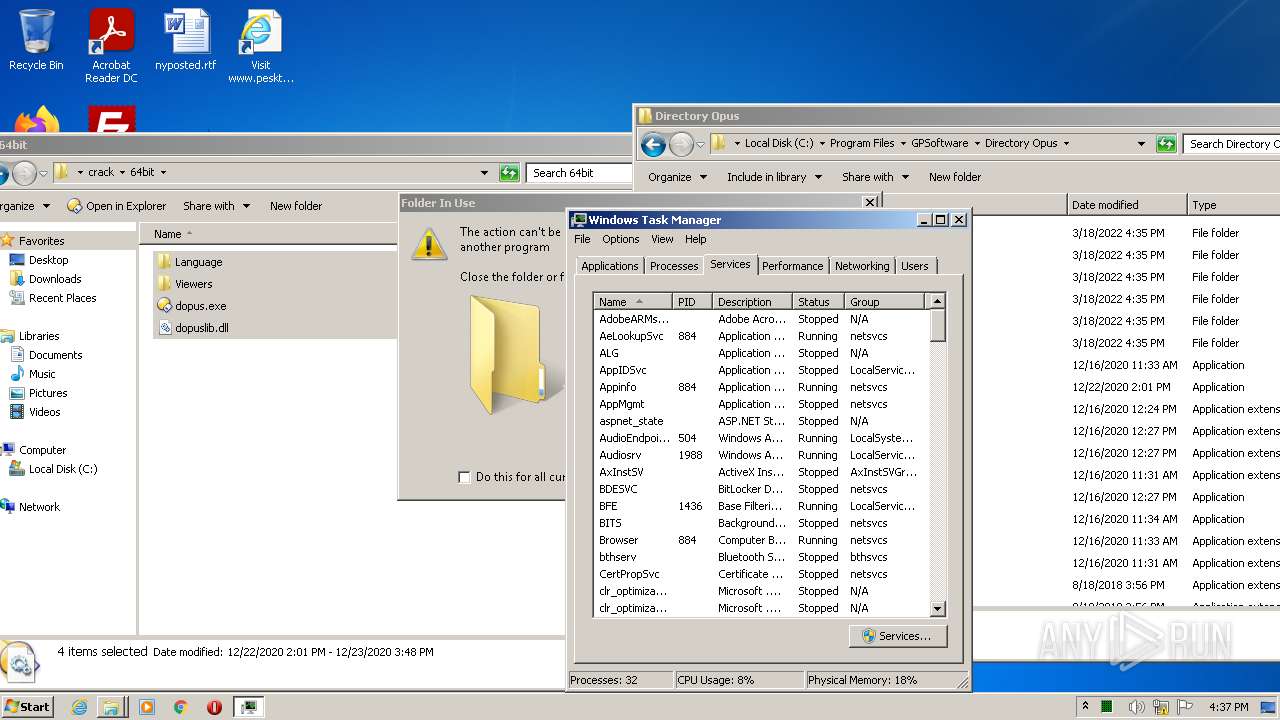
Registers / Runs the DLL via REGSVR32.EXE
- DOpusInstall.tmp (PID: 2016)
Actions looks like stealing of personal data
- svchost.exe (PID: 884)
- regsvr32.exe (PID: 2380)
- regsvr32.exe (PID: 3484)
- SearchProtocolHost.exe (PID: 3080)
- SetAppUserModelId-Win32.exe (PID: 2064)
- DOpusInstall.tmp (PID: 2016)
- dopusrt.exe (PID: 3616)
- DOpusInstall.tmp (PID: 3192)
- dopusrt.exe (PID: 1432)
- Explorer.EXE (PID: 584)
- dopusrt.exe (PID: 3672)
- explorer.exe (PID: 2508)
- dopus.exe (PID: 908)
- DllHost.exe (PID: 4028)
- taskmgr.exe (PID: 2564)
- consent.exe (PID: 2988)
- DllHost.exe (PID: 3248)
- dopusrt.exe (PID: 2840)
- dopus.exe (PID: 1560)
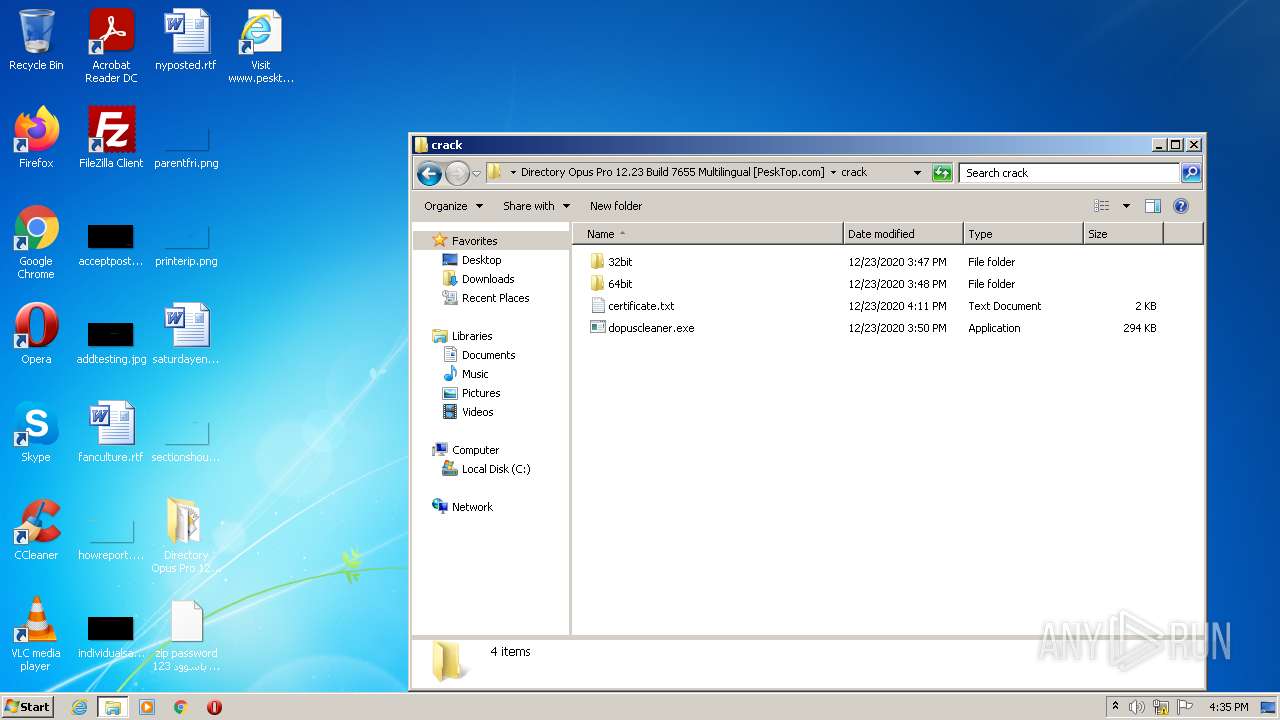
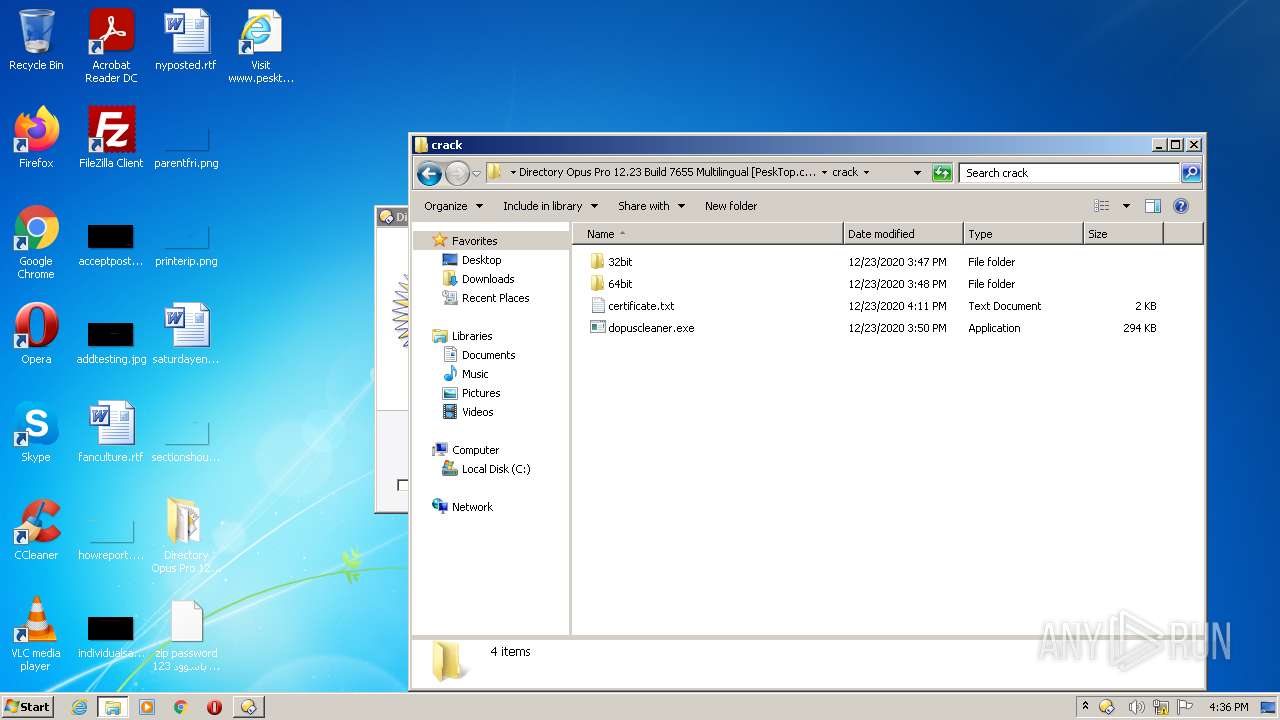
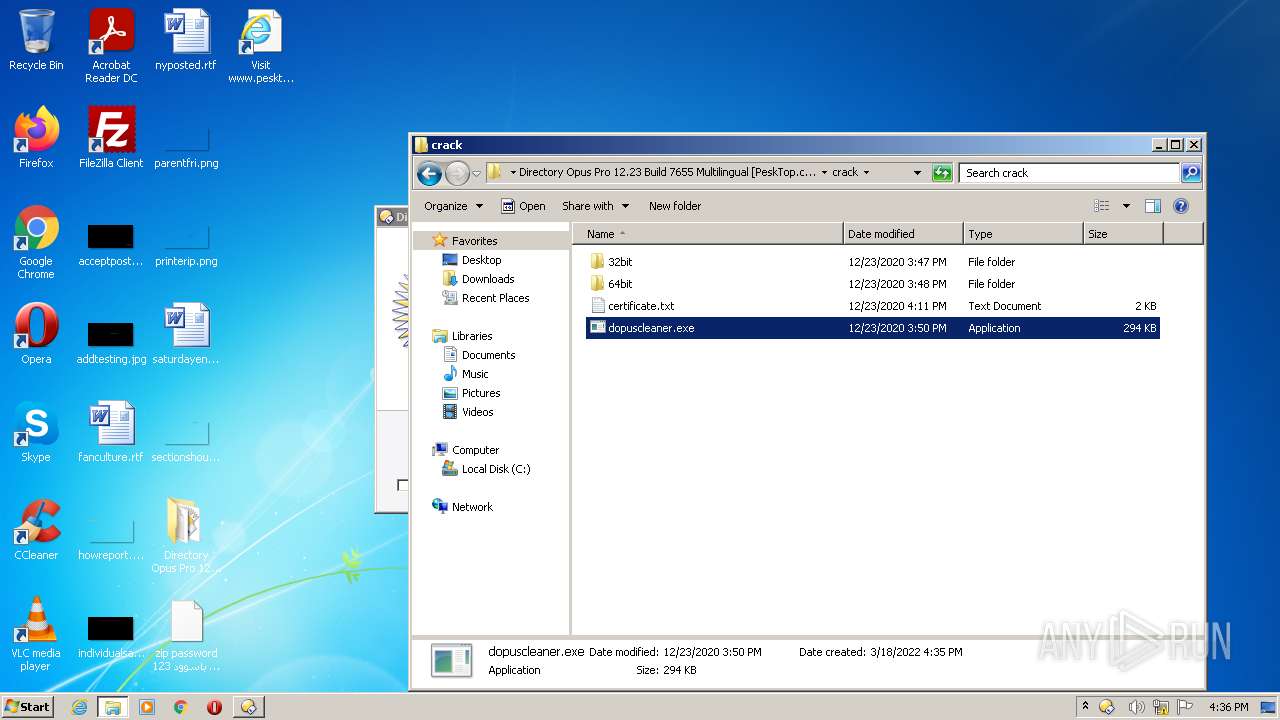
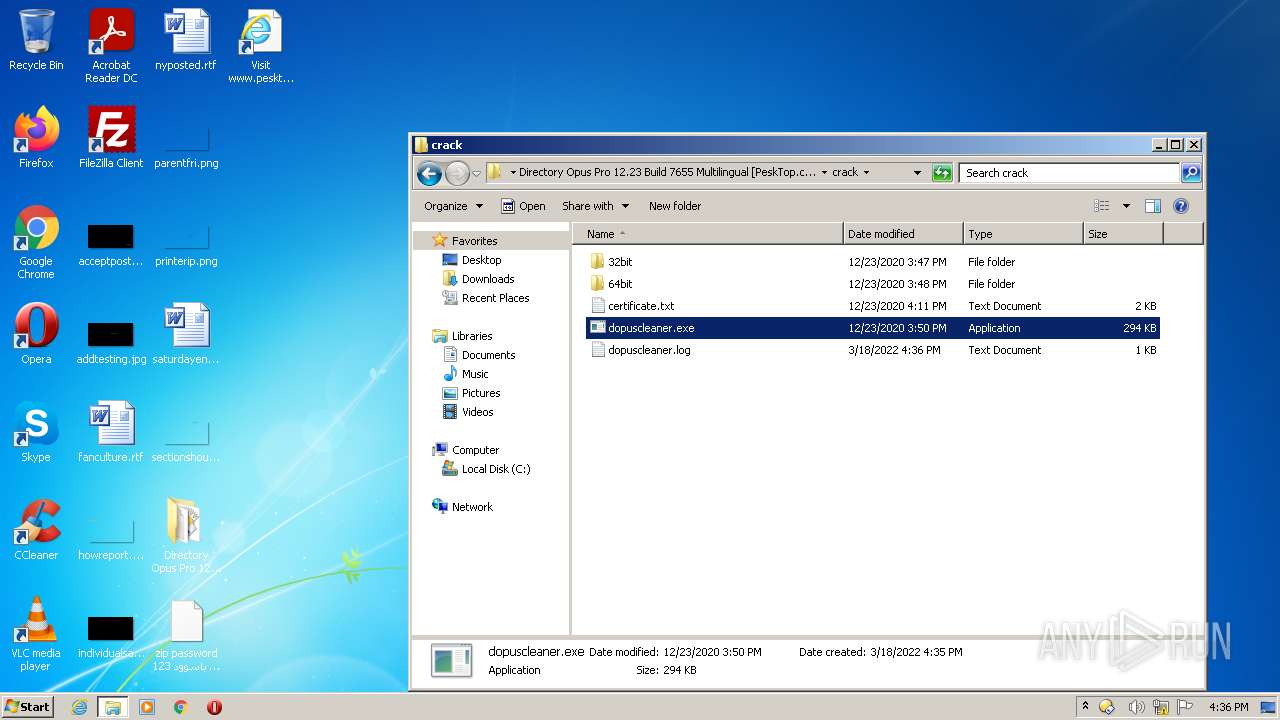
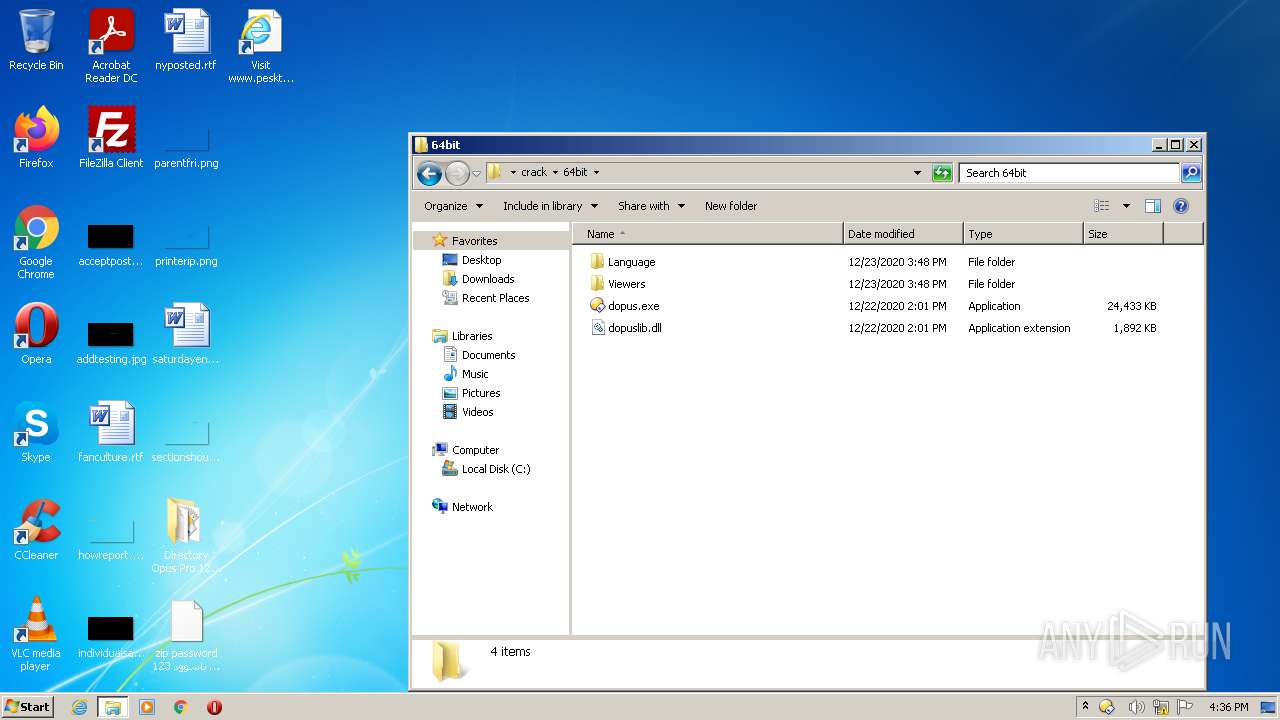
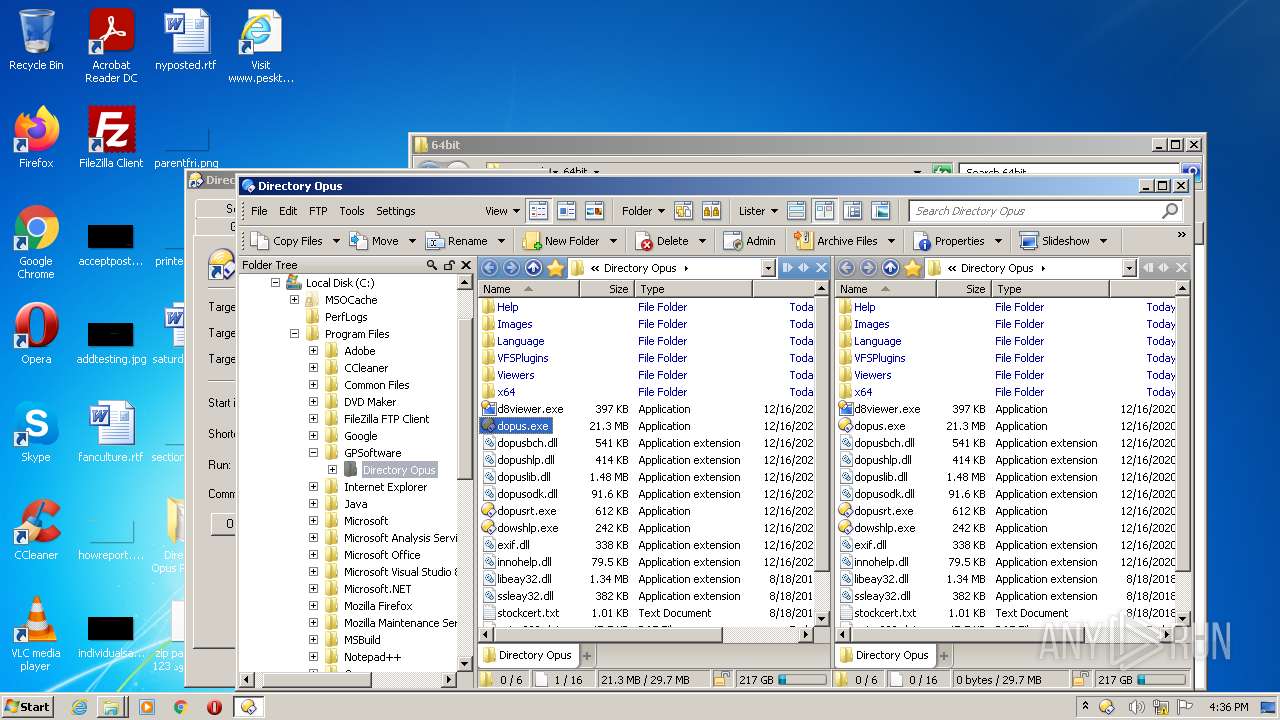
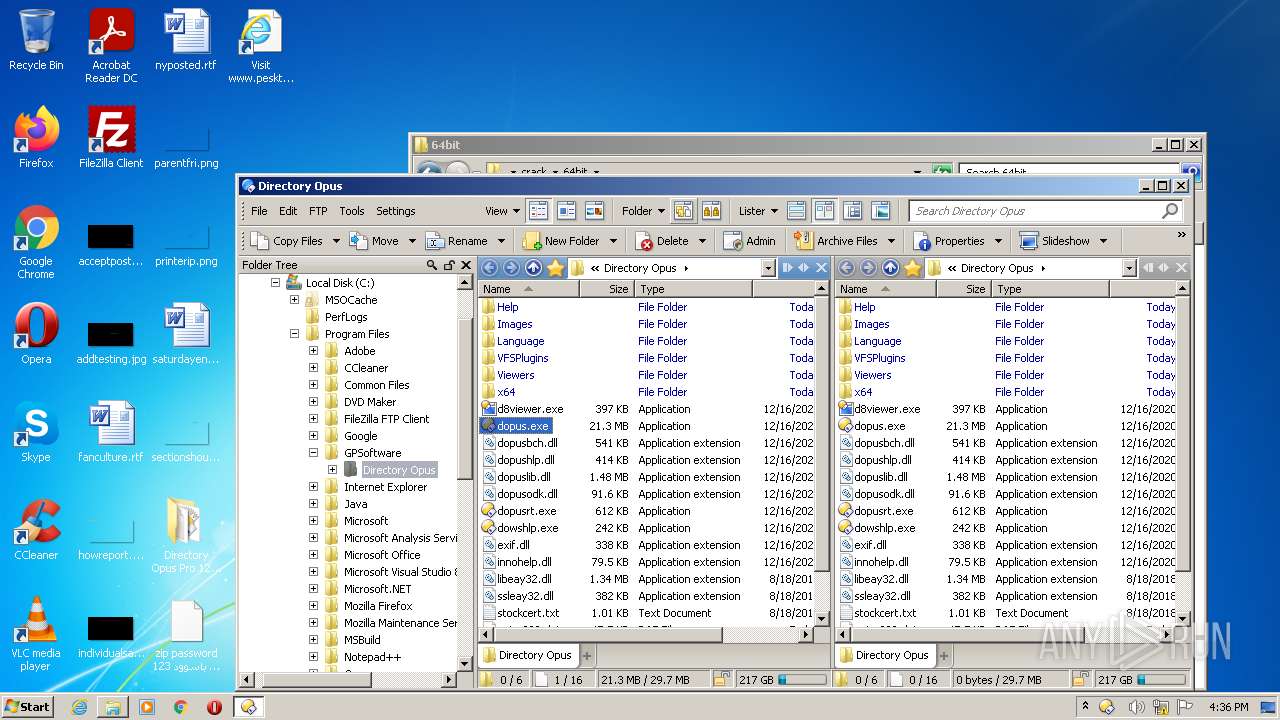
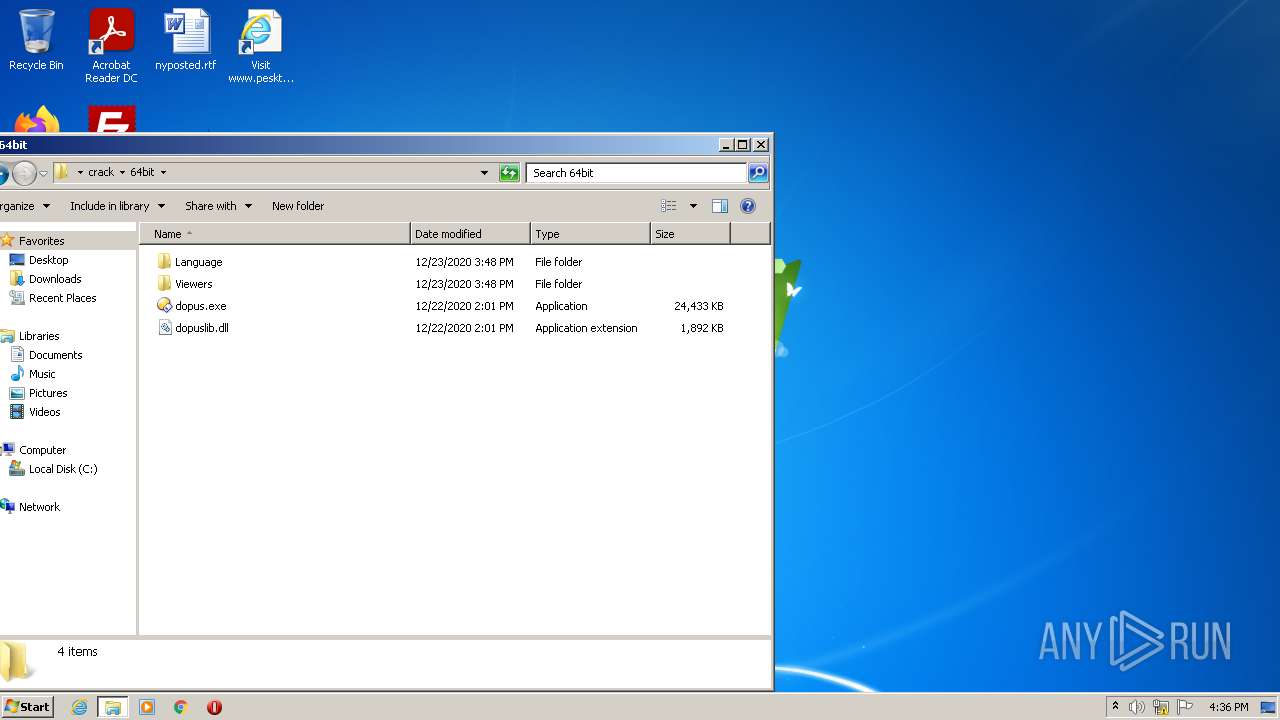
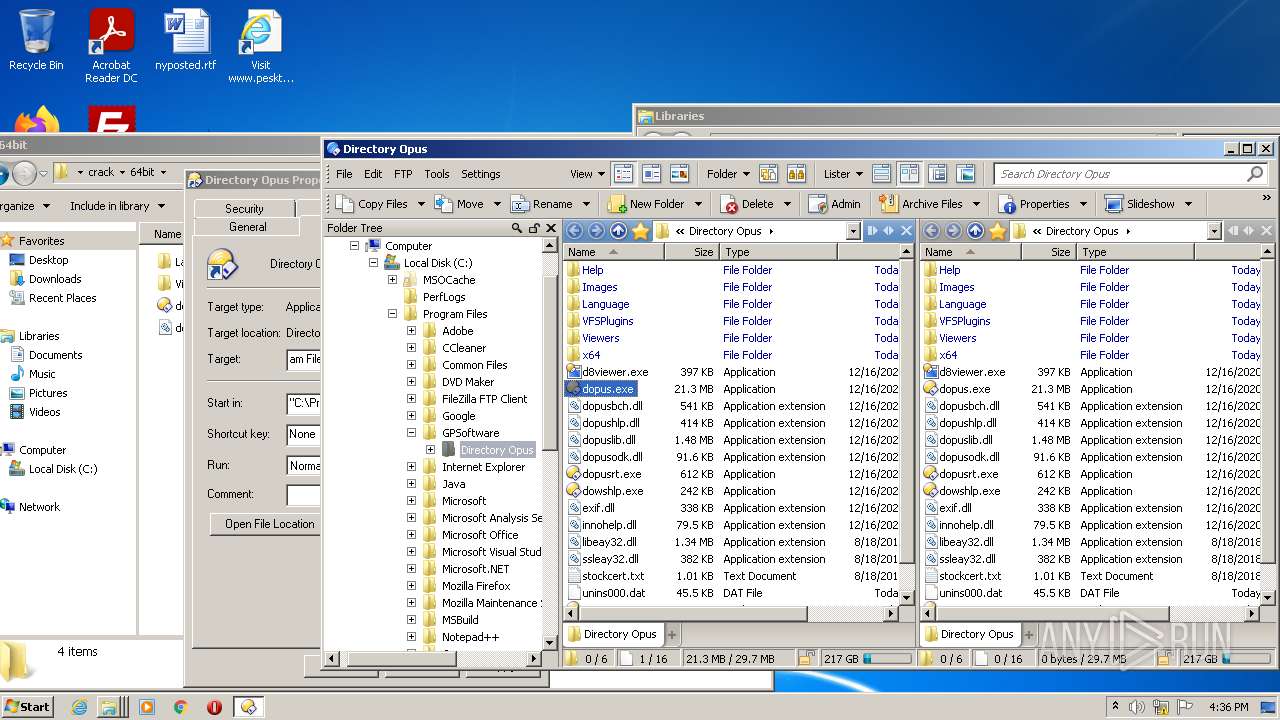
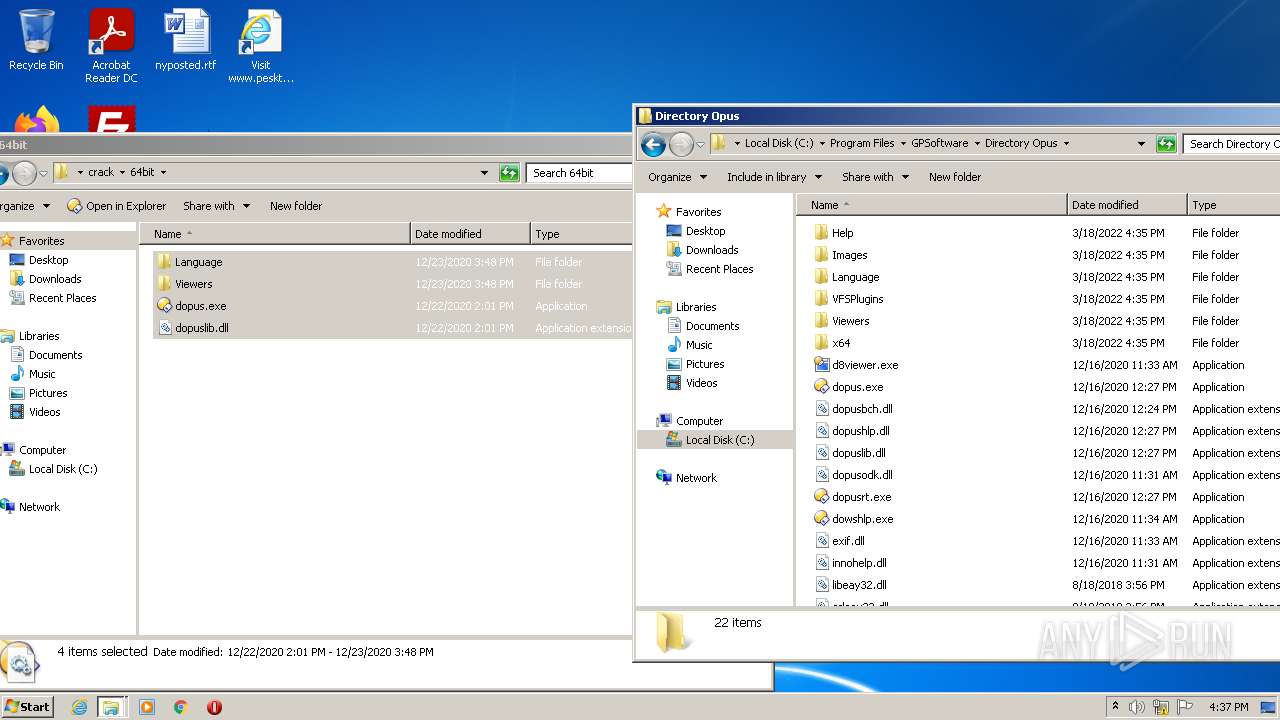
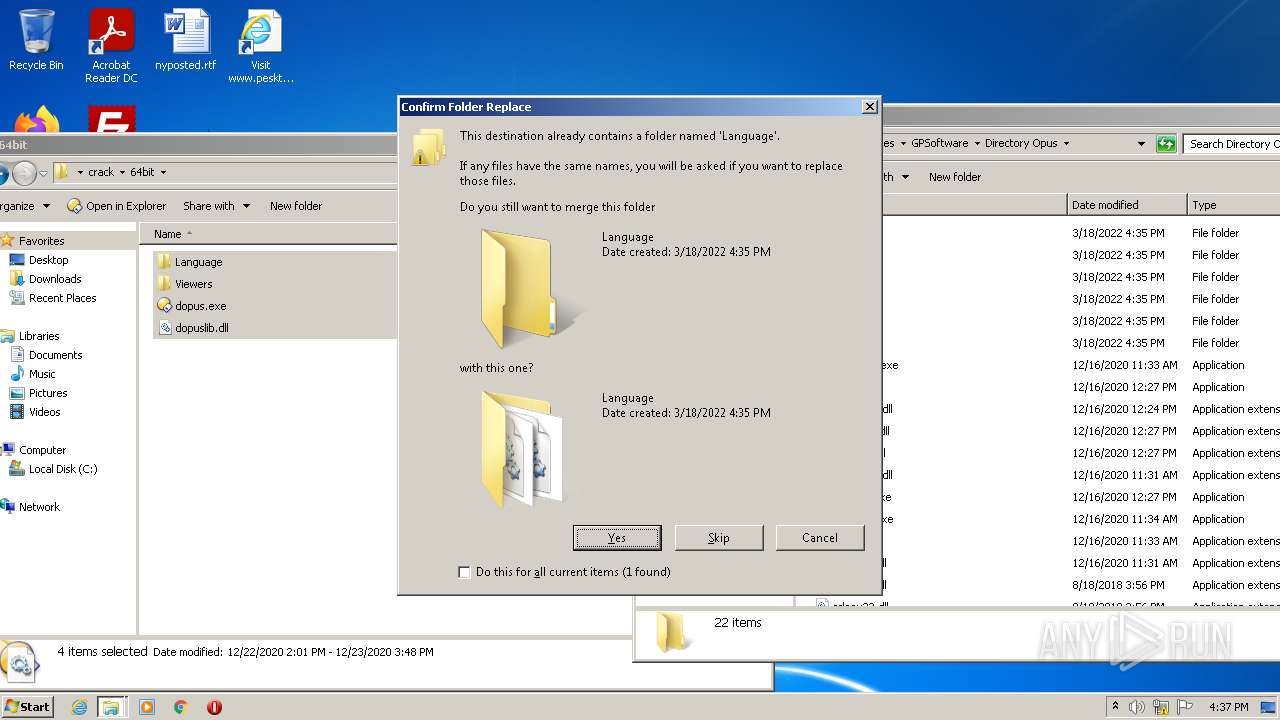
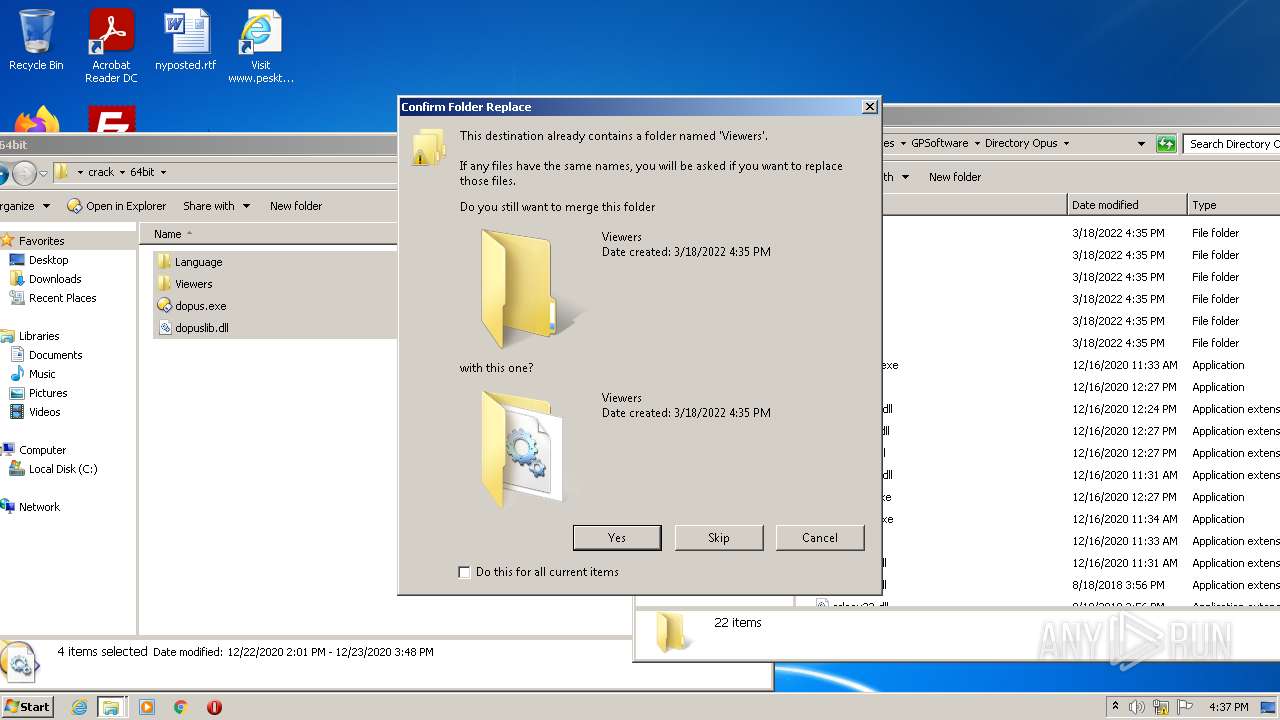
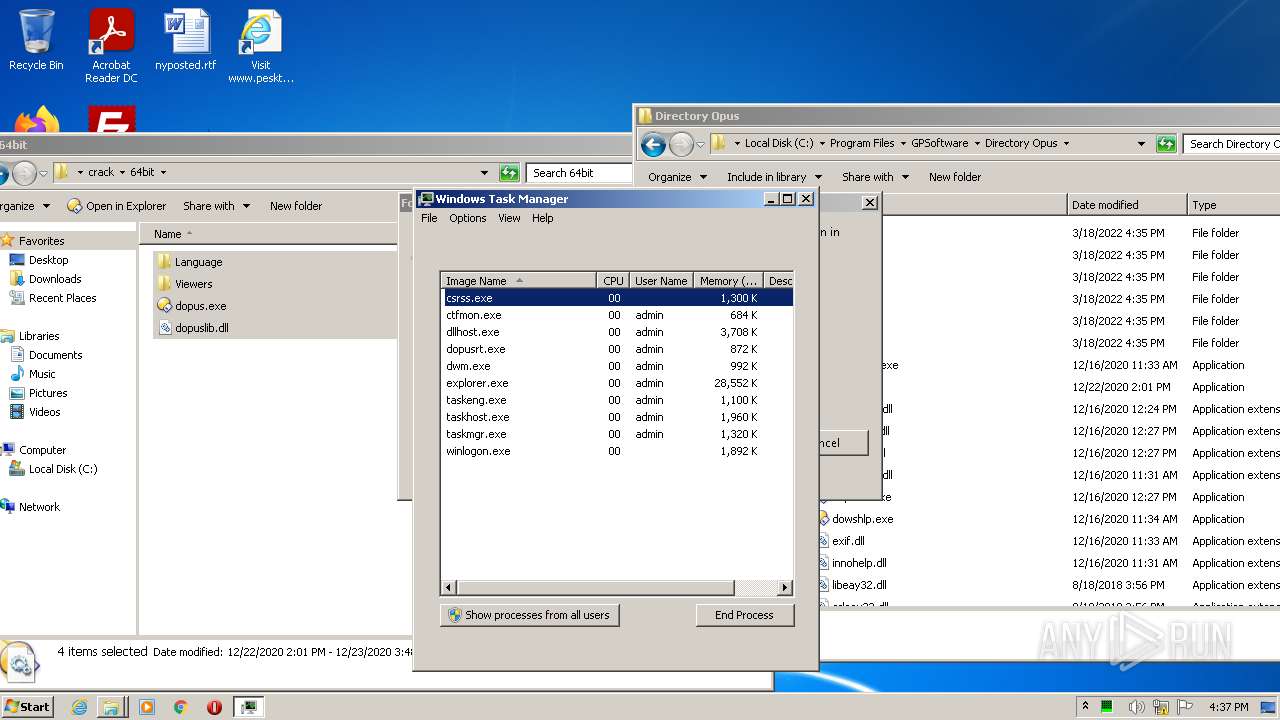
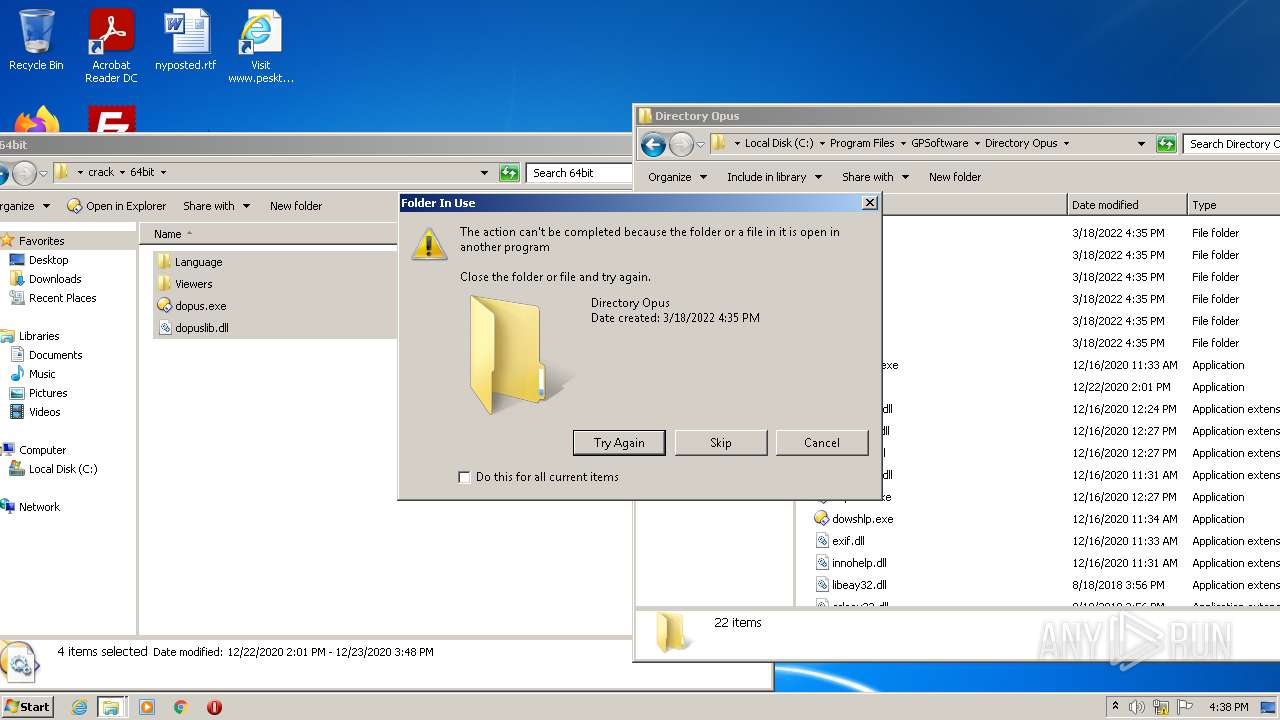
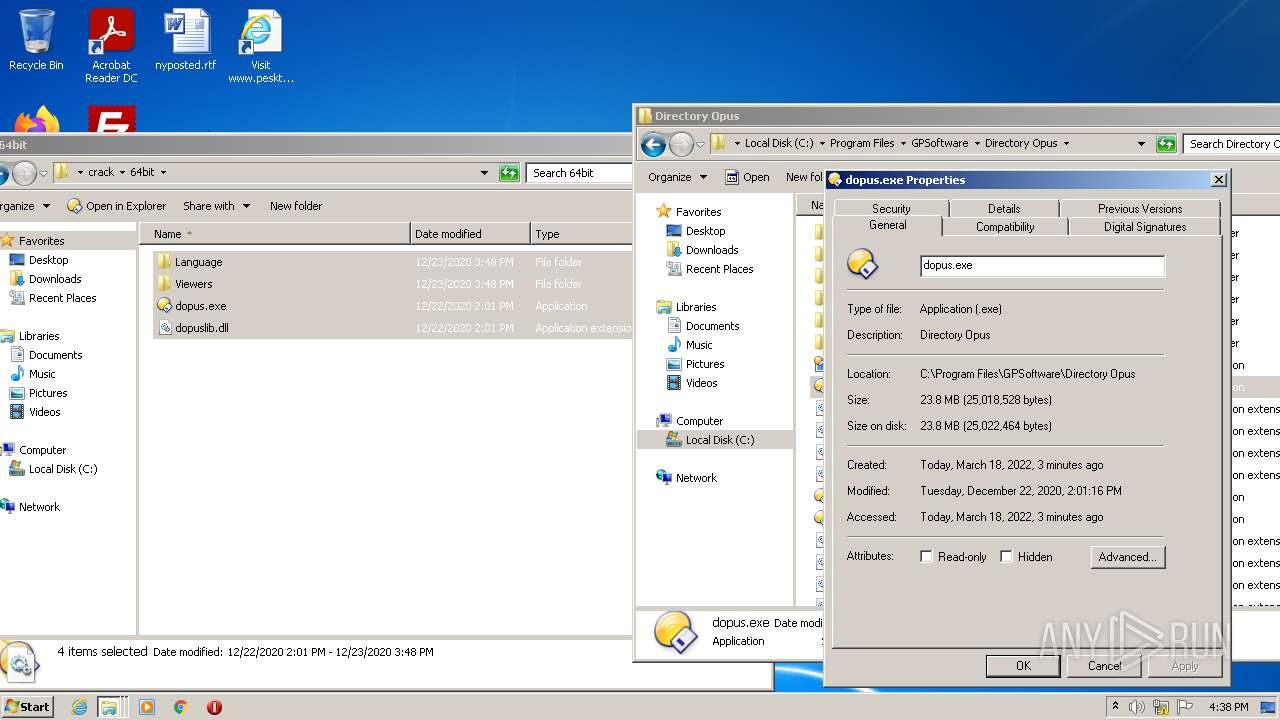
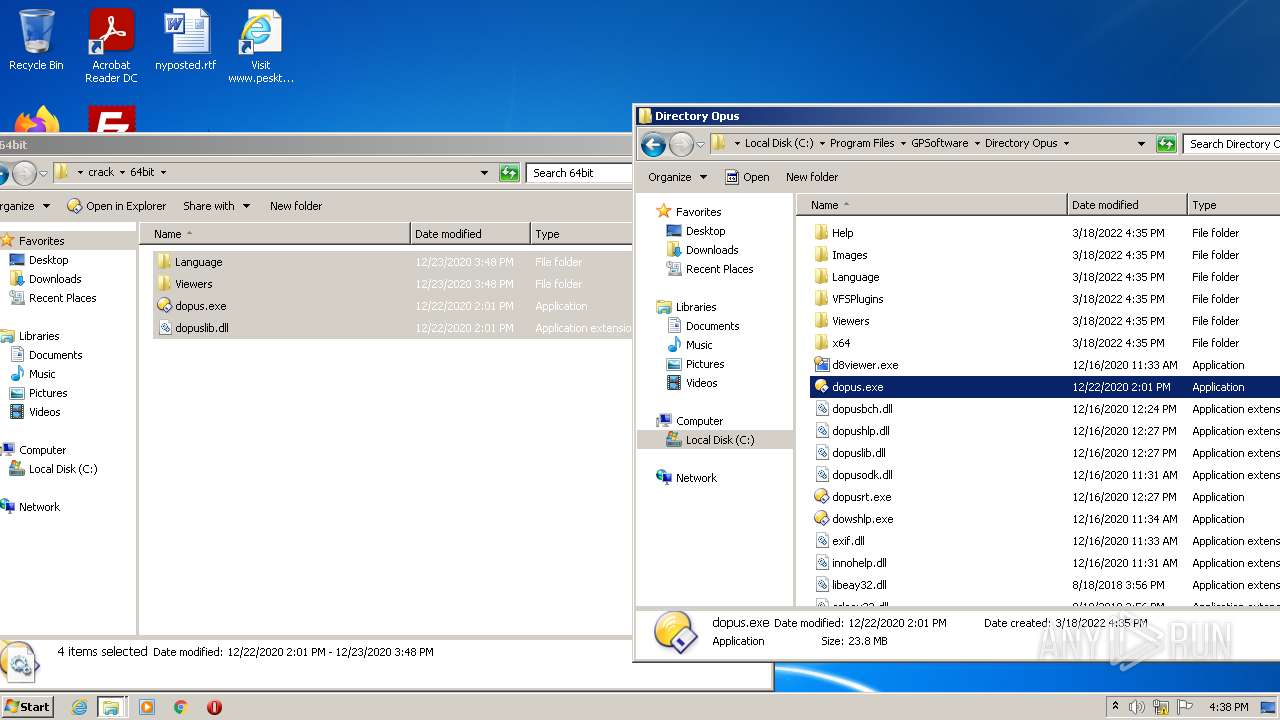
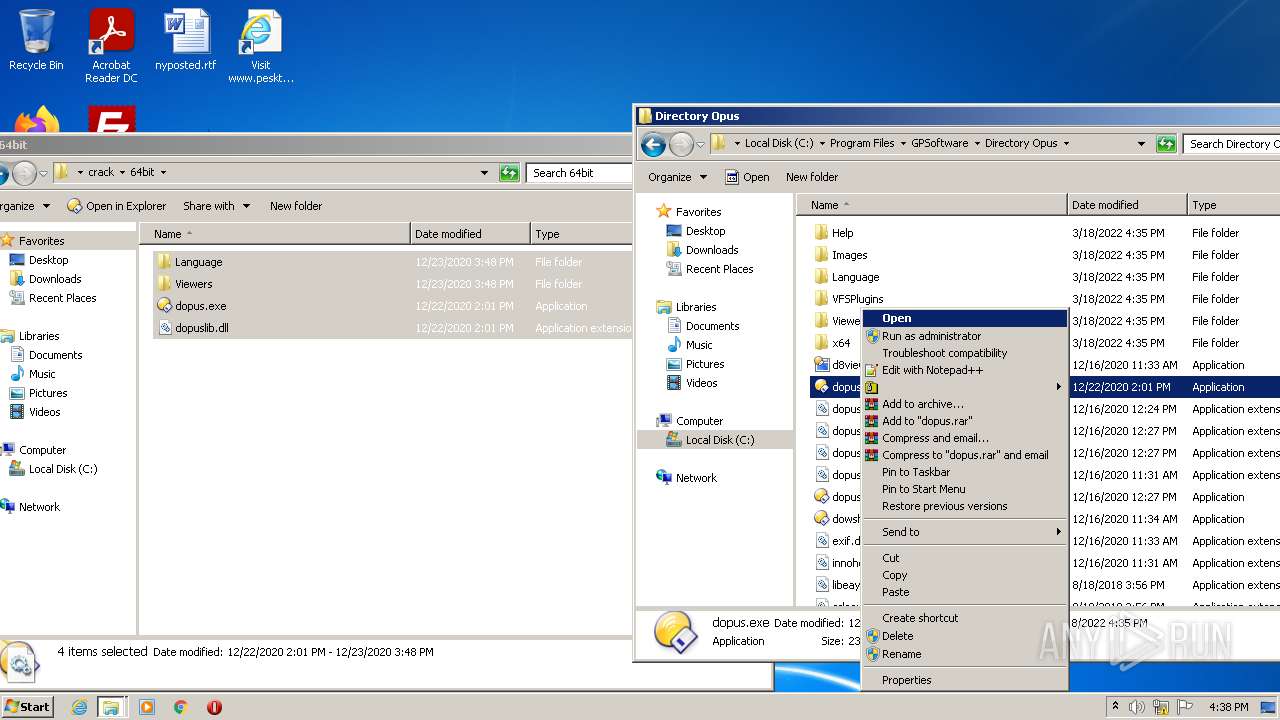
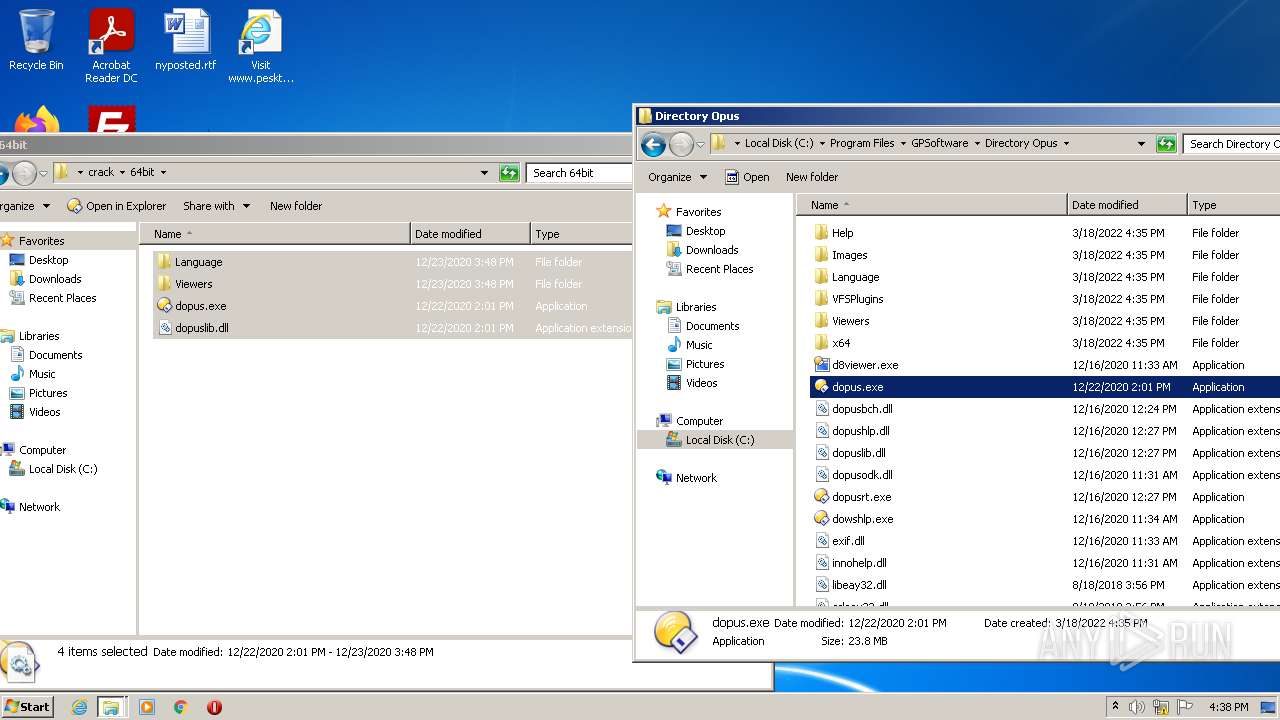
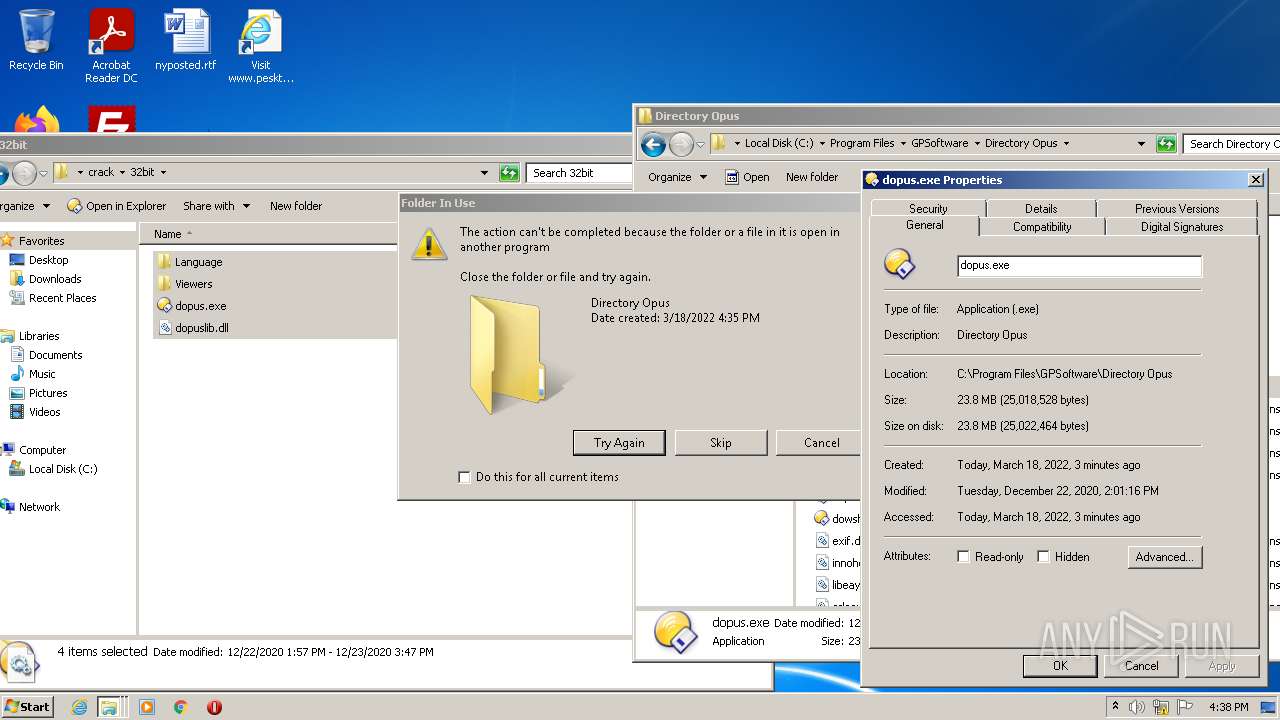
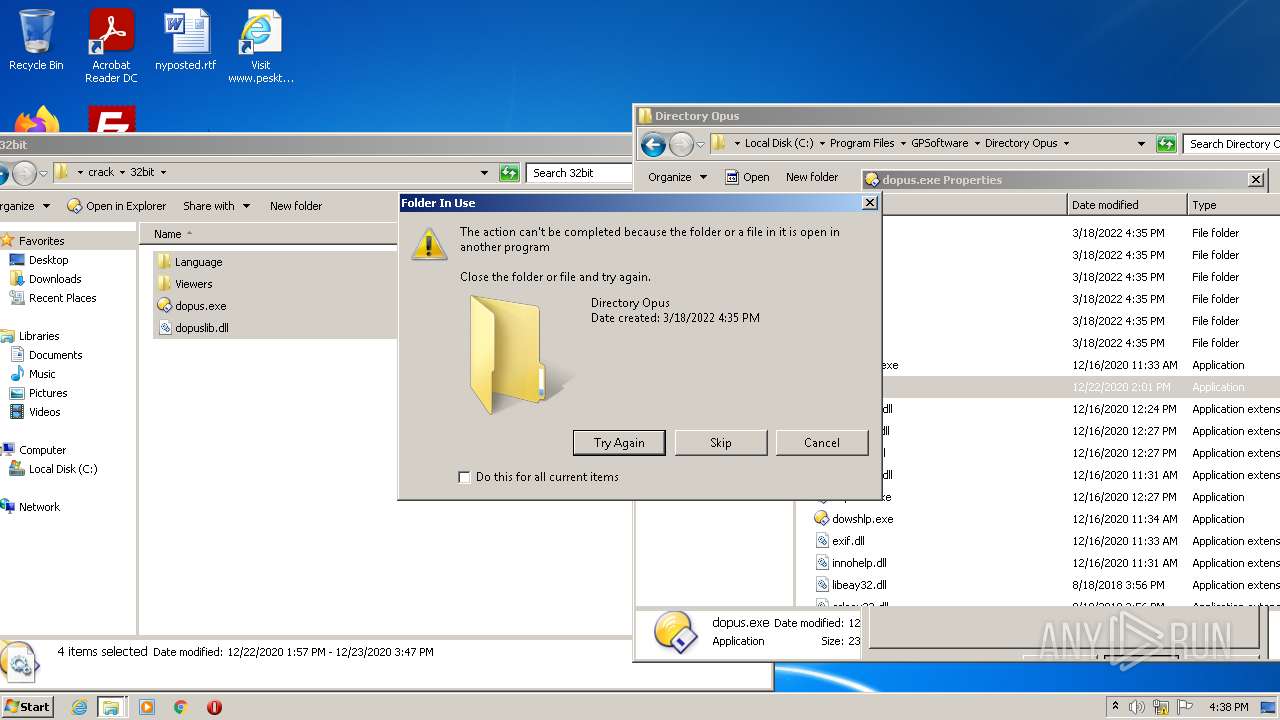
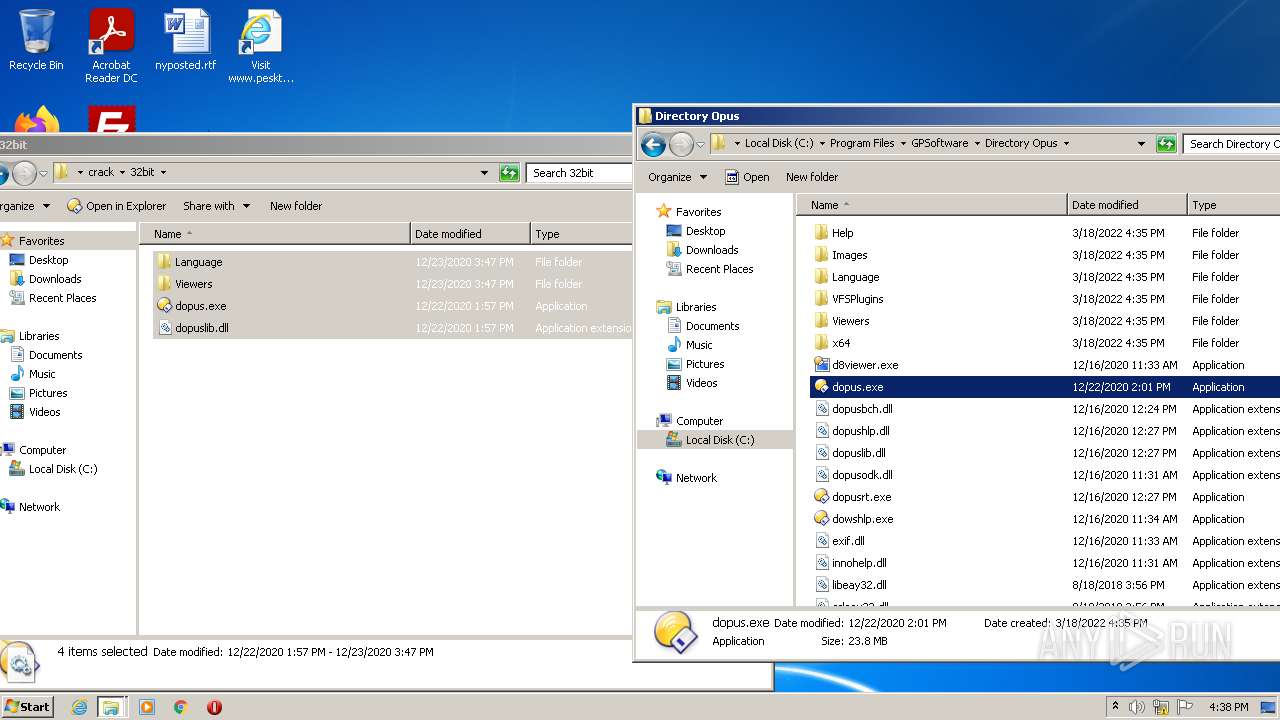
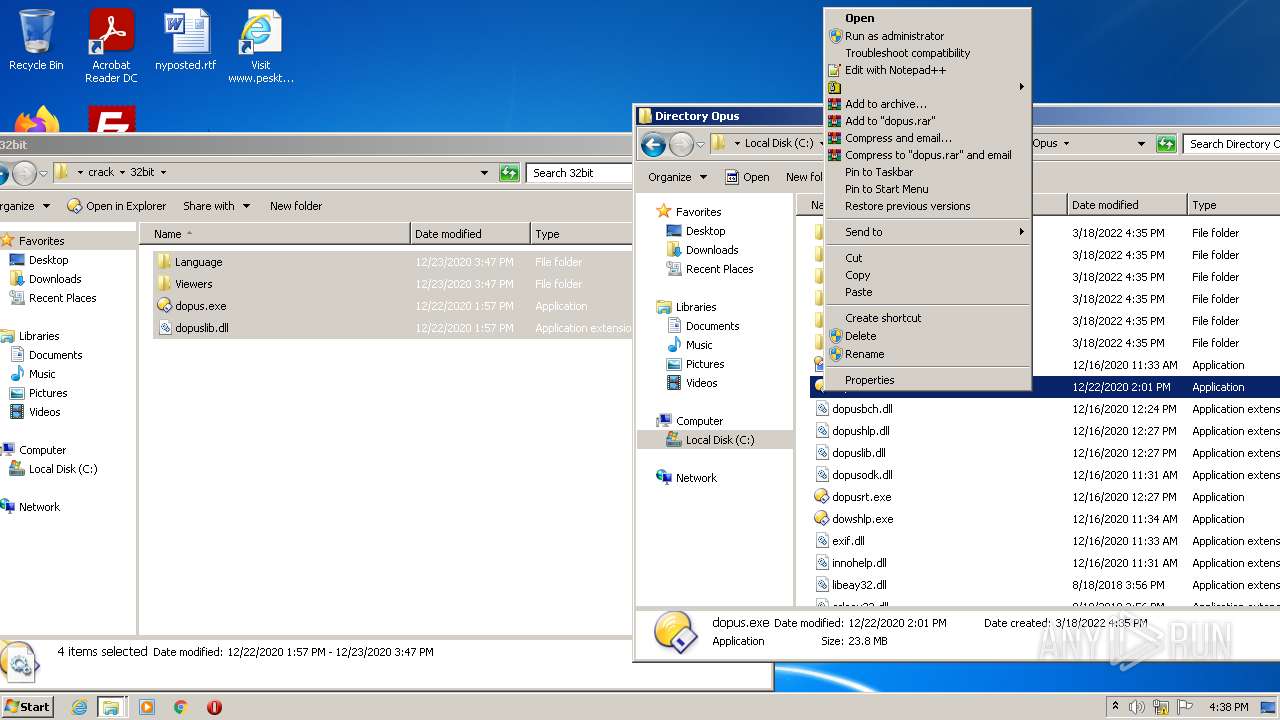
Application was dropped or rewritten from another process
- dopusrt.exe (PID: 3616)
- dopus.exe (PID: 908)
- dopusrt.exe (PID: 1432)
- dopuscleaner.exe (PID: 3084)
- dopusrt.exe (PID: 2840)
- dopusrt.exe (PID: 3672)
- dopus.exe (PID: 1560)
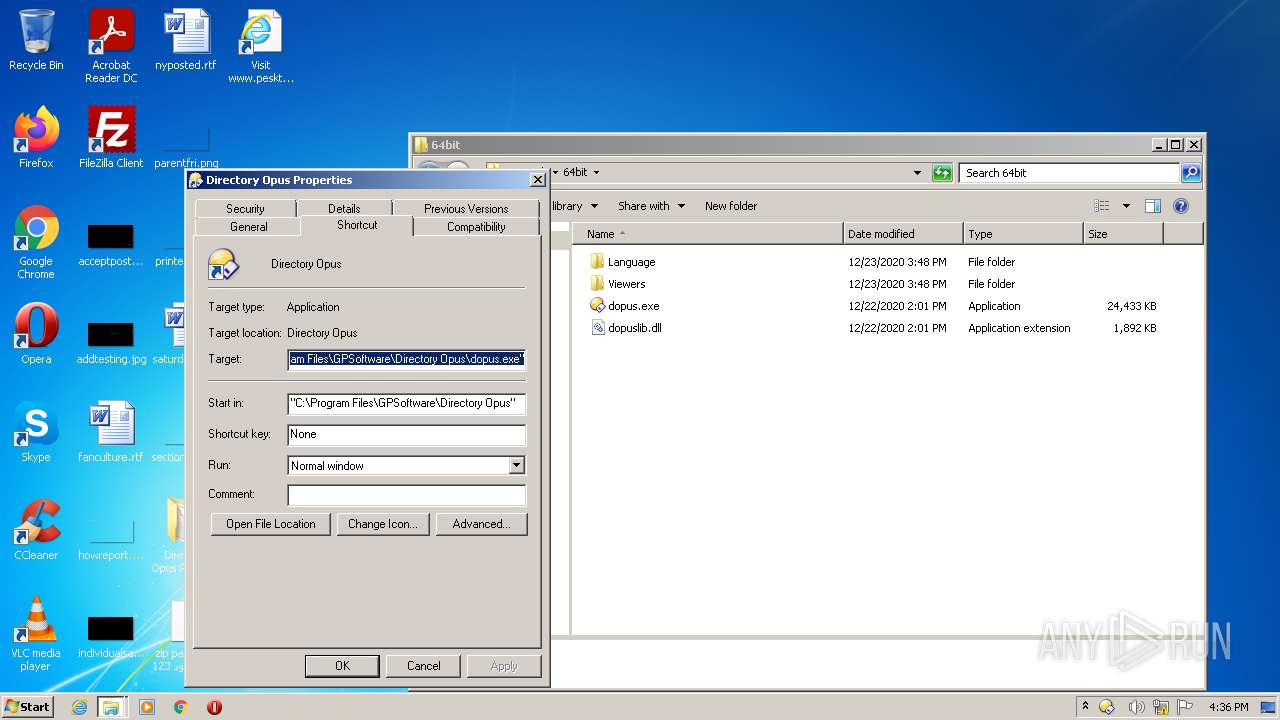
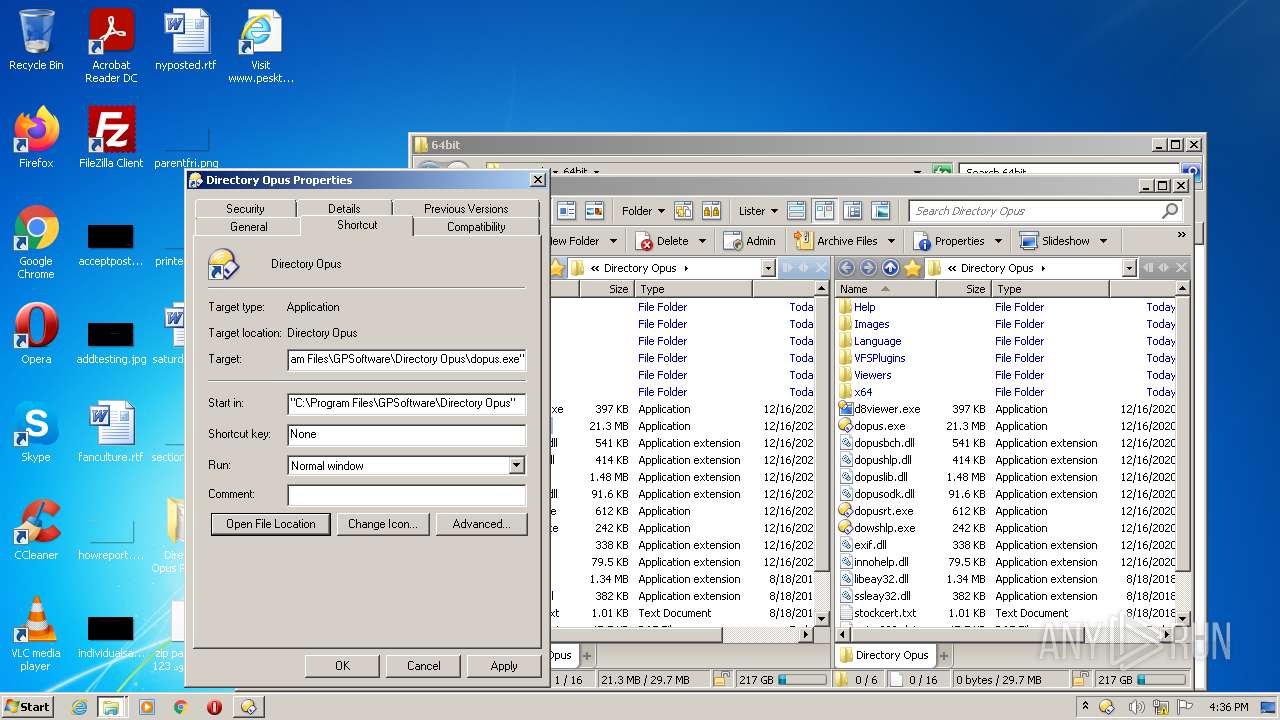
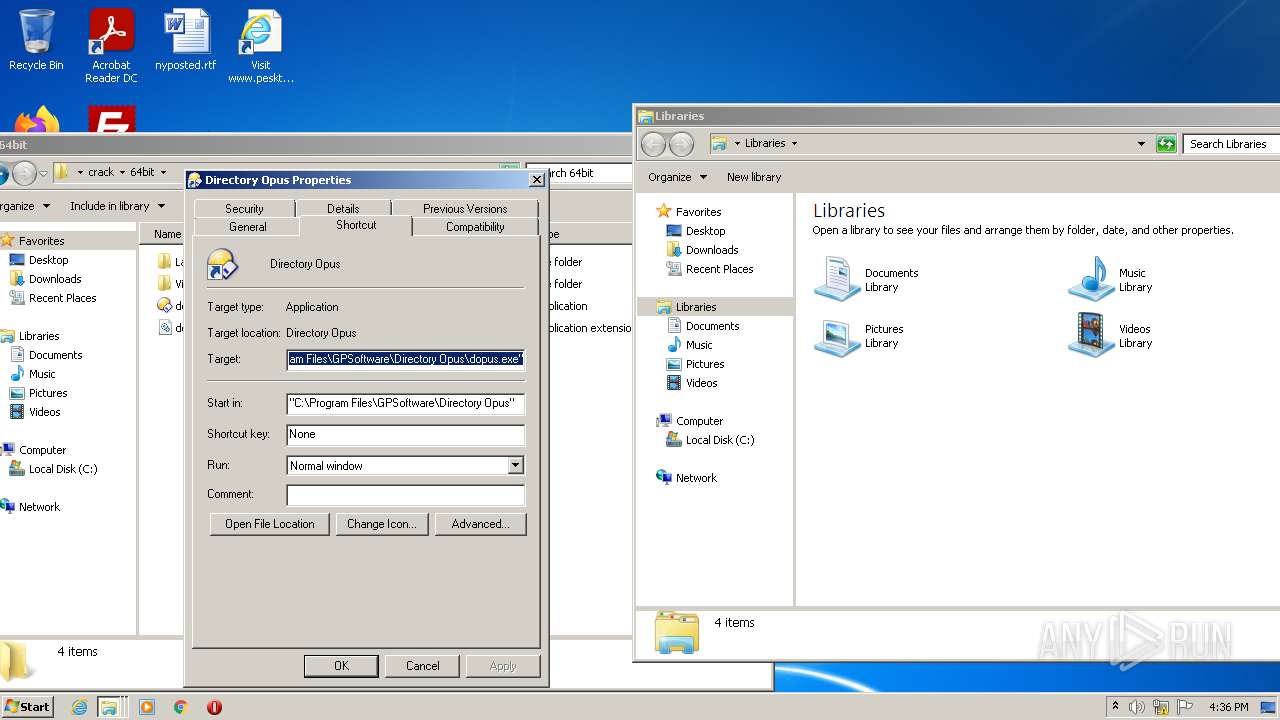
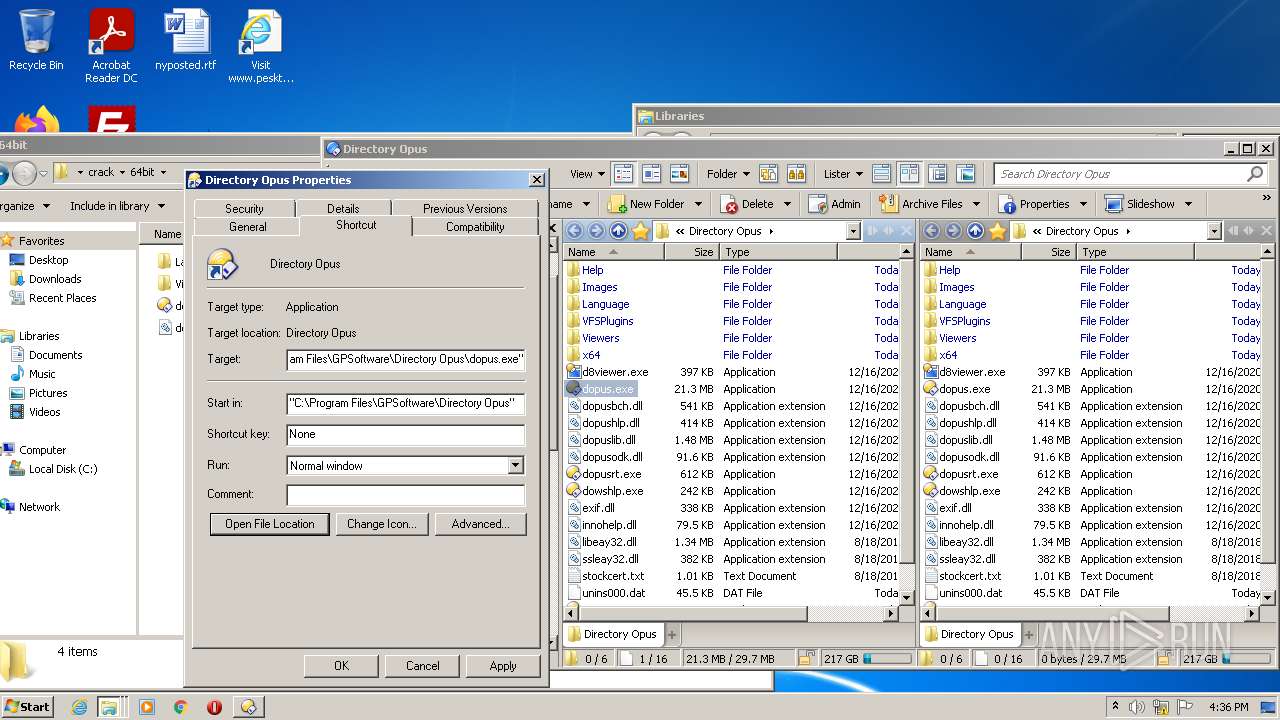
Writes to a start menu file
- dopus.exe (PID: 908)
Changes the autorun value in the registry
- dopus.exe (PID: 908)
SUSPICIOUS
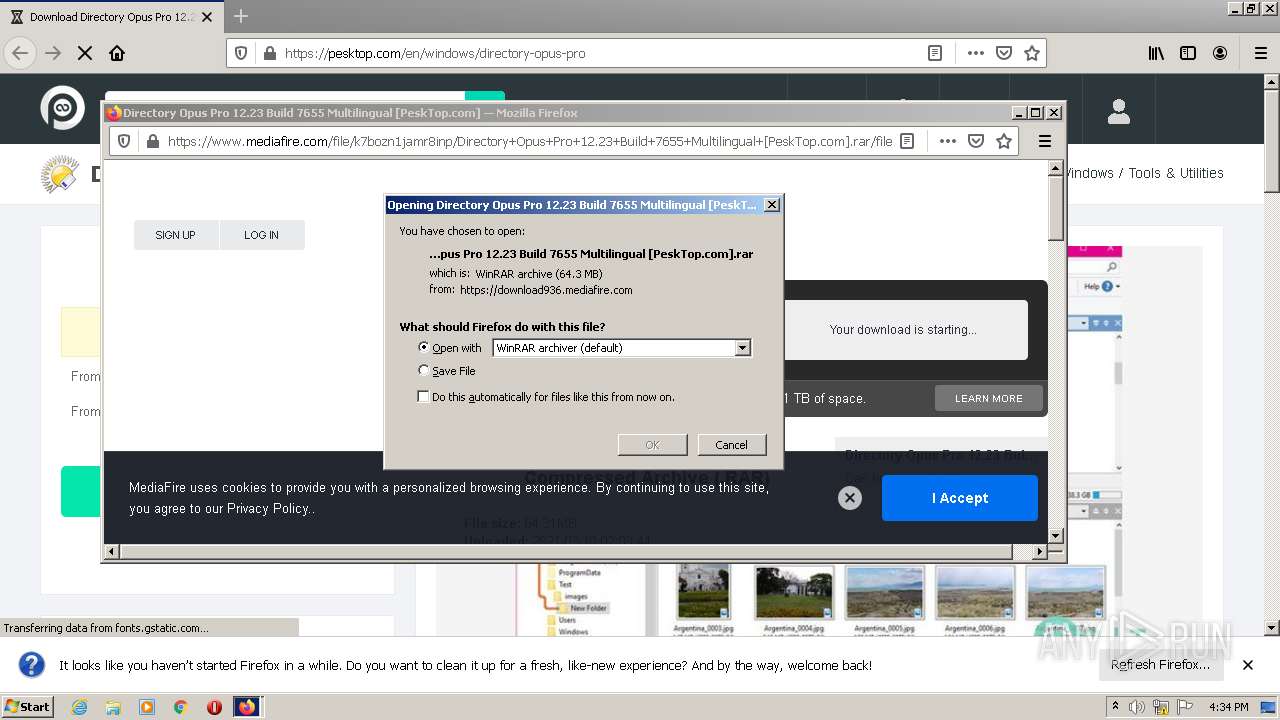
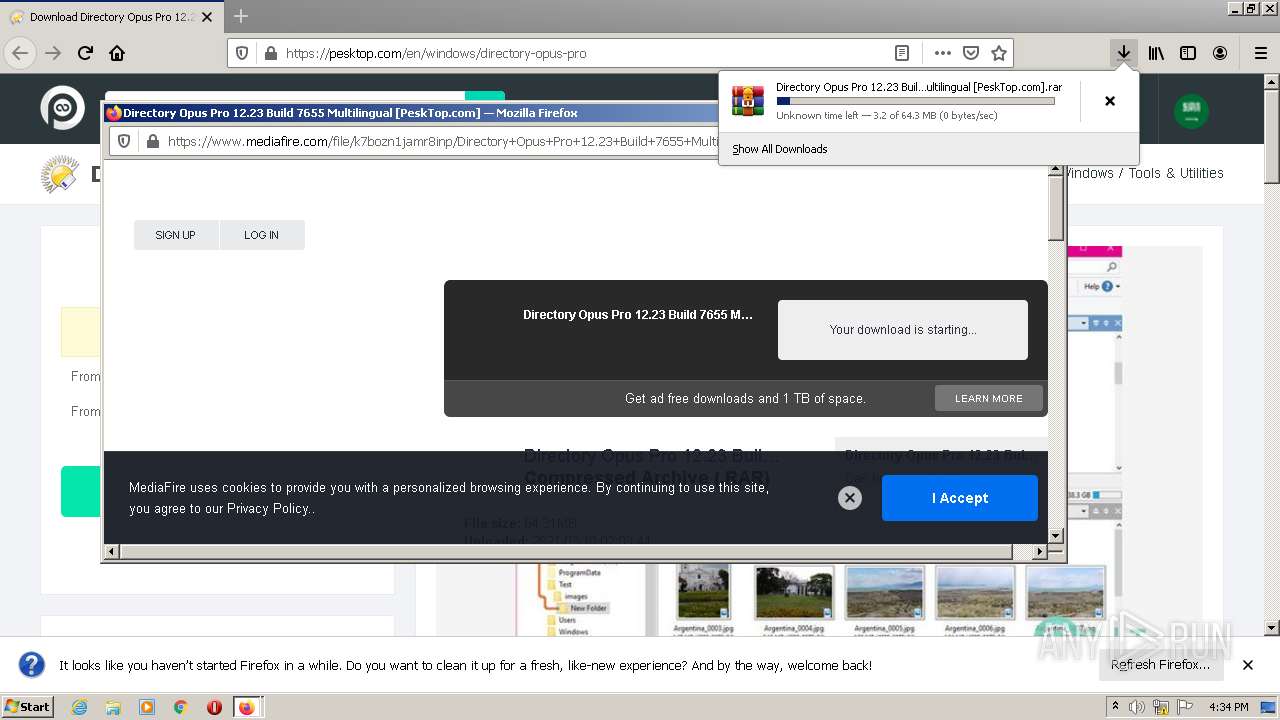
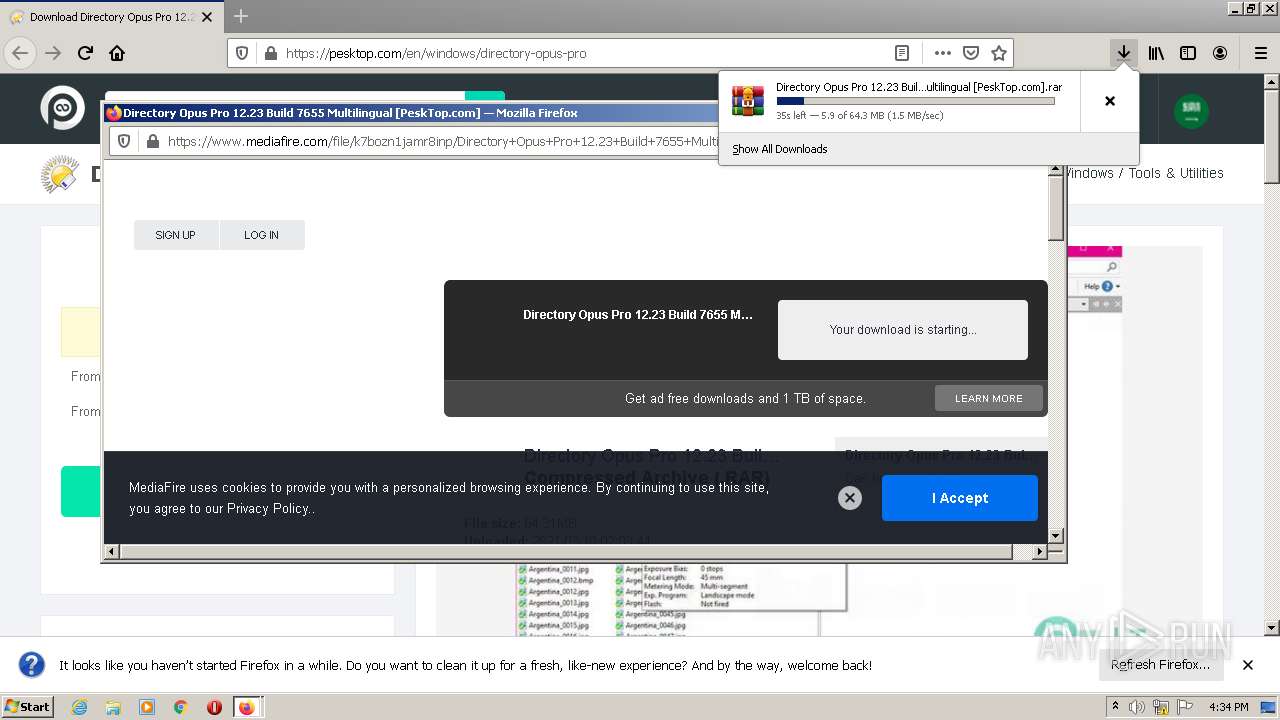
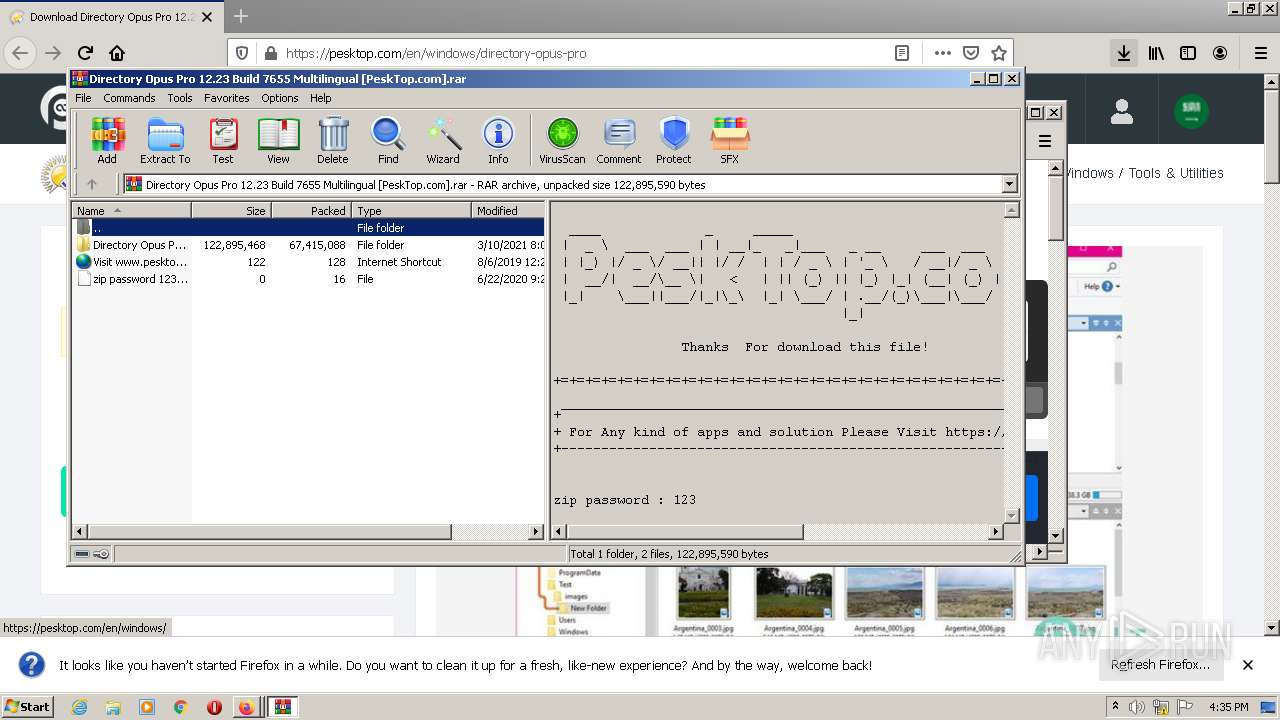
Executable content was dropped or overwritten
- firefox.exe (PID: 3036)
- WinRAR.exe (PID: 2356)
- DOpusInstall.exe (PID: 3596)
- DOpusInstall.exe (PID: 896)
- DOpusInstall.tmp (PID: 2016)
Drops a file that was compiled in debug mode
- firefox.exe (PID: 3036)
- WinRAR.exe (PID: 2356)
- DOpusInstall.tmp (PID: 2016)
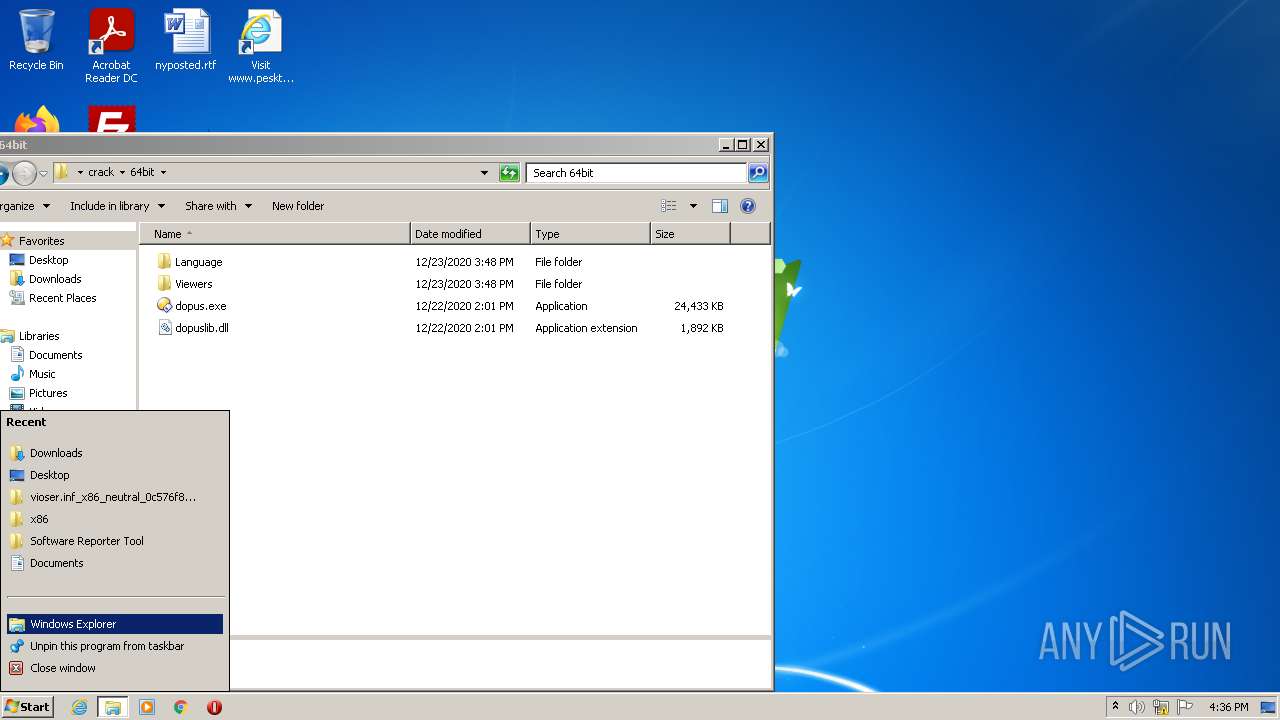
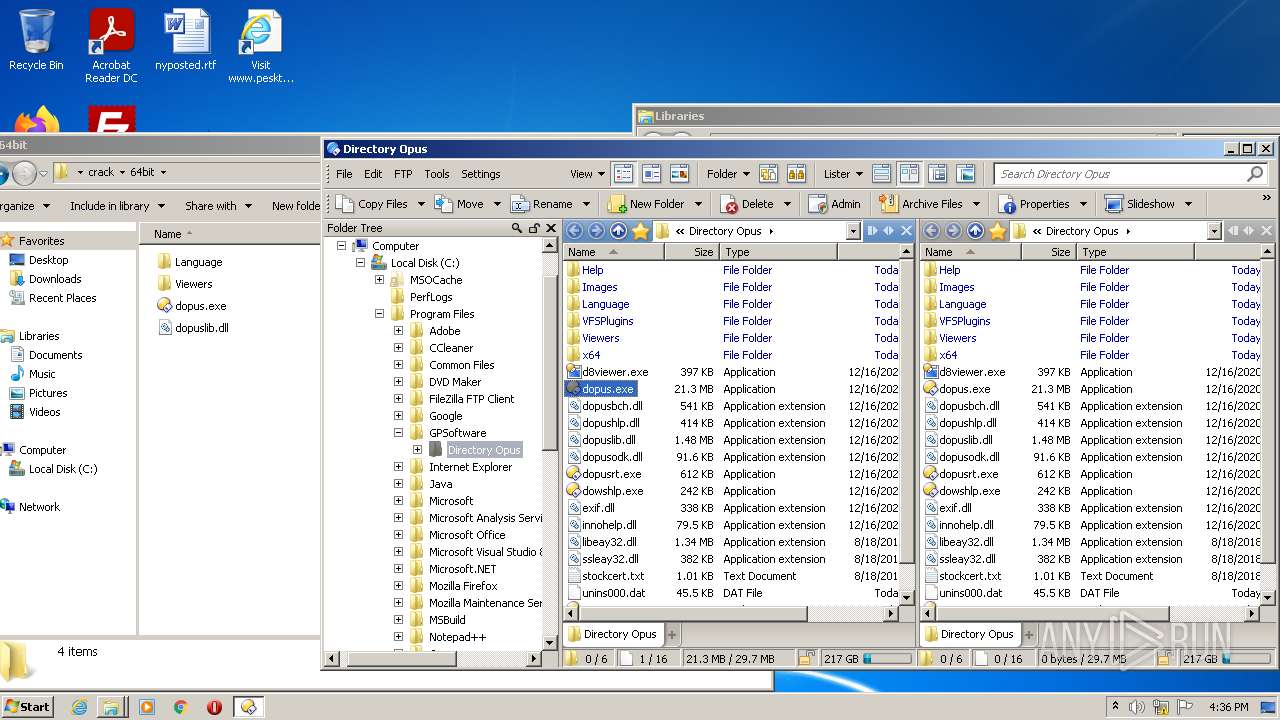
Creates files in the user directory
- Explorer.EXE (PID: 584)
- dopus.exe (PID: 908)
- dopus.exe (PID: 1560)
Reads the computer name
- WinRAR.exe (PID: 2356)
- DOpusInstall.tmp (PID: 3192)
- dopus.exe (PID: 908)
- dopusrt.exe (PID: 1432)
- dopus.exe (PID: 1560)
- DOpusInstall.tmp (PID: 2016)
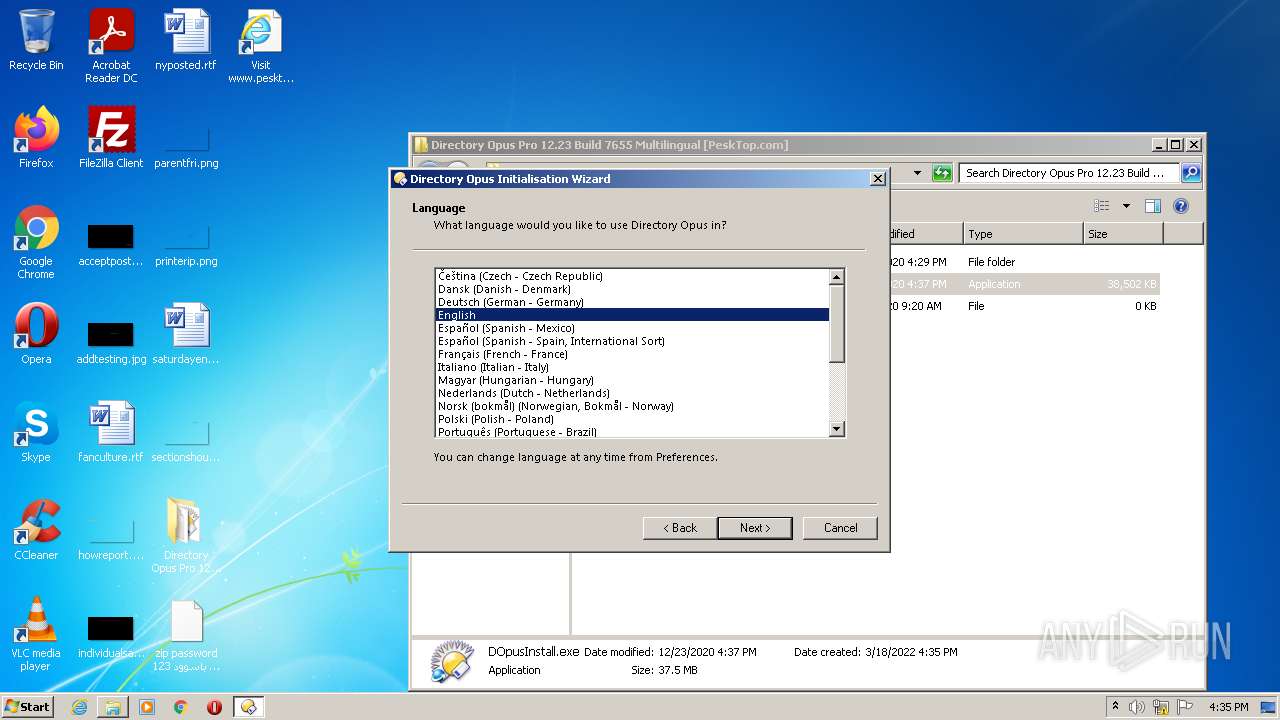
Checks supported languages
- WinRAR.exe (PID: 2356)
- DOpusInstall.exe (PID: 3596)
- DOpusInstall.tmp (PID: 3192)
- DOpusInstall.exe (PID: 896)
- DOpusInstall.tmp (PID: 2016)
- dopusrt.exe (PID: 3616)
- SetAppUserModelId-Win32.exe (PID: 2064)
- dopus.exe (PID: 908)
- dopusrt.exe (PID: 1432)
- dopusrt.exe (PID: 3672)
- dopuscleaner.exe (PID: 3084)
- dopusrt.exe (PID: 2840)
- dopus.exe (PID: 1560)
Reads the Windows organization settings
- DOpusInstall.tmp (PID: 2016)
Reads Windows owner or organization settings
- DOpusInstall.tmp (PID: 2016)
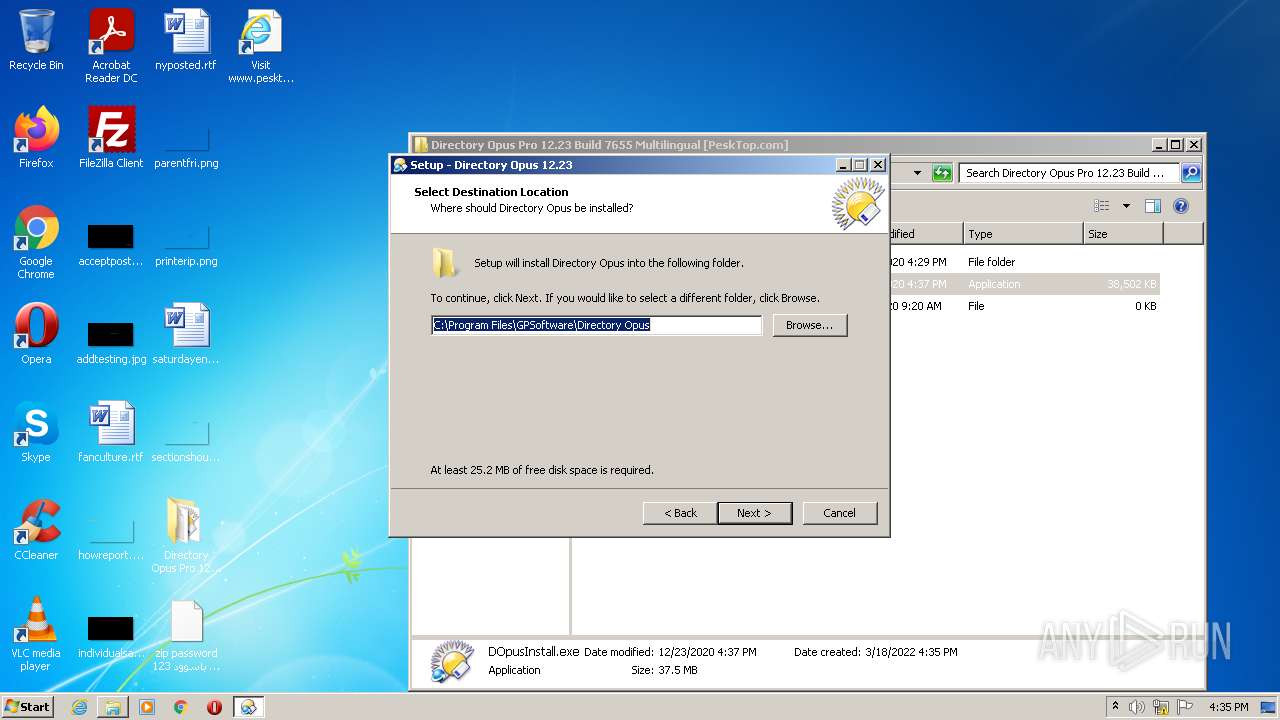
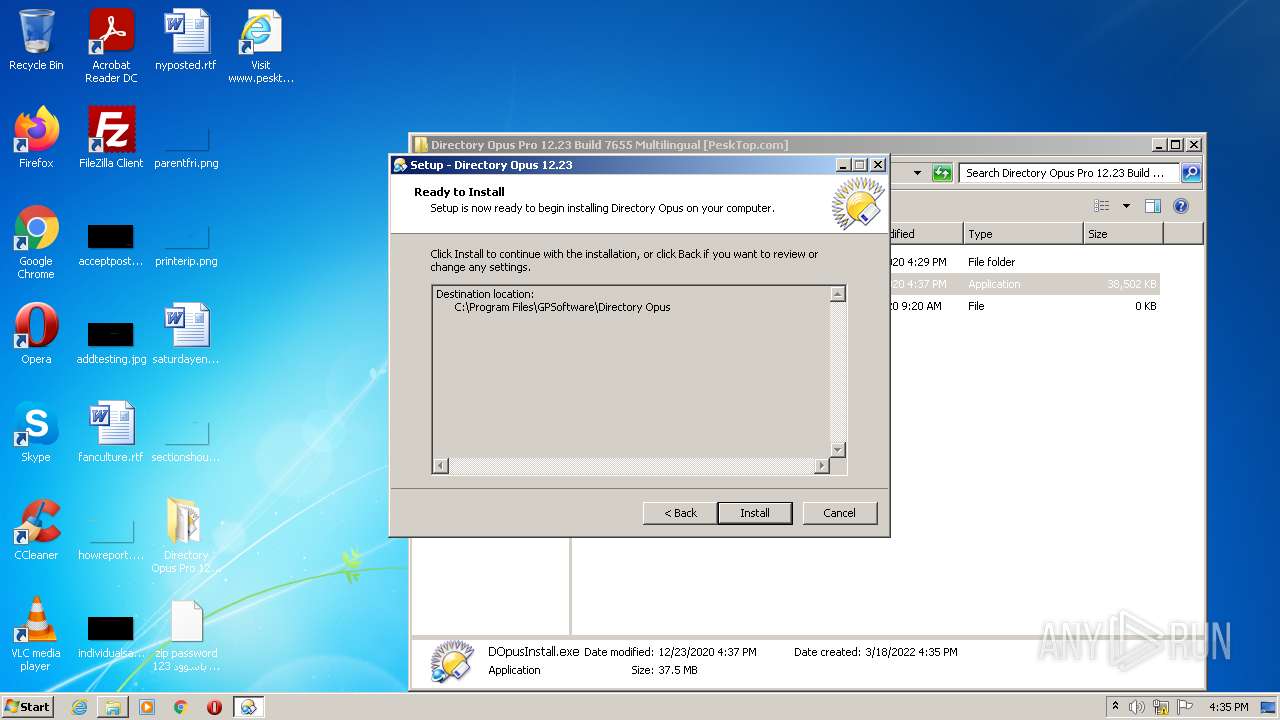
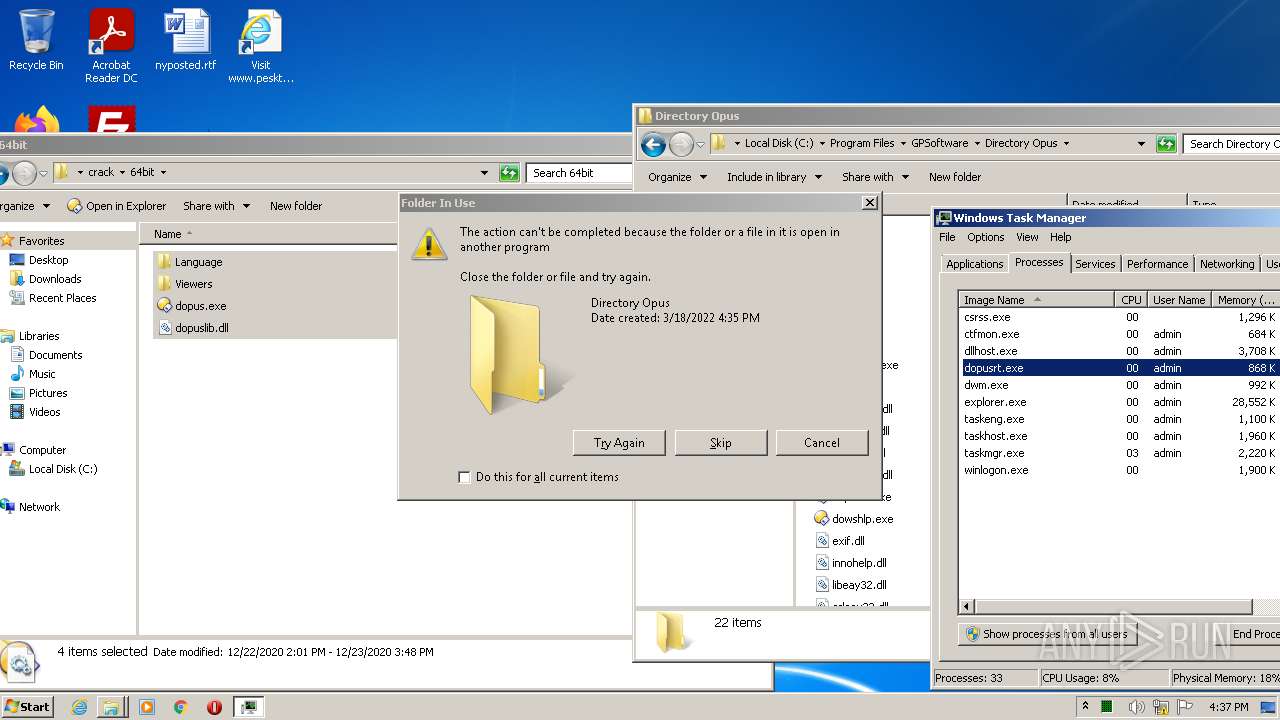
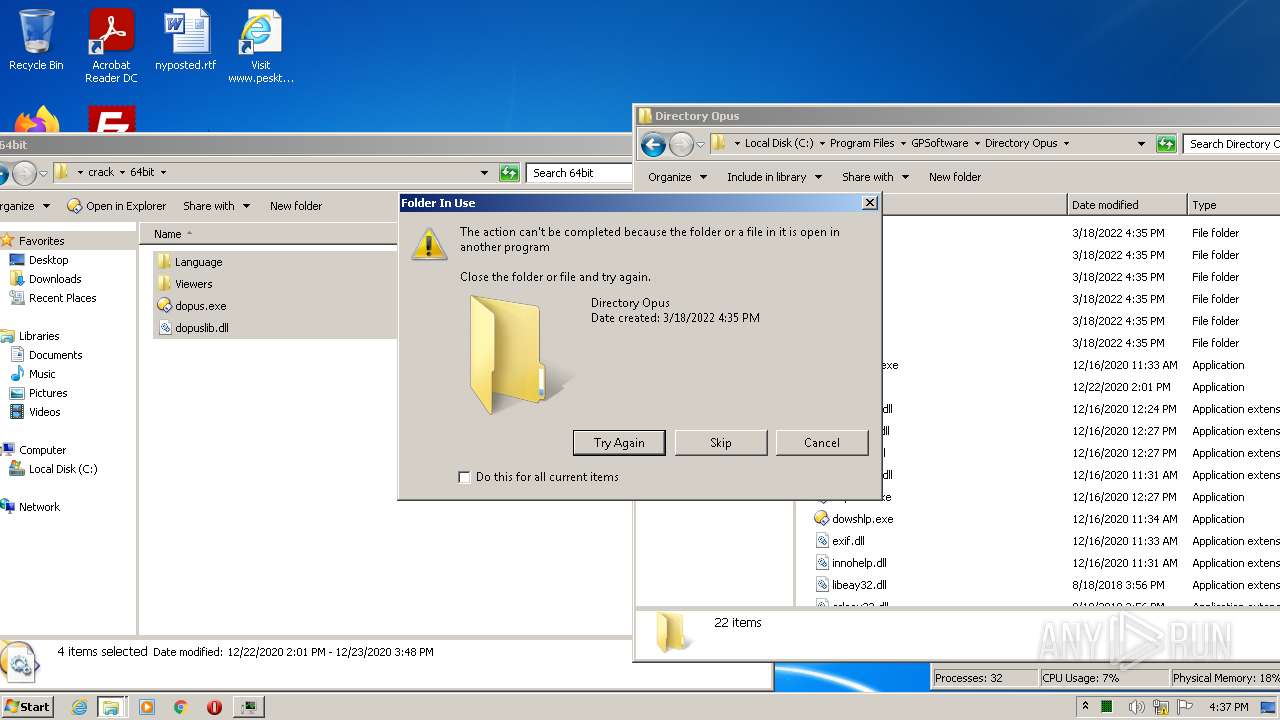
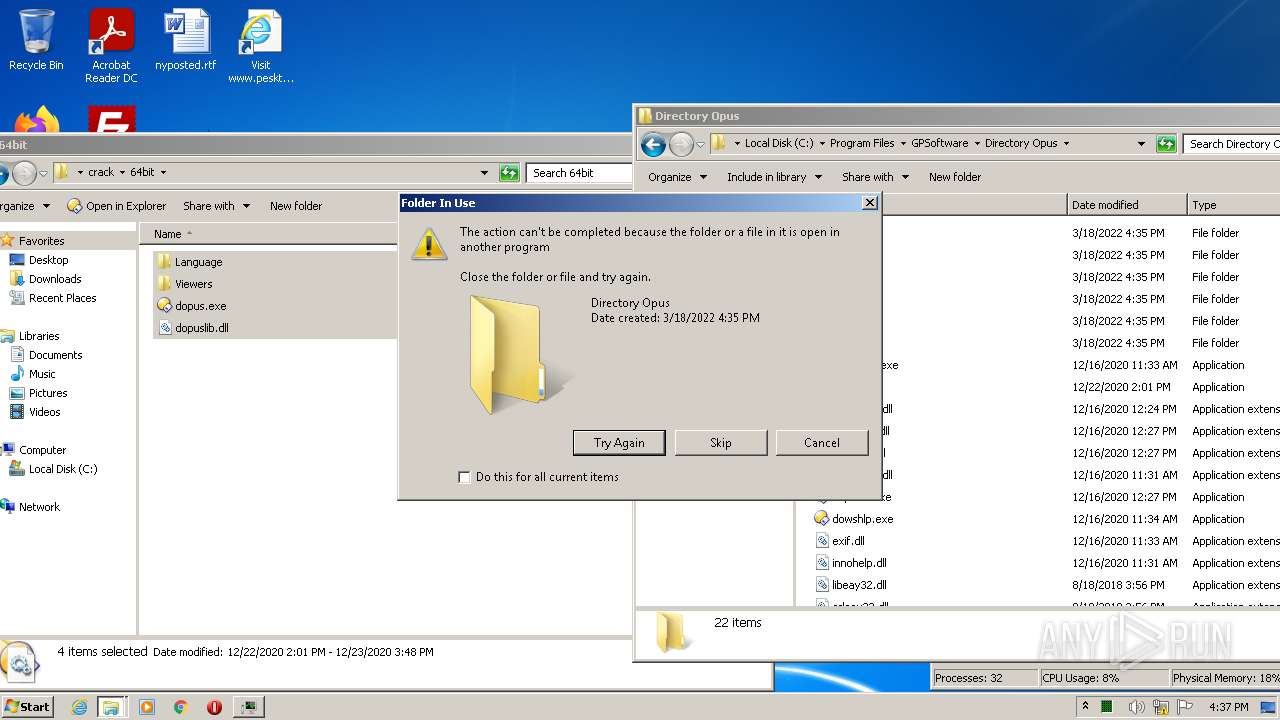
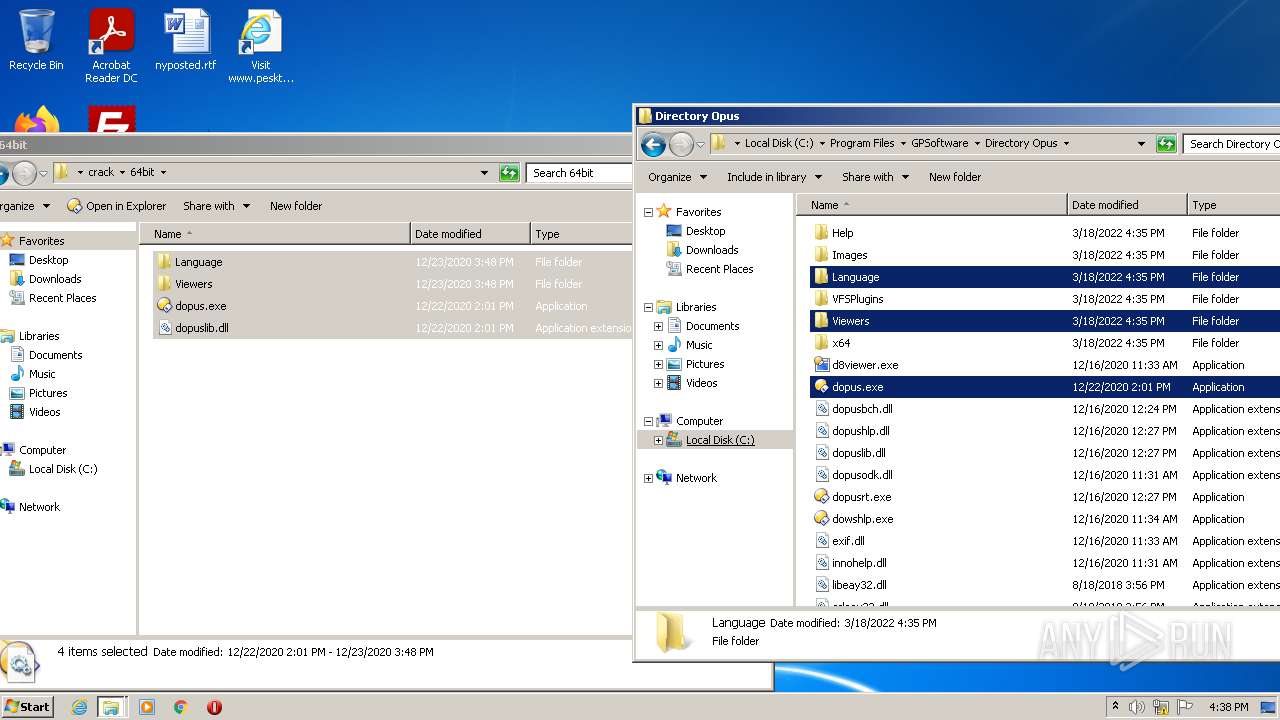
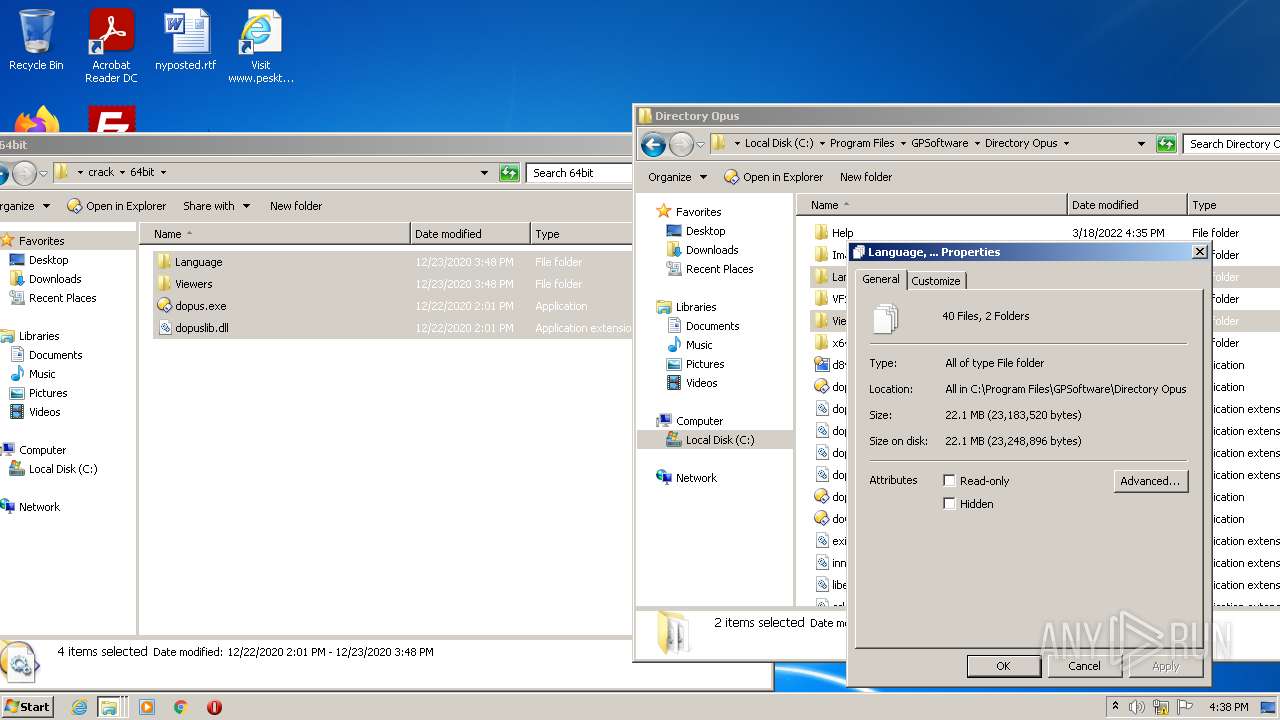
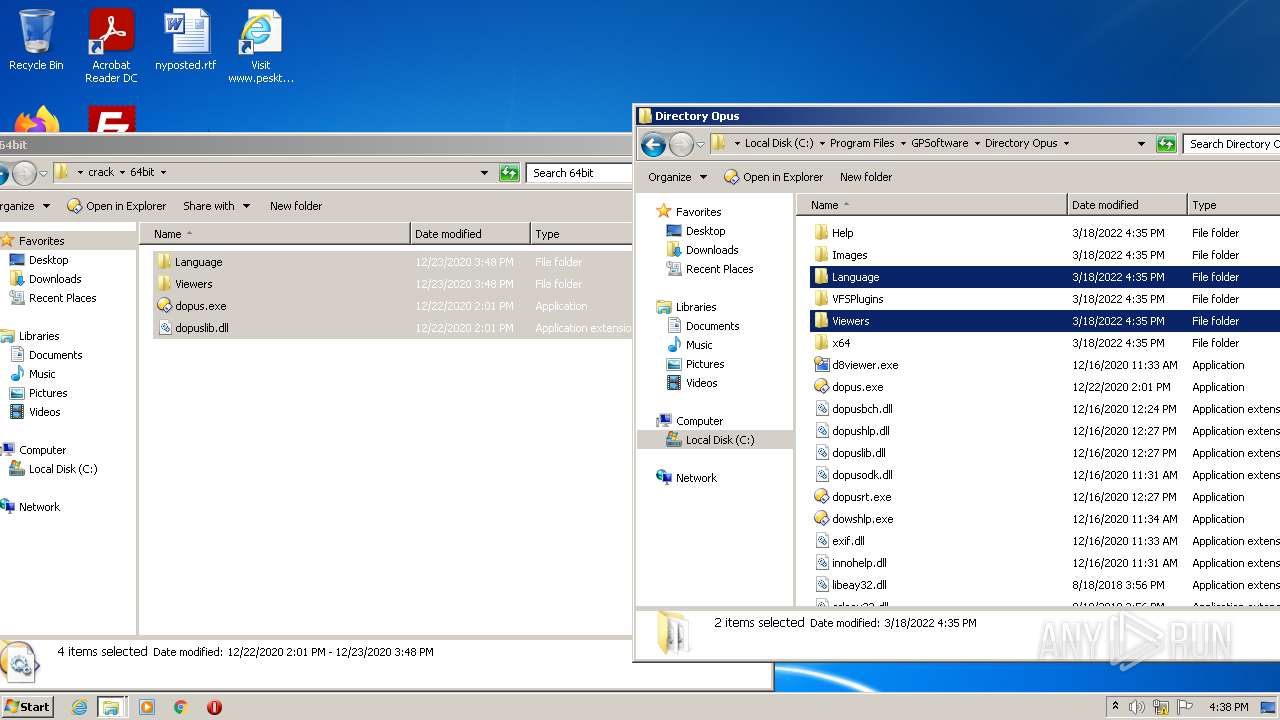
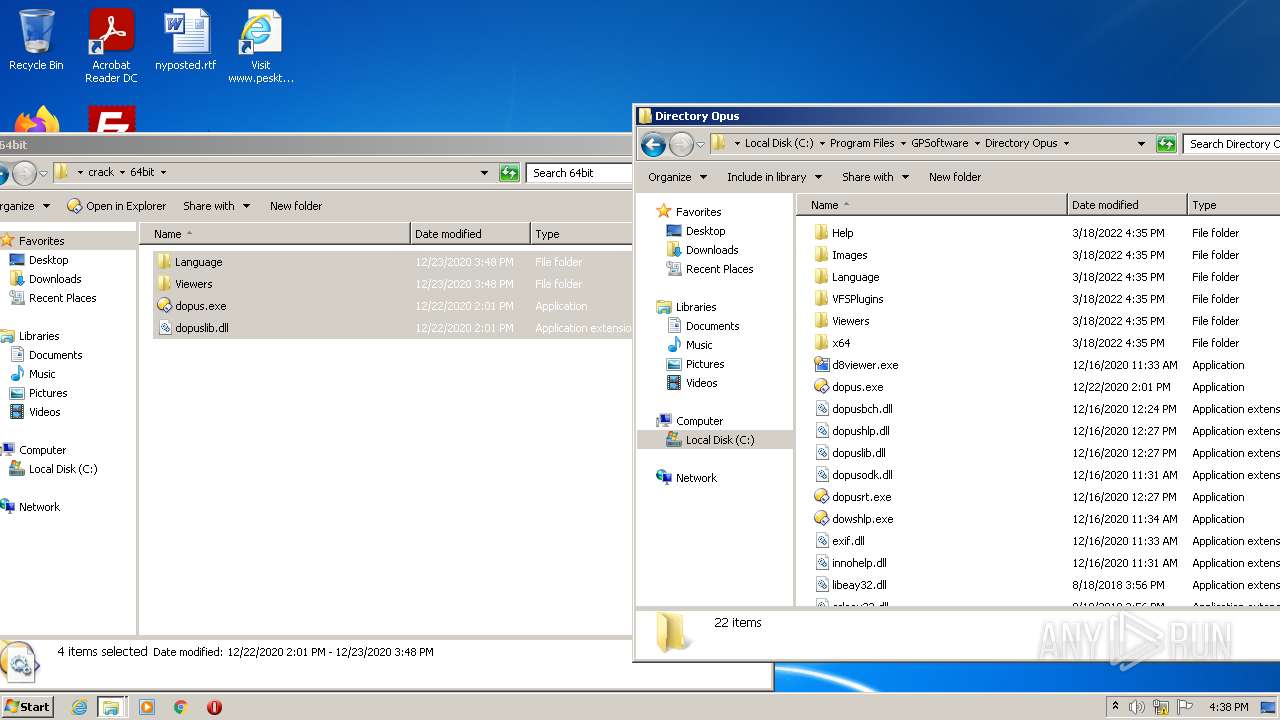
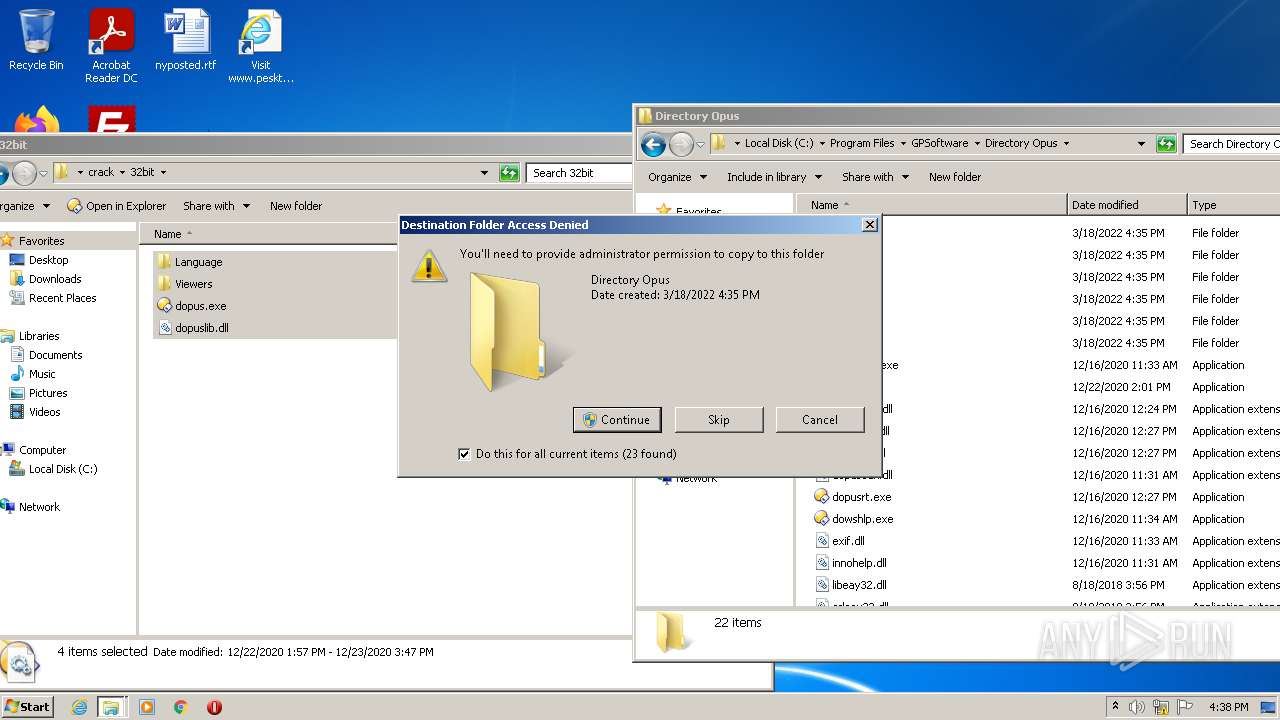
Creates a directory in Program Files
- DOpusInstall.tmp (PID: 2016)
Drops a file with too old compile date
- DOpusInstall.tmp (PID: 2016)
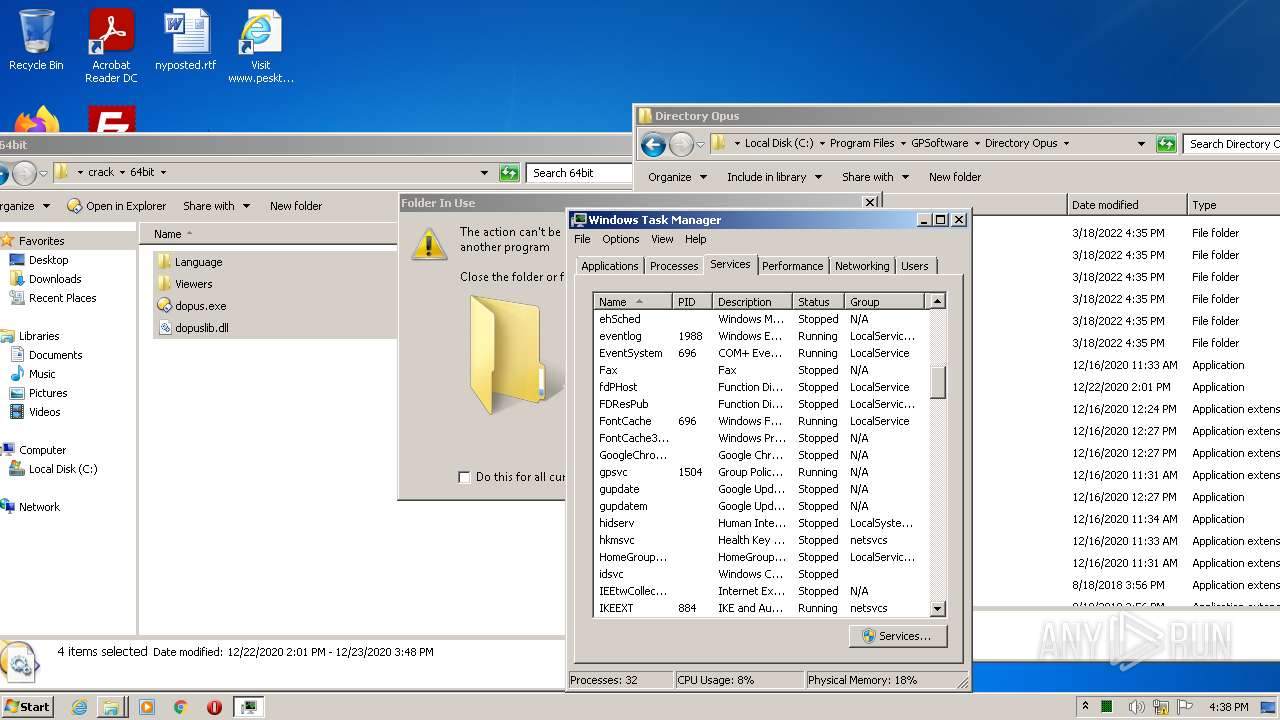
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2380)
- regsvr32.exe (PID: 3484)
- dopus.exe (PID: 908)
Changes default file association
- regsvr32.exe (PID: 3484)
- dopus.exe (PID: 908)
- dopus.exe (PID: 1560)
Creates files in the program directory
- dopus.exe (PID: 908)
Application launched itself
- Explorer.EXE (PID: 584)
Reads default file associations for system extensions
- dopus.exe (PID: 908)
- dopus.exe (PID: 1560)
- Explorer.EXE (PID: 584)
Reads mouse settings
- dopus.exe (PID: 908)
- dopus.exe (PID: 1560)
Executed via COM
- DllHost.exe (PID: 4028)
- DllHost.exe (PID: 3248)
INFO
Checks supported languages
- firefox.exe (PID: 3036)
- firefox.exe (PID: 3880)
- firefox.exe (PID: 2936)
- firefox.exe (PID: 856)
- firefox.exe (PID: 2592)
- firefox.exe (PID: 1036)
- firefox.exe (PID: 2964)
- firefox.exe (PID: 2068)
- firefox.exe (PID: 2732)
- regsvr32.exe (PID: 2380)
- regsvr32.exe (PID: 3484)
- Explorer.EXE (PID: 584)
- explorer.exe (PID: 2508)
- consent.exe (PID: 1624)
- DllHost.exe (PID: 4028)
- taskmgr.exe (PID: 2564)
- consent.exe (PID: 2988)
- consent.exe (PID: 3164)
- DllHost.exe (PID: 3248)
Reads the computer name
- firefox.exe (PID: 3036)
- firefox.exe (PID: 3880)
- firefox.exe (PID: 2592)
- firefox.exe (PID: 2964)
- firefox.exe (PID: 1036)
- firefox.exe (PID: 2068)
- firefox.exe (PID: 856)
- firefox.exe (PID: 2732)
- explorer.exe (PID: 2508)
- consent.exe (PID: 1624)
- DllHost.exe (PID: 4028)
- taskmgr.exe (PID: 2564)
- consent.exe (PID: 2988)
- consent.exe (PID: 3164)
- DllHost.exe (PID: 3248)
Creates files in the program directory
- firefox.exe (PID: 3036)
- DOpusInstall.tmp (PID: 2016)
- SetAppUserModelId-Win32.exe (PID: 2064)
Reads CPU info
- firefox.exe (PID: 3036)
Application launched itself
- firefox.exe (PID: 2936)
- firefox.exe (PID: 3036)
Reads the date of Windows installation
- firefox.exe (PID: 3036)
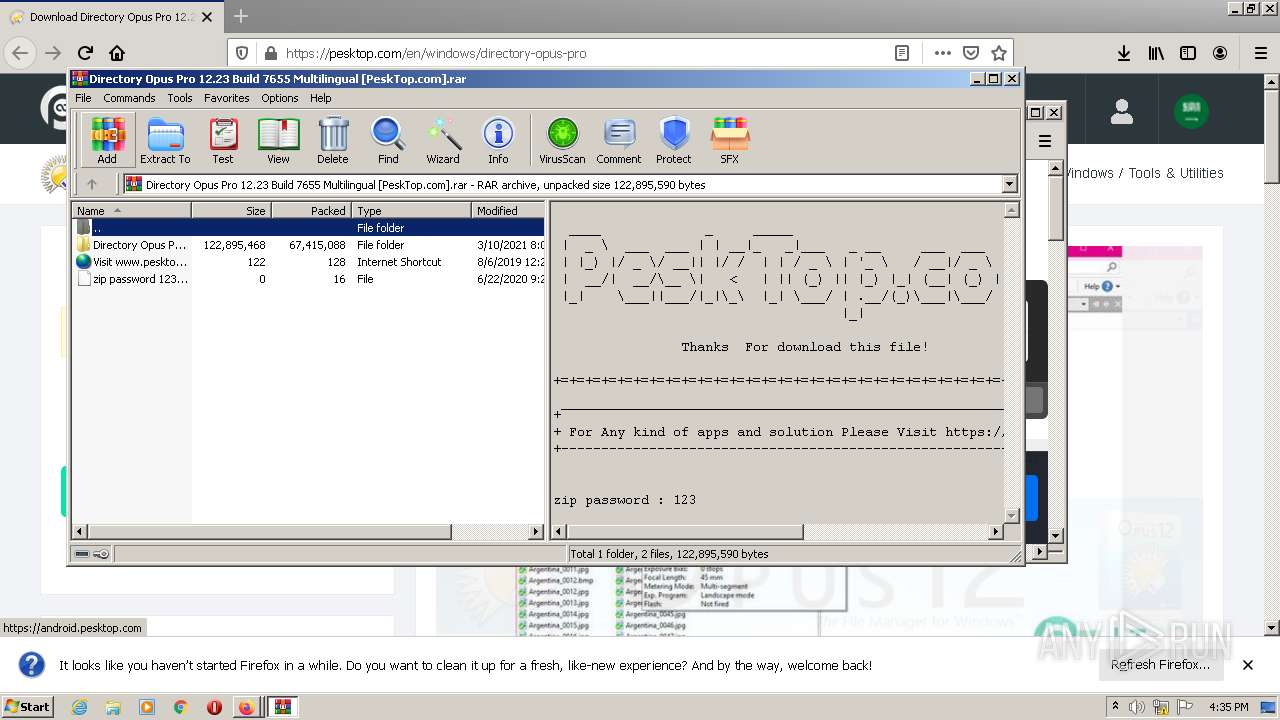
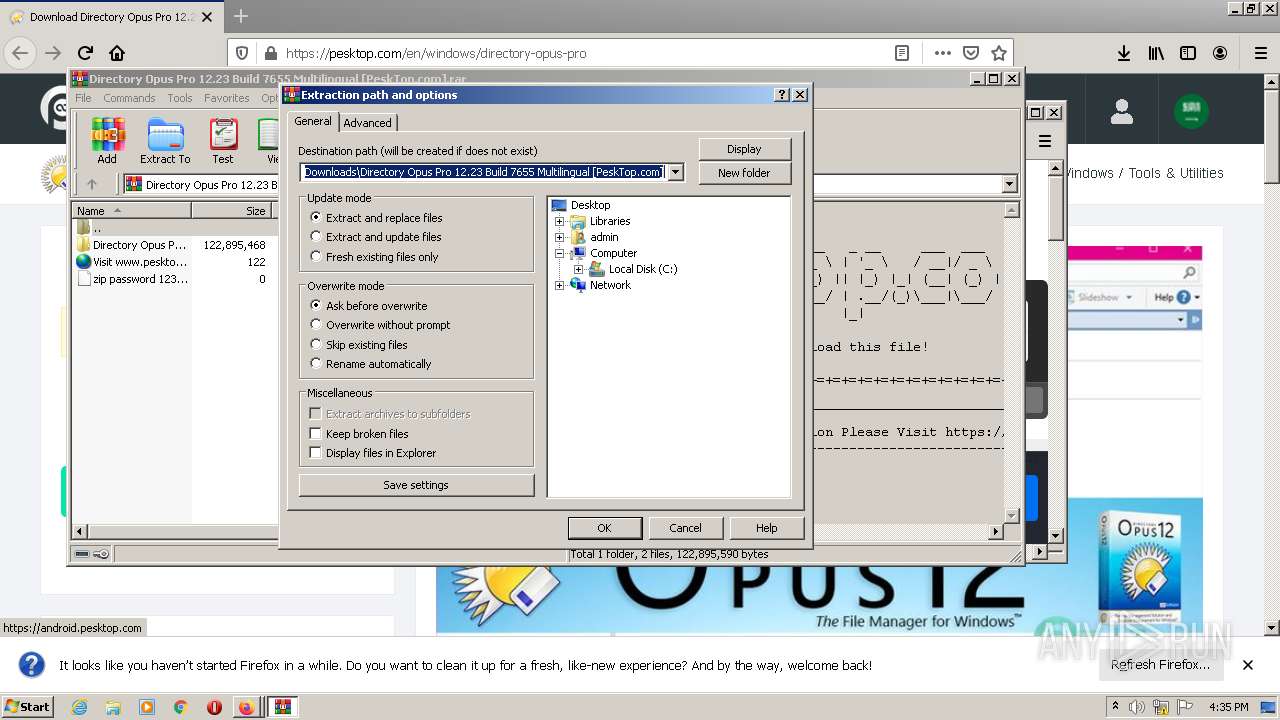
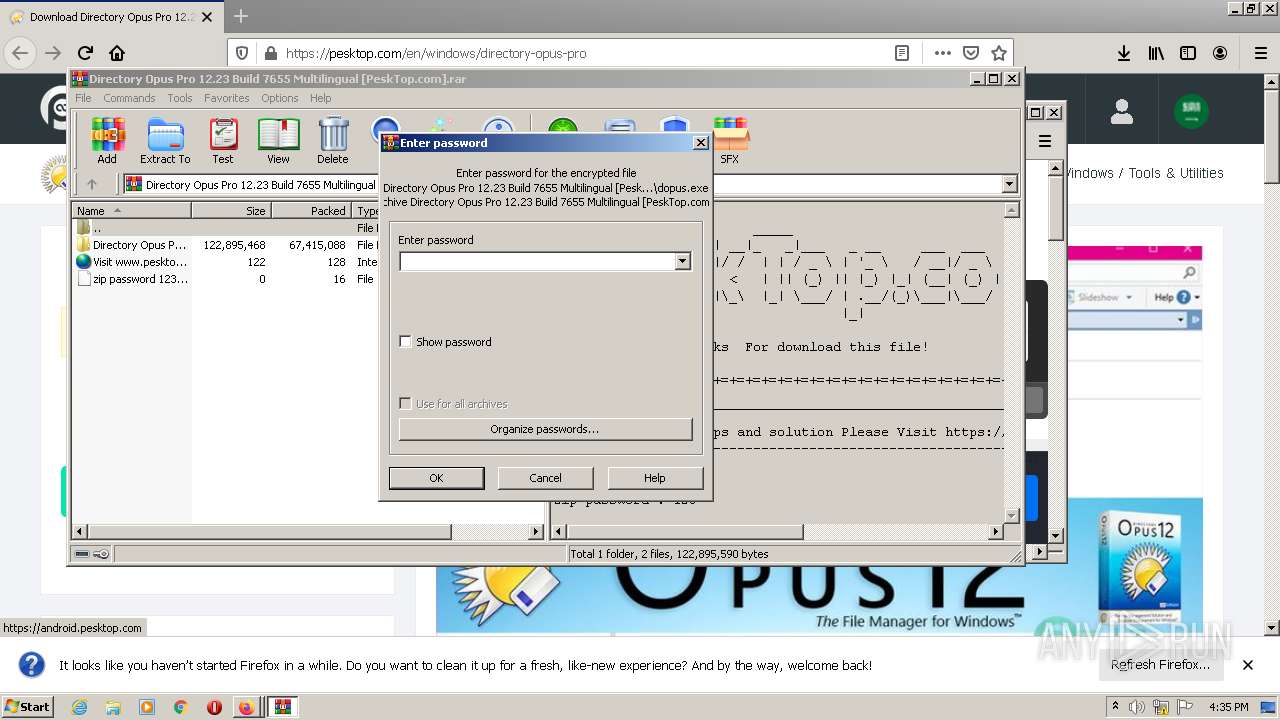
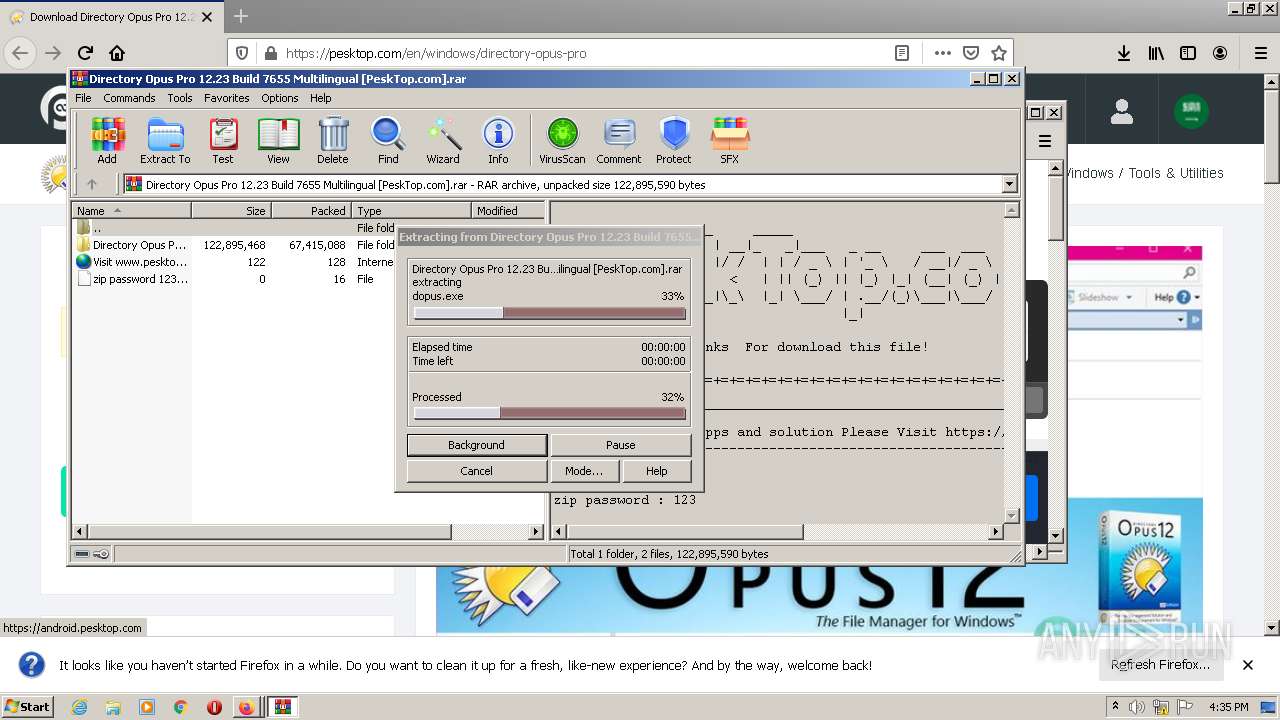
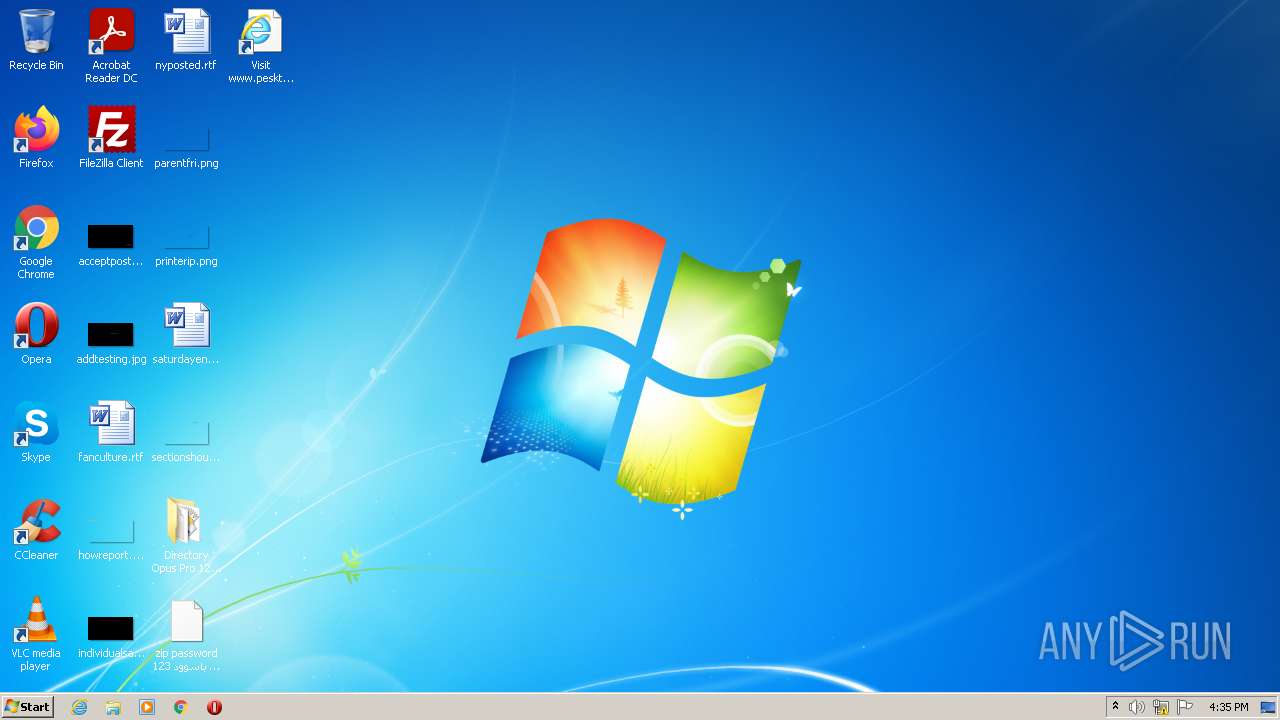
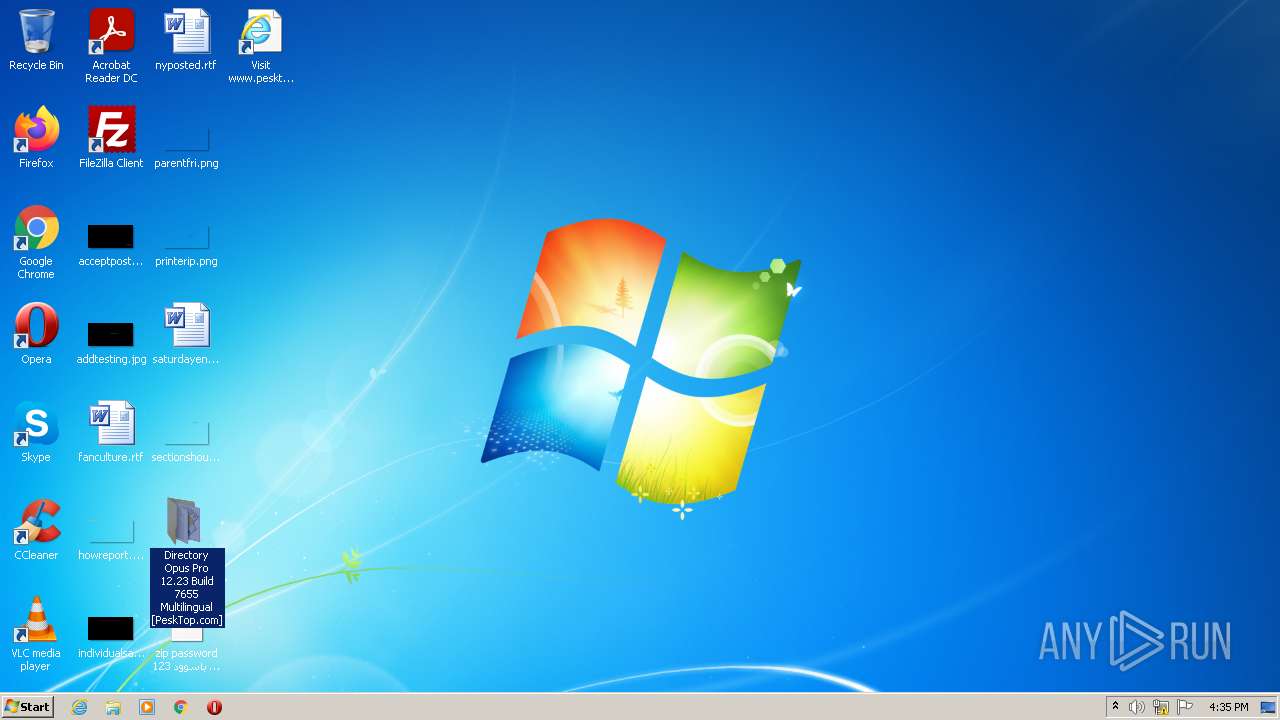
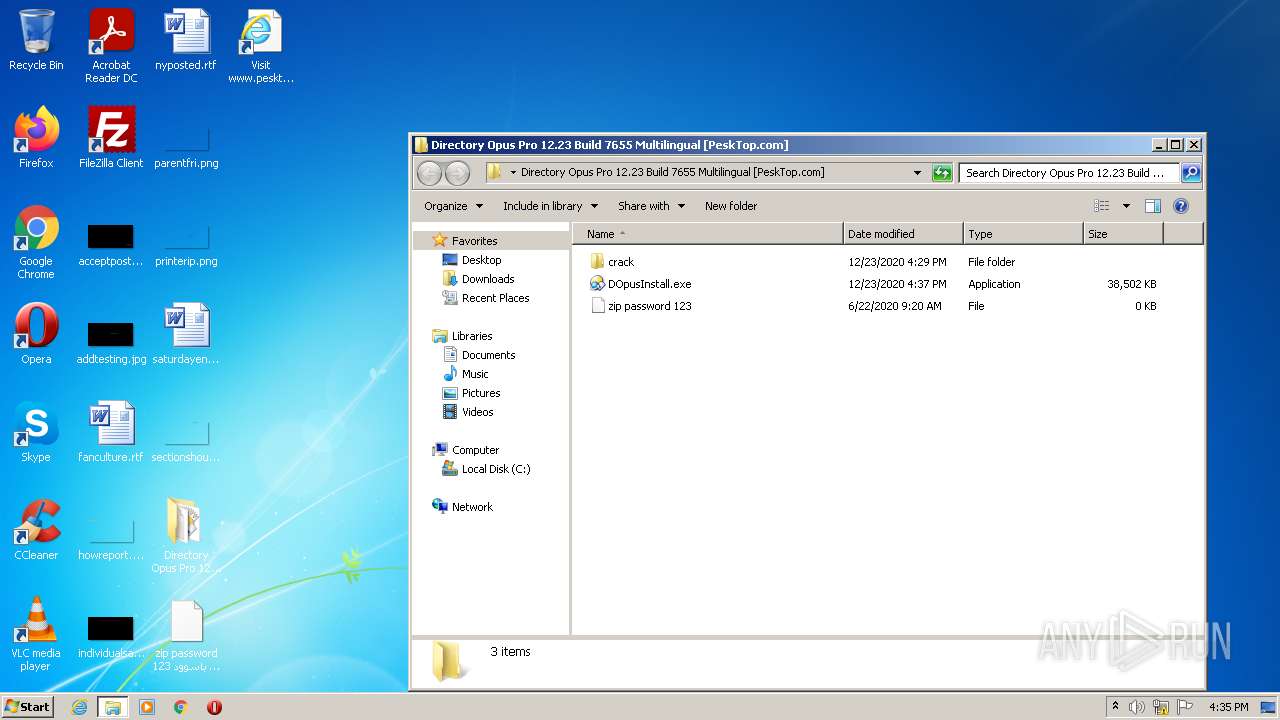
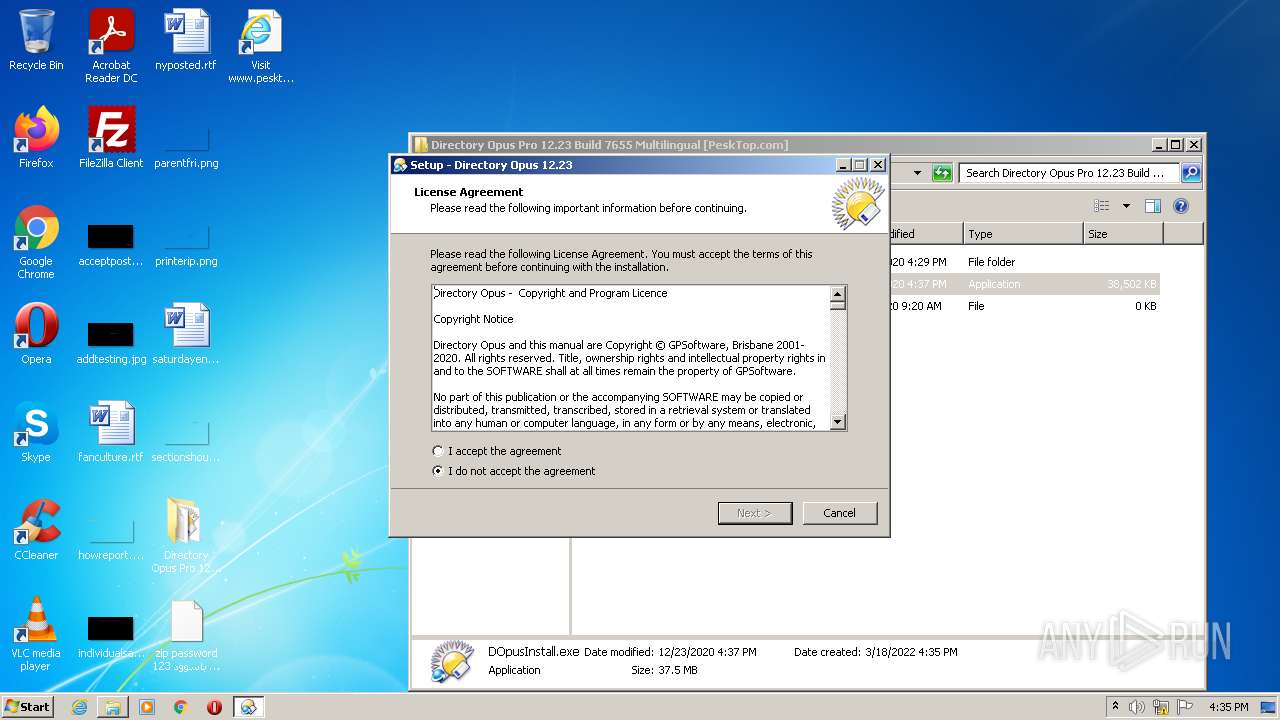
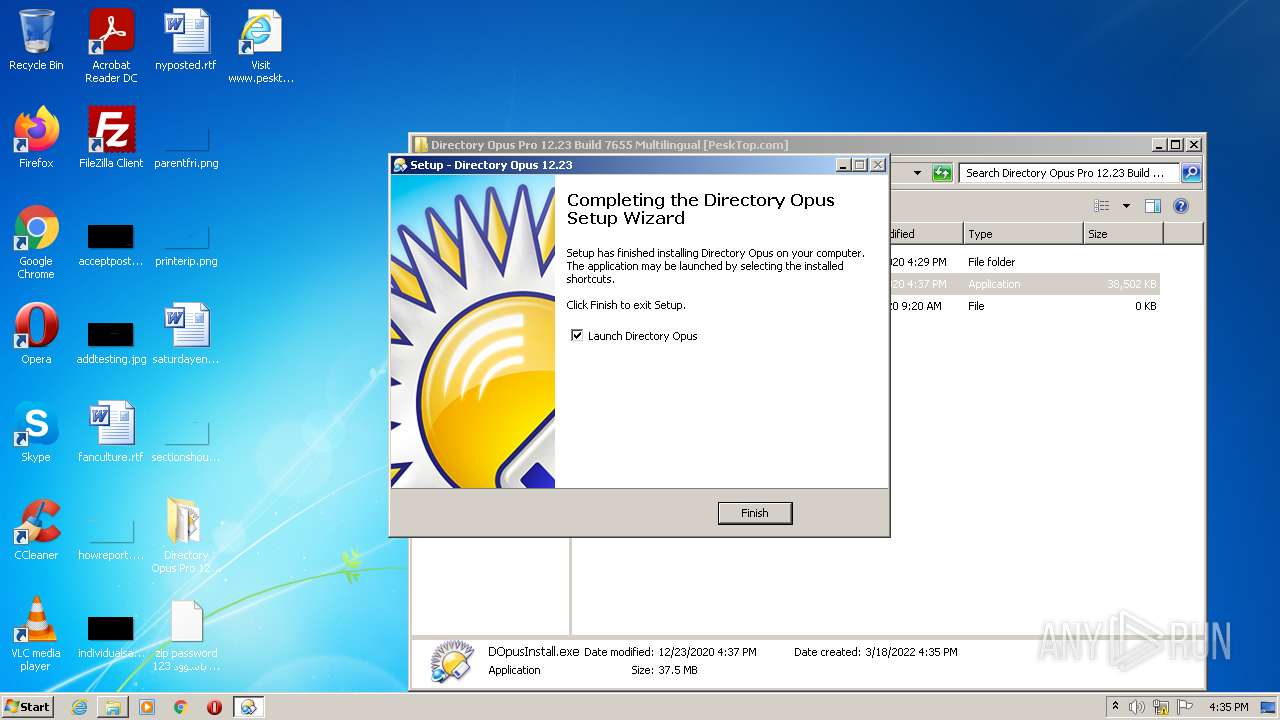
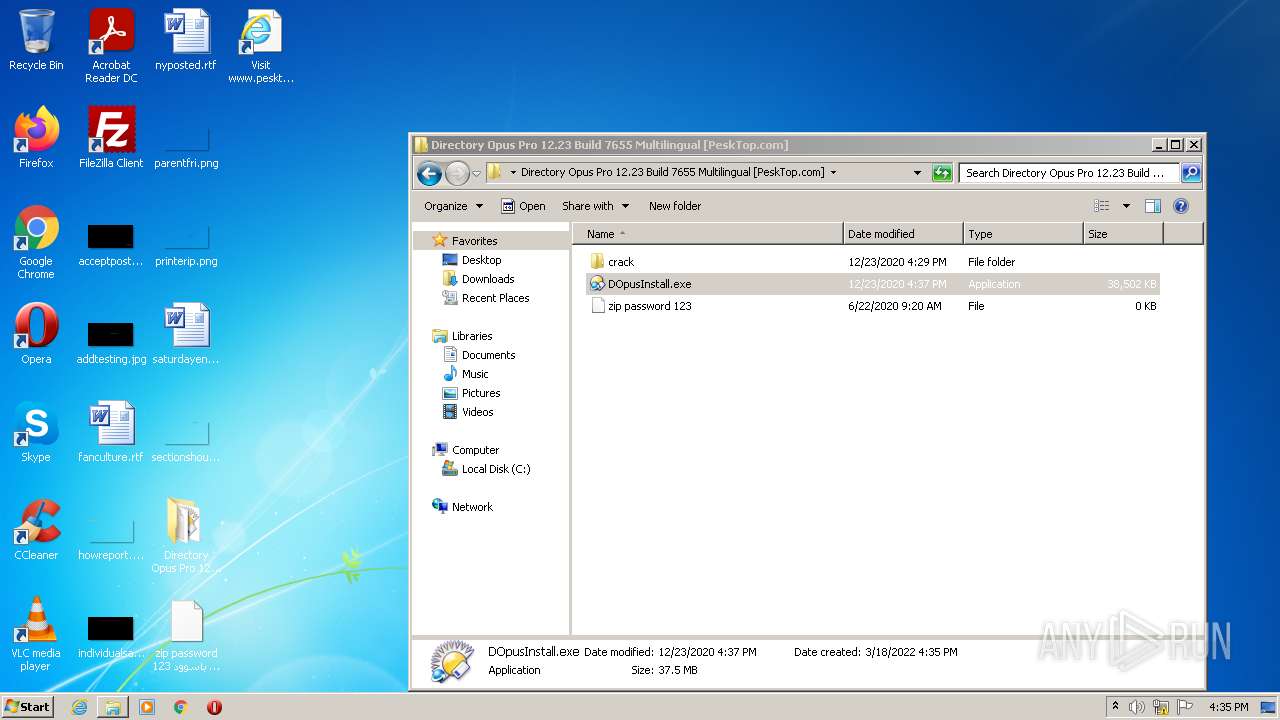
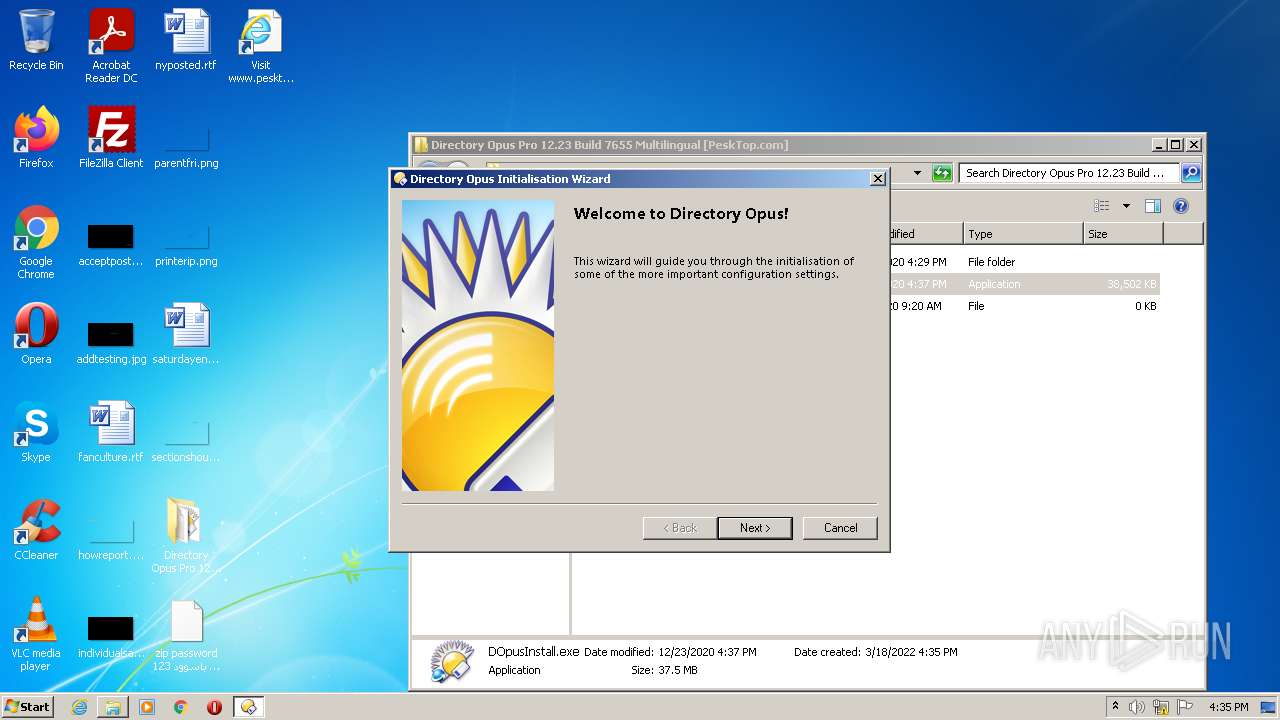
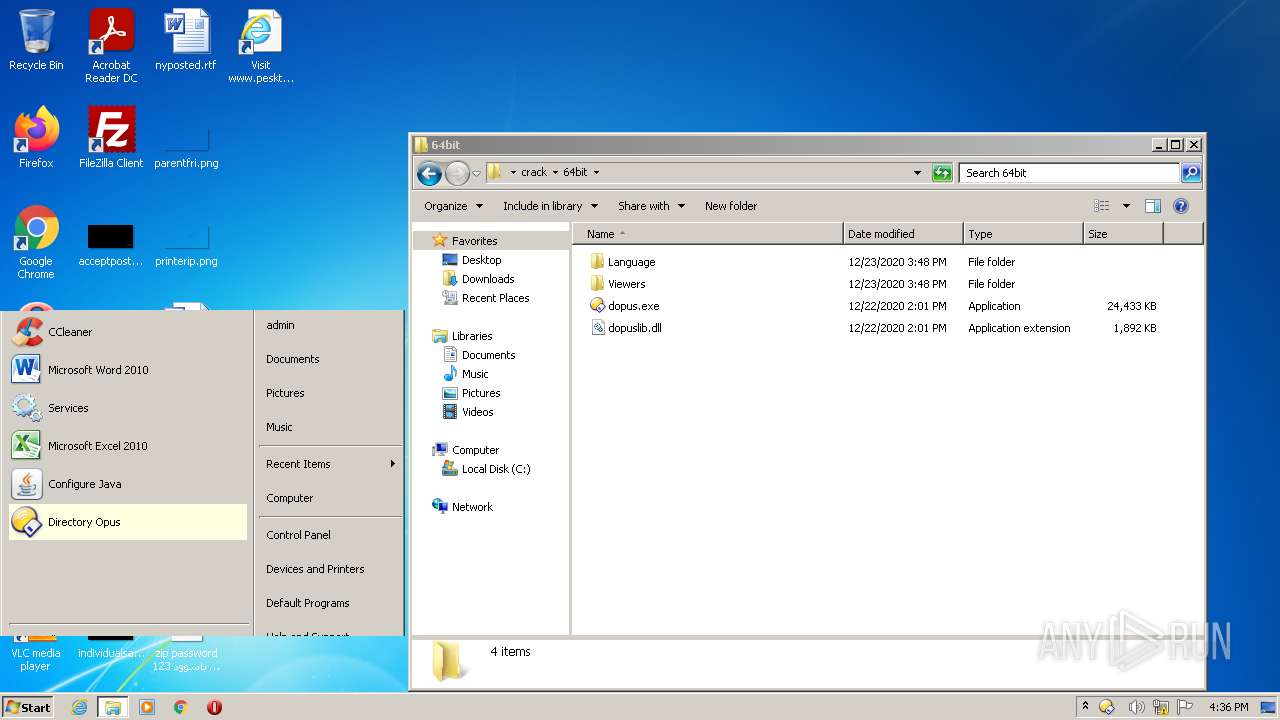
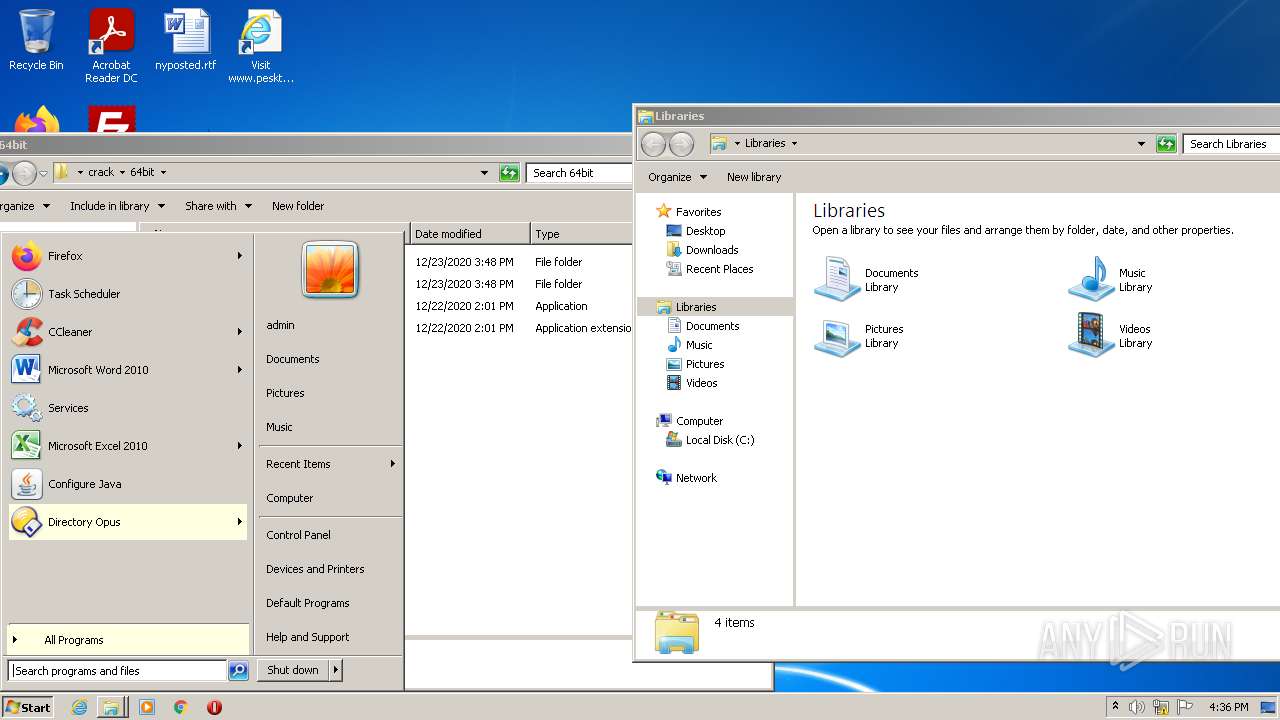
Manual execution by user
- WinRAR.exe (PID: 2356)
- DOpusInstall.exe (PID: 3596)
Checks Windows Trust Settings
- firefox.exe (PID: 3036)
- Explorer.EXE (PID: 584)
- consent.exe (PID: 2988)
- consent.exe (PID: 3164)
- consent.exe (PID: 1624)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2356)
- DOpusInstall.tmp (PID: 2016)
Creates files in the user directory
- firefox.exe (PID: 3036)
Application was dropped or rewritten from another process
- DOpusInstall.tmp (PID: 3192)
- DOpusInstall.tmp (PID: 2016)
- SetAppUserModelId-Win32.exe (PID: 2064)
Loads dropped or rewritten executable
- DOpusInstall.tmp (PID: 2016)
Reads the hosts file
- regsvr32.exe (PID: 2380)
Creates a software uninstall entry
- DOpusInstall.tmp (PID: 2016)
Reads settings of System Certificates
- Explorer.EXE (PID: 584)
- consent.exe (PID: 2988)
- consent.exe (PID: 1624)
- consent.exe (PID: 3164)
Reads Microsoft Office registry keys
- Explorer.EXE (PID: 584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
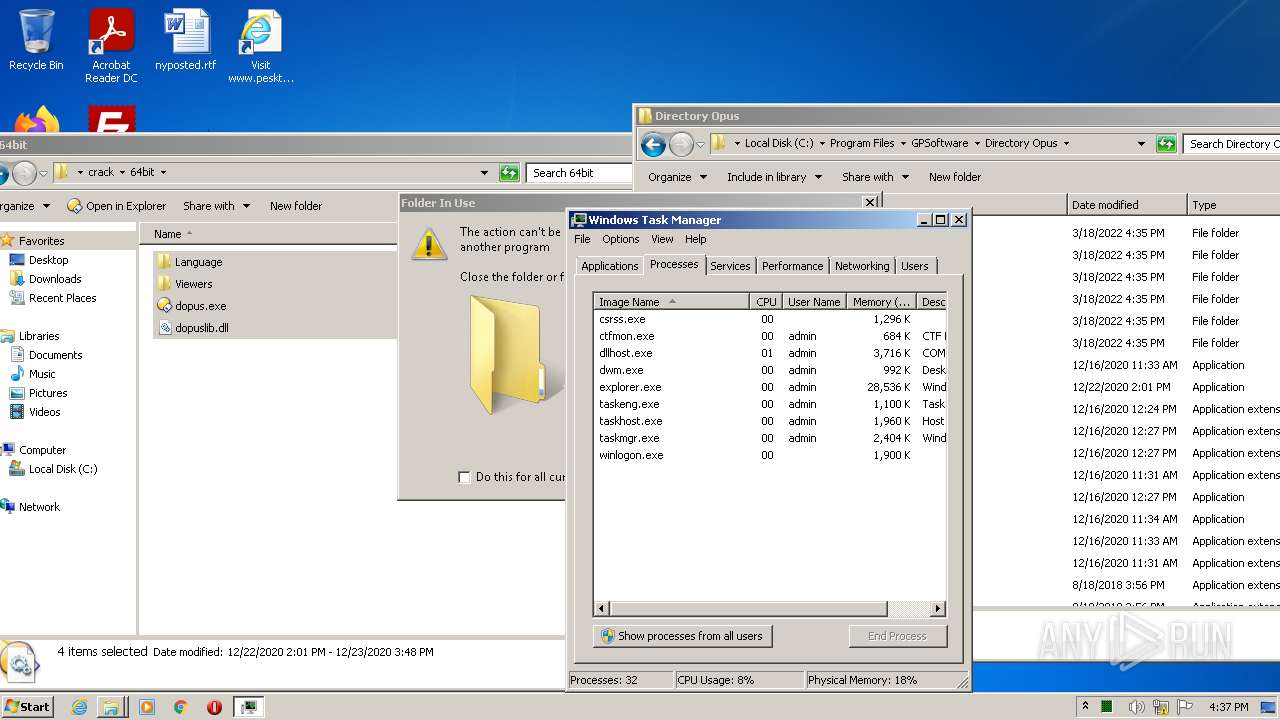
Total processes
82
Monitored processes
34
Malicious processes
17
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3036.13.1171930726\1774596652" -childID 2 -isForBrowser -prefsHandle 3168 -prefMapHandle 3112 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3036 "\\.\pipe\gecko-crash-server-pipe.3036" 3184 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 884 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
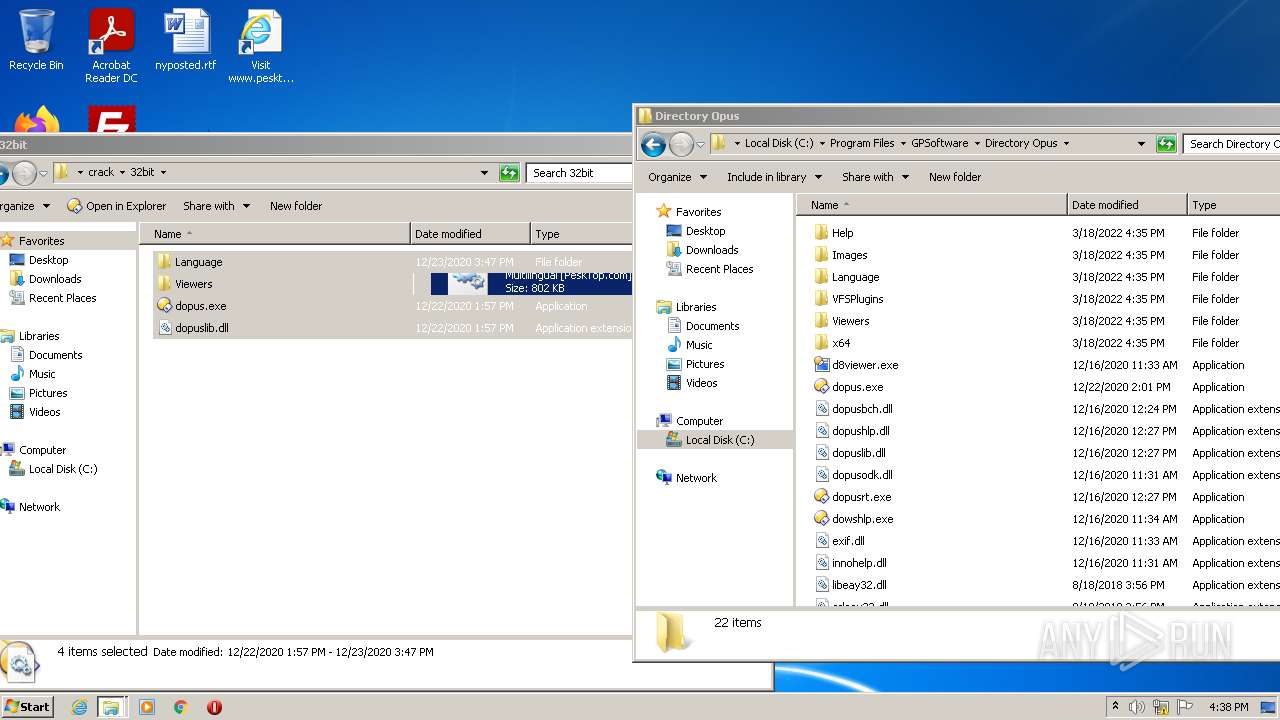
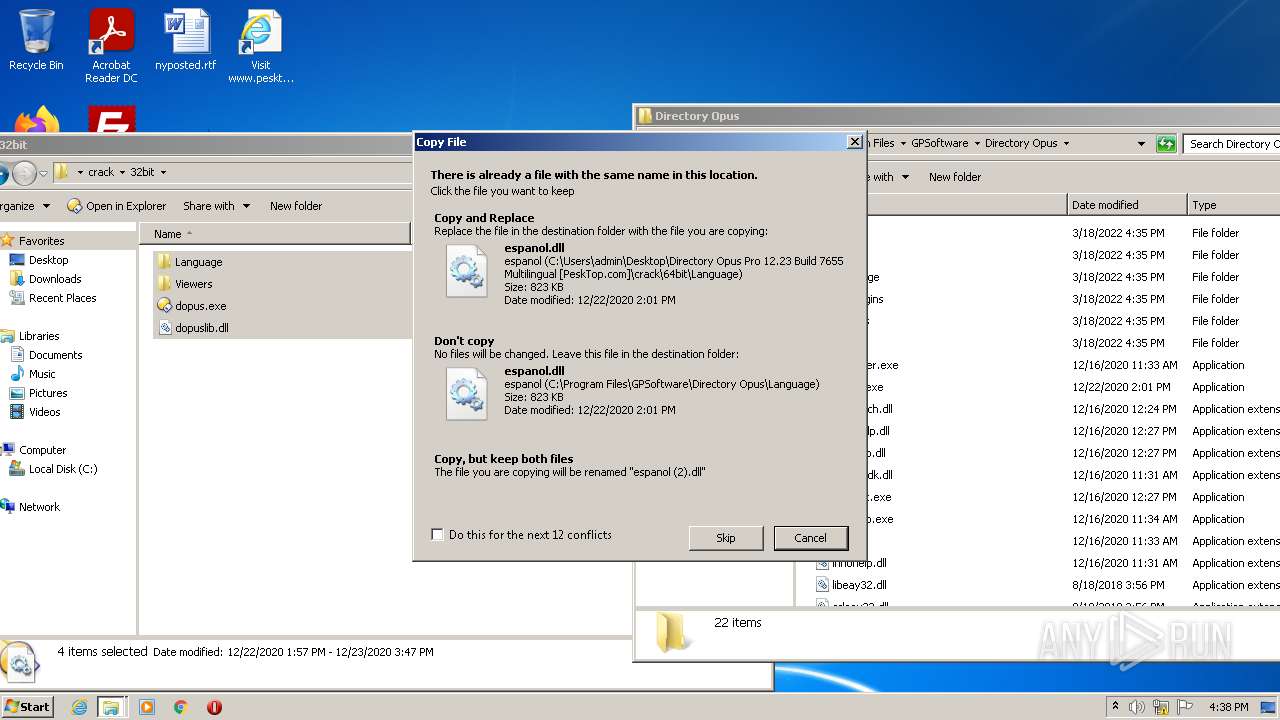
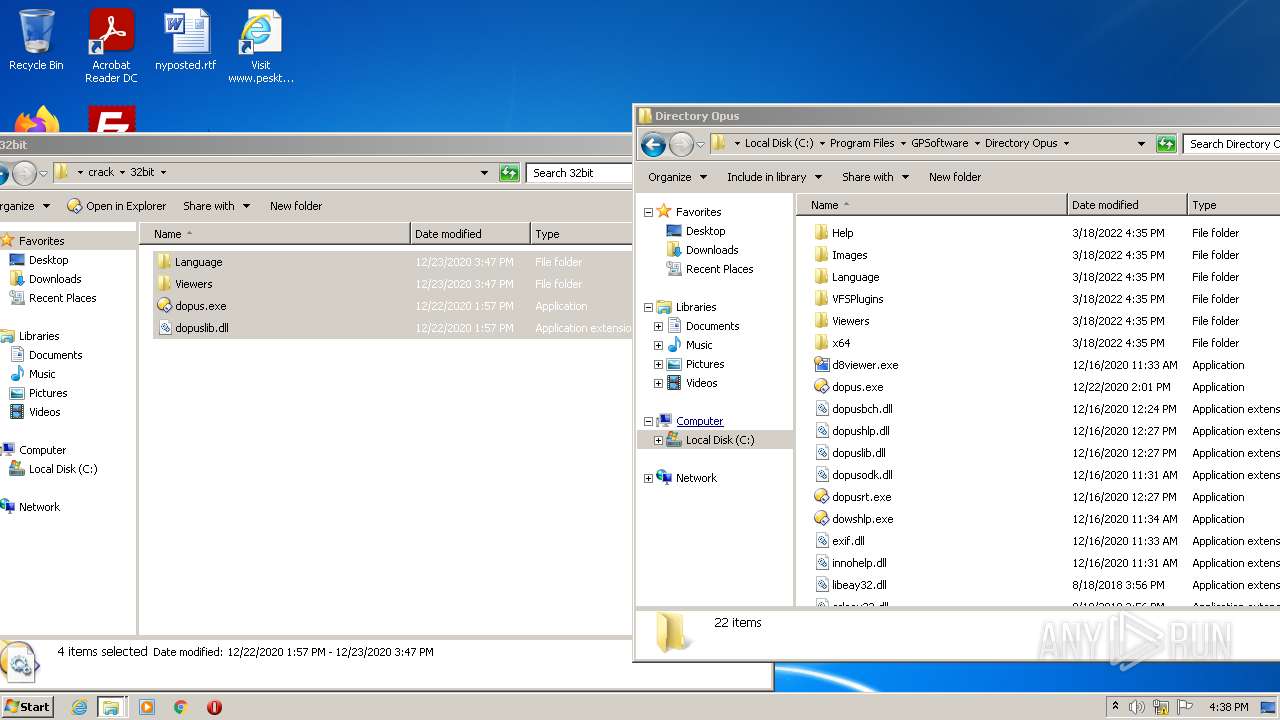
| 896 | "C:\Users\admin\Desktop\Directory Opus Pro 12.23 Build 7655 Multilingual [PeskTop.com]\DOpusInstall.exe" /SPAWNWND=$401B2 /NOTIFYWND=$401C2 | C:\Users\admin\Desktop\Directory Opus Pro 12.23 Build 7655 Multilingual [PeskTop.com]\DOpusInstall.exe | DOpusInstall.tmp | ||||||||||||
User: admin Company: GPSoftware Integrity Level: HIGH Description: Directory Opus Exit code: 0 Version: 12.23 Modules
| |||||||||||||||
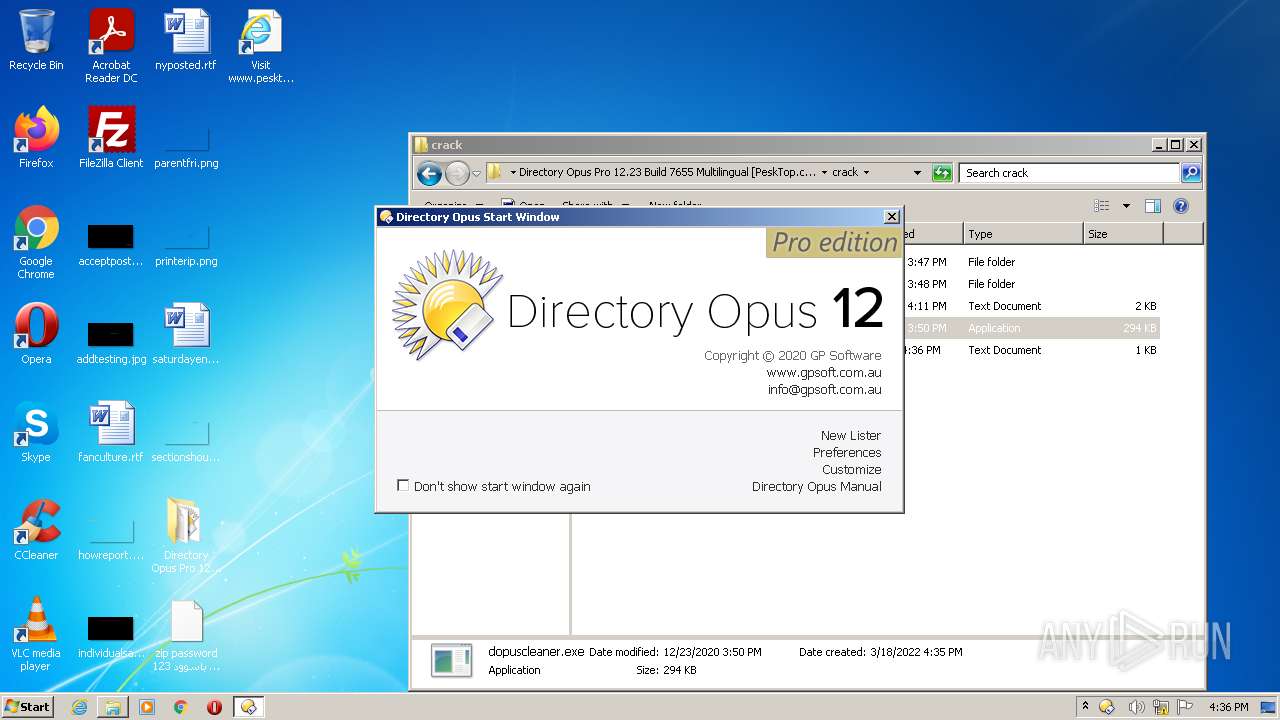
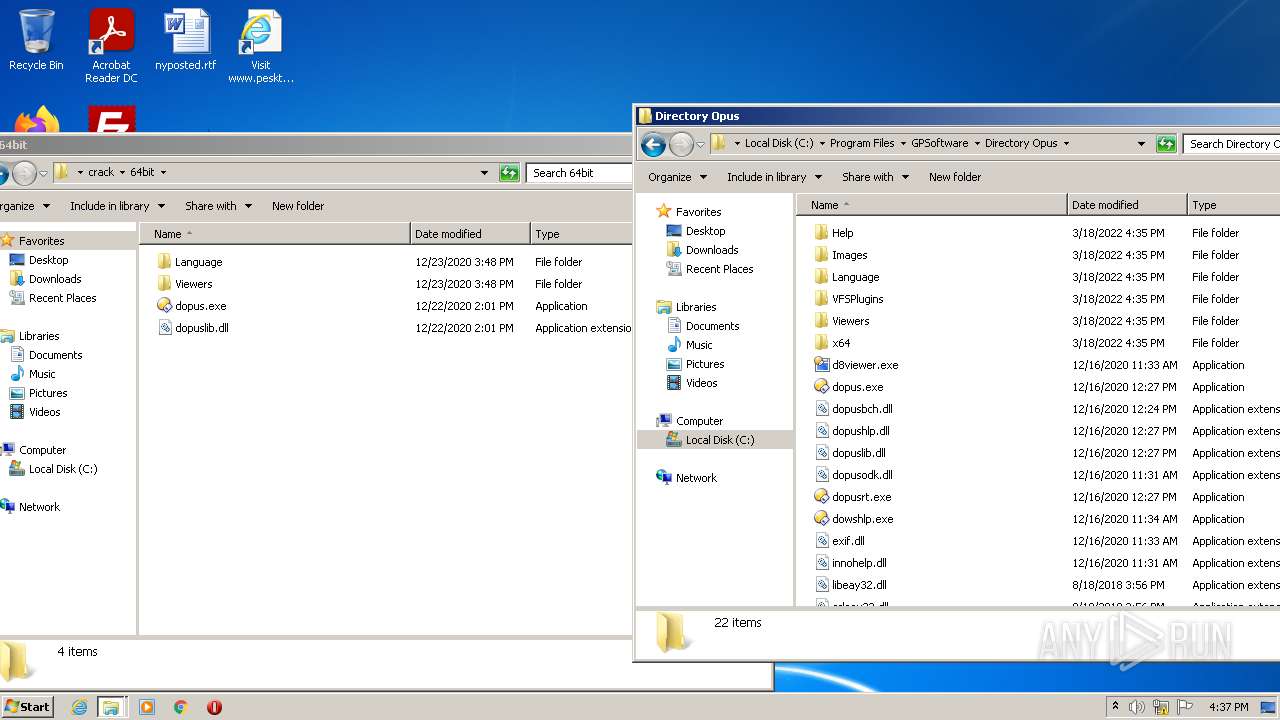
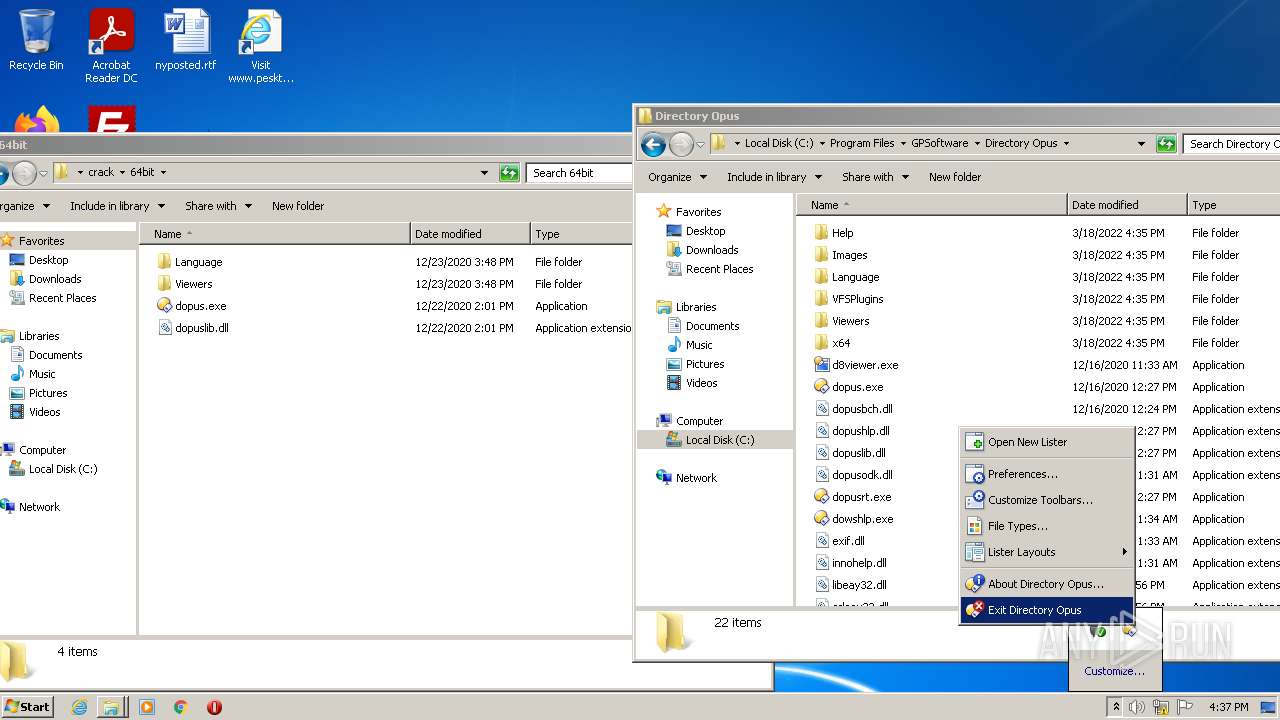
| 908 | "C:\Program Files\GPSoftware\Directory Opus\dopus.exe" /ignoresetup autolister=layout | C:\Program Files\GPSoftware\Directory Opus\dopus.exe | DOpusInstall.tmp | ||||||||||||
User: admin Company: GP Software Integrity Level: MEDIUM Description: Directory Opus Exit code: 1 Version: 12.23.0.0 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3036.21.631339709\1035330547" -childID 4 -isForBrowser -prefsHandle 3824 -prefMapHandle 3820 -prefsLen 7470 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3036 "\\.\pipe\gecko-crash-server-pipe.3036" 3776 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\GPSoftware\Directory Opus\dopusrt.exe" /dblclk | C:\Program Files\GPSoftware\Directory Opus\dopusrt.exe | dopus.exe | ||||||||||||
User: admin Company: GP Software Integrity Level: MEDIUM Description: Directory Opus Helper Application Exit code: 1 Version: 12.23.0.0 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\GPSoftware\Directory Opus\dopus.exe" nodef event dopusrt-startup-00118411 | C:\Program Files\GPSoftware\Directory Opus\dopus.exe | dopusrt.exe | ||||||||||||
User: admin Company: GP Software Integrity Level: MEDIUM Description: Directory Opus Exit code: 1 Version: 12.23.0.0 Modules
| |||||||||||||||
| 1624 | consent.exe 884 220 0038ED20 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2016 | "C:\Users\admin\AppData\Local\Temp\is-JC0GQ.tmp\DOpusInstall.tmp" /SL5="$40146,38550052,803328,C:\Users\admin\Desktop\Directory Opus Pro 12.23 Build 7655 Multilingual [PeskTop.com]\DOpusInstall.exe" /SPAWNWND=$401B2 /NOTIFYWND=$401C2 | C:\Users\admin\AppData\Local\Temp\is-JC0GQ.tmp\DOpusInstall.tmp | DOpusInstall.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
61 380
Read events
59 848
Write events
1 461
Delete events
71
Modification events
| (PID) Process: | (2936) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: A1F52DA357000000 | |||
| (PID) Process: | (3036) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 5C002EA357000000 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 000000001A000000250000003CFC1C00000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFF0EAC7FE9B2FD70100000000 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000470100007C020000FF5A17013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01 | |||
| (PID) Process: | (3036) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3036) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3036) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3036) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3036) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (3036) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
Executable files
241
Suspicious files
180
Text files
222
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3036 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\protections.sqlite-journal | binary | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\default\https+++pesktop.com\.metadata-v2-tmp | binary | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage.sqlite-journal | binary | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_cCD0CRvCzfA9aWg | binary | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\default\https+++pesktop.com\.metadata-v2 | binary | |
MD5:— | SHA256:— | |||
| 3036 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:994A33896BB41A278A315D0D796422B6 | SHA256:54EC50A20FFF8CC016710E49437CF6A11D3FE5EE7B28C185E4A9AAFEE2908B63 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
97
DNS requests
152
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3036 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3036 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3036 | firefox.exe | POST | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/ | US | der | 472 b | whitelisted |
3036 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3036 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3036 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3036 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3036 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3036 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3036 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3036 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3036 | firefox.exe | 172.67.185.140:443 | pesktop.com | — | US | suspicious |
3036 | firefox.exe | 54.148.72.145:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3036 | firefox.exe | 18.66.248.55:443 | firefox.settings.services.mozilla.com | Massachusetts Institute of Technology | US | suspicious |
3036 | firefox.exe | 151.101.130.133:443 | www.paypalobjects.com | Fastly | US | malicious |
3036 | firefox.exe | 104.18.31.182:80 | ocsp.sectigo.com | Cloudflare Inc | US | unknown |
3036 | firefox.exe | 35.166.247.165:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3036 | firefox.exe | 172.67.72.27:443 | cdn.pushmaster-cdn.xyz | — | US | suspicious |
3036 | firefox.exe | 172.217.16.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3036 | firefox.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
pesktop.com |
| suspicious |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
analytics.wifi4games.com |
| unknown |
www.paypalobjects.com |
| whitelisted |
resources.infolinks.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3036 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3036 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3036 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3036 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |