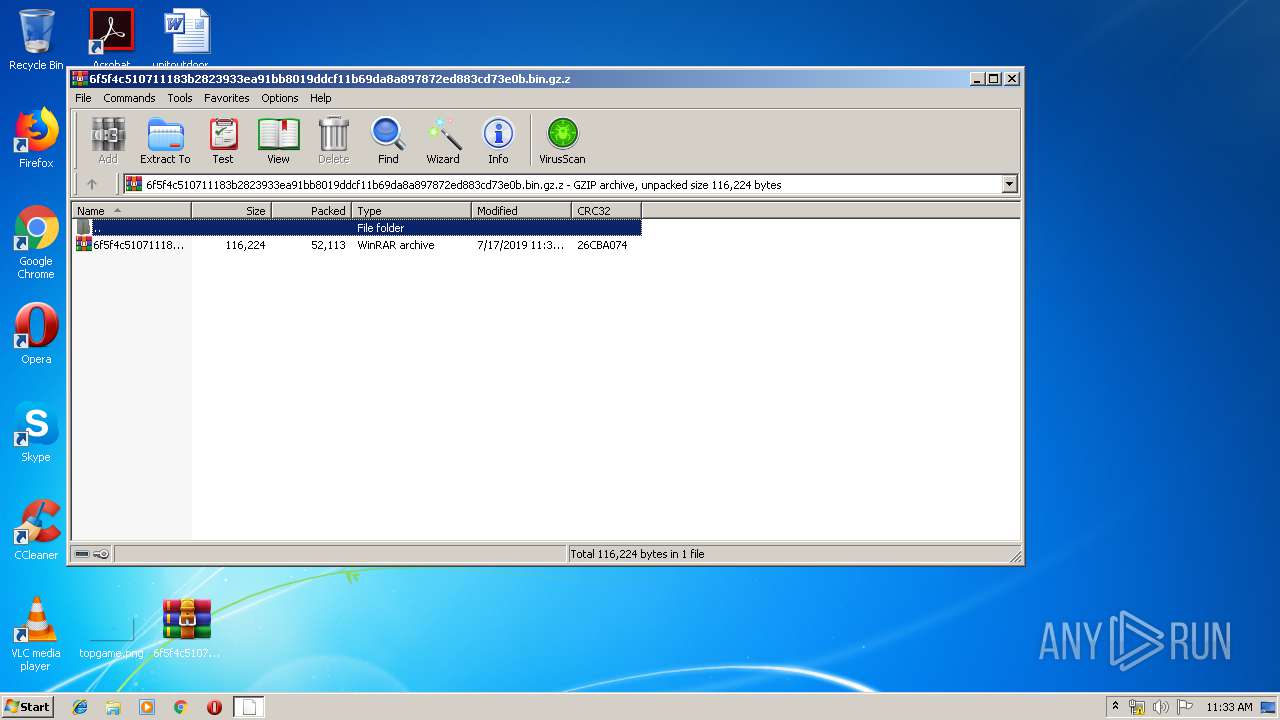
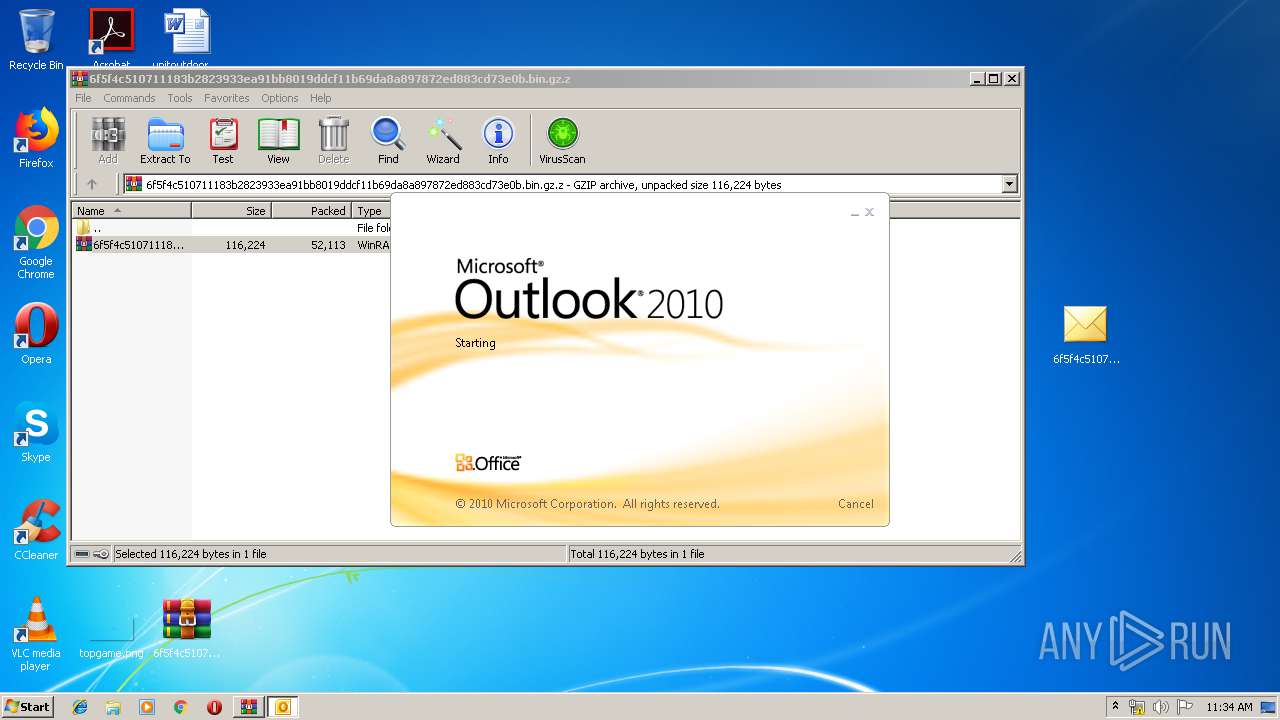
| File name: | 6f5f4c510711183b2823933ea91bb8019ddcf11b69da8a897872ed883cd73e0b.bin.gz |
| Full analysis: | https://app.any.run/tasks/d1ba0cda-1c91-442d-8f6b-e62a7321eb40 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 10:33:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/gzip |
| File info: | gzip compressed data, max compression, from Unix |
| MD5: | D1FF788E4A6166E2E4F5F5096ED2BE78 |
| SHA1: | 530C2E193316A268C8E809205AD98D1B0E7BAB54 |
| SHA256: | A2EDDF8C25583BBF7E99D0FCC4CC2E34219FCA9BE0FE54F56215B520AD0A6F00 |
| SSDEEP: | 768:SIQ2/qjoYi1ChQA9SsdvRVeEM9NFwzvP+UdKoiZ7b7cT5wYuc/IjHP3Mlaqq9KIO:SXjYCuA9SkvGtGv/KNZ7bPxdDP39Q9 |
MALICIOUS
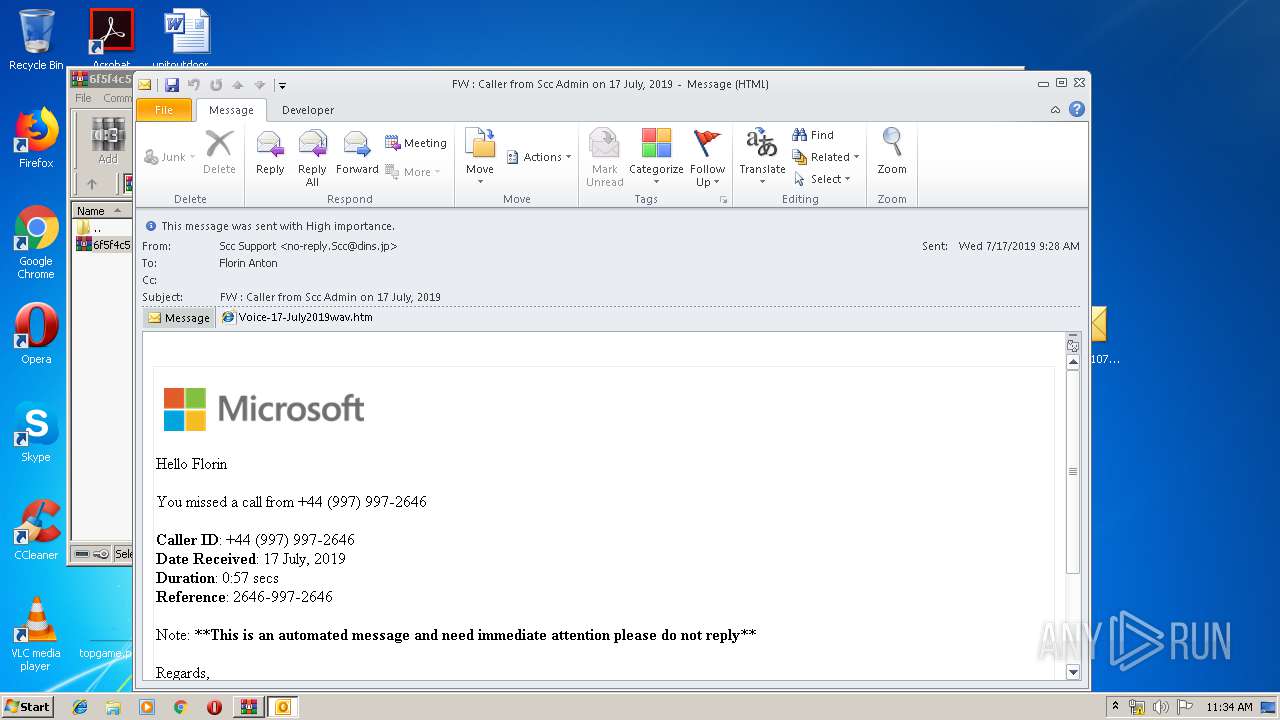
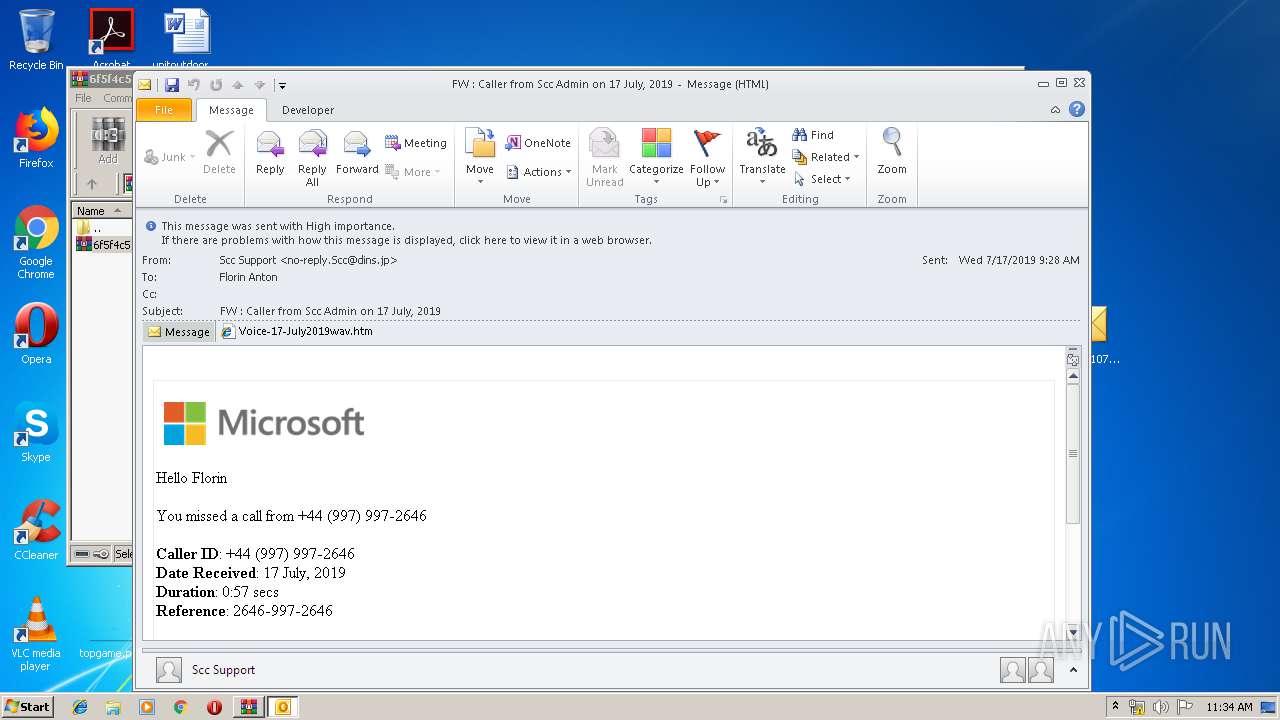
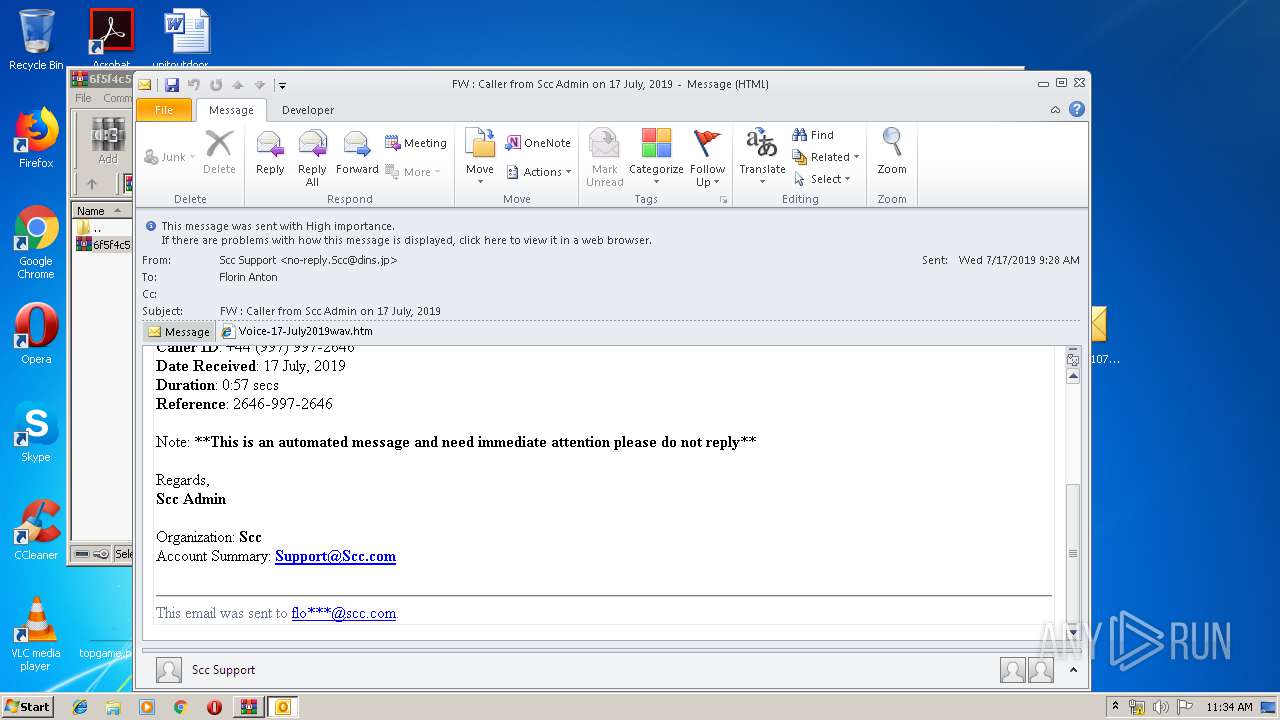
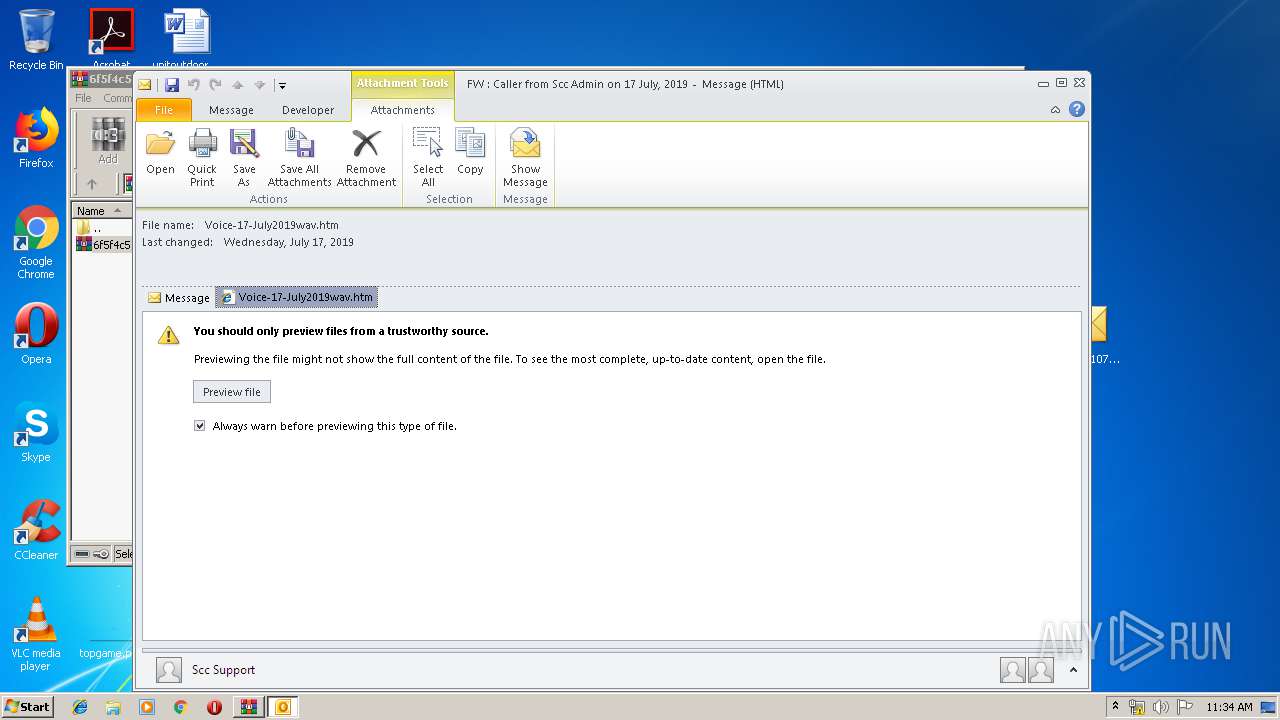
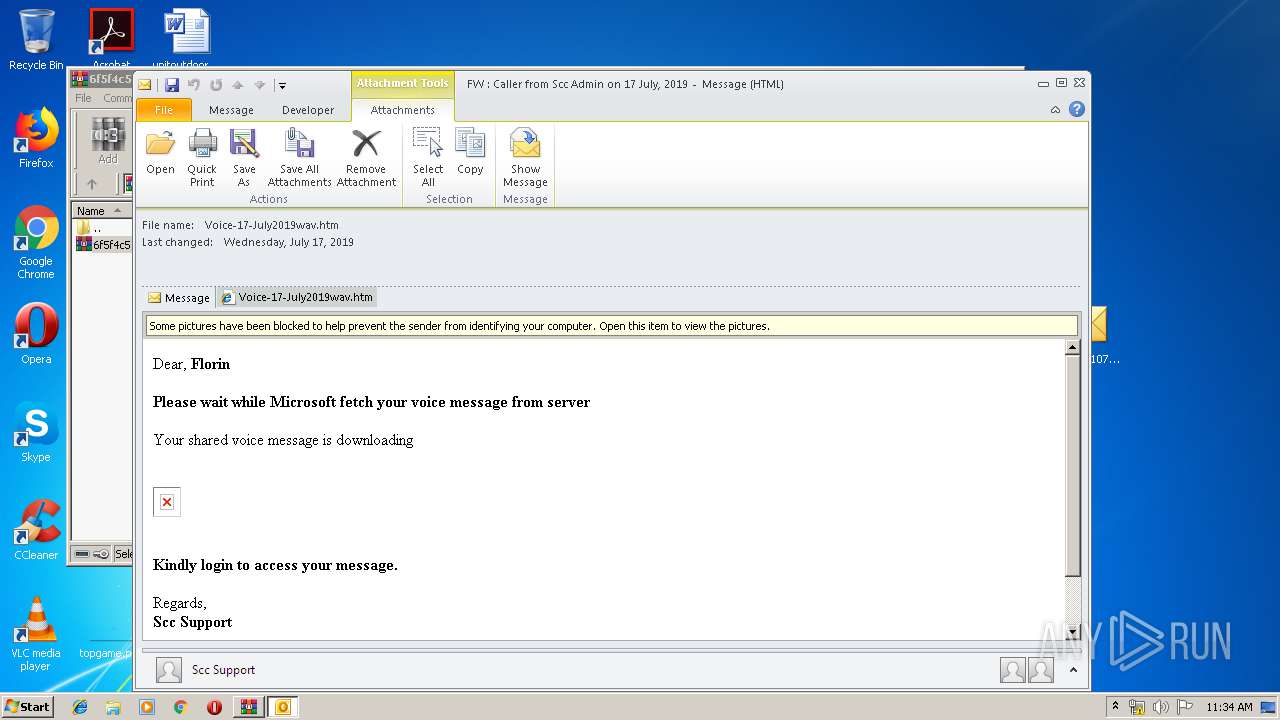
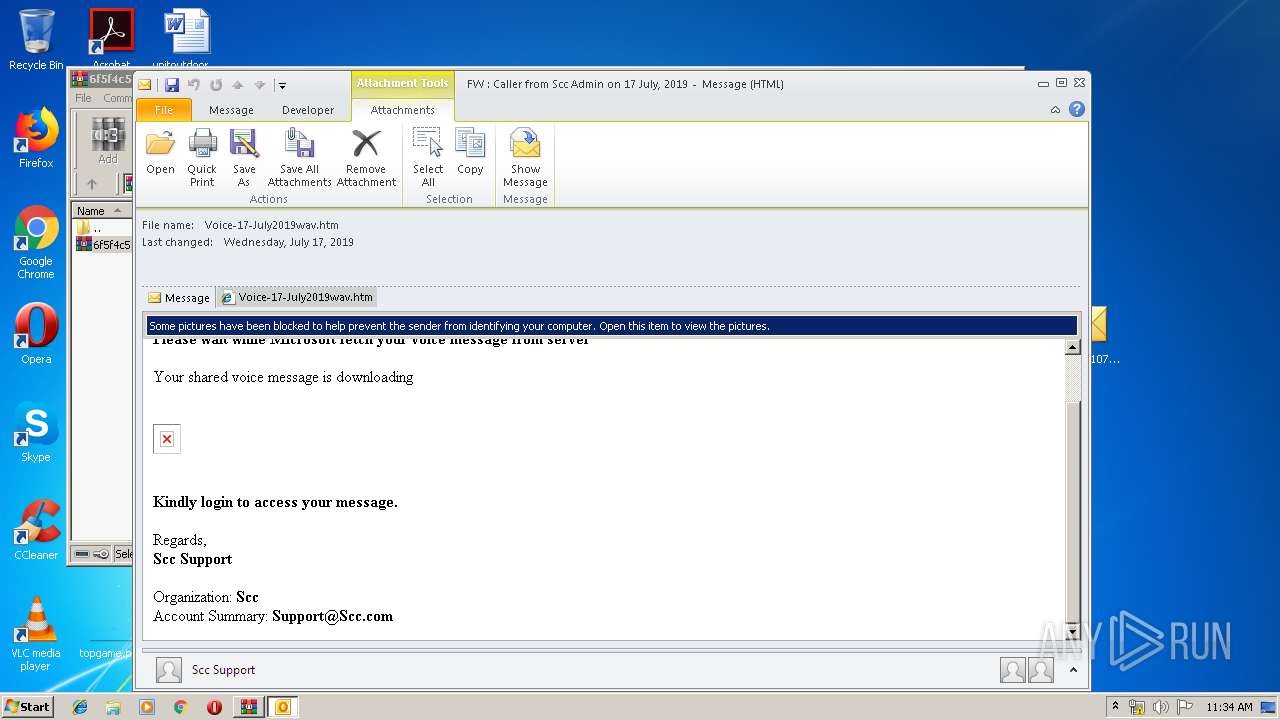
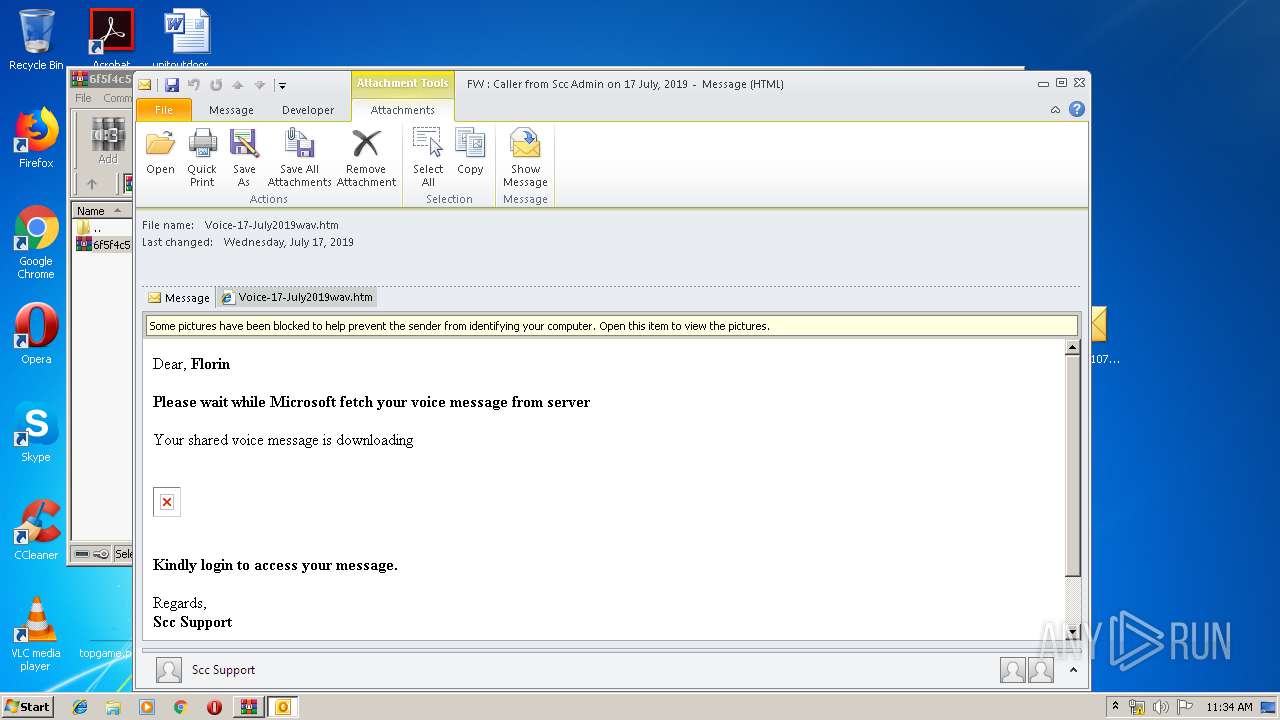
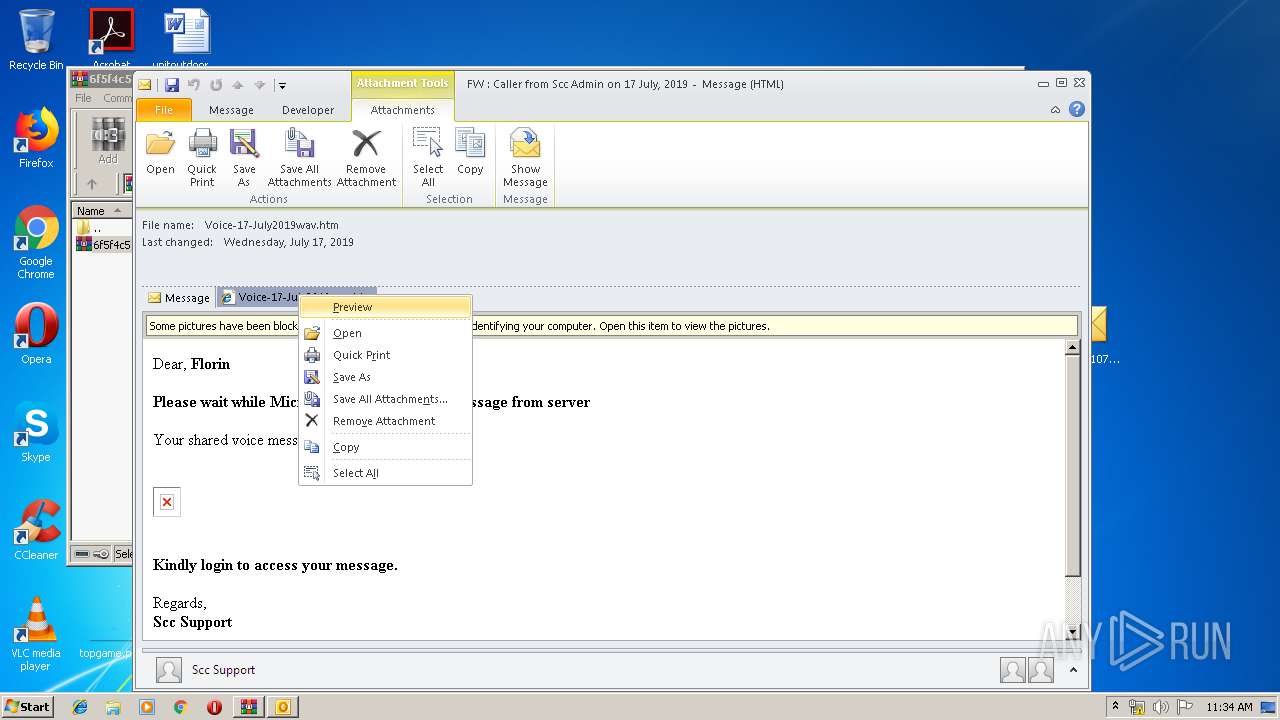
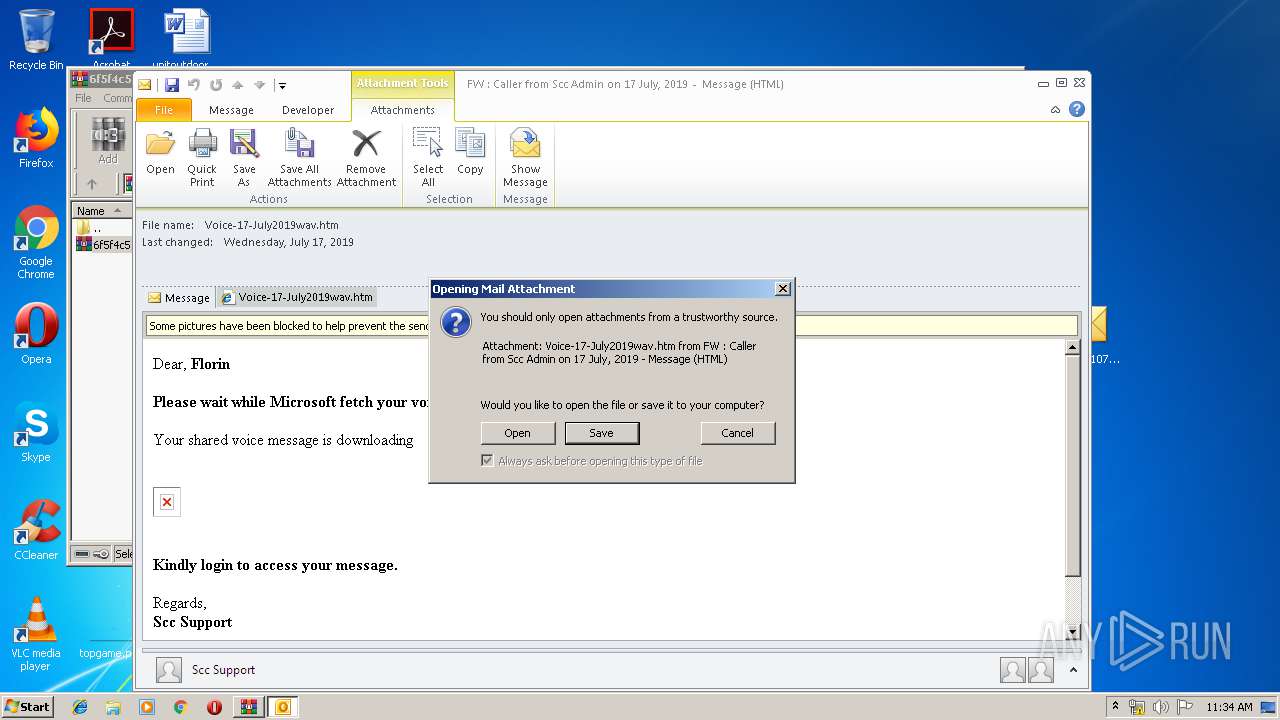
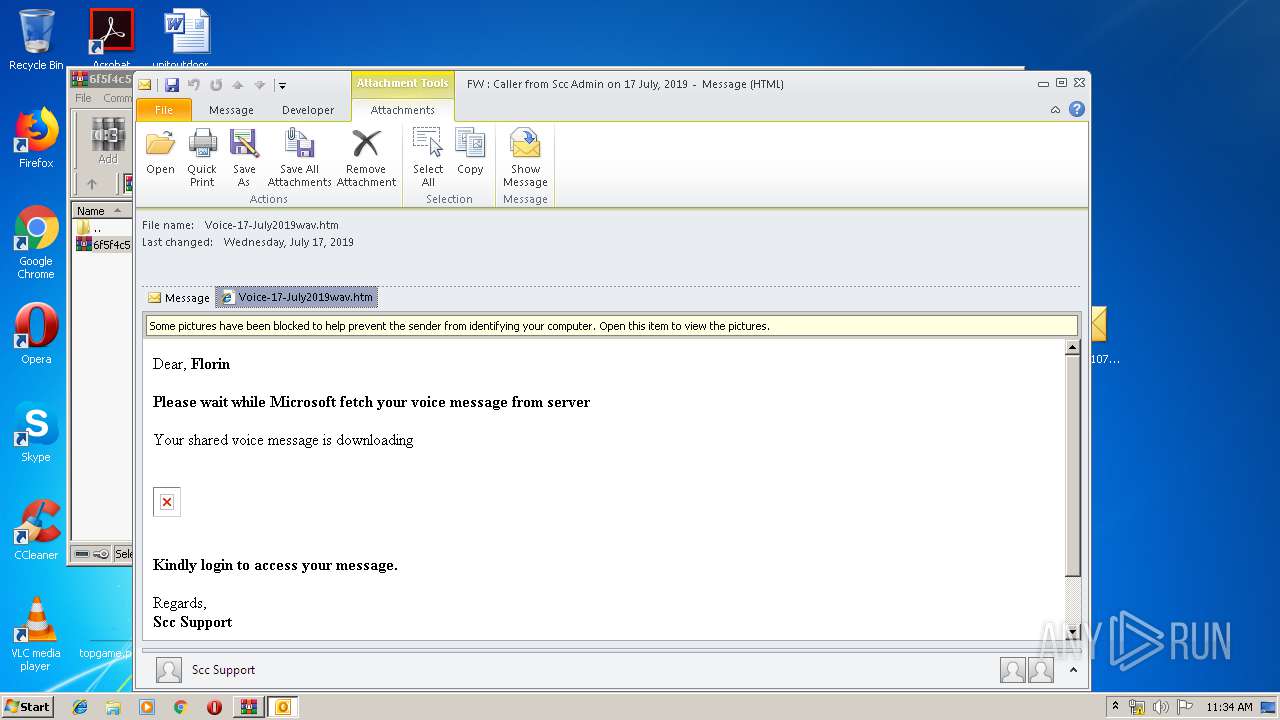
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3836)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3836)
Reads internet explorer settings
- prevhost.exe (PID: 3688)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3836)
Executed via COM
- prevhost.exe (PID: 3688)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3836)
INFO
Manual execution by user
- OUTLOOK.EXE (PID: 3836)
Changes internet zones settings
- iexplore.exe (PID: 3776)
Reads Internet Cache Settings
- iexplore.exe (PID: 2240)
Reads internet explorer settings
- iexplore.exe (PID: 2240)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | (none) |
| ModifyDate: | 0000:00:00 00:00:00 |
| ExtraFlags: | Maximum Compression |
| OperatingSystem: | Unix |
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2240 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3776 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3688 | C:\Windows\system32\prevhost.exe {F8B8412B-DEA3-4130-B36C-5E8BE73106AC} -Embedding | C:\Windows\system32\prevhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Preview Handler Surrogate Host Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
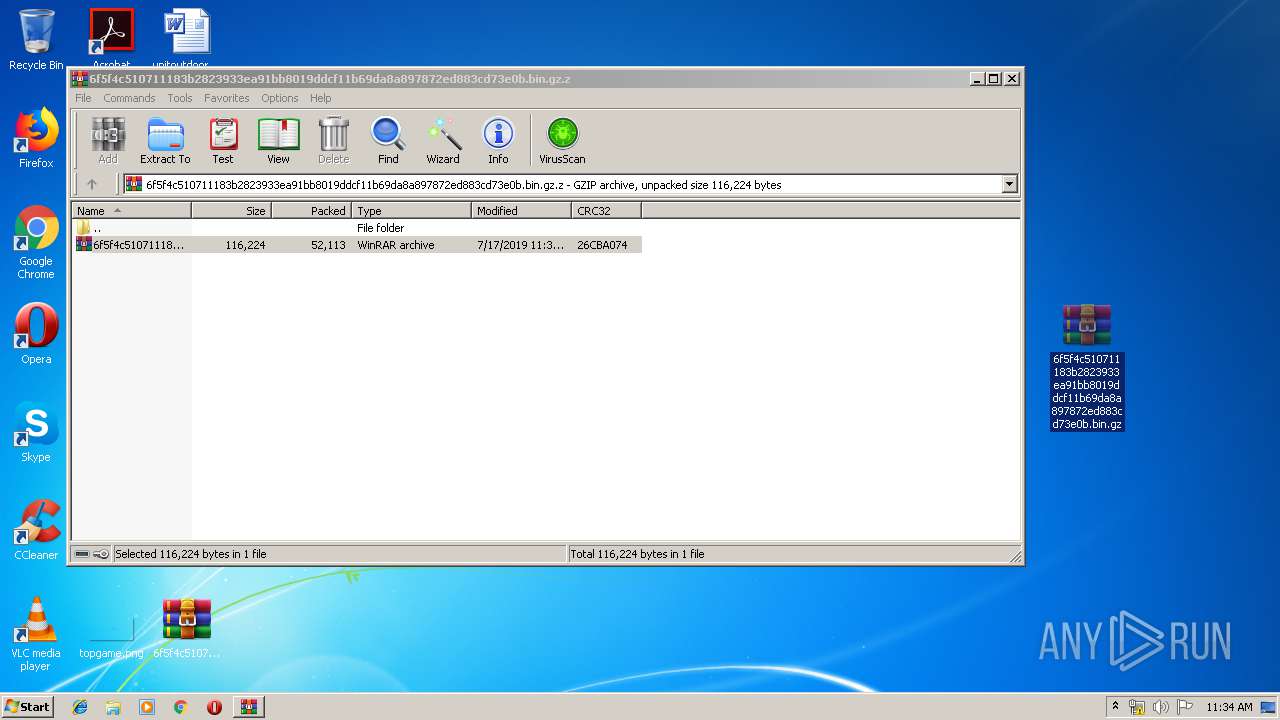
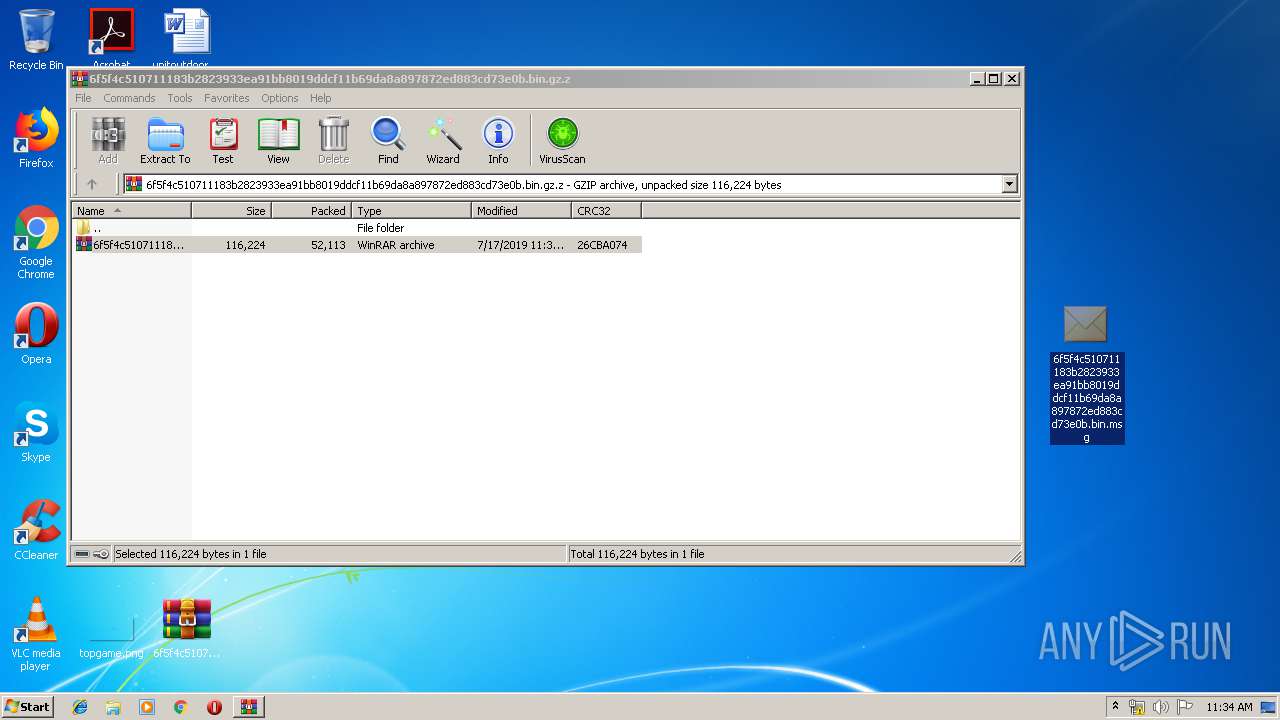
| 3768 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\6f5f4c510711183b2823933ea91bb8019ddcf11b69da8a897872ed883cd73e0b.bin.gz.z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
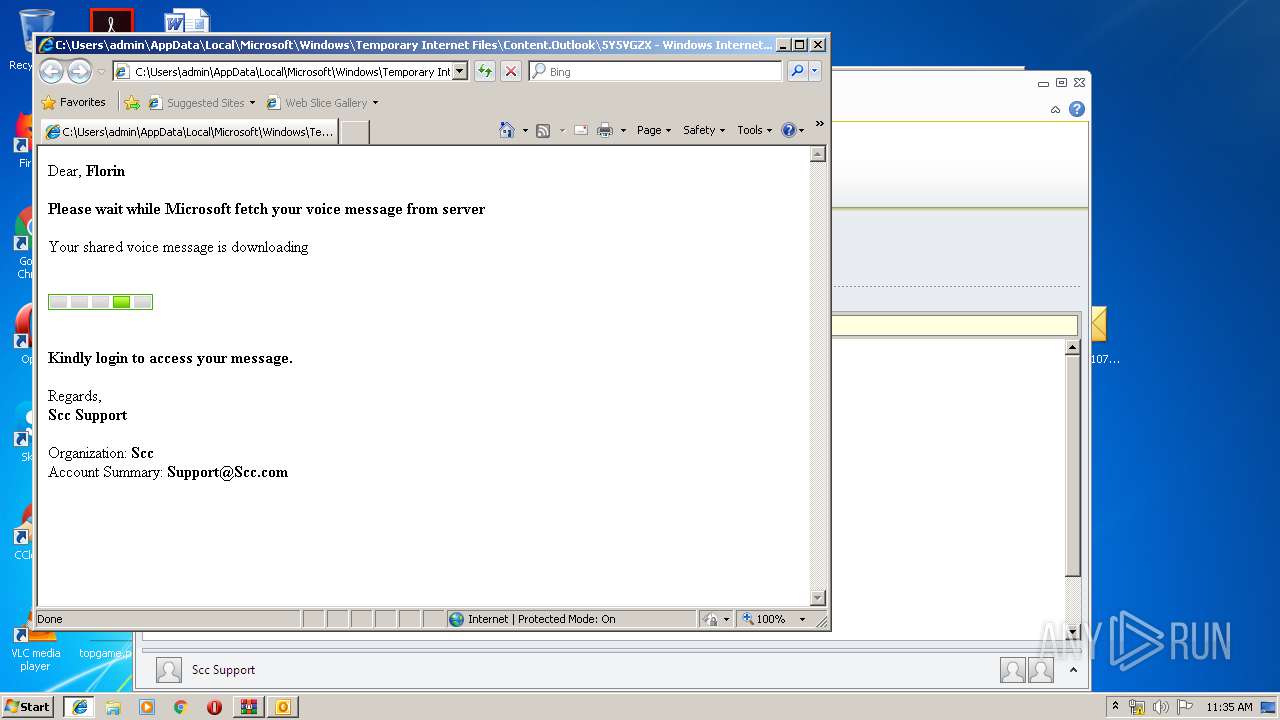
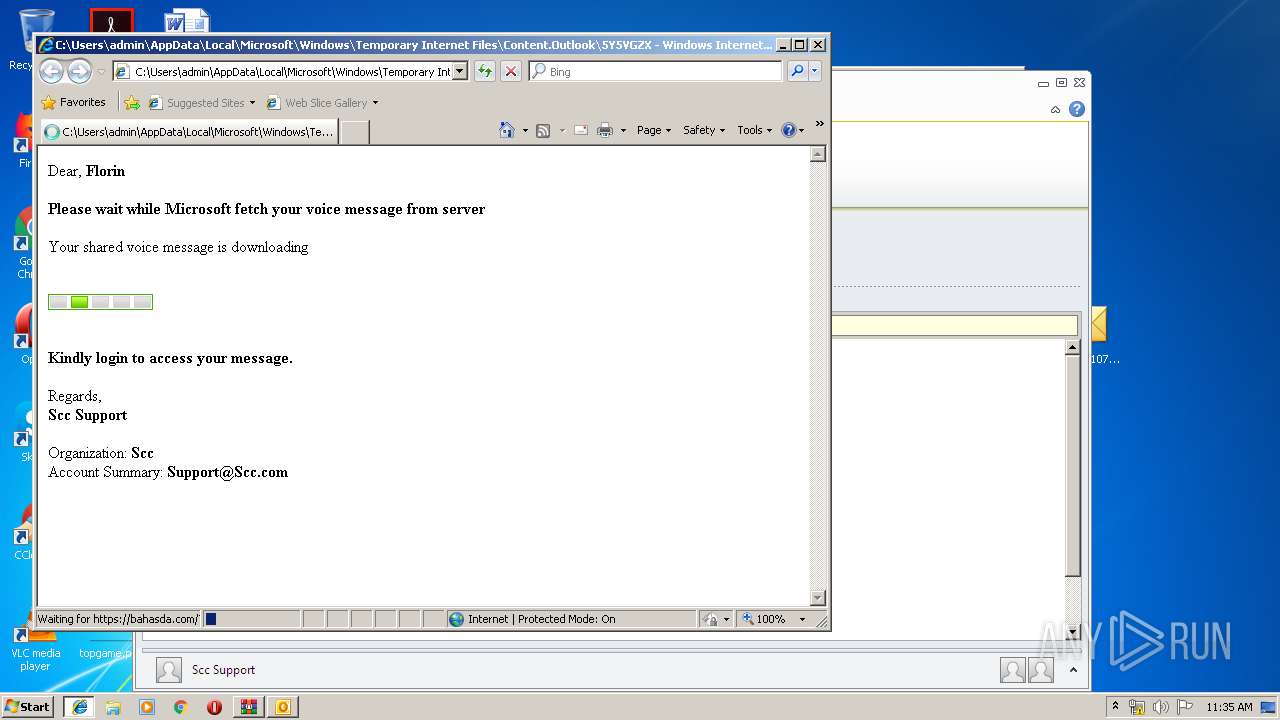
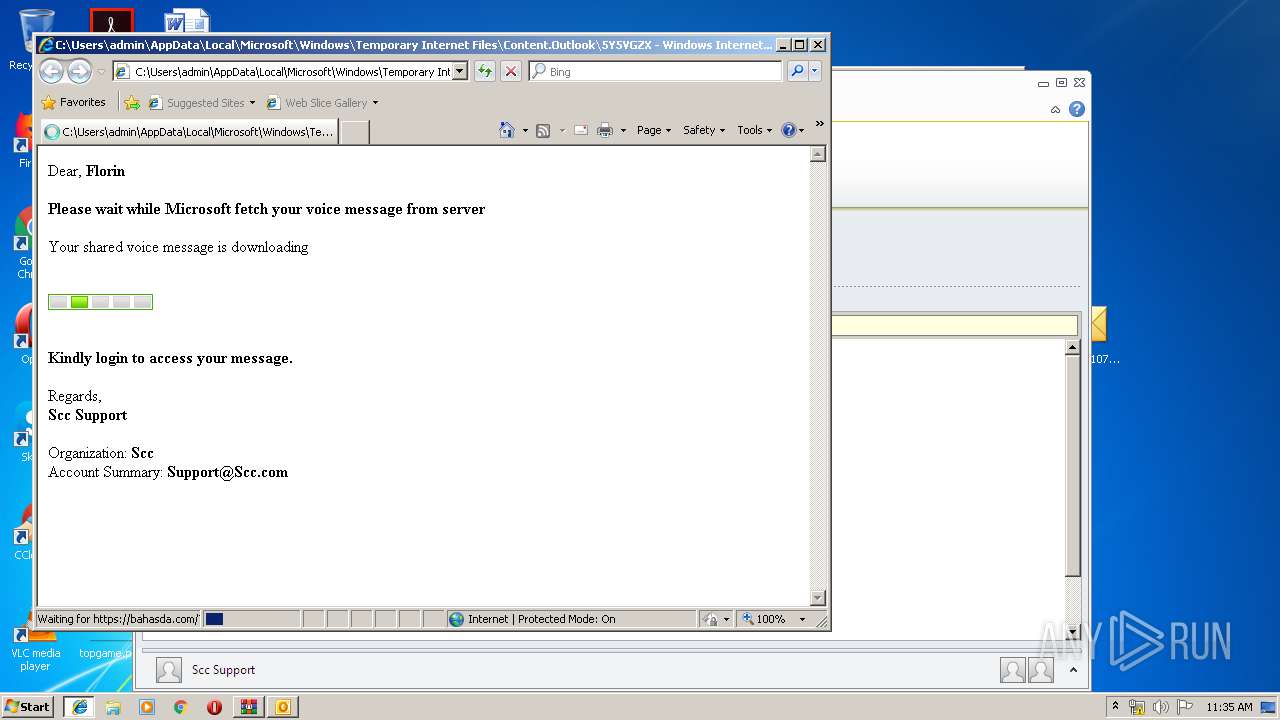
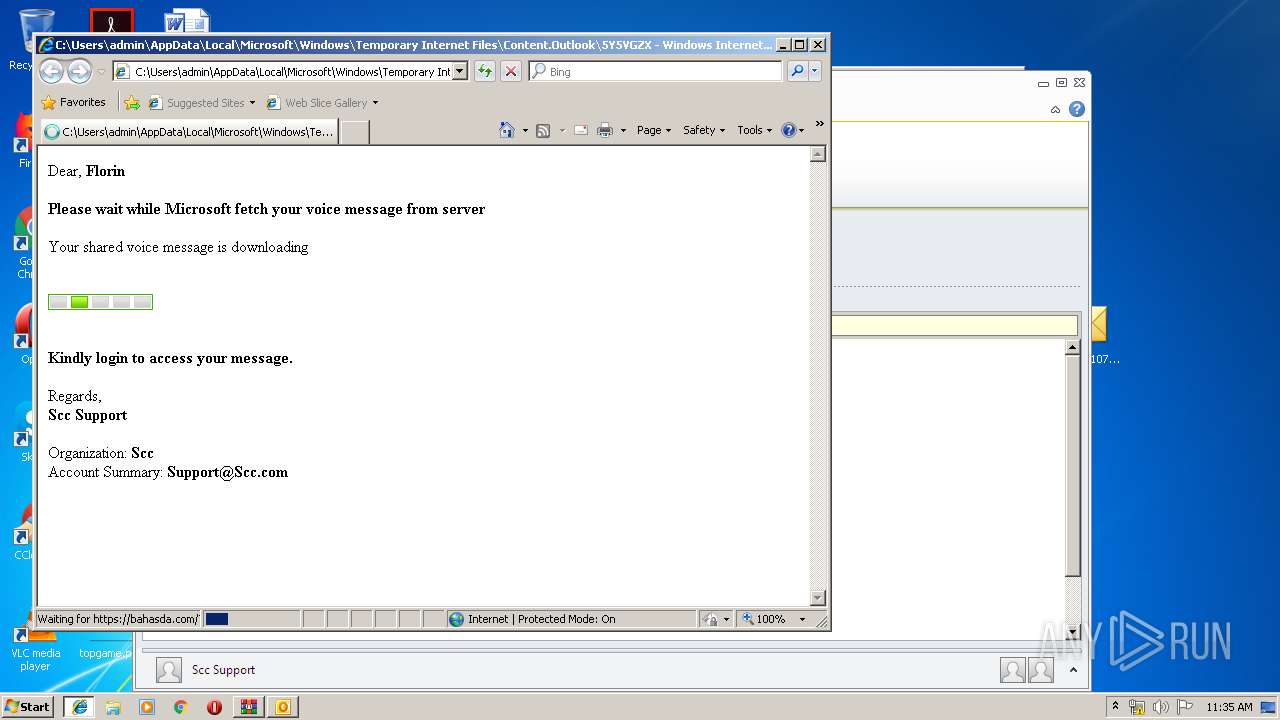
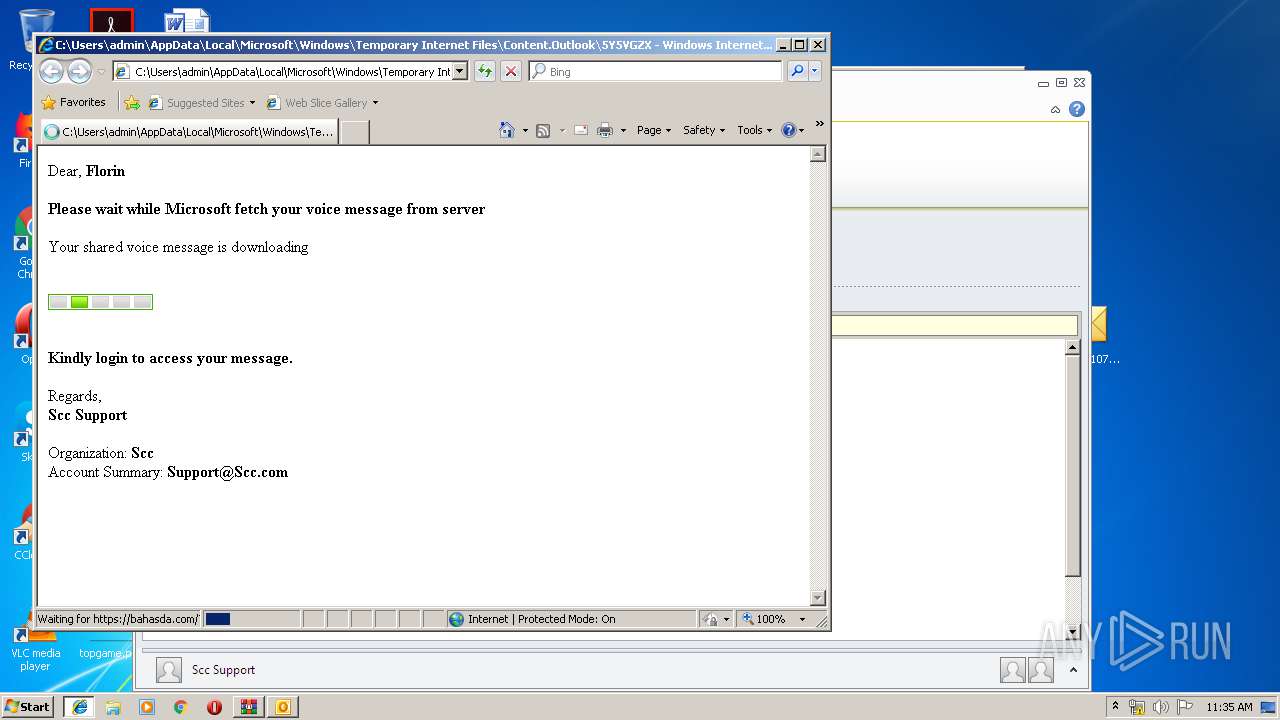
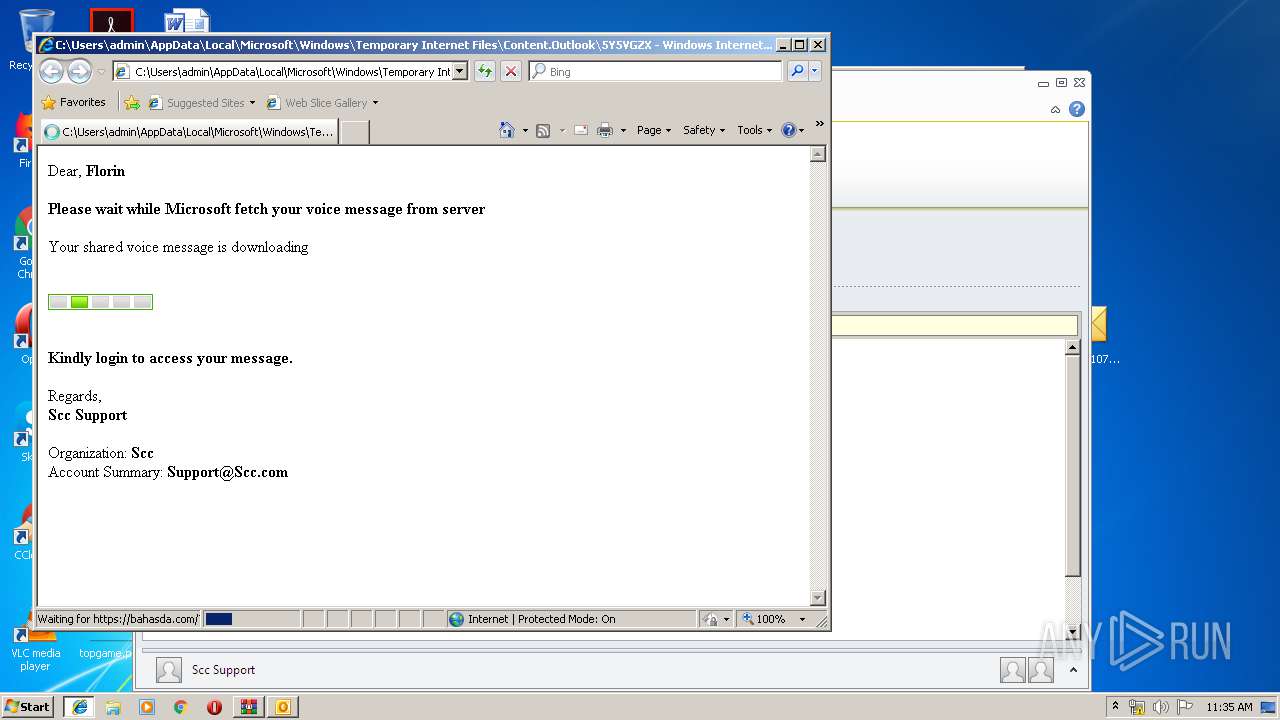
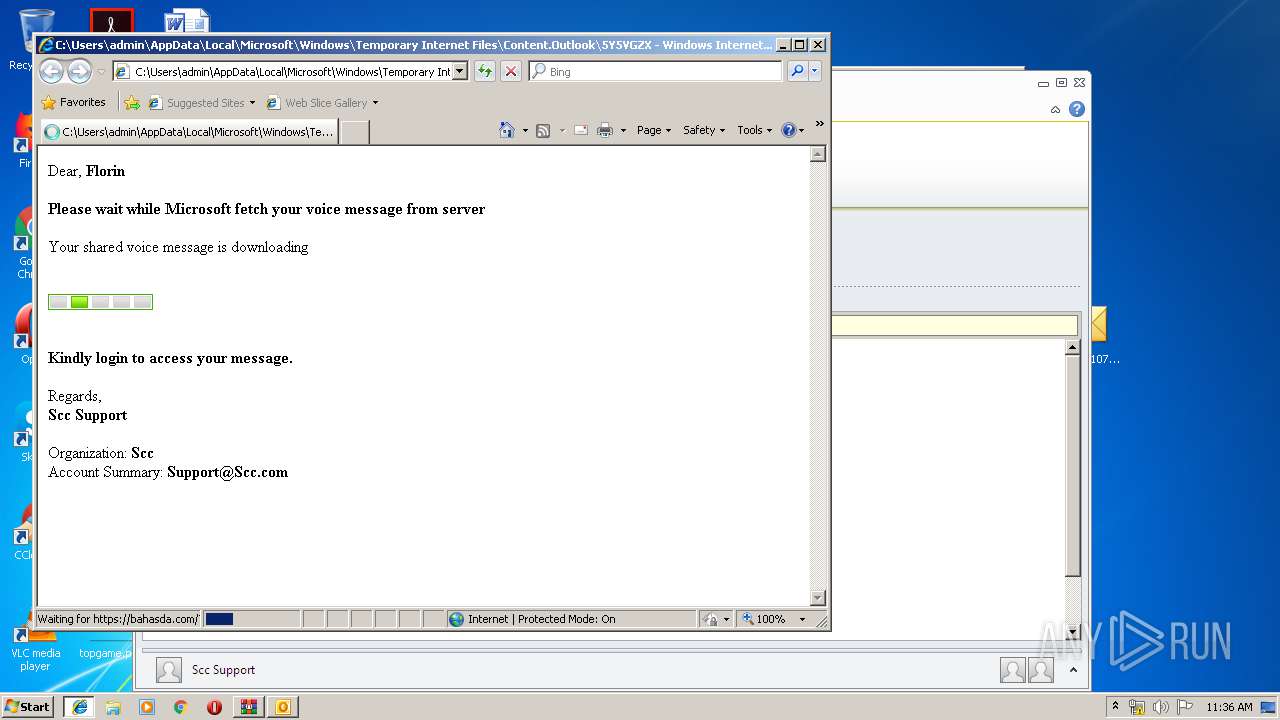
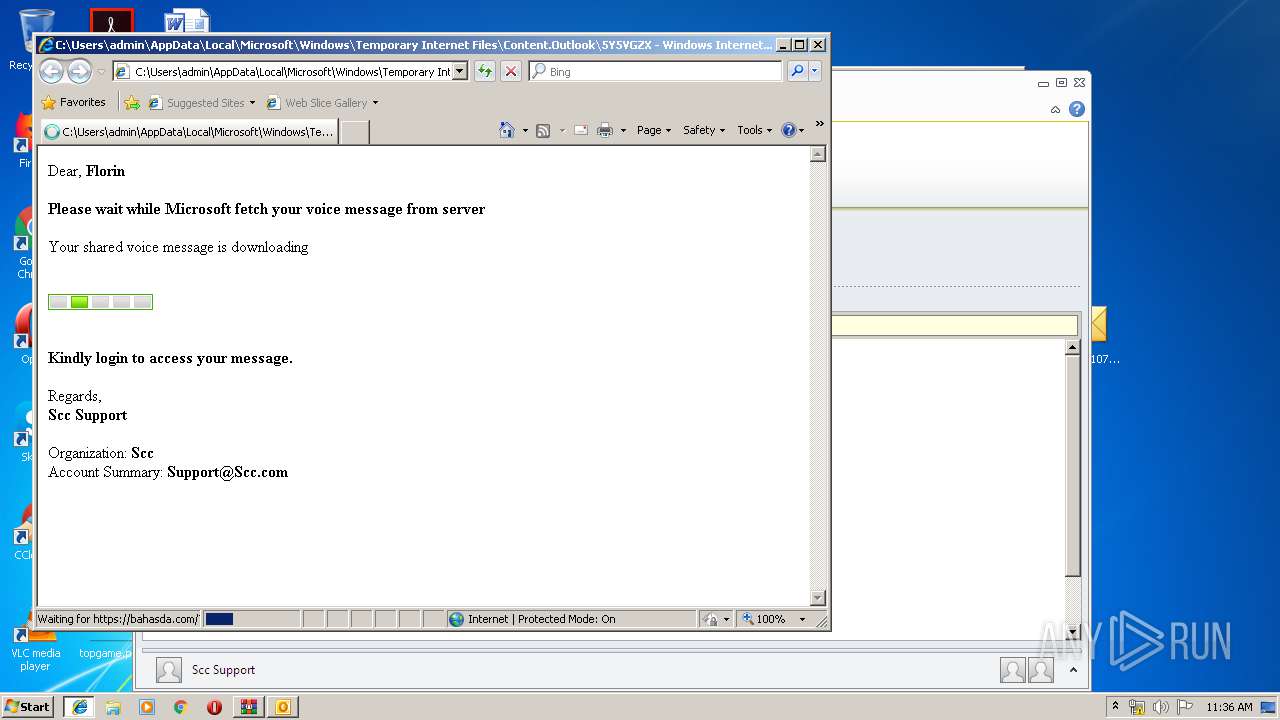
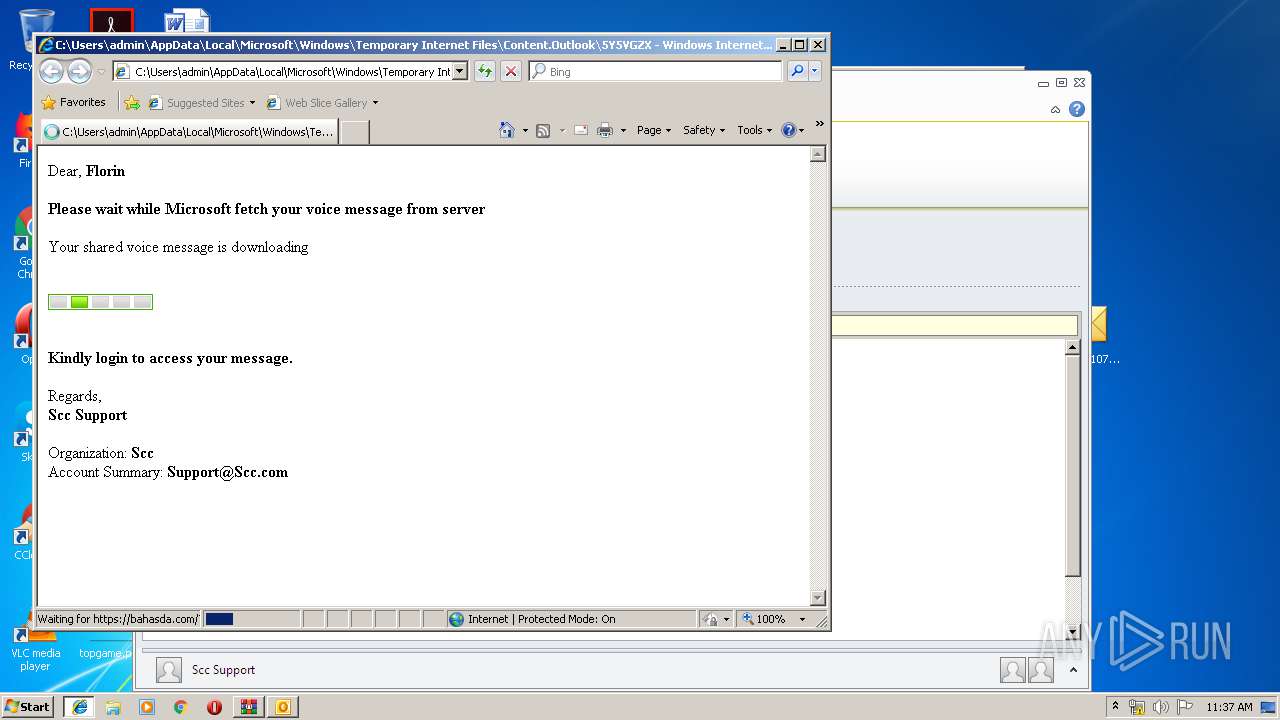
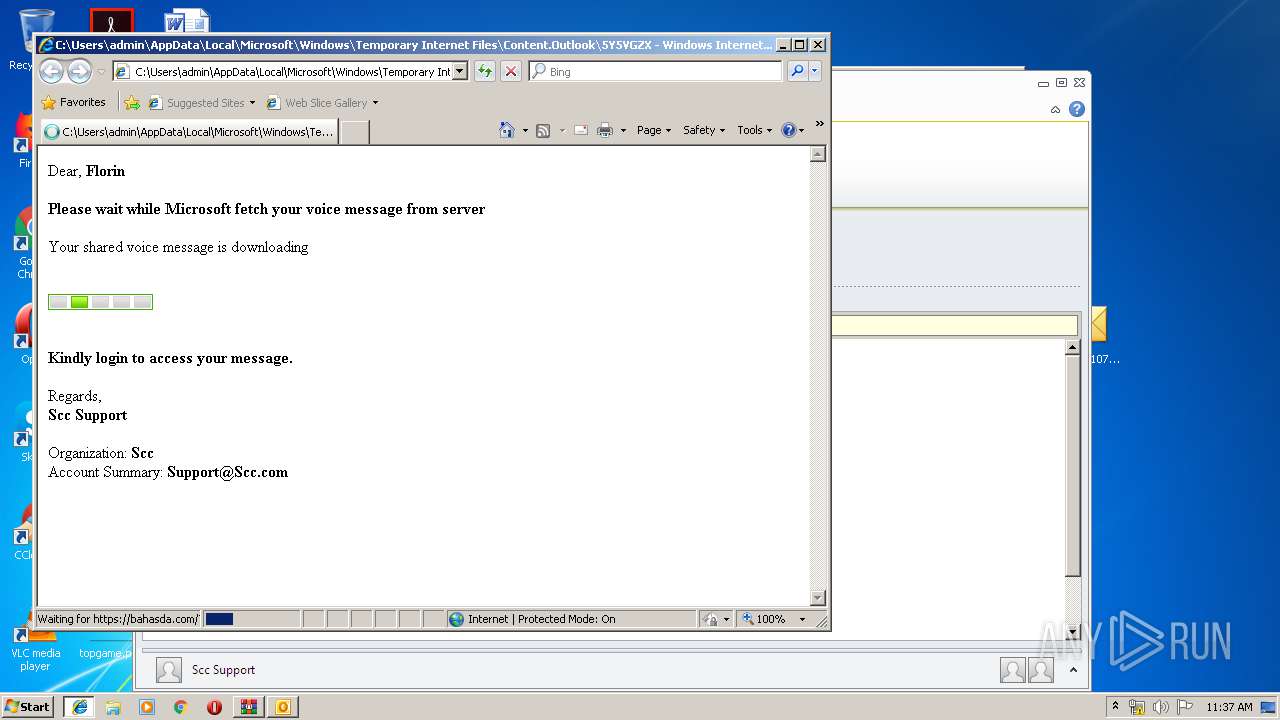
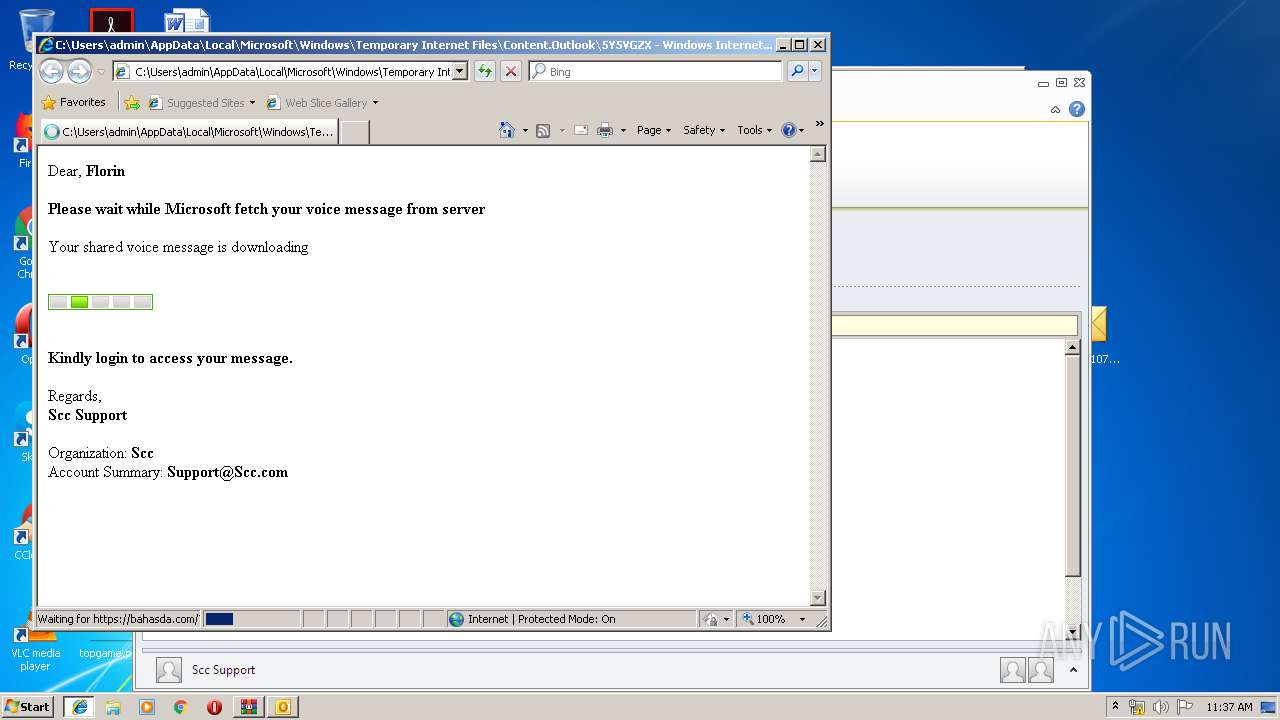
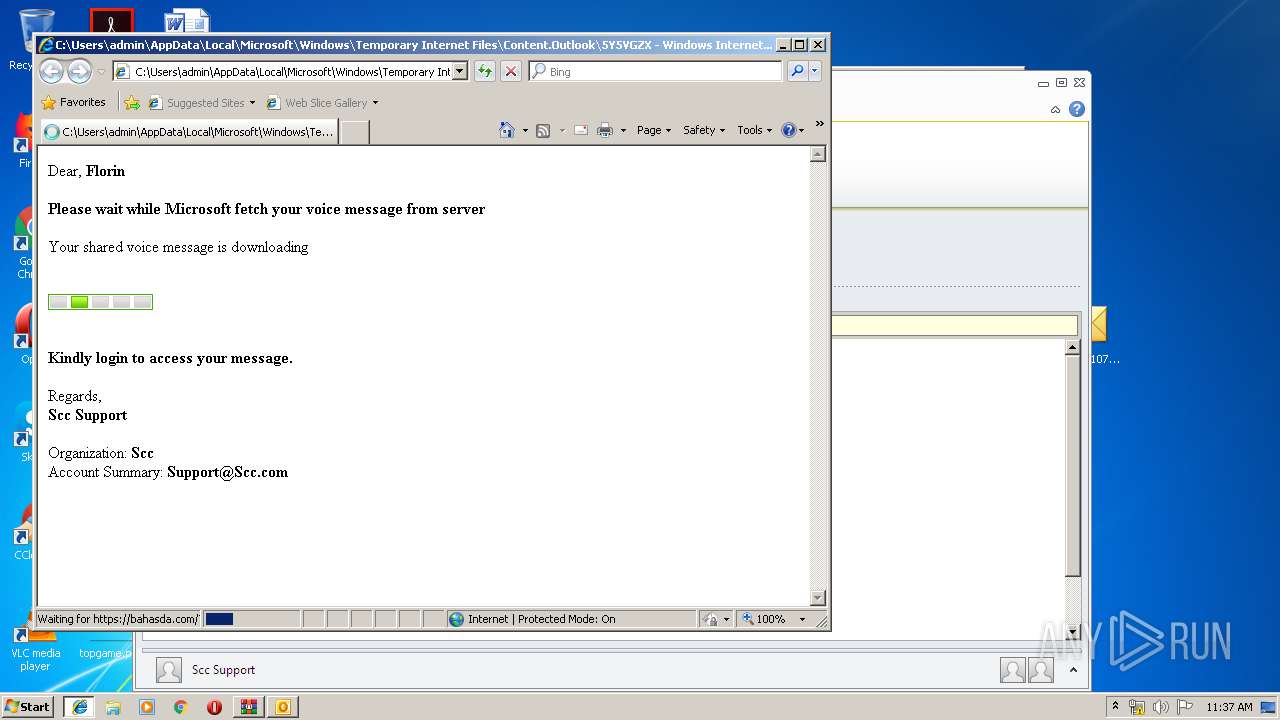
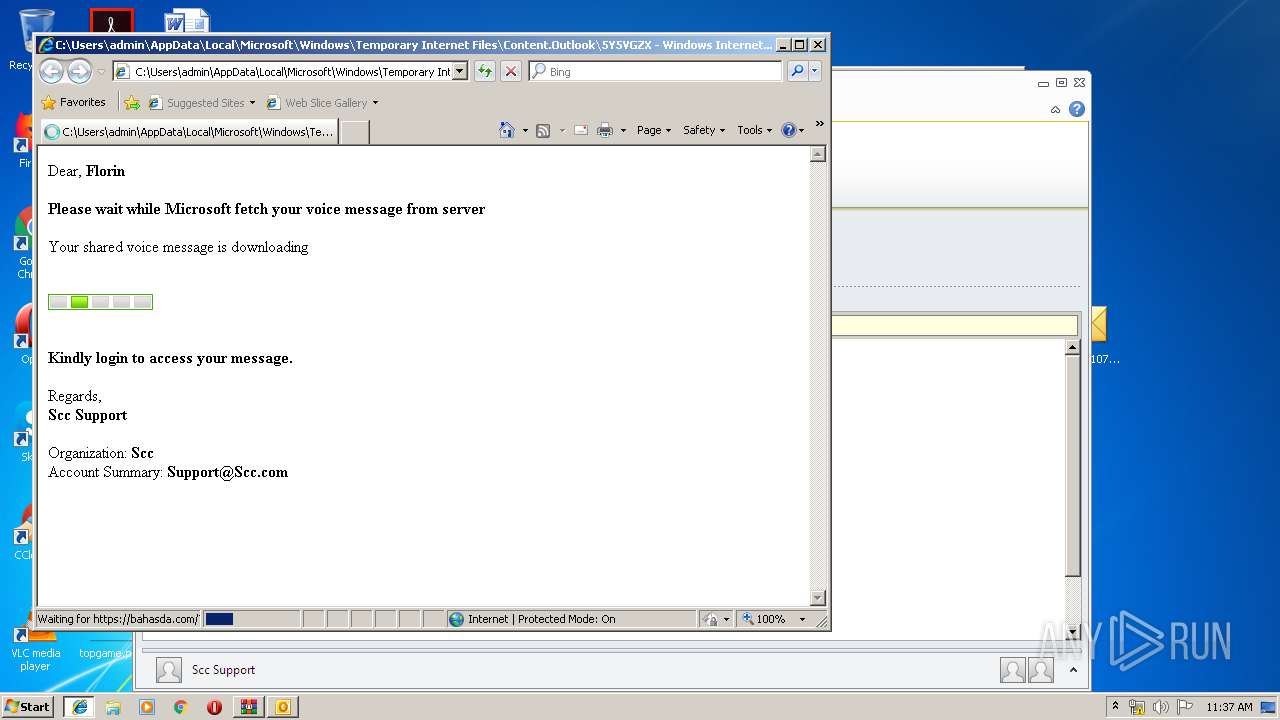
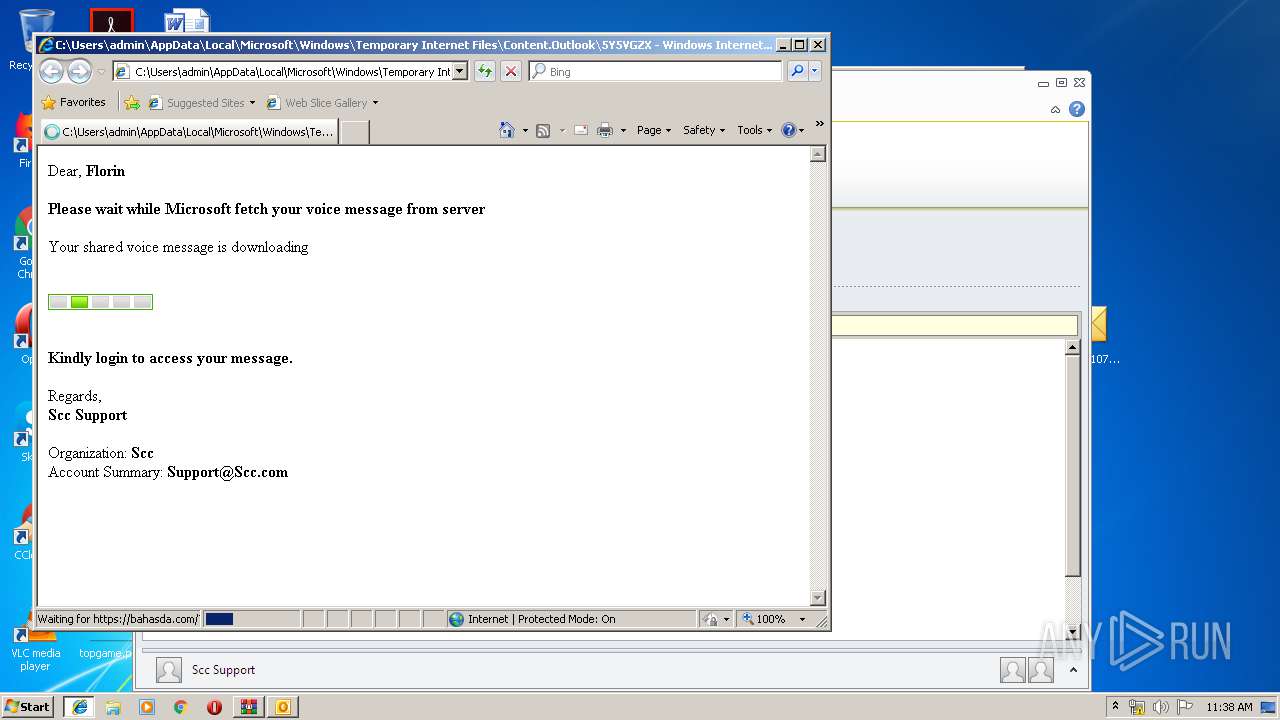
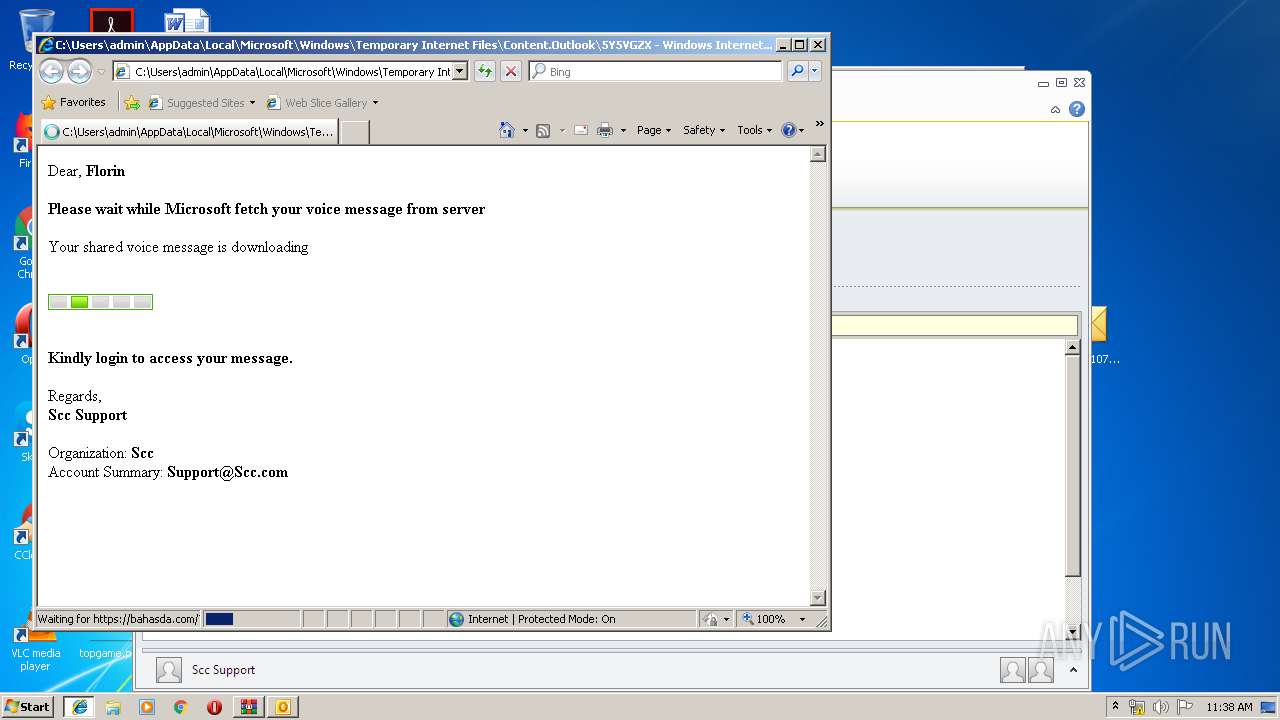
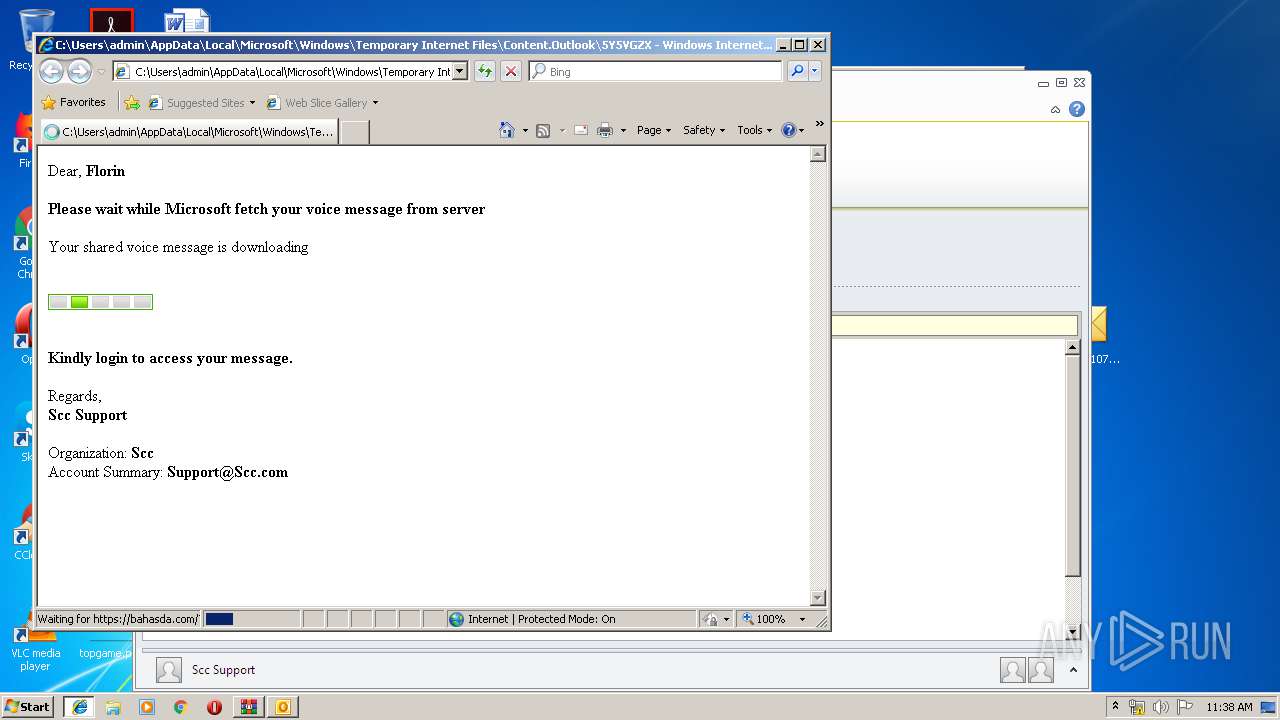
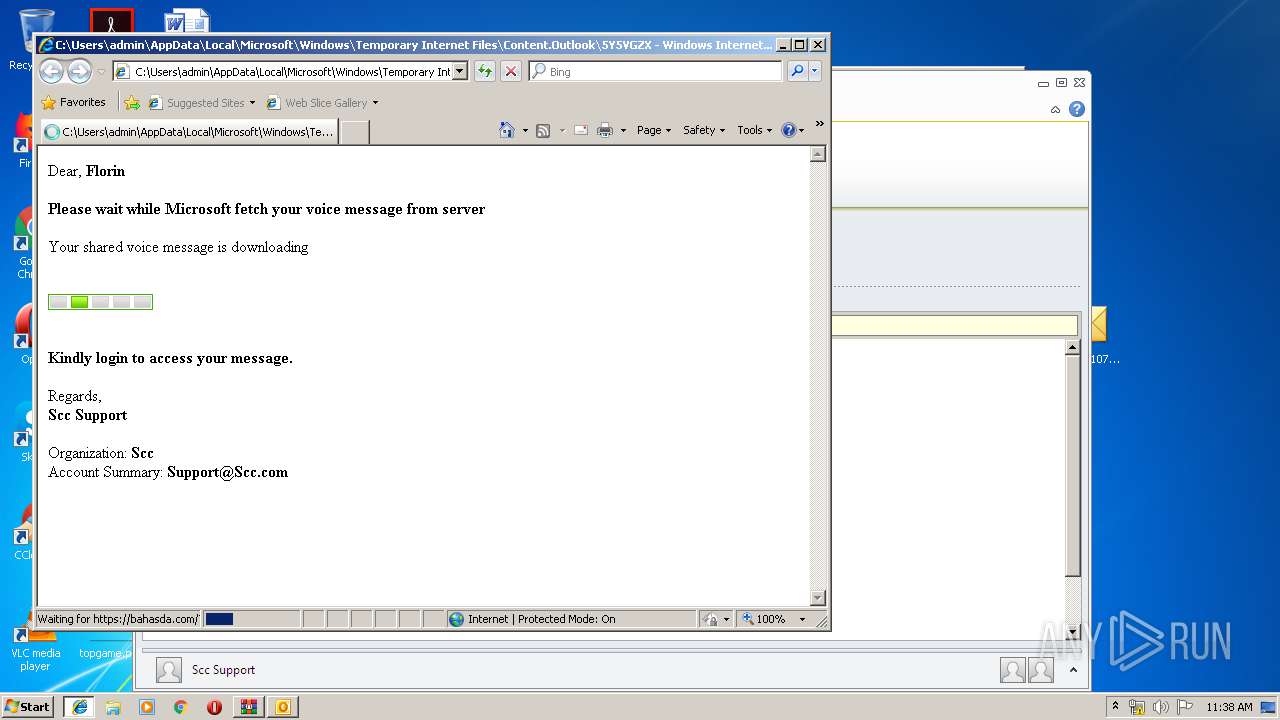
| 3776 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\5Y5VGZXT\Voice-17-July2019wav.htm | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3836 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\Desktop\6f5f4c510711183b2823933ea91bb8019ddcf11b69da8a897872ed883cd73e0b.bin.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
2 152
Read events
1 678
Write events
454
Delete events
20
Modification events
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\6f5f4c510711183b2823933ea91bb8019ddcf11b69da8a897872ed883cd73e0b.bin.gz.z | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3768) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3836) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3836) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
Executable files
0
Suspicious files
0
Text files
29
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3768.14512\6f5f4c510711183b2823933ea91bb8019ddcf11b69da8a897872ed883cd73e0b.bin.gz | — | |
MD5:— | SHA256:— | |||
| 3836 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4CF3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3836 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\5Y5VGZXT\Voice-17-July2019wav (2).htm\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3776 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3776 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3836 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3836 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\64A53CC3.dat | image | |
MD5:1767DA587465A52A74E4A63000D3EC0D | SHA256:CE7B8581FA1ACFCA82E0FA4D24B2B786E467FC863420E6EEF50A05238947ADB2 | |||
| 3836 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_0812DC4D68E911429C0CA40F26E29B94.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 3836 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_27357786FCA956449D290DDF0A255B39.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 2240 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3836 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3776 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3836 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3776 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2240 | iexplore.exe | 142.44.211.130:443 | bahasda.com | OVH SAS | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
bahasda.com |
| unknown |