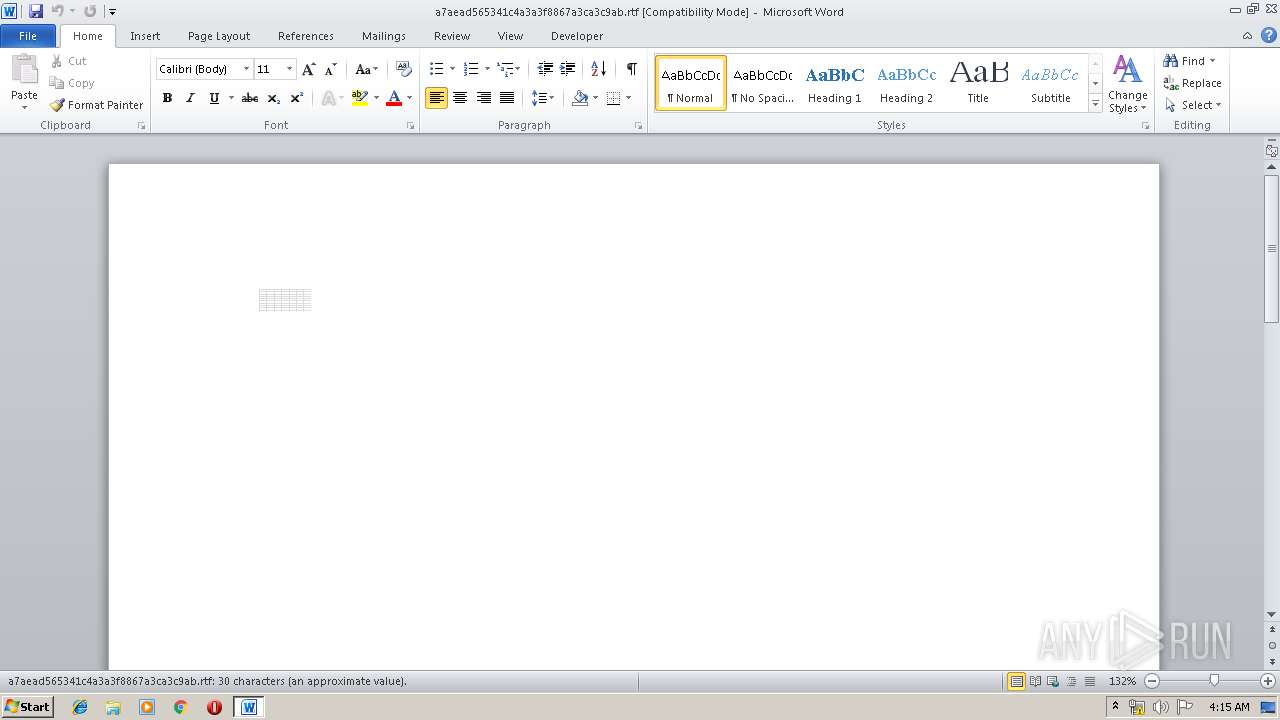
| File name: | a7aead565341c4a3a3f8867a3ca3c9ab |
| Full analysis: | https://app.any.run/tasks/0cc8d526-3e21-42c5-ba01-02c905d1f7d2 |
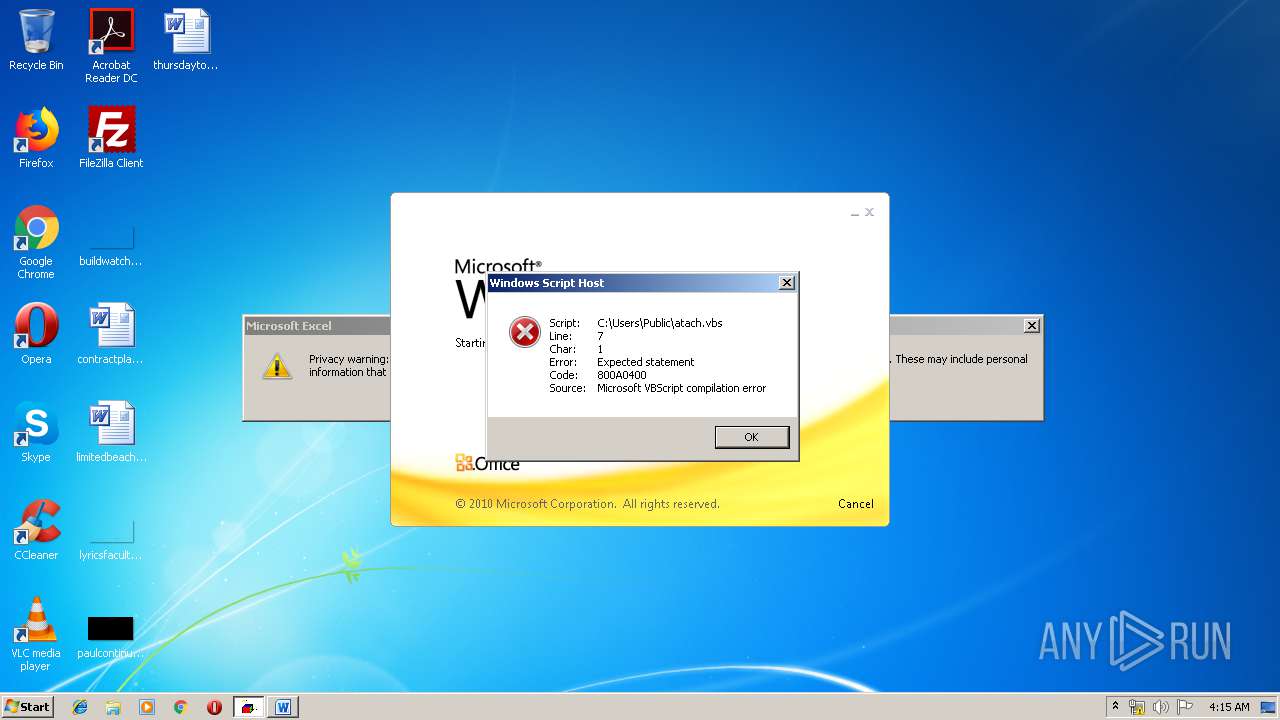
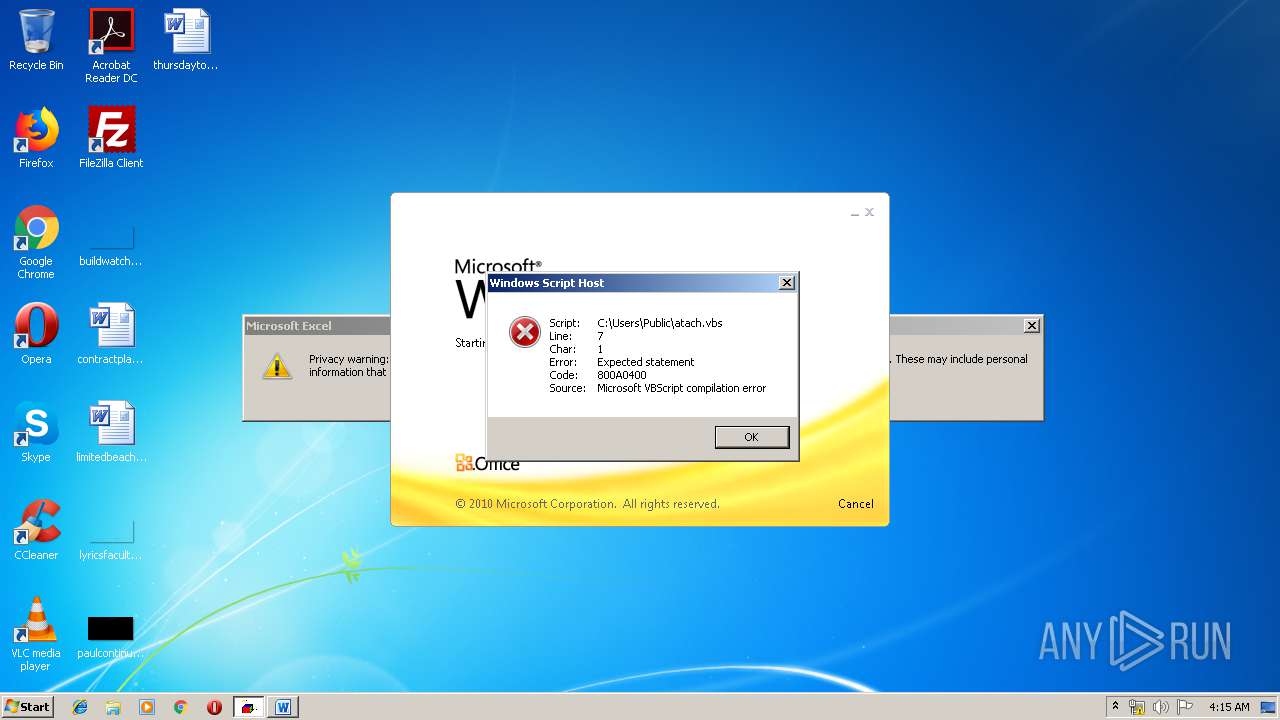
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 03:14:37 |
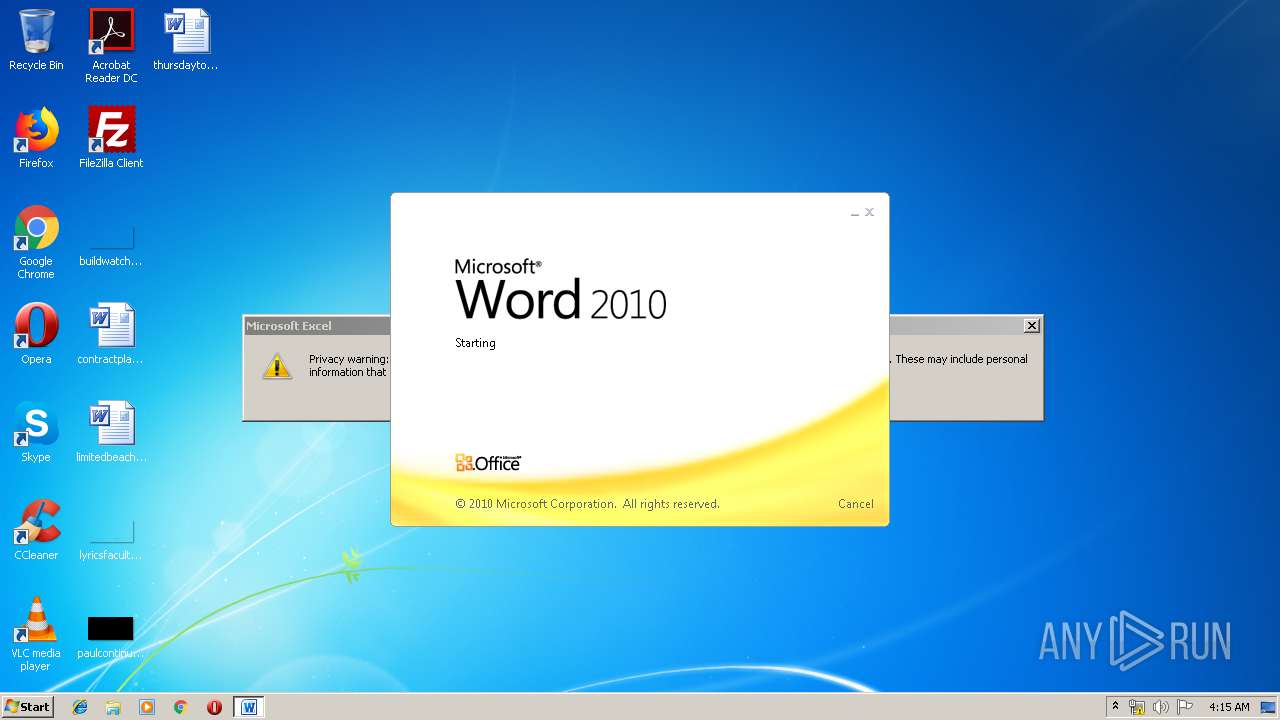
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | A7AEAD565341C4A3A3F8867A3CA3C9AB |
| SHA1: | 61EDA60023DA167657C1B89251E4C11CC40DF87A |
| SHA256: | A2D41FFA099E587EB692A7E90B37B978A4A49E4F2A00BA383027F1DBC10328AC |
| SSDEEP: | 768:qaKf8YDEP6d3MzuuUdjTCMJhIS4NX8l0l/cHnQeEHpljeDXrdBj1ANlY7S4cwHNX:qfCqNdjOi4UHHQxJlwrdboY7Scttt |
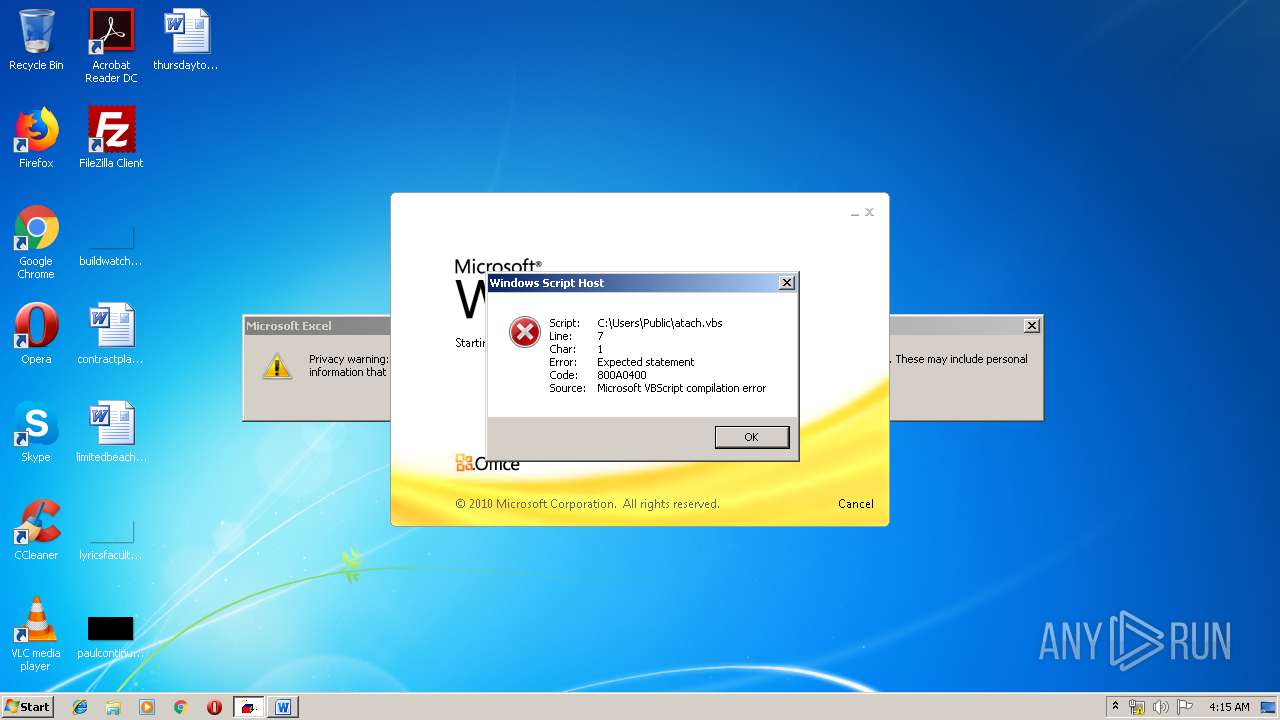
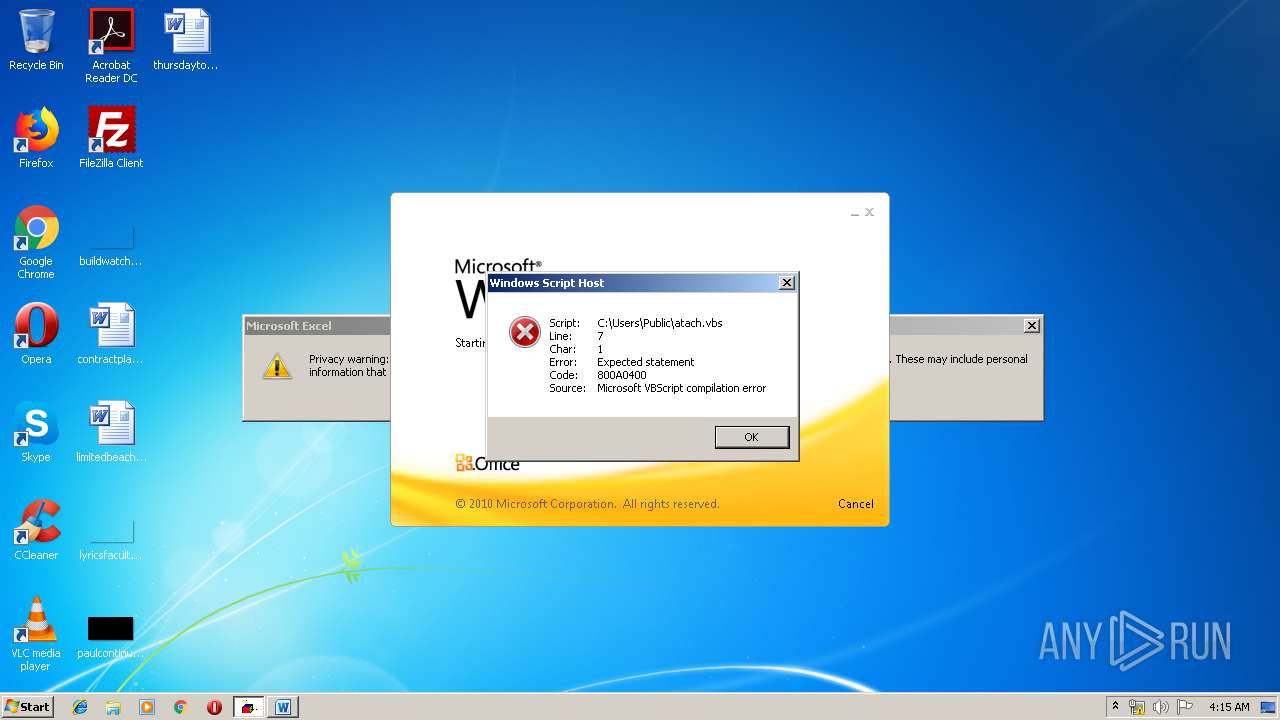
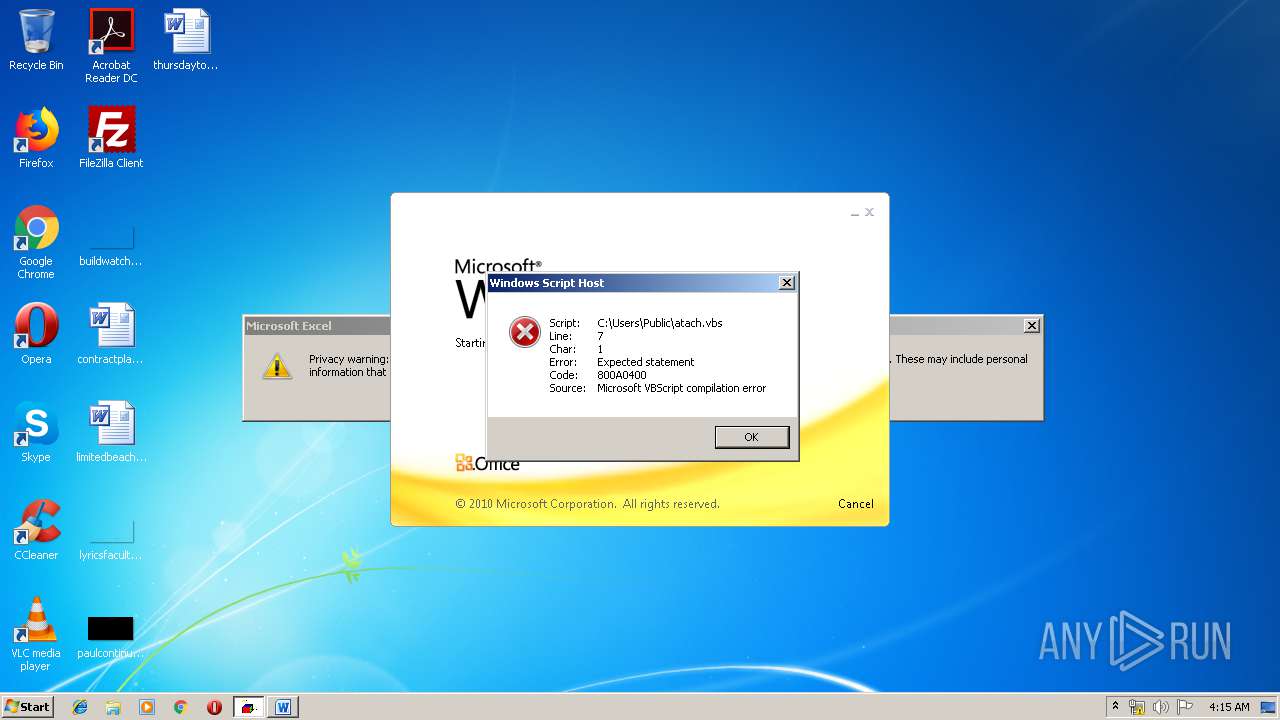
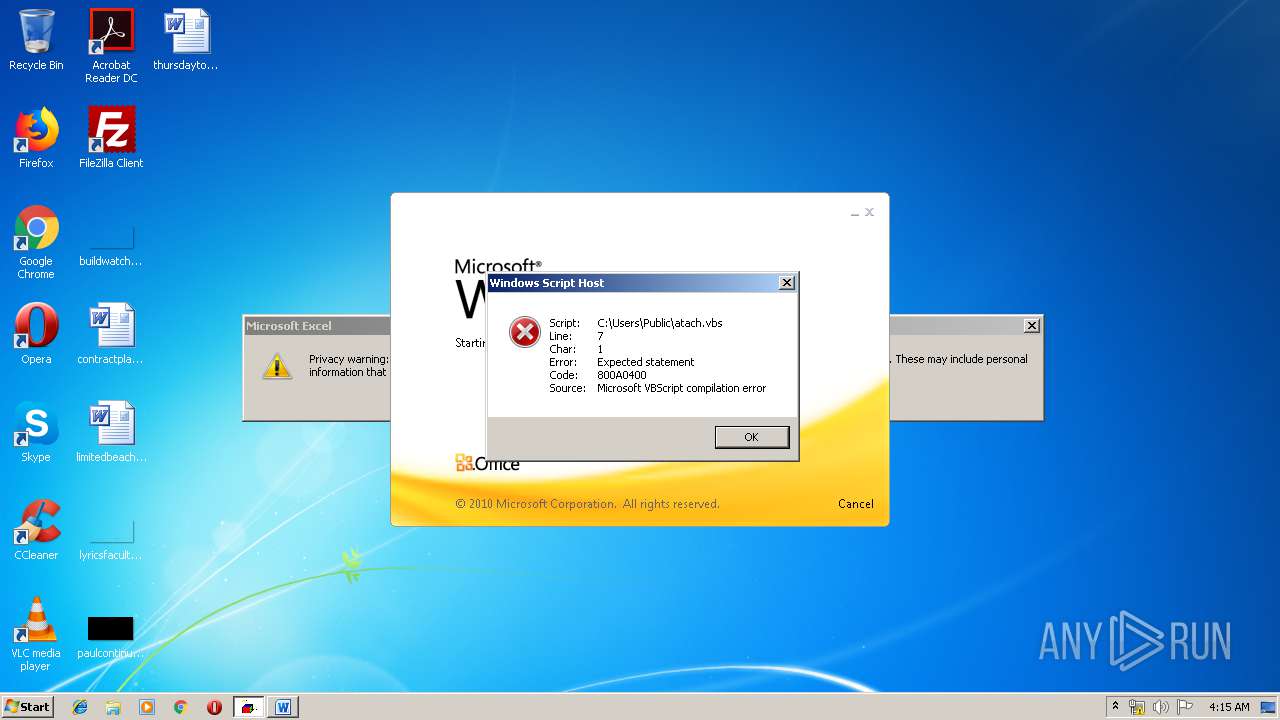
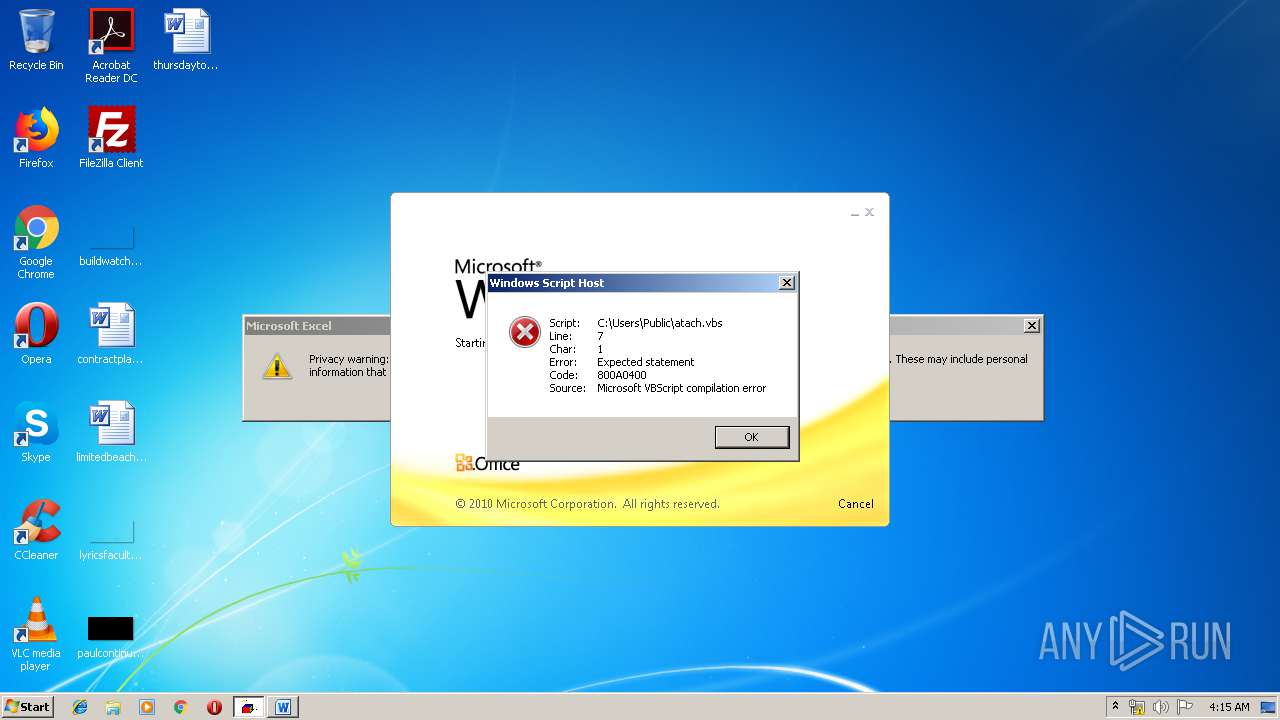
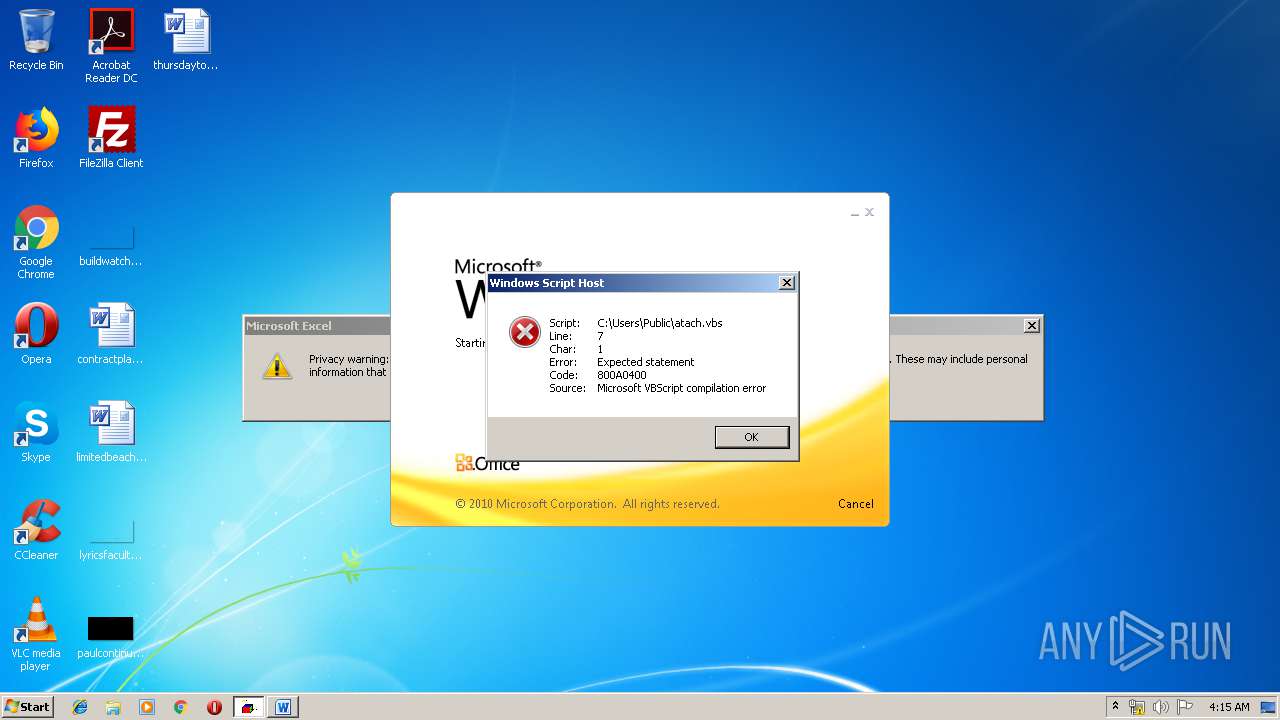
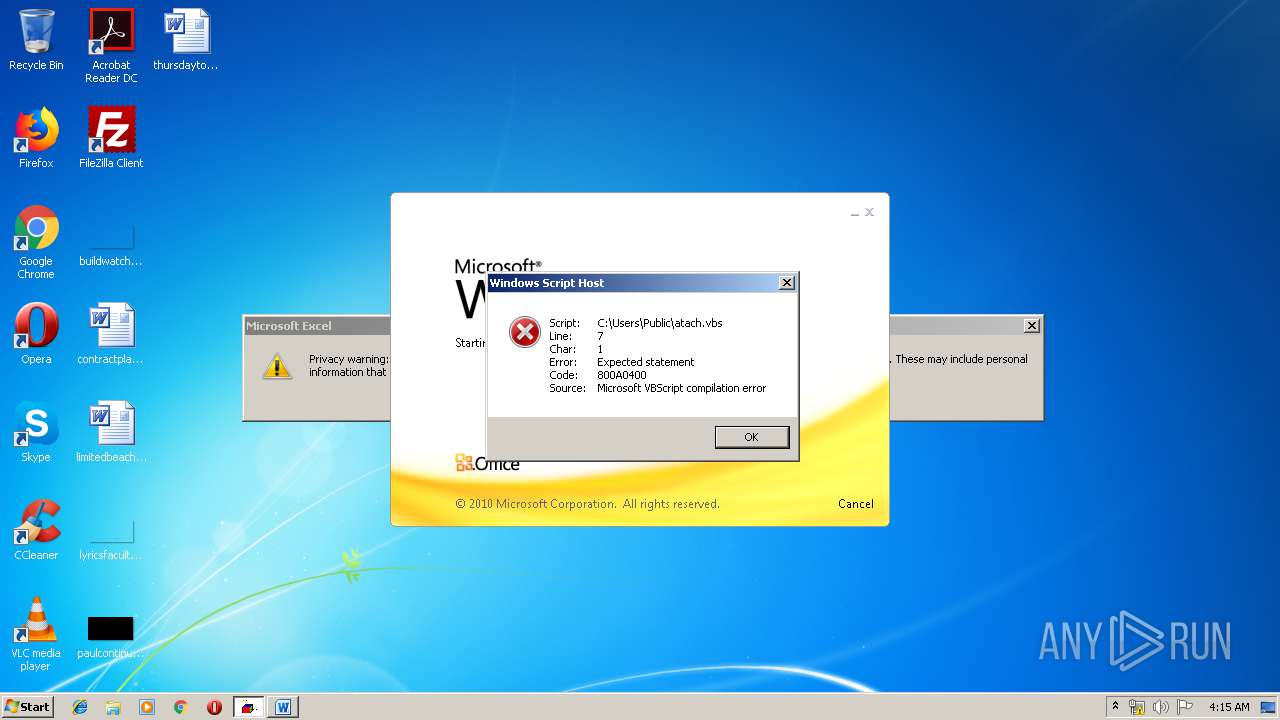
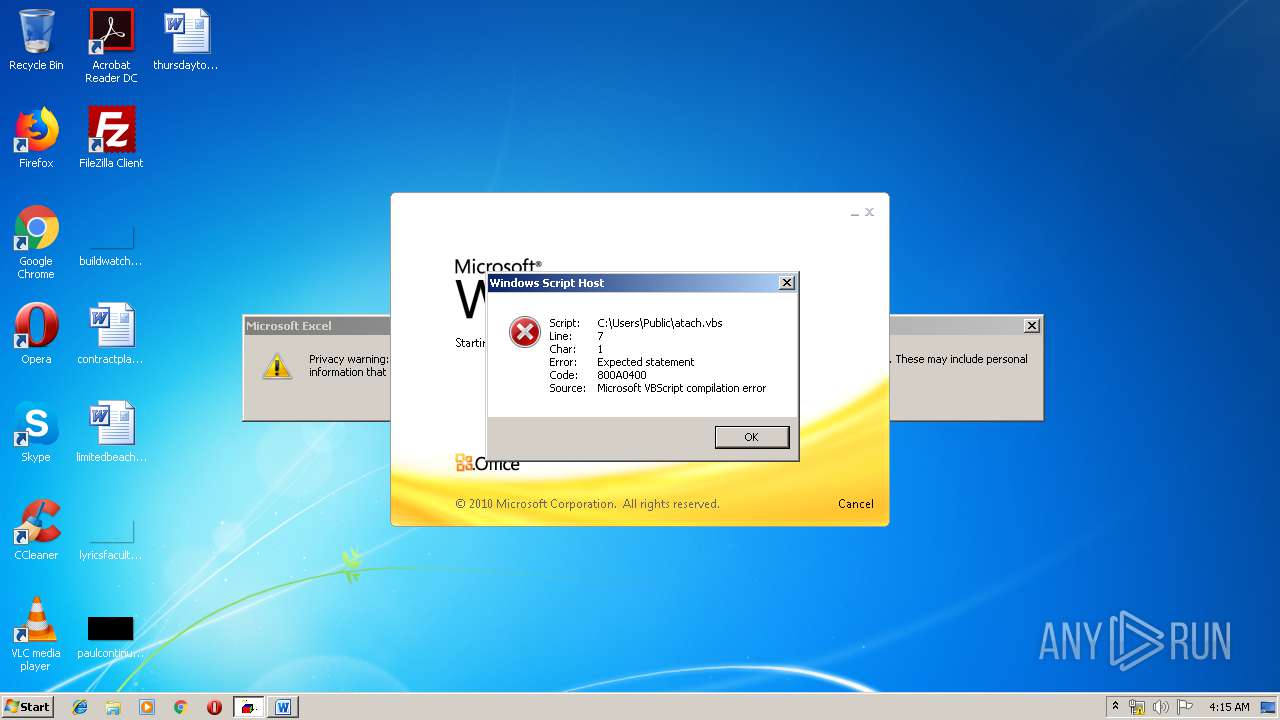
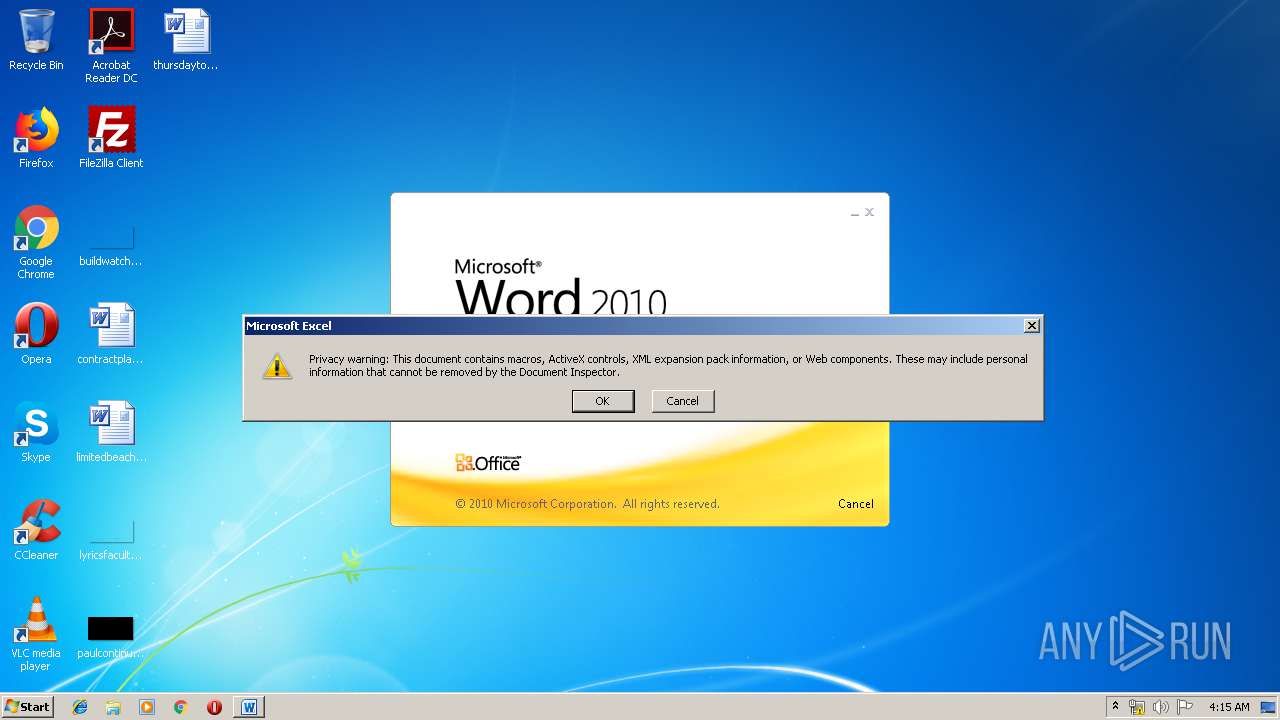
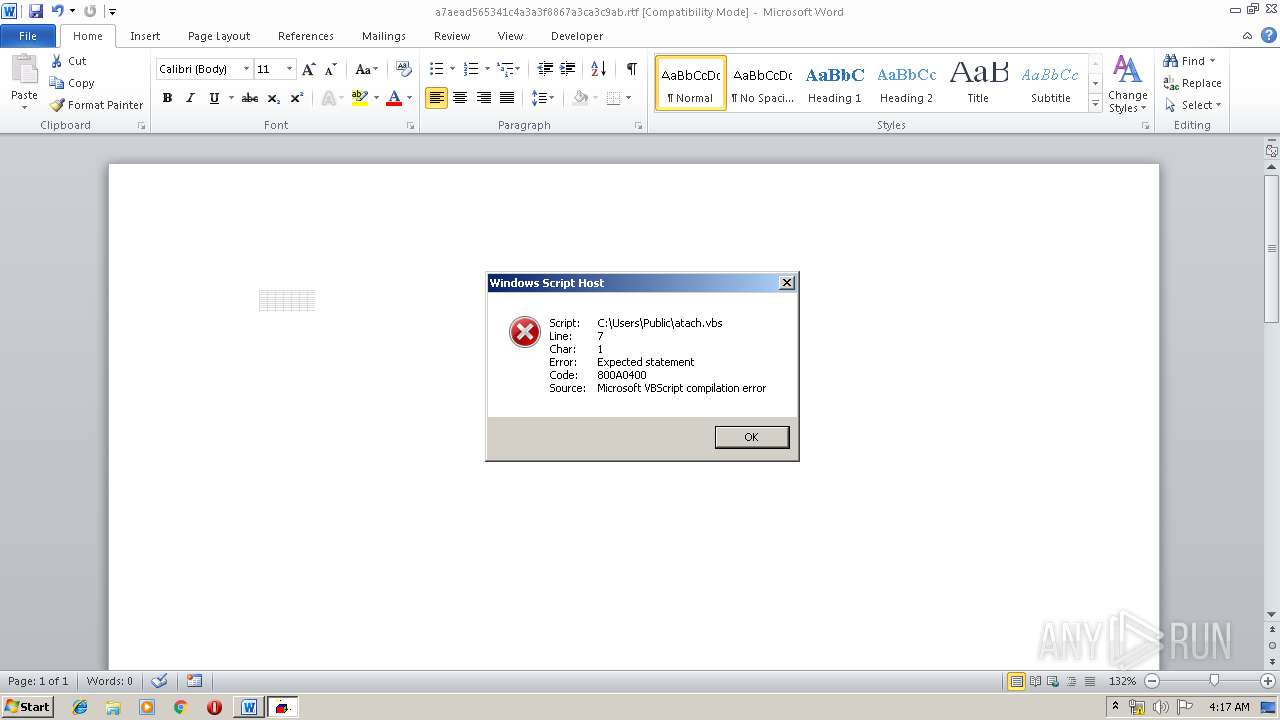
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3192)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3648)
- cmd.exe (PID: 3600)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3976)
- EXCEL.EXE (PID: 1324)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3976)
- EXCEL.EXE (PID: 1324)
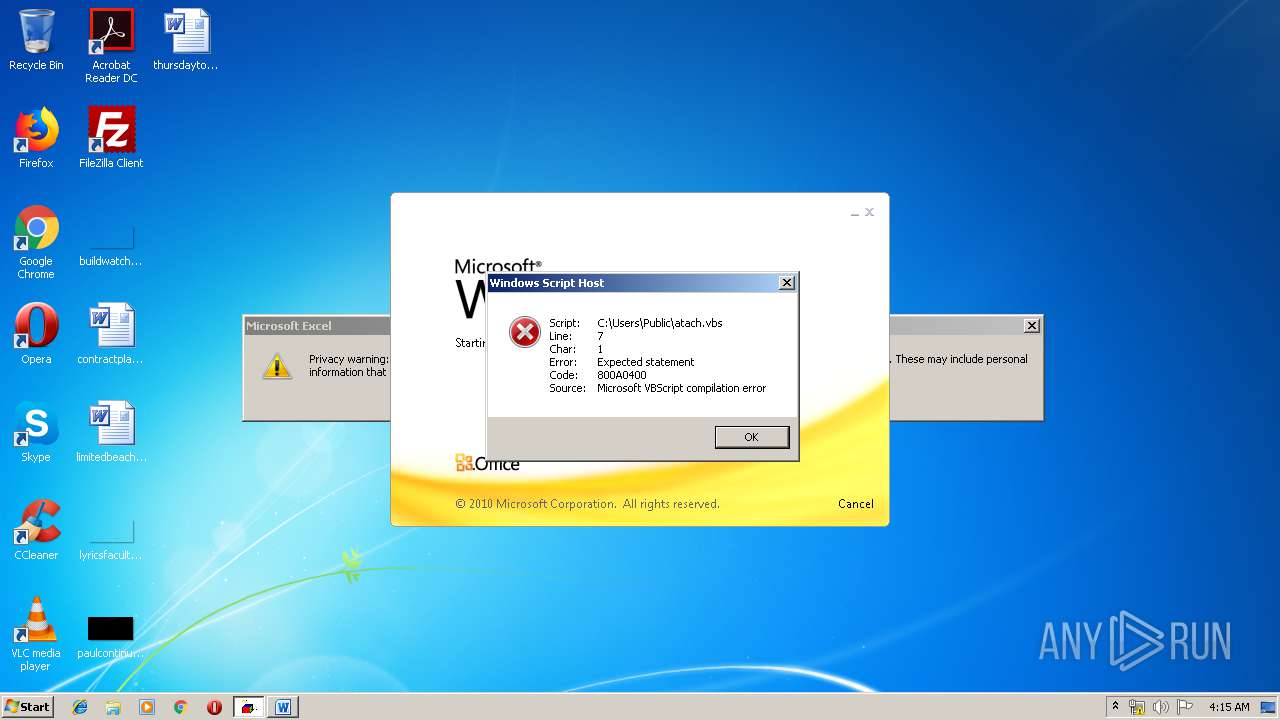
Application was dropped or rewritten from another process
- WScript.exe (PID: 3344)
- WScript.exe (PID: 3448)
- amsi.dll (PID: 1860)
- WScript.exe (PID: 2648)
- WScript.exe (PID: 3080)
- amsi.dll (PID: 3724)
Loads dropped or rewritten executable
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3192)
- svchost.exe (PID: 844)
- SearchProtocolHost.exe (PID: 1992)
- WScript.exe (PID: 3344)
- explorer.exe (PID: 292)
- cmd.exe (PID: 3648)
- cmd.exe (PID: 3600)
- WScript.exe (PID: 3080)
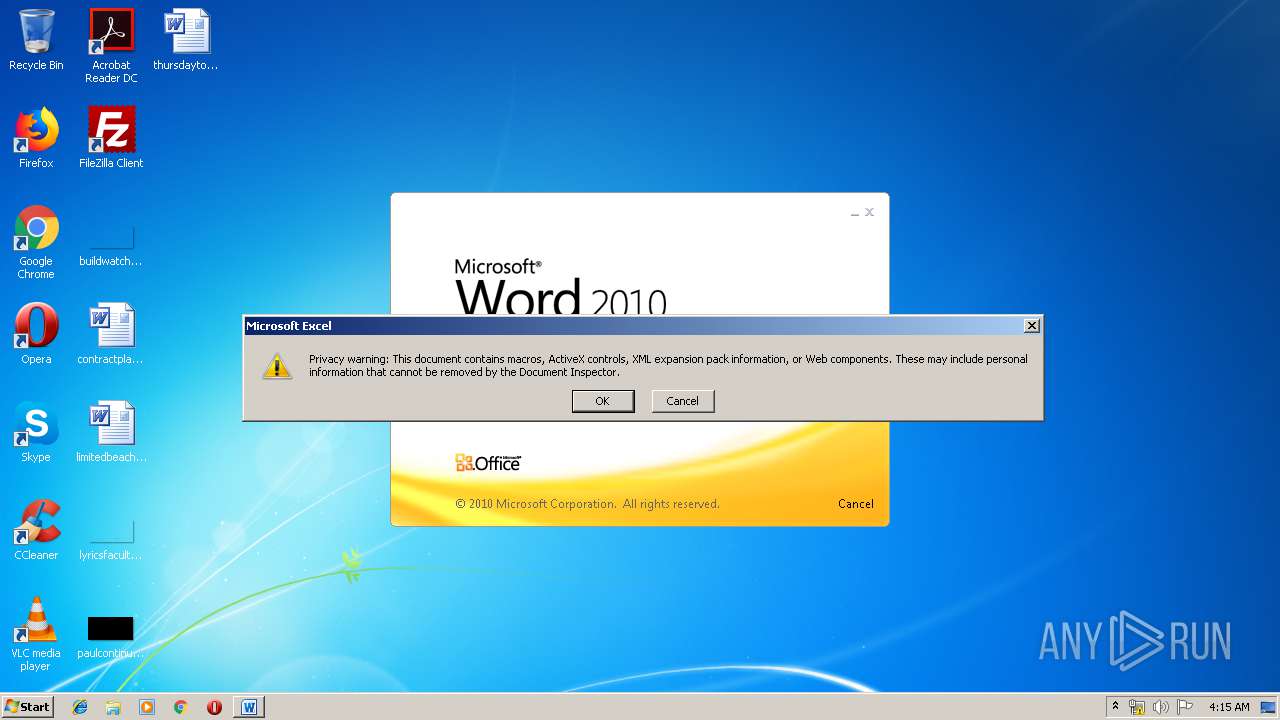
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 3976)
- excelcnv.exe (PID: 1632)
- EXCEL.EXE (PID: 1324)
Executes scripts
- cmd.exe (PID: 3192)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3648)
- cmd.exe (PID: 3600)
Starts application with an unusual extension
- WScript.exe (PID: 3344)
- WScript.exe (PID: 3080)
Starts itself from another location
- WScript.exe (PID: 3344)
Executable content was dropped or overwritten
- WScript.exe (PID: 3344)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3976)
- WINWORD.EXE (PID: 3684)
- excelcnv.exe (PID: 1632)
- EXCEL.EXE (PID: 1324)
Creates files in the user directory
- WINWORD.EXE (PID: 3684)
- EXCEL.EXE (PID: 3976)
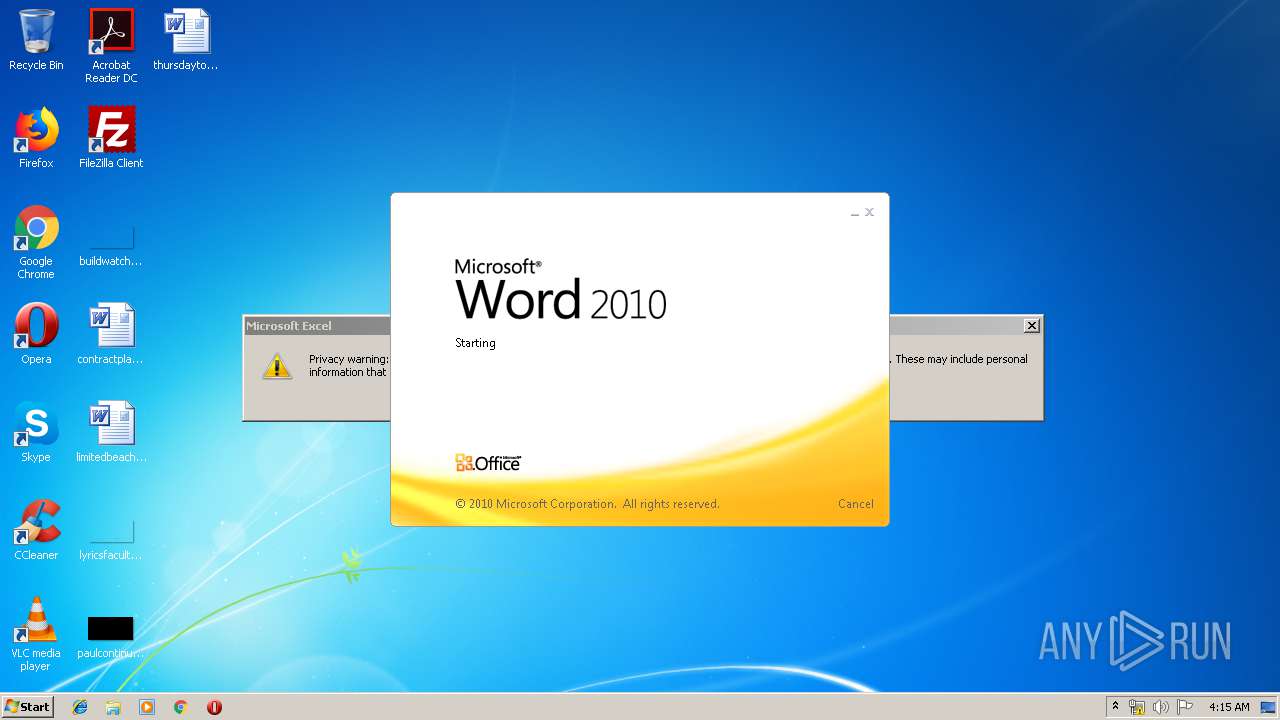
Starts Microsoft Office Application
- explorer.exe (PID: 292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Karla |
|---|---|
| LastModifiedBy: | Karla |
| CreateDate: | 2019:06:16 21:51:00 |
| ModifyDate: | 2019:06:16 21:53:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | 2 minutes |
| Pages: | 1 |
| Words: | 6 |
| Characters: | 34 |
| CharactersWithSpaces: | 39 |
| InternalVersionNumber: | 57433 |
Total processes
60
Monitored processes
21
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 844 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1356 | ping 127.0.0.1 -n 5 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Microsoft Office\Office14\excelcnv.exe" -Embedding | C:\Program Files\Microsoft Office\Office14\excelcnv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1860 | "C:\Users\Public\amsi.dll" "C:\Users\Public\atach.vbs" | C:\Users\Public\amsi.dll | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1992 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | ping 127.0.0.1 -n 3 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | ping 127.0.0.1 -n 3 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2648 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\WindowsDefender.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
2 639
Read events
1 764
Write events
859
Delete events
16
Modification events
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8<= |
Value: 383C3D00640E0000010000000000000000000000 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482704 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482705 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 640E000028C206F8163DD50100000000 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n>= |
Value: 6E3E3D00640E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | n>= |
Value: 6E3E3D00640E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3684) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
10
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF8B8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3976 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR182.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3976 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFE4D419492EA3C1DB.TMP | — | |
MD5:— | SHA256:— | |||
| 1632 | excelcnv.exe | C:\Users\admin\AppData\Local\Temp\CVRAD33.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3684 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC914459B483F85A6.TMP | — | |
MD5:— | SHA256:— | |||
| 1324 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRBE9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3976 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\F8W8Pz9Z[1].txt | text | |
MD5:— | SHA256:— | |||
| 3976 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@pastebin[1].txt | text | |
MD5:— | SHA256:— | |||
| 3976 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\yvyE642L[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | EXCEL.EXE | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
1860 | amsi.dll | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
1324 | EXCEL.EXE | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
3724 | amsi.dll | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |