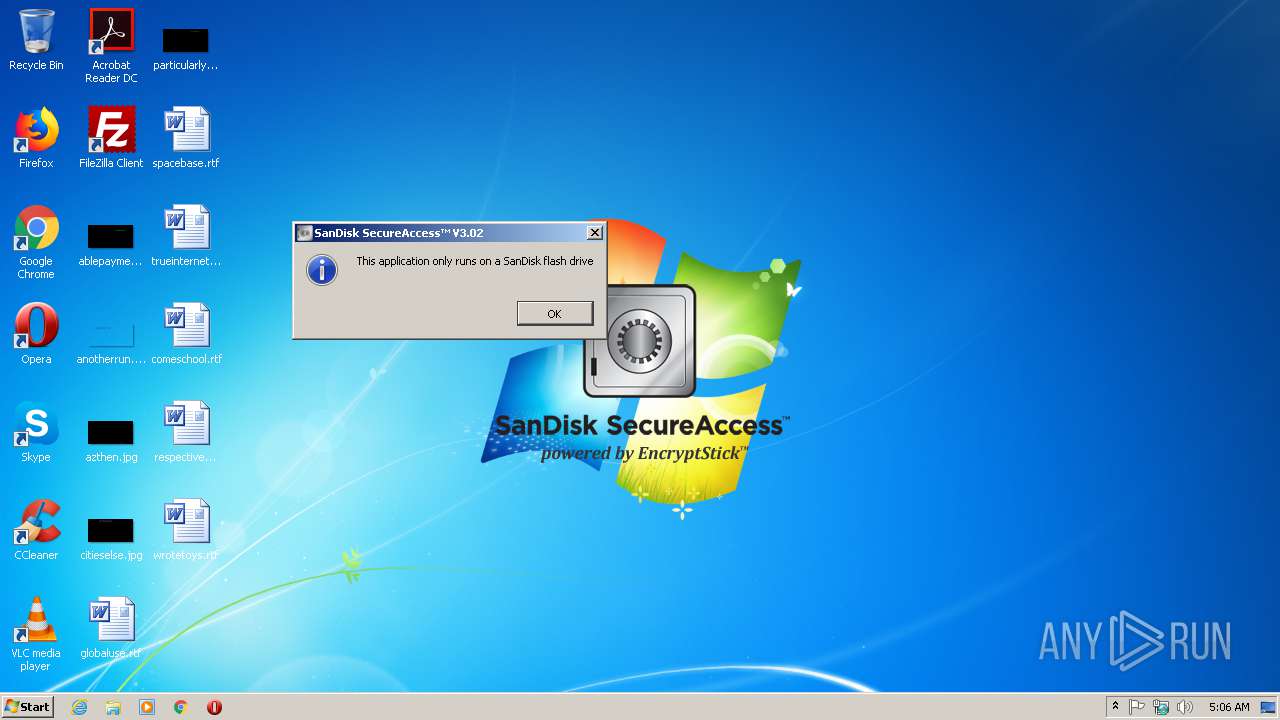
| File name: | SanDiskSecureAccessV3_win.exe |
| Full analysis: | https://app.any.run/tasks/d5757c1a-8cc0-463a-982f-e5e4e0107d90 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 04:05:48 |
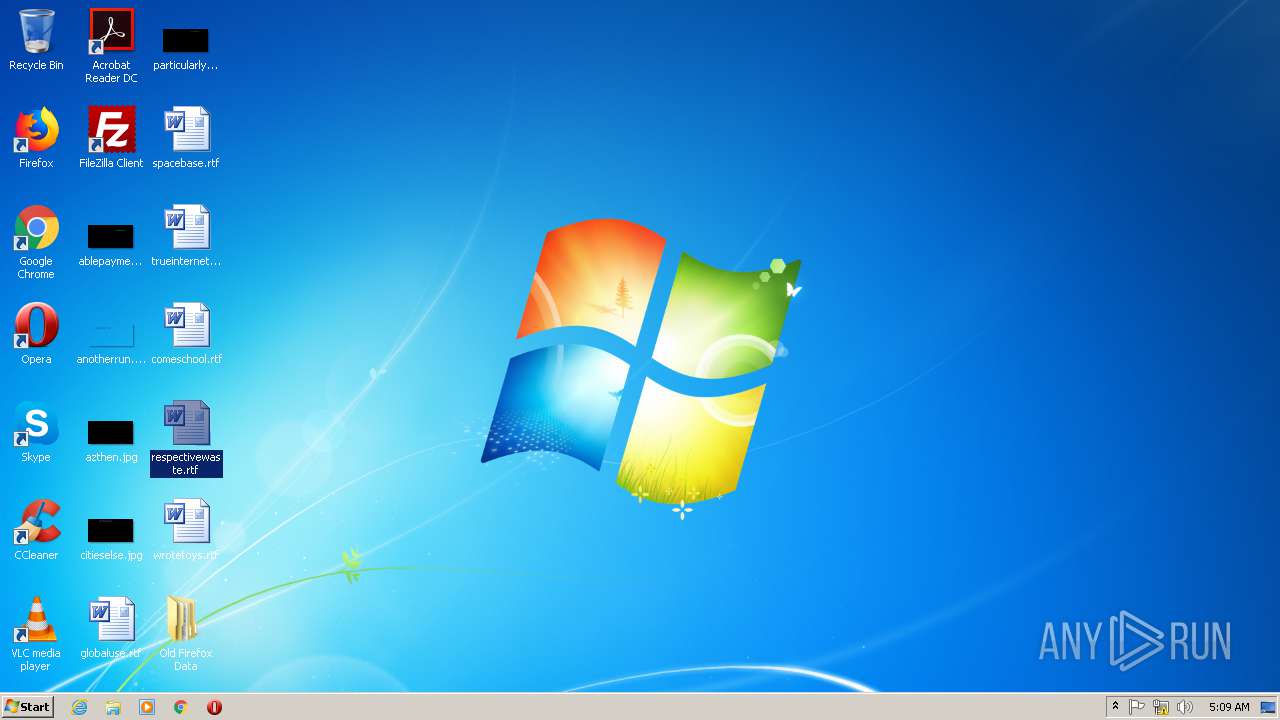
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | BBC9D55498594BB8A7C825E4D8644769 |
| SHA1: | CD09C3EDA7B22214D6013B6C631584F084137E10 |
| SHA256: | A2D3ACDC6C04E9C37AE9A609D4129486D742DE85350773E62BEF3A3493088426 |
| SSDEEP: | 196608:Z937CQTytLjGZBlCHsv2EYyjsS2xWgYS9FCRGtCLOOJAs0tQZcz:ZAQTyt3K8Hs+EJjBIWgD9FC86OMW |
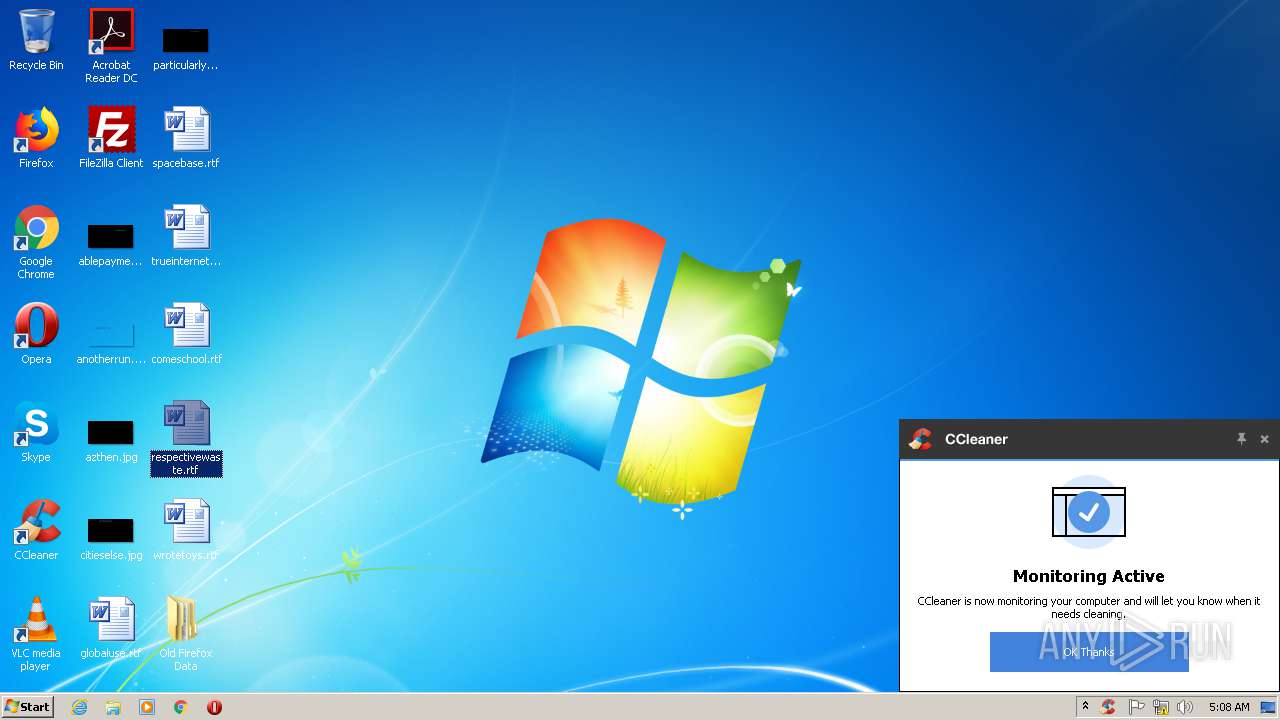
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2208)
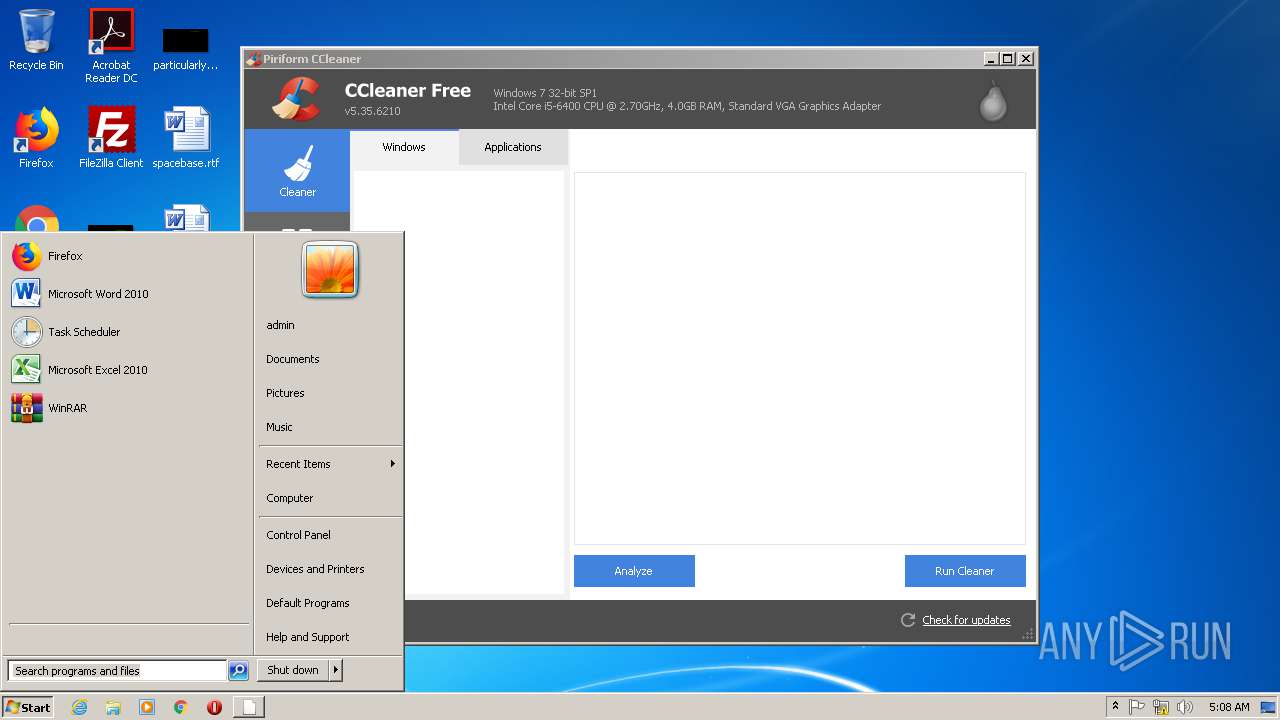
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2964)
- CCleaner.exe (PID: 1588)
- CCleaner.exe (PID: 2184)
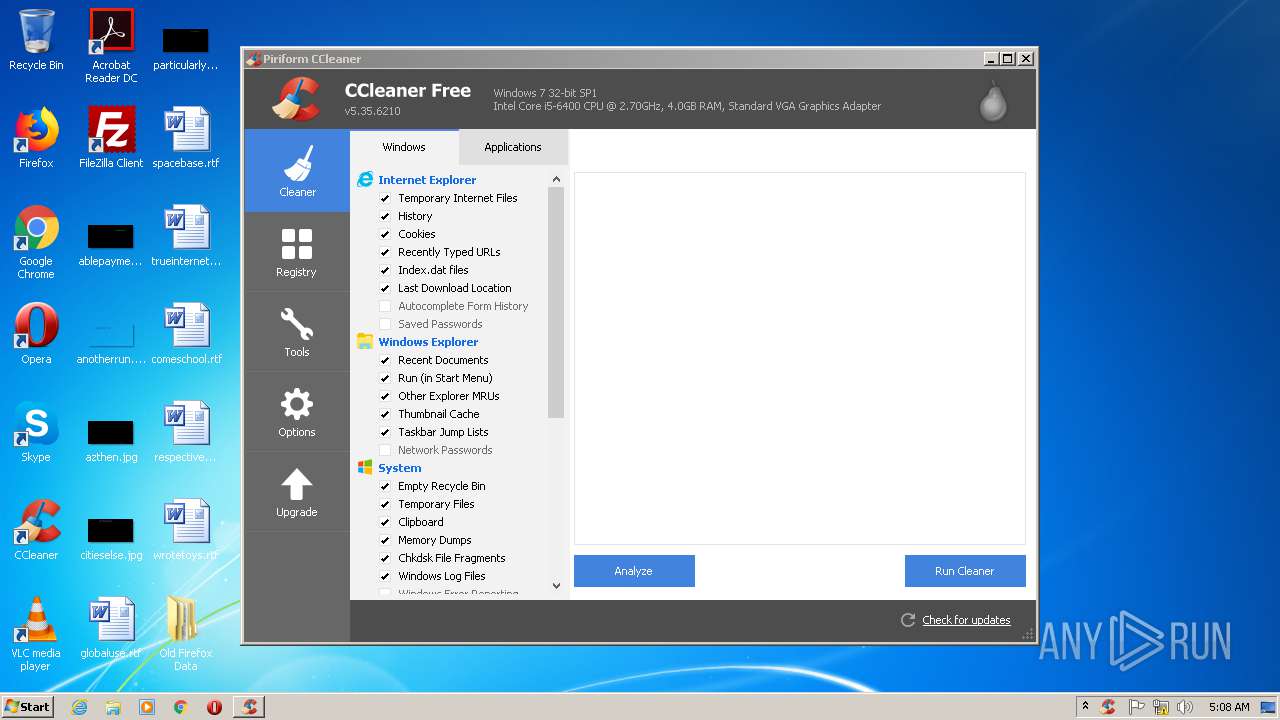
Changes the autorun value in the registry
- CCleaner.exe (PID: 2184)
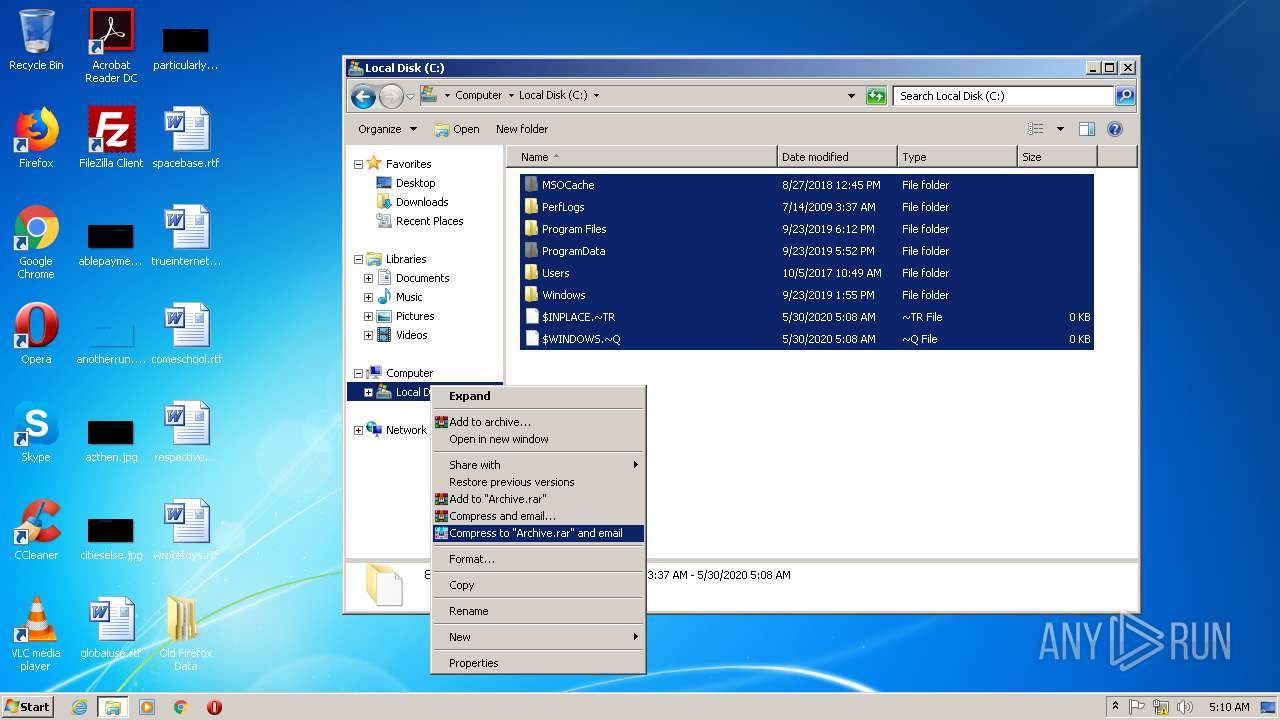
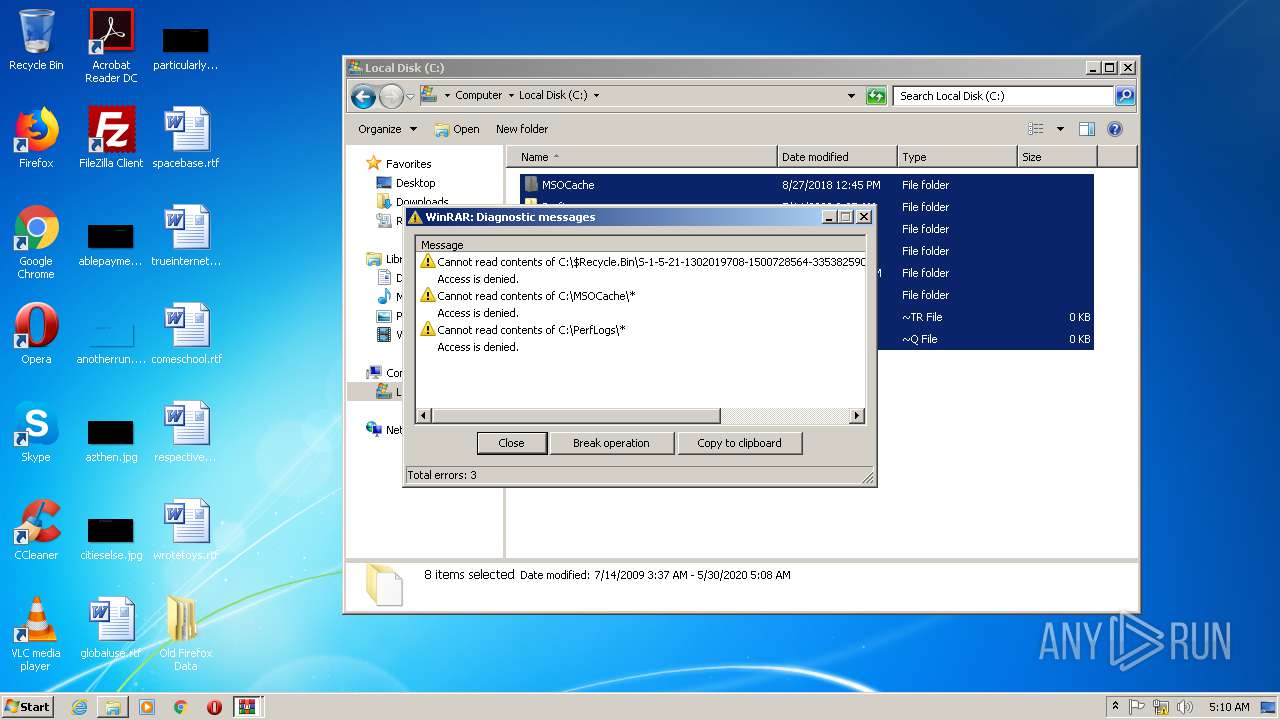
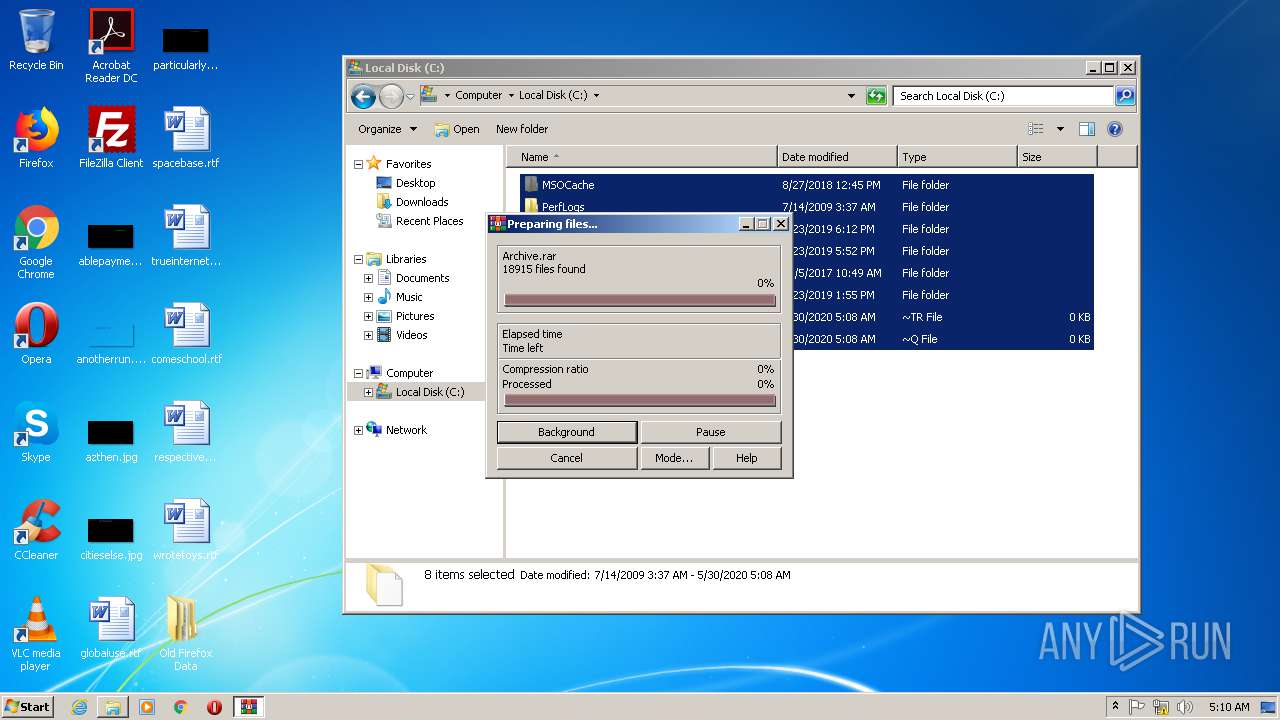
Actions looks like stealing of personal data
- CCleaner.exe (PID: 1588)
- CCleaner.exe (PID: 2184)
- WinRAR.exe (PID: 2772)
Changes settings of System certificates
- CCleaner.exe (PID: 1588)
SUSPICIOUS
Creates files in the program directory
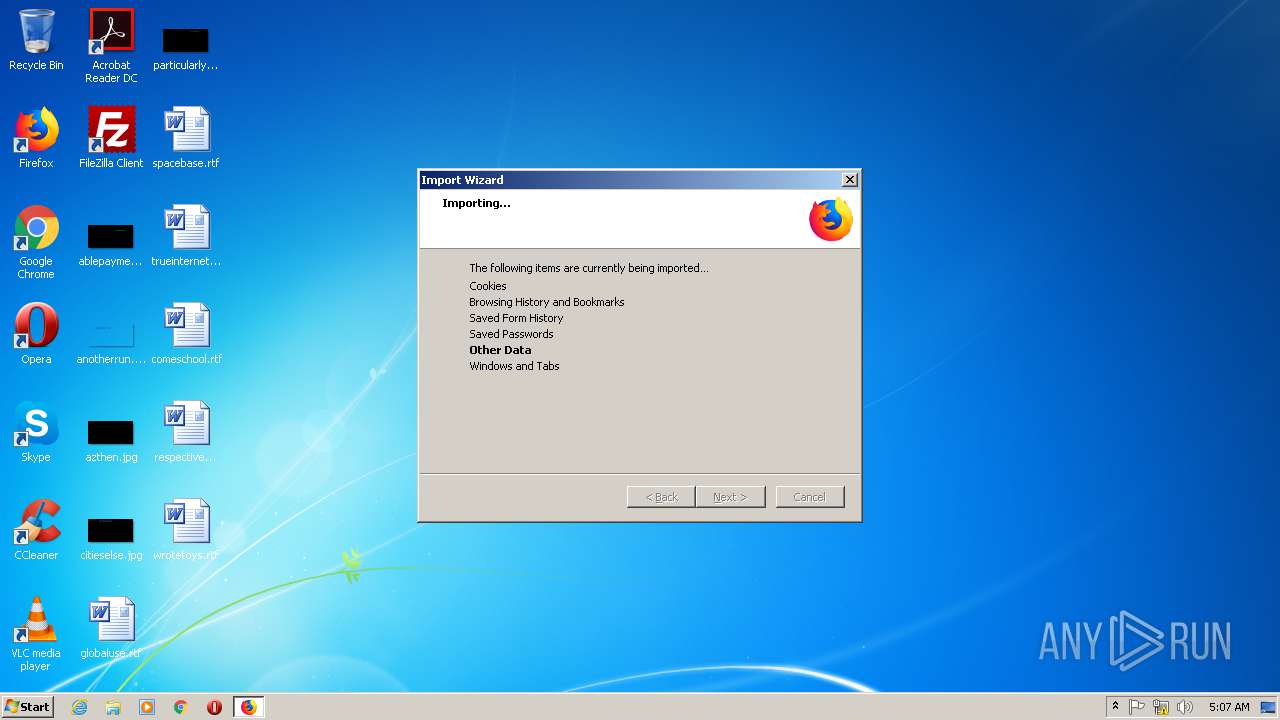
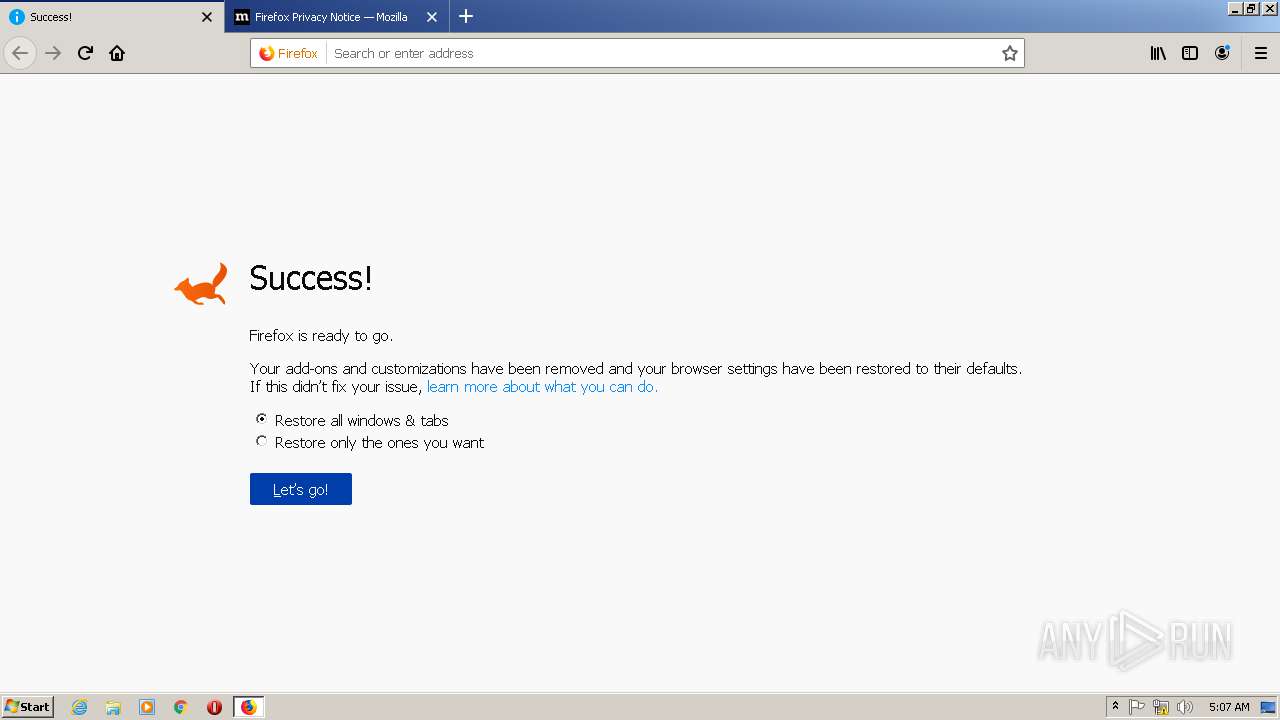
- firefox.exe (PID: 2664)
- firefox.exe (PID: 2192)
Executable content was dropped or overwritten
- firefox.exe (PID: 2664)
Executed as Windows Service
- taskhost.exe (PID: 3908)
Creates files in the user directory
- CCleaner.exe (PID: 1588)
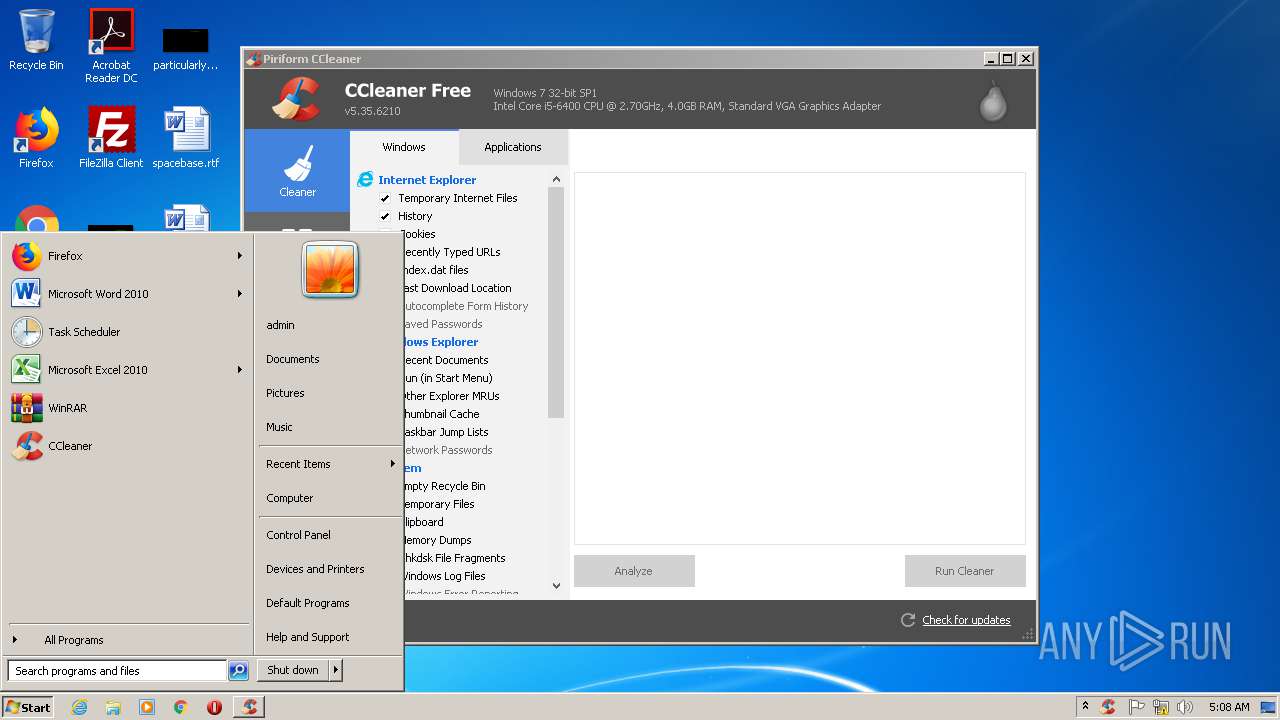
Reads internet explorer settings
- CCleaner.exe (PID: 1588)
- CCleaner.exe (PID: 2184)
Executed via Task Scheduler
- CCleaner.exe (PID: 1588)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 1588)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 1588)
Reads Internet Cache Settings
- CCleaner.exe (PID: 1588)
- taskhost.exe (PID: 3908)
Application launched itself
- CCleaner.exe (PID: 1588)
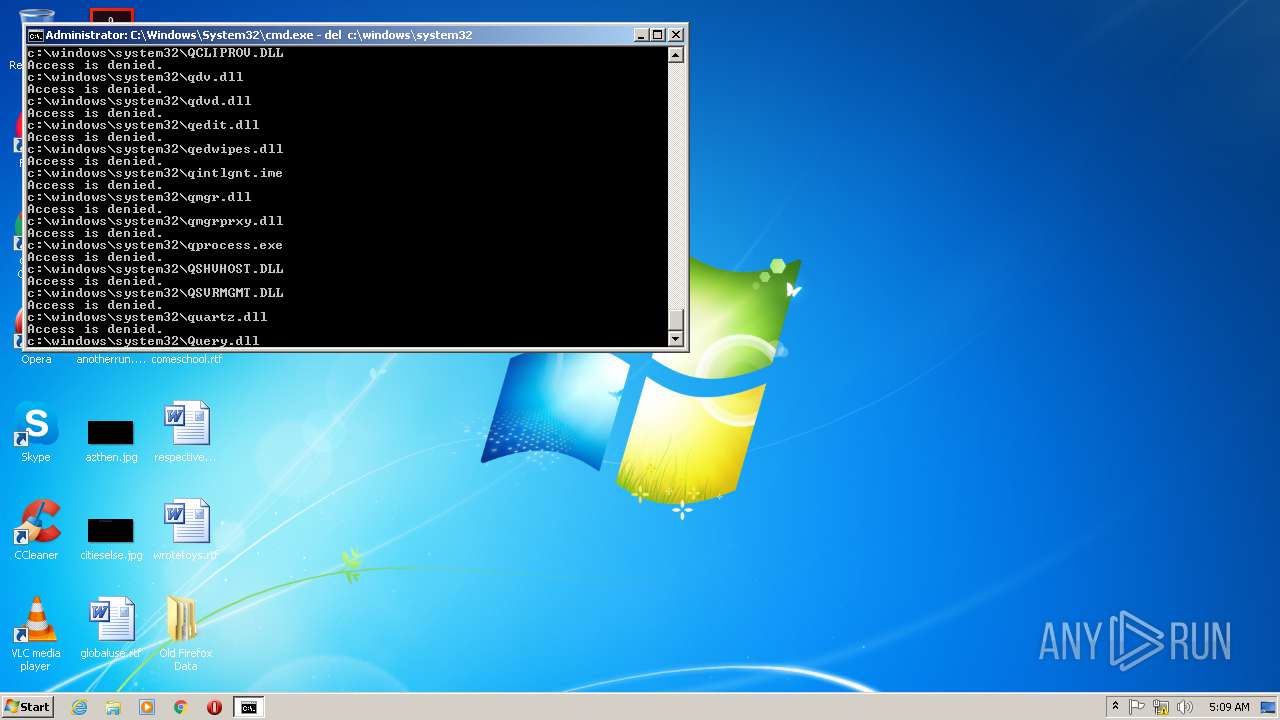
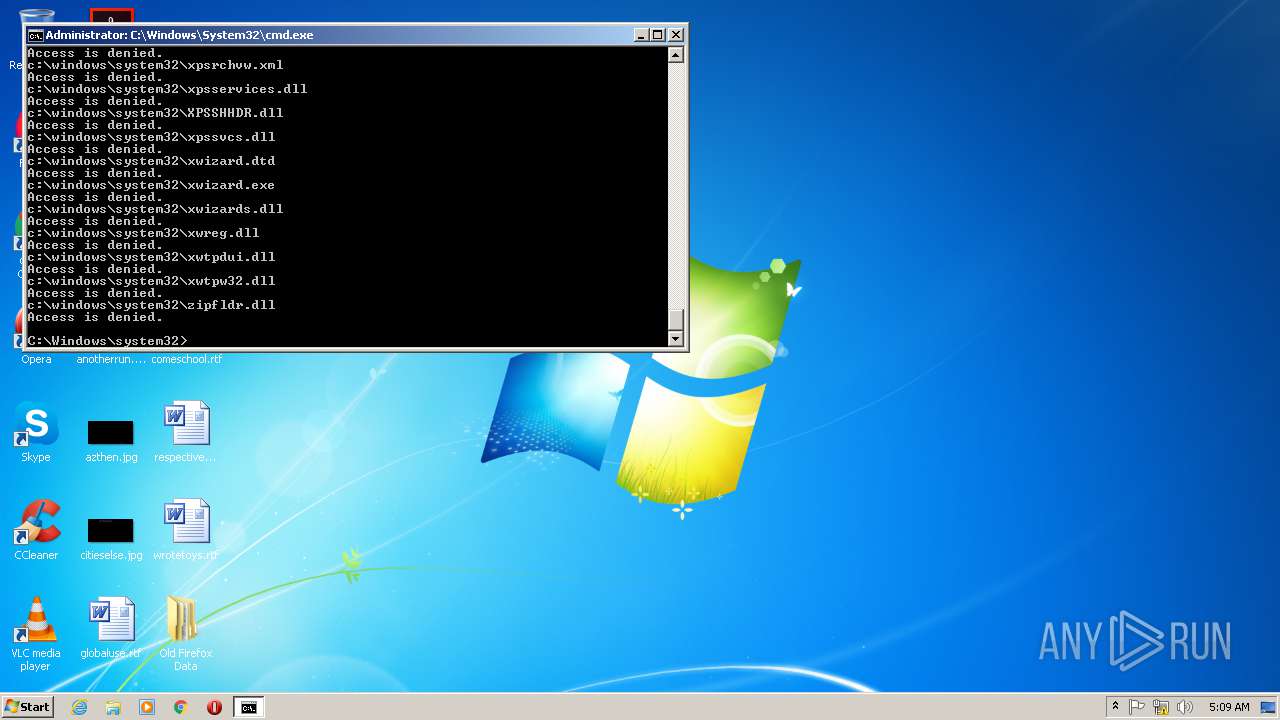
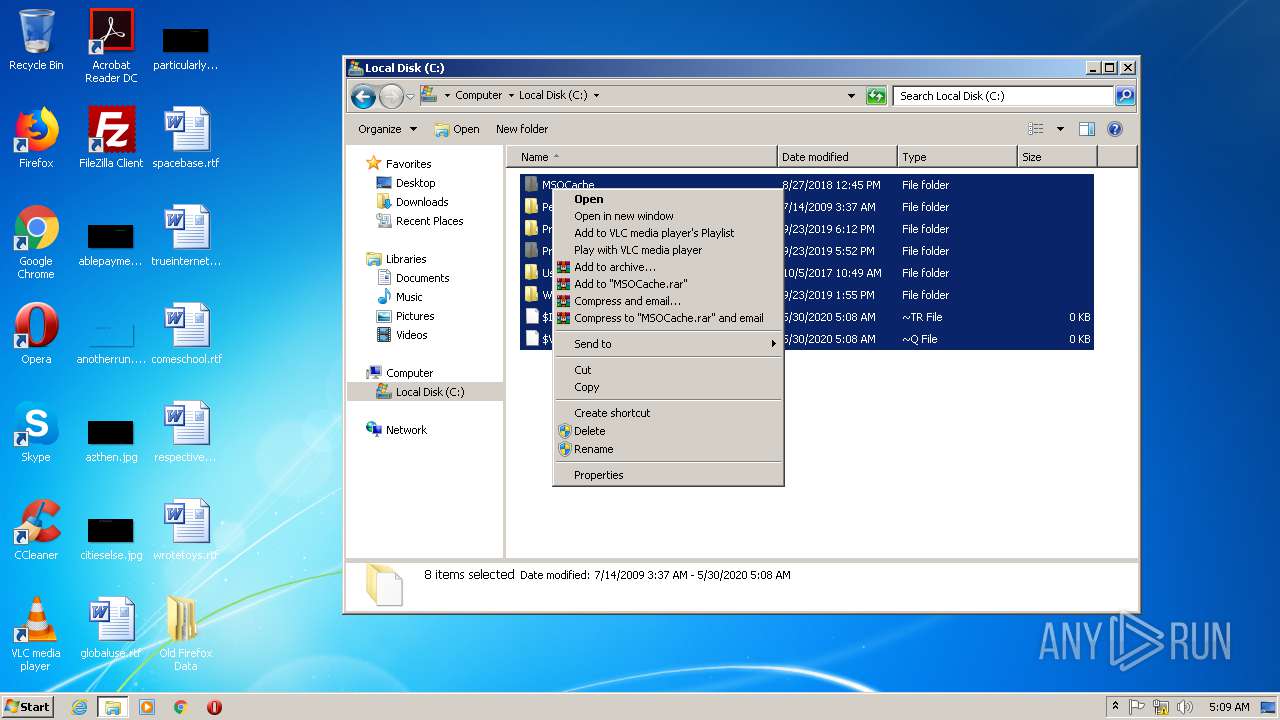
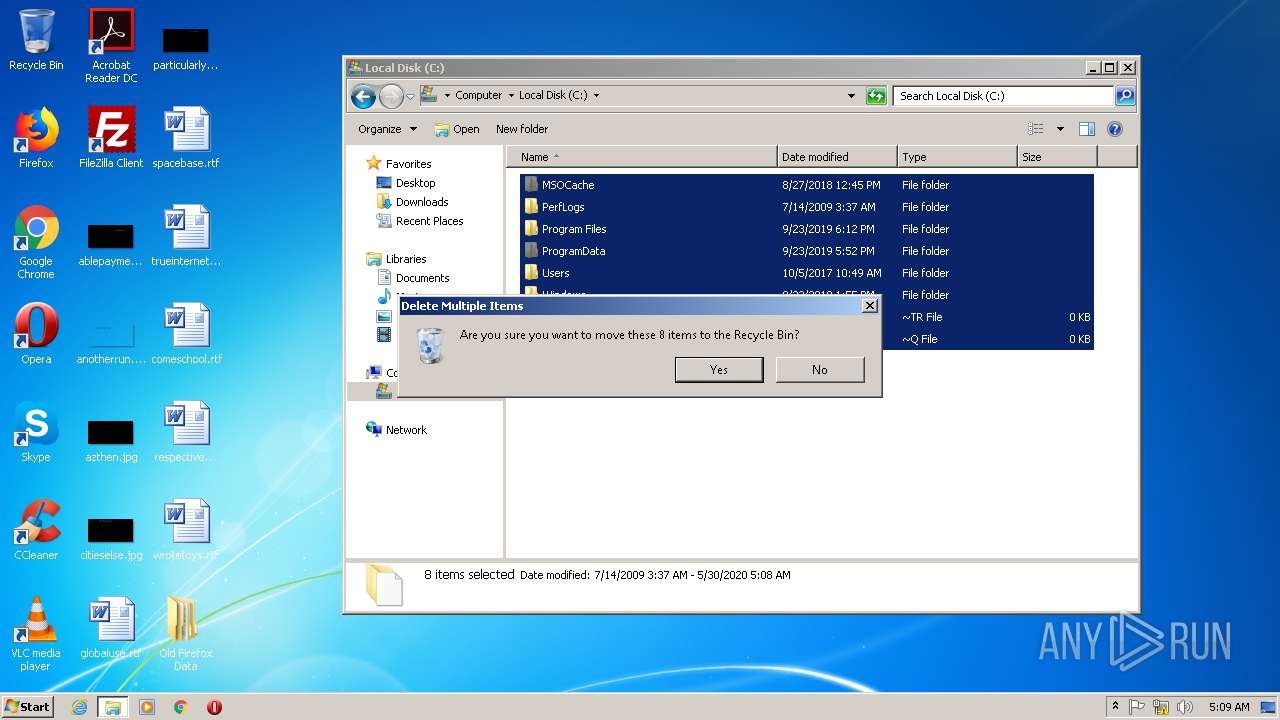
Removes files from Windows directory
- cmd.exe (PID: 312)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 1588)
INFO
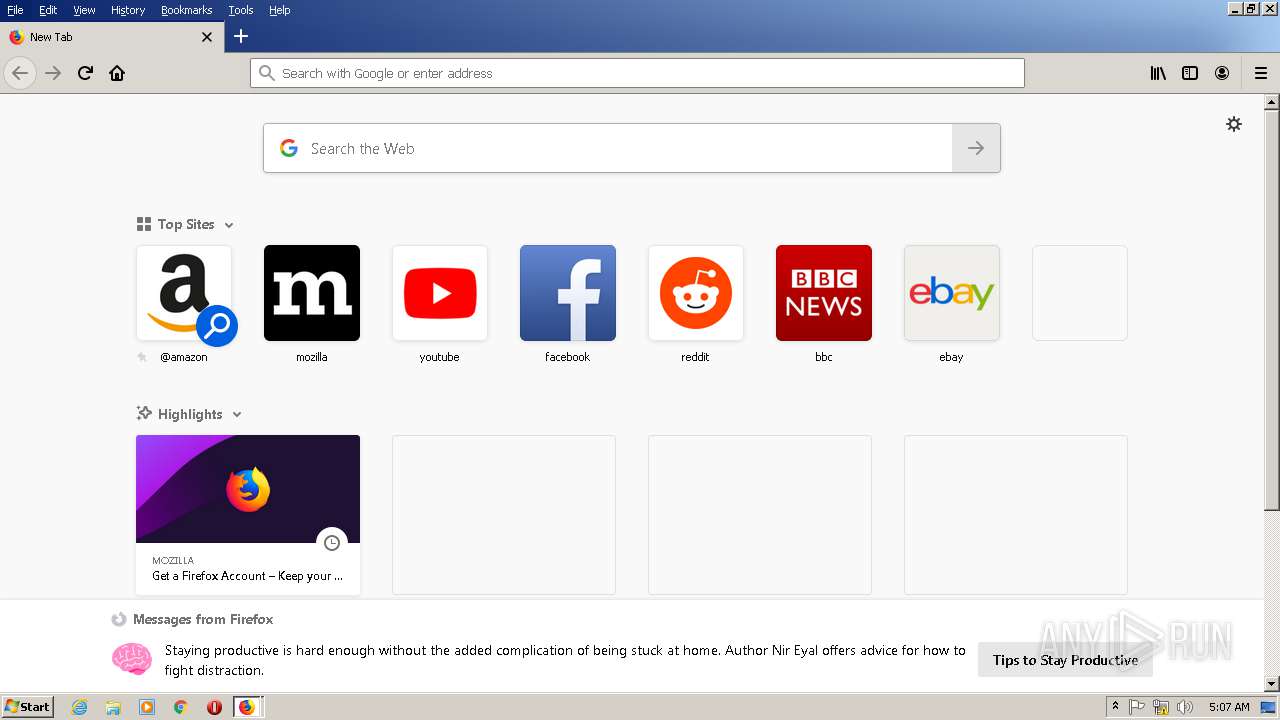
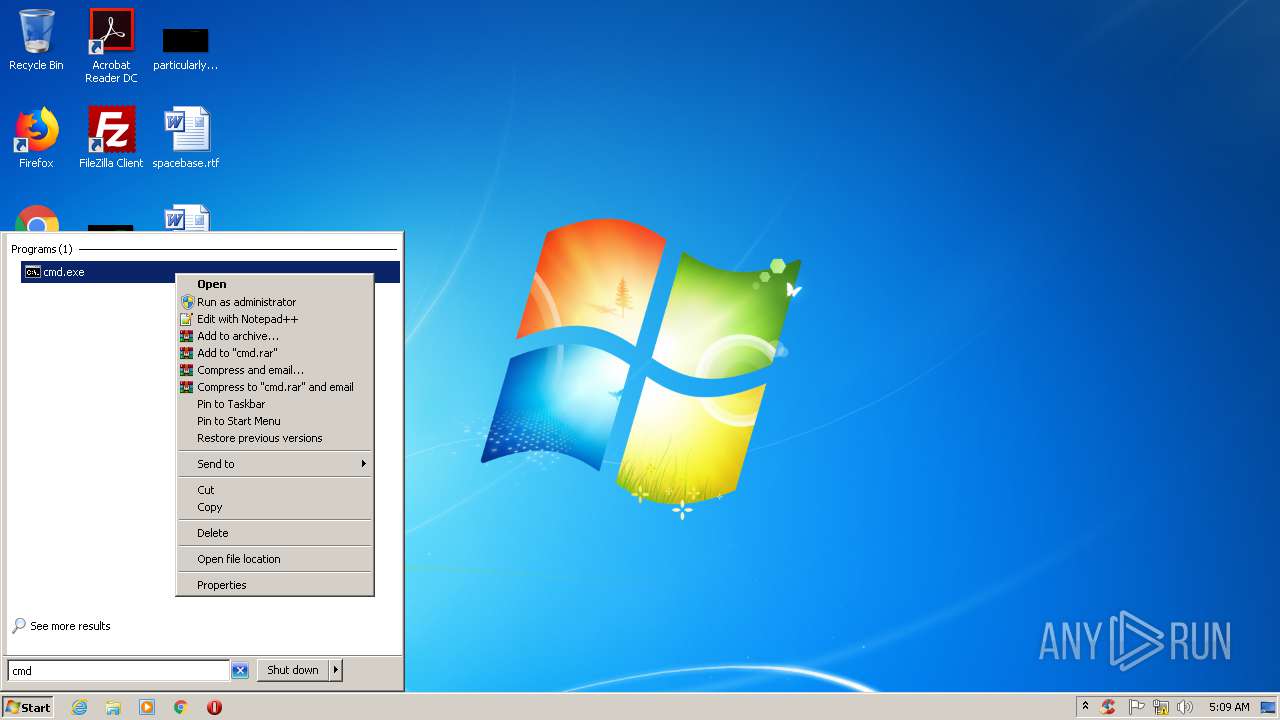
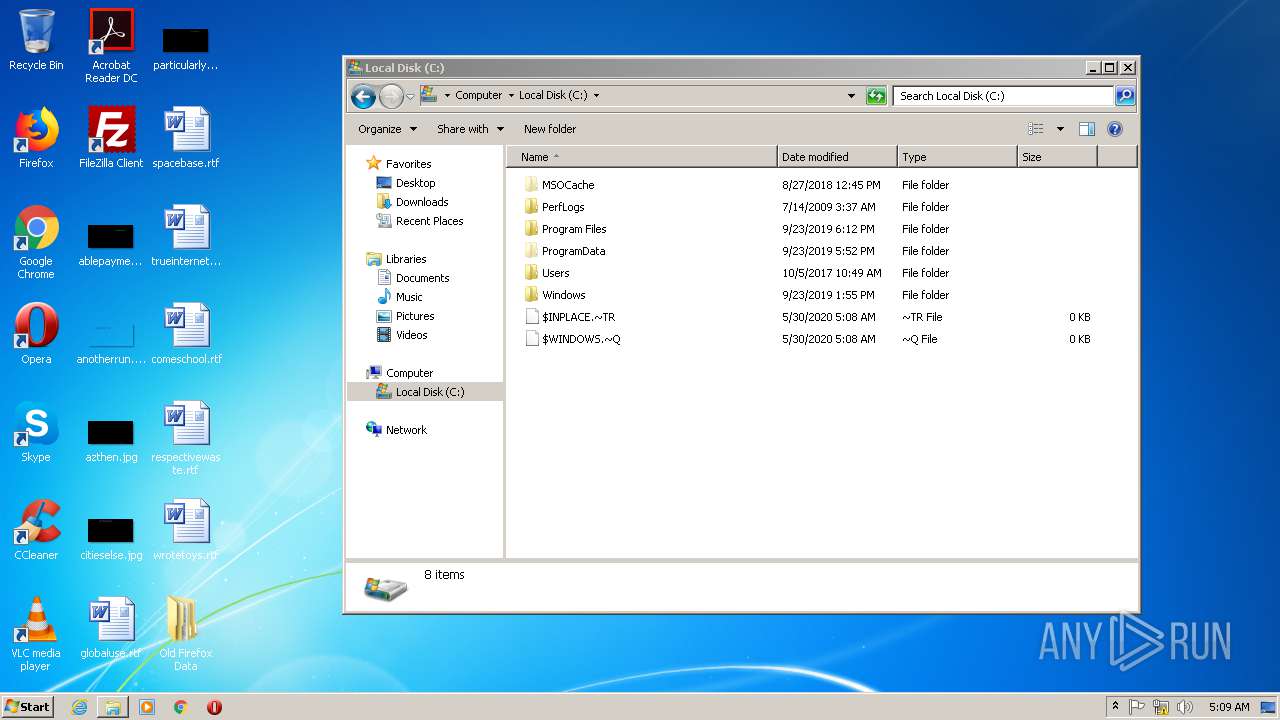
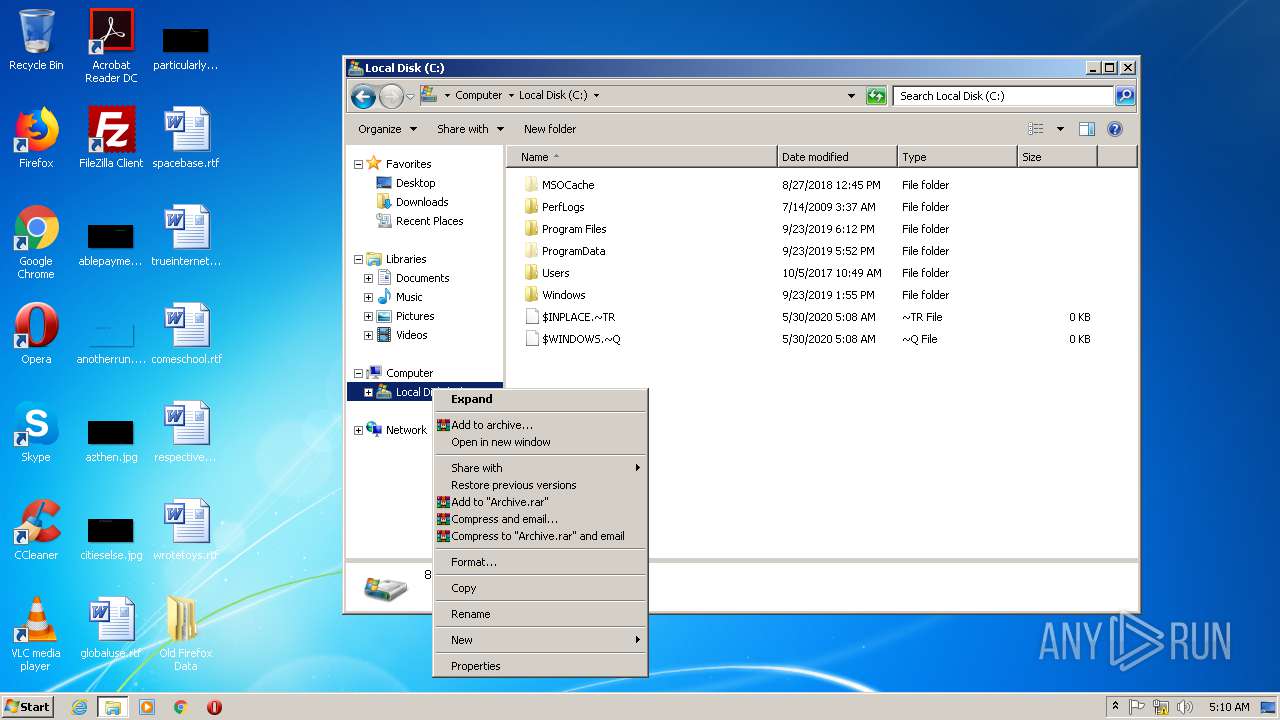
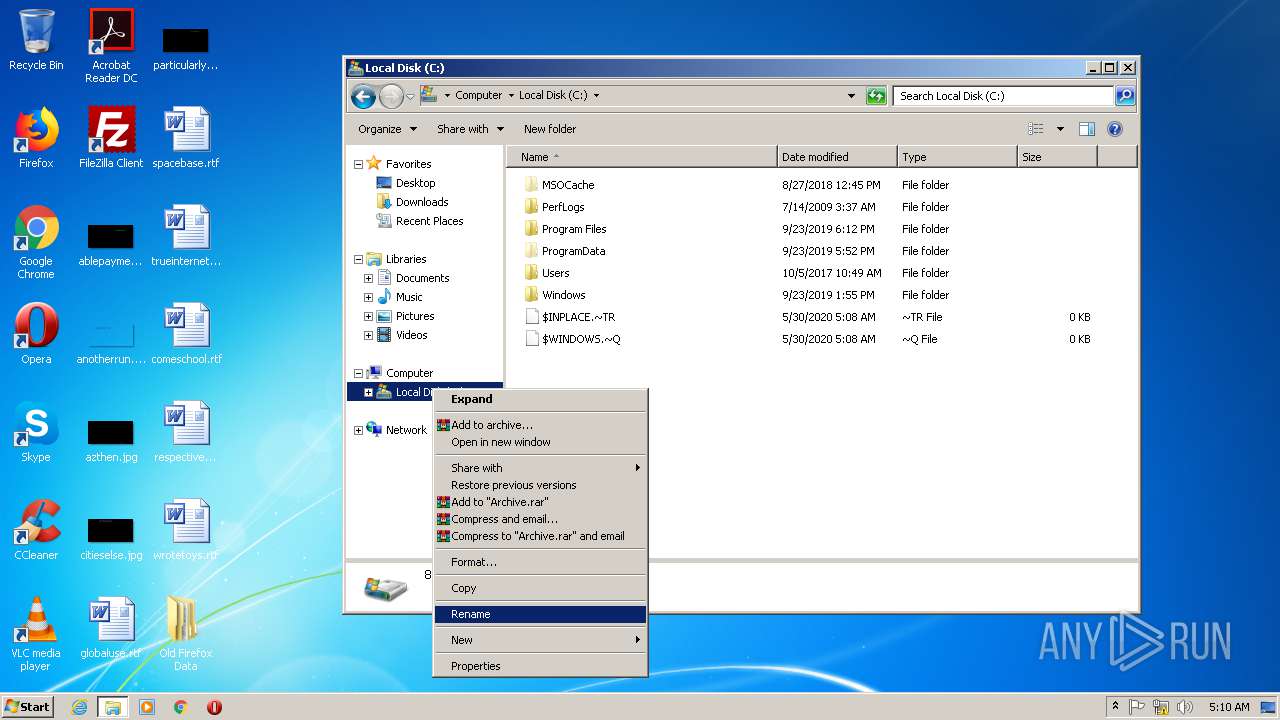
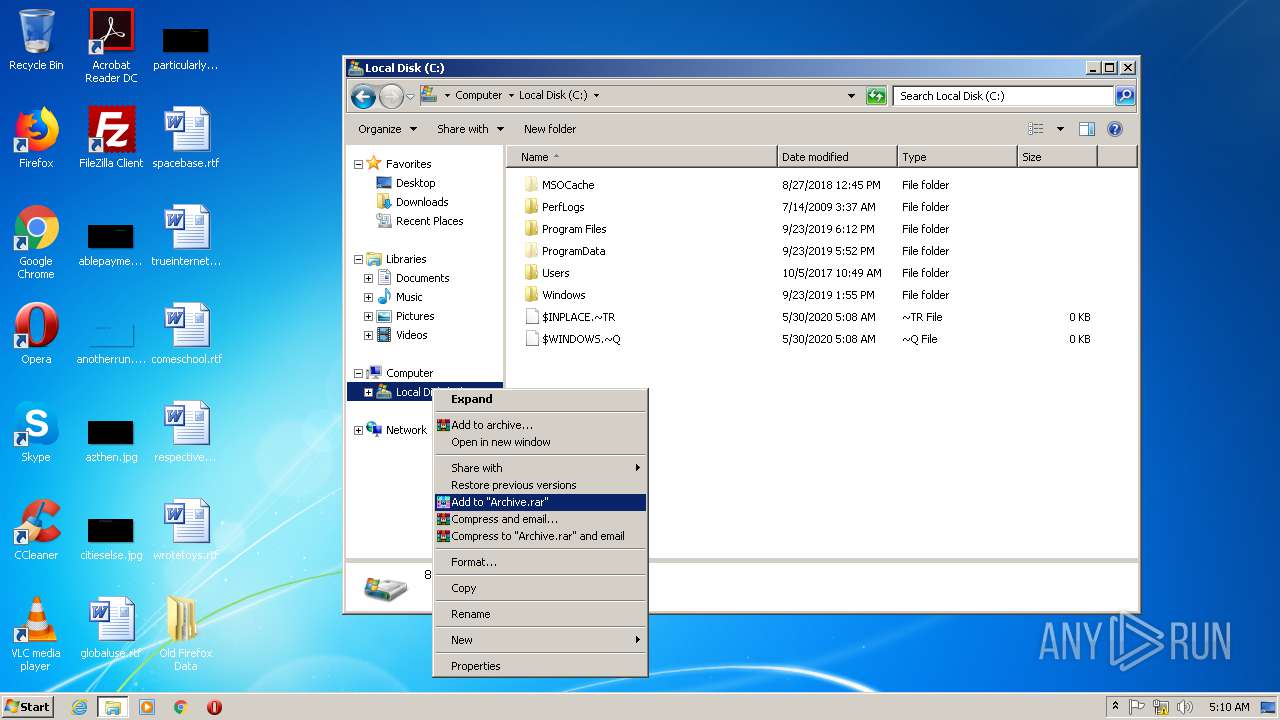
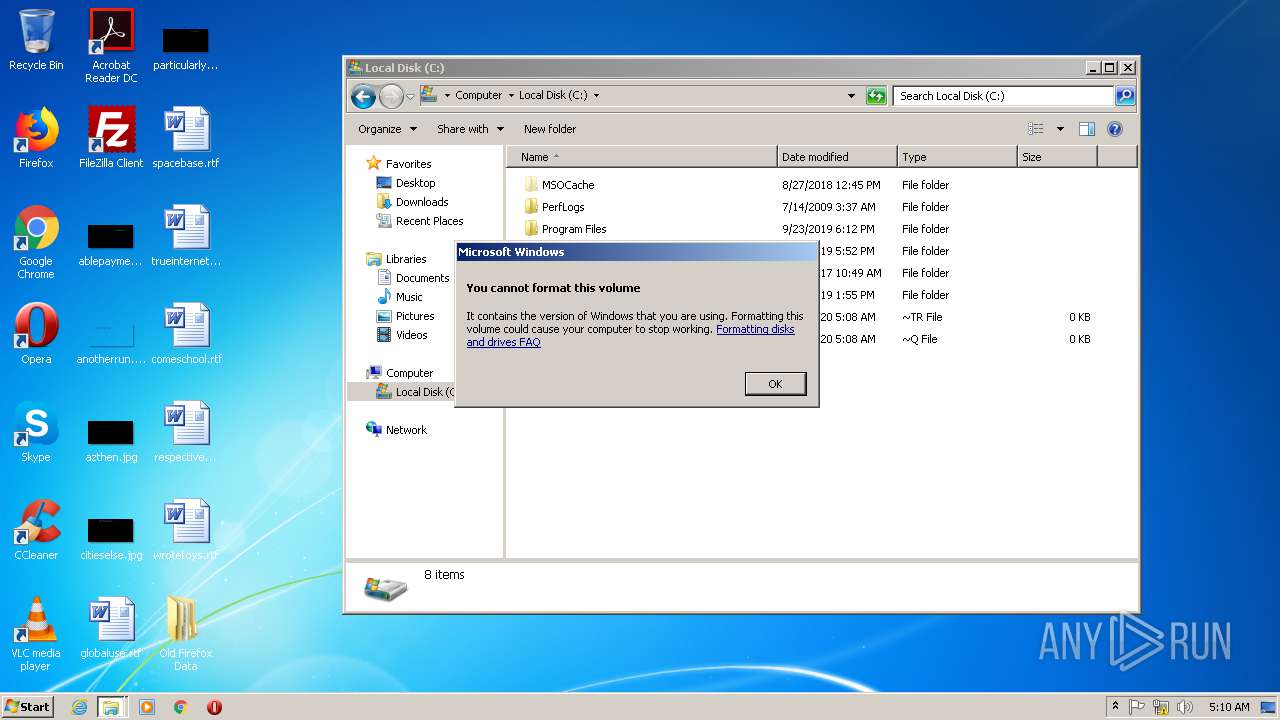
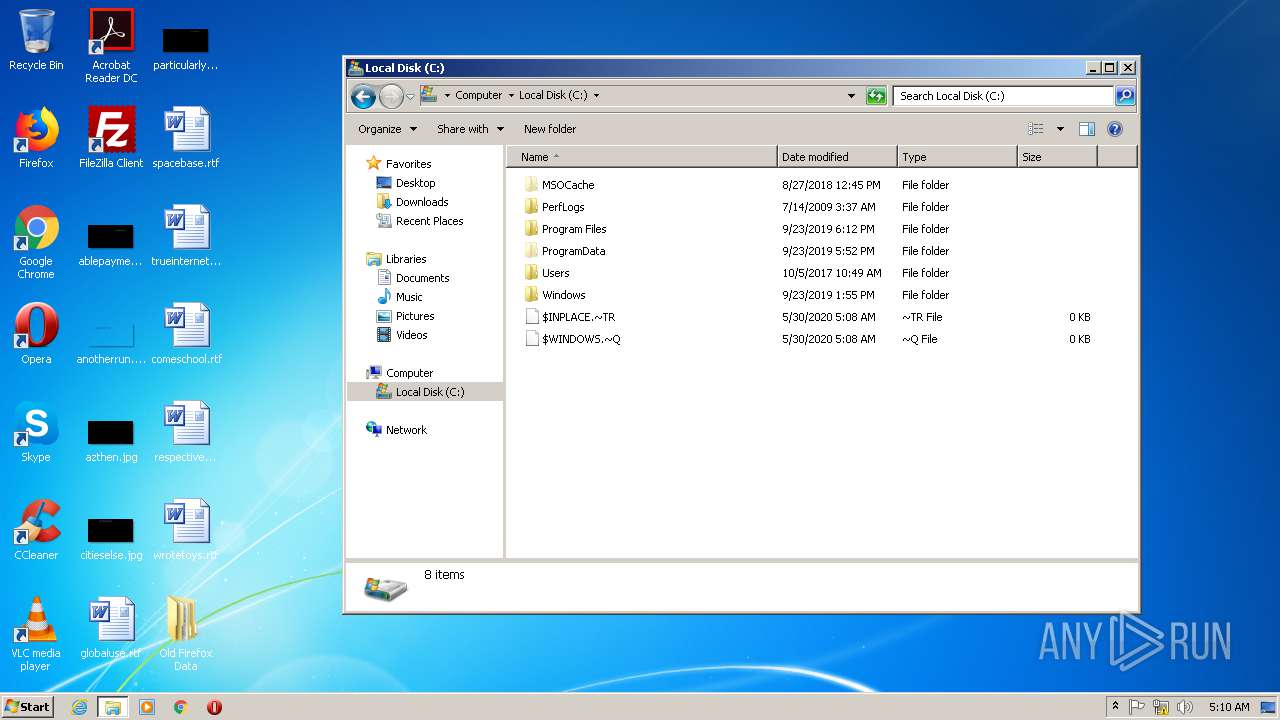
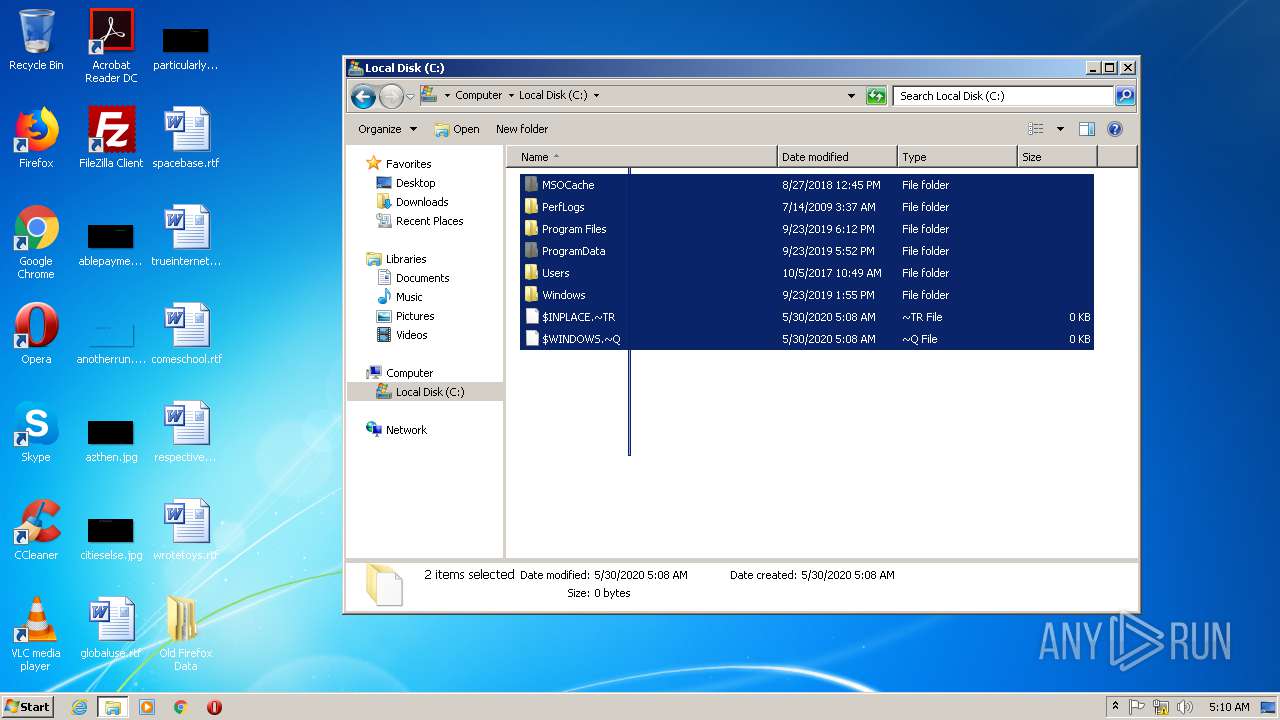
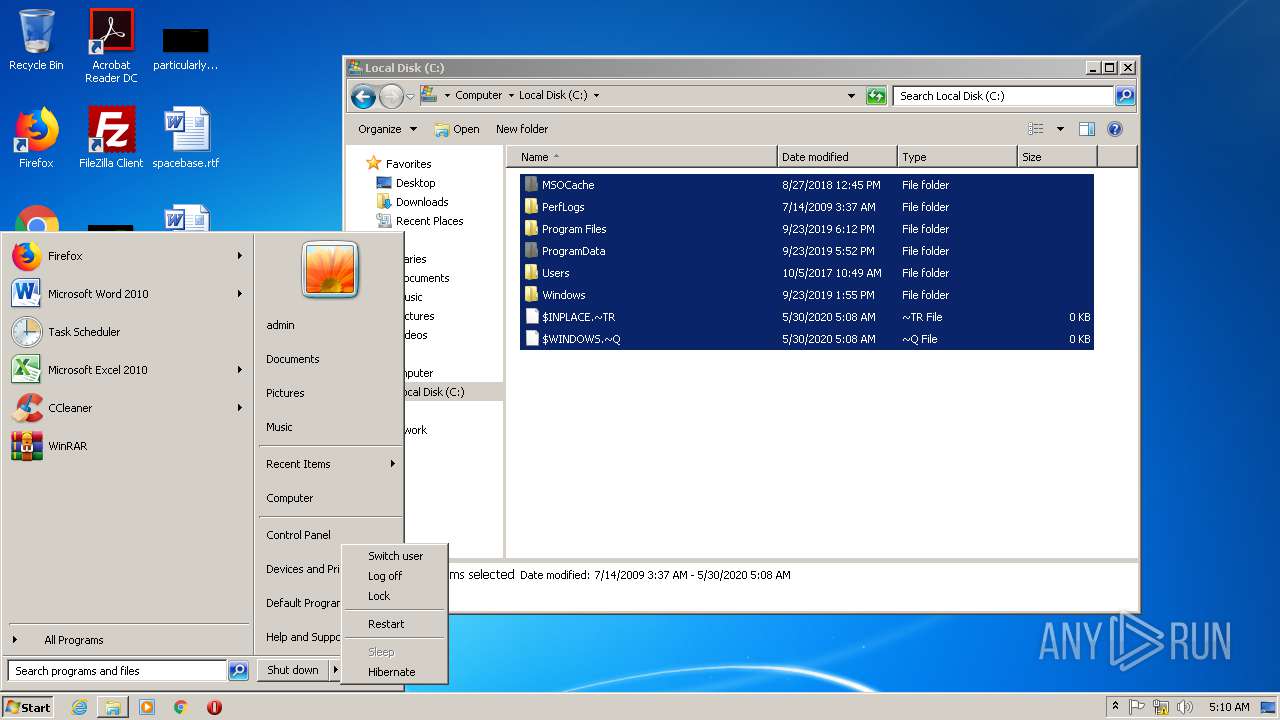
Manual execution by user
- firefox.exe (PID: 4076)
- CCleaner.exe (PID: 2964)
- cmd.exe (PID: 312)
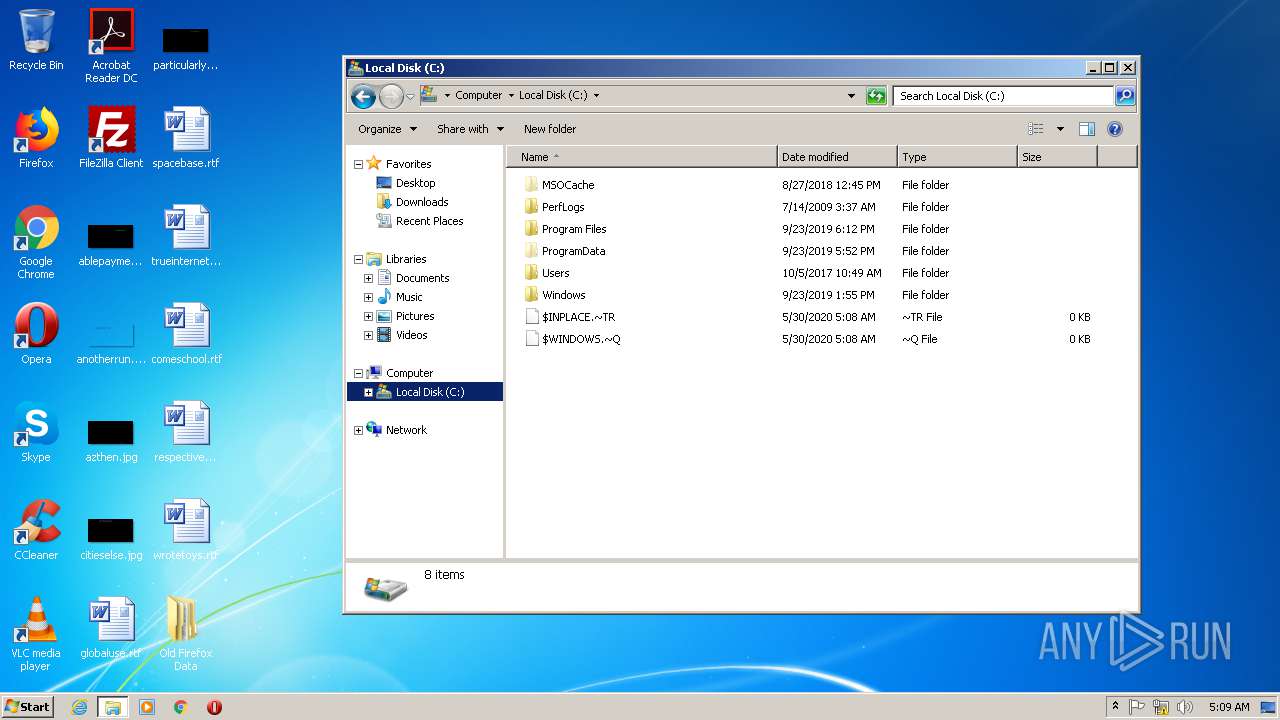
- explorer.exe (PID: 2152)
- WinRAR.exe (PID: 2772)
Application launched itself
- firefox.exe (PID: 2192)
- firefox.exe (PID: 4076)
- firefox.exe (PID: 2664)
Reads CPU info
- firefox.exe (PID: 2192)
- firefox.exe (PID: 2664)
Reads Internet Cache Settings
- firefox.exe (PID: 2192)
- pingsender.exe (PID: 3572)
- pingsender.exe (PID: 788)
- firefox.exe (PID: 2664)
- pingsender.exe (PID: 3944)
Reads settings of System Certificates
- pingsender.exe (PID: 3572)
- pingsender.exe (PID: 788)
- pingsender.exe (PID: 3944)
- CCleaner.exe (PID: 1588)
Creates files in the user directory
- firefox.exe (PID: 2192)
- firefox.exe (PID: 2664)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2192)
- firefox.exe (PID: 2664)
Dropped object may contain TOR URL's
- firefox.exe (PID: 2664)
Adds / modifies Windows certificates
- pingsender.exe (PID: 3572)
- pingsender.exe (PID: 788)
- pingsender.exe (PID: 3944)
Changes settings of System certificates
- pingsender.exe (PID: 788)
- pingsender.exe (PID: 3572)
- pingsender.exe (PID: 3944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:15 17:58:53+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 8523776 |
| InitializedDataSize: | 241664 |
| UninitializedDataSize: | 8847360 |
| EntryPoint: | 0x10912c0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.37.0 |
| ProductVersionNumber: | 6.0.37.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ENC Security Systems BV |
| FileDescription: | SanDisk SecureAccessV3 |
| FileVersion: | 6.0.37 |
| InternalName: | SanDisk SecureAccessV3 |
| LegalCopyright: | ENC Security Systems BV |
| LegalTrademarks1: | All Rights Reserved |
| LegalTrademarks2: | All Rights Reserved |
| OriginalFileName: | SanDiskSecureAccessV3_win.exe |
| ProductName: | SanDisk SecureAccessV3 |
| ProductVersion: | 6.0.37 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jun-2018 15:58:53 |
| Detected languages: |
|
| CompanyName: | ENC Security Systems BV |
| FileDescription: | SanDisk SecureAccessV3 |
| FileVersion: | 6.0.37 |
| InternalName: | SanDisk SecureAccessV3 |
| LegalCopyright: | ENC Security Systems BV |
| LegalTrademarks1: | All Rights Reserved |
| LegalTrademarks2: | All Rights Reserved |
| OriginalFilename: | SanDiskSecureAccessV3_win.exe |
| ProductName: | SanDisk SecureAccessV3 |
| ProductVersion: | 6.0.37 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000138 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Jun-2018 15:58:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00870000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00871000 | 0x00821000 | 0x00820600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90614 |
.rsrc | 0x01092000 | 0x0003B000 | 0x0003AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.33007 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06467 | 638 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.53595 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 6.54691 | 38056 | UNKNOWN | English - United States | RT_ICON |
4 | 6.57897 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 6.50891 | 9640 | UNKNOWN | English - United States | RT_ICON |
6 | 6.54603 | 4264 | UNKNOWN | English - United States | RT_ICON |
7 | 6.4821 | 2440 | UNKNOWN | English - United States | RT_ICON |
8 | 6.28412 | 1128 | UNKNOWN | English - United States | RT_ICON |
IDI_ICON1 | 2.99352 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
OLEAUT32.dll |
SETUPAPI.dll |
SHELL32.dll |
USER32.dll |
Total processes
76
Monitored processes
27
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 532 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2664.48.369079527\1573663071" -childID 7 -isForBrowser -prefsHandle 4360 -prefMapHandle 4364 -prefsLen 9408 -prefMapSize 184959 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2664 "\\.\pipe\gecko-crash-server-pipe.2664" 4376 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/eccaed1b-7e2e-463e-8b64-ca7c61e098cd/first-shutdown/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\nzjt9k1u.default-1590811630677\saved-telemetry-pings\eccaed1b-7e2e-463e-8b64-ca7c61e098cd | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2192.0.2094409495\992035636" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2192 "\\.\pipe\gecko-crash-server-pipe.2192" 1184 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 68.0.1 Modules
| |||||||||||||||
| 2152 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\CCleaner\CCleaner.exe" /monitor | C:\Program Files\CCleaner\CCleaner.exe | CCleaner.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 1073807364 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2208 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\AppData\Local\Temp\SanDiskSecureAccessV3_win.exe" | C:\Users\admin\AppData\Local\Temp\SanDiskSecureAccessV3_win.exe | — | explorer.exe | |||||||||||
User: admin Company: ENC Security Systems BV Integrity Level: MEDIUM Description: SanDisk SecureAccessV3 Exit code: 0 Version: 6.0.37 Modules
| |||||||||||||||
Total events
15 276
Read events
2 039
Write events
9 411
Delete events
3 826
Modification events
| (PID) Process: | (2192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 8D62770000000000 | |||
| (PID) Process: | (4076) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 8D62770000000000 | |||
| (PID) Process: | (2192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3572) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2664) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 0000000000000000 | |||
| (PID) Process: | (3572) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3572) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3572) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
2
Suspicious files
140
Text files
123
Unknown types
158
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\3E2DE7D250D7D2A9B4979A1BEB416C67B8104FB6 | der | |
MD5:— | SHA256:— | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.sbstore | binary | |
MD5:D886A47C89D9C49C795DA345BC236990 | SHA256:A03C5E2656D2F292BF5794C8EEB8D223CD6BA4F4BFB2ED1F325460E879D0BCF7 | |||
| 2192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
48
DNS requests
91
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1588 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
2192 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1588 | CCleaner.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
3572 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1052 | svchost.exe | GET | 200 | 23.210.253.93:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | NL | der | 813 b | whitelisted |
1588 | CCleaner.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8EJH | US | der | 1.49 Kb | whitelisted |
2664 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2664 | firefox.exe | POST | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
2664 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2192 | firefox.exe | POST | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2192 | firefox.exe | 2.16.107.40:80 | detectportal.firefox.com | Akamai International B.V. | — | malicious |
2192 | firefox.exe | 143.204.201.119:443 | snippets.cdn.mozilla.net | — | US | suspicious |
2192 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2192 | firefox.exe | 143.204.201.3:443 | tracking-protection.cdn.mozilla.net | — | US | malicious |
2192 | firefox.exe | 172.217.22.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2192 | firefox.exe | 143.204.201.102:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
3572 | pingsender.exe | 34.210.247.128:443 | incoming.telemetry.mozilla.org | Amazon.com, Inc. | US | unknown |
2664 | firefox.exe | 2.16.107.58:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
2664 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2664 | firefox.exe | 52.209.204.108:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |