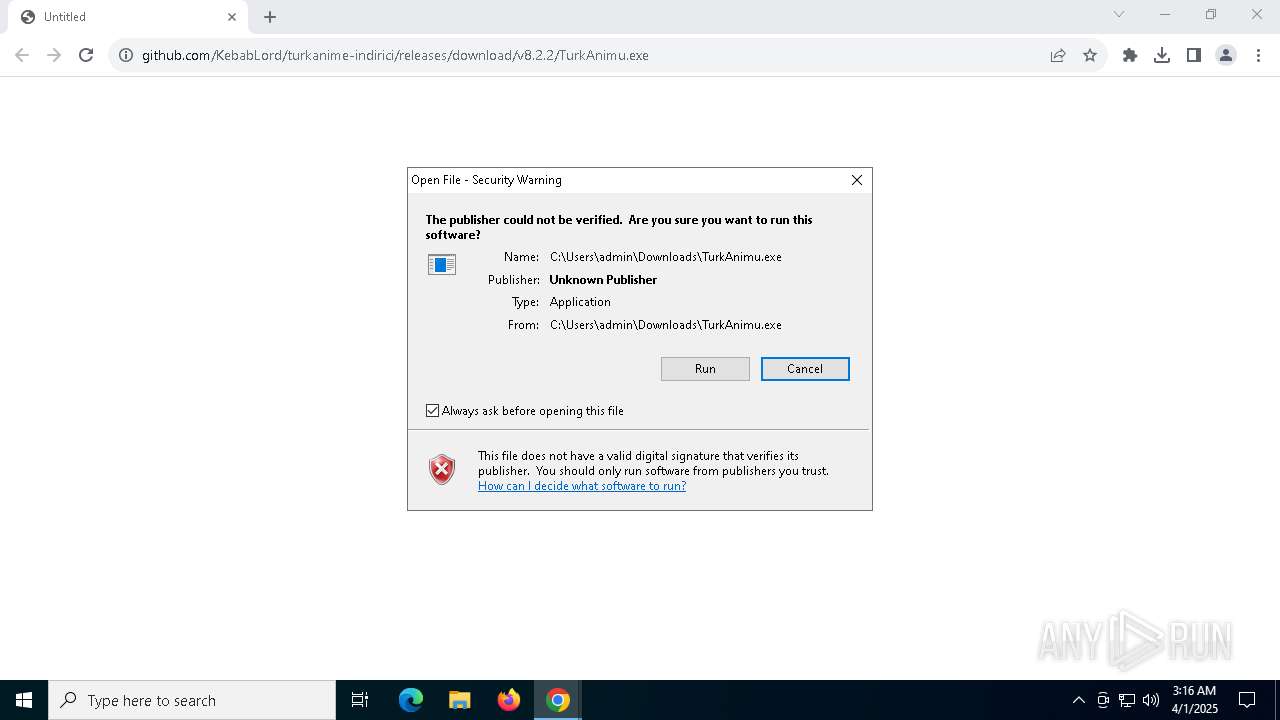
| URL: | https://github.com/KebabLord/turkanime-indirici/releases/download/v8.2.2/TurkAnimu.exe |
| Full analysis: | https://app.any.run/tasks/f1b05cd7-8d59-4909-8e64-48bc8df6734e |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2025, 03:15:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E6D7C7A3F0E82CFD200429A068160D55 |
| SHA1: | A0EB39999509C24140BEC02DEDC377DBCDDCCD70 |
| SHA256: | A2D32B43DA58C93F1A2DE4625CD68BD2B2569BB55C4AC22F2BA7213A4CFAEC30 |
| SSDEEP: | 3:N8tEdvEJAyELOIK6zAr2kCR6C/Mt0dA:2ulEJAyiON6sK/6sMtkA |
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
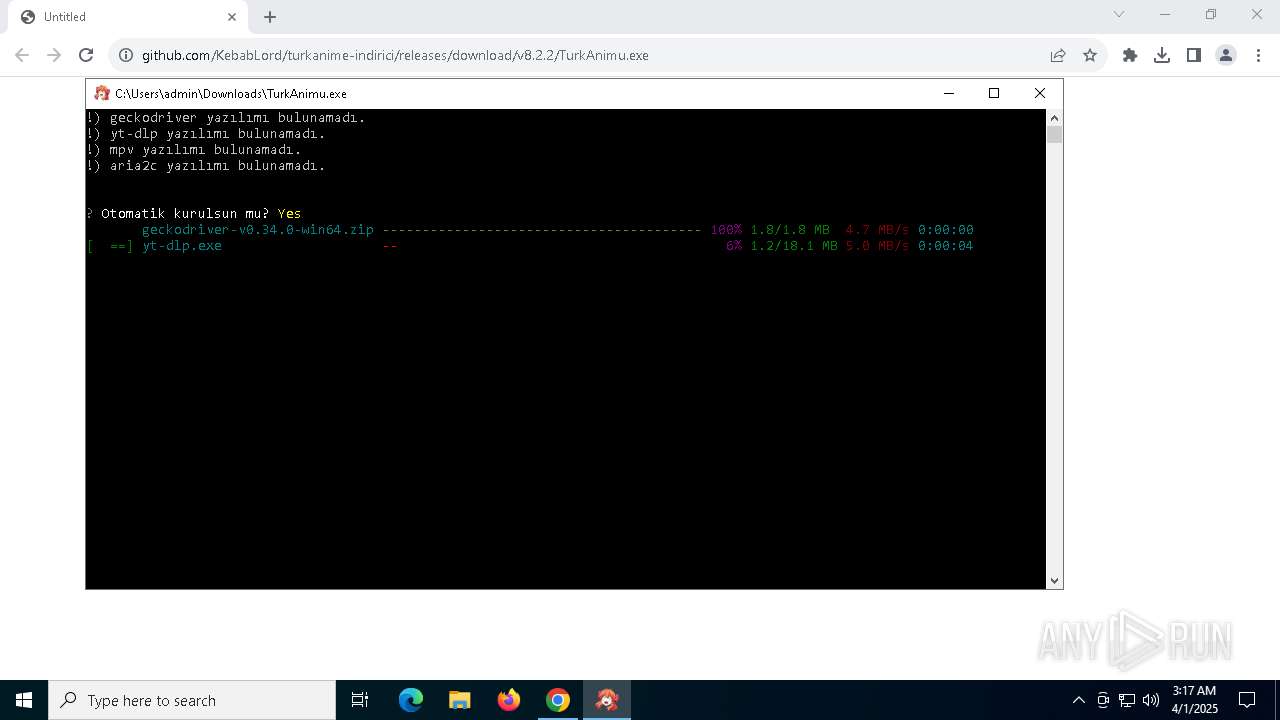
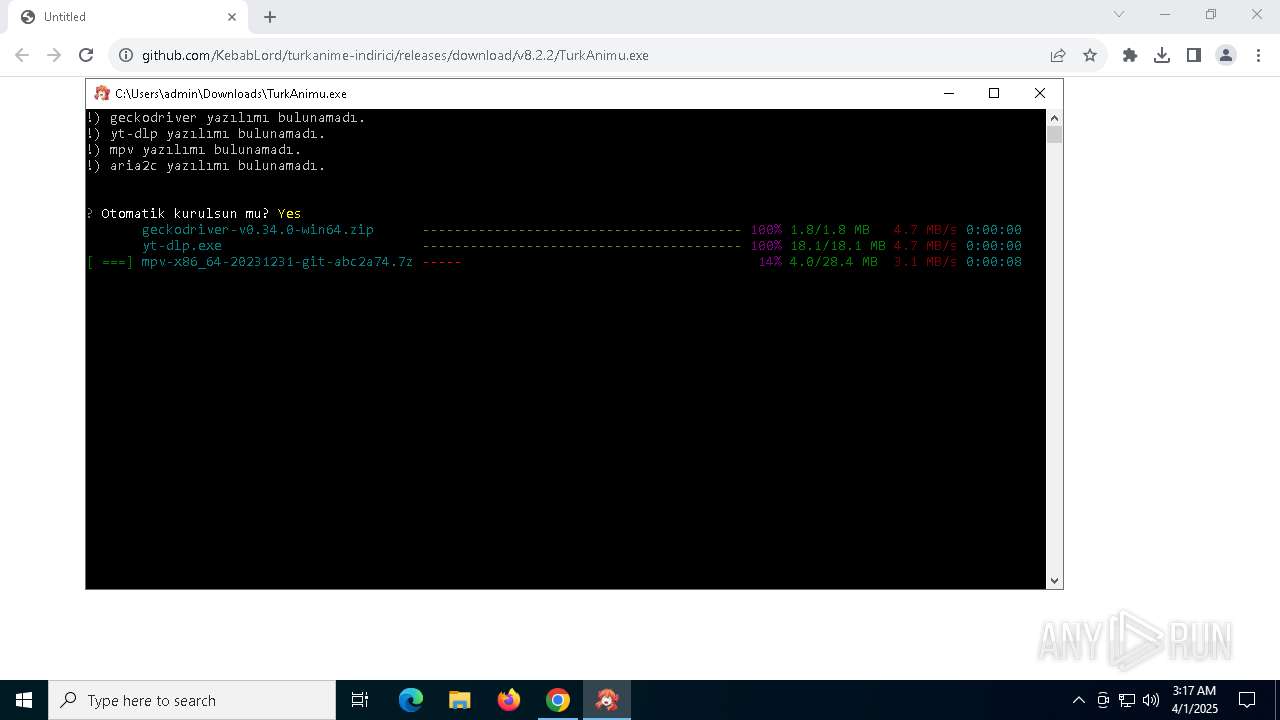
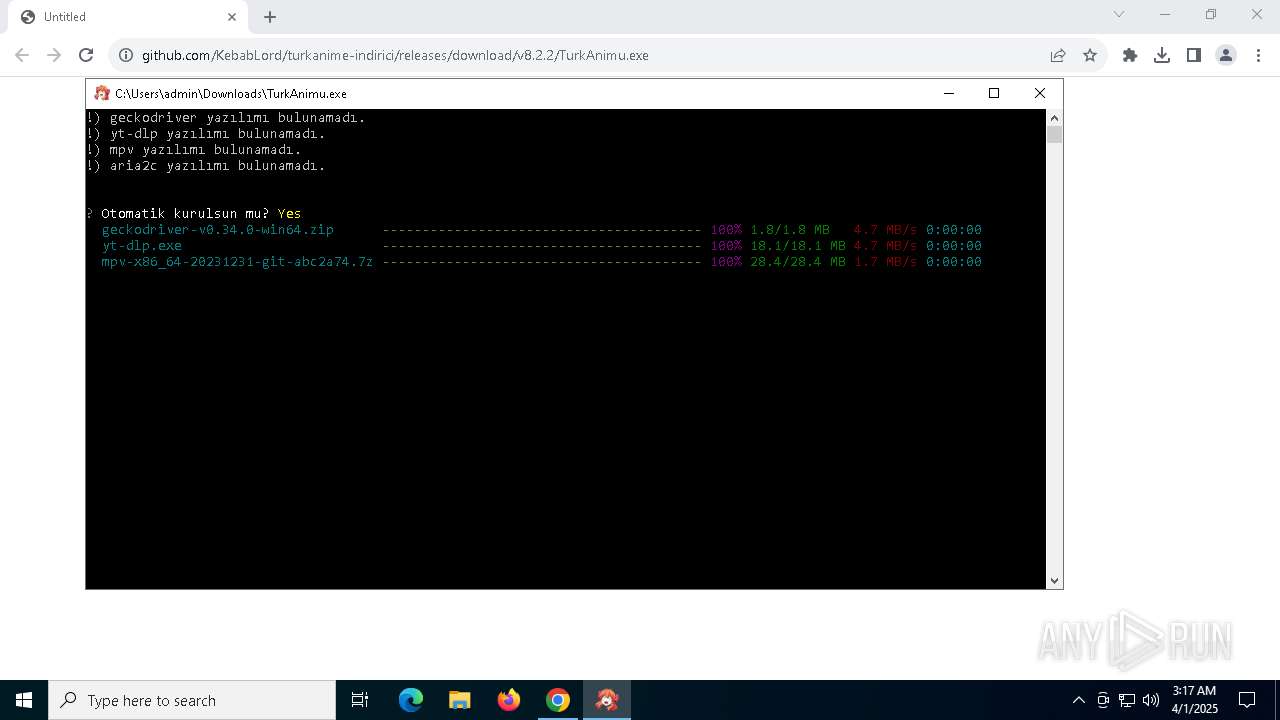
Process drops python dynamic module
- TurkAnimu.exe (PID: 8160)
- yt-dlp.exe (PID: 2644)
Process drops legitimate windows executable
- TurkAnimu.exe (PID: 8160)
- yt-dlp.exe (PID: 2644)
- TurkAnimu.exe (PID: 4040)
The process drops C-runtime libraries
- TurkAnimu.exe (PID: 8160)
- yt-dlp.exe (PID: 2644)
Executable content was dropped or overwritten
- TurkAnimu.exe (PID: 8160)
- yt-dlp.exe (PID: 2644)
- TurkAnimu.exe (PID: 4040)
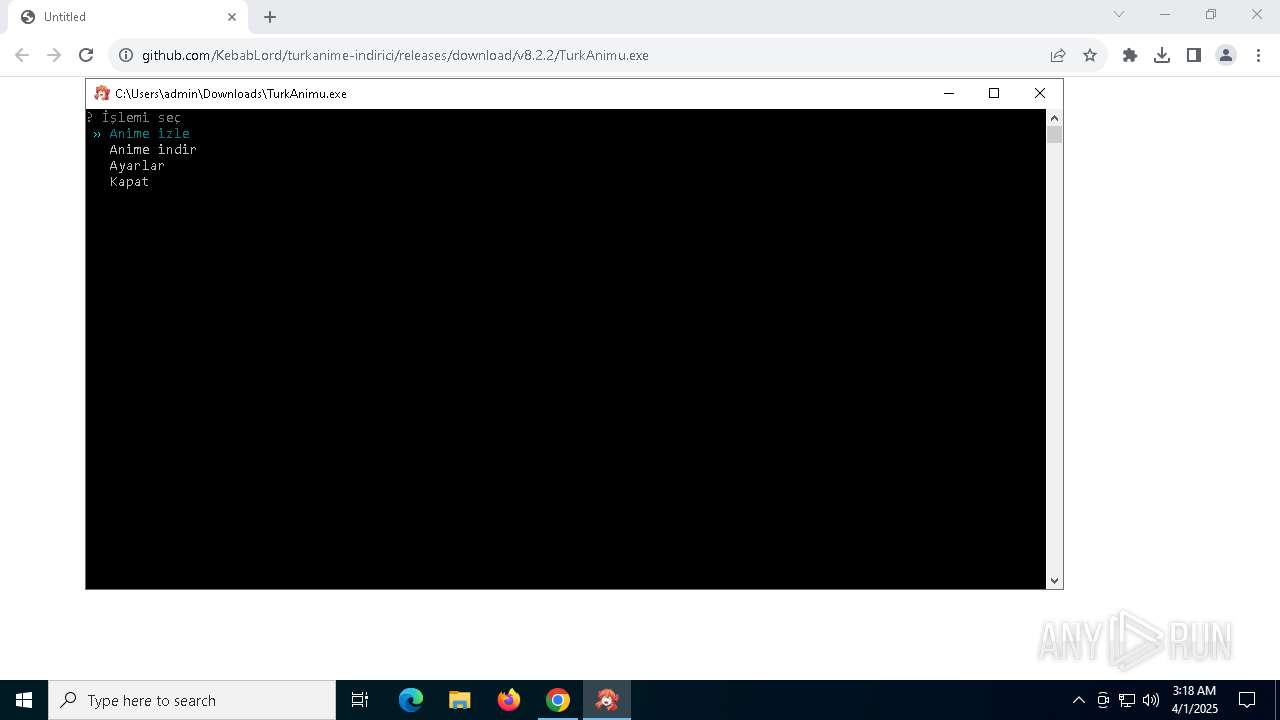
Application launched itself
- TurkAnimu.exe (PID: 8160)
- yt-dlp.exe (PID: 2644)
Loads Python modules
- TurkAnimu.exe (PID: 4040)
- yt-dlp.exe (PID: 7188)
The executable file from the user directory is run by the CMD process
- geckodriver.exe (PID: 2568)
- yt-dlp.exe (PID: 2644)
- aria2c.exe (PID: 924)
- mpv.exe (PID: 5324)
- geckodriver.exe (PID: 5332)
There is functionality for taking screenshot (YARA)
- TurkAnimu.exe (PID: 4040)
Starts CMD.EXE for commands execution
- TurkAnimu.exe (PID: 4040)
- yt-dlp.exe (PID: 7188)
- selenium-manager.exe (PID: 4012)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 776)
Uses WMIC.EXE
- cmd.exe (PID: 7264)
INFO
Checks supported languages
- TurkAnimu.exe (PID: 8160)
- TurkAnimu.exe (PID: 4040)
- geckodriver.exe (PID: 2568)
- yt-dlp.exe (PID: 2644)
- yt-dlp.exe (PID: 7188)
- mpv.exe (PID: 5324)
- aria2c.exe (PID: 924)
- selenium-manager.exe (PID: 4012)
- geckodriver.exe (PID: 5332)
- geckodriver.exe (PID: 2780)
Reads the computer name
- TurkAnimu.exe (PID: 8160)
- TurkAnimu.exe (PID: 4040)
- yt-dlp.exe (PID: 2644)
- selenium-manager.exe (PID: 4012)
- geckodriver.exe (PID: 2780)
Executable content was dropped or overwritten
- chrome.exe (PID: 7368)
- chrome.exe (PID: 1240)
Autorun file from Downloads
- chrome.exe (PID: 5124)
Create files in a temporary directory
- TurkAnimu.exe (PID: 8160)
- TurkAnimu.exe (PID: 4040)
- yt-dlp.exe (PID: 2644)
- geckodriver.exe (PID: 2780)
The sample compiled with english language support
- TurkAnimu.exe (PID: 8160)
- chrome.exe (PID: 1240)
- TurkAnimu.exe (PID: 4040)
- yt-dlp.exe (PID: 2644)
Reads the software policy settings
- slui.exe (PID: 8072)
- slui.exe (PID: 6752)
Application launched itself
- chrome.exe (PID: 7368)
- firefox.exe (PID: 5404)
- firefox.exe (PID: 5156)
PyInstaller has been detected (YARA)
- TurkAnimu.exe (PID: 8160)
- TurkAnimu.exe (PID: 4040)
Checks operating system version
- TurkAnimu.exe (PID: 4040)
- yt-dlp.exe (PID: 7188)
Drops encrypted JS script (Microsoft Script Encoder)
- TurkAnimu.exe (PID: 4040)
Checks proxy server information
- TurkAnimu.exe (PID: 4040)
- slui.exe (PID: 6752)
- selenium-manager.exe (PID: 4012)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7036)
- WMIC.exe (PID: 5796)
Reads the machine GUID from the registry
- yt-dlp.exe (PID: 7188)
Application based on Rust
- geckodriver.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
208
Monitored processes
73
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | C:\WINDOWS\system32\cmd.exe /c "aria2c --version" | C:\Windows\SysWOW64\cmd.exe | — | TurkAnimu.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "cmd" /c "wmic os get osarchitecture" | C:\Windows\SysWOW64\cmd.exe | — | selenium-manager.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | aria2c --version | C:\Users\admin\TurkAnimu\aria2c.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1164 | C:\WINDOWS\system32\cmd.exe /c "geckodriver --version" | C:\Windows\SysWOW64\cmd.exe | — | TurkAnimu.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5260 --field-trial-handle=1888,i,8440251899608497838,4480675823101224066,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5720 --field-trial-handle=1888,i,8440251899608497838,4480675823101224066,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1244 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | yt-dlp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5592 --field-trial-handle=1888,i,8440251899608497838,4480675823101224066,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1452 | C:\WINDOWS\system32\cmd.exe /c "mpv --version" | C:\Windows\SysWOW64\cmd.exe | — | TurkAnimu.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | C:\WINDOWS\system32\cmd.exe /c "mpv --version" | C:\Windows\SysWOW64\cmd.exe | — | TurkAnimu.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 329
Read events
23 303
Write events
20
Delete events
6
Modification events
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5124) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000668EB45EB4A2DB01 | |||
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (7368) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
Executable files
265
Suspicious files
401
Text files
1 048
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c093.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
100
DNS requests
90
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7368 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7592 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7592 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7592 | chrome.exe | 185.199.111.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
6544 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (naupsithizeekee .com) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (naupsithizeekee .com) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (naupsithizeekee .com) |