| File name: | zukaz-Copy.txt.ps1 |
| Full analysis: | https://app.any.run/tasks/d35b0bb3-ebb8-438e-96ae-04dec2b782a7 |
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2024, 17:08:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | C26768A5961C38415AE0D4100ED280ED |
| SHA1: | AD96A0593E494DDF98FEB3094521F858AE53ABB0 |
| SHA256: | A2934D3110084FBB9656BA92A0A94F5508B5000E8461F3135E60C1E7C7E94CAA |
| SSDEEP: | 12:s5XIrBQXqrXG3MTbG3PCFhqAiAaGwMn0k8Q:s1IGXqi8G3PCFhiGPV8Q |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5124)
SUSPICIOUS
Potential Corporate Privacy Violation
- powershell.exe (PID: 5124)
- svchost.exe (PID: 2192)
Checks for external IP
- powershell.exe (PID: 5124)
- svchost.exe (PID: 2192)
Executable content was dropped or overwritten
- powershell.exe (PID: 5124)
INFO
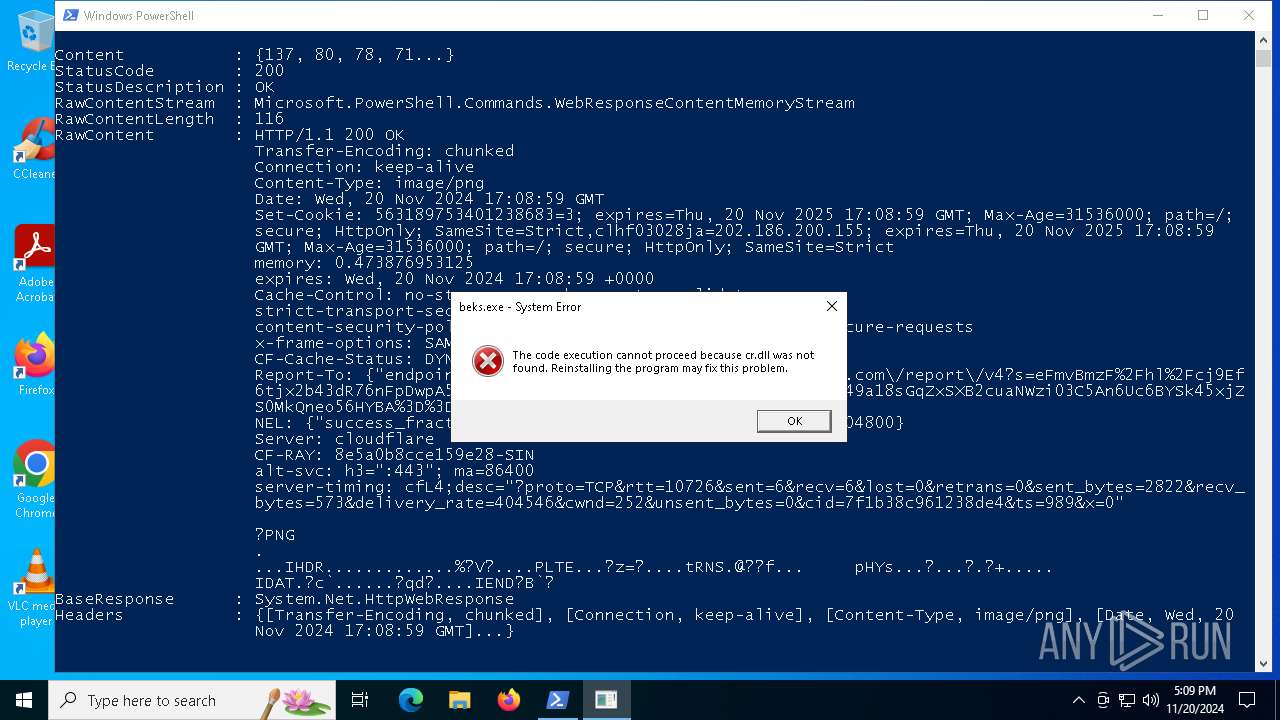
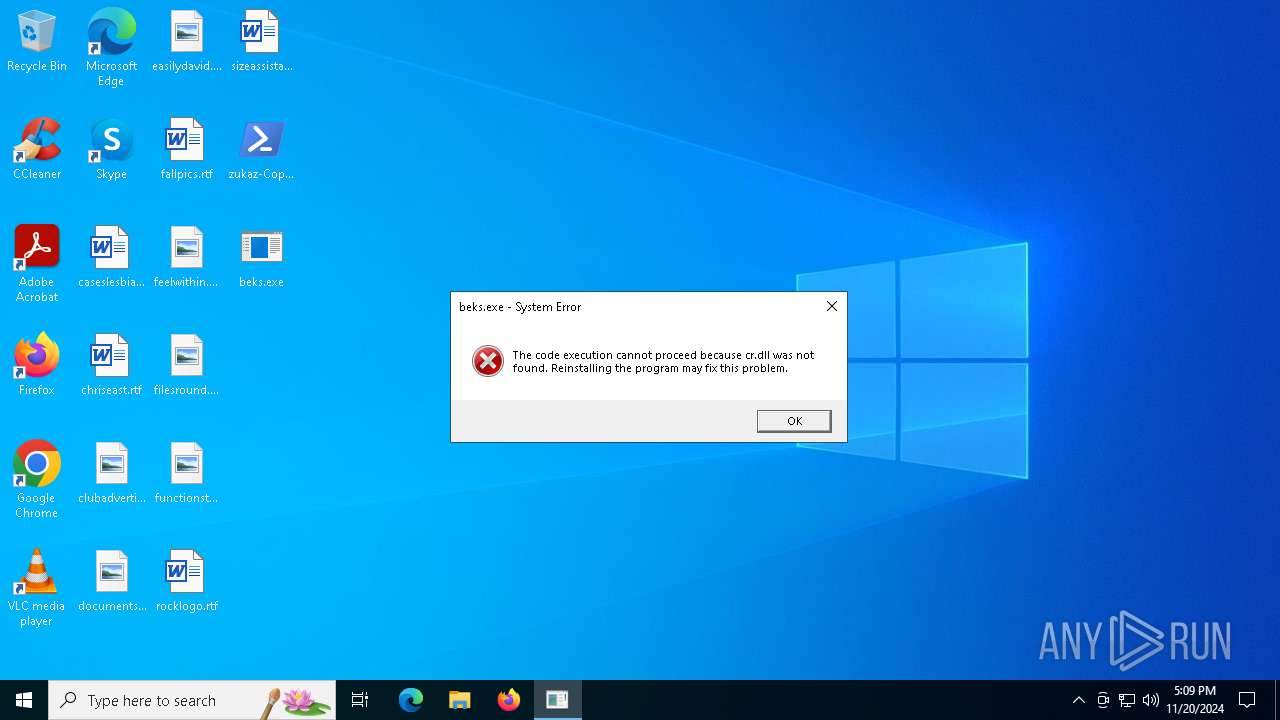
The executable file from the user directory is run by the Powershell process
- beks.exe (PID: 2020)
Manual execution by a user
- beks.exe (PID: 5868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
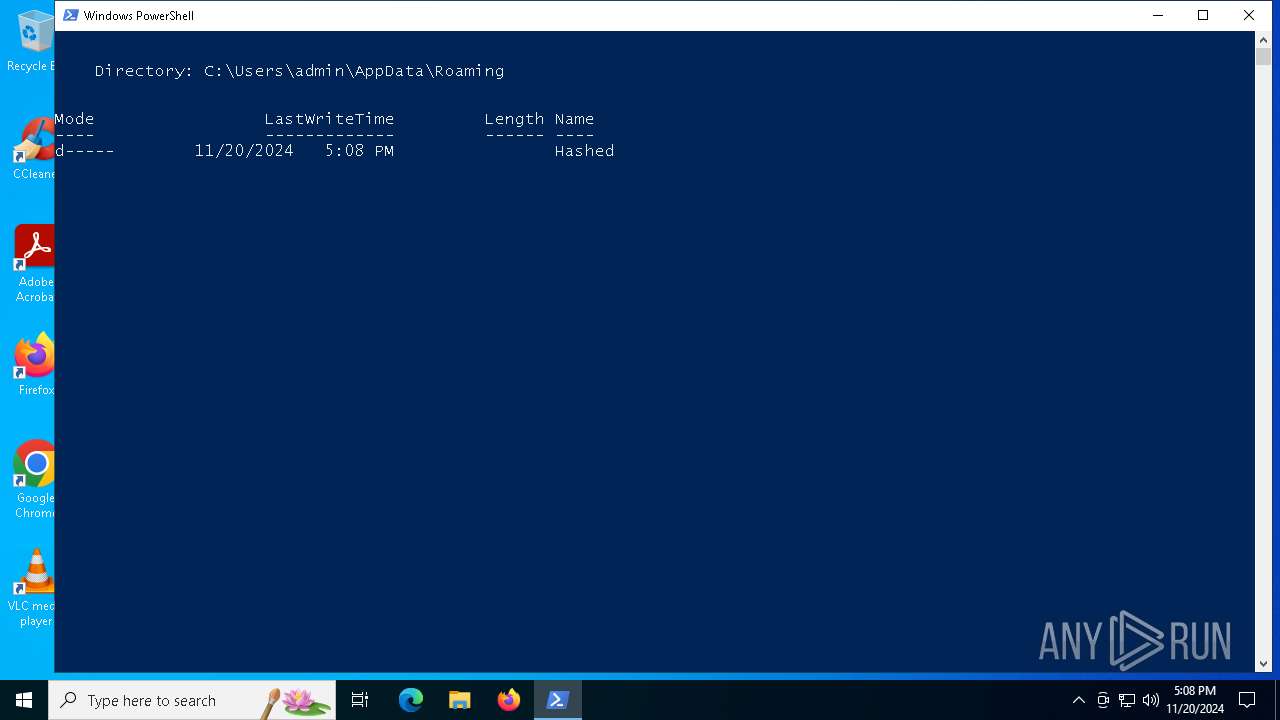
| 2020 | "C:\Users\admin\AppData\Roaming\Hashed\beks.exe" | C:\Users\admin\AppData\Roaming\Hashed\beks.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5124 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\zukaz-Copy.txt.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5868 | "C:\Users\admin\Desktop\beks.exe" | C:\Users\admin\Desktop\beks.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225781 Modules
| |||||||||||||||
Total events
8 827
Read events
8 827
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
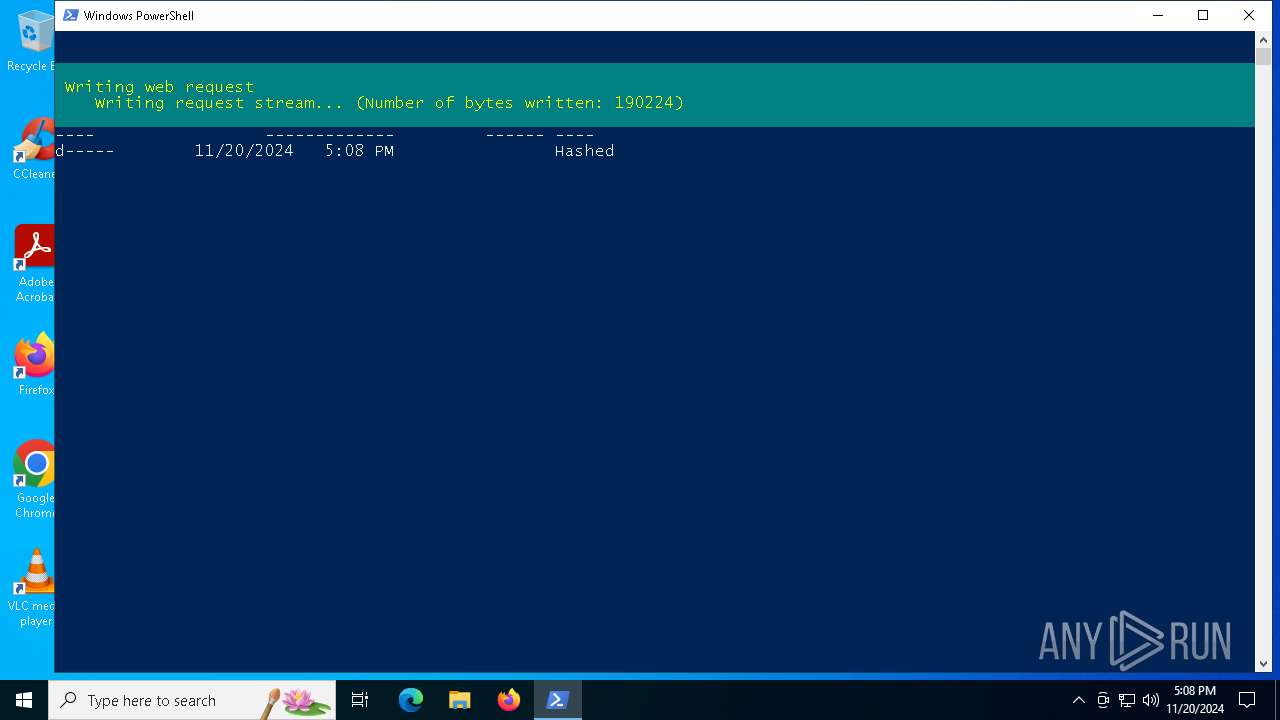
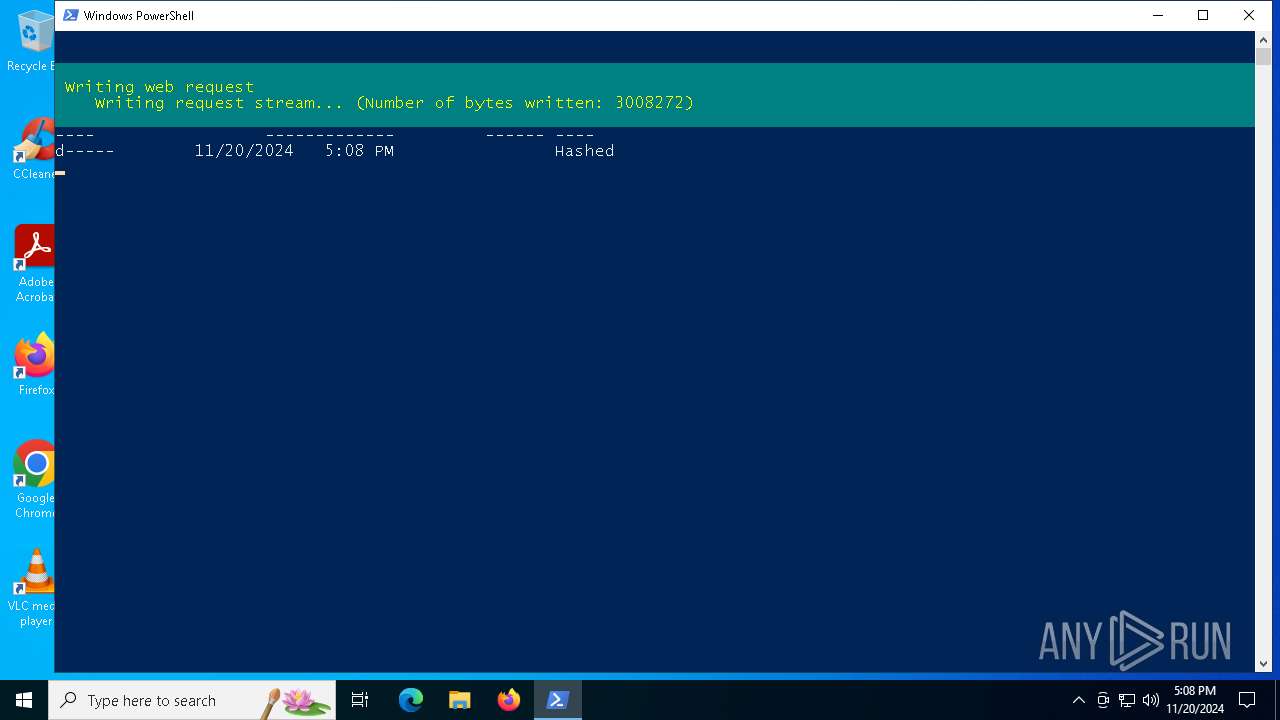
| 5124 | powershell.exe | C:\Users\admin\AppData\Roaming\Hashed\beks.exe | executable | |
MD5:02A3FF6CF40A59890512E2199C3A3256 | SHA256:A539405F9E4C86CE4ADE7FDFE39ECC2DA493083654F5CD6662BB14B9BBB9CA53 | |||
| 5124 | powershell.exe | C:\Users\admin\AppData\Roaming\pkzd.zip | compressed | |
MD5:5CB3B50E145EBE31F3EFFF1A79E85445 | SHA256:59AEB2712A0D12740366A62CC3C6FAA8A3CE66317FC74DCC4C1A997D95EEF9E9 | |||
| 5124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WE6UT2EHQ0NDL30NGUW5.temp | binary | |
MD5:C8EB6E58AF2E10BA7F03C0D43BB745B4 | SHA256:A503A8C81D2B687C0D1CA6C461E9A378259C3AF059D47AA46D66F5673D64BA52 | |||
| 5124 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B53CEEAAE67CC00394594FCDFAB379C5 | SHA256:176D09B8883BF6B41BAAE843182A65E2F2457A154D27FD6DF15376FF2CE1BFC8 | |||
| 5124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFea16c.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 5124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lvlbdkjf.qpu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5124 | powershell.exe | C:\Users\admin\AppData\Roaming\Hashed\cr.dll | executable | |
MD5:2A53C7F50B074DB464F7DACFCBAD3BE8 | SHA256:EE5C5DD1AEE927A6BCB8E390A0D2C5ADCDA66DA5EC9E7D41B22014DD3181E793 | |||
| 5124 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ecpc0rpv.qeo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:C8EB6E58AF2E10BA7F03C0D43BB745B4 | SHA256:A503A8C81D2B687C0D1CA6C461E9A378259C3AF059D47AA46D66F5673D64BA52 | |||
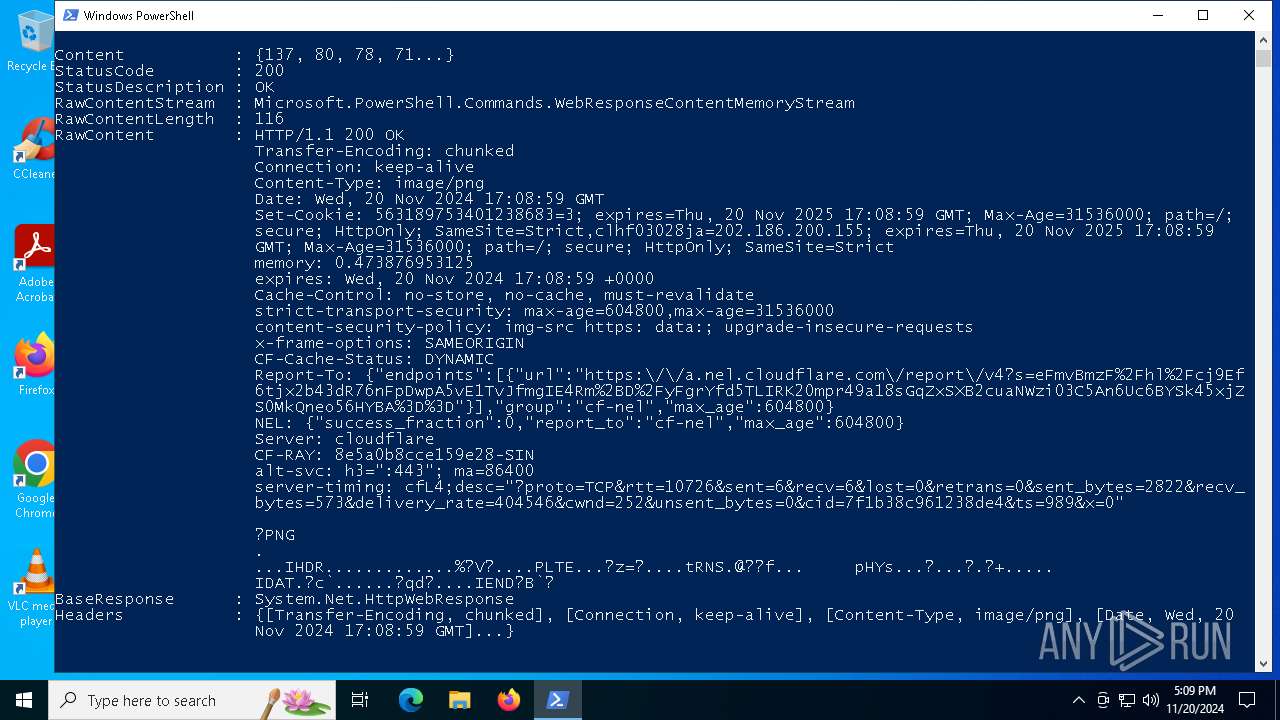
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
30
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4932 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2576 | RUXIMICS.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2576 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 185.61.154.193:443 | https://fadeaway.supply/krekan.zip | unknown | compressed | 3.49 Mb | unknown |
— | — | POST | 200 | 104.21.56.156:443 | https://steep-number.cyou/api | unknown | text | 15 b | unknown |
— | — | POST | 200 | 172.67.152.241:443 | https://steep-number.cyou/api | unknown | text | 48 b | unknown |
— | — | POST | 200 | 104.21.56.156:443 | https://steep-number.cyou/api | unknown | text | 15 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2576 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4932 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.158:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4932 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2576 | RUXIMICS.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4932 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fadeaway.supply |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
iplogger.co |
| shared |
steep-number.cyou |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report