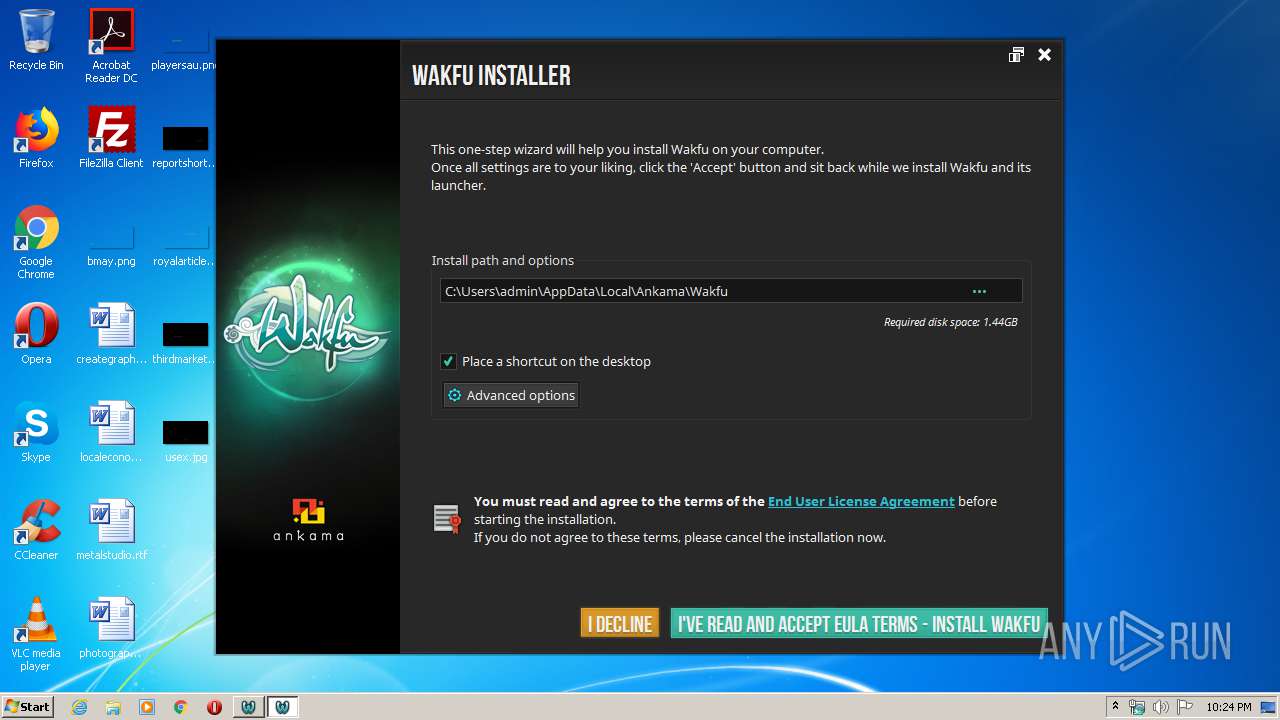
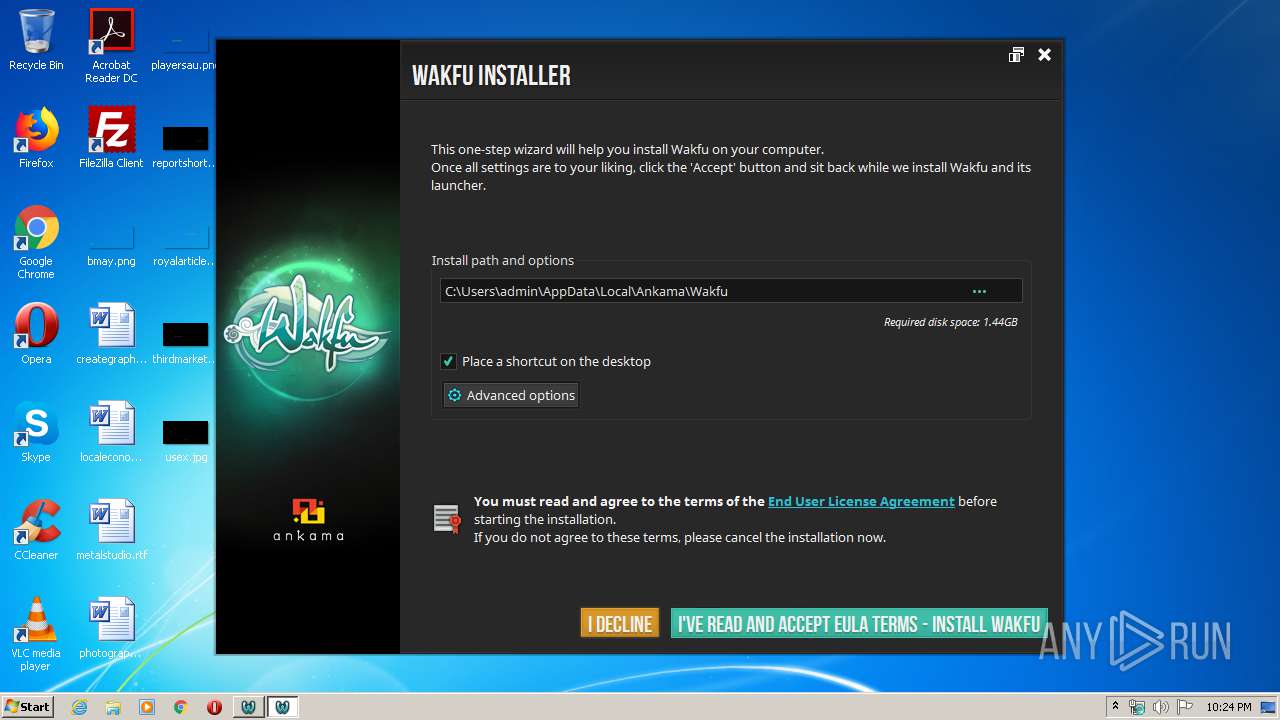
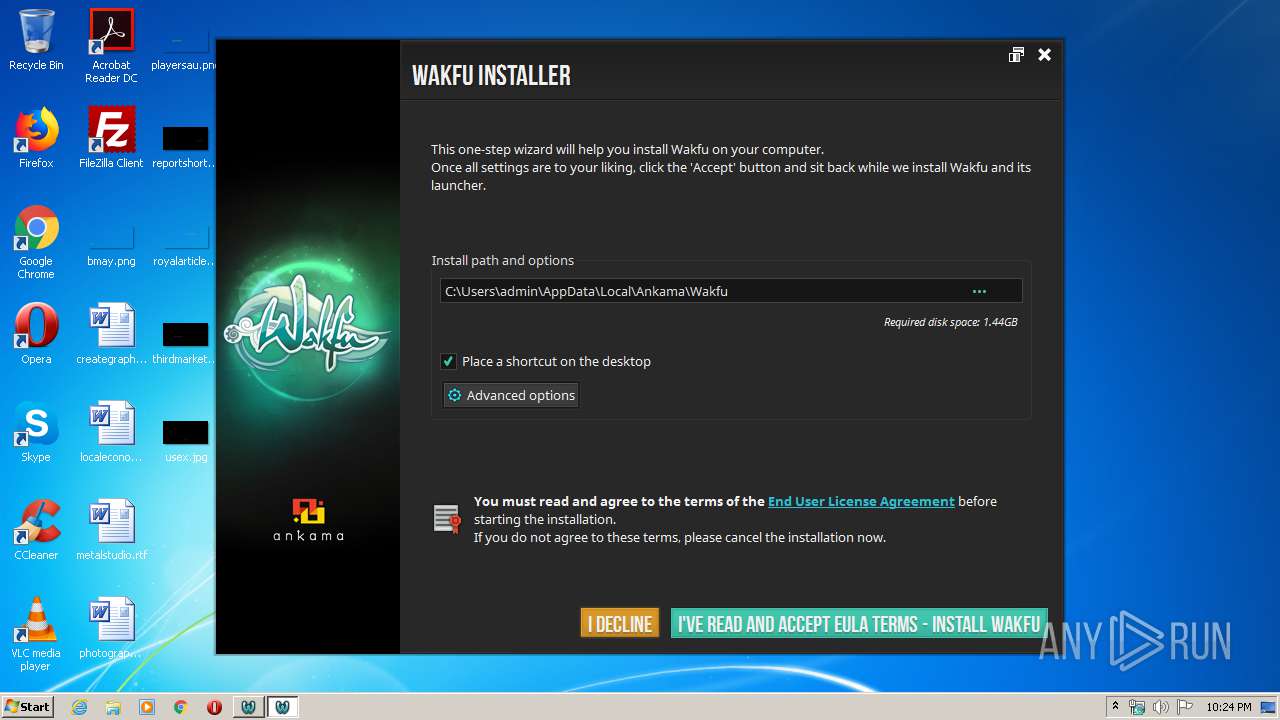
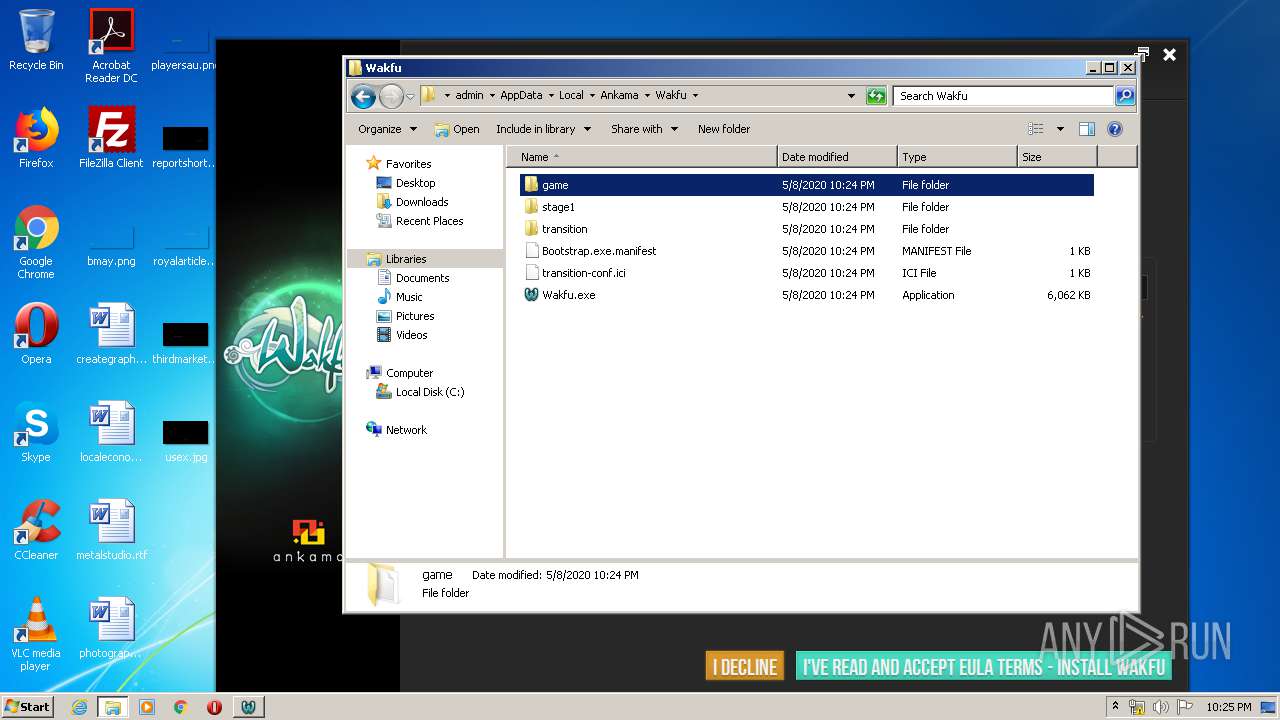
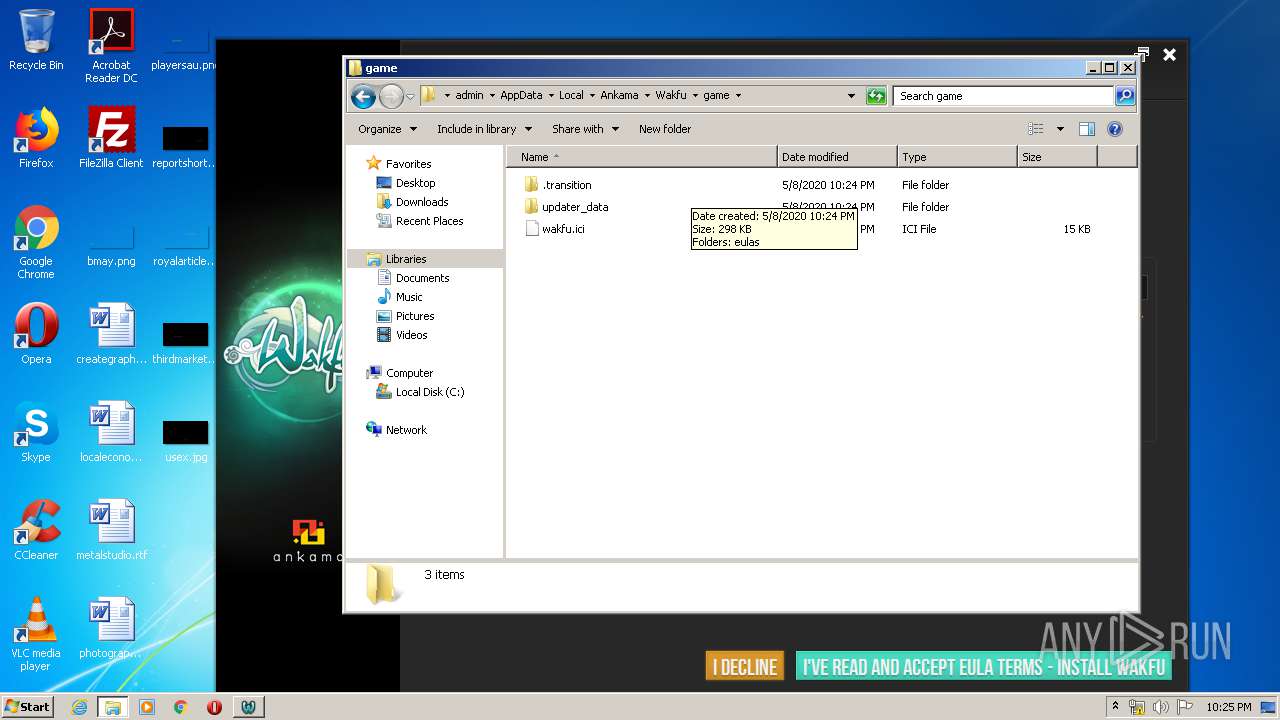
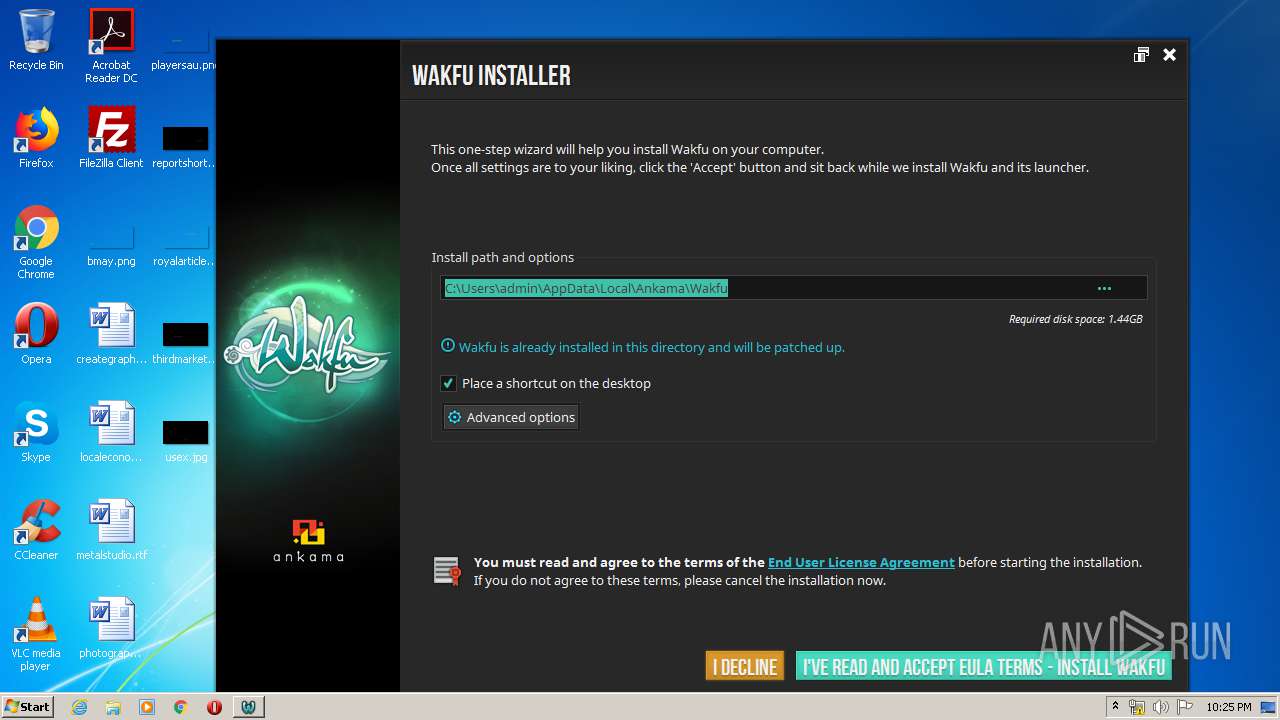
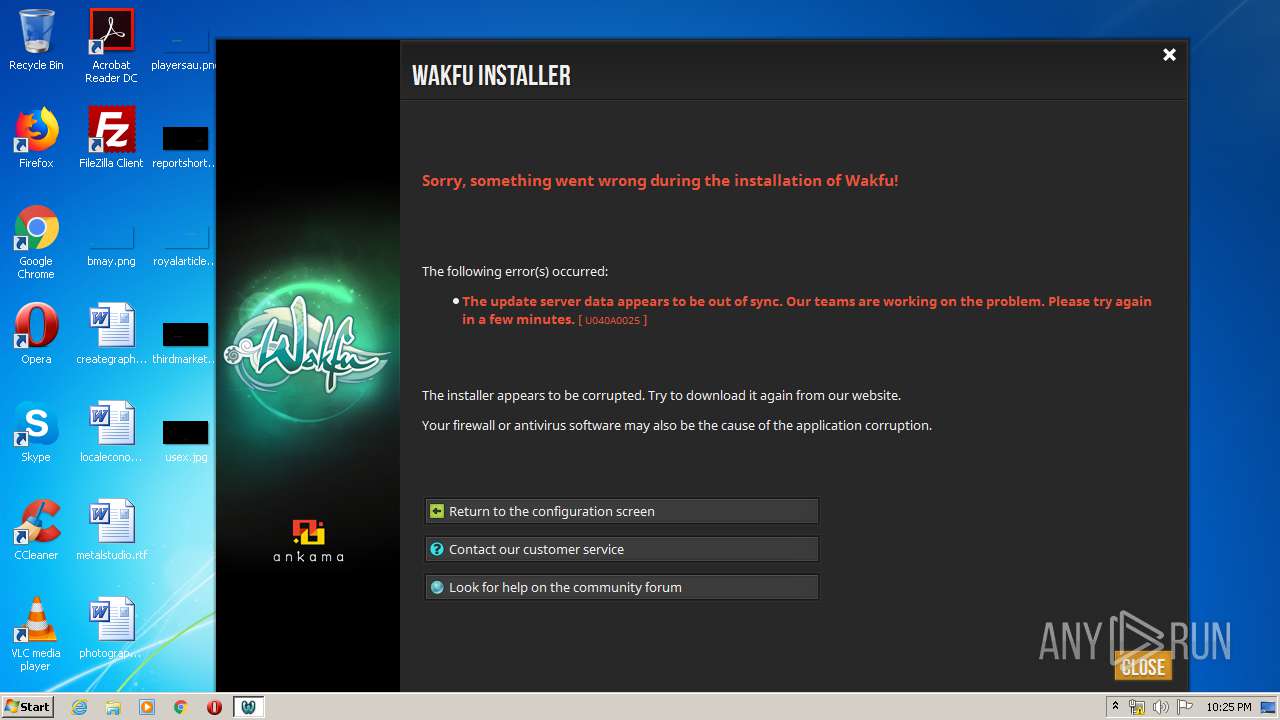
| File name: | Wakfu.exe |
| Full analysis: | https://app.any.run/tasks/43b410bb-fbec-49d2-a03c-03d0d80e28e5 |
| Verdict: | Malicious activity |
| Analysis date: | May 08, 2020, 21:24:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2CF6B655BFCBC5EE0AD5EEE36877E45A |
| SHA1: | 9AE86E448131EFF62DAC7E70DF17B2C456480E96 |
| SHA256: | A28B521B10516D10B7E5C5B292BA97F2C7FFE277C240BF425B2CA35B1BF6E07A |
| SSDEEP: | 98304:bih+vsKNeh5vGxX78FmLCN1gZZDfWGwI+89jzhm7frmXPWRfeVN:e4ovQ2mLCN1UV9nTjzQbrC+R23 |
MALICIOUS
Application was dropped or rewritten from another process
- transition.exe (PID: 312)
- transition-service.exe (PID: 3892)
Loads dropped or rewritten executable
- transition.exe (PID: 312)
- transition-service.exe (PID: 3892)
SUSPICIOUS
Executable content was dropped or overwritten
- Wakfu.exe (PID: 2184)
- transition.exe (PID: 312)
INFO
Dropped object may contain Bitcoin addresses
- Wakfu.exe (PID: 2184)
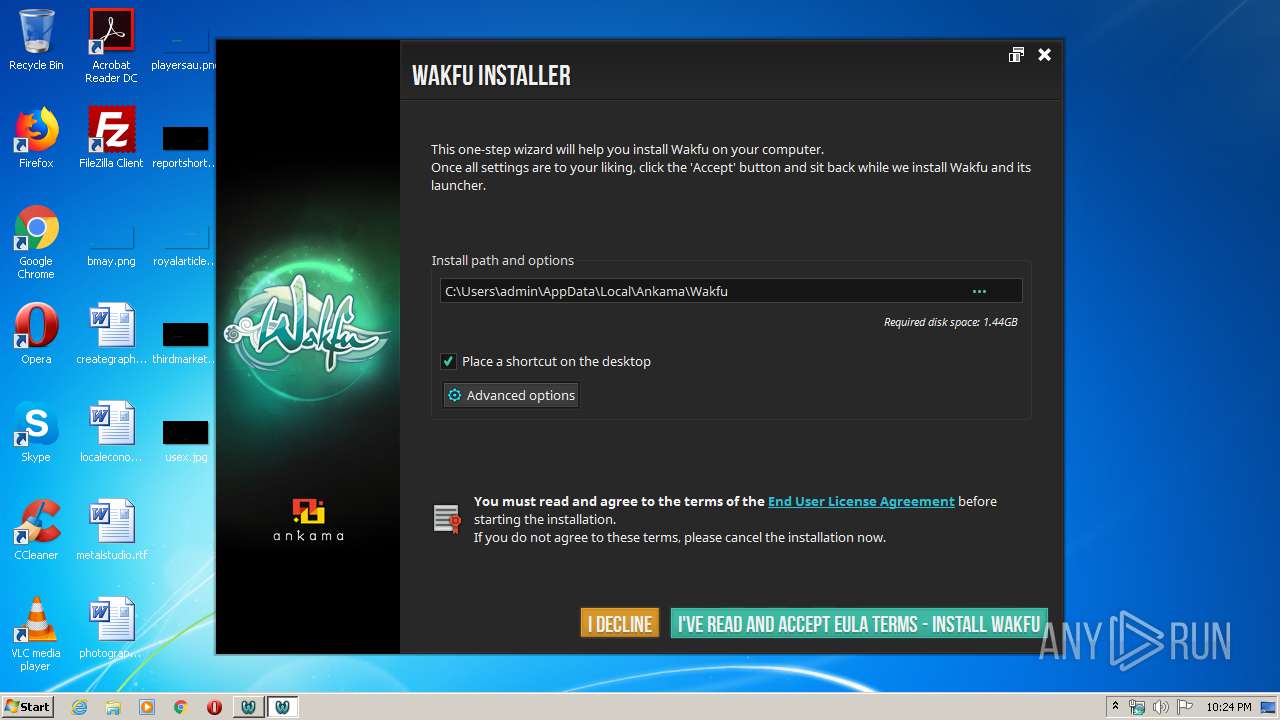
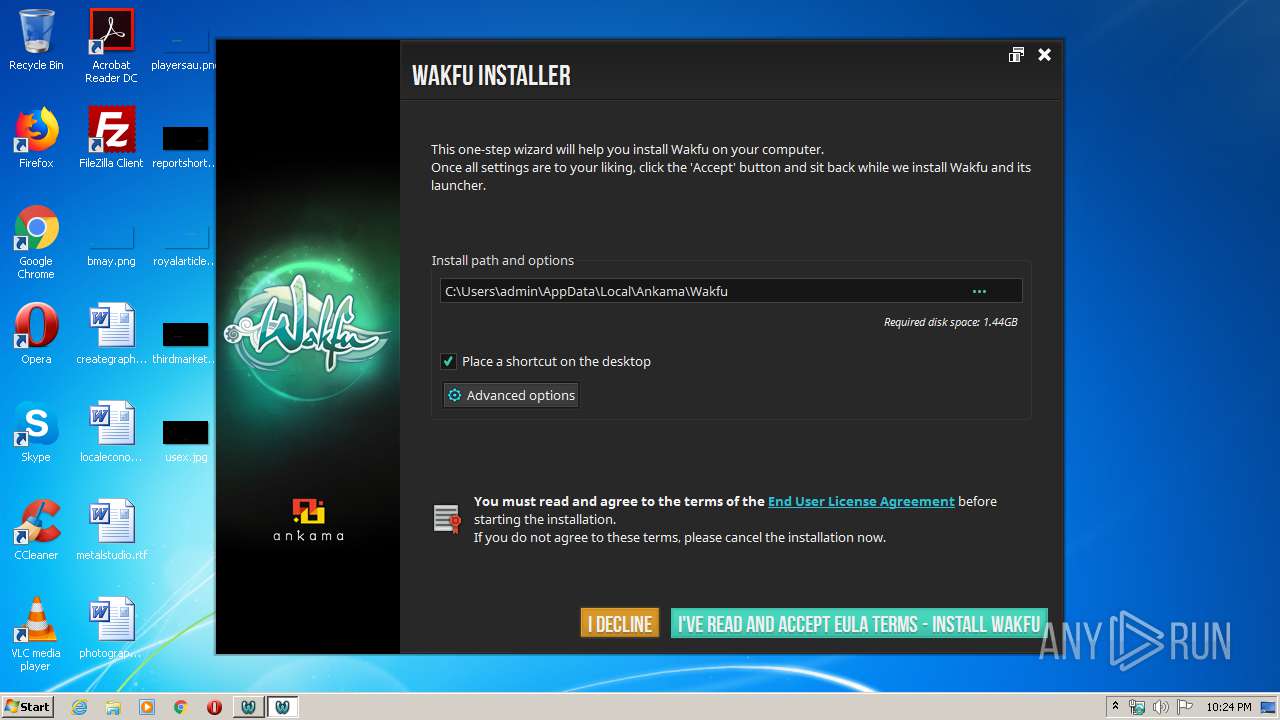
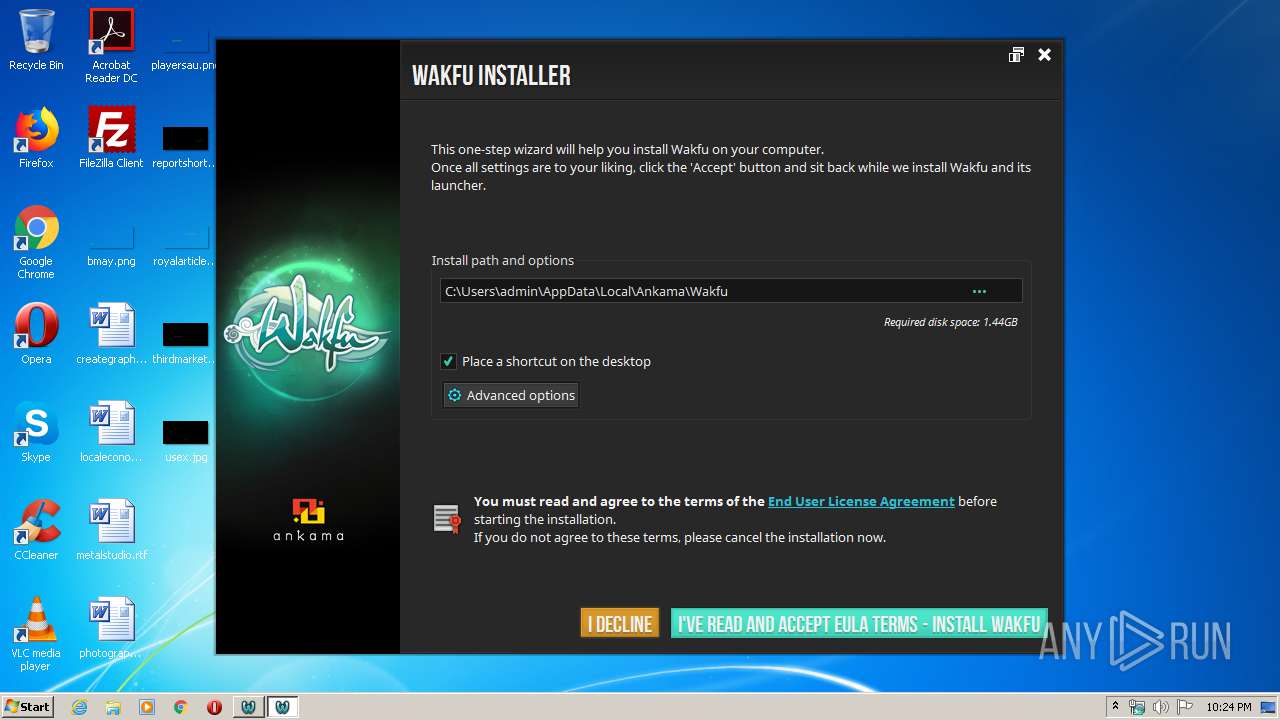
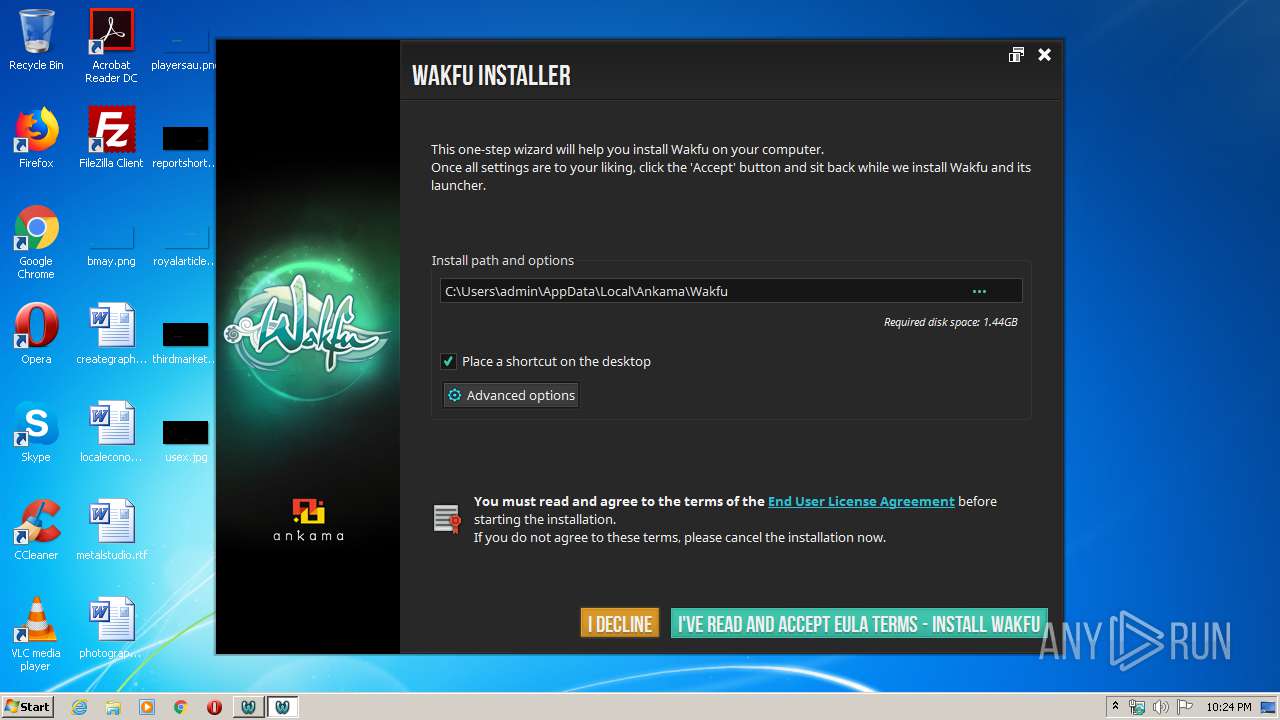
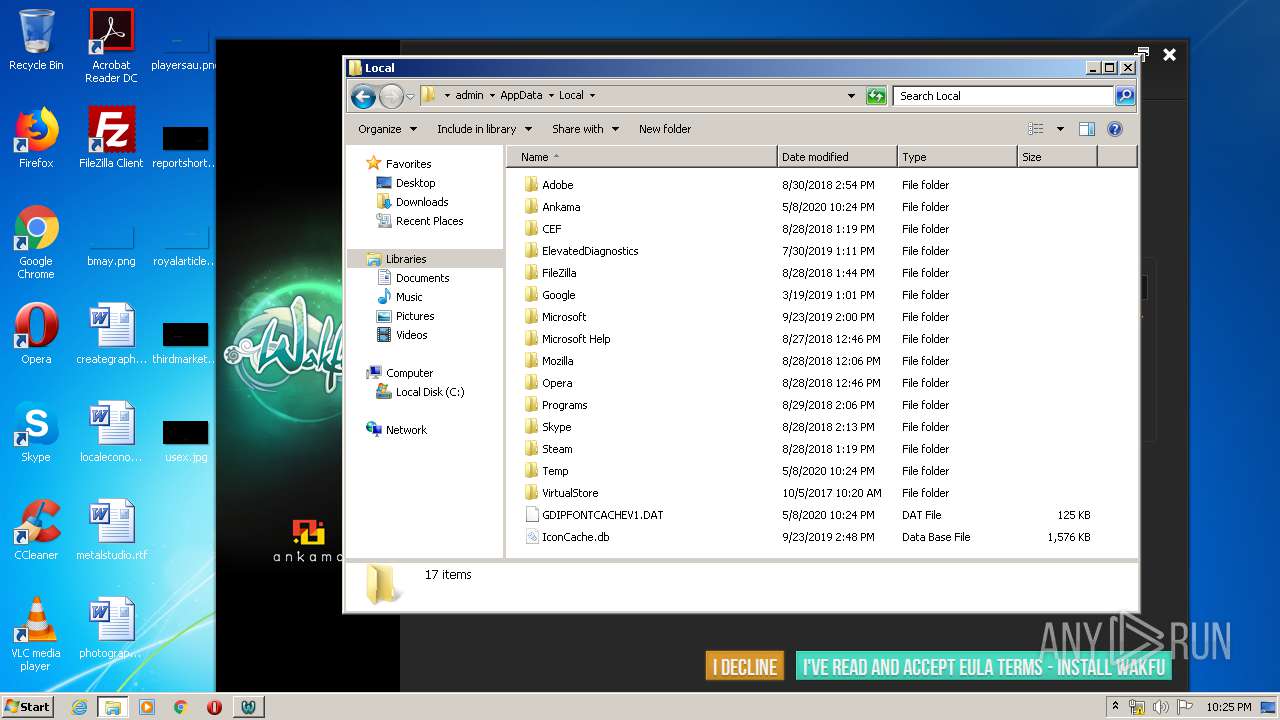
Manual execution by user
- explorer.exe (PID: 2688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:04:21 08:32:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 560640 |
| InitializedDataSize: | 5513728 |
| UninitializedDataSize: | 12288 |
| EntryPoint: | 0x14b0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.11.1.0 |
| ProductVersionNumber: | 1.65535.65535.65535 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
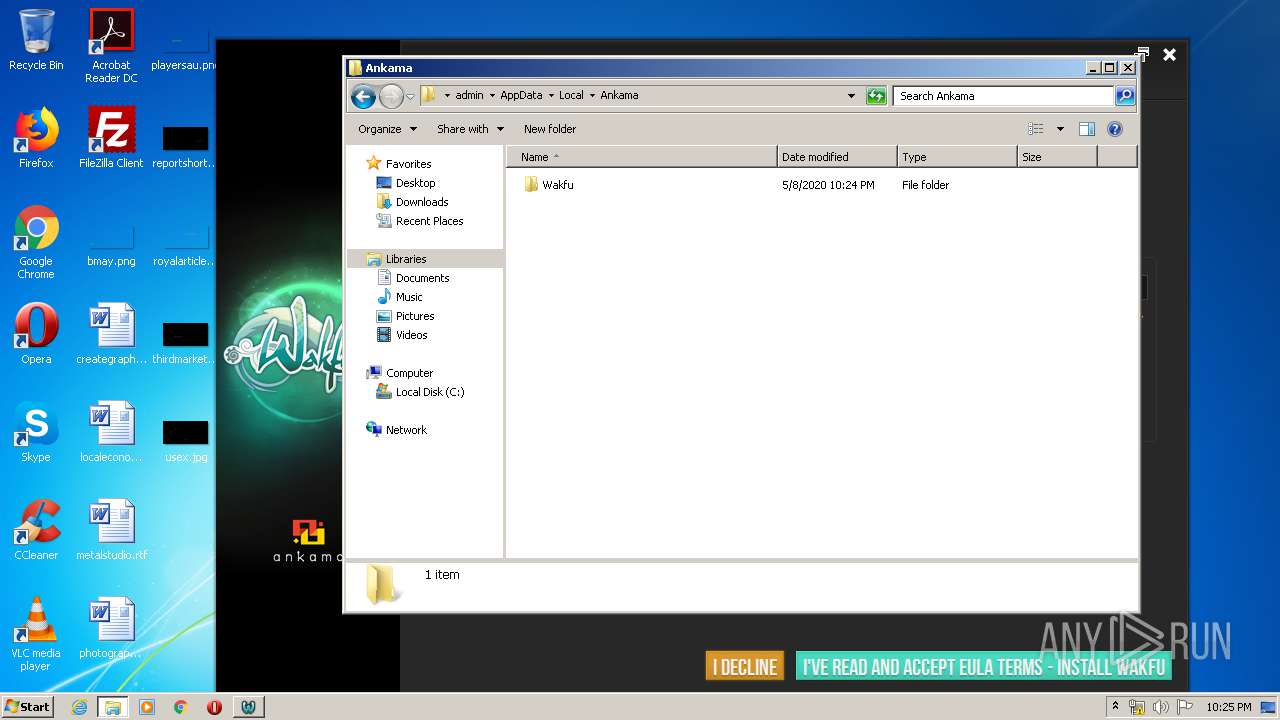
| CompanyName: | Ankama Studio |
| FileDescription: | Launcher Wakfu |
| FileVersion: | 3.11.1 |
| LegalCopyright: | (c) Ankama Studio 2015 |
| LegalTrademarks1: | All Rights Reserved |
| LegalTrademarks2: | All Rights Reserved |
| OriginalFileName: | Wakfu |
| ProductName: | Launcher Wakfu |
| ProductVersion: | 1.20150413.170616 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Apr-2015 06:32:15 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Ankama Studio |
| FileDescription: | Launcher Wakfu |
| FileVersion: | 3.11.1 |
| LegalCopyright: | (c) Ankama Studio 2015 |
| LegalTrademarks1: | All Rights Reserved |
| LegalTrademarks2: | All Rights Reserved |
| OriginalFilename: | Wakfu |
| ProductName: | Launcher Wakfu |
| ProductVersion: | 1.20150413.170616 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 16 |
| Time date stamp: | 21-Apr-2015 06:32:15 |
| Pointer to Symbol Table: | 0x00569A00 |
| Number of symbols: | 12566 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00088D3C | 0x00088E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.12418 |
.data | 0x0008A000 | 0x00006354 | 0x00006400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.125585 |
.rdata | 0x00091000 | 0x00007DE0 | 0x00007E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09027 |
.bss | 0x00099000 | 0x00002F80 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0009C000 | 0x000017E4 | 0x00001800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.40825 |
.CRT | 0x0009E000 | 0x00000034 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.278927 |
.tls | 0x0009F000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.22482 |
.rsrc | 0x000A0000 | 0x004A9444 | 0x004A9600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98055 |
/4 | 0x0054A000 | 0x00000500 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.20759 |
/19 | 0x0054B000 | 0x000110EF | 0x00011200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.98408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09584 | 1004 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.91401 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
3 | 2.94617 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
4 | 2.67456 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
5 | 2.56354 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
6 | 7.91701 | 7108 | UNKNOWN | English - United States | RT_ICON |
7 | 7.87471 | 17831 | UNKNOWN | English - United States | RT_ICON |
8 | 4.68142 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 4.36476 | 9640 | UNKNOWN | English - United States | RT_ICON |
10 | 1 | 2 | UNKNOWN | English - United States | RT_RCDATA |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
MSIMG32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.dll |
WINHTTP.dll |
msi.dll |
Total processes
49
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "transition.exe" "--no-footprint" "--no-restart" "--bootstrap-path=C:\Users\admin\AppData\Local\Temp\Wakfu.exe" "--launched-from=C:\Users\admin\AppData\Local\Temp" | C:\Users\admin\AppData\Local\Temp\akma02064\transition.exe | Wakfu.exe | ||||||||||||
User: admin Company: Ankama Integrity Level: MEDIUM Description: Updater Ankama Exit code: 0 Version: 3.2.0.0 Modules
| |||||||||||||||
| 2184 | "C:\Users\admin\AppData\Local\Temp\Wakfu.exe" | C:\Users\admin\AppData\Local\Temp\Wakfu.exe | explorer.exe | ||||||||||||
User: admin Company: Ankama Studio Integrity Level: MEDIUM Description: Launcher Wakfu Exit code: 0 Version: 3.11.1 Modules
| |||||||||||||||
| 2688 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3892 | "C:\Users\admin\AppData\Local\Temp\akma02064\transition-service.exe" "--port=49437" | C:\Users\admin\AppData\Local\Temp\akma02064\transition-service.exe | transition.exe | ||||||||||||
User: admin Company: Ankama Integrity Level: HIGH Description: Ankama update service Exit code: 0 Version: 3.2.0.0 Modules
| |||||||||||||||
Total events
451
Read events
430
Write events
21
Delete events
0
Modification events
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\styles |
| Operation: | write | Name: | ankamastyle.dll |
Value: 40805 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QStyleFactoryInterface:\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\styles |
| Operation: | write | Name: | ankamastyle.dll |
Value: 2020-05-08T22:24:21 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\updater |
| Operation: | write | Name: | core.dll |
Value: 40805 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\updater |
| Operation: | write | Name: | network_proxy.dll |
Value: 40805 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\updater |
| Operation: | write | Name: | diagnostic_tool.dll |
Value: 40805 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\updater |
| Operation: | write | Name: | optionsdialog.dll |
Value: 40805 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\updater |
| Operation: | write | Name: | uniqueinstance.dll |
Value: 40805 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\updater |
| Operation: | write | Name: | eula.dll |
Value: 40805 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\updater |
| Operation: | write | Name: | about.dll |
Value: 40805 | |||
| (PID) Process: | (312) transition.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\akma02064\plugins\imageformats |
| Operation: | write | Name: | qgif4.dll |
Value: 40805 | |||
Executable files
27
Suspicious files
0
Text files
50
Unknown types
13
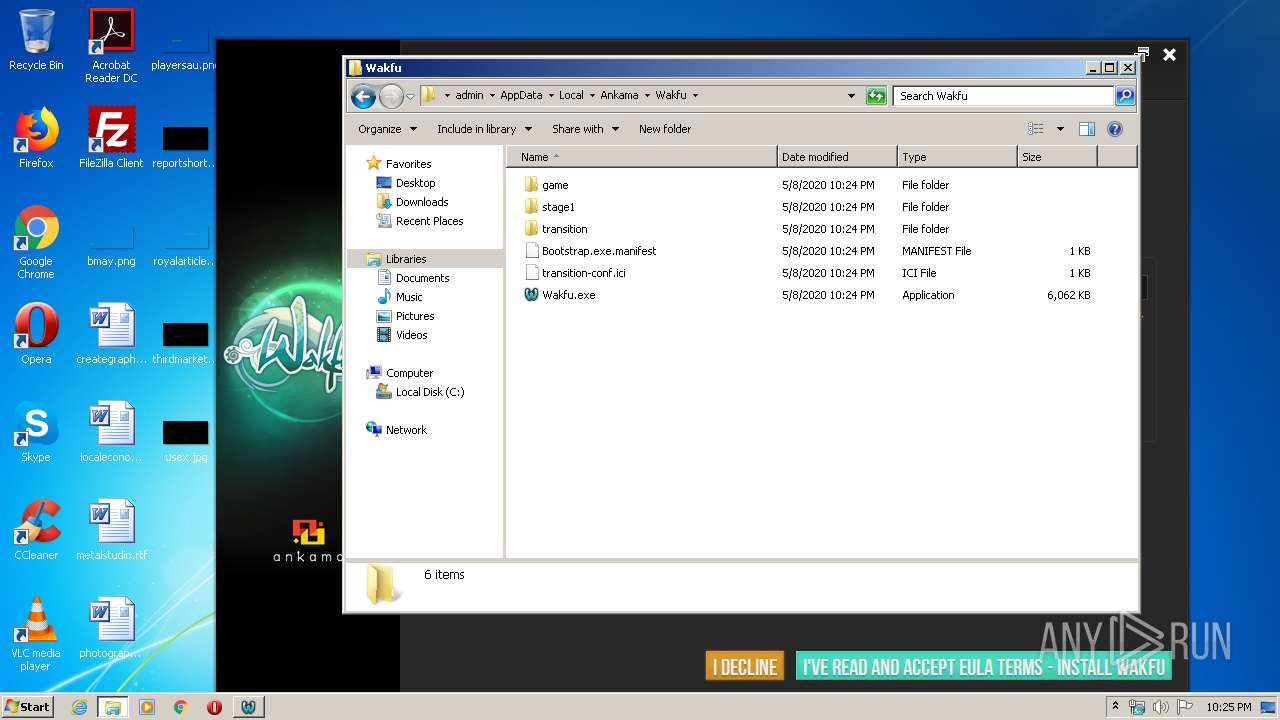
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\extra\stage1\installer_banner.jpg | image | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\VERSION | text | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\installer_banner.jpg | image | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\extra\stage1\repair_wakfu.png | image | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\installer_uninstall.png | image | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\extra\stage1\installer_uninstall.png | image | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\extra\stage1\eulas\eula_de.html | html | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\extra\stage1\eulas\eula_en.html | html | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\repair_wakfu.png | image | |
MD5:— | SHA256:— | |||
| 2184 | Wakfu.exe | C:\Users\admin\AppData\Local\Temp\akma02064\eulas\eula_es.html | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
8
DNS requests
1
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
312 | transition.exe | HEAD | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/transition-win32/updates/state.ici | US | text | 16 b | whitelisted |
312 | transition.exe | GET | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/transition-win32/updates/state.ici | US | text | 16 b | whitelisted |
312 | transition.exe | HEAD | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/wakfu/updates/state.ici | US | text | 16 b | whitelisted |
312 | transition.exe | HEAD | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/transition-win32/updates/state.ici | US | text | 16 b | whitelisted |
312 | transition.exe | HEAD | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/wakfu/updates/mesh | US | text | 16 b | whitelisted |
312 | transition.exe | HEAD | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/wakfu/updates/signature | US | text | 16 b | whitelisted |
312 | transition.exe | GET | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/transition-win32/updates/state.ici | US | text | 16 b | whitelisted |
312 | transition.exe | GET | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/wakfu/updates/state.ici | US | text | 16 b | whitelisted |
312 | transition.exe | GET | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/wakfu/updates/mesh | US | text | 16 b | whitelisted |
312 | transition.exe | GET | 403 | 104.16.71.20:80 | http://dl.ak.ankama.com/updates/uc1/projects/wakfu/updates/signature | US | text | 16 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
312 | transition.exe | 104.16.71.20:80 | dl.ak.ankama.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.ak.ankama.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
312 | transition.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
Process | Message |
|---|---|
transition.exe | |
transition.exe | transition.exe--no-footprint--no-restart--bootstrap-path=C:\Users\admin\AppData\Local\Temp\Wakfu.exe--launched-from=C:\Users\admin\AppData\Local\Temp |