| File name: | labelImg.exe |
| Full analysis: | https://app.any.run/tasks/4b4e6ca0-661a-4543-8a00-46f766f1a4df |
| Verdict: | Malicious activity |
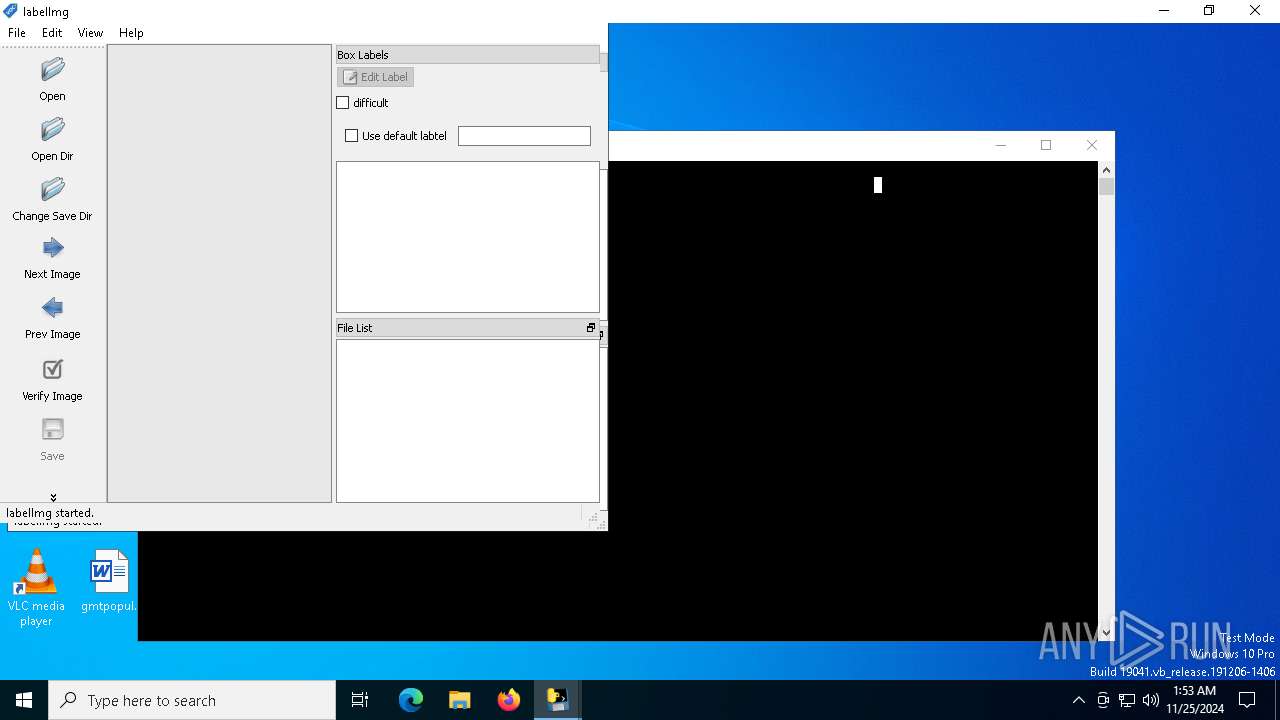
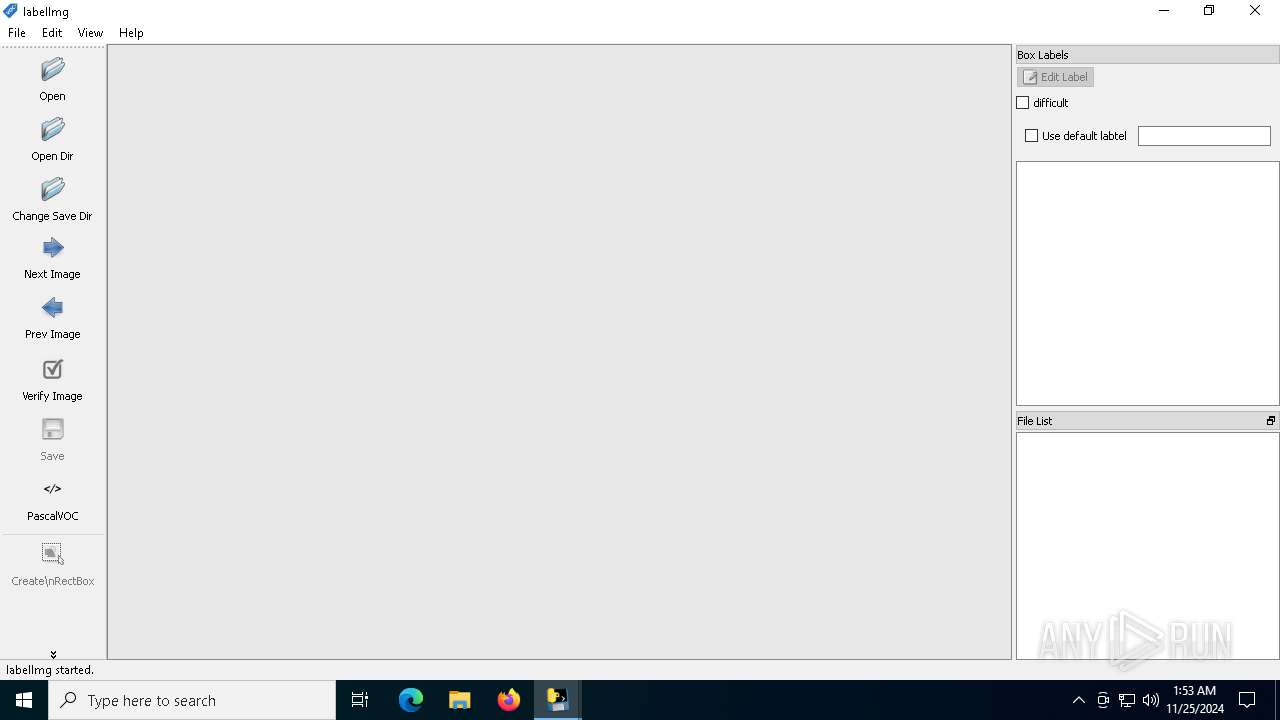
| Analysis date: | November 25, 2024, 01:52:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 4 sections |
| MD5: | 2265CE694442C118F5543689C8C61ECB |
| SHA1: | 1D88F572DBAC54087F6D068E748FF82CC2483763 |
| SHA256: | A288A77ED0D69AFE9F9128EC02760702BEB8E59665001AFCD92FF308423CAB83 |
| SSDEEP: | 98304:15/z/wx5NNhJAl4RcCjQvHI3WPY5Site9sn9DD5qy8qTd8E6XzQKy6NIuxmffUxU:ZJbRybZw80NHsm48CXmgtkzfQK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops python dynamic module
- labelImg.exe (PID: 2796)
Executable content was dropped or overwritten
- labelImg.exe (PID: 2796)
Application launched itself
- labelImg.exe (PID: 2796)
Reads security settings of Internet Explorer
- labelImg.exe (PID: 1544)
INFO
Checks supported languages
- labelImg.exe (PID: 2796)
- labelImg.exe (PID: 1544)
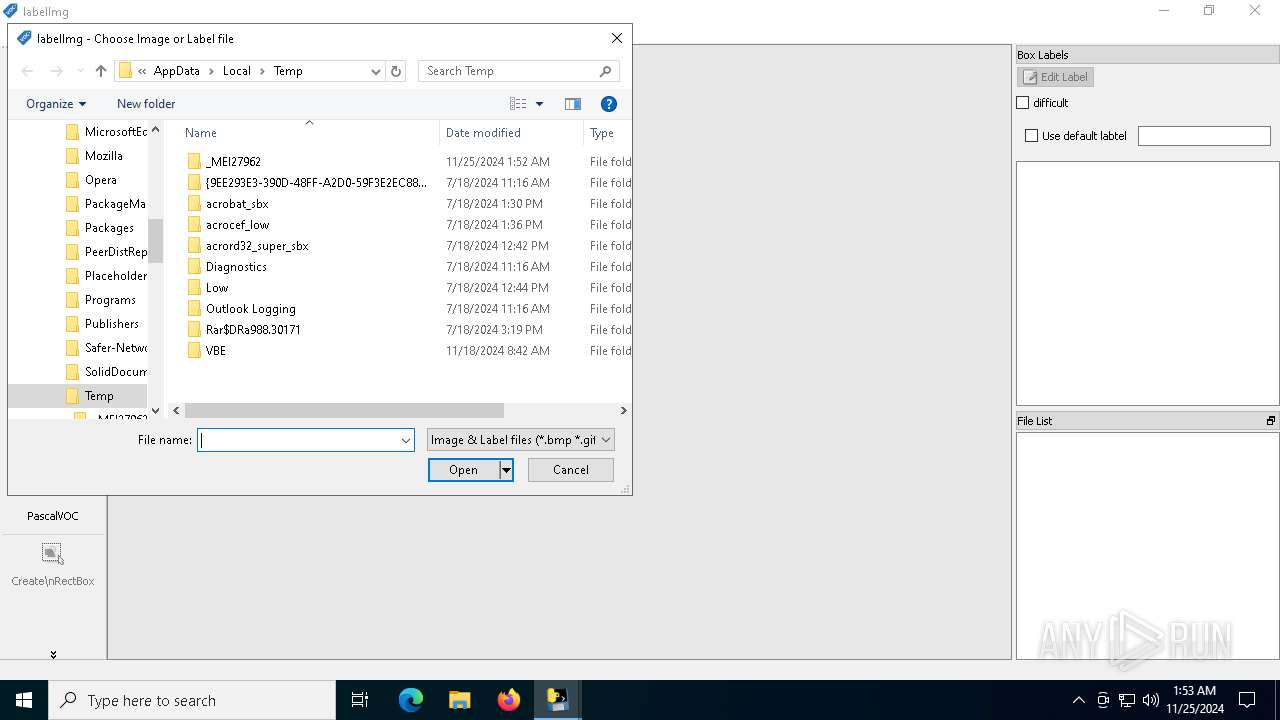
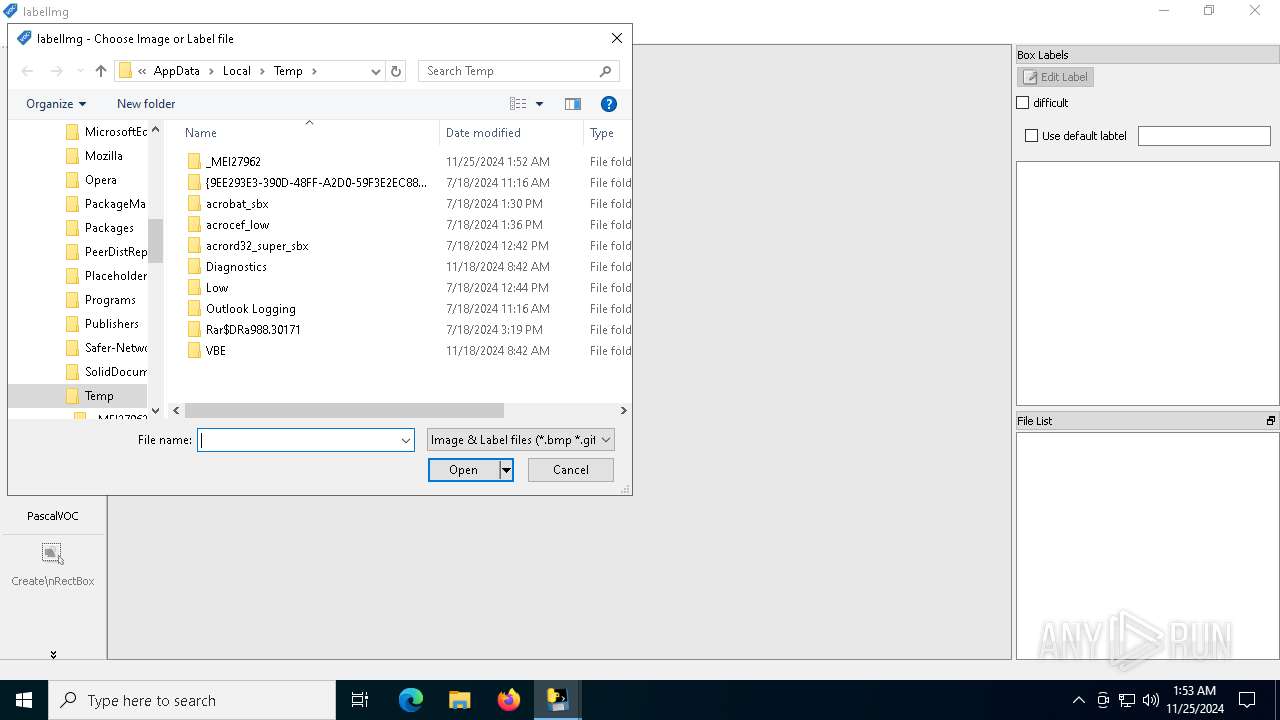
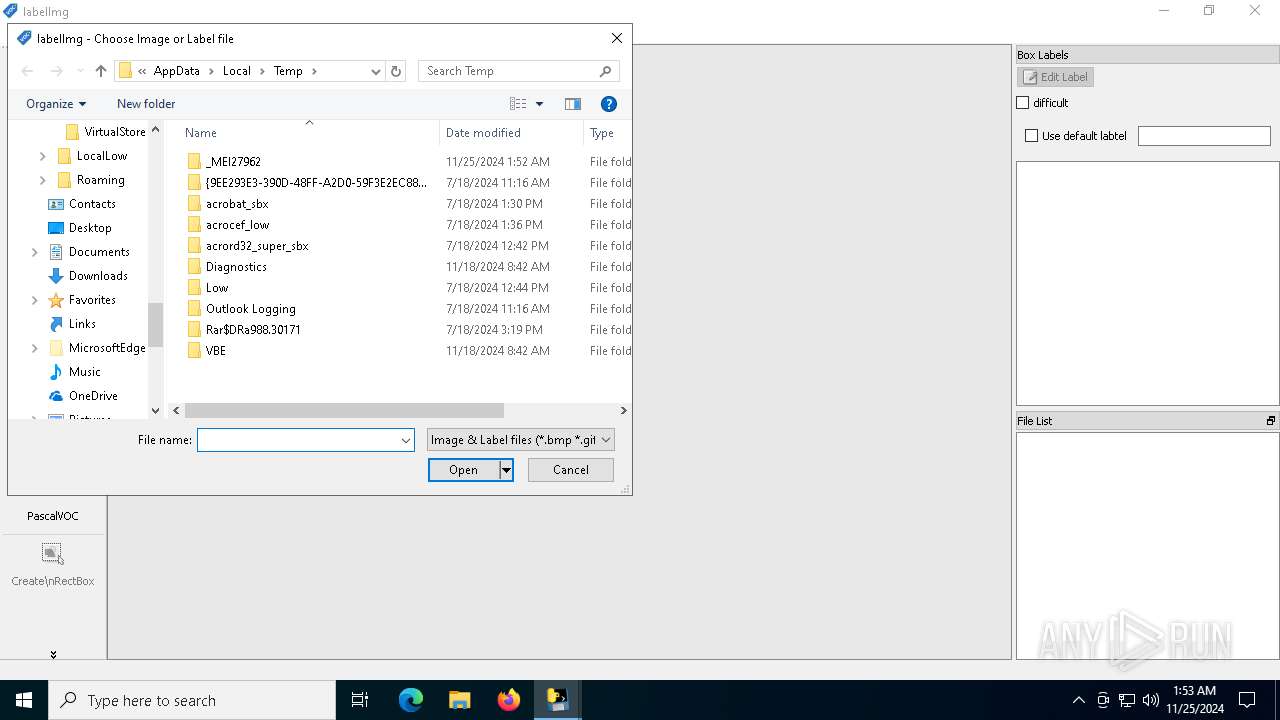
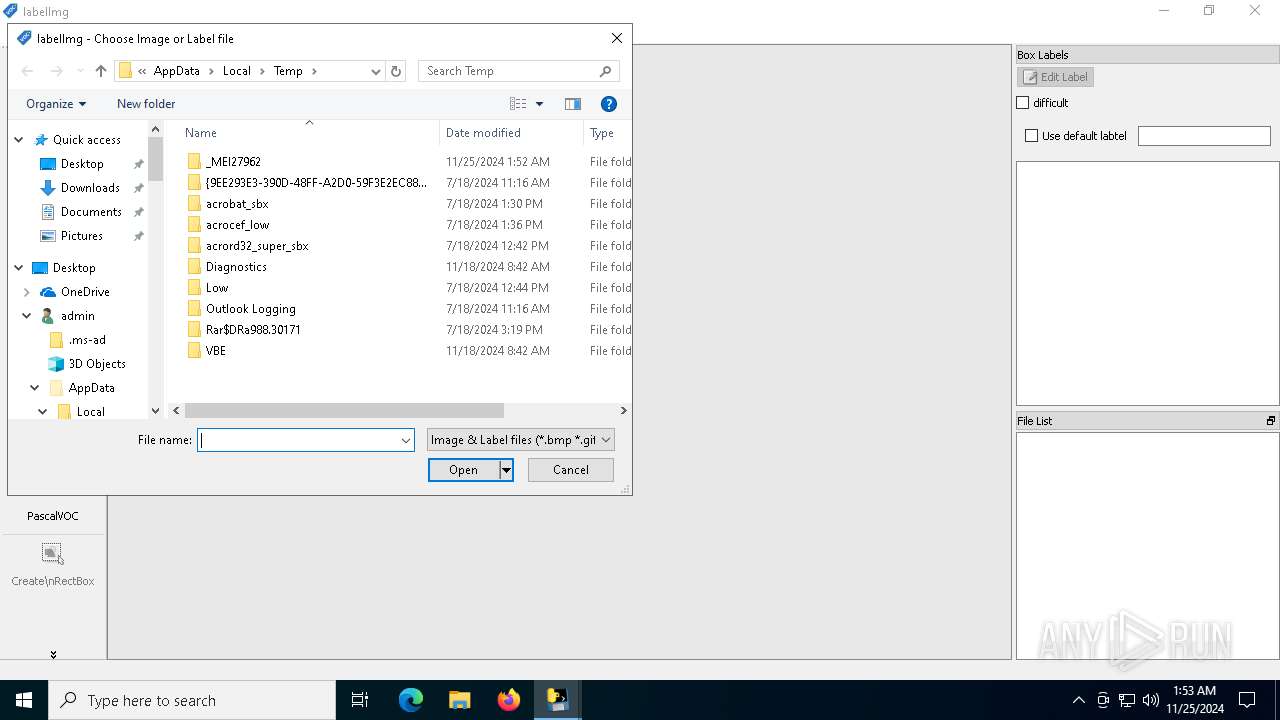
Create files in a temporary directory
- labelImg.exe (PID: 2796)
Reads the computer name
- labelImg.exe (PID: 1544)
Drops encrypted VBS script (Microsoft Script Encoder)
- labelImg.exe (PID: 1544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:03:23 22:26:54+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 105472 |
| InitializedDataSize: | 128512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb2f7 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
Total processes
128
Monitored processes
3
Malicious processes
2
Suspicious processes
0
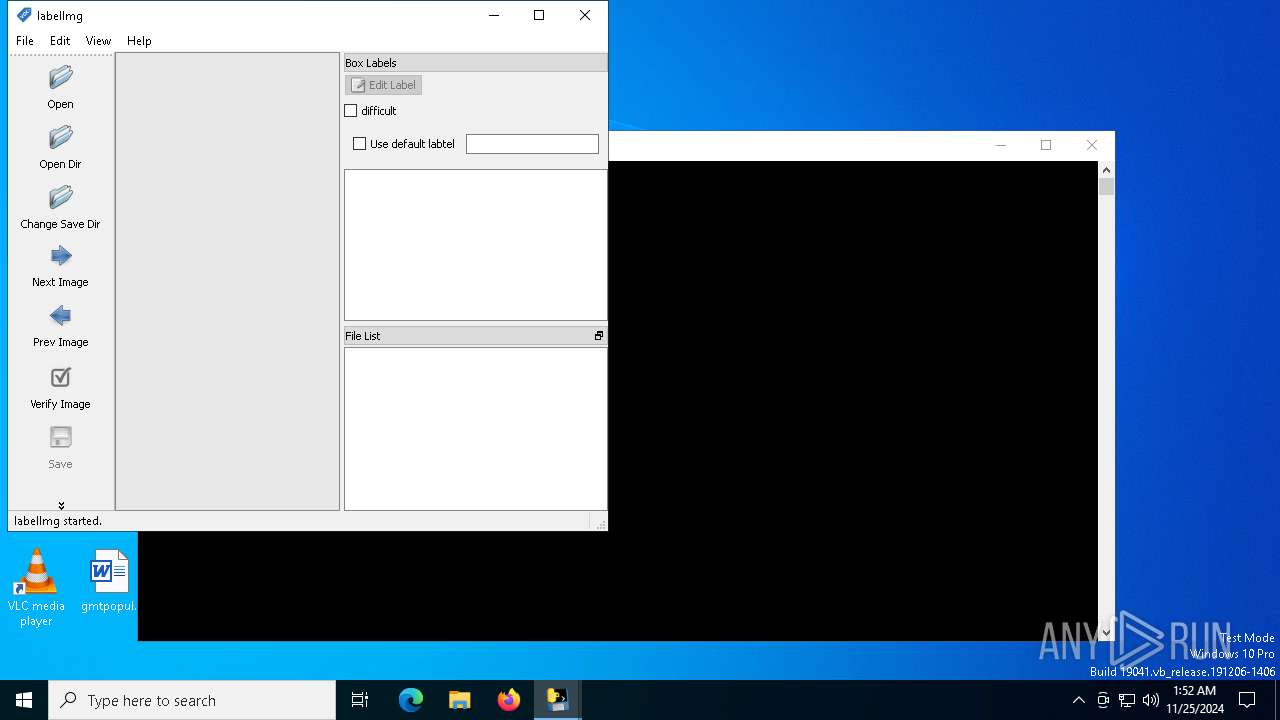
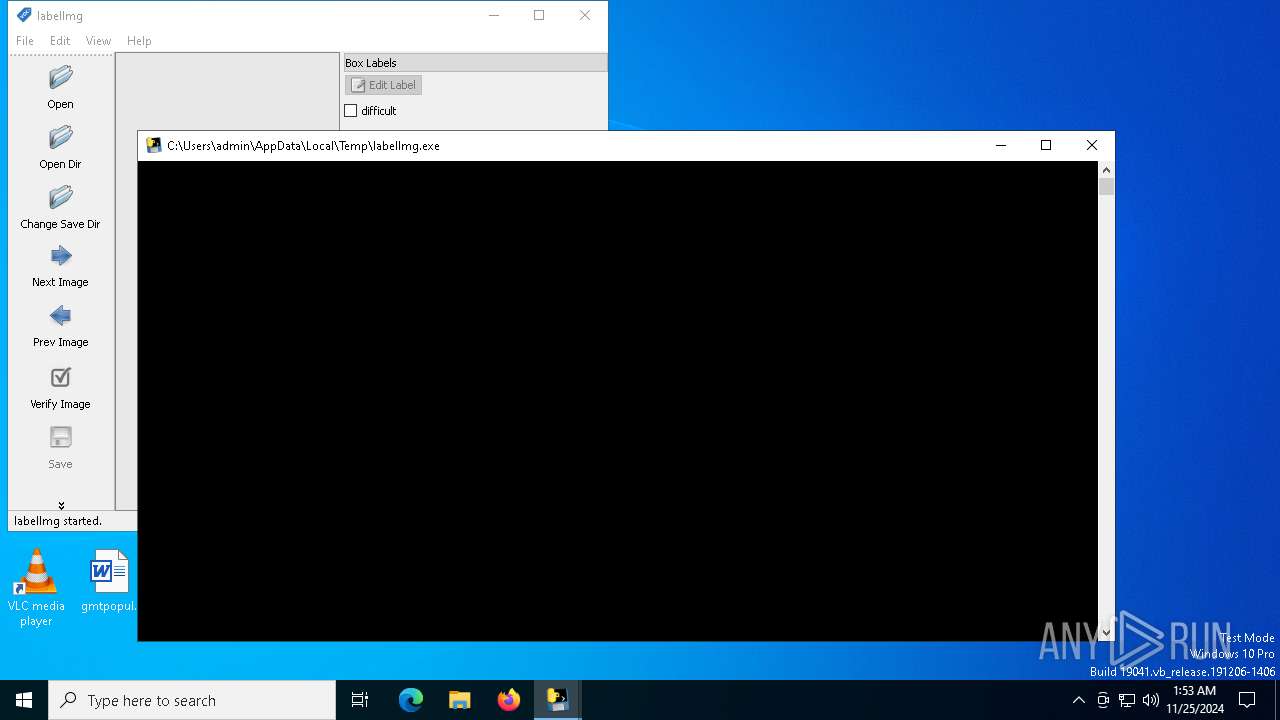
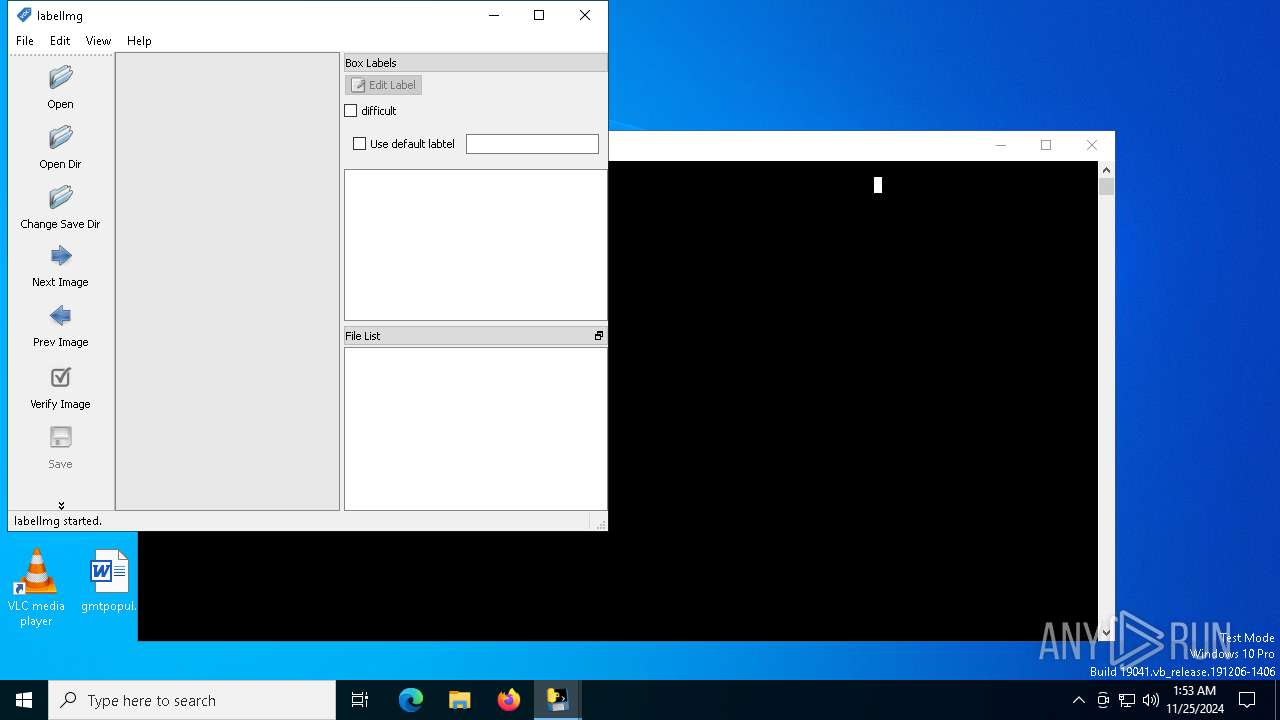
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1544 | "C:\Users\admin\AppData\Local\Temp\labelImg.exe" | C:\Users\admin\AppData\Local\Temp\labelImg.exe | — | labelImg.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2796 | "C:\Users\admin\AppData\Local\Temp\labelImg.exe" | C:\Users\admin\AppData\Local\Temp\labelImg.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | labelImg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 931
Read events
4 833
Write events
93
Delete events
5
Modification events
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qgif4.dll |
Value: 40807 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qgif4.dll |
Value: 2024-11-25T01:52:43 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qico4.dll |
Value: 40807 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qico4.dll |
Value: 2024-11-25T01:52:43 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qjpeg4.dll |
Value: 40807 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qjpeg4.dll |
Value: 2024-11-25T01:52:43 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qmng4.dll |
Value: 40807 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qmng4.dll |
Value: 2024-11-25T01:52:43 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qsvg4.dll |
Value: 40807 | |||
| (PID) Process: | (1544) labelImg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\imageformats |
| Operation: | write | Name: | qtga4.dll |
Value: 40807 | |||
Executable files
34
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\win32pipe.pyd | executable | |
MD5:E1F9FC63175A0E6799CBB58A094A80FA | SHA256:955E1A98D2DDCAA64ACF4E47135434E6557427B52D6BAC59AAAE2DAFEA463CD3 | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\python27.dll | executable | |
MD5:676FC65E4A49A525DF0ECDE3596F3AE5 | SHA256:C9192FE69D7EEF69B1E27E630AE643DCB0838B7BC0AC43E69A979F5A726256C1 | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\select.pyd | executable | |
MD5:4F1C033A4B8B1BC19565A78655C0E385 | SHA256:029D60725554EF87BF13C667B01AD32159DD2852FACA43F3A81D71D0062A3A33 | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\_ssl.pyd | executable | |
MD5:6F47CDDCC5C74CF22A1B5CF710935EBF | SHA256:D9FADB044CA15EE133F157180197F6867FE21D03FB3A4F601A6F356150F1D08D | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\unicodedata.pyd | executable | |
MD5:B4530ADC9CBA15114A001D1AAE2E98B3 | SHA256:C7C85F717B8A3676716BB2106E31B288EA1DFE90D1802180169CF92488F47DDE | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\pyexpat.pyd | executable | |
MD5:67DA26AED9CBD7FCEBE9F7B8CE0A6448 | SHA256:0B7FC6F03587372C01F717F9B63B646AD2F6E18D139B792921399B4CEF0B65E1 | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\accessible\qtaccessiblewidgets4.dll | executable | |
MD5:C3109CAF637EA01EB6165F472A6FE820 | SHA256:25A520A44B3292A1C65D23C07B6B36DF69BE9018BA250AB2E24D5C5116C3B77E | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\codecs\qjpcodecs4.dll | executable | |
MD5:875A260560C78F5DAB835AB84A3DC2ED | SHA256:1896B90FAB05A0C9D53D3B2D954728B99903FD29D466401FC8948AB07135B413 | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\PyQt4.QtGui.pyd | executable | |
MD5:B806D430EC727119799BF314659CED0C | SHA256:15F50E8FBDF2EF5524F331978B267582B6196B5379993478DCED546E51250253 | |||
| 2796 | labelImg.exe | C:\Users\admin\AppData\Local\Temp\_MEI27962\qt4_plugins\codecs\qkrcodecs4.dll | executable | |
MD5:8A4AC179E4BEAE544712414707D9DBC3 | SHA256:E76FD99799D5FE8F247D3026BF05966B93941358CBE404A546DAB30356D215CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4076 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1448 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1448 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6092 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |