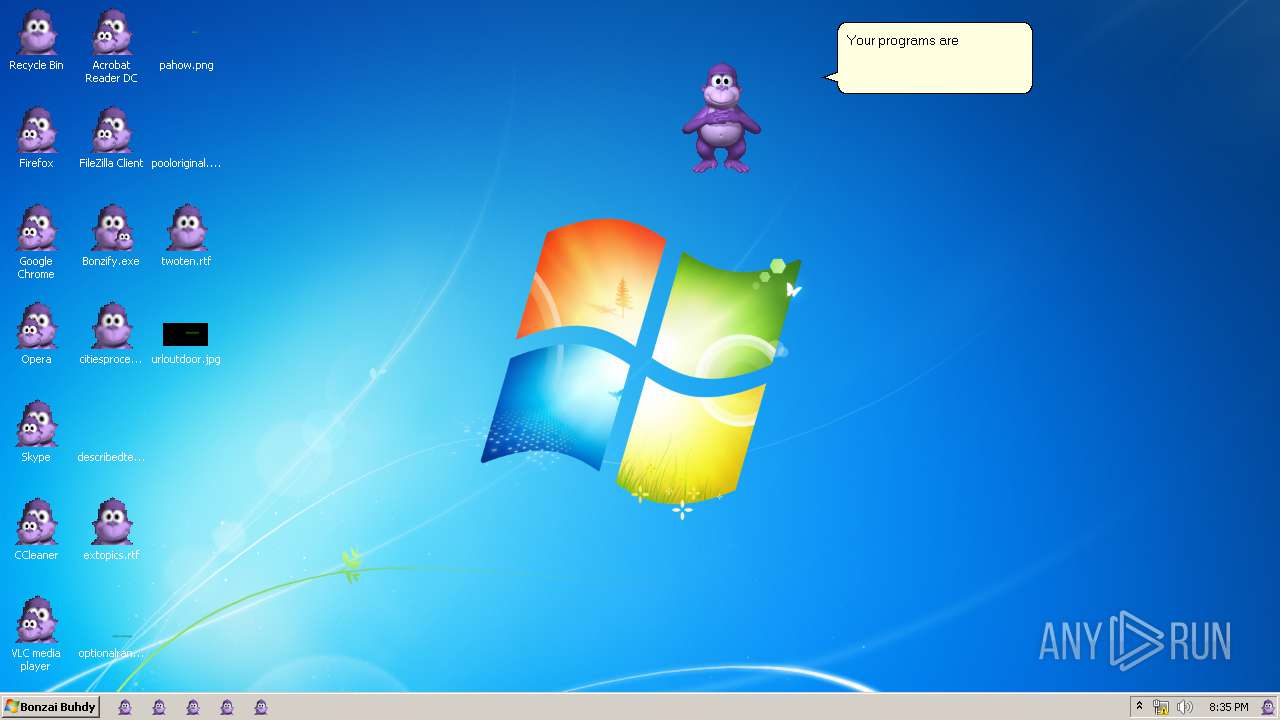
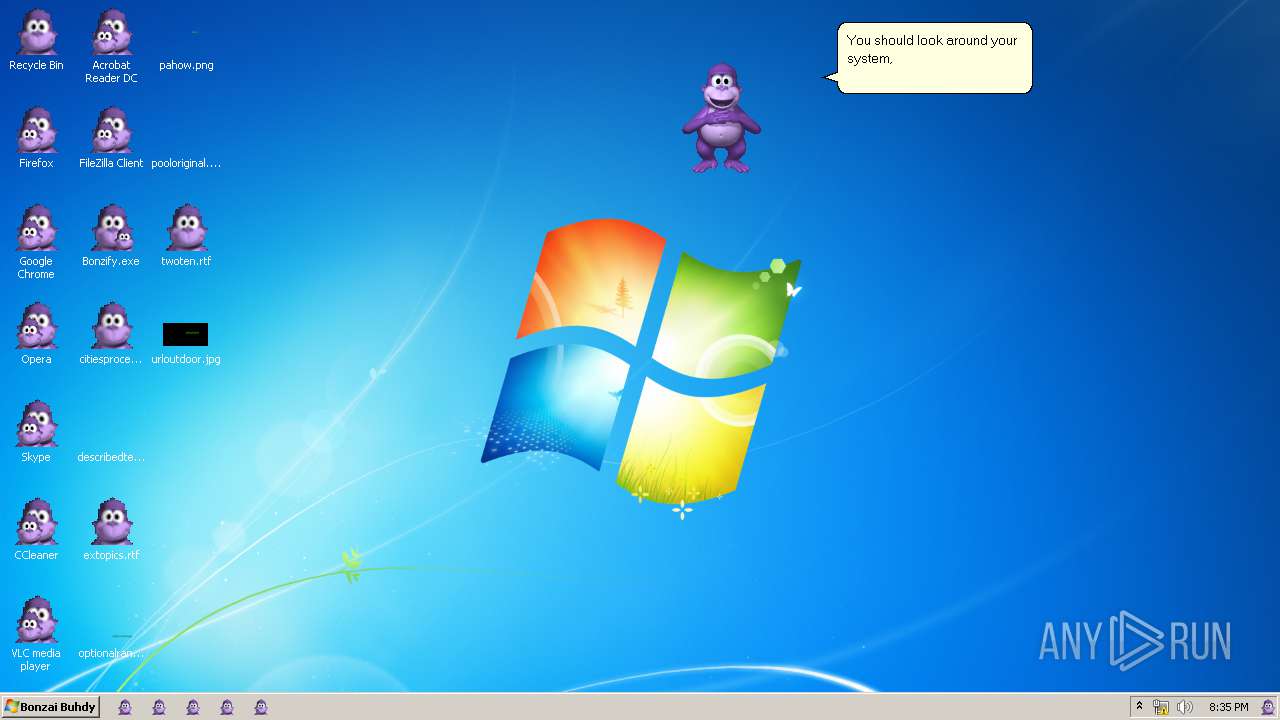
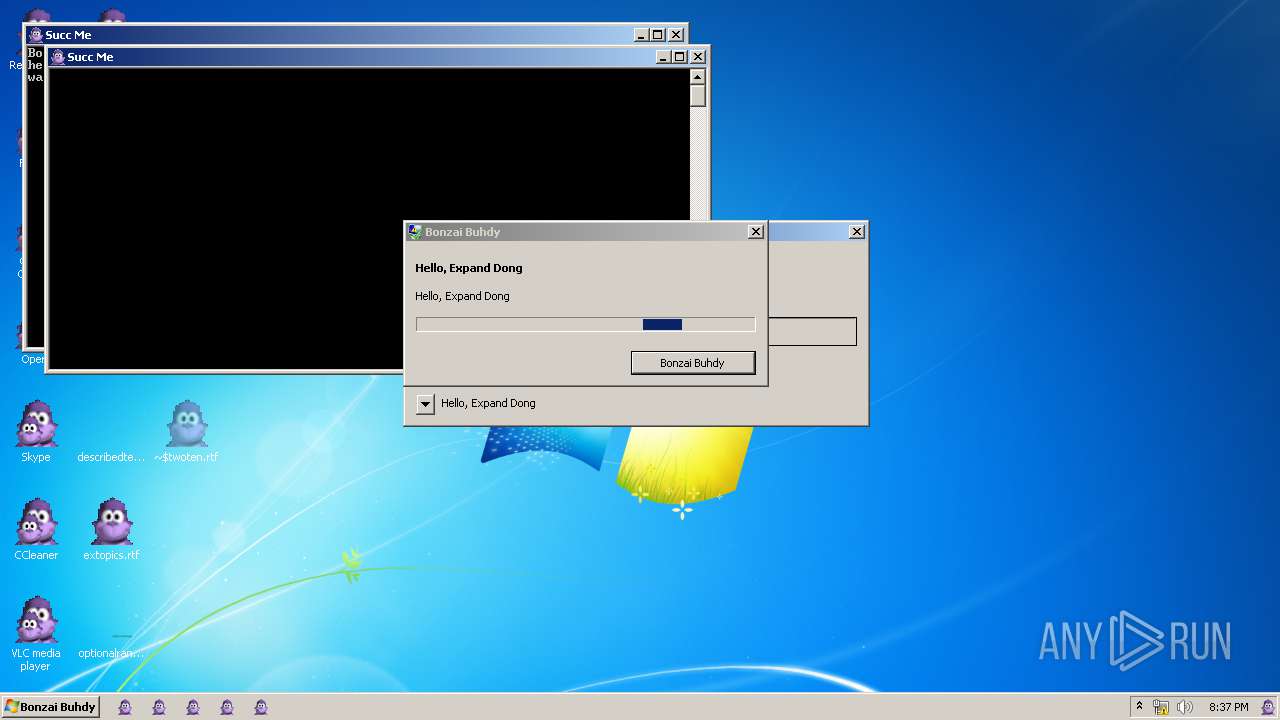
| File name: | Bonzify.exe |
| Full analysis: | https://app.any.run/tasks/7213d1cd-0db9-4810-ab81-01c0b946a5d3 |
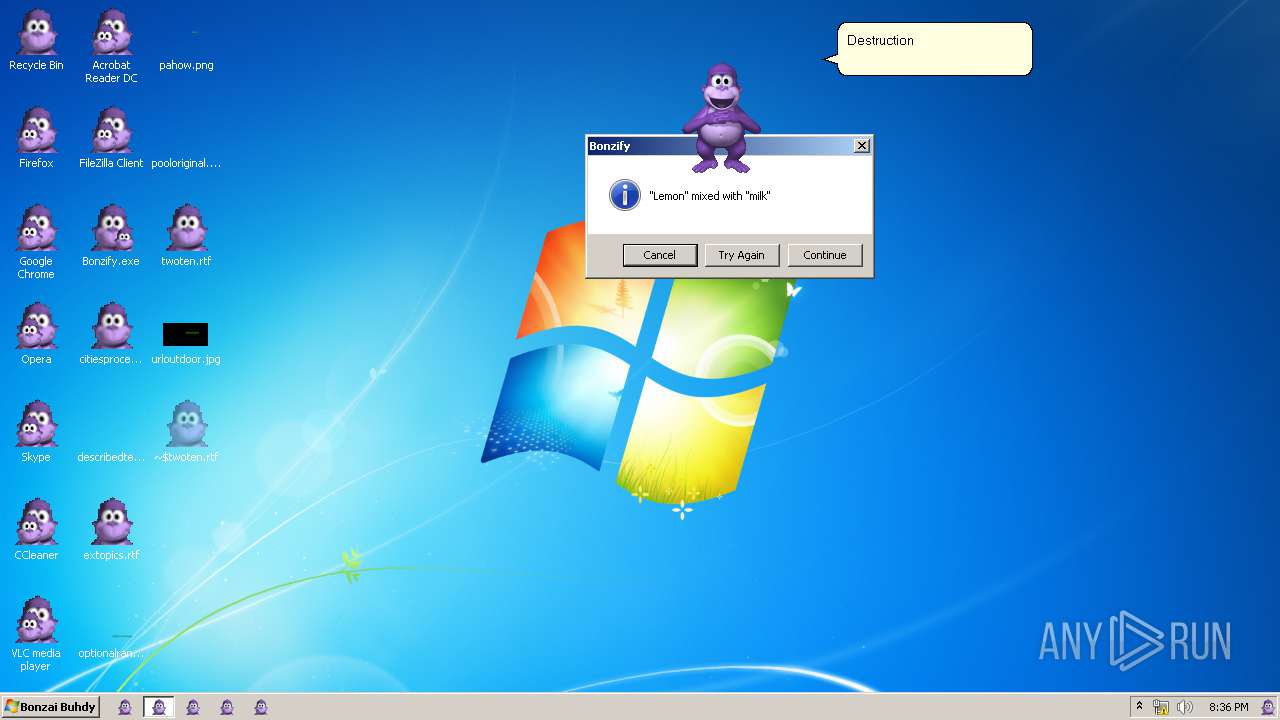
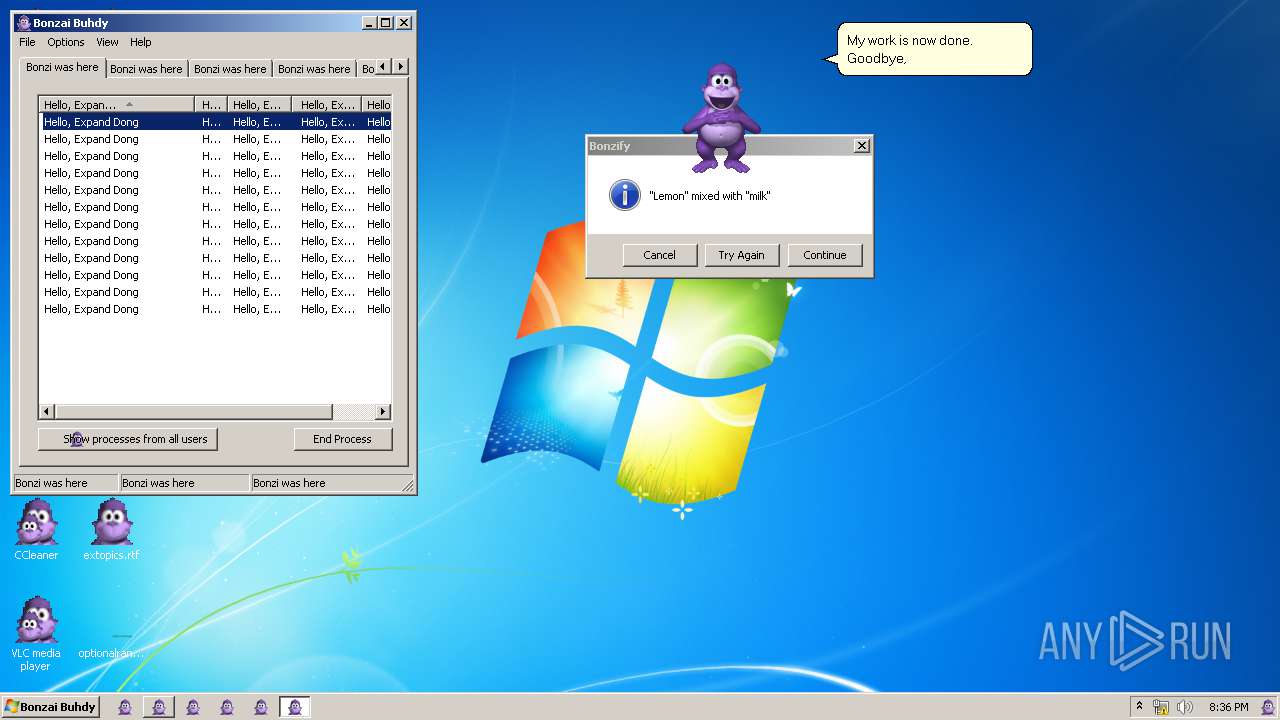
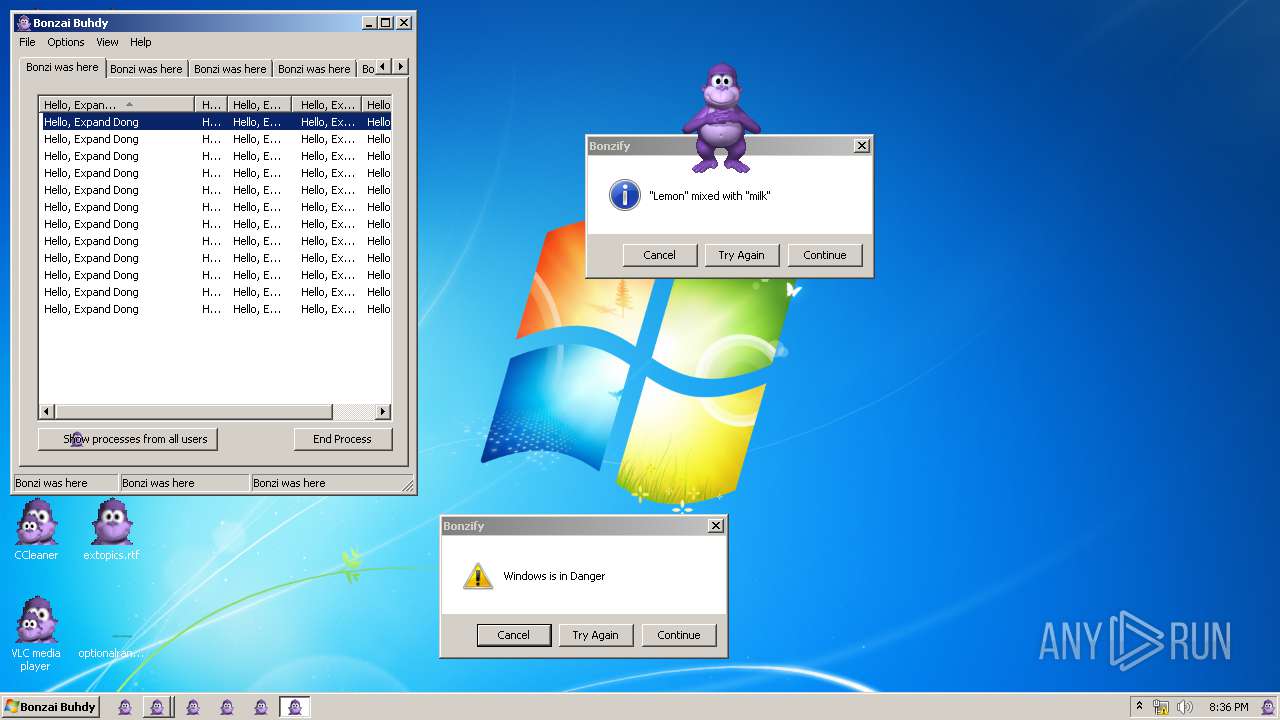
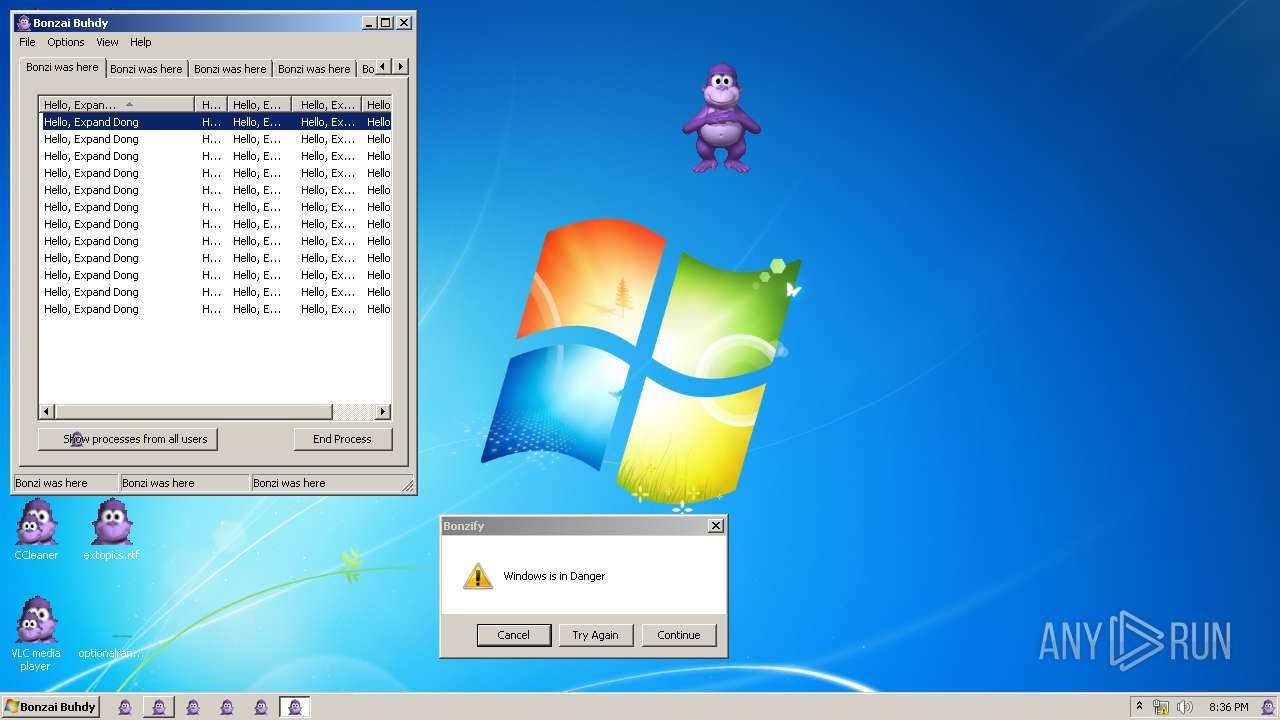
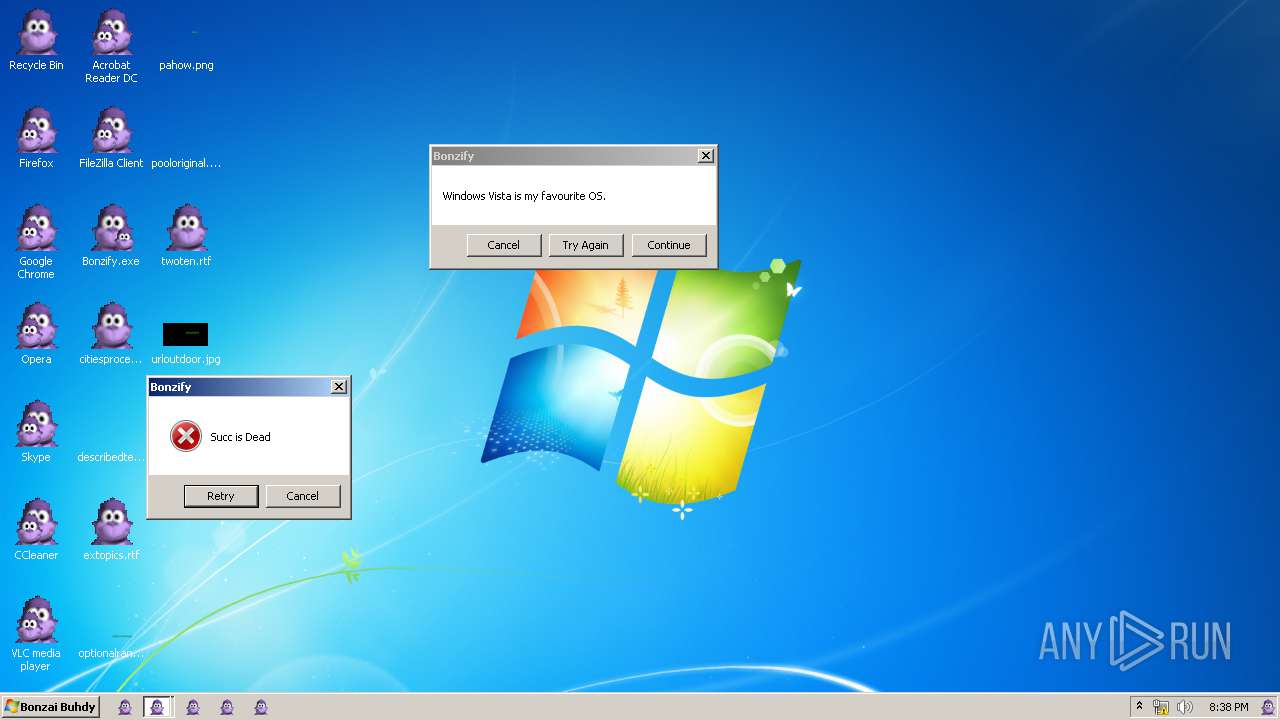
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 19:33:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0D4F41A264B6BA17F9B0D2B698A991E6 |
| SHA1: | E13E1FACBCB92267D8E124ED3298DD35594AC9F4 |
| SHA256: | A2788DB60E63CA687412193B80ADB7D9D95D9C4135B8A26387DFC1A0475C2962 |
| SSDEEP: | 196608:1dAMaWetTeAkLIdx751qFTkub//73lc6u7b5VJ2Yx5xIdk3:RaWedh+Idx75QYub//73lc6u7bLMYxD |
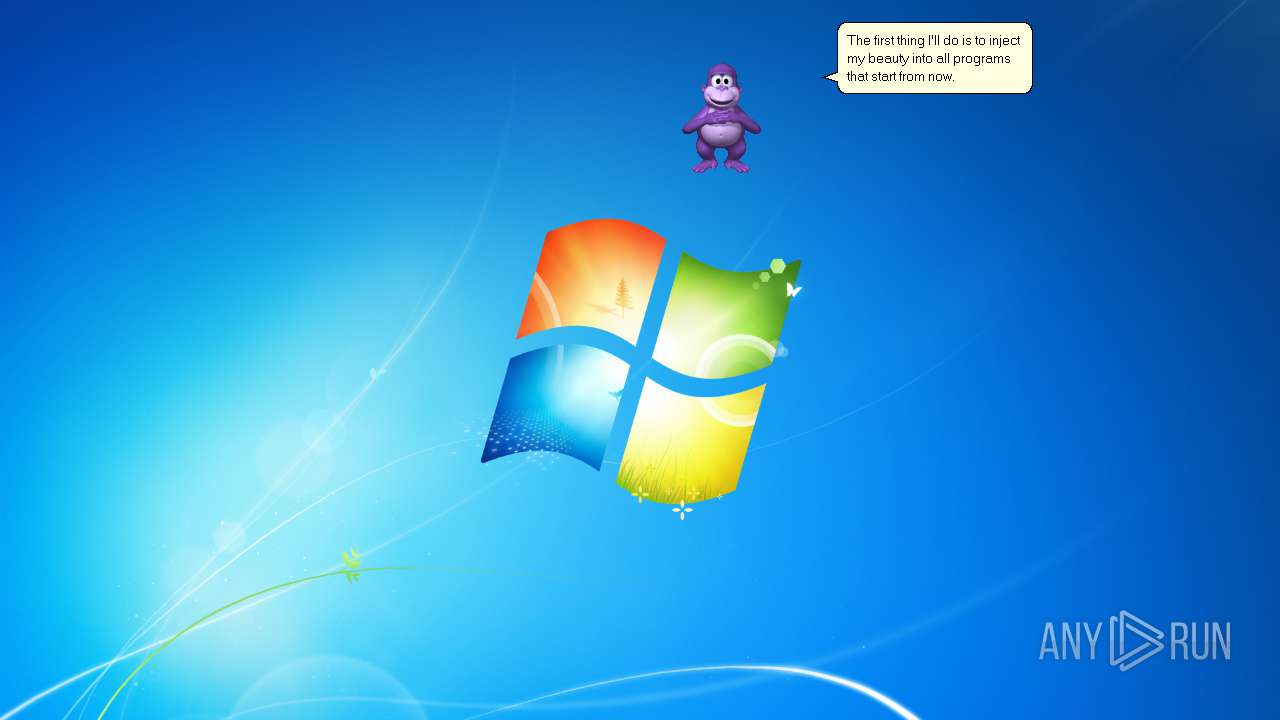
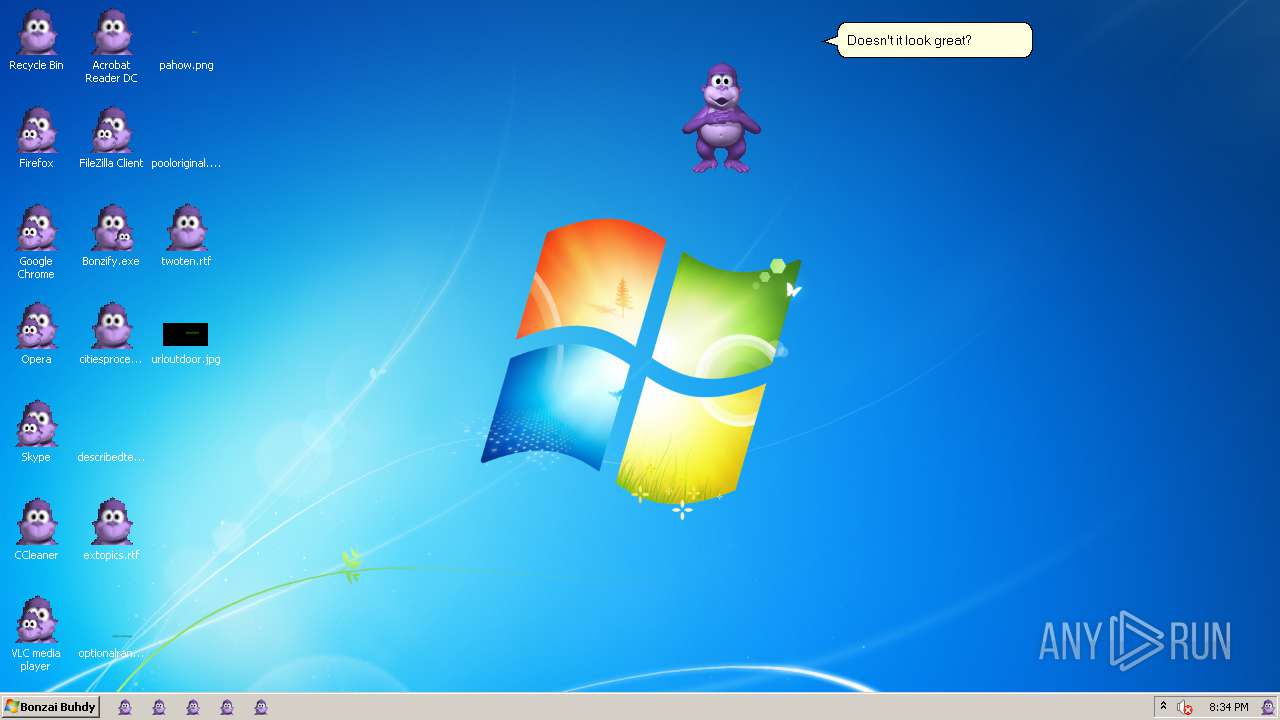
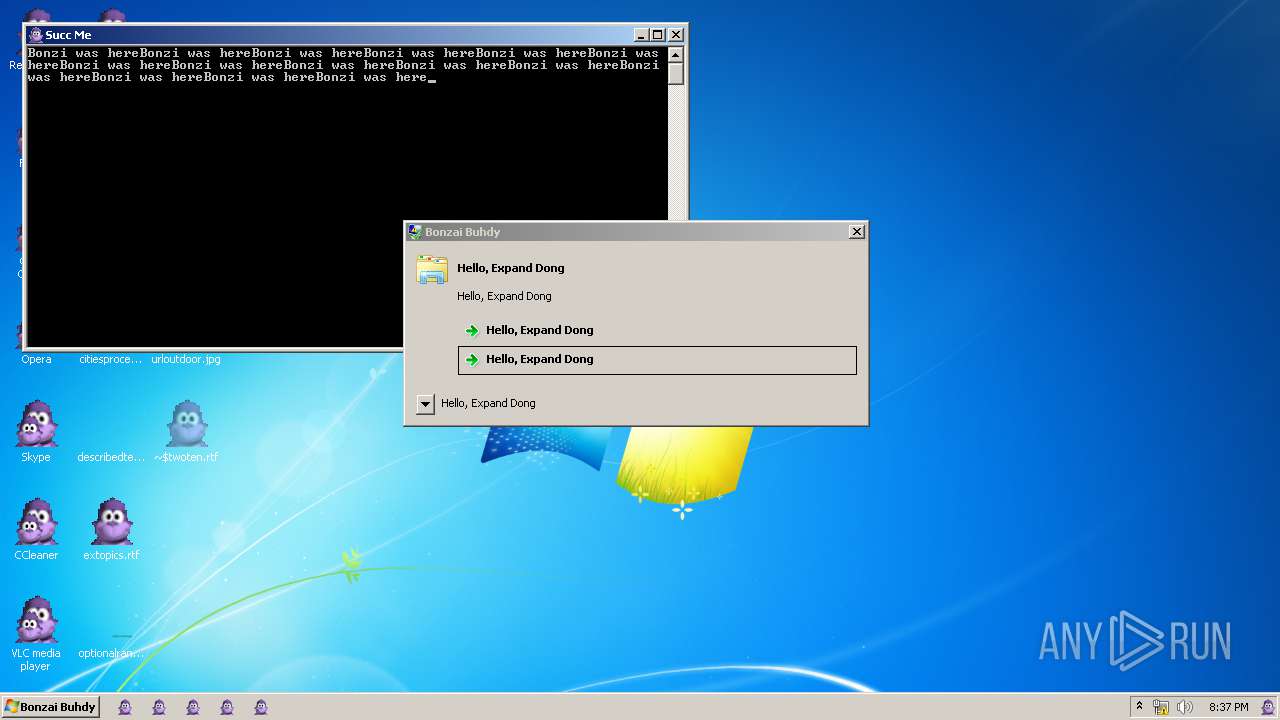
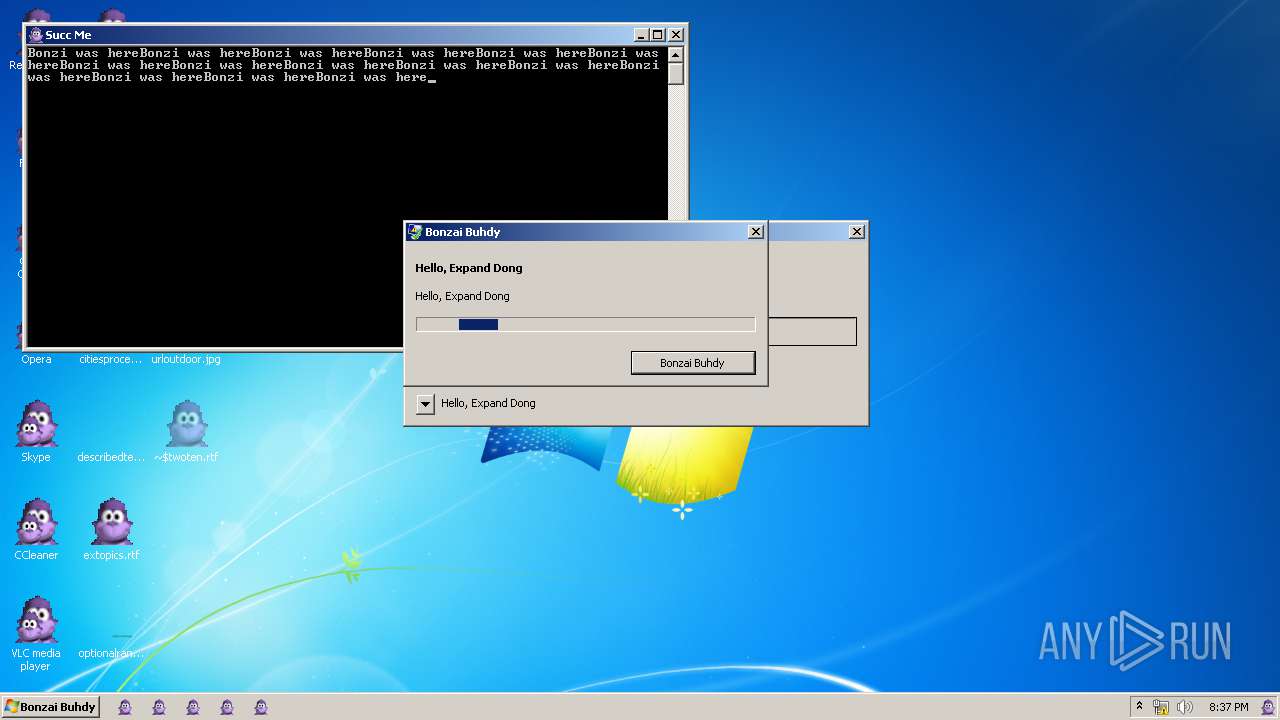
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 2752)
- INSTALLER.exe (PID: 3736)
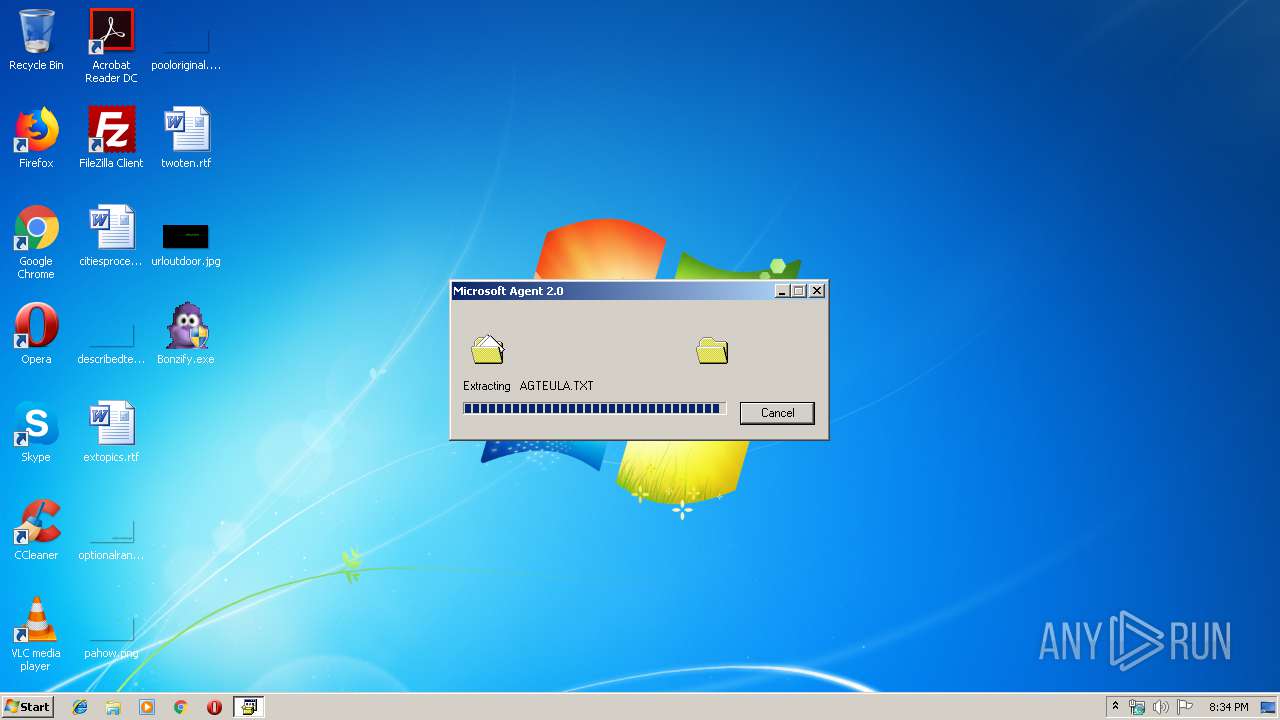
Application was dropped or rewritten from another process
- INSTALLER.exe (PID: 2752)
- INSTALLER.exe (PID: 3736)
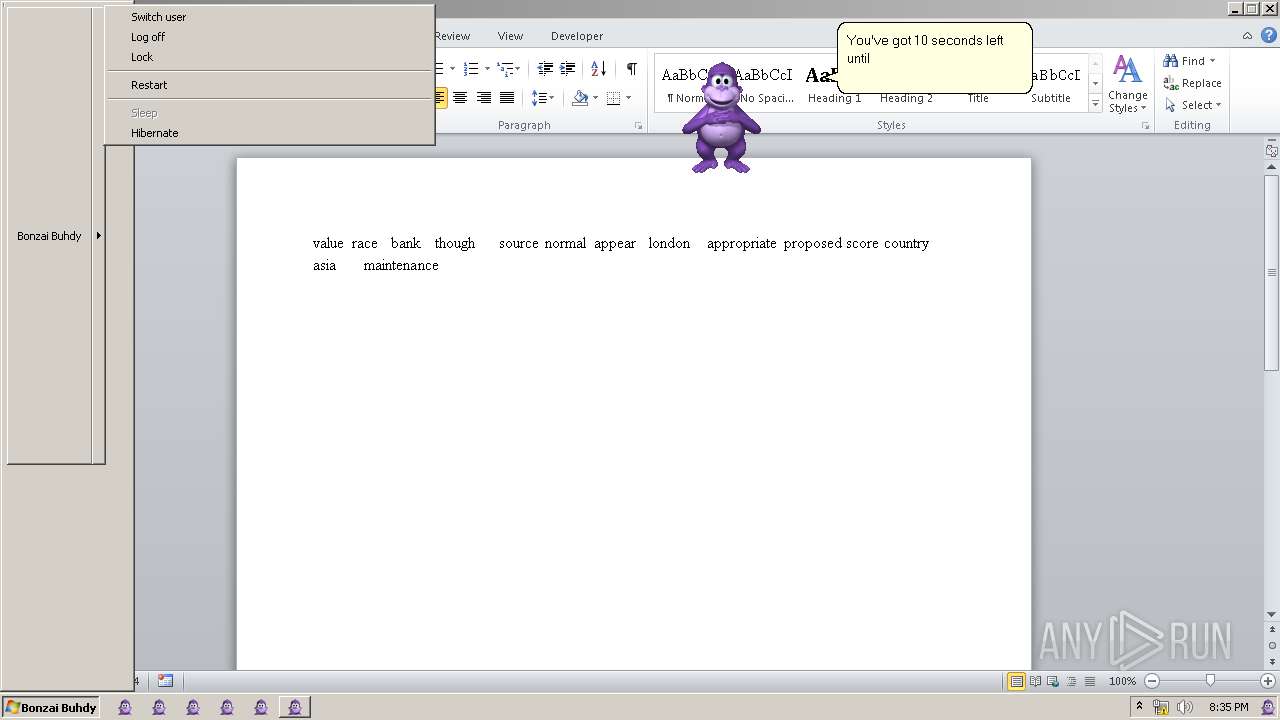
Changes the autorun value in the registry
- INSTALLER.exe (PID: 3736)
- Bonzify.exe (PID: 3008)
- explorer.exe (PID: 2320)
- WINWORD.EXE (PID: 1188)
- taskmgr.exe (PID: 1016)
- DllHost.exe (PID: 3300)
- ehmsas.exe (PID: 2836)
- explorer.exe (PID: 2964)
- svchost.exe (PID: 2820)
- raserver.exe (PID: 3708)
- WerFault.exe (PID: 812)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2732)
- AgentSvr.exe (PID: 4024)
- INSTALLER.exe (PID: 3736)
- INSTALLER.exe (PID: 2752)
- regsvr32.exe (PID: 3812)
- explorer.exe (PID: 2320)
- DllHost.exe (PID: 1032)
- WINWORD.EXE (PID: 1188)
- SearchProtocolHost.exe (PID: 1732)
- DllHost.exe (PID: 1752)
- svchost.exe (PID: 3992)
- OSPPSVC.EXE (PID: 2604)
- WerFault.exe (PID: 3908)
- WerFault.exe (PID: 2400)
- SearchProtocolHost.exe (PID: 2248)
- DllHost.exe (PID: 2856)
- werfault.exe (PID: 3864)
- taskmgr.exe (PID: 1016)
- WerFault.exe (PID: 3188)
- WerFault.exe (PID: 4060)
- conhost.exe (PID: 1348)
- WerFault.exe (PID: 3096)
- wermgr.exe (PID: 2596)
- conhost.exe (PID: 3716)
- conhost.exe (PID: 3036)
- RMActivate.exe (PID: 2224)
- IMEPADSV.EXE (PID: 3032)
- aspnet_state.exe (PID: 3932)
- taskmgr.exe (PID: 3092)
- SearchIndexer.exe (PID: 2448)
- wmpshare.exe (PID: 2824)
- svchost.exe (PID: 3296)
- consent.exe (PID: 2348)
- DllHost.exe (PID: 3084)
- svchost.exe (PID: 2820)
- DllHost.exe (PID: 1432)
- conhost.exe (PID: 1796)
- openfiles.exe (PID: 2284)
- WerFault.exe (PID: 3140)
- IMTCPROP.exe (PID: 1520)
- conhost.exe (PID: 3784)
- NAPSTAT.EXE (PID: 2584)
- conhost.exe (PID: 3428)
- DllHost.exe (PID: 3300)
- wermgr.exe (PID: 2304)
- jsc.exe (PID: 3028)
- secinit.exe (PID: 2480)
- conhost.exe (PID: 2552)
- conhost.exe (PID: 2768)
- posix.exe (PID: 2784)
- conhost.exe (PID: 3904)
- ntvdm.exe (PID: 3680)
- isoburn.exe (PID: 3648)
- conhost.exe (PID: 3984)
- WerFault.exe (PID: 2072)
- SetupUtility.exe (PID: 3688)
- MdRes.exe (PID: 3452)
- sbunattend.exe (PID: 3524)
- ehmsas.exe (PID: 2836)
- qprocess.exe (PID: 3160)
- conhost.exe (PID: 4080)
- wmpnscfg.exe (PID: 3396)
- WerFault.exe (PID: 1856)
- LocationNotifications.exe (PID: 284)
- conhost.exe (PID: 2720)
- msg.exe (PID: 2440)
- conhost.exe (PID: 3364)
- aspnet_state.exe (PID: 1396)
- explorer.exe (PID: 2964)
- rdrleakdiag.exe (PID: 3228)
- WerFault.exe (PID: 3920)
- wbengine.exe (PID: 3500)
- lodctr.exe (PID: 1008)
- conhost.exe (PID: 2712)
- conhost.exe (PID: 316)
- netcfg.exe (PID: 3812)
- fxssvc.exe (PID: 1576)
- WmiPrvSE.exe (PID: 1052)
- sdiagnhost.exe (PID: 1952)
- IMJPDSVR.EXE (PID: 2296)
- conhost.exe (PID: 2544)
- conhost.exe (PID: 3780)
- appidpolicyconverter.exe (PID: 3248)
- WFS.exe (PID: 116)
- cmak.exe (PID: 2908)
- raserver.exe (PID: 3708)
- extrac32.exe (PID: 2872)
- conhost.exe (PID: 2288)
- WerFault.exe (PID: 812)
- winlogon.exe (PID: 2632)
- ehshell.exe (PID: 3800)
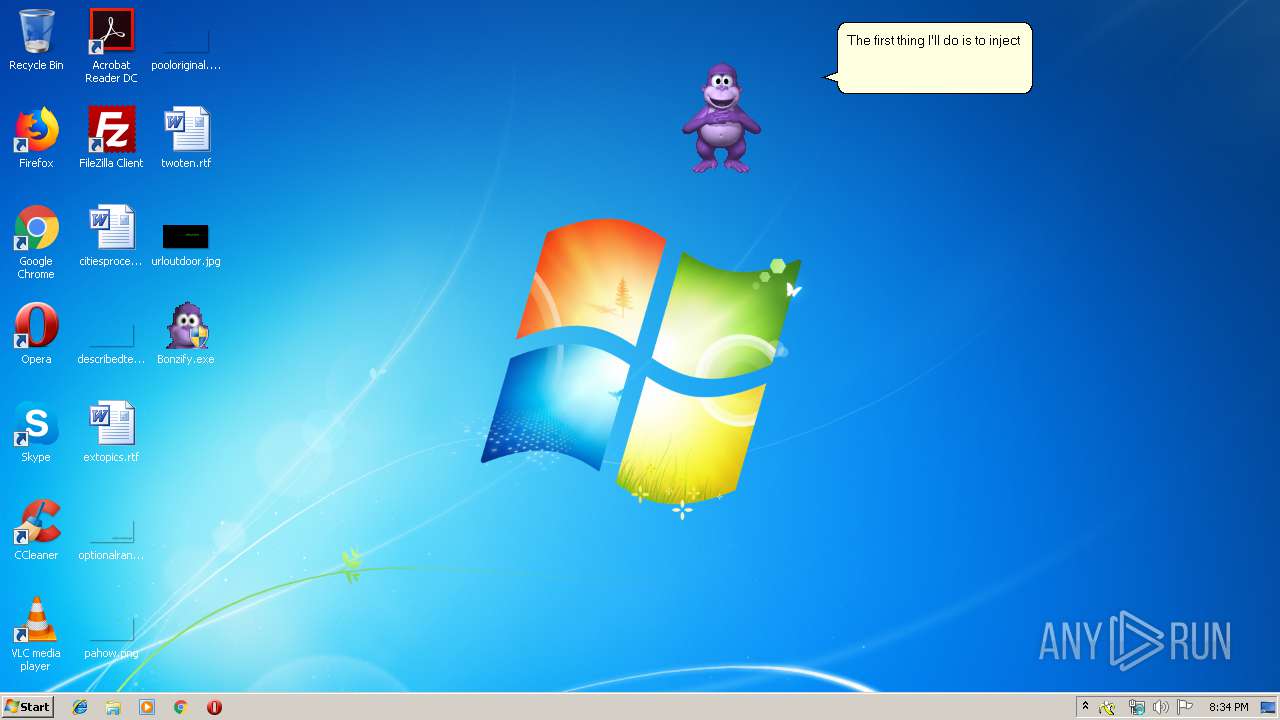
Changes AppInit_DLLs value (autorun option)
- Bonzify.exe (PID: 3008)
Loads the Task Scheduler COM API
- explorer.exe (PID: 2320)
- explorer.exe (PID: 2964)
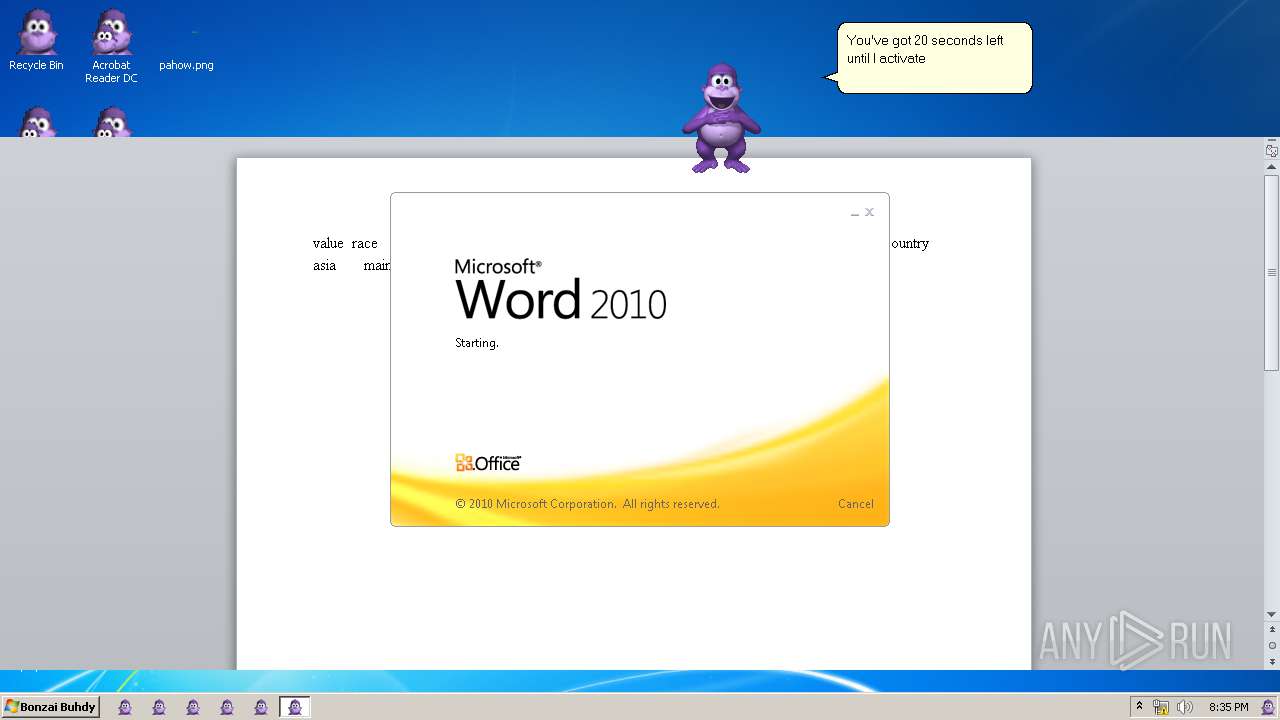
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1188)
Changes internet zones settings
- WerFault.exe (PID: 3096)
- OSPPSVC.EXE (PID: 2604)
- taskmgr.exe (PID: 1016)
- explorer.exe (PID: 2320)
- DllHost.exe (PID: 3084)
- taskmgr.exe (PID: 3092)
- svchost.exe (PID: 2820)
- conhost.exe (PID: 3784)
- WerFault.exe (PID: 3140)
- posix.exe (PID: 2784)
- WerFault.exe (PID: 2072)
- conhost.exe (PID: 4080)
- LocationNotifications.exe (PID: 284)
- WerFault.exe (PID: 3920)
- explorer.exe (PID: 2964)
- WerFault.exe (PID: 812)
- cmak.exe (PID: 2908)
Changes the Startup folder
- svchost.exe (PID: 2820)
Modifies Windows Defender service settings
- svchost.exe (PID: 2820)
SUSPICIOUS
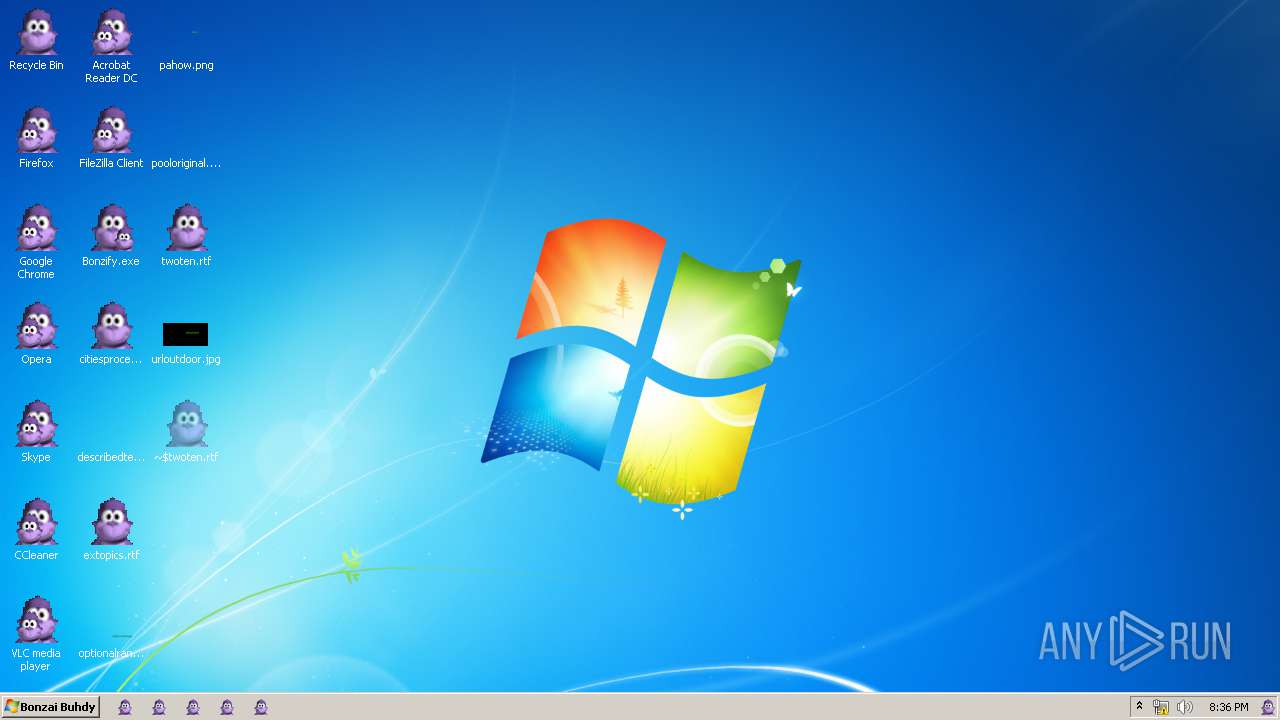
Creates files in the Windows directory
- Bonzify.exe (PID: 3008)
- INSTALLER.exe (PID: 2752)
- INSTALLER.exe (PID: 3736)
- WerFault.exe (PID: 3908)
- WerFault.exe (PID: 3096)
- WerFault.exe (PID: 3140)
- SetupUtility.exe (PID: 3688)
- WerFault.exe (PID: 3920)
- fxssvc.exe (PID: 1576)
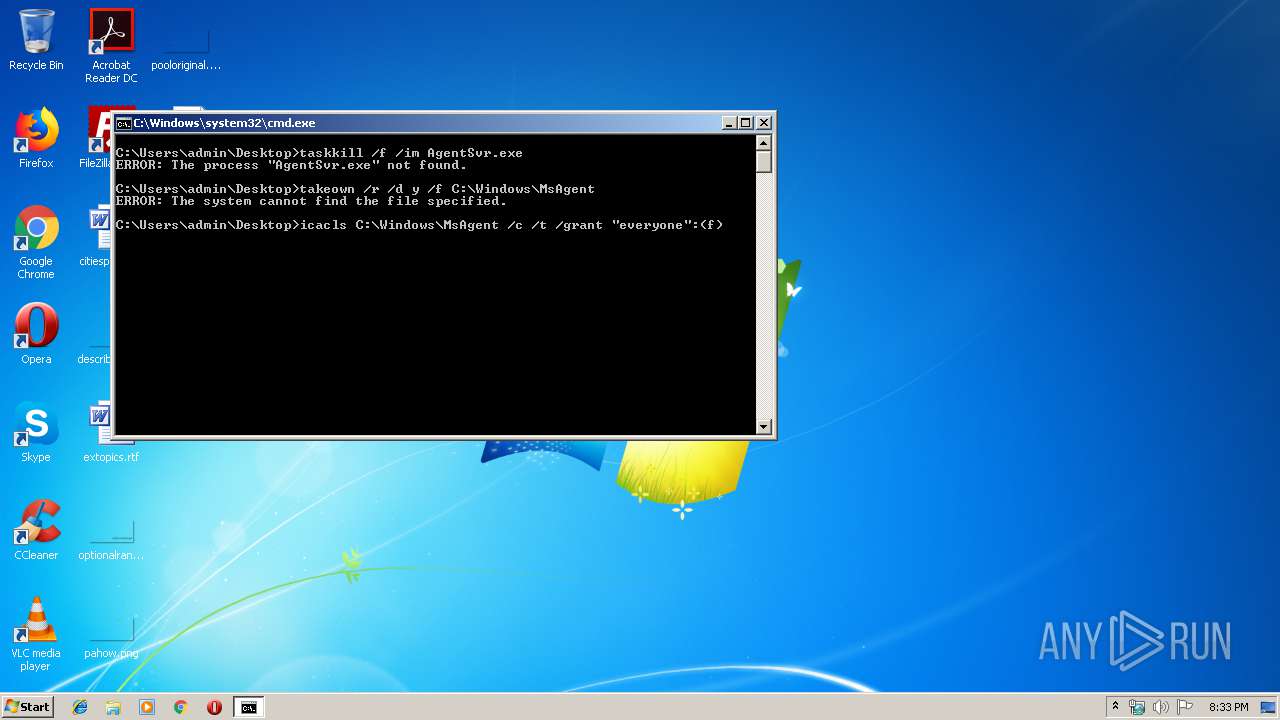
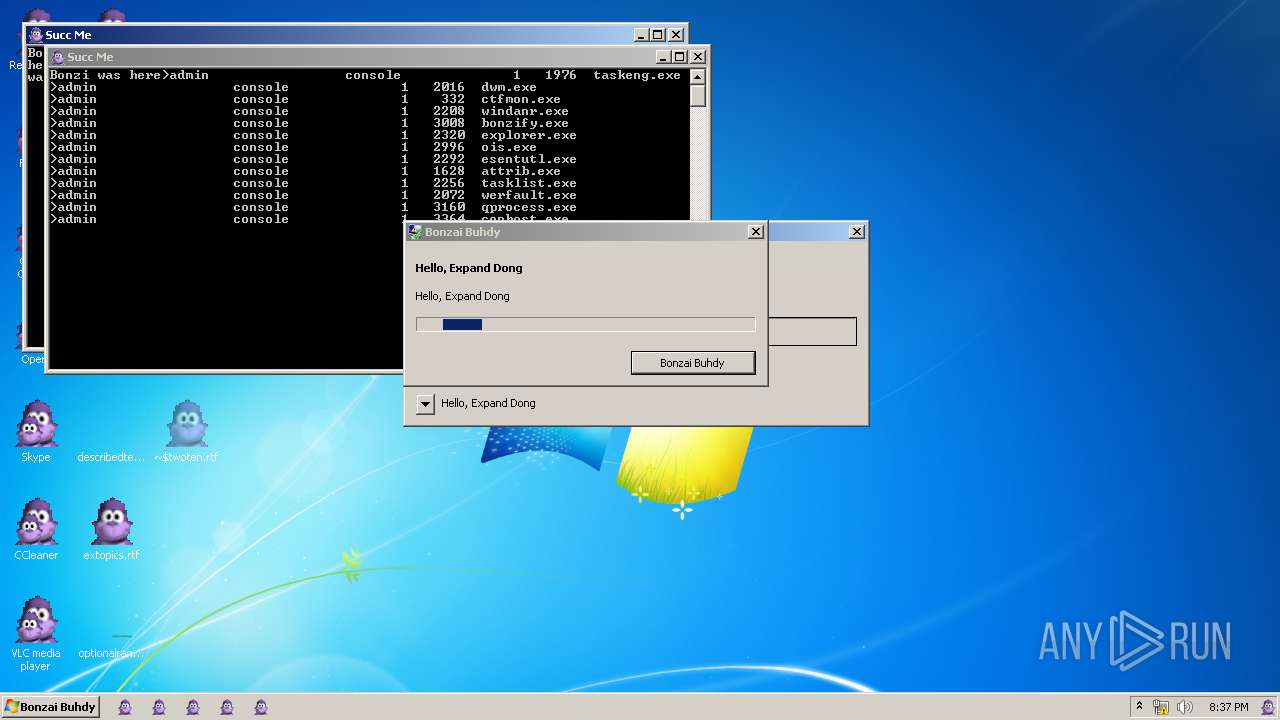
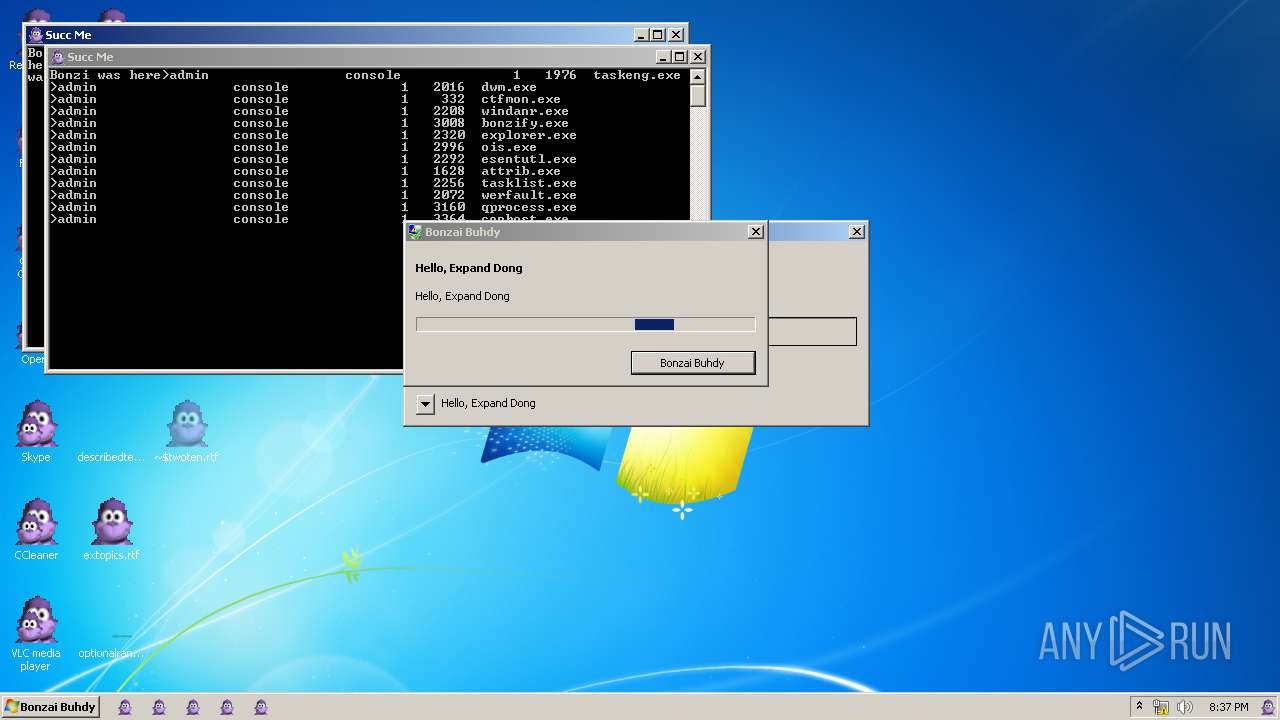
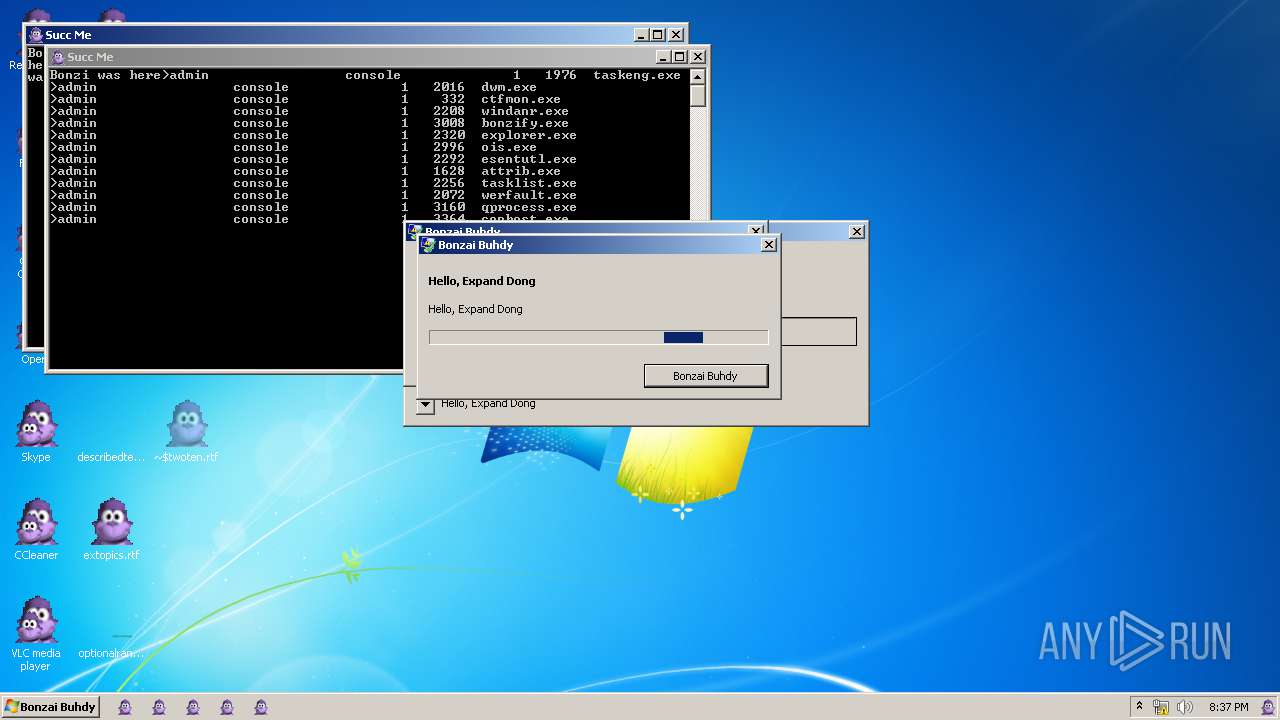
Starts CMD.EXE for commands execution
- Bonzify.exe (PID: 3008)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 3588)
Executable content was dropped or overwritten
- Bonzify.exe (PID: 3008)
- INSTALLER.exe (PID: 3736)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3588)
Removes files from Windows directory
- INSTALLER.exe (PID: 2752)
- INSTALLER.exe (PID: 3736)
- WerFault.exe (PID: 3908)
- WerFault.exe (PID: 3096)
- WerFault.exe (PID: 3140)
- WerFault.exe (PID: 3920)
Creates COM task schedule object
- regsvr32.exe (PID: 2788)
- regsvr32.exe (PID: 3820)
- regsvr32.exe (PID: 2072)
- regsvr32.exe (PID: 3844)
- regsvr32.exe (PID: 3604)
- regsvr32.exe (PID: 2840)
- regsvr32.exe (PID: 3968)
- regsvr32.exe (PID: 2732)
- regsvr32.exe (PID: 3812)
- taskmgr.exe (PID: 1016)
- explorer.exe (PID: 2320)
- taskmgr.exe (PID: 3092)
- WerFault.exe (PID: 2072)
- svchost.exe (PID: 2820)
- explorer.exe (PID: 2964)
- WFS.exe (PID: 116)
Creates a software uninstall entry
- INSTALLER.exe (PID: 3736)
- svchost.exe (PID: 2820)
Executed via COM
- AgentSvr.exe (PID: 4024)
- DllHost.exe (PID: 2856)
Reads Internet Cache Settings
- explorer.exe (PID: 2320)
Creates files in the user directory
- explorer.exe (PID: 2320)
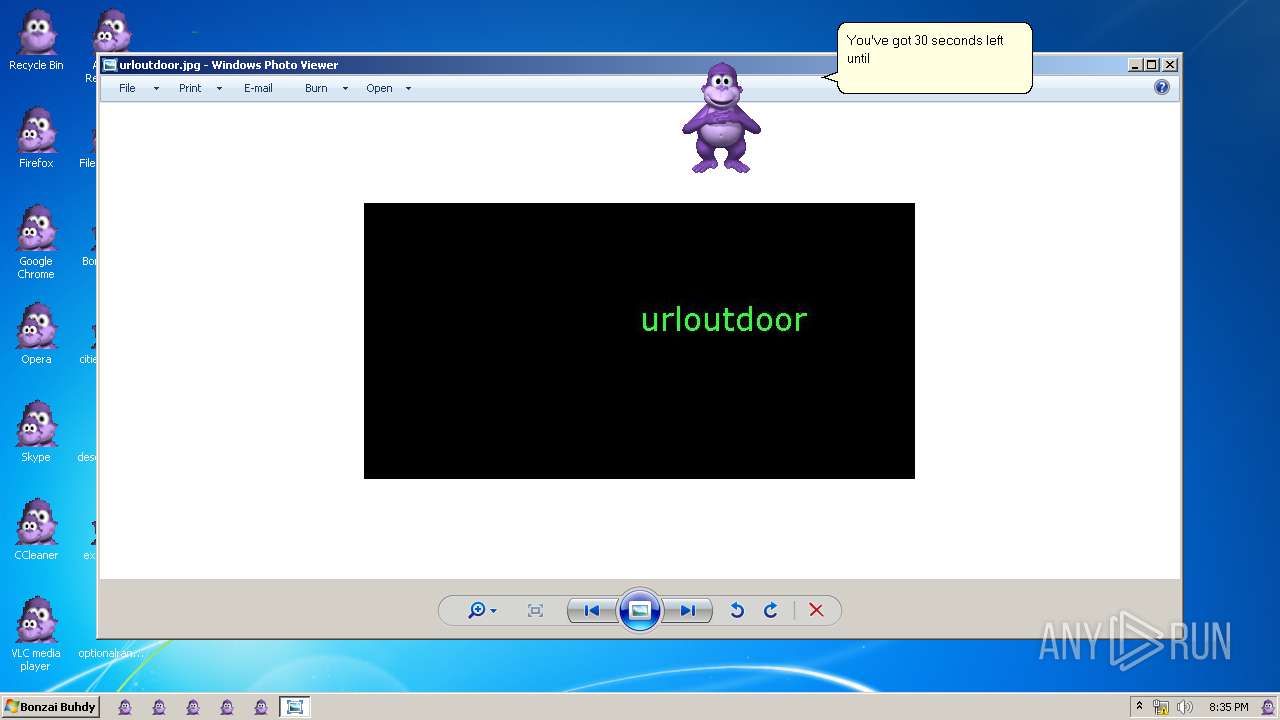
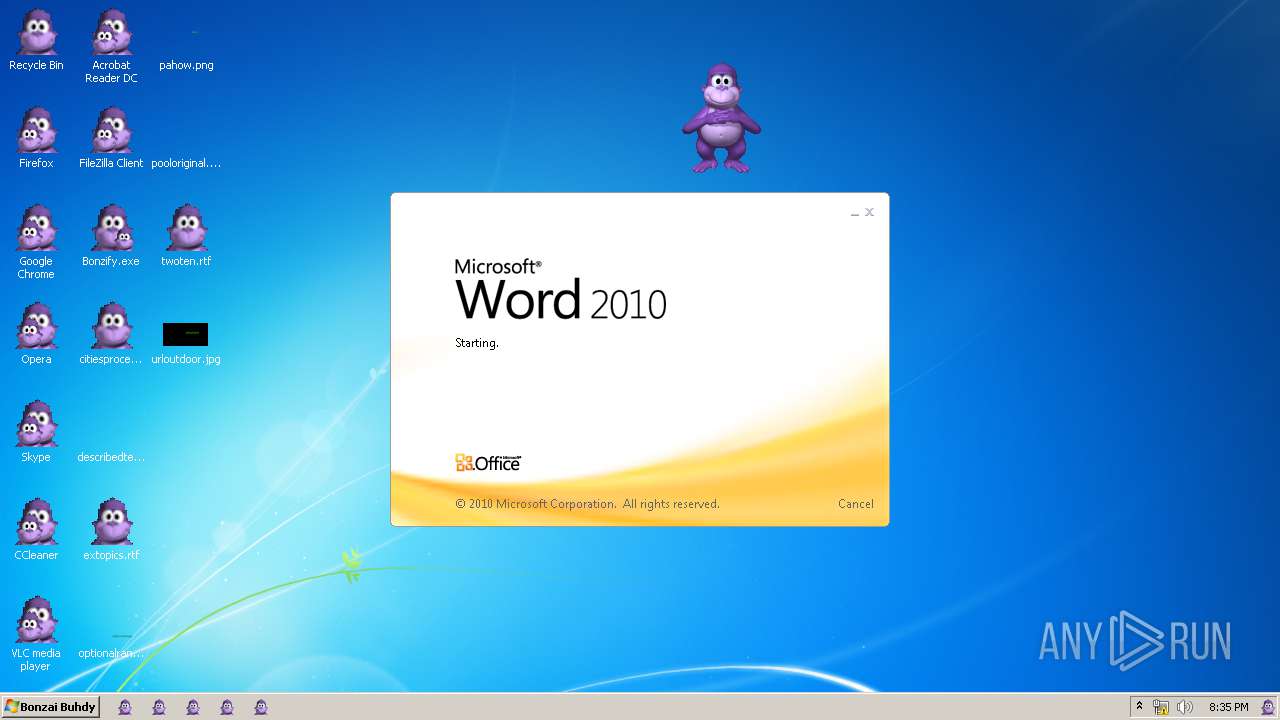
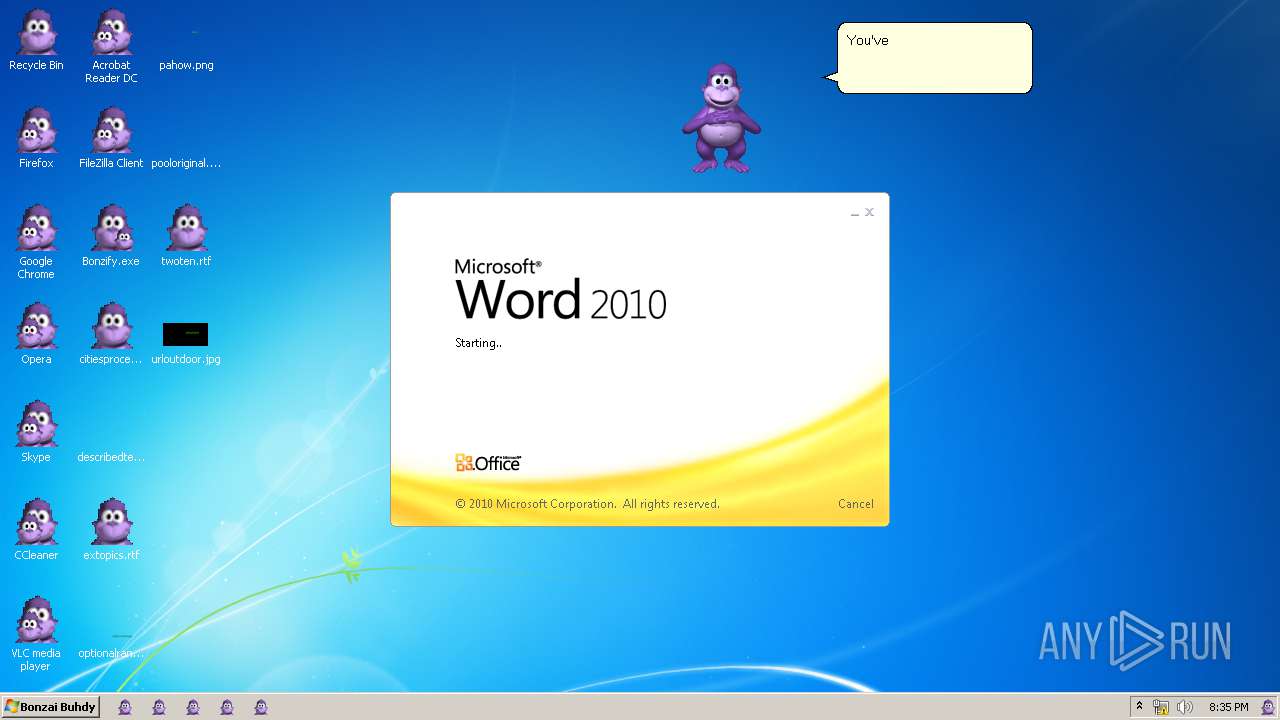
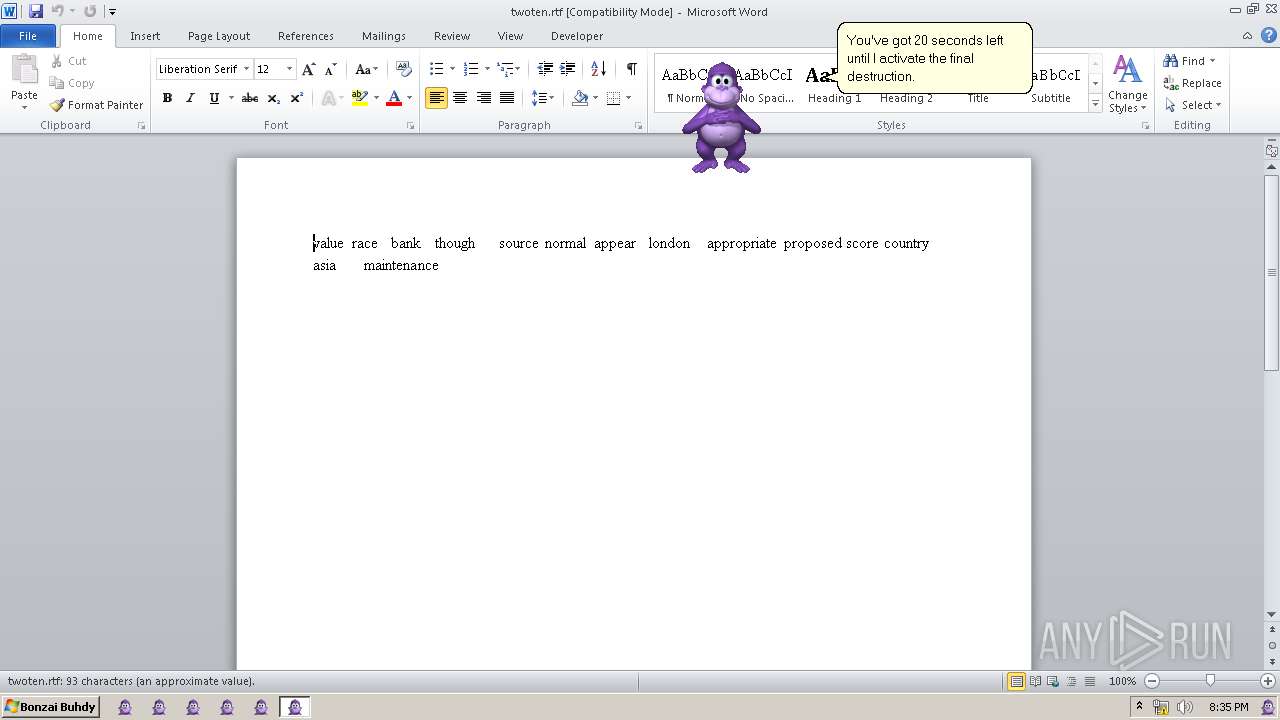
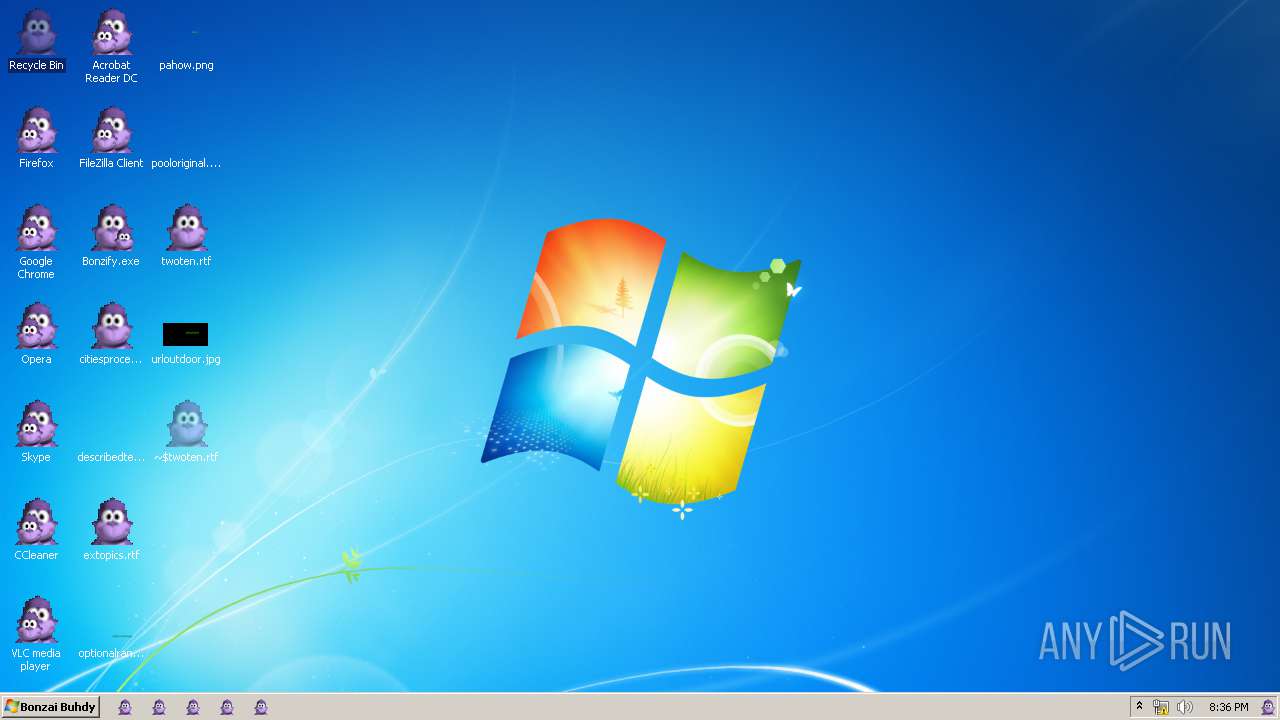
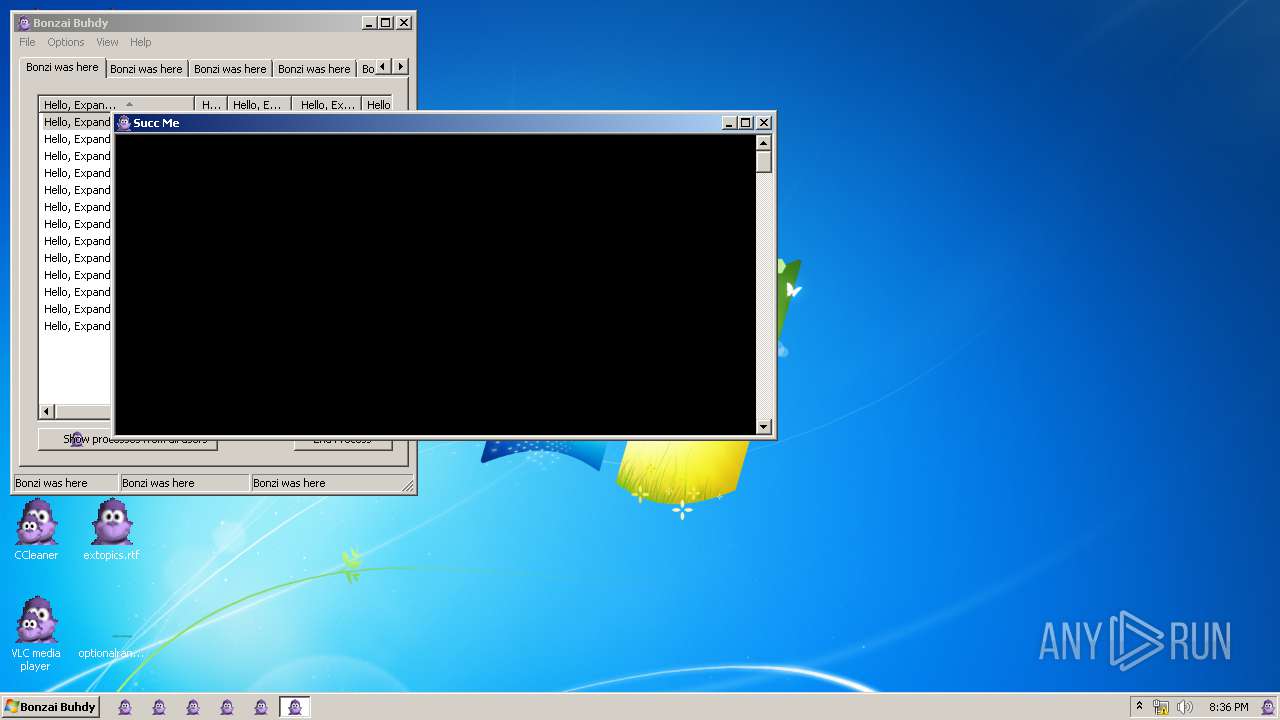
Starts Microsoft Office Application
- explorer.exe (PID: 2320)
Changes the desktop background image
- OSPPSVC.EXE (PID: 2604)
- conhost.exe (PID: 2552)
Creates executable files which already exist in Windows
- WerFault.exe (PID: 3096)
Creates files in the program directory
- WerFault.exe (PID: 3096)
- wermgr.exe (PID: 2596)
- WerFault.exe (PID: 3140)
- wermgr.exe (PID: 2304)
- fxssvc.exe (PID: 1576)
Modifies the open verb of a shell class
- wermgr.exe (PID: 2596)
- svchost.exe (PID: 2820)
Changes IE settings (feature browser emulation)
- taskmgr.exe (PID: 3092)
- conhost.exe (PID: 3984)
- WFS.exe (PID: 116)
Application launched itself
- taskmgr.exe (PID: 3092)
Uses TASKLIST.EXE to query information about running processes
- ntvdm.exe (PID: 3680)
Executes application which crashes
- explorer.exe (PID: 2320)
Creates or modifies windows services
- svchost.exe (PID: 2820)
Executed as Windows Service
- fxssvc.exe (PID: 1576)
Writes to a desktop.ini file (may be used to cloak folders)
- WFS.exe (PID: 116)
INFO
Dropped object may contain Bitcoin addresses
- Bonzify.exe (PID: 3008)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1188)
Application was crashed
- OSPPSVC.EXE (PID: 2604)
- SearchProtocolHost.exe (PID: 1732)
- svchost.exe (PID: 3992)
- WerFault.exe (PID: 3908)
- DllHost.exe (PID: 1432)
- explorer.exe (PID: 2320)
- WerFault.exe (PID: 2072)
- LocationNotifications.exe (PID: 284)
- fxssvc.exe (PID: 1576)
Creates files in the user directory
- WINWORD.EXE (PID: 1188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:22 18:35:45+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 4096 |
| InitializedDataSize: | 6696960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Jun-2019 16:35:45 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 22-Jun-2019 16:35:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000F88 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.53481 |
.rdata | 0x00002000 | 0x00000FE8 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.32117 |
.data | 0x00003000 | 0x00000020 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00004000 | 0x00661BD8 | 0x00661C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.84955 |
.reloc | 0x00666000 | 0x000001C4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.08408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.01704 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
100 | 7.82633 | 5249795 | UNKNOWN | UNKNOWN | DATA |
101 | 7.78087 | 400536 | UNKNOWN | UNKNOWN | DATA |
102 | 7.93147 | 1021232 | UNKNOWN | UNKNOWN | DATA |
103 | 4.90328 | 161 | UNKNOWN | UNKNOWN | DATA |
104 | 4.49923 | 46 | UNKNOWN | UNKNOWN | DATA |
110 | 5.30918 | 15360 | UNKNOWN | UNKNOWN | DATA |
IDI_BONZI | 2.32824 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
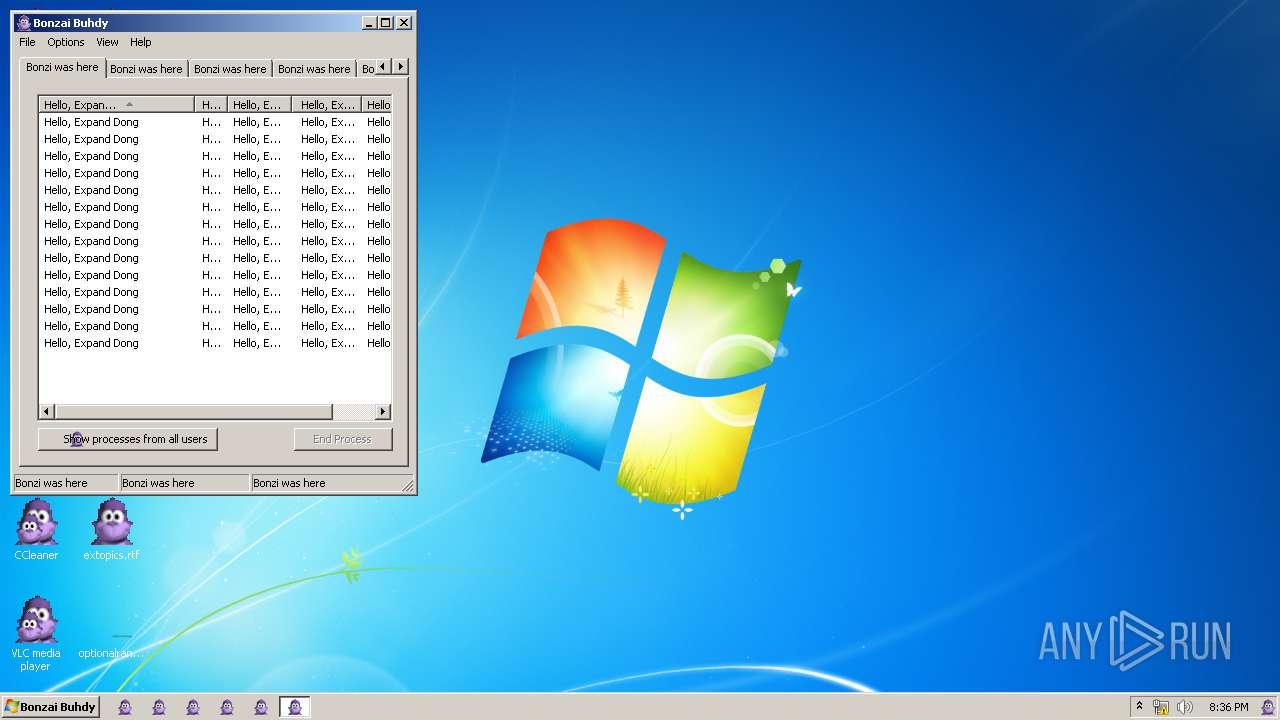
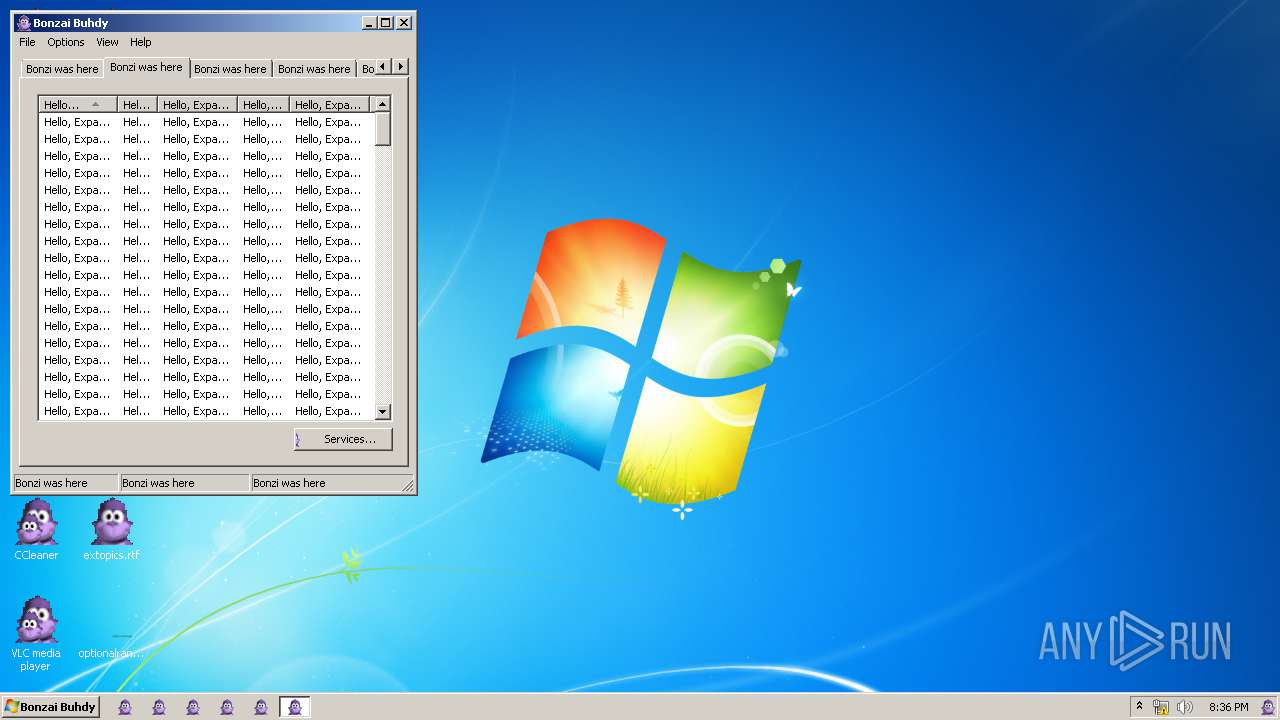
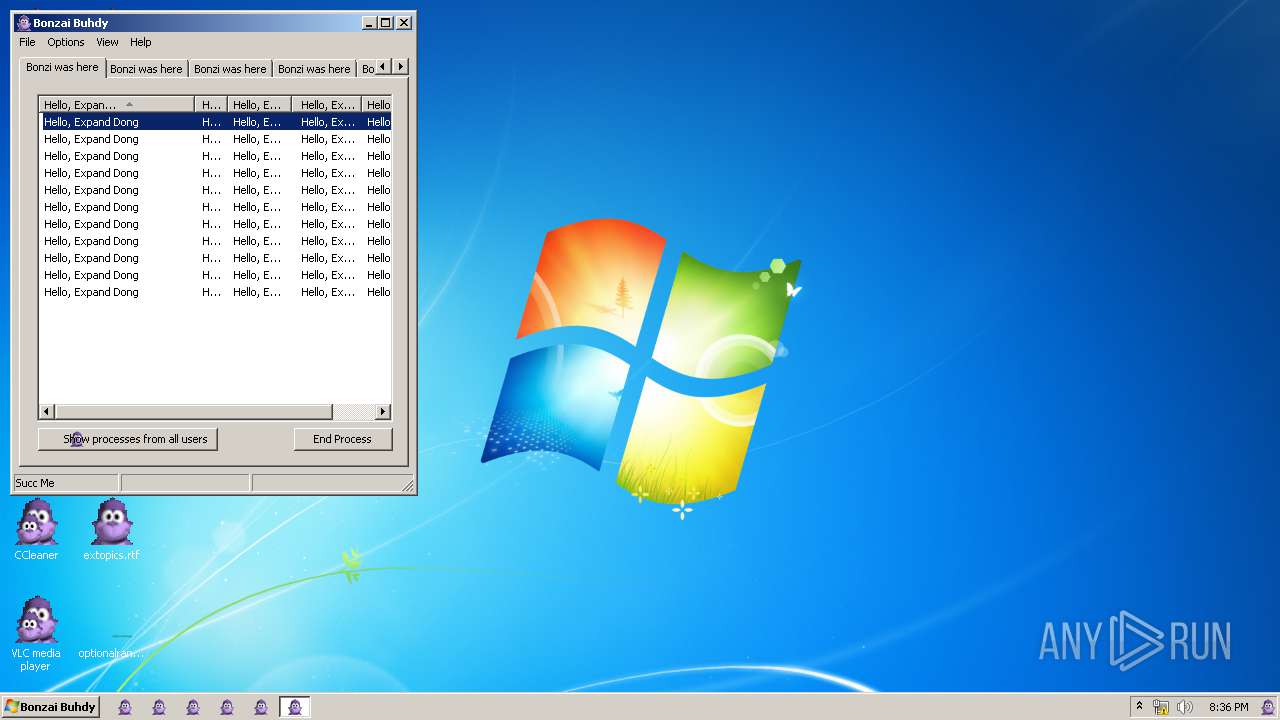
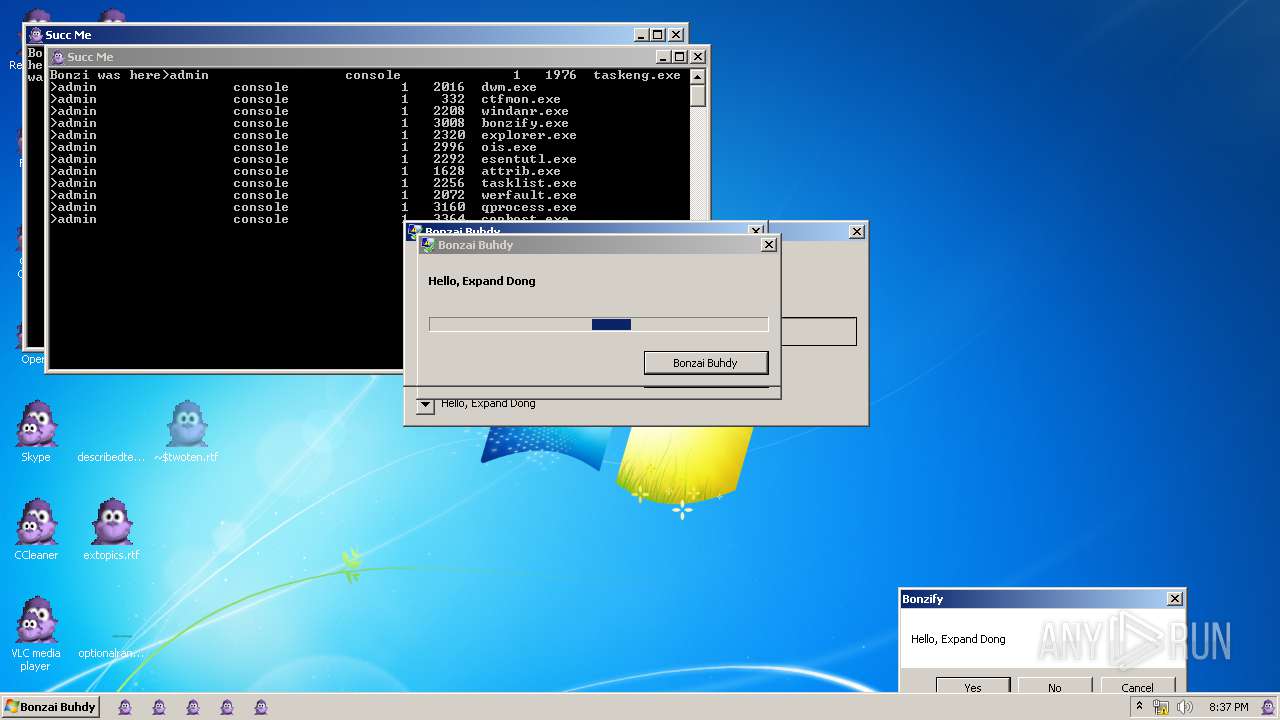
Total processes
181
Monitored processes
124
Malicious processes
19
Suspicious processes
16
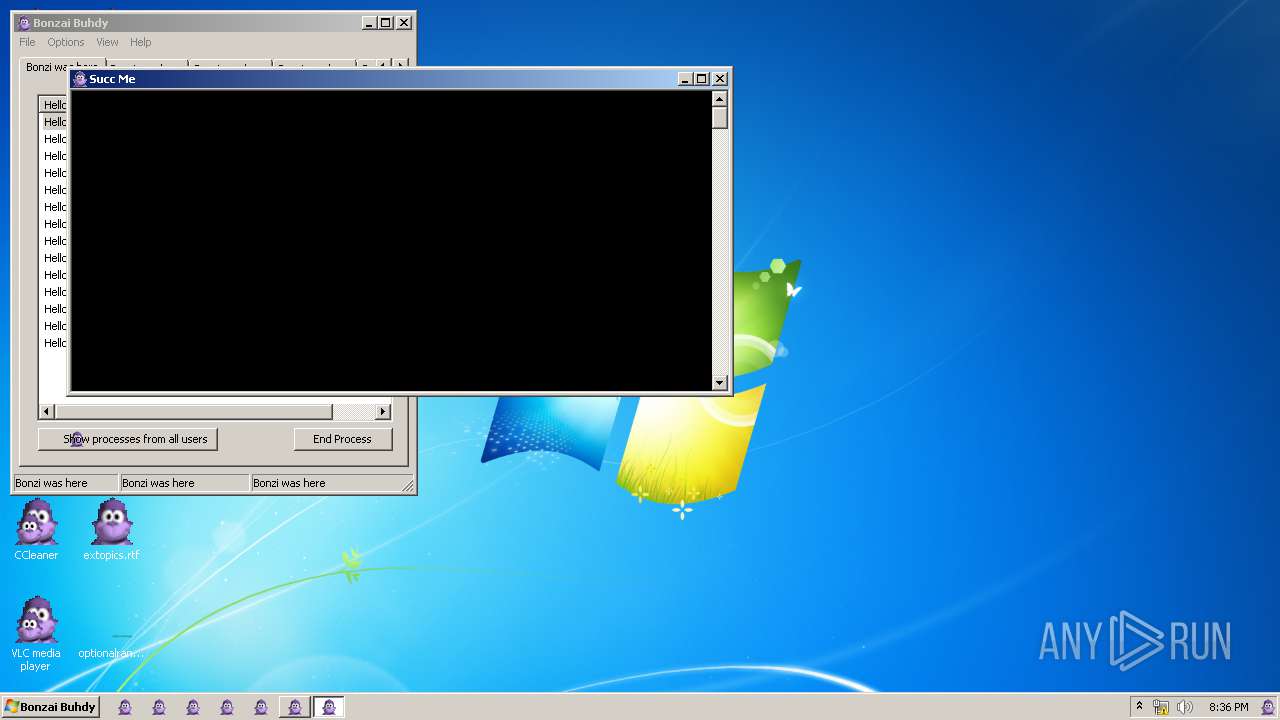
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\System32\WFS.exe" | C:\Windows\System32\WFS.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Fax and Scan Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 284 | "C:\Windows\System32\LocationNotifications.exe" | C:\Windows\System32\LocationNotifications.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Location Activity Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 812 | C:\Windows\system32\WerFault.exe -u -p 1576 -s 560 | C:\Windows\system32\WerFault.exe | svchost.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "C:\Windows\System32\lodctr.exe" | C:\Windows\System32\lodctr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1032 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1052 | "C:\Windows\System32\wbem\WmiPrvSE.exe" | C:\Windows\System32\wbem\WmiPrvSE.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Provider Host Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\twoten.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1348 | \??\C:\Windows\system32\conhost.exe | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 459
Read events
5 159
Write events
5 266
Delete events
34
Modification events
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.1 |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 1.5 | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.1\CLSID |
| Operation: | write | Name: | |
Value: {F5BE8BD2-7DE6-11D0-91FE-00C04FD701A5} | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.2 |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control.2\CLSID |
| Operation: | write | Name: | |
Value: {D45FD31B-5C6E-11D1-9EC1-00C04FD7081F} | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Agent.Control\CurVer |
| Operation: | write | Name: | |
Value: Agent.Control.2 | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F} |
| Operation: | write | Name: | |
Value: Microsoft Agent Control 2.0 | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\ProgID |
| Operation: | write | Name: | |
Value: Agent.Control.2 | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\VersionIndependentProgID |
| Operation: | write | Name: | |
Value: Agent.Control | |||
| (PID) Process: | (3604) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D45FD31B-5C6E-11D1-9EC1-00C04FD7081F}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Windows\msagent\AgentCtl.dll | |||
Executable files
13
Suspicious files
9
Text files
65
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | INSTALLER.exe | C:\Windows\lhsp\tv\SET1E36.tmp | — | |
MD5:— | SHA256:— | |||
| 3736 | INSTALLER.exe | C:\Windows\lhsp\tv\SET1E56.tmp | — | |
MD5:— | SHA256:— | |||
| 3736 | INSTALLER.exe | C:\Windows\lhsp\help\SET1E67.tmp | — | |
MD5:— | SHA256:— | |||
| 3736 | INSTALLER.exe | C:\Windows\fonts\SET1E78.tmp | — | |
MD5:— | SHA256:— | |||
| 3736 | INSTALLER.exe | C:\Windows\INF\SET1E88.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | Bonzify.exe | C:\Windows\executables.bin | binary | |
MD5:— | SHA256:— | |||
| 3736 | INSTALLER.exe | C:\Windows\system32\SET1E99.tmp | — | |
MD5:— | SHA256:— | |||
| 3736 | INSTALLER.exe | C:\Windows\INF\setupapi.app.log | ini | |
MD5:— | SHA256:— | |||
| 3736 | INSTALLER.exe | C:\Windows\Temp\OLD1EA3.tmp | — | |
MD5:— | SHA256:— | |||
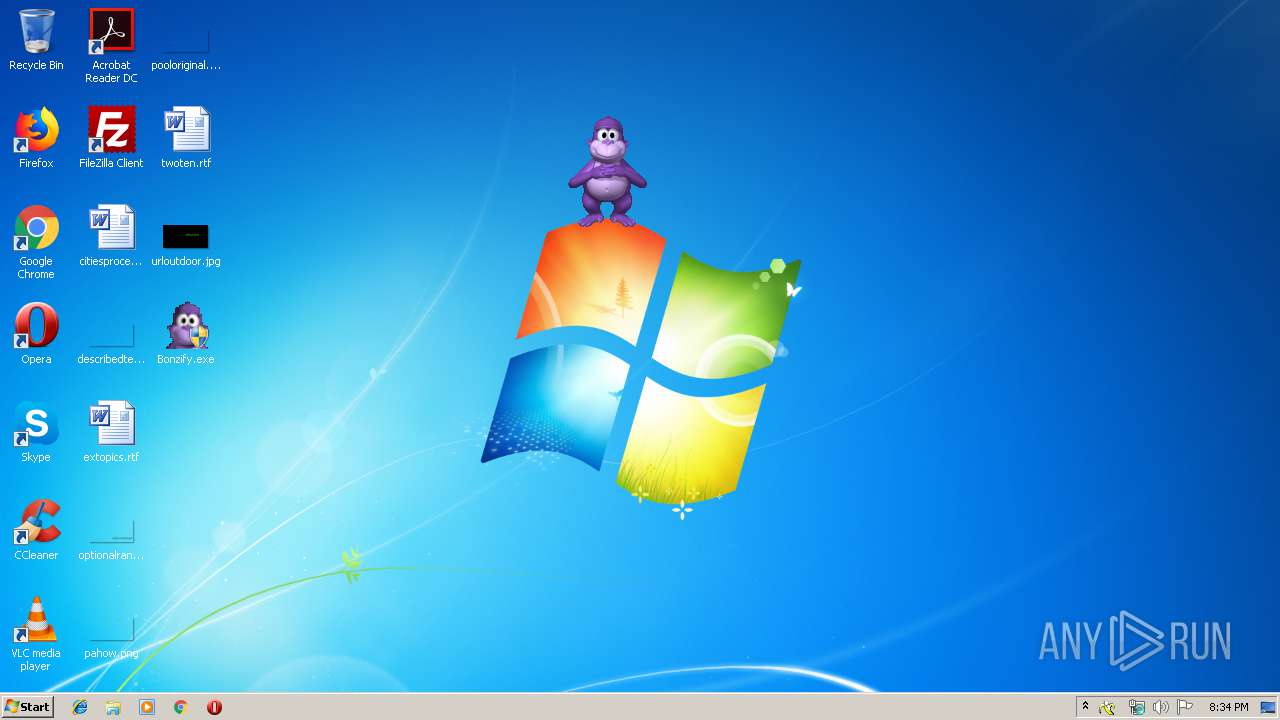
| 3008 | Bonzify.exe | C:\Windows\msagent\chars\Bonzi.acs | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2072 | WerFault.exe | GET | — | 20.44.86.127:80 | http://watson.microsoft.com/StageOne/explorer_exe/6_1_7601_17514/4ce796f3/IMM32_dll/6_1_7601_17514/4ce7b845/c0000005/0000386e.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2072 | WerFault.exe | 20.44.86.127:80 | watson.microsoft.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2072 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
2072 | WerFault.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
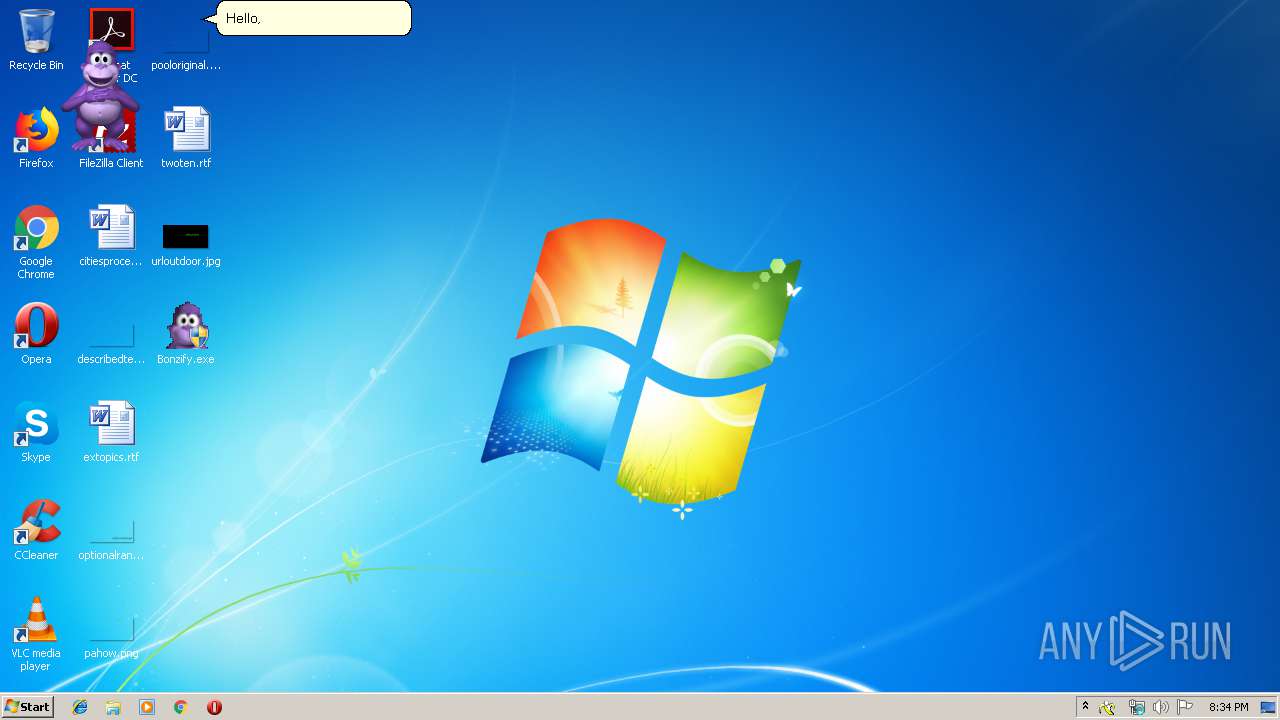
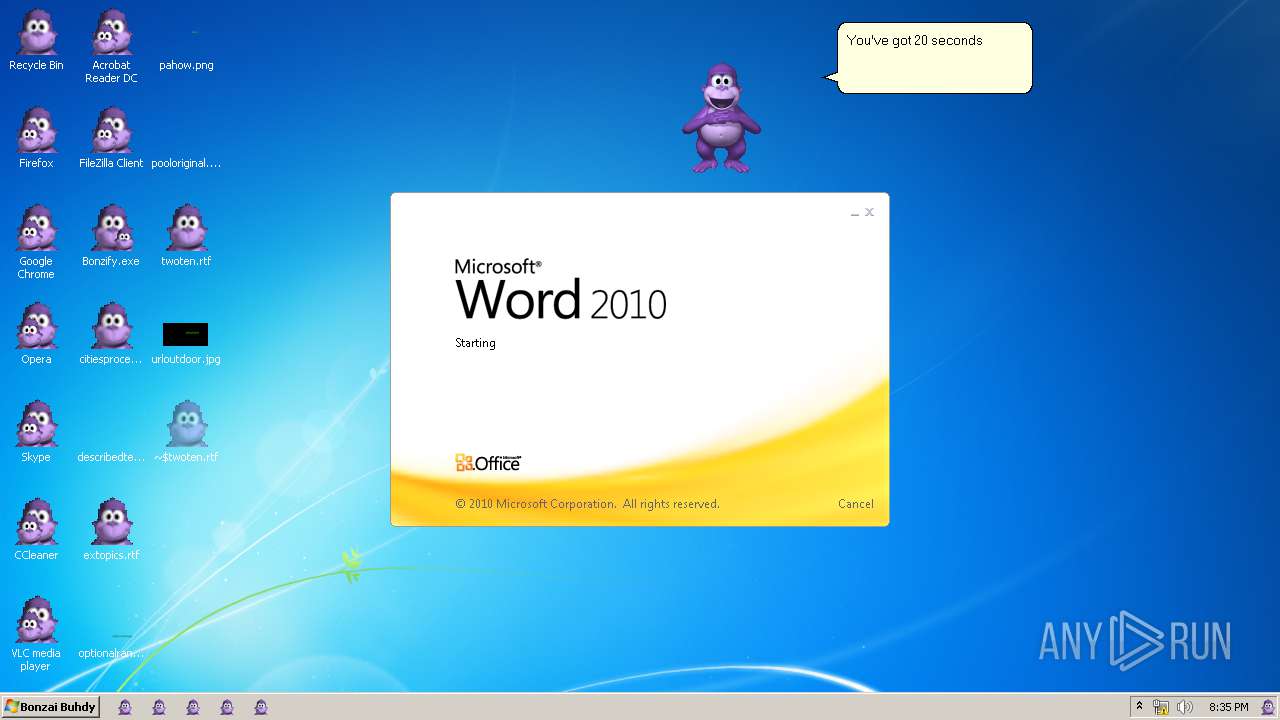
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|