| File name: | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c |
| Full analysis: | https://app.any.run/tasks/0f2f6893-ff70-4e72-9e38-deac226e6e32 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 12:53:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
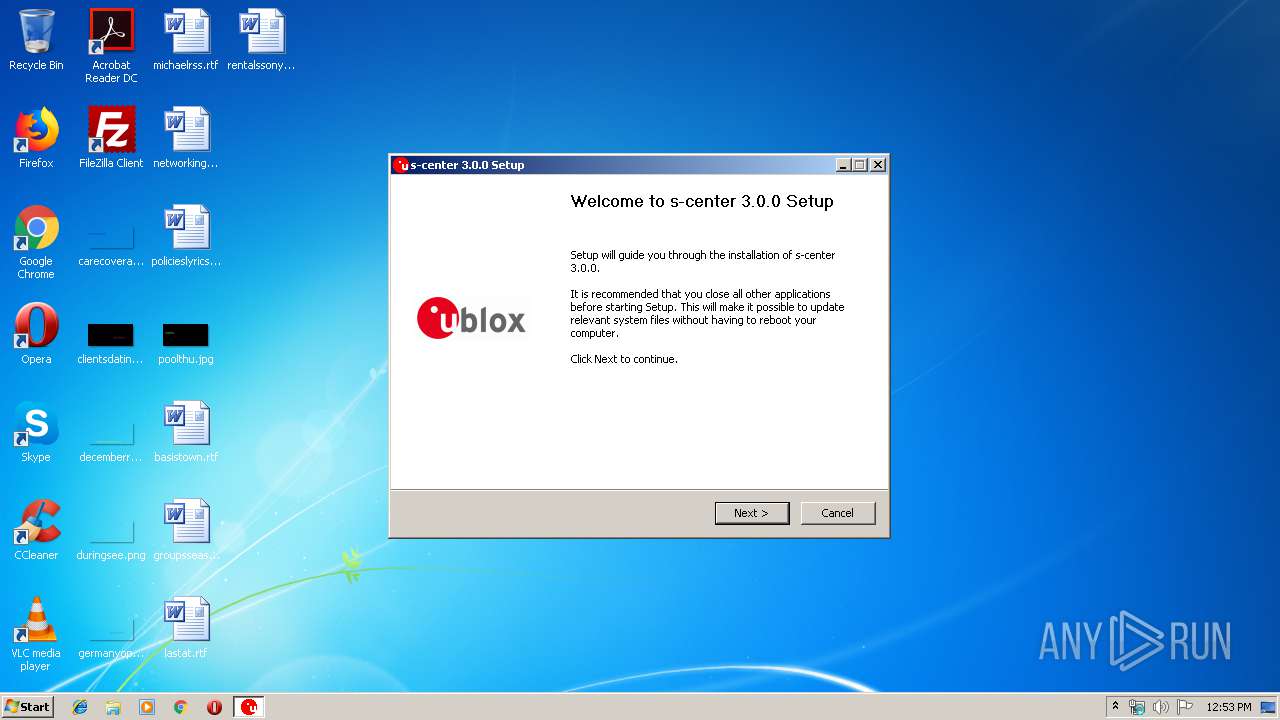
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E84881AF868E7448347BC320F934BDAB |
| SHA1: | FD1ABC451C26AF937F2E31ACBD9DE57126BFC08A |
| SHA256: | A27884ED7F7DB5DAF723B32ACB9B7DB24A48955EC03DD0AC0F0B4B2BD3EDAD0C |
| SSDEEP: | 196608:zlmg7h0cdFv53KtFlKch7/yzqey3xu7XEJ:zlm2F0tvKchUy8IJ |
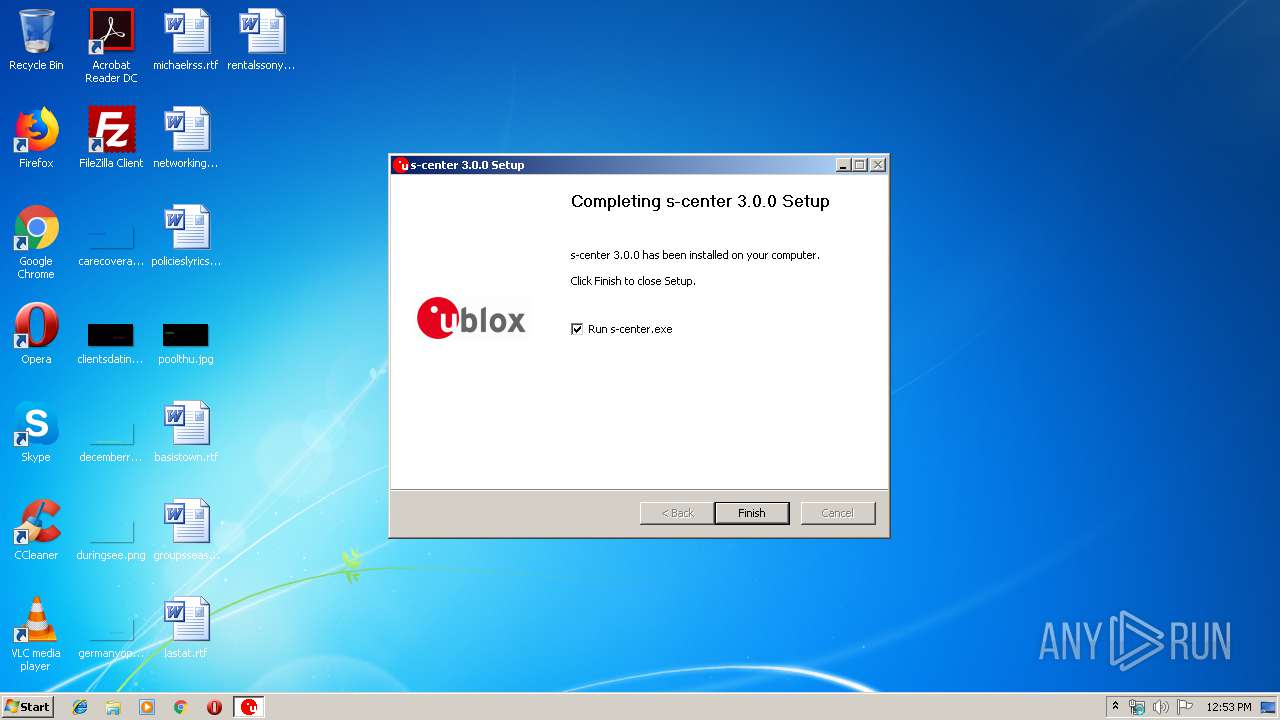
MALICIOUS
Loads dropped or rewritten executable
- a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe (PID: 4060)
SUSPICIOUS
Creates a software uninstall entry
- a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe (PID: 4060)
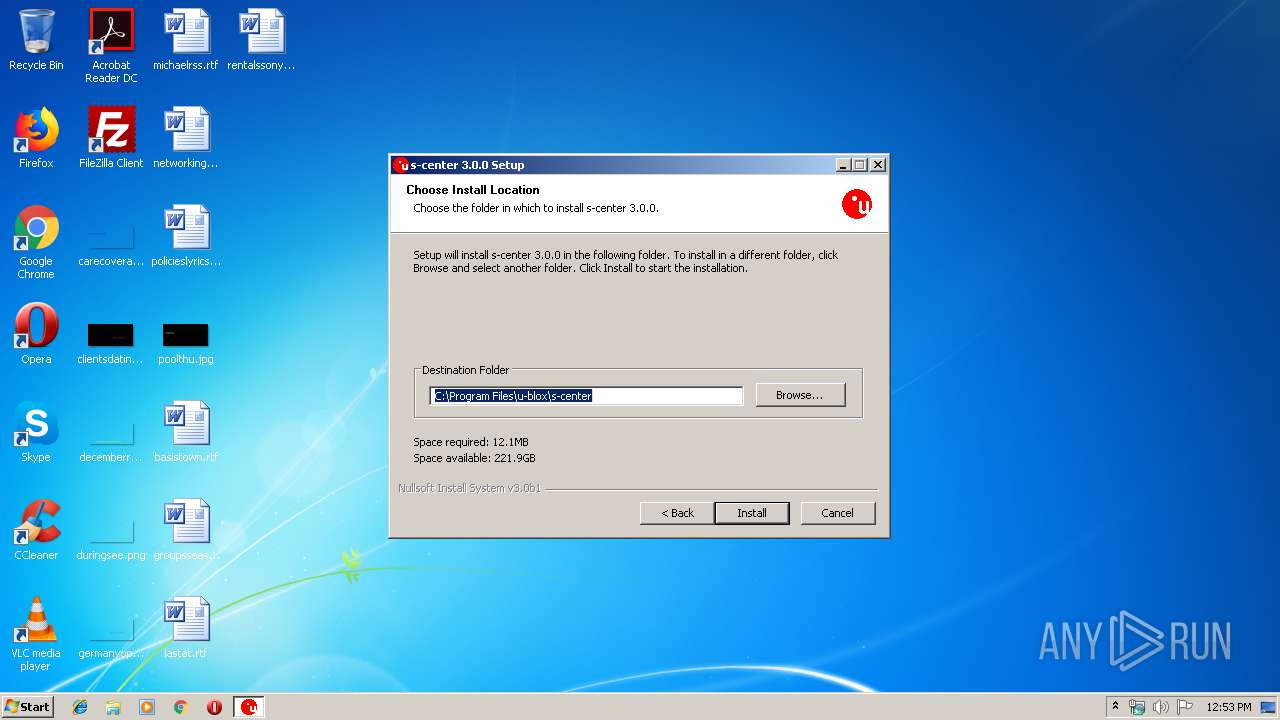
Creates files in the program directory
- a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe (PID: 4060)
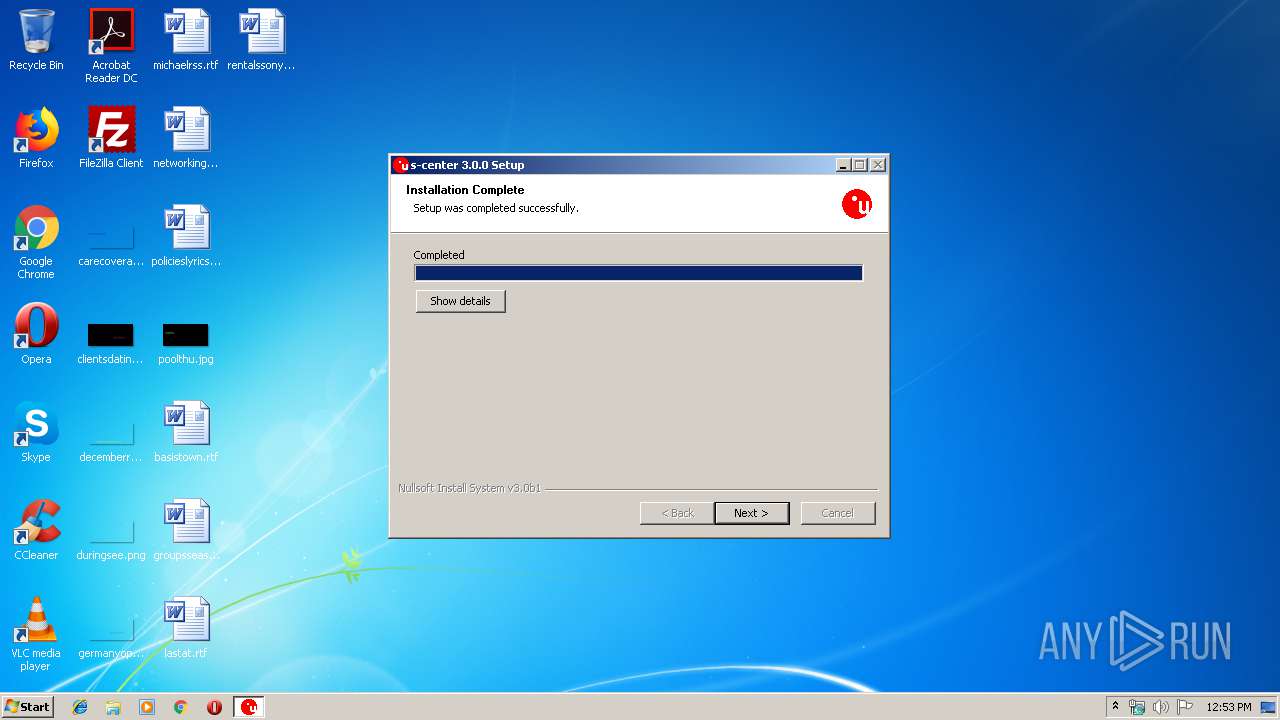
Executable content was dropped or overwritten
- a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe (PID: 4060)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:10:07 06:40:23+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30e2 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Oct-2014 04:40:23 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-Oct-2014 04:40:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005DF4 | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50963 |
.rdata | 0x00007000 | 0x000012DA | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10051 |
.data | 0x00009000 | 0x000254B8 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.13022 |
.ndata | 0x0002F000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x00004118 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.17321 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0787 | 530 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0.391731 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.28574 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2916 | "C:\Users\admin\AppData\Local\Temp\a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe" | C:\Users\admin\AppData\Local\Temp\a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\AppData\Local\Temp\a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe" | C:\Users\admin\AppData\Local\Temp\a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
352
Read events
350
Write events
2
Delete events
0
Modification events
| (PID) Process: | (4060) a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\s-center |
| Operation: | write | Name: | DisplayName |
Value: s-center (remove only) | |||
| (PID) Process: | (4060) a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\s-center |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\u-blox\s-center\Uninstall.exe | |||
Executable files
7
Suspicious files
2
Text files
37
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Program Files\u-blox\s-center\u-blox tcp reflector.exe | executable | |
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Program Files\u-blox\s-center\User Guide.pdf | ||
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Program Files\u-blox\s-center\python27.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Program Files\u-blox\s-center\nrfutil.exe | executable | |
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Users\admin\AppData\Local\Temp\nsoB60D.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Program Files\u-blox\s-center\readme.txt | text | |
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Users\admin\AppData\Local\Temp\nsoB60D.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Program Files\u-blox\s-center\Release Note.txt | text | |
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\u-blox\s-center\s-center.lnk | lnk | |
MD5:— | SHA256:— | |||
| 4060 | a27884ed7f7db5daf723b32acb9b7db24a48955ec03dd0ac0f0b4b2bd3edad0c.exe | C:\Program Files\u-blox\s-center\s-center.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report