| download: | new_pp.exe |
| Full analysis: | https://app.any.run/tasks/f5428a4c-7390-4e5e-b38d-ae25cf1d2e9a |
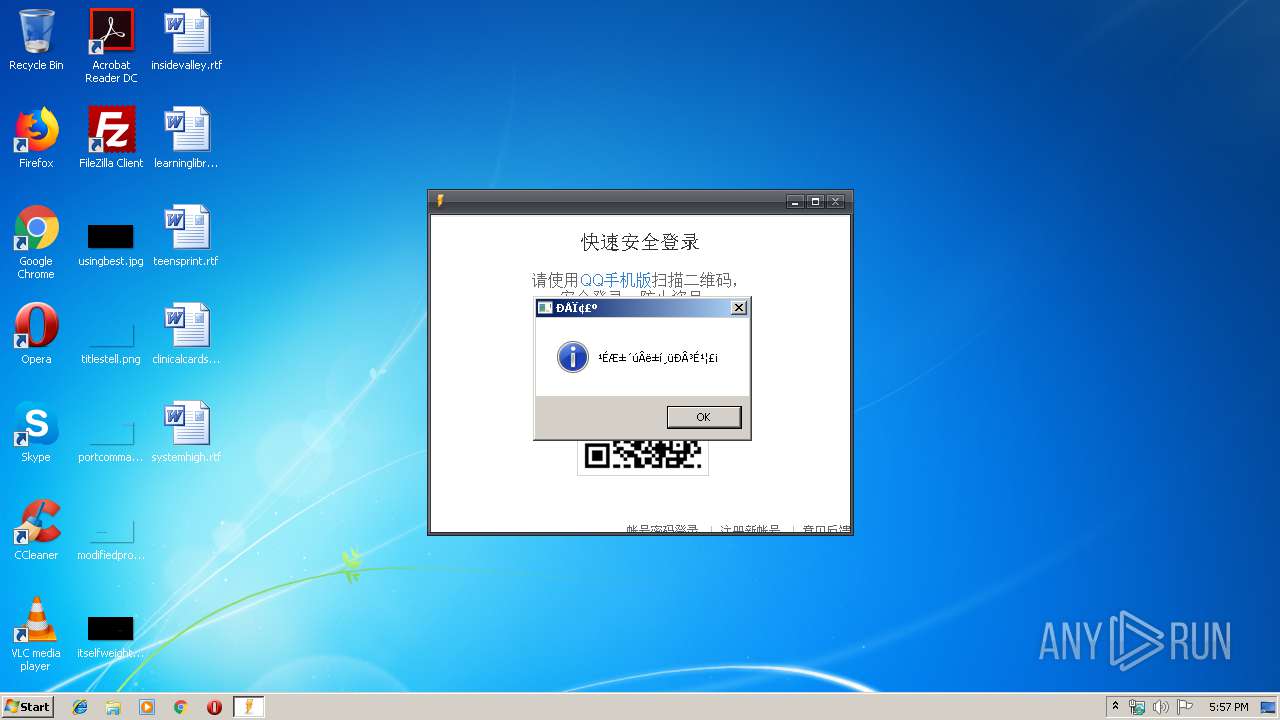
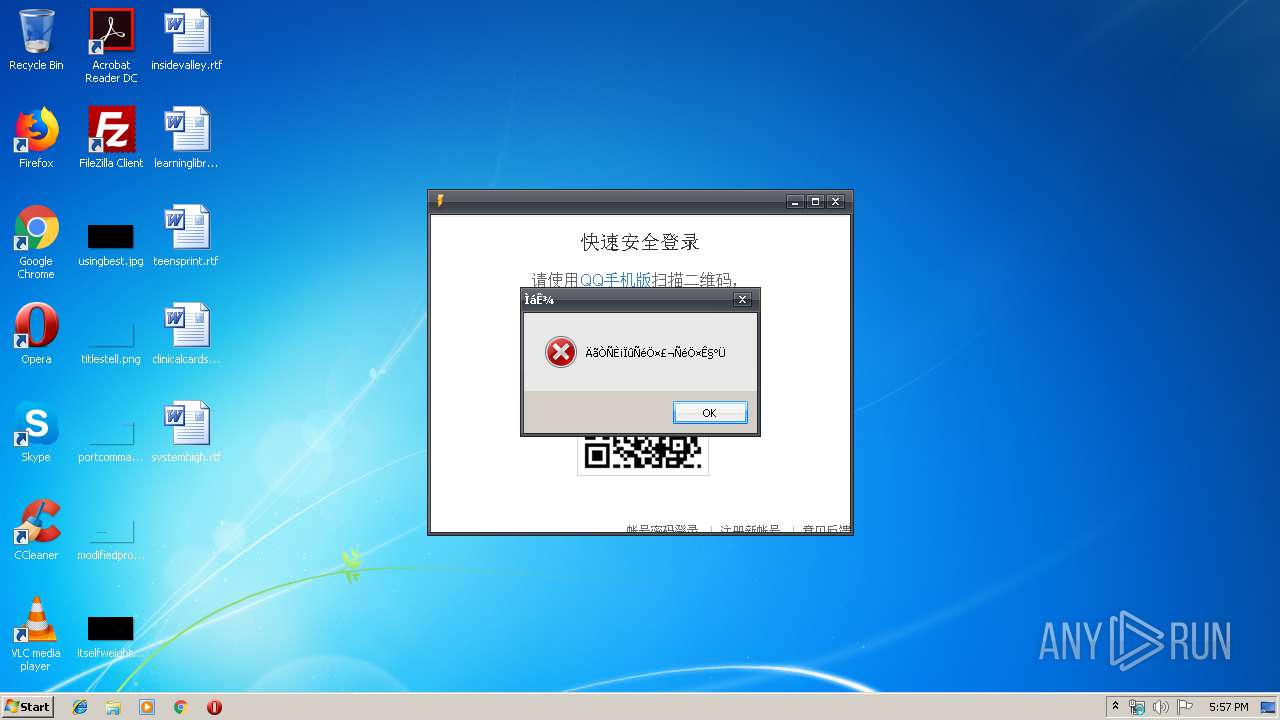
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 17:54:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 03180BC769A92968A47DCA1CC5B516D7 |
| SHA1: | C41B2DCA9DA24A41F03013B7998F2BCECBC78A8B |
| SHA256: | A276B8A6E3C204E635B26BA20561DD524F67B770424B878E87D55D6861CC657D |
| SSDEEP: | 98304:xkNVA+6znf30CURInwZfgcaXBfVuMriHqyZG3A56QkL+23/Lpd:xWVF6f30C+InWfgcaXGpKyMwMQkq0/j |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- new_pp.exe (PID: 1896)
Reads internet explorer settings
- new_pp.exe (PID: 1896)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:03 17:27:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1232896 |
| InitializedDataSize: | 1544192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7ed000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.0.0 |
| ProductVersionNumber: | 1.3.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
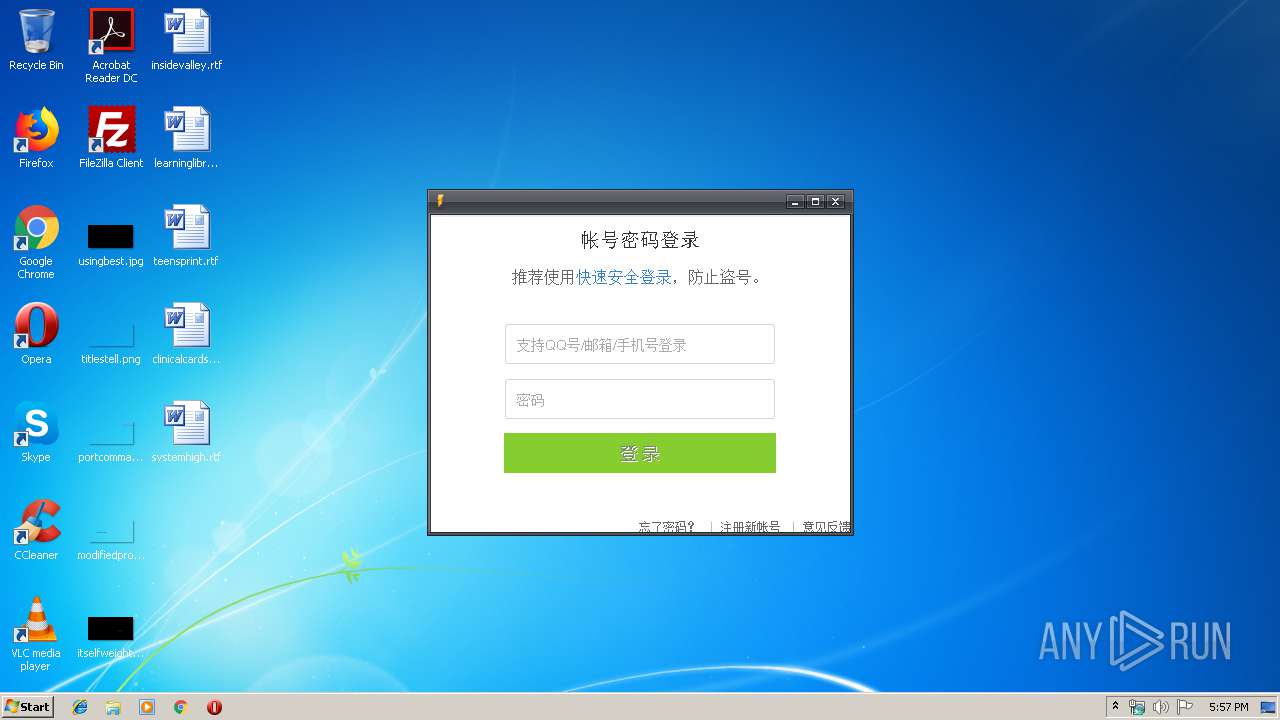
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.3.0.0 |
| FileDescription: | 闪电下单 |
| ProductName: | 闪电下单 |
| ProductVersion: | 1.3.0.0 |
| CompanyName: | 酷 |
| LegalCopyright: | 酷版权所有 |
| Comments: | 闪电下单 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Dec-2019 16:27:28 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000138 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 03-Dec-2019 16:27:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x002EB000 | 0x00186000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97567 | |
.rsrc | 0x002EC000 | 0x0001F848 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.30812 |
.idata | 0x0030C000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.220958 |
0x0030D000 | 0x002EC000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0388884 | |
isqklgac | 0x005F9000 | 0x001F4000 | 0x001F4000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.85509 |
rqovjowu | 0x007ED000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.626264 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 2.61806 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.76201 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.008 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.2647 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.27411 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 3.68476 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
127 | 3.4183 | 12 | Latin 1 / Western European | Chinese - PRC | RT_MENU |
150 | 6.68362 | 152 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
Imports
comctl32.dll |
kernel32.dll |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1896 | "C:\Users\admin\AppData\Local\Temp\new_pp.exe" | C:\Users\admin\AppData\Local\Temp\new_pp.exe | explorer.exe | ||||||||||||
User: admin Company: 酷 Integrity Level: MEDIUM Description: 闪电下单 Exit code: 0 Version: 1.3.0.0 Modules
| |||||||||||||||
Total events
167
Read events
125
Write events
42
Delete events
0
Modification events
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: new_pp.exe | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | vga.drv 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\new_pp_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\new_pp_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\new_pp_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\new_pp_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\new_pp_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1896) new_pp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\new_pp_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1896 | new_pp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\TCapIframeApi[1].js | — | |
MD5:— | SHA256:— | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@ui.ptlogin2.qq[1].txt | text | |
MD5:— | SHA256:— | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\c_login_2[1].js | text | |
MD5:— | SHA256:— | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\ptui_ver[1].js | text | |
MD5:— | SHA256:— | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\login[1].htm | html | |
MD5:— | SHA256:— | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\load[1].gif | image | |
MD5:00EF871B291BC03A497D608A5BD8EC99 | SHA256:81A161D5793AC2A33F02DDCD64FB0DC2D028616DAC084E4F64E77F4898B0C4E4 | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\tcaptcha-frame.ae3fc568[1].js | text | |
MD5:— | SHA256:— | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\icon_24_c_3[1].png | image | |
MD5:4FF0D1008075A82E9A030B7F2F8927C0 | SHA256:57DE6C0087C6E8FF15C2AD6205E85A7751D959B11F28D93B65B08798B96D538B | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\cross_proxy[1].htm | html | |
MD5:EED469DA9C7546B4431B5B7FC58D9FEC | SHA256:EDF9606BD61D1440BB9B15DE29ACC230380F1C2A194C21D69CF91CB13C499A11 | |||
| 1896 | new_pp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
16
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1896 | new_pp.exe | GET | — | 120.25.241.243:80 | http://120.25.241.243/stockcode.ini | CN | — | — | unknown |
1896 | new_pp.exe | GET | — | 120.25.241.243:80 | http://120.25.241.243/stockcode.ini | CN | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1896 | new_pp.exe | 120.25.241.243:80 | — | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
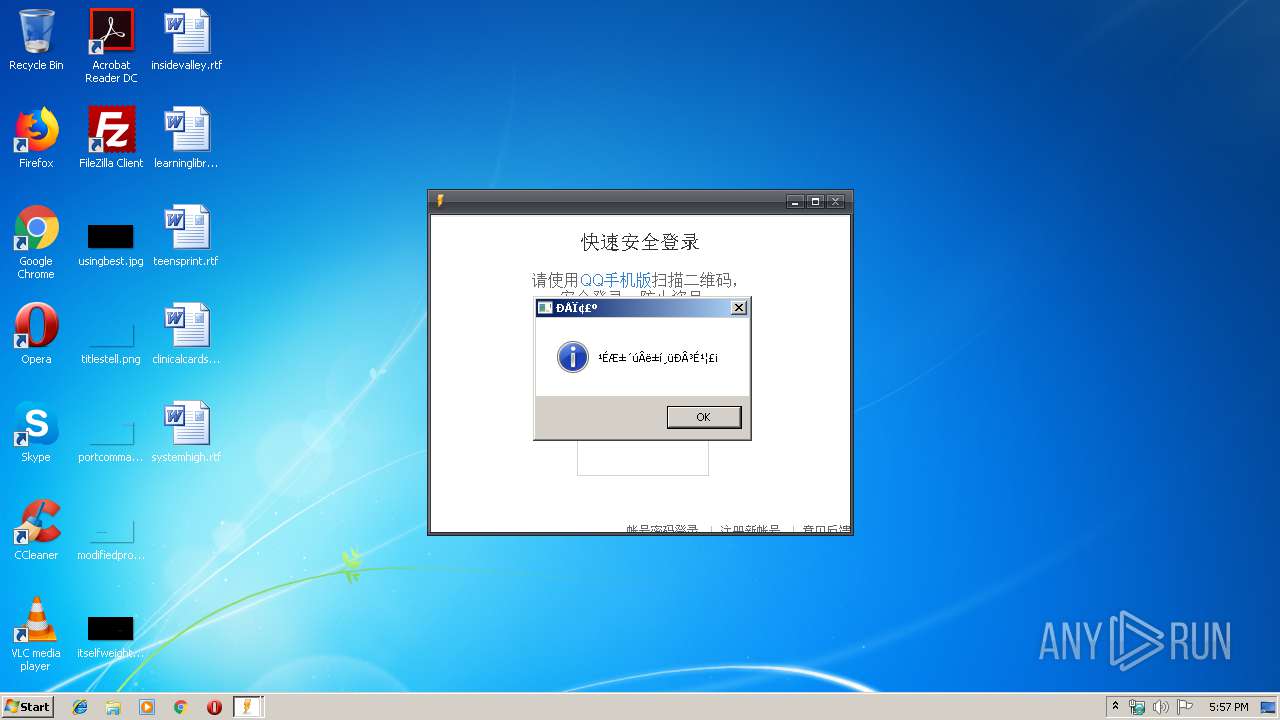
1896 | new_pp.exe | 203.205.235.164:80 | ui.ptlogin2.qq.com | — | CN | unknown |
1896 | new_pp.exe | 203.205.235.164:443 | ui.ptlogin2.qq.com | — | CN | unknown |
1896 | new_pp.exe | 14.215.138.25:443 | tajs.qq.com | China Telecom (Group) | CN | suspicious |
1896 | new_pp.exe | 125.39.83.11:443 | ty.captcha.qq.com | CHINA UNICOM China169 Backbone | CN | unknown |
1896 | new_pp.exe | 203.205.158.62:443 | imgcache.qq.com | Tencent Building, Kejizhongyi Avenue | CN | suspicious |
1896 | new_pp.exe | 203.205.158.37:443 | cdn-go.cn | Tencent Building, Kejizhongyi Avenue | CN | unknown |
1896 | new_pp.exe | 150.109.207.81:443 | captcha.gtimg.com | — | US | unknown |
1896 | new_pp.exe | 203.205.235.65:443 | ssl.captcha.qq.com | — | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ui.ptlogin2.qq.com |
| whitelisted |
imgcache.qq.com |
| whitelisted |
ty.captcha.qq.com |
| unknown |
tajs.qq.com |
| whitelisted |
cdn-go.cn |
| suspicious |
localhost.sec.qq.com |
| unknown |
localhost.ptlogin2.qq.com |
| unknown |
ssl.captcha.qq.com |
| whitelisted |
ssl.ptlogin2.qq.com |
| suspicious |
captcha.gtimg.com |
| whitelisted |
Threats
Process | Message |
|---|---|
new_pp.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|