| File name: | Windows7-Windows10_2.0.2.exe |
| Full analysis: | https://app.any.run/tasks/3e303218-800a-473a-8aa5-6166a1ba6d99 |
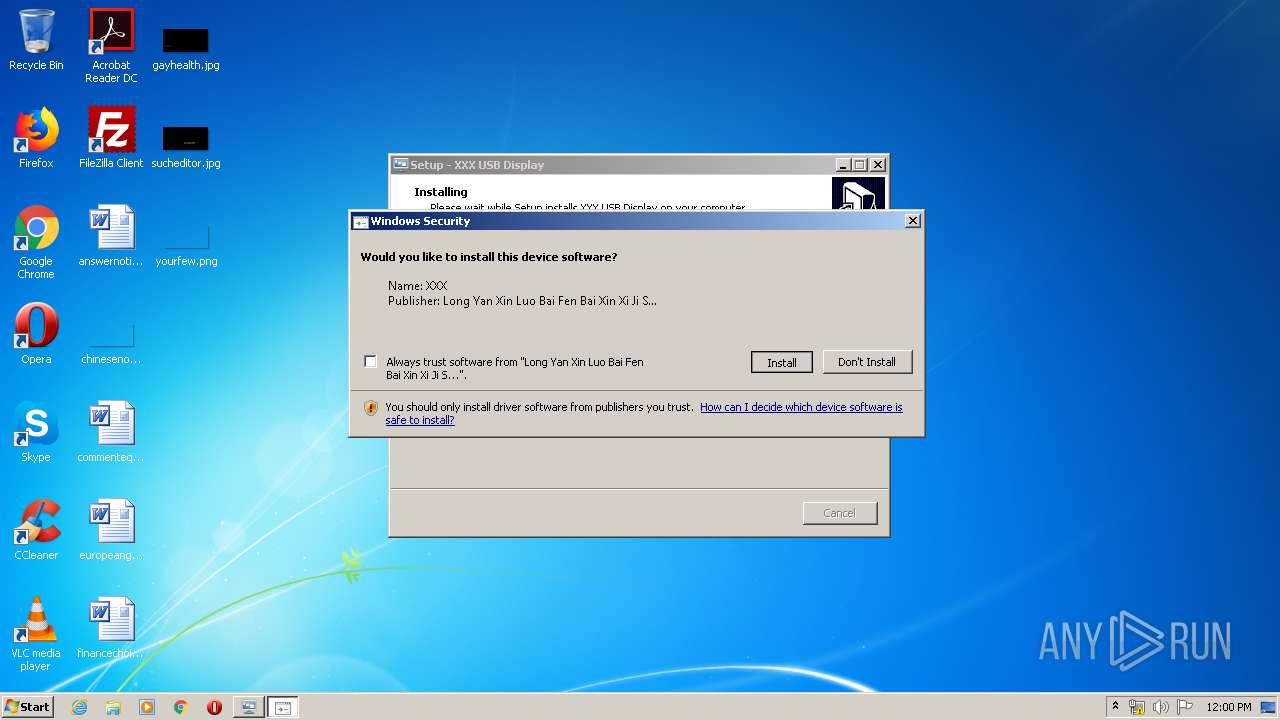
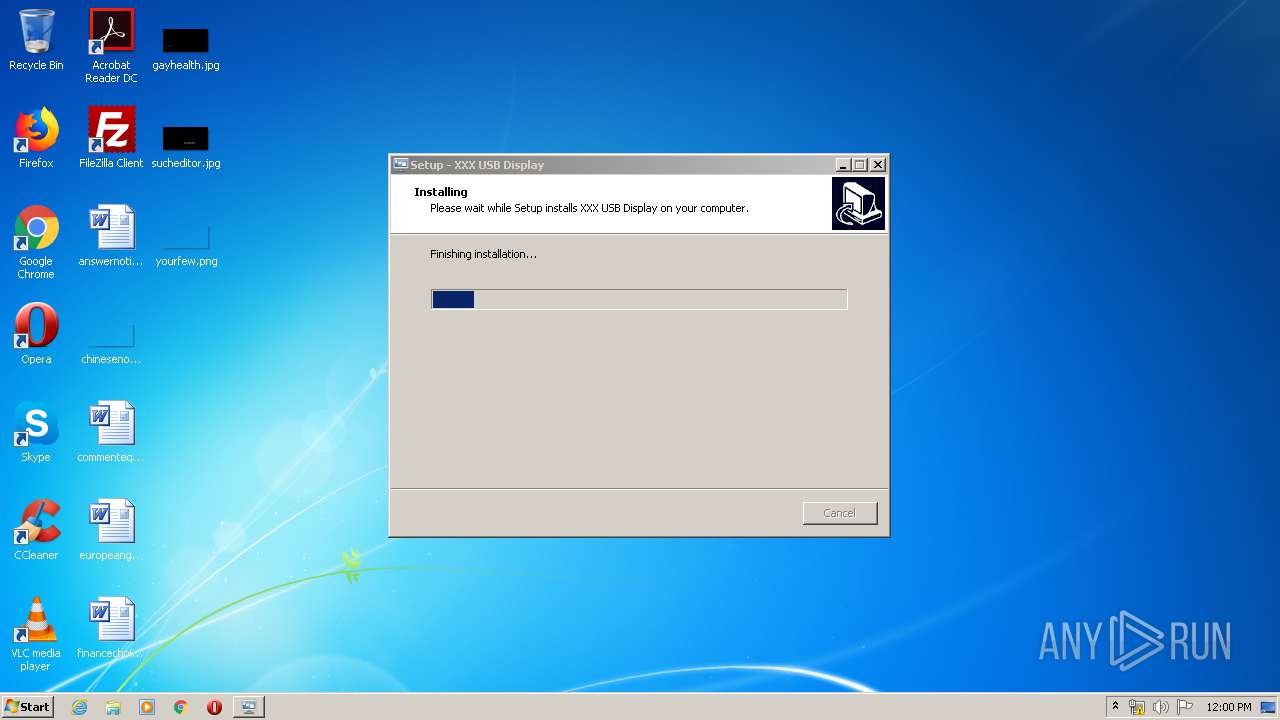
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2020, 11:59:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C0023B71F42E0703CEDFEE3A1B18E308 |
| SHA1: | B96C96227E25B373E3BFCD7503A26E4015CB3A79 |
| SHA256: | A25AD4C0E6622986B7B25E85EE0F89C32457703AE67398DF440200649FCF25E4 |
| SSDEEP: | 98304:n5il9zT8snnr1EFBvPmLpQS9GqWZaZ7dBw2Jg5fxdwBKw:a90ynBEzCQ8GqNldBw2Afpw |
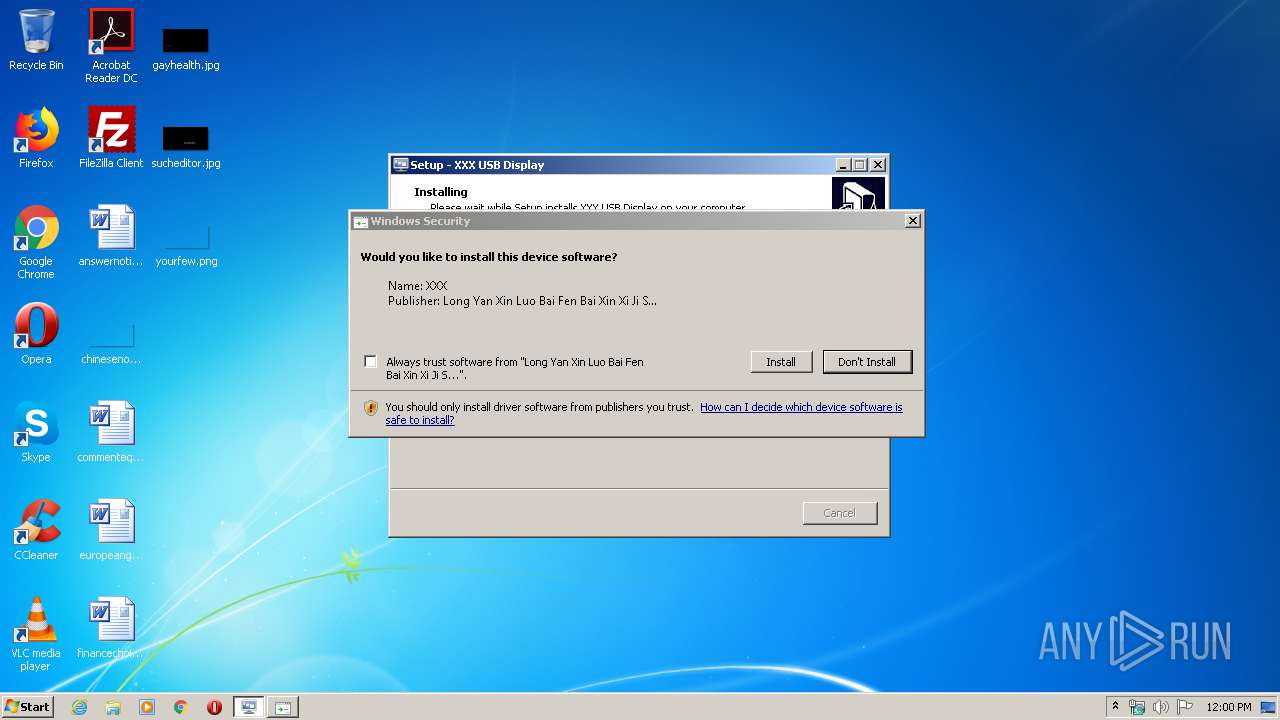
MALICIOUS
Changes the autorun value in the registry
- Windows7-Windows10_2.0.2.tmp (PID: 2496)
Application was dropped or rewritten from another process
- devcon.exe (PID: 4068)
SUSPICIOUS
Executable content was dropped or overwritten
- Windows7-Windows10_2.0.2.exe (PID: 3308)
- Windows7-Windows10_2.0.2.exe (PID: 2484)
- DrvInst.exe (PID: 3684)
- devcon.exe (PID: 4068)
- Windows7-Windows10_2.0.2.tmp (PID: 2496)
Creates files in the user directory
- Windows7-Windows10_2.0.2.tmp (PID: 2496)
Executed via COM
- DrvInst.exe (PID: 3684)
Removes files from Windows directory
- DrvInst.exe (PID: 3684)
Creates files in the driver directory
- DrvInst.exe (PID: 3684)
Creates files in the Windows directory
- DrvInst.exe (PID: 3684)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3684)
Executed as Windows Service
- vssvc.exe (PID: 2796)
INFO
Creates a software uninstall entry
- Windows7-Windows10_2.0.2.tmp (PID: 2496)
Application was dropped or rewritten from another process
- Windows7-Windows10_2.0.2.tmp (PID: 3188)
- Windows7-Windows10_2.0.2.tmp (PID: 2496)
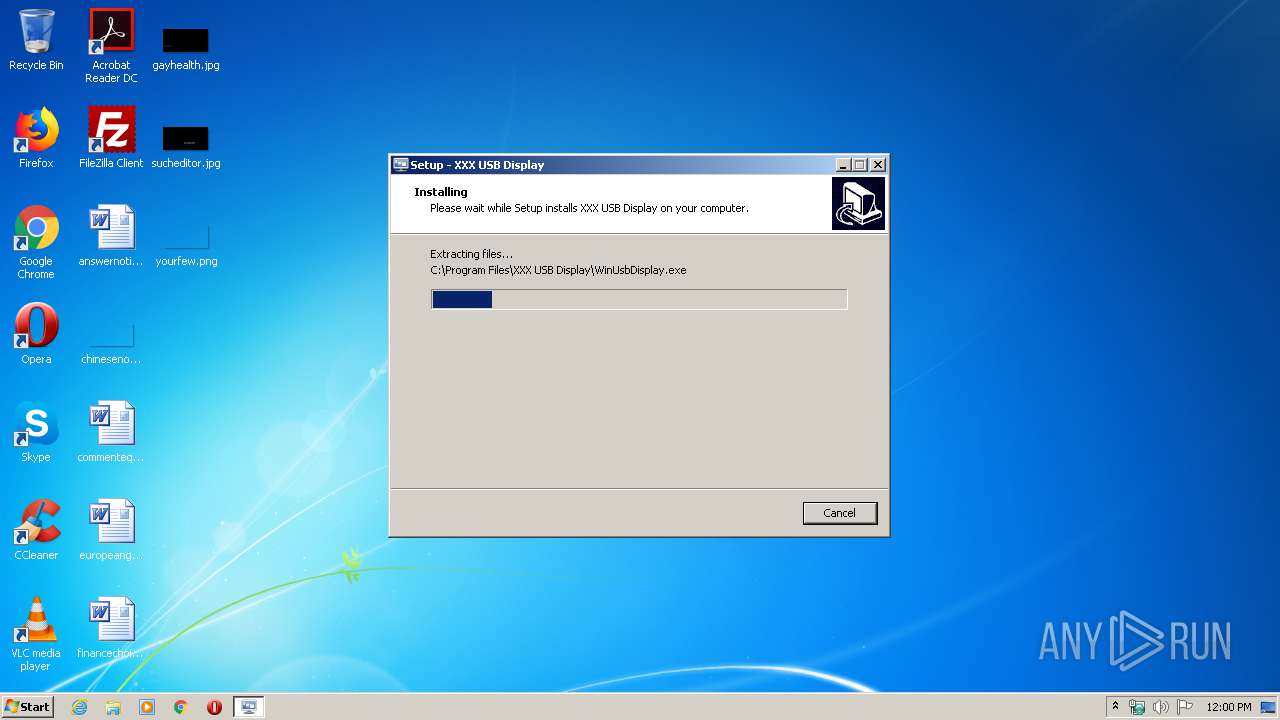
Creates files in the program directory
- Windows7-Windows10_2.0.2.tmp (PID: 2496)
Reads settings of System Certificates
- DrvInst.exe (PID: 3684)
Searches for installed software
- DrvInst.exe (PID: 3684)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2796)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3684)
Changes settings of System certificates
- DrvInst.exe (PID: 3684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 103936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.2.0 |
| ProductVersionNumber: | 2.0.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
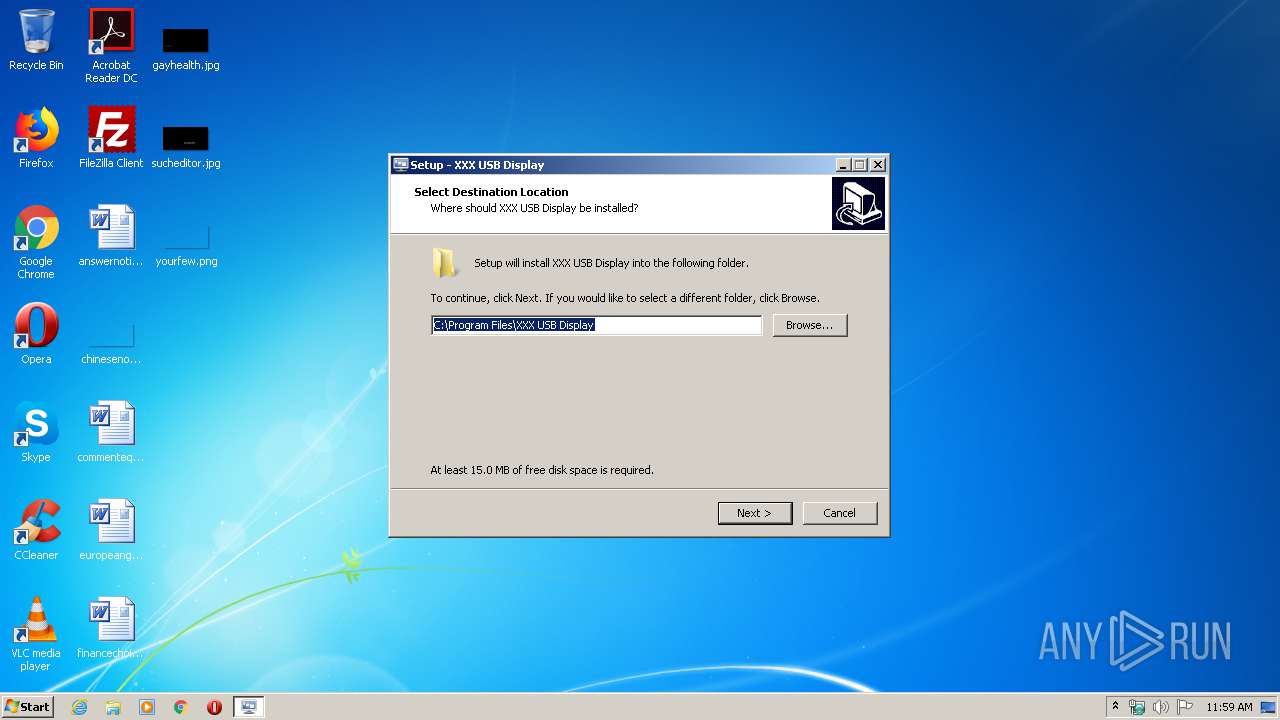
| CompanyName: | XXX |
| FileDescription: | XXX USB Display Setup |
| FileVersion: | 2.0.2 |
| LegalCopyright: | Copyright © XXX 2019 |
| ProductName: | XXX USB Display |
| ProductVersion: | 2.0.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | XXX |
| FileDescription: | XXX USB Display Setup |
| FileVersion: | 2.0.2 |
| LegalCopyright: | Copyright © XXX 2019 |
| ProductName: | XXX USB Display |
| ProductVersion: | 2.0.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A1D0 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64375 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74012 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x0000091C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x00018500 | 0x00018600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.51577 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.92743 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.94832 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.19452 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.14812 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.12637 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.12485 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.83781 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.8115 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.81319 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
46
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2484 | "C:\Users\admin\AppData\Local\Temp\Windows7-Windows10_2.0.2.exe" /SPAWNWND=$A012E /NOTIFYWND=$90140 | C:\Users\admin\AppData\Local\Temp\Windows7-Windows10_2.0.2.exe | Windows7-Windows10_2.0.2.tmp | ||||||||||||
User: admin Company: XXX Integrity Level: HIGH Description: XXX USB Display Setup Exit code: 0 Version: 2.0.2 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\AppData\Local\Temp\is-N2SFG.tmp\Windows7-Windows10_2.0.2.tmp" /SL5="$701CA,4579221,146432,C:\Users\admin\AppData\Local\Temp\Windows7-Windows10_2.0.2.exe" /SPAWNWND=$A012E /NOTIFYWND=$90140 | C:\Users\admin\AppData\Local\Temp\is-N2SFG.tmp\Windows7-Windows10_2.0.2.tmp | Windows7-Windows10_2.0.2.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2796 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3188 | "C:\Users\admin\AppData\Local\Temp\is-KDNEN.tmp\Windows7-Windows10_2.0.2.tmp" /SL5="$90140,4579221,146432,C:\Users\admin\AppData\Local\Temp\Windows7-Windows10_2.0.2.exe" | C:\Users\admin\AppData\Local\Temp\is-KDNEN.tmp\Windows7-Windows10_2.0.2.tmp | — | Windows7-Windows10_2.0.2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3308 | "C:\Users\admin\AppData\Local\Temp\Windows7-Windows10_2.0.2.exe" | C:\Users\admin\AppData\Local\Temp\Windows7-Windows10_2.0.2.exe | explorer.exe | ||||||||||||
User: admin Company: XXX Integrity Level: MEDIUM Description: XXX USB Display Setup Exit code: 0 Version: 2.0.2 Modules
| |||||||||||||||
| 3684 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{48947bd0-9bea-725d-e7d6-eb611c2d0c7d}\MSUSBDisplay.inf" "0" "679d0b0d7" "0000032C" "WinSta0\Default" "00000554" "208" "C:\Program Files\XXX USB Display\lib_usb" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3980 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{5591eb00-5bd1-7444-5ef5-d16810f23250} Global\{0173fedc-f1ea-02e4-c64c-cd3060162176} C:\Windows\System32\DriverStore\Temp\{30265d05-1253-25cb-7216-e74e160bf965}\MSUSBDisplay.inf C:\Windows\System32\DriverStore\Temp\{30265d05-1253-25cb-7216-e74e160bf965}\MSUSBDisplay.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4068 | "C:\Program Files\XXX USB Display\tool\x86\devcon.exe" dp_add "C:\Program Files\XXX USB Display\lib_usb\MSUSBDisplay.inf" USB\VID_534D&PID_6021&MI_03 | C:\Program Files\XXX USB Display\tool\x86\devcon.exe | Windows7-Windows10_2.0.2.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.10586.0 (th2_release.151029-1700) Modules
| |||||||||||||||
Total events
1 876
Read events
628
Write events
1 248
Delete events
0
Modification events
| (PID) Process: | (2496) Windows7-Windows10_2.0.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: C009000088BB33F12DD8D501 | |||
| (PID) Process: | (2496) Windows7-Windows10_2.0.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 087AD5536800083EDD859474EE9E3F6C22CAE3459C9EE14AC3FC388CF0EDDE5C | |||
| (PID) Process: | (2496) Windows7-Windows10_2.0.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2496) Windows7-Windows10_2.0.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\XXX USB Display\libyuv.dll | |||
| (PID) Process: | (2496) Windows7-Windows10_2.0.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: FBA2E99AB080F7F0257BB74ED2EC9103345AB659CC5DEB6B1839A074486F2B77 | |||
| (PID) Process: | (4068) devcon.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (4068) devcon.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2496) Windows7-Windows10_2.0.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Usb Display |
Value: C:\Program Files\XXX USB Display\WinUsbDisplay.exe | |||
| (PID) Process: | (2496) Windows7-Windows10_2.0.2.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Hardware Profiles\0001\System\CurrentControlSet\SERVICES\dfmirage\DEVICE0 |
| Operation: | write | Name: | Attach.ToDesktop |
Value: 0 | |||
| (PID) Process: | (2496) Windows7-Windows10_2.0.2.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files\XXX USB Display\WinUsbDisplay.exe |
Value: HIGHDPIAWARE | |||
Executable files
39
Suspicious files
3
Text files
36
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\is-LDMMI.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\is-E223V.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\is-DP9SA.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\is-R220A.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\is-66P7E.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\is-FMEBE.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\is-T550L.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\tool\x64\is-OPVH0.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\tool\x64\is-G8Q1U.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | Windows7-Windows10_2.0.2.tmp | C:\Program Files\XXX USB Display\tool\x86\is-GRKIQ.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report