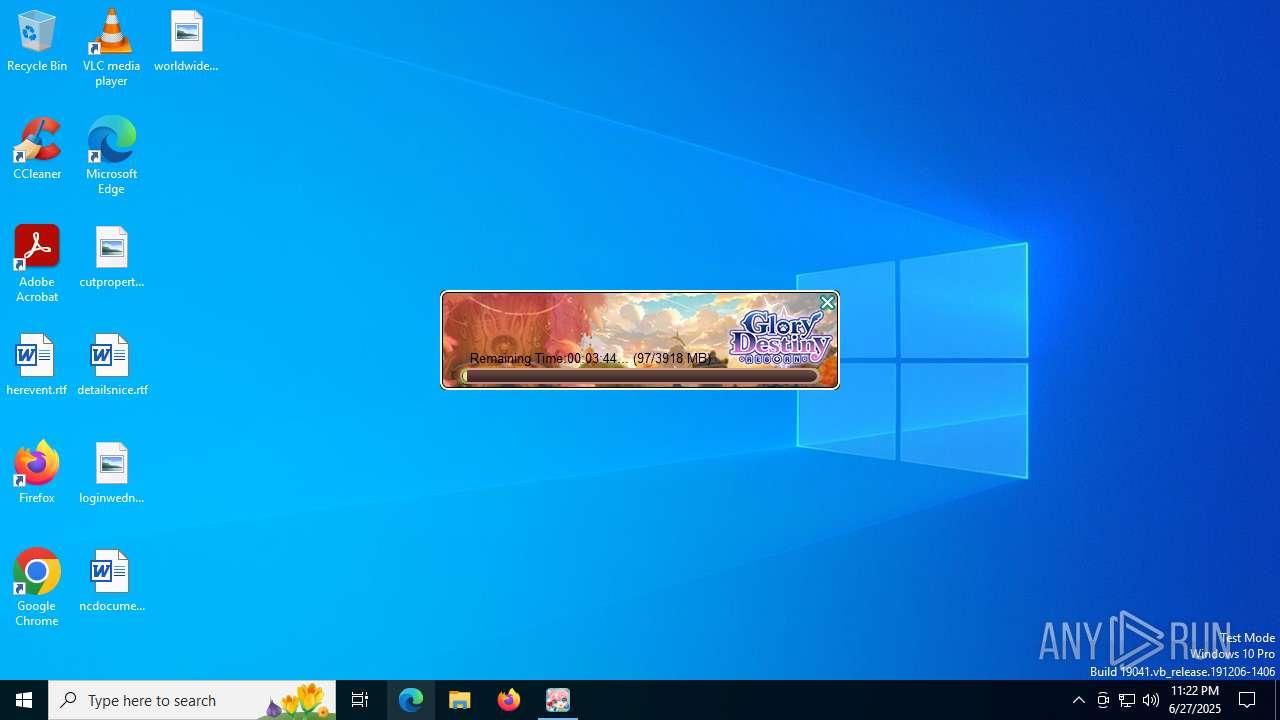
| File name: | downloader.exe |
| Full analysis: | https://app.any.run/tasks/bf1749a6-ca00-49f2-9a2c-e18b8bb9b291 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2025, 23:22:35 |
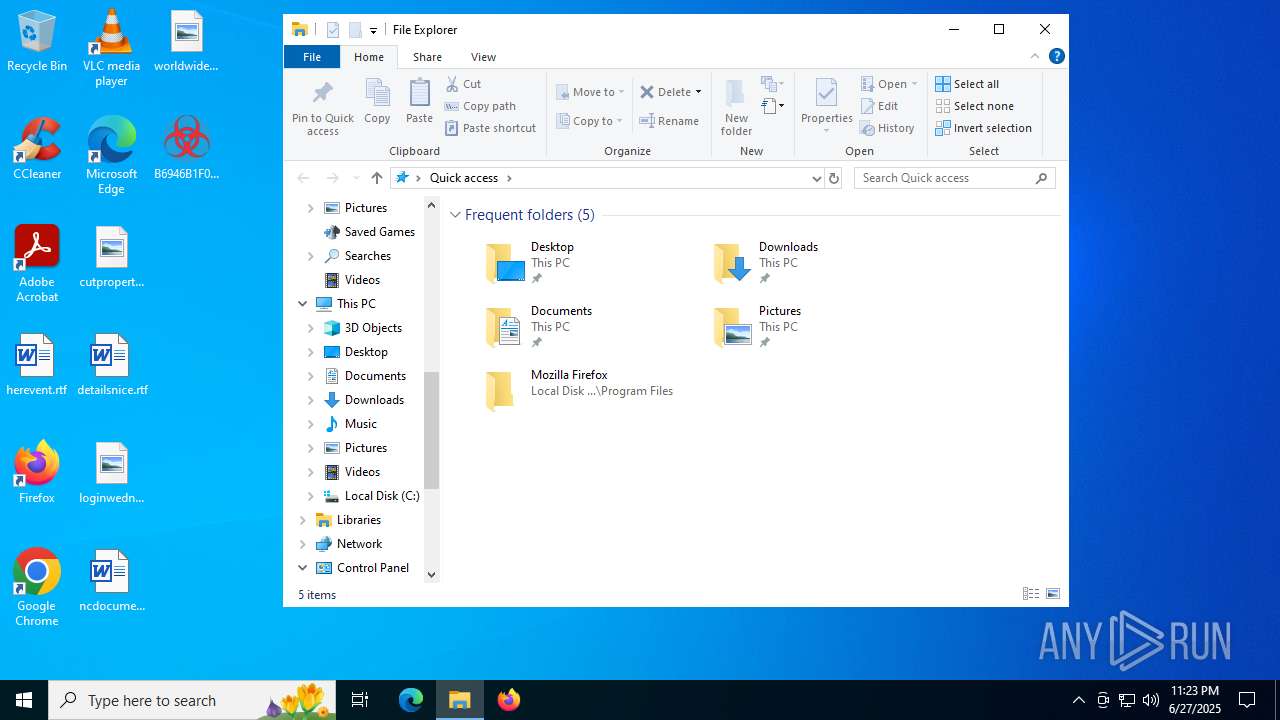
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | C8039AD0C8C2DC485CE36F7AE894E213 |
| SHA1: | EC43564C372A36204A7731FD5132658E3A4E6D5B |
| SHA256: | A2552B80EB856209C4FF750B98299CC9EE8B1E50773E09FC0FB0979D1A41130B |
| SSDEEP: | 98304:zgjexyPE+Ksxo108j37sZmSMH0Bl7PGR5NENotctFmNzjZINnCp:SiZ |
MALICIOUS
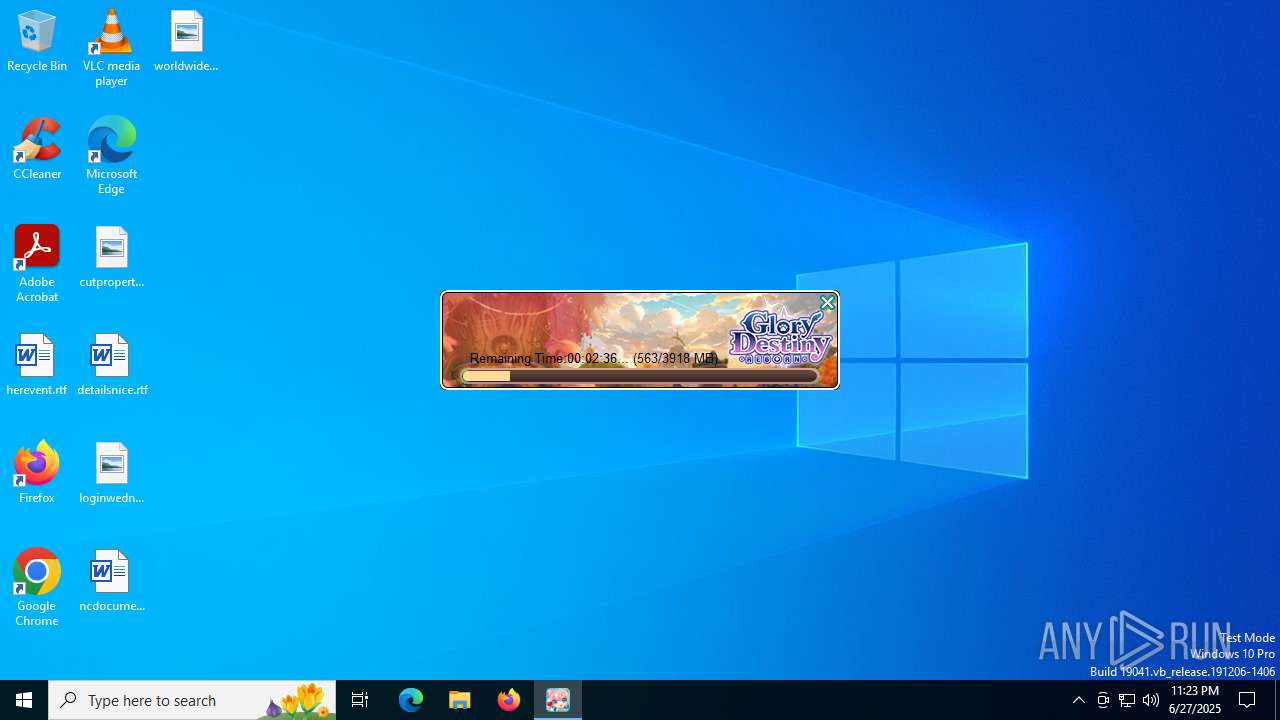
XWORM has been detected (YARA)
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Create files in the Startup directory
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Uses Task Scheduler to run other applications
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Changes the autorun value in the registry
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
SUSPICIOUS
Executable content was dropped or overwritten
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Reads security settings of Internet Explorer
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Reads the date of Windows installation
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Checks for external IP
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
INFO
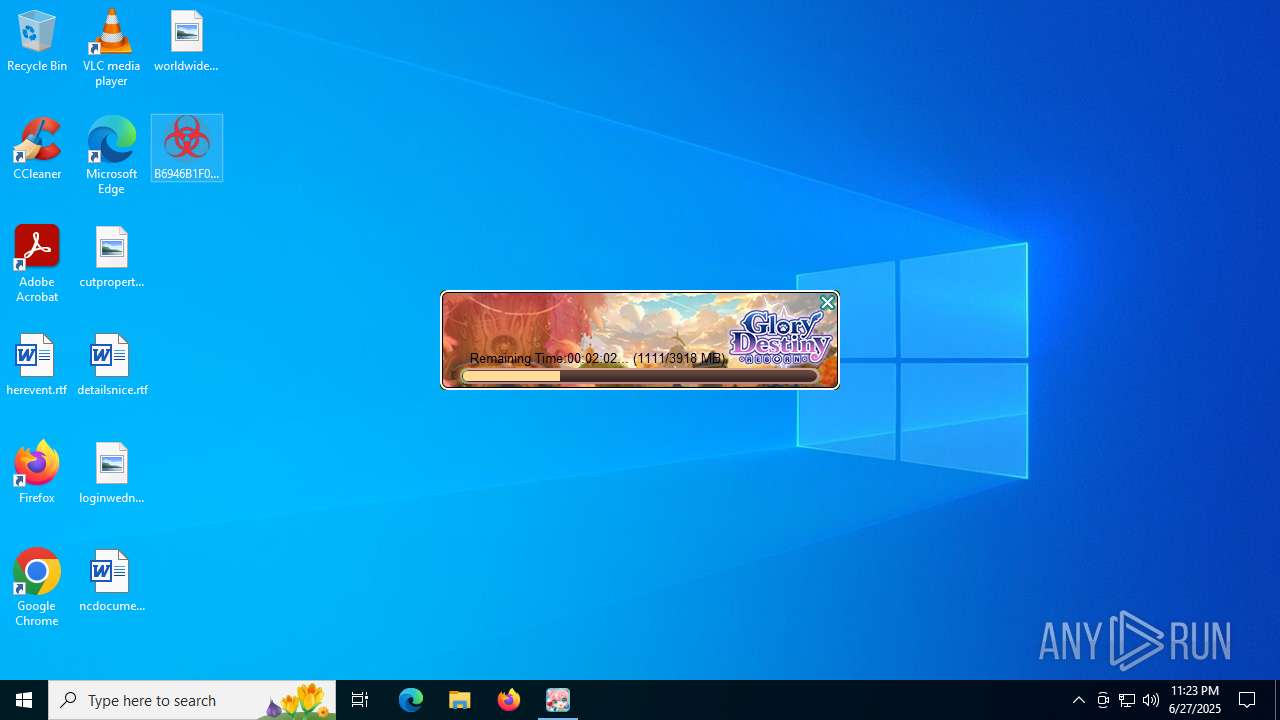
Create files in a temporary directory
- downloader.exe (PID: 1800)
Reads the computer name
- downloader.exe (PID: 1800)
- identity_helper.exe (PID: 7612)
- identity_helper.exe (PID: 7496)
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Checks supported languages
- downloader.exe (PID: 1800)
- identity_helper.exe (PID: 7612)
- identity_helper.exe (PID: 7496)
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
The sample compiled with english language support
- downloader.exe (PID: 1800)
Manual execution by a user
- msedge.exe (PID: 5884)
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Application launched itself
- msedge.exe (PID: 5884)
- msedge.exe (PID: 8052)
Reads Environment values
- identity_helper.exe (PID: 7496)
- identity_helper.exe (PID: 7612)
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Reads the machine GUID from the registry
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Checks proxy server information
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Disables trace logs
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Creates files or folders in the user directory
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Process checks computer location settings
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Launching a file from a Registry key
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Launching a file from the Startup directory
- B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe (PID: 6412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(6412) B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe
C2127.0.0.1:7000
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep timeXWorm V5.6
USB drop nameUSB.exe
MutexUtJ7ZasGXWAI3fWM
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:26 11:27:53+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 2456064 |
| InitializedDataSize: | 1152512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1adabc |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.0.1 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | X-LEGEND ENTERTAINMENT |
| FileDescription: | downloader |
| FileVersion: | 003.003.01.01 |
| InternalName: | UpgradeClient |
| LegalCopyright: | Copyright (C) 2023 |
| OriginalFileName: | downloader.exe |
| ProductName: | downloader |
| ProductVersion: | 003.003.01.01 |
Total processes
171
Monitored processes
32
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5176,i,2285643622879835898,10490330109441220326,262144 --variations-seed-version --mojo-platform-channel-handle=5124 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\AppData\Local\Temp\downloader.exe" | C:\Users\admin\AppData\Local\Temp\downloader.exe | explorer.exe | ||||||||||||
User: admin Company: X-LEGEND ENTERTAINMENT Integrity Level: HIGH Description: downloader Exit code: 0 Version: 003.003.01.01 Modules
| |||||||||||||||
| 2144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2372,i,2285643622879835898,10490330109441220326,262144 --variations-seed-version --mojo-platform-channel-handle=2364 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2216 | "C:\Users\admin\AppData\Local\Temp\downloader.exe" | C:\Users\admin\AppData\Local\Temp\downloader.exe | — | explorer.exe | |||||||||||
User: admin Company: X-LEGEND ENTERTAINMENT Integrity Level: MEDIUM Description: downloader Exit code: 3221226540 Version: 003.003.01.01 Modules
| |||||||||||||||
| 2716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4388f208,0x7ffc4388f214,0x7ffc4388f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2804 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3564,i,3276279599854113945,10519005973138712388,262144 --variations-seed-version --mojo-platform-channel-handle=3636 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3556,i,3276279599854113945,10519005973138712388,262144 --variations-seed-version --mojo-platform-channel-handle=3608 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2456,i,2285643622879835898,10490330109441220326,262144 --variations-seed-version --mojo-platform-channel-handle=2736 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4328,i,3276279599854113945,10519005973138712388,262144 --variations-seed-version --mojo-platform-channel-handle=4280 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
7 697
Read events
7 655
Write events
42
Delete events
0
Modification events
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 45DE9F3D2C972F00 | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F897A53D2C972F00 | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328538 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {79CBED6A-5B9D-40E5-A8FD-F3C7098939E4} | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328538 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {450E27C2-D37B-4D0B-A8D5-9AB442756AED} | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328538 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {52D76017-43E4-4519-9B10-A616810887E2} | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328538 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0B78B8DF-1893-4ED0-BCC7-90CD2942B459} | |||
Executable files
32
Suspicious files
440
Text files
91
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17825f.TMP | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17825f.TMP | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17826e.TMP | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17827e.TMP | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17827e.TMP | — | |
MD5:— | SHA256:— | |||
| 5884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17827e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
102
DNS requests
84
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEGDUKU22KGmcLGO30X34eu4%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 143.204.99.128:80 | http://ocsp.r2m04.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTihuFvpmFDw5hOcIp918Jm5B3CQgQUH1KSYVaCVH%2BBZtgdPQqqMlyH3QgCEAELYlnUBNCv4XzEJQoa3II%3D | unknown | — | — | unknown |
6320 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 18.245.38.41:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEk8qlS4%2B0YpYvbhdG8DOXyc%3D | unknown | — | — | whitelisted |
6828 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:umzCIQfETPdjb1pBdbCssLGozAT97GAdyO5gh1MxV14&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.180:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7872 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6412 | B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe | GET | 200 | 45.125.247.123:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1800 | downloader.exe | 130.211.25.215:443 | en-fn-api.x-legend.com | GOOGLE | US | whitelisted |
764 | lsass.exe | 104.18.38.233:80 | ocsp.usertrust.com | CLOUDFLARENET | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1800 | downloader.exe | 18.245.86.103:443 | dlg.x-legend.tw | — | US | unknown |
764 | lsass.exe | 18.245.38.41:80 | ocsp.rootca1.amazontrust.com | — | US | whitelisted |
764 | lsass.exe | 143.204.99.128:80 | ocsp.r2m04.amazontrust.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
en-fn-api.x-legend.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
dlg.x-legend.tw |
| unknown |
ocsp.rootca1.amazontrust.com |
| whitelisted |
ocsp.r2m04.amazontrust.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |
6828 | msedge.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6828 | msedge.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6412 | B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe | A Network Trojan was detected | ET MALWARE Common Stealer Behavior - Source IP Associated with Hosting Provider Check via ip.api .com |
6412 | B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
6412 | B6946B1F0370C2ECDA4EA6339ECF79092AC46DA1D5E79331E07674DA2BD3BF42.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.tw domain |