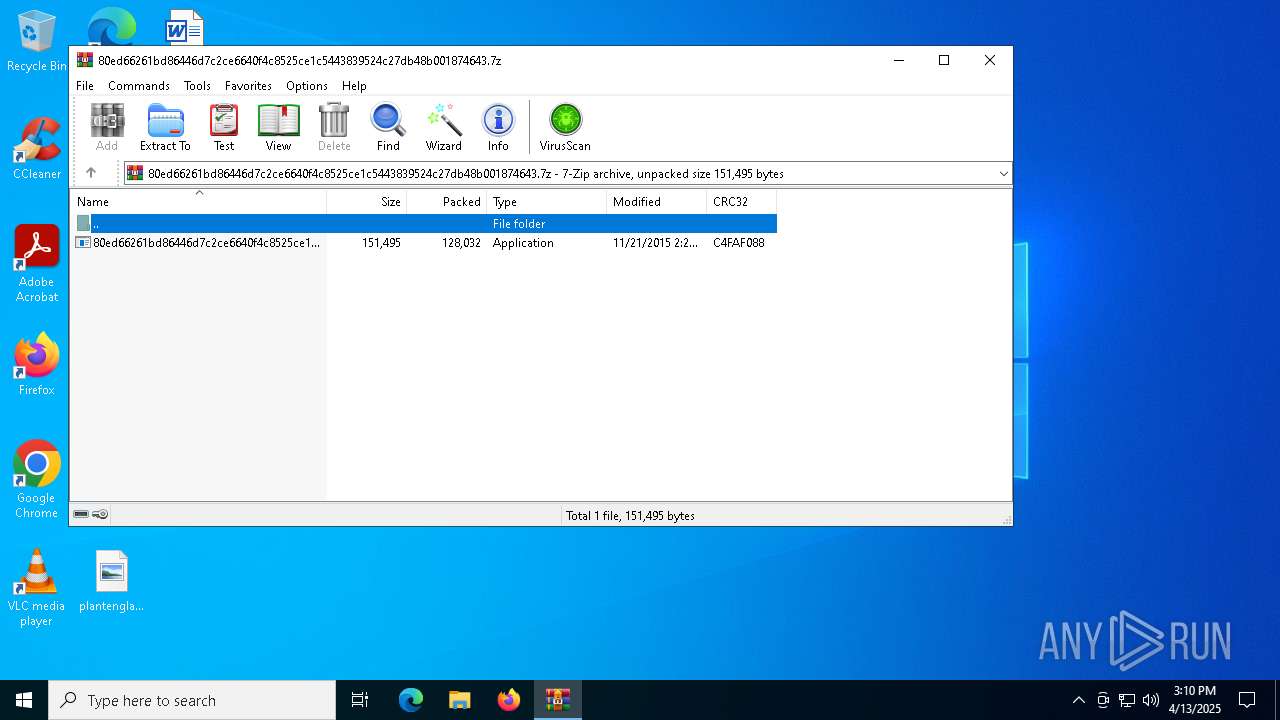
| File name: | 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.7z |
| Full analysis: | https://app.any.run/tasks/22898fa5-81f5-40ad-a6d4-2d89718f8f6b |
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2025, 15:10:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | AD5A08F48F402FBF464FBB64E8356759 |
| SHA1: | 99D8EA826B72CF23F2ACDE69C8B7D2458AE88B54 |
| SHA256: | A251795E6B1DCAC29E33B013DDDCB0B658DB568756ADDC99616AD2430106A493 |
| SSDEEP: | 3072:/j81YtR5R0XNOqK3wqNv54/hBcUpJxyjzIVhqB4MY/:/Y1Yloq3wqbChBcUpejAhq23/ |
MALICIOUS
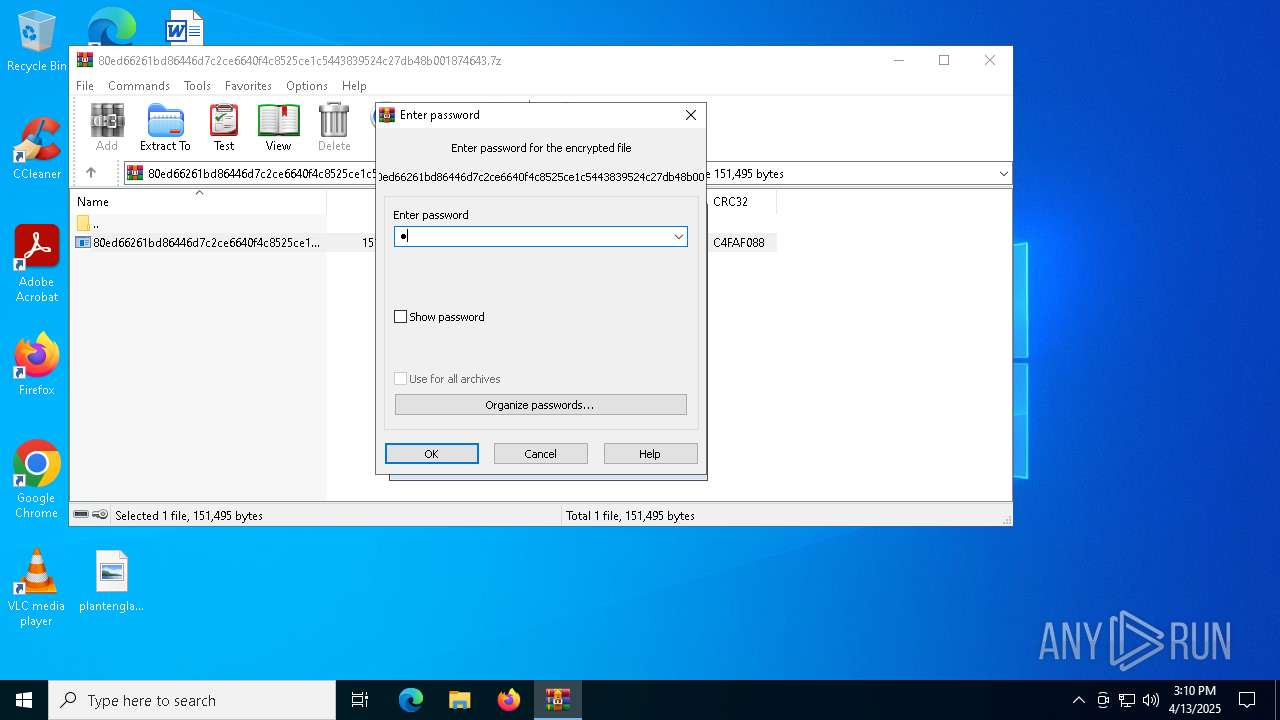
Generic archive extractor
- WinRAR.exe (PID: 2568)
Changes the autorun value in the registry
- explorer.exe (PID: 5512)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 1452)
Executable content was dropped or overwritten
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 1452)
- explorer.exe (PID: 5512)
Application launched itself
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 1452)
The process creates files with name similar to system file names
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 1452)
There is functionality for taking screenshot (YARA)
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 1452)
Executes as Windows Service
- VSSVC.exe (PID: 6752)
INFO
Executable content was dropped or overwritten
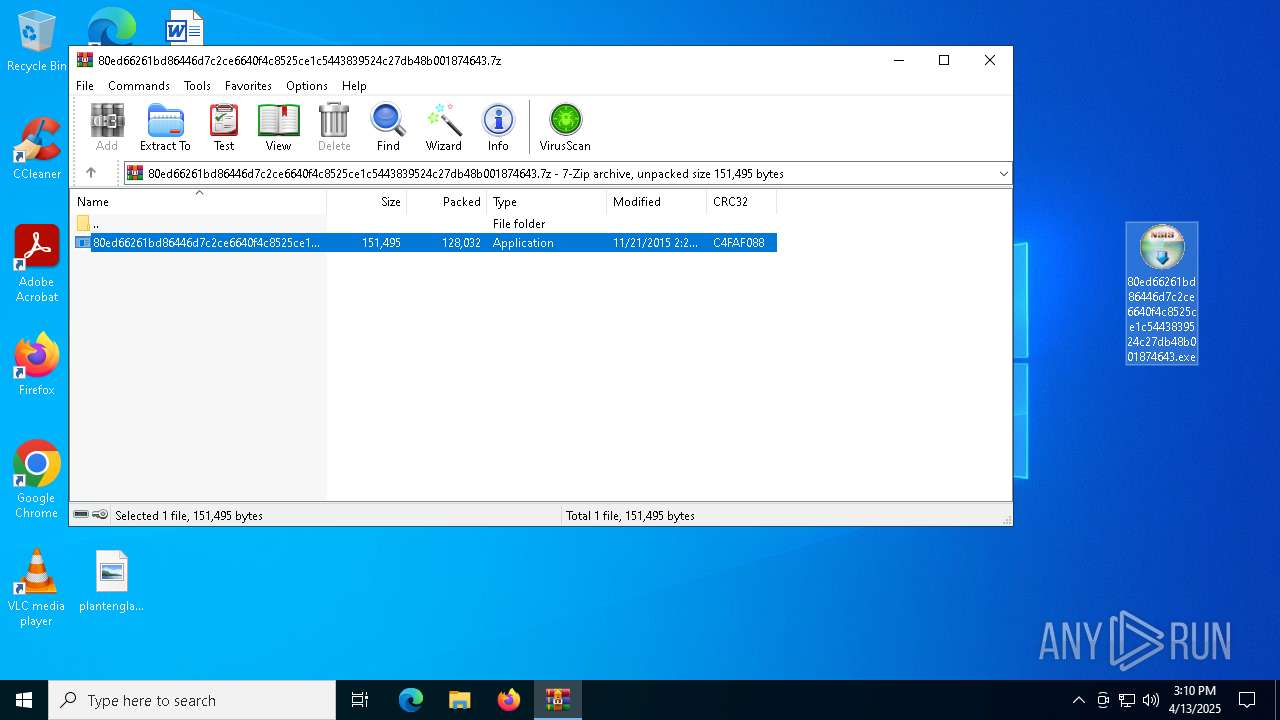
- WinRAR.exe (PID: 2568)
Checks supported languages
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 1452)
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 660)
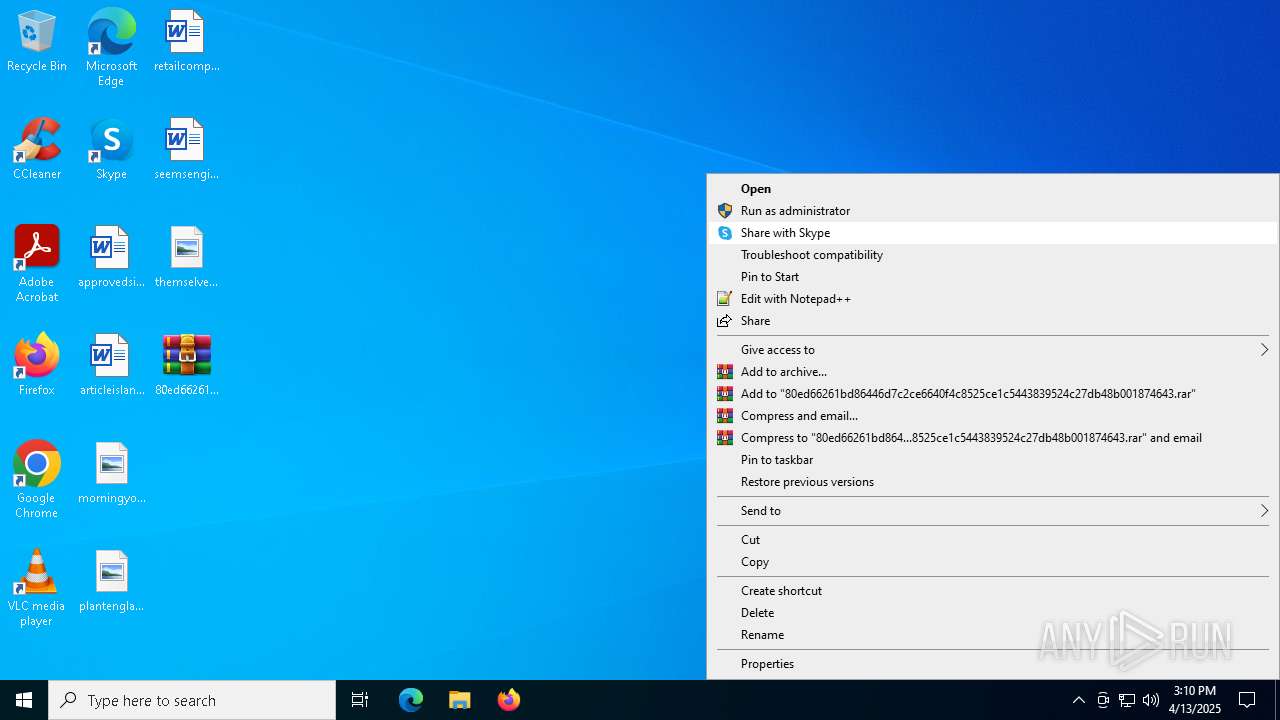
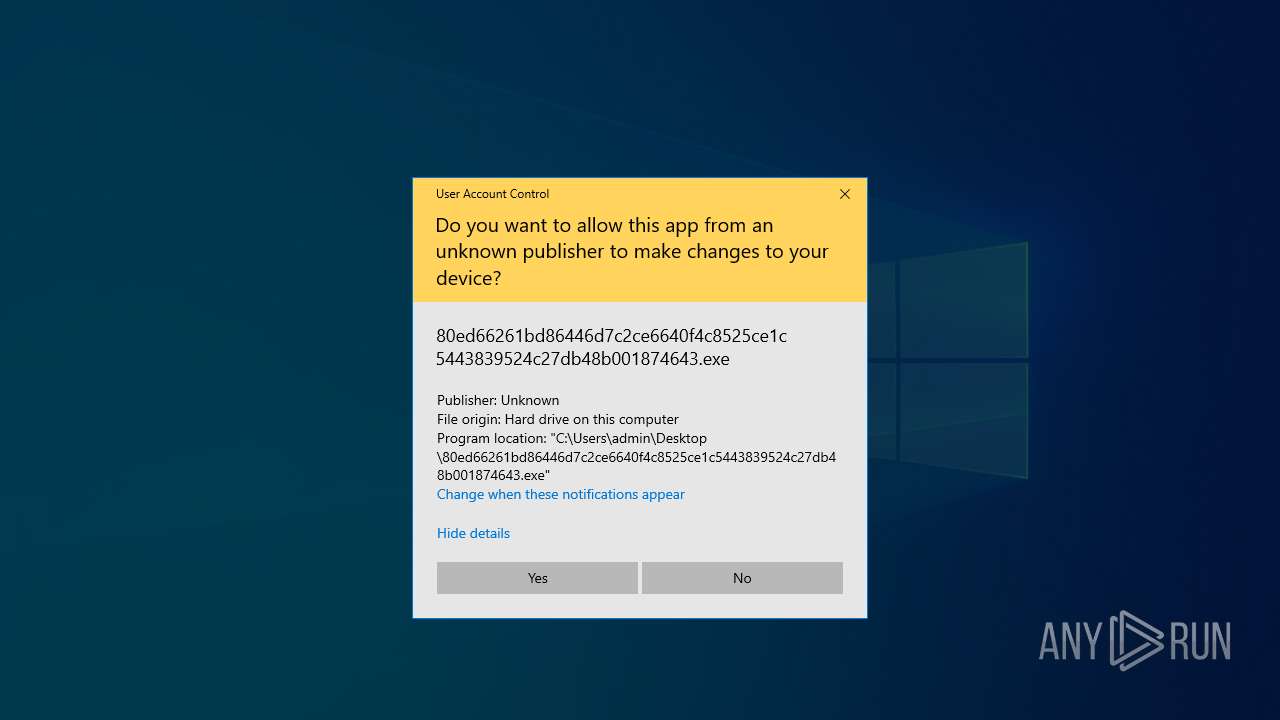
Manual execution by a user
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 1452)
Create files in a temporary directory
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 1452)
Reads the machine GUID from the registry
- 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe (PID: 660)
Creates files or folders in the user directory
- explorer.exe (PID: 5512)
Checks proxy server information
- svchost.exe (PID: 6620)
Reads security settings of Internet Explorer
- svchost.exe (PID: 6620)
Reads the software policy settings
- slui.exe (PID: 6944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2015:11:21 02:26:41+00:00 |
| ArchivedFileName: | 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe |
Total processes
139
Monitored processes
10
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Users\admin\Desktop\80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe" | C:\Users\admin\Desktop\80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | — | 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 976 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | "C:\Users\admin\Desktop\80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe" | C:\Users\admin\Desktop\80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5512 | "C:\WINDOWS\syswow64\explorer.exe" | C:\Windows\SysWOW64\explorer.exe | 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | -k netsvcs | C:\Windows\SysWOW64\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6944 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 355
Read events
21 332
Write events
4 023
Delete events
0
Modification events
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.7z | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
4
Suspicious files
15
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2568.35347\80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | executable | |
MD5:5AFBD4CD8F009A87F9F01BFBFF99E988 | SHA256:80ED66261BD86446D7C2CE6640F4C8525CE1C5443839524C27DB48B001874643 | |||
| 1452 | 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | C:\Users\admin\AppData\Local\Temp\README_gu.txt | binary | |
MD5:45381E4118FE3203CADA29A73605FED1 | SHA256:E7EACDE843B9EA74C40D074610174C2230526B8ADE99CD3F100B445CEE7060F9 | |||
| 1452 | 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | C:\Users\admin\AppData\Local\Temp\pottychair.dll | executable | |
MD5:D9AE34810DA663AAABFCE770E0DB1907 | SHA256:898C4165F0092EC86FFEBF40F6402B26566EEDC13F26AA37D802EDC5F48FB38B | |||
| 6620 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\42995AE0FEC5E647698078694F5B7391 | binary | |
MD5:E1A0931E8FAA3CC58D1774F82AC00C56 | SHA256:470DBDDE27A1320AED697530240D34A0AC124E9AB52FCE7B15233D7C910322FC | |||
| 6620 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:F2E21F07C3F5867D7B226FE3F45A5E5A | SHA256:26049285468E98C1A91B48C203D2532FA226AA32588F101B5E45AF9E381EAAFC | |||
| 1452 | 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | C:\Users\admin\AppData\Local\Temp\DromondKorfball | binary | |
MD5:897F28E9F39F31EE48A0E8AB078C2285 | SHA256:CFA45316354A2469444DAAC327C907E86A9150008255BA21DC4D5FDB7268D709 | |||
| 6620 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5026C025B597E6A7C455BC1473E76F49 | binary | |
MD5:C84DE42973E2A44D7D31E28ED4A8C958 | SHA256:1C640FD0D4E090AB28167DDBC7D229B6B3DB8D86852BD3BF4FBE1E60EA90C01C | |||
| 6620 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\42995AE0FEC5E647698078694F5B7391 | binary | |
MD5:598C80B6219A515E7A7320009F867920 | SHA256:E90EE877777A532F8BDCF7AB6CF4C6ABB5C2CB6F3DC5EF73D1DDADD0C22E5484 | |||
| 6620 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7BC181335C3346F76EF8A8BCFE6C5519 | binary | |
MD5:5FAA2975181B9505C3A6DB84702C477E | SHA256:450CF1AD58C43FCCB26C97638FBB532543C0CD5F6C570E3C676CBB53CDB781E4 | |||
| 1452 | 80ed66261bd86446d7c2ce6640f4c8525ce1c5443839524c27db48b001874643.exe | C:\Users\admin\AppData\Local\Temp\nsfEAC1.tmp\System.dll | executable | |
MD5:883EFF06AC96966270731E4E22817E11 | SHA256:44E5DFD551B38E886214BD6B9C8EE913C4C4D1F085A6575D97C3E892B925DA82 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
71
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6620 | svchost.exe | POST | 404 | 65.109.37.150:80 | http://markaz-e-umeed.com.pk/UKXj_6.php?d=sln5w1x4adoe5h | unknown | — | — | unknown |
6620 | svchost.exe | GET | 200 | 2.19.217.103:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5428 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6620 | svchost.exe | POST | 200 | 185.53.178.54:80 | http://florencebeauty.pl/luvrLh.php?f=sln5w1x4adoe5h | unknown | — | — | malicious |
6620 | svchost.exe | POST | 301 | 51.91.236.193:80 | http://golfgiovanilombardia.it/OzGkyc.php?p=sln5w1x4adoe5h | unknown | — | — | malicious |
6620 | svchost.exe | GET | 200 | 2.16.2.75:80 | http://e6.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBTUejiAQejpjQc4fOz2ttjyD6VkMQQUDcXM%2FZvuFAWhTDCCpT5eisNYCdICEgP7D7k8UVYcSZs8O1lJIDl3VA%3D%3D | unknown | — | — | whitelisted |
5428 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6620 | svchost.exe | POST | 202 | 35.215.104.243:80 | http://djmfr.com/MNf6vV.php?a=sln5w1x4adoe5h | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6620 | svchost.exe | 65.109.37.150:80 | markaz-e-umeed.com.pk | Hetzner Online GmbH | FI | unknown |
6620 | svchost.exe | 51.91.236.193:80 | golfgiovanilombardia.it | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
markaz-e-umeed.com.pk |
| unknown |
golfgiovanilombardia.it |
| unknown |
x1.c.lencr.org |
| whitelisted |
e6.o.lencr.org |
| whitelisted |