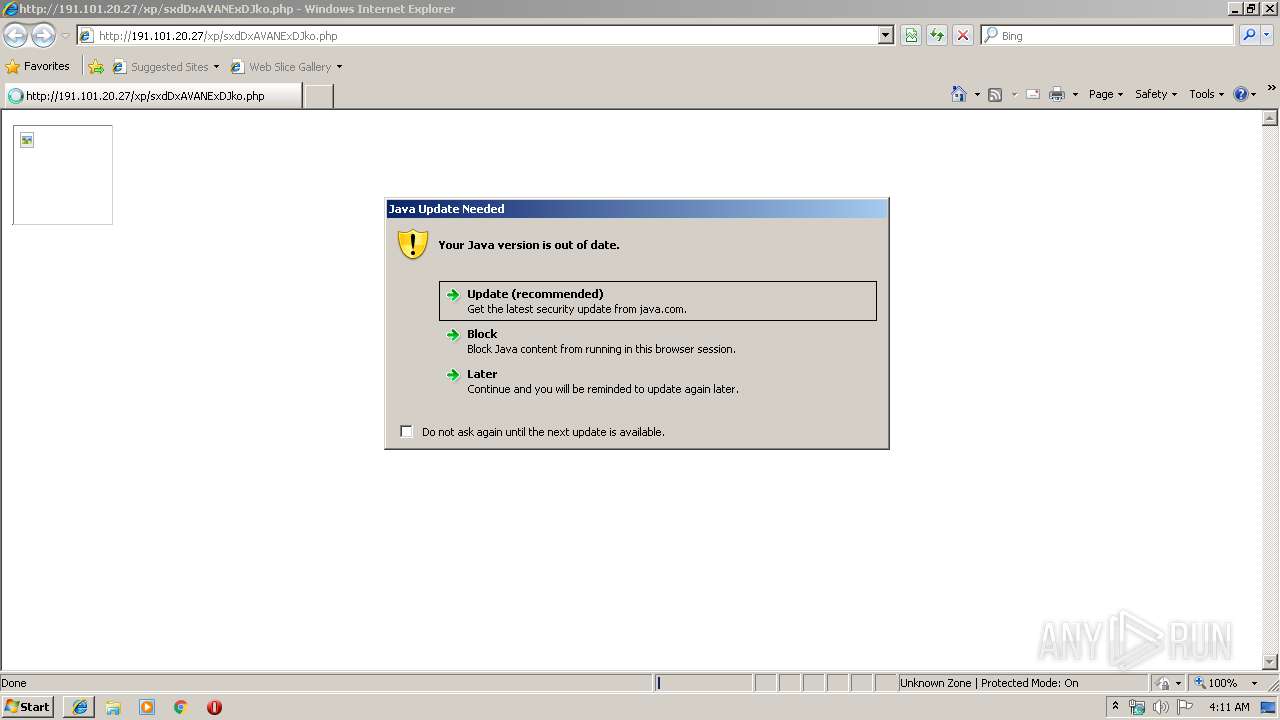
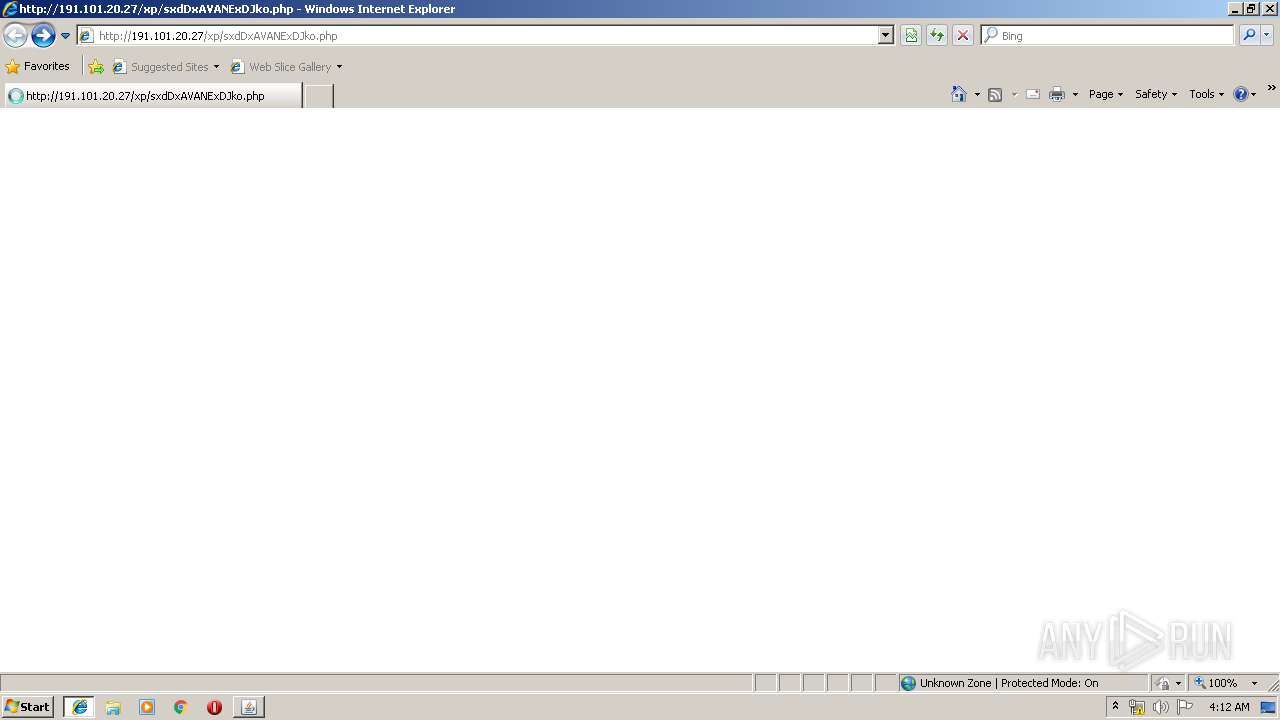
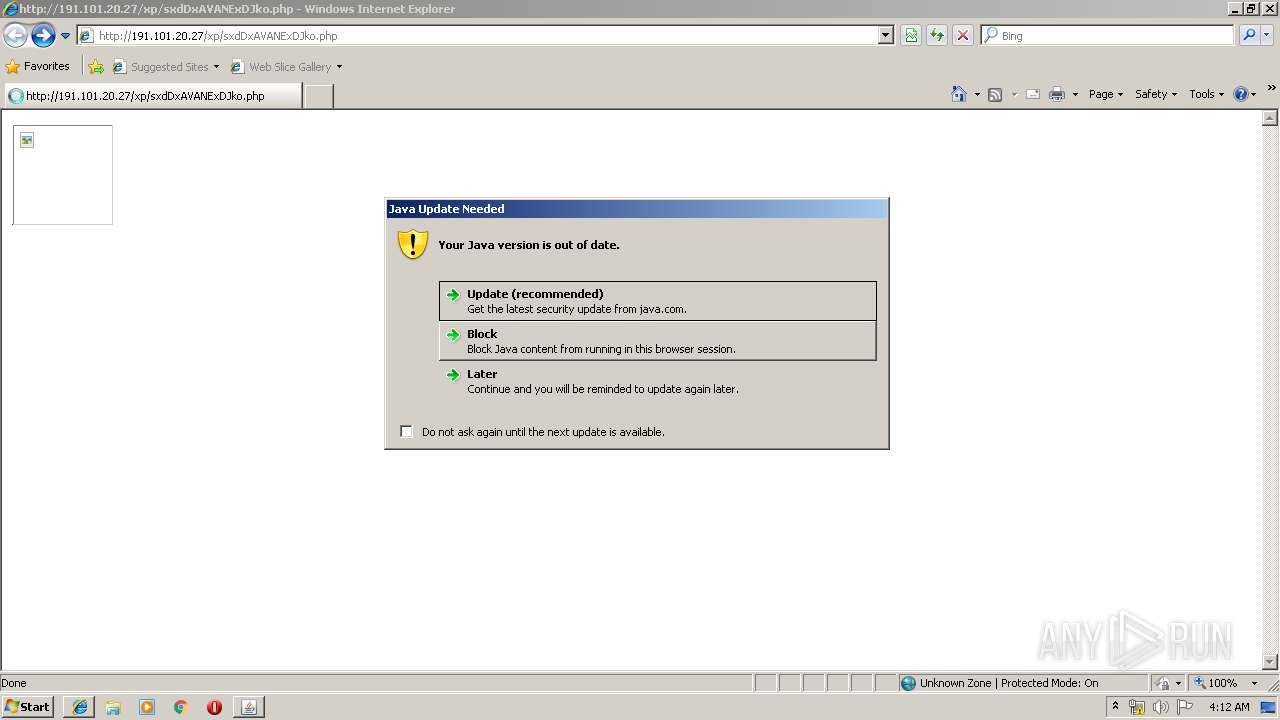
| URL: | http://191.101.20.27/xp/sxdDxAVANExDJko.php |
| Full analysis: | https://app.any.run/tasks/3b8c356c-fb3e-4459-910d-e609e2c669f2 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 04:10:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 22382B39F006D0D7CBE4FF9F72642C5B |
| SHA1: | 9AE6A56EF84875E4C154108F042B15E774720C4E |
| SHA256: | A24418389694ACF0D15A6765DEA8EBCBBAA7540C1E30F63C9BD480B2F400683A |
| SSDEEP: | 3:N1KkU1BSCWvH:CkUrSCWvH |
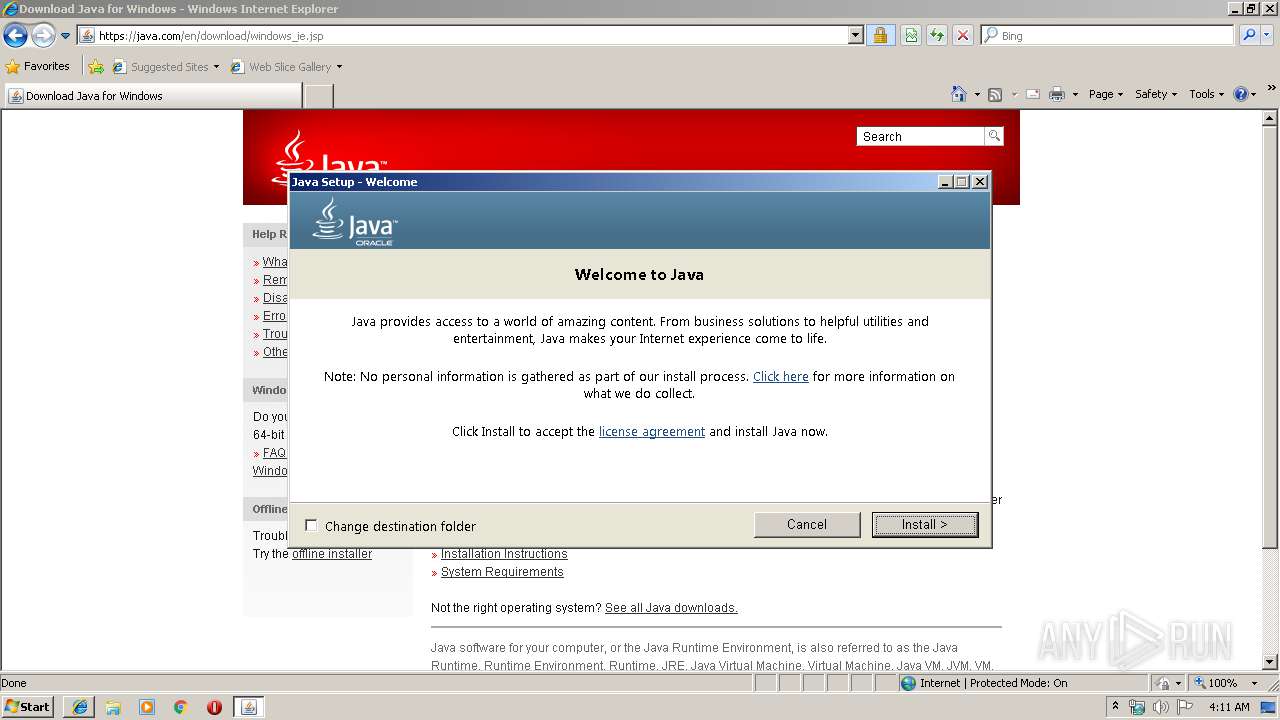
MALICIOUS
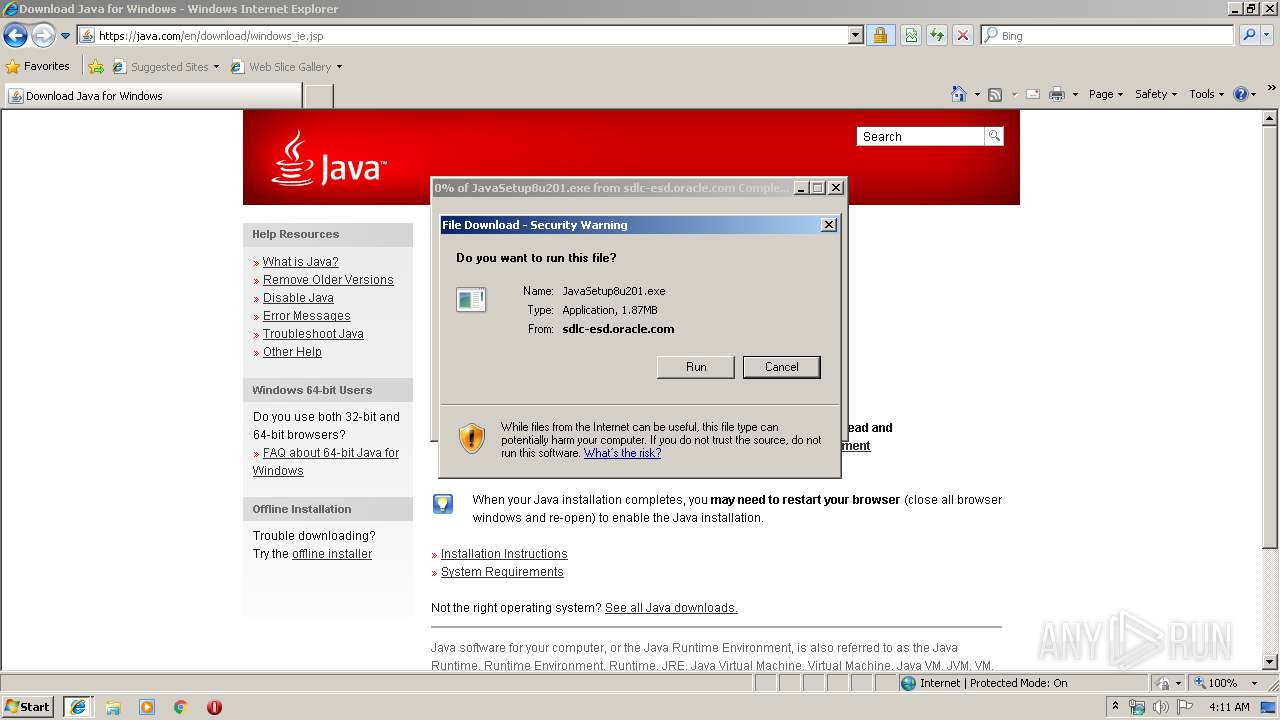
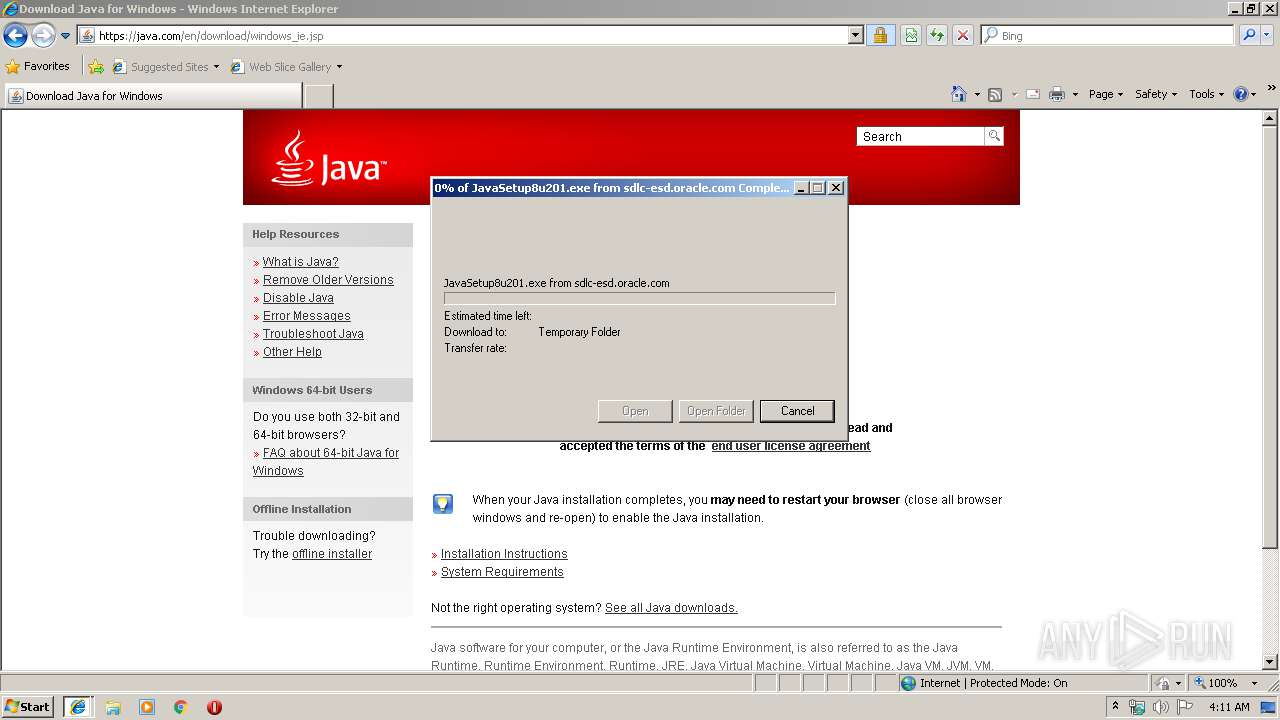
Application was dropped or rewritten from another process
- JavaSetup8u201[1].exe (PID: 3880)
- JavaSetup8u201[1].exe (PID: 3272)
- JavaSetup8u201[1].exe (PID: 2624)
- LZMA_EXE (PID: 292)
- LZMA_EXE (PID: 2988)
- bspatch.exe (PID: 3796)
- javaw.exe (PID: 2252)
- unpack200.exe (PID: 916)
- unpack200.exe (PID: 2740)
- unpack200.exe (PID: 3236)
- unpack200.exe (PID: 2124)
- unpack200.exe (PID: 2600)
- ssvagent.exe (PID: 1012)
- unpack200.exe (PID: 1580)
- unpack200.exe (PID: 2924)
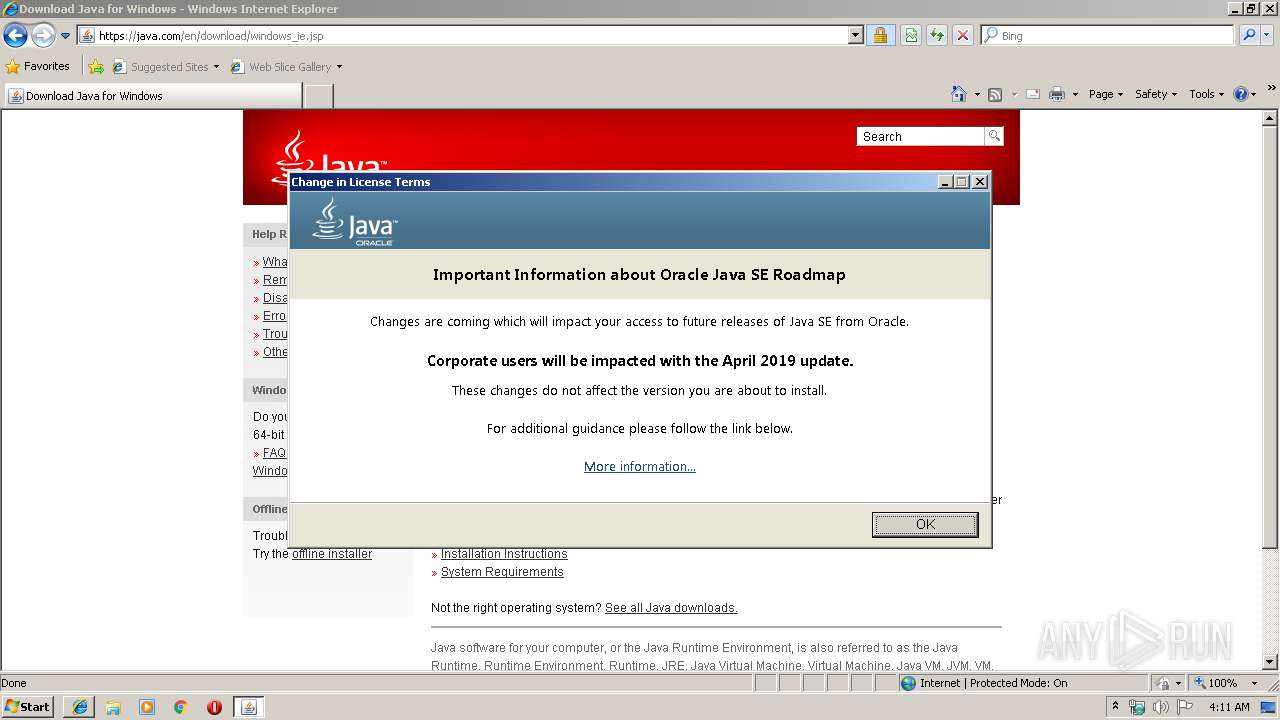
Changes settings of System certificates
- JavaSetup8u201[1].exe (PID: 3272)
Loads dropped or rewritten executable
- javaw.exe (PID: 2252)
- installer.exe (PID: 3964)
- javaw.exe (PID: 2988)
- javaw.exe (PID: 3556)
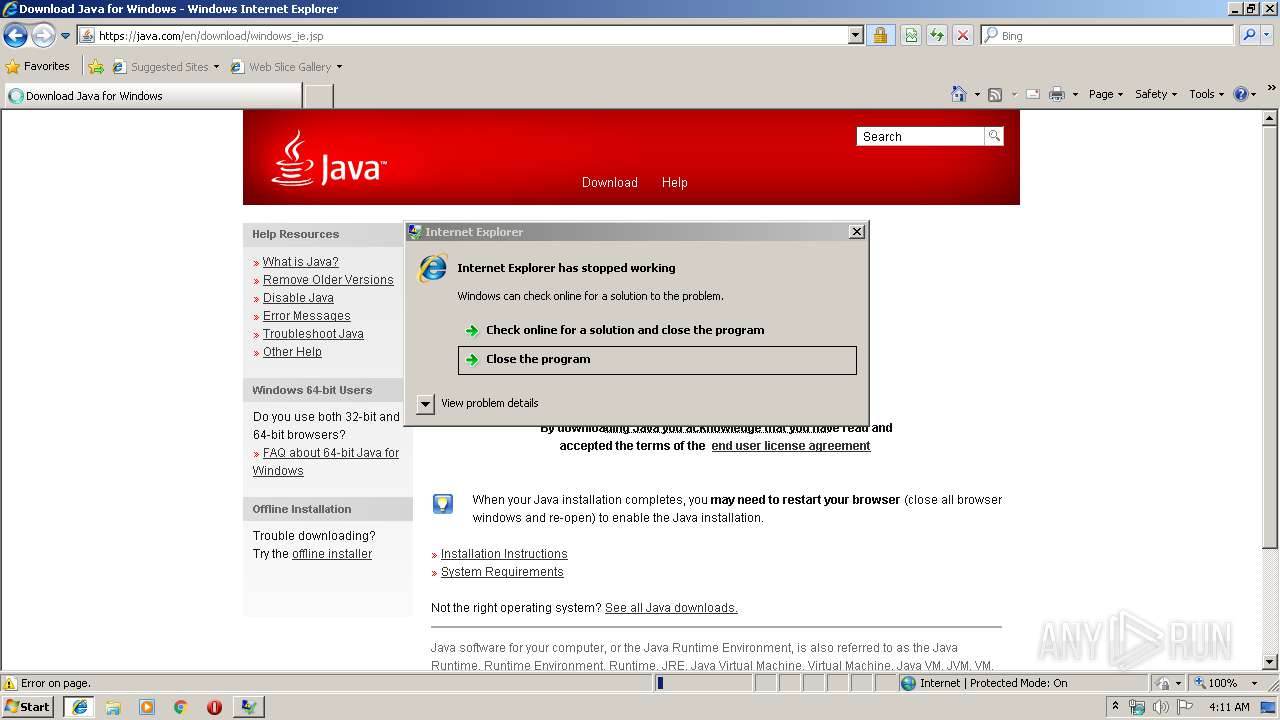
- WerFault.exe (PID: 1476)
- iexplore.exe (PID: 2572)
- javaw.exe (PID: 3888)
- jp2launcher.exe (PID: 2060)
- javaw.exe (PID: 128)
- unpack200.exe (PID: 2924)
- unpack200.exe (PID: 3236)
- unpack200.exe (PID: 1580)
- iexplore.exe (PID: 928)
- unpack200.exe (PID: 2600)
- javaw.exe (PID: 2920)
- unpack200.exe (PID: 916)
- javaw.exe (PID: 3412)
- unpack200.exe (PID: 2124)
- unpack200.exe (PID: 2740)
- javaw.exe (PID: 1216)
- javaw.exe (PID: 2876)
- ssvagent.exe (PID: 1012)
- javaw.exe (PID: 2124)
SUSPICIOUS
Creates executable files which already exist in Windows
- WerFault.exe (PID: 1476)
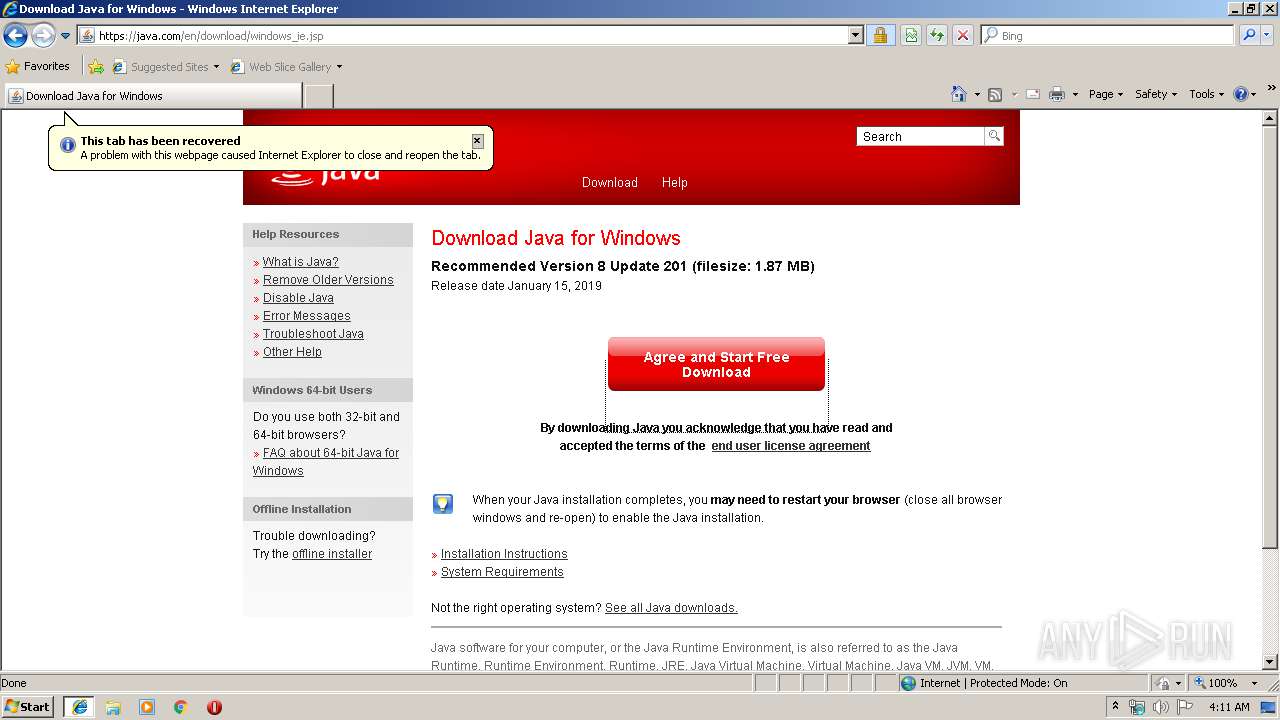
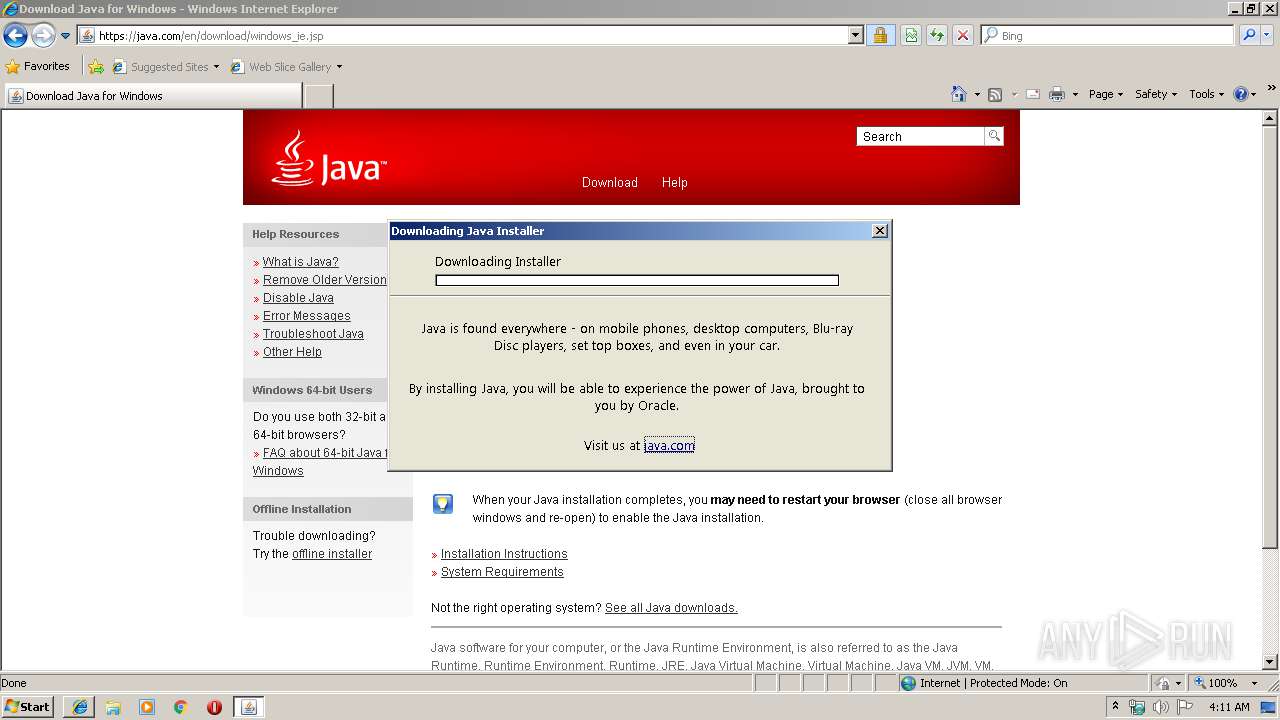
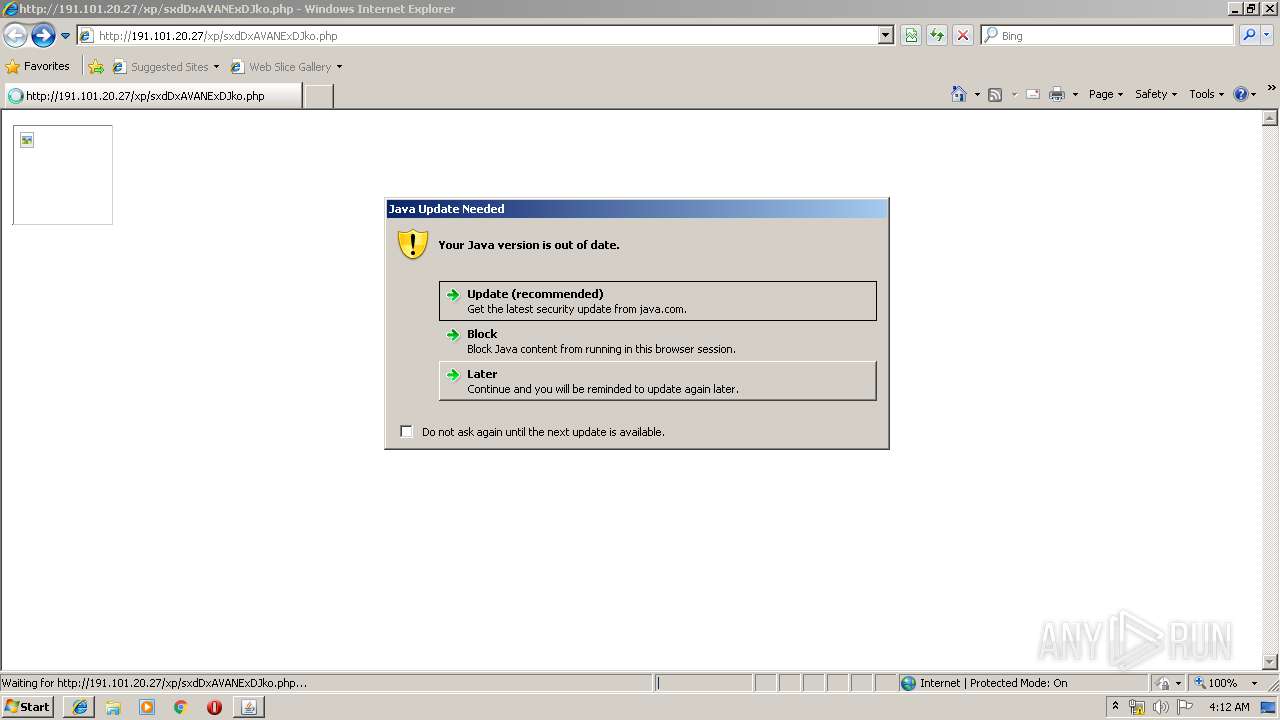
Executes JAVA applets
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 928)
- installer.exe (PID: 3964)
Executable content was dropped or overwritten
- iexplore.exe (PID: 928)
- iexplore.exe (PID: 1920)
- JavaSetup8u201[1].exe (PID: 2624)
- msiexec.exe (PID: 3528)
- JavaSetup8u201[1].exe (PID: 3272)
- installer.exe (PID: 3964)
Adds / modifies Windows certificates
- JavaSetup8u201[1].exe (PID: 3272)
Reads internet explorer settings
- JavaSetup8u201[1].exe (PID: 3272)
Starts application with an unusual extension
- JavaSetup8u201[1].exe (PID: 3272)
Creates files in the program directory
- bspatch.exe (PID: 3796)
- unpack200.exe (PID: 916)
- unpack200.exe (PID: 2740)
- unpack200.exe (PID: 3236)
- unpack200.exe (PID: 2924)
- unpack200.exe (PID: 2124)
- unpack200.exe (PID: 1580)
- unpack200.exe (PID: 2600)
- javaw.exe (PID: 2252)
- installer.exe (PID: 3964)
Modifies the open verb of a shell class
- installer.exe (PID: 3964)
Creates files in the Windows directory
- installer.exe (PID: 3964)
Removes files from Windows directory
- installer.exe (PID: 3964)
Check for Java to be installed
- installer.exe (PID: 3964)
Creates files in the user directory
- jp2launcher.exe (PID: 2060)
Creates COM task schedule object
- ssvagent.exe (PID: 1012)
- installer.exe (PID: 3964)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1920)
Creates files in the user directory
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 928)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2328)
Reads Internet Cache Settings
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 928)
- iexplore.exe (PID: 1920)
Reads internet explorer settings
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 928)
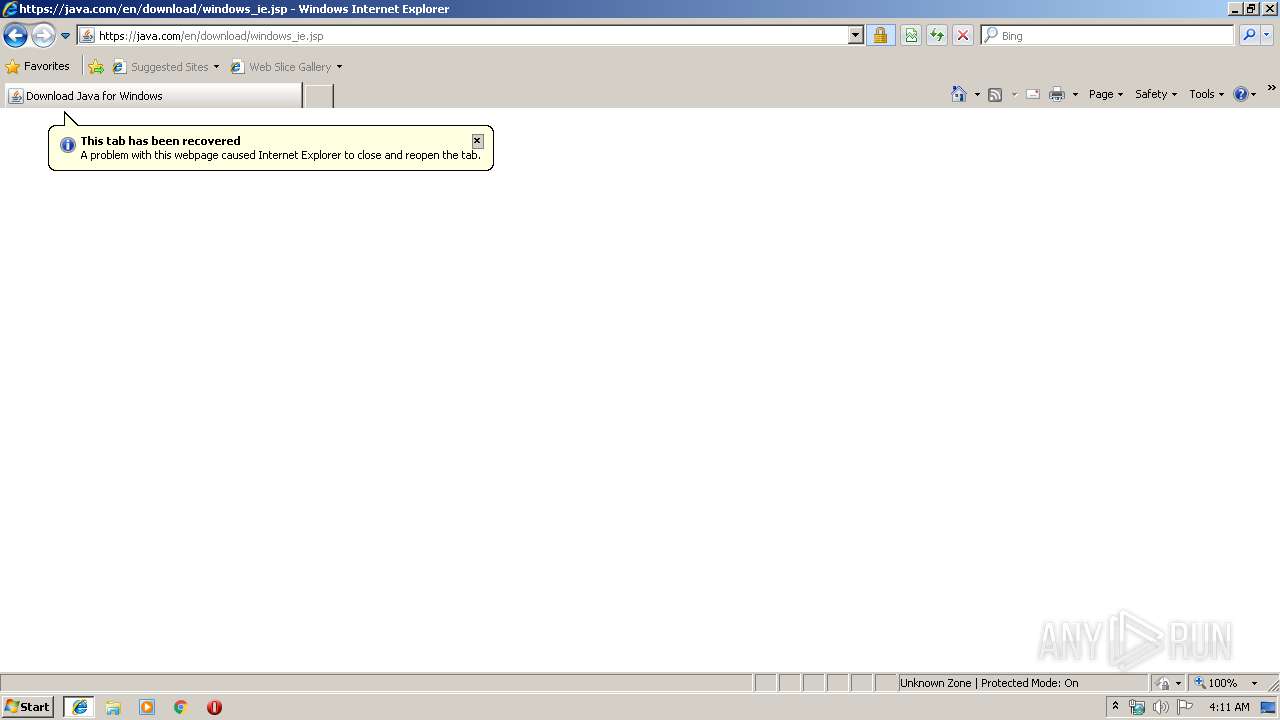
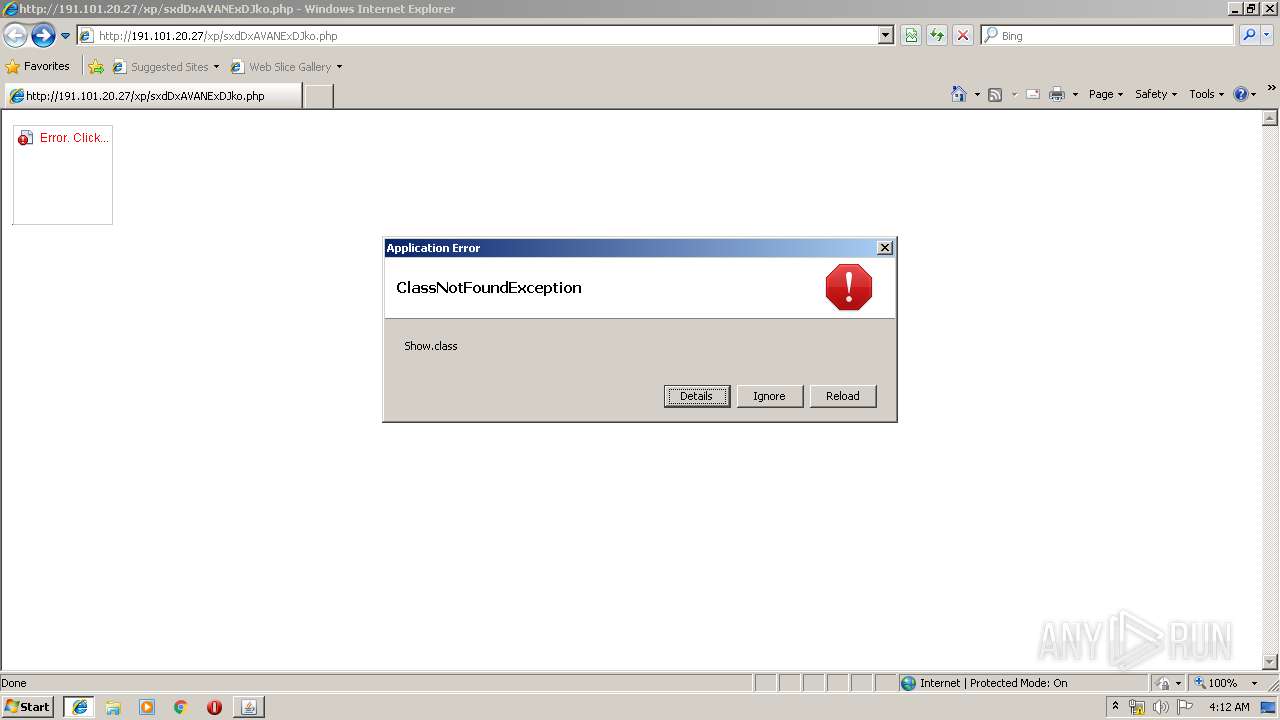
Application was crashed
- iexplore.exe (PID: 2572)
Changes settings of System certificates
- iexplore.exe (PID: 1920)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1920)
Reads settings of System Certificates
- iexplore.exe (PID: 1920)
Application launched itself
- iexplore.exe (PID: 1920)
- msiexec.exe (PID: 3528)
- AcroRd32.exe (PID: 2372)
- AcroRd32.exe (PID: 2516)
Creates a software uninstall entry
- msiexec.exe (PID: 3528)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2604)
Creates files in the program directory
- msiexec.exe (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
43
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.92.2" "update" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 292 | "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_201\LZMA_EXE" d "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_201\jre1.8.0_201patch.msi" "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_201\msi.tmp" | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_201\LZMA_EXE | — | JavaSetup8u201[1].exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 928 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Java\jre1.8.0_201\bin\unpack200.exe" -r "C:\Program Files\Java\jre1.8.0_201\lib/plugin.pack" "C:\Program Files\Java\jre1.8.0_201\lib/plugin.jar" | C:\Program Files\Java\jre1.8.0_201\bin\unpack200.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2010.9 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1920 CREDAT:71940 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Java\jre1.8.0_201\bin\ssvagent.exe" -doHKCUSSVSetup | C:\Program Files\Java\jre1.8.0_201\bin\ssvagent.exe | — | installer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 11.201.2.09 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.92.2" "1553227968" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer /o /eo /l /b /id 928 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" /o /eo /l /b /id 928 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1476 | C:\Windows\system32\WerFault.exe -u -p 2572 -s 3316 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
34 941
Read events
1 916
Write events
24 394
Delete events
8 631
Modification events
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {847DD889-4C58-11E9-A302-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (1920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30703000500160004000B0008007D03 | |||
Executable files
159
Suspicious files
23
Text files
419
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
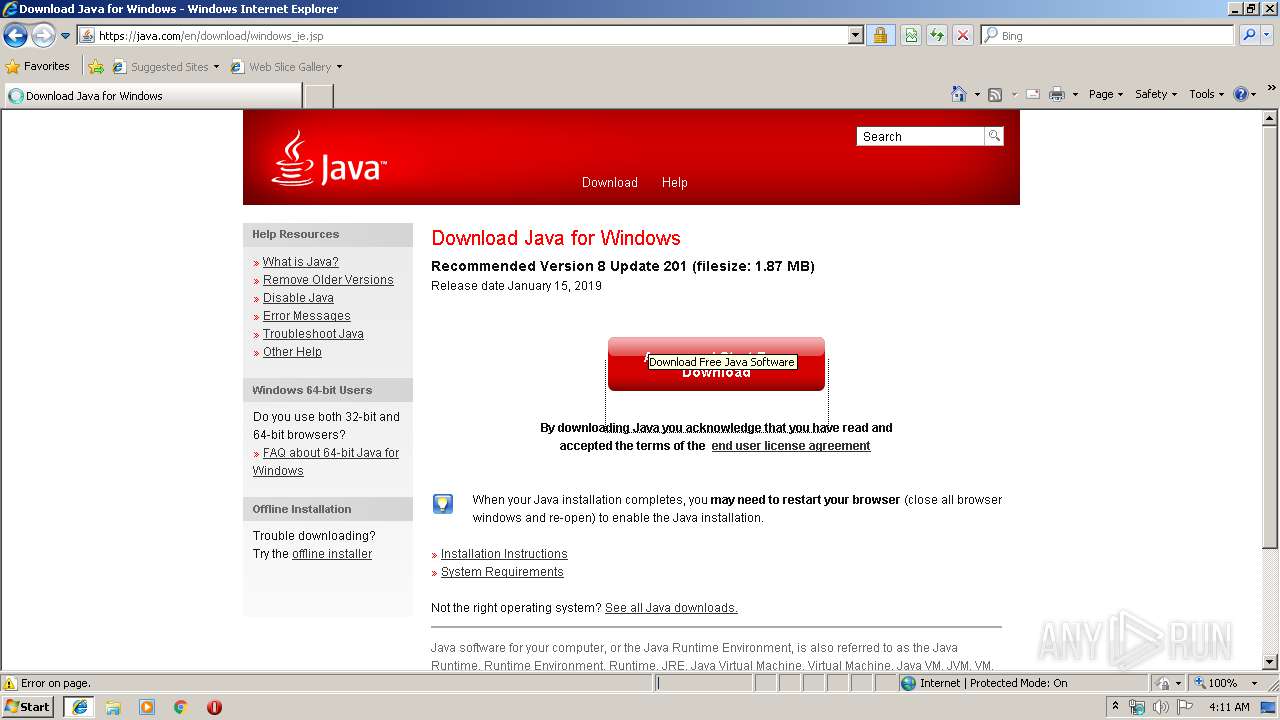
| 2572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\LS5S2NMY\windows_ie[1].jsp | — | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019032220190323\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019032220190323\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\LS5S2NMY\windows_ie[1].htm | html | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@java[1].txt | text | |
MD5:— | SHA256:— | |||
| 2572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\IW3LJ1QR\global[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
66
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2572 | iexplore.exe | GET | 301 | 184.31.91.194:80 | http://java.com/inst-dl-redirect/ | NL | — | — | whitelisted |
2572 | iexplore.exe | GET | 301 | 184.31.91.194:80 | http://java.com/inst-dl-redirect | NL | — | — | whitelisted |
2572 | iexplore.exe | GET | 200 | 191.101.20.27:80 | http://191.101.20.27/xp/sxdDxAVANExDJko.php | NL | html | 8.16 Kb | suspicious |
928 | iexplore.exe | GET | 200 | 191.101.20.27:80 | http://191.101.20.27/xp/sxdDxAVANExDJko.php | NL | html | 8.16 Kb | suspicious |
1920 | iexplore.exe | GET | 404 | 191.101.20.27:80 | http://191.101.20.27/favicon.ico | NL | html | 329 b | suspicious |
928 | iexplore.exe | GET | 200 | 191.101.20.27:80 | http://191.101.20.27/xp/sxdDxAVANExDJko.php | NL | html | 8.16 Kb | suspicious |
2060 | jp2launcher.exe | GET | 404 | 191.101.20.27:80 | http://191.101.20.27/xp/Show.class | NL | html | 331 b | suspicious |
2060 | jp2launcher.exe | GET | 404 | 191.101.20.27:80 | http://191.101.20.27/xp/Show/class.class | NL | html | 337 b | suspicious |
1920 | iexplore.exe | GET | 404 | 191.101.20.27:80 | http://191.101.20.27/favicon.ico | NL | html | 329 b | suspicious |
2060 | jp2launcher.exe | GET | 404 | 191.101.20.27:80 | http://191.101.20.27/xp/Show.class | NL | html | 331 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2572 | iexplore.exe | 23.45.74.86:443 | c.go-mpulse.net | Akamai Technologies, Inc. | NL | whitelisted |
2572 | iexplore.exe | 191.101.20.27:80 | — | Swiftway Sp. z o.o. | NL | suspicious |
1920 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1920 | iexplore.exe | 191.101.20.27:80 | — | Swiftway Sp. z o.o. | NL | suspicious |
2572 | iexplore.exe | 184.31.91.194:80 | java.com | Akamai International B.V. | NL | whitelisted |
2572 | iexplore.exe | 184.31.91.194:443 | java.com | Akamai International B.V. | NL | whitelisted |
2572 | iexplore.exe | 2.16.186.58:443 | dyn-beacon.akamaized.net | Akamai International B.V. | — | whitelisted |
2572 | iexplore.exe | 54.72.243.109:443 | consent.trustarc.com | Amazon.com, Inc. | IE | unknown |
— | — | 54.72.243.109:443 | consent.trustarc.com | Amazon.com, Inc. | IE | unknown |
2572 | iexplore.exe | 2.18.232.194:443 | sdlc-esd.oracle.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
java.com |
| whitelisted |
consent.trustarc.com |
| shared |
dyn-beacon.akamaized.net |
| whitelisted |
s.go-mpulse.net |
| whitelisted |
oracle.112.2o7.net |
| whitelisted |
c.go-mpulse.net |
| whitelisted |
364bf6cc.akstat.io |
| whitelisted |
javadl.oracle.com |
| whitelisted |
sdlc-esd.oracle.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2060 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
2060 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |