| File name: | vcredist_x86.exe |
| Full analysis: | https://app.any.run/tasks/ba706eea-b395-4f1a-9ae9-a8bba7250f71 |
| Verdict: | No threats detected |
| Analysis date: | June 09, 2019, 13:38:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0FC525B6B7B96A87523DAA7A0013C69D |
| SHA1: | DF7F0A73BFA077E483E51BFB97F5E2ECEEDFB6A3 |
| SHA256: | A22895E55B26202EAE166838EDBE2EA6AAD00D7EA600C11F8A31EDE5CBCE2048 |
| SSDEEP: | 98304:hQEKzHx15bWUuBrNatjJh2eNUrzKRL/RaIswn7aBOC5qZxVqFb2iExMc7FvxwGvf:WRDnuBotjJh2emr8L/YIsG7MOgqHG64 |
MALICIOUS
Loads dropped or rewritten executable
- vcredist_x86.exe (PID: 3192)
SUSPICIOUS
Executable content was dropped or overwritten
- vcredist_x86.exe (PID: 3192)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:04:29 20:27:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 232448 |
| InitializedDataSize: | 142336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27e1e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.0.30501.0 |
| ProductVersionNumber: | 12.0.30501.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
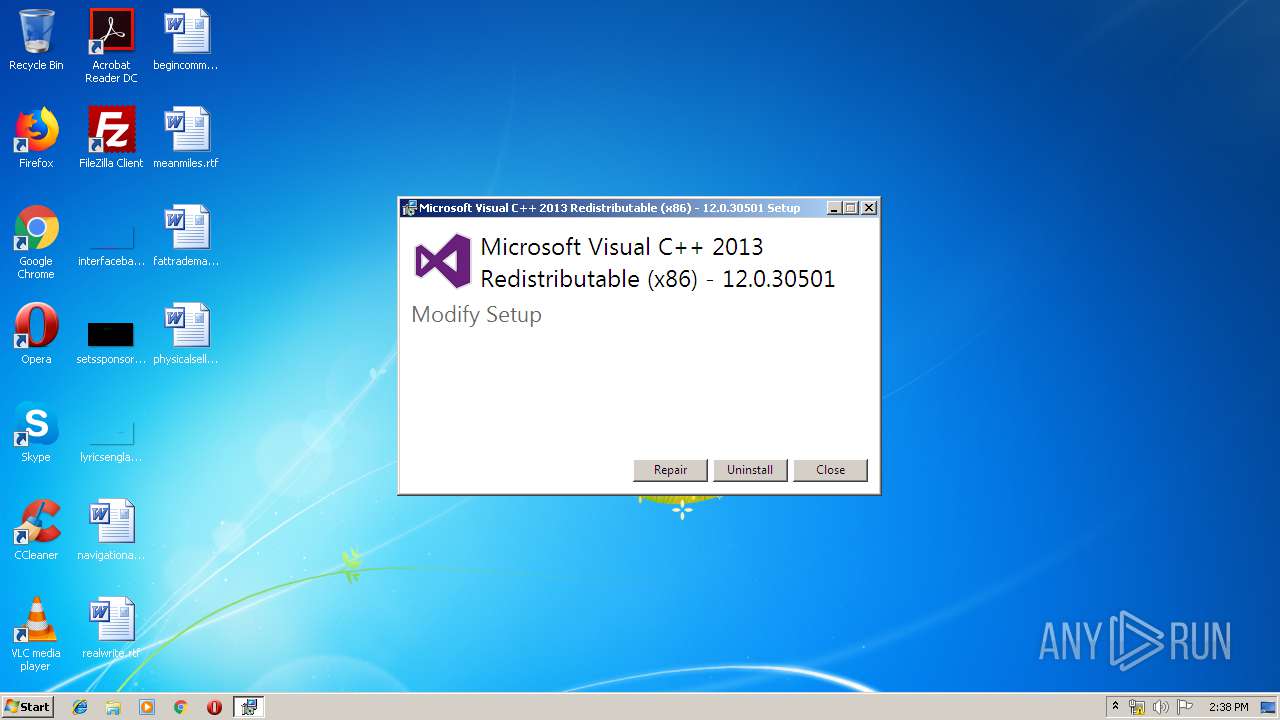
| FileDescription: | Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 |
| FileVersion: | 12.0.30501.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | vcredist_x86.exe |
| ProductName: | Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 |
| ProductVersion: | 12.0.30501.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Apr-2014 18:27:40 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 |
| FileVersion: | 12.0.30501.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | vcredist_x86.exe |
| ProductName: | Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 |
| ProductVersion: | 12.0.30501.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 29-Apr-2014 18:27:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00038B74 | 0x00038C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50549 |
.rdata | 0x0003A000 | 0x00019AAE | 0x00019C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.96457 |
.data | 0x00054000 | 0x00003020 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.6738 |
.wixburn8 | 0x00058000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.735162 |
.tls | 0x00059000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0005A000 | 0x000037E4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.43729 |
.reloc | 0x0005E000 | 0x000042FA | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.69662 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2207 | 1032 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
Total processes
31
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3192 | "C:\Users\admin\AppData\Local\Temp\vcredist_x86.exe" | C:\Users\admin\AppData\Local\Temp\vcredist_x86.exe | explorer.exe | ||||||||||||
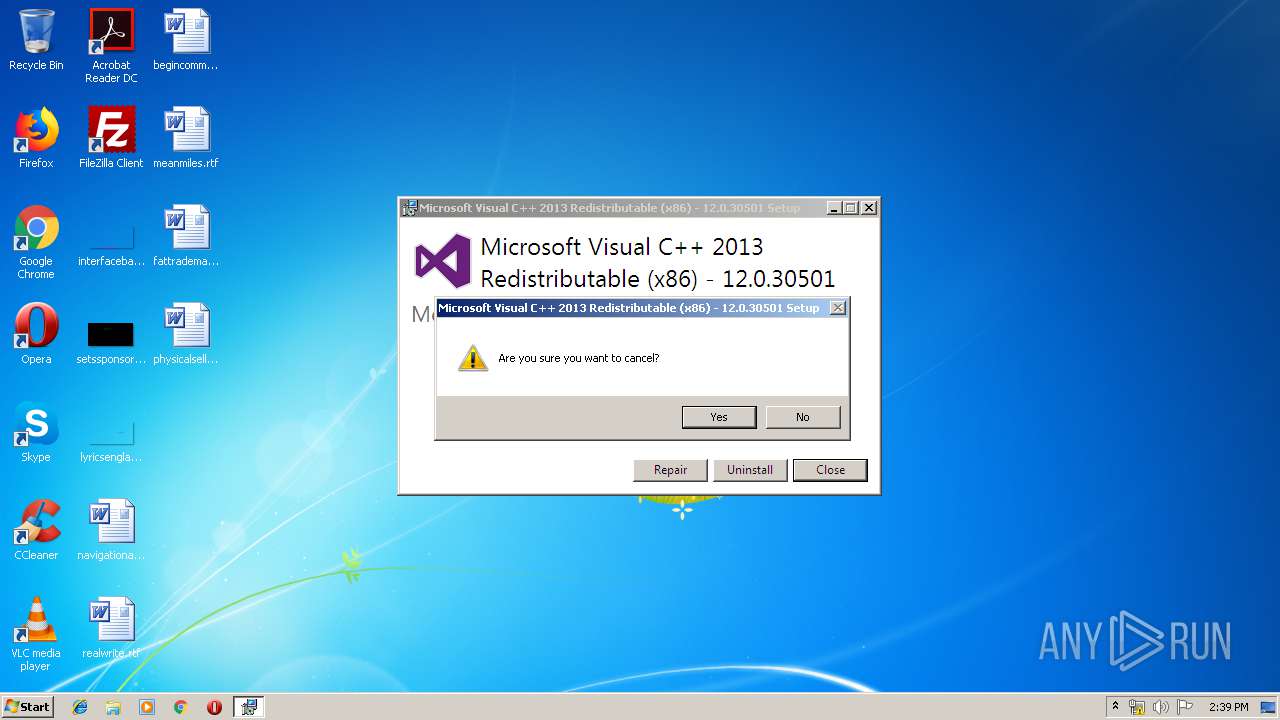
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2013 Redistributable (x86) - 12.0.30501 Exit code: 1602 Version: 12.0.30501.0 Modules
| |||||||||||||||
Total events
43
Read events
43
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3192 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\dd_vcredist_x86_20190609143853.log | text | |
MD5:— | SHA256:— | |||
| 3192 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\{f65db027-aff3-4070-886a-0d87064aabb1}\.ba1\license.rtf | text | |
MD5:1E47EE7B71B22488068343DF4CE30534 | SHA256:8518F0420972C1DBE8A323FFC6F57863AF0B80C6A3B27FD0C6FC9BDABB7E2D13 | |||
| 3192 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\{f65db027-aff3-4070-886a-0d87064aabb1}\.ba1\wixstdba.dll | executable | |
MD5:A52E5220EFB60813B31A82D101A97DCB | SHA256:E7C8E7EDD9112137895820E789BAAAECA41626B01FB99FEDE82968DDB66D02CF | |||
| 3192 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\{f65db027-aff3-4070-886a-0d87064aabb1}\.ba1\BootstrapperApplicationData.xml | xml | |
MD5:4E9AD8FEE683402B9FB3381549B7F98B | SHA256:148F262B214F5E472BA32DB9824342BBDA91D6F4C751A2DA0BBC2B70E2794BD2 | |||
| 3192 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\{f65db027-aff3-4070-886a-0d87064aabb1}\.ba1\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
| 3192 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\{f65db027-aff3-4070-886a-0d87064aabb1}\.ba1\thm.xml | xml | |
MD5:0056F10A42638EA8B4BEFC614741DDD6 | SHA256:6B1BA0DEA830E556A58C883290FAA5D49C064E546CBFCD0451596A10CC693F87 | |||
| 3192 | vcredist_x86.exe | C:\Users\admin\AppData\Local\Temp\{f65db027-aff3-4070-886a-0d87064aabb1}\.ba1\logo.png | image | |
MD5:D6BD210F227442B3362493D046CEA233 | SHA256:335A256D4779EC5DCF283D007FB56FD8211BBCAF47DCD70FE60DED6A112744EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report