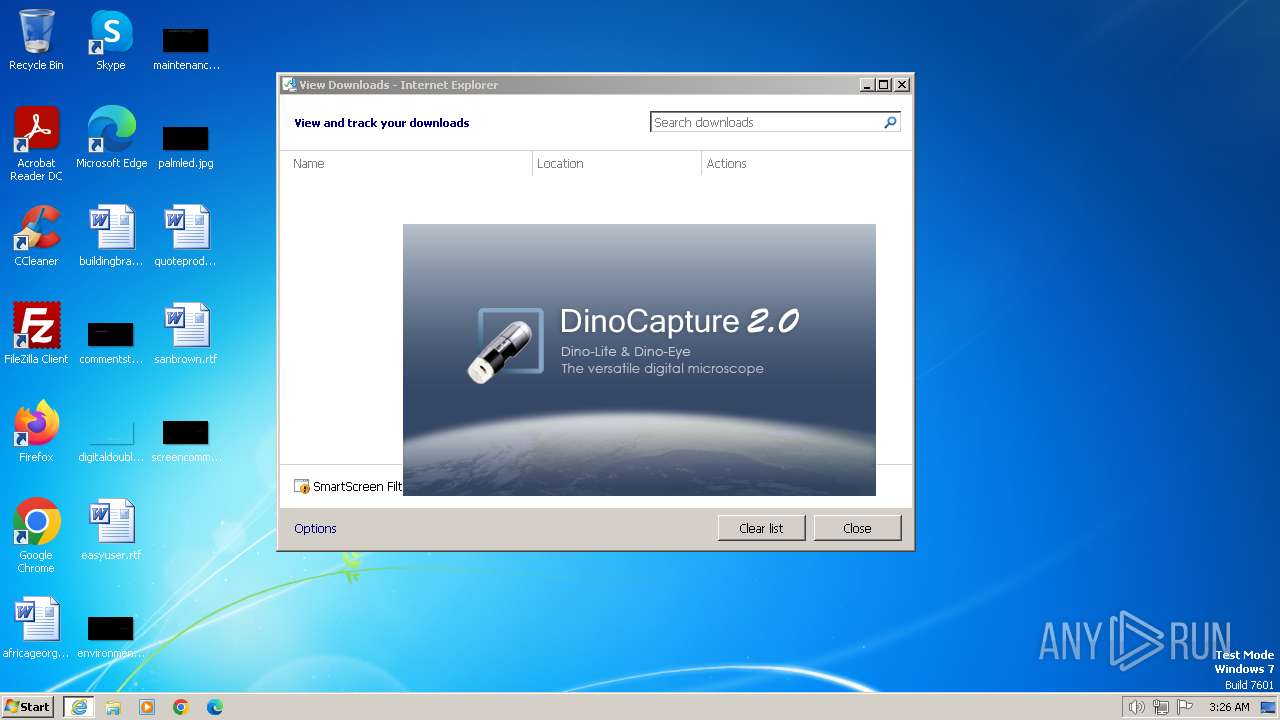
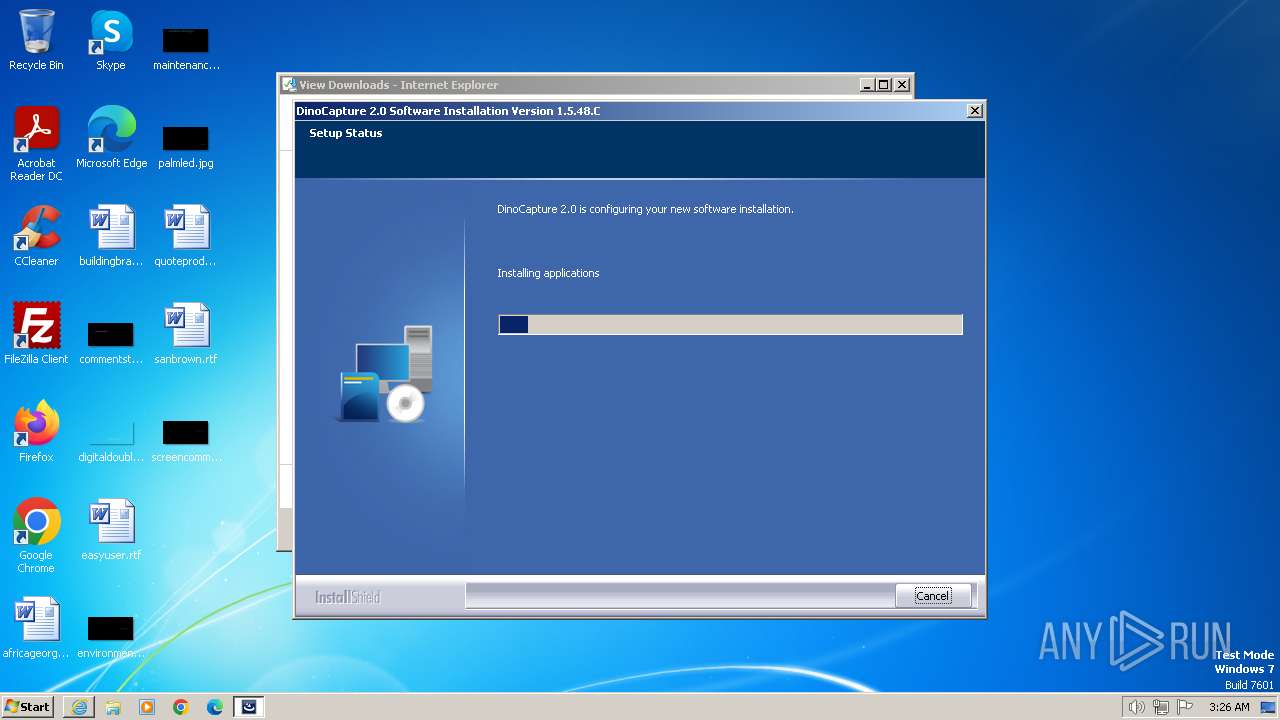
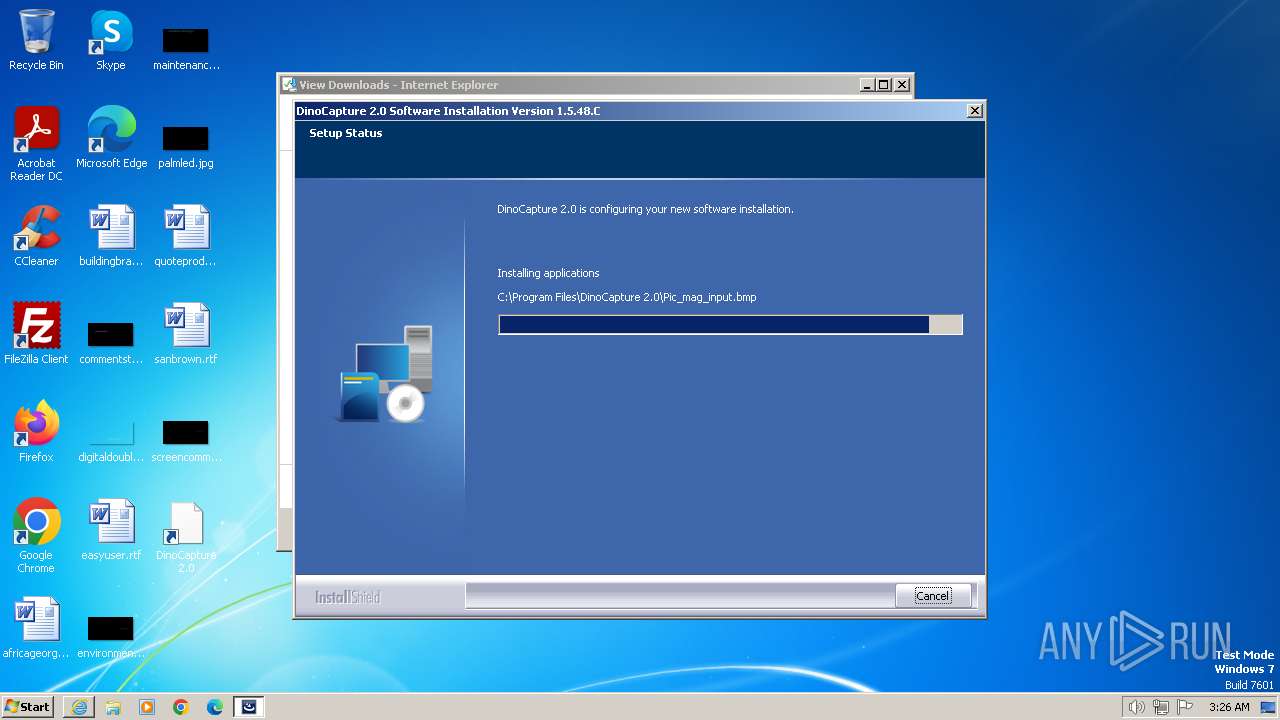
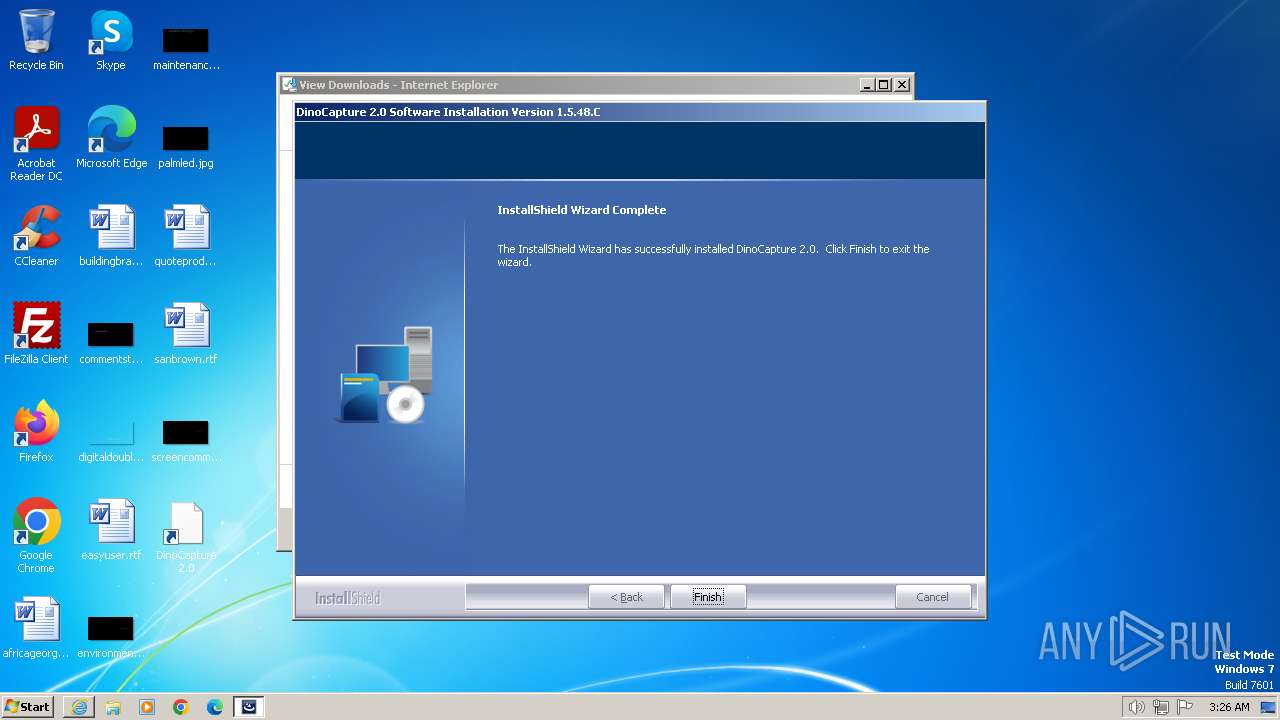
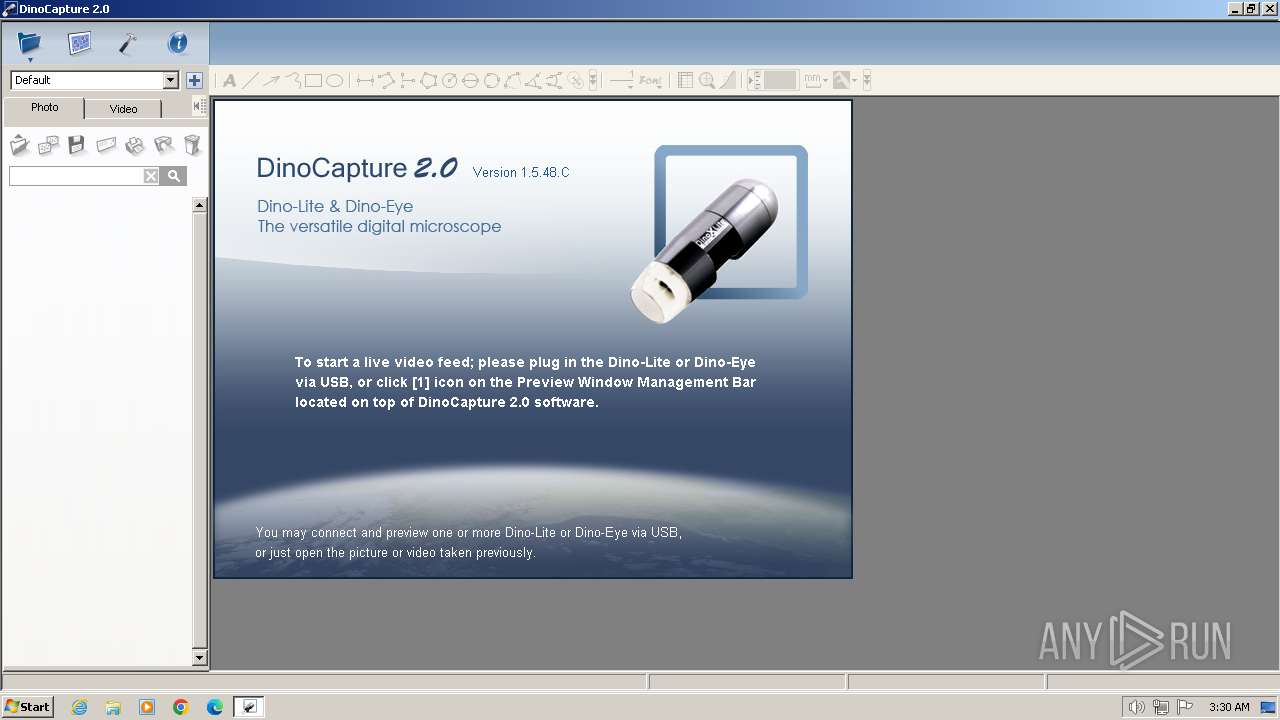
| URL: | https://files.dinolite.us/downloads/software/dnc2/latest/dinocapture2.exe |
| Full analysis: | https://app.any.run/tasks/93e27c34-d9b8-4c72-aa8e-ab587bfba501 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 03:25:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6960AD7CA8402285F70CAFB409DDE6F4 |
| SHA1: | 888D037C396FFF6765752999BDF9E204C36B2D9D |
| SHA256: | A226C82E2B2EA5CE6B414F7FCC2781ADFF75871C6699E562D10C41F7B6E25FC3 |
| SSDEEP: | 3:N8MgKJVLQL6KNA7GWFrYN:2MbL8iKuM |
MALICIOUS
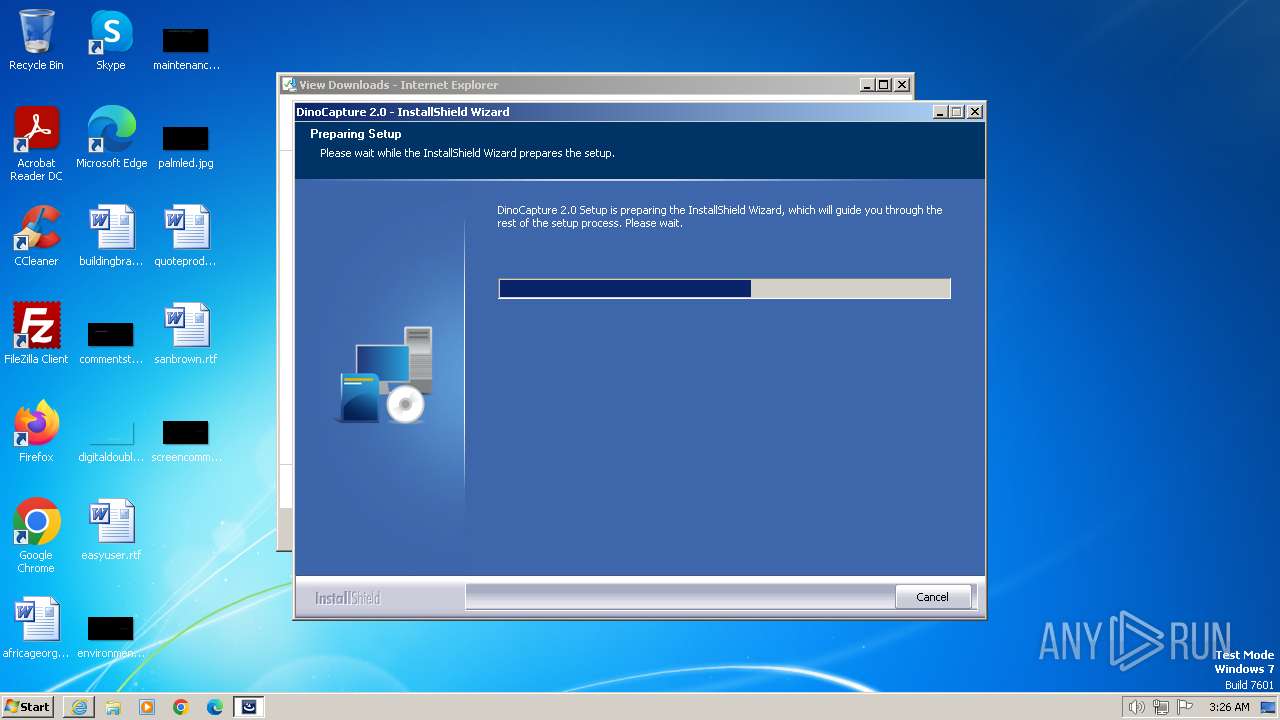
Drops the executable file immediately after the start
- dinocapture2.exe (PID: 956)
- Edge3Driver.tmp (PID: 1368)
- setup.exe (PID: 2792)
- Edge3Driver.exe (PID: 2100)
Creates a writable file in the system directory
- setup.exe (PID: 2792)
- Edge3Driver.tmp (PID: 1368)
SUSPICIOUS
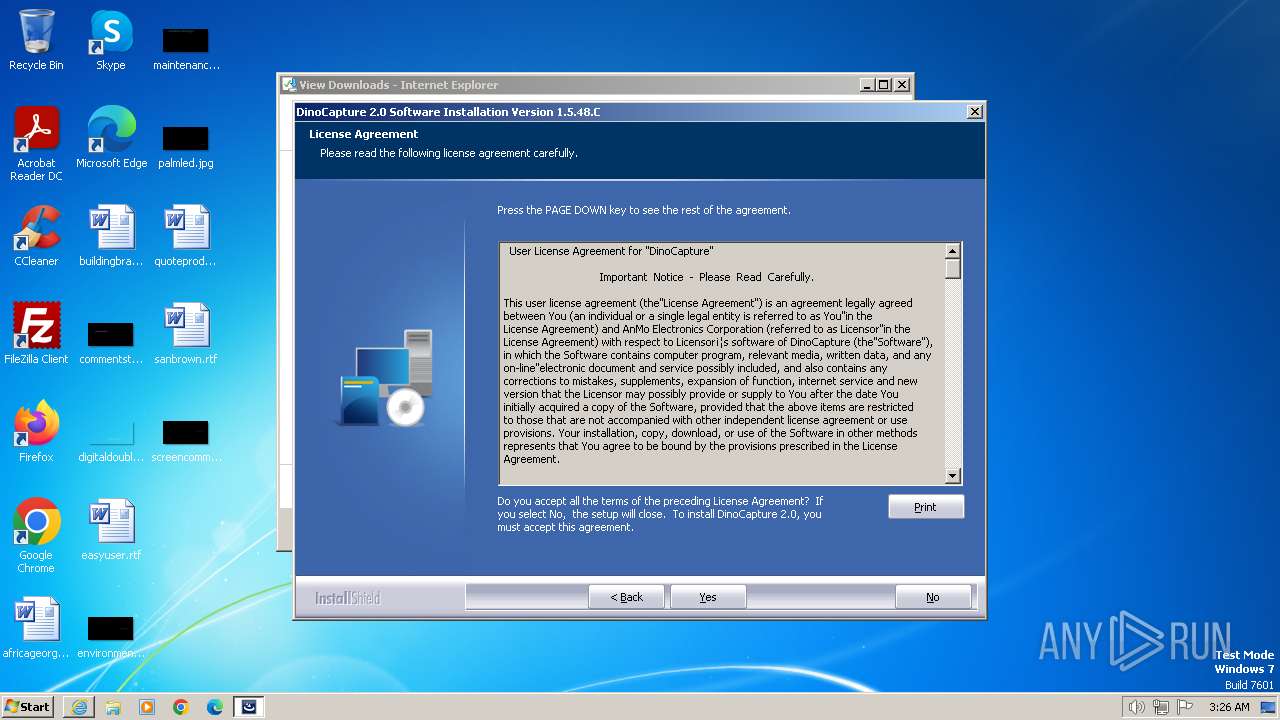
Searches for installed software
- setup.exe (PID: 2792)
- dinocapture2.exe (PID: 956)
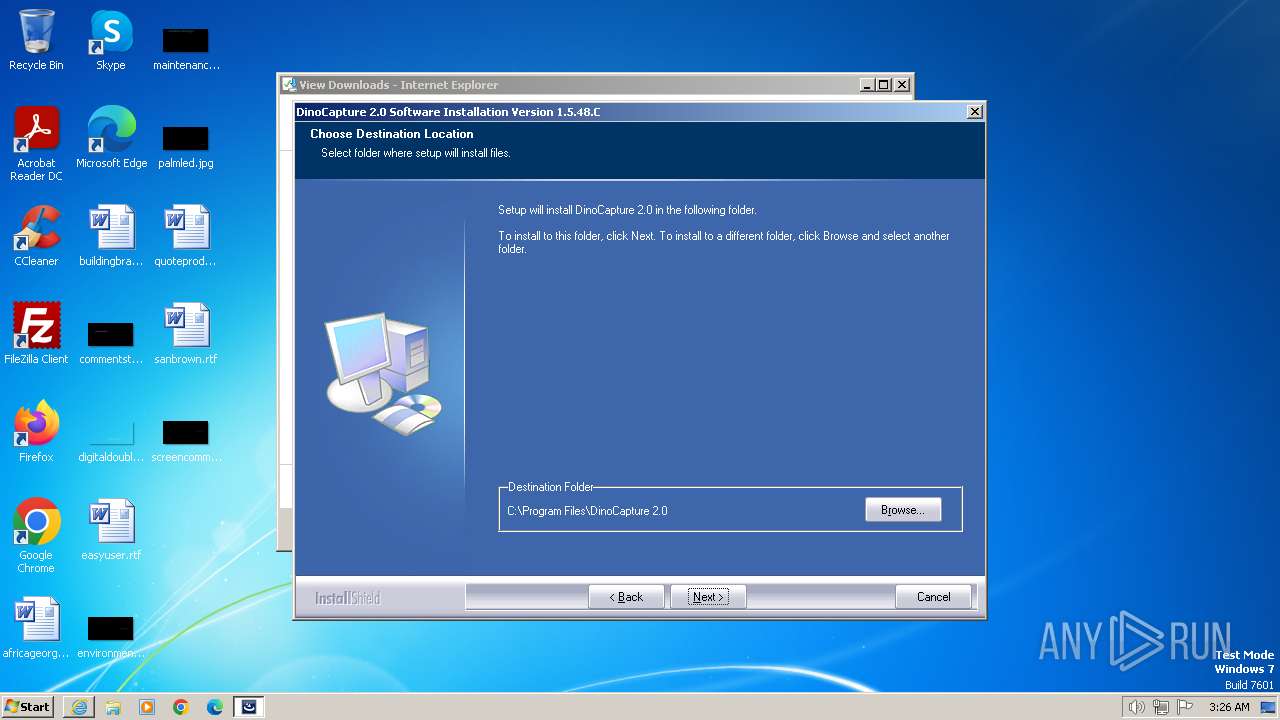
Creates a software uninstall entry
- setup.exe (PID: 2792)
The process drops C-runtime libraries
- setup.exe (PID: 2792)
Creates/Modifies COM task schedule object
- setup.exe (PID: 2792)
Executable content was dropped or overwritten
- dinocapture2.exe (PID: 956)
- setup.exe (PID: 2792)
- Edge3Driver.tmp (PID: 1368)
- Edge3Driver.exe (PID: 2100)
Process drops legitimate windows executable
- setup.exe (PID: 2792)
Reads the Windows owner or organization settings
- setup.exe (PID: 2792)
- Edge3Driver.tmp (PID: 1368)
Drops a system driver (possible attempt to evade defenses)
- Edge3Driver.tmp (PID: 1368)
Creates files in the driver directory
- Edge3Driver.tmp (PID: 1368)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 584)
- cmd.exe (PID: 3352)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 1424)
- cmd.exe (PID: 3316)
- cmd.exe (PID: 2028)
- cmd.exe (PID: 2740)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 3492)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 668)
- cmd.exe (PID: 1932)
- cmd.exe (PID: 884)
- cmd.exe (PID: 1604)
- cmd.exe (PID: 292)
- cmd.exe (PID: 3412)
Starts CMD.EXE for commands execution
- DinoCapture.exe (PID: 3256)
INFO
Drops the executable file immediately after the start
- iexplore.exe (PID: 3664)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3664)
Reads the computer name
- dinocapture2.exe (PID: 956)
- setup.exe (PID: 2792)
- install-filter.exe (PID: 1336)
- Edge3Driver.tmp (PID: 1368)
- install-filter.exe (PID: 2320)
- systeminfo.exe (PID: 3372)
- DinoCapture.exe (PID: 3256)
Application launched itself
- iexplore.exe (PID: 2160)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2160)
Create files in a temporary directory
- dinocapture2.exe (PID: 956)
- setup.exe (PID: 2792)
- Edge3Driver.exe (PID: 2100)
- DinoCapture.exe (PID: 3256)
The process uses the downloaded file
- iexplore.exe (PID: 2160)
Creates files in the program directory
- setup.exe (PID: 2792)
- Edge3Driver.tmp (PID: 1368)
- DinoCapture.exe (PID: 3256)
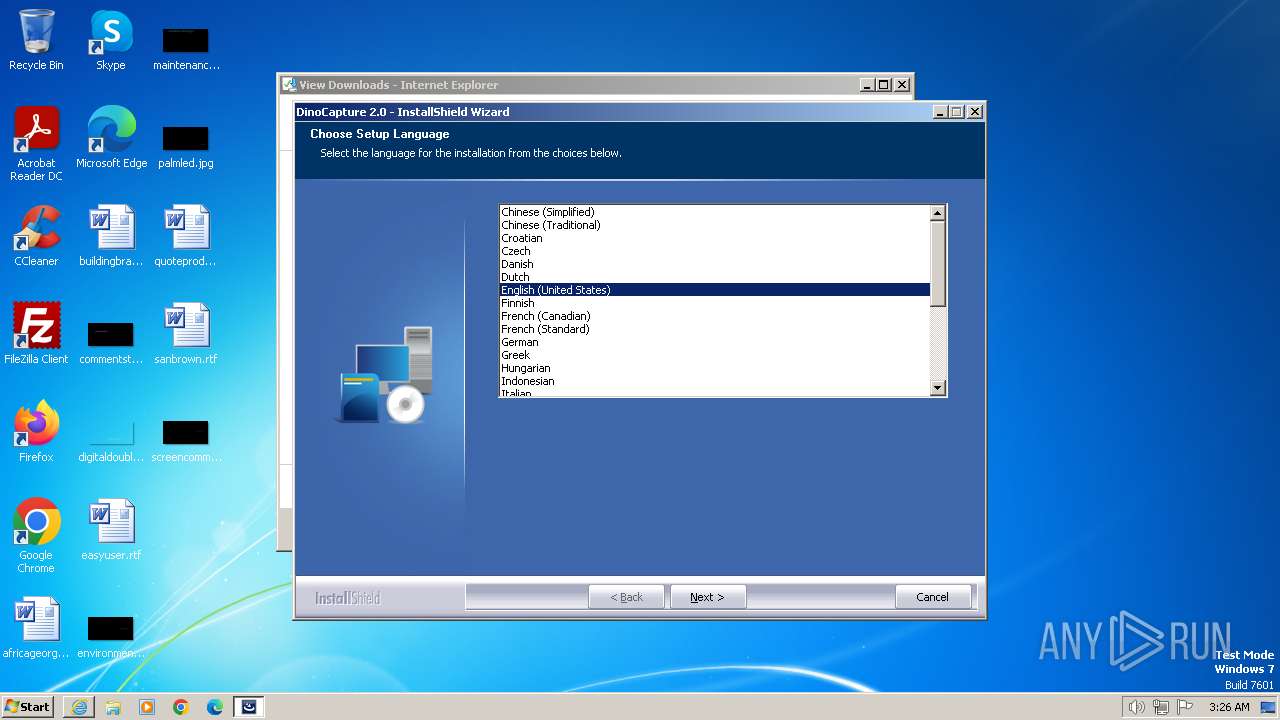
Checks supported languages
- dinocapture2.exe (PID: 956)
- setup.exe (PID: 2792)
- install-filter.exe (PID: 1336)
- install-filter.exe (PID: 2320)
- Edge3Driver.exe (PID: 2100)
- Edge3Driver.tmp (PID: 1368)
- DinoCapture.exe (PID: 3256)
- systeminfo.exe (PID: 3372)
Reads the machine GUID from the registry
- setup.exe (PID: 2792)
- systeminfo.exe (PID: 3372)
Creates a software uninstall entry
- Edge3Driver.tmp (PID: 1368)
Manual execution by a user
- DinoCapture.exe (PID: 3256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
117
Monitored processes
47
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | REG ADD "HKLM\SOFTWARE\DinoCapture 2.0" /v p3index /t REG_SZ /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | cmd.exe /c REG ADD "HKLM\SOFTWARE\DinoCapture 2.0" /v p3index /t REG_SZ /d 0 /f | C:\Windows\System32\cmd.exe | — | DinoCapture.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 560 | REG ADD "HKLM\SOFTWARE\DinoCapture 2.0" /v p1x /t REG_SZ /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | cmd.exe /c REG ADD "HKLM\SOFTWARE\DinoCapture 2.0" /v p0x /t REG_SZ /d 0 /f | C:\Windows\System32\cmd.exe | — | DinoCapture.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 604 | REG ADD "HKLM\SOFTWARE\DinoCapture 2.0" /v p3x /t REG_SZ /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | cmd.exe /c REG ADD "HKLM\SOFTWARE\DinoCapture 2.0" /v p2x /t REG_SZ /d 0 /f | C:\Windows\System32\cmd.exe | — | DinoCapture.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 884 | cmd.exe /c REG ADD "HKLM\SOFTWARE\DinoCapture 2.0" /v p3c /t REG_SZ /d "?A" /f | C:\Windows\System32\cmd.exe | — | DinoCapture.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\dinocapture2.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\dinocapture2.exe | iexplore.exe | ||||||||||||
User: admin Company: AnMo Electronics Corporation Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Exit code: 0 Version: 1.5.48.C Modules
| |||||||||||||||
| 1072 | cmd.exe /c REG ADD "HKLM\SOFTWARE\DinoCapture 2.0" /v p2c /t REG_SZ /d "?A" /f | C:\Windows\System32\cmd.exe | — | DinoCapture.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1336 | "C:\Program Files\DinoCapture 2.0\install-filter.exe" install --device=USB\VID_A168&PID_09B0&MI_00 | C:\Program Files\DinoCapture 2.0\install-filter.exe | — | Edge3Driver.tmp | |||||||||||
User: admin Company: http://libusb-win32.sourceforge.net Integrity Level: HIGH Description: libusb-win32 - Install-Filter Exit code: 0 Version: 1.2.6.0 Modules
| |||||||||||||||
Total events
27 444
Read events
27 225
Write events
165
Delete events
54
Modification events
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31088172 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31088172 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
198
Suspicious files
58
Text files
222
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\dinocapture2.exe.ygwddy5.partial | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\dinocapture2.exe | — | |
MD5:— | SHA256:— | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9F0.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:131436685CE873FC2C469779B6496BDC | SHA256:63F022583E3A65E7999FCC19984871CA9061A0303F07EEDF9D72D6D67910059E | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 956 | dinocapture2.exe | C:\Users\admin\AppData\Local\Temp\{919F9AAE-6BC7-4428-9BD2-85CF49ED041A}\Disk1\0x0404.ini | text | |
MD5:D2375044346BA50DD1E3F1208185FD0E | SHA256:CDDB0BBF712C57ACC6B8AD2D20514B25331A93FD1B95C1A2155C2F670A5C5CEA | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:B493FE38CA6D1CA069521E1270654727 | SHA256:42A99D14B0FB7557EF7B145740AFC1078C82CB8CC0EAA330F1C20475143E6269 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
21
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3664 | iexplore.exe | GET | 304 | 80.239.138.112:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | unknown | — | — | unknown |
2160 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
2160 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
3664 | iexplore.exe | GET | 304 | 80.239.138.112:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bd117e088266f0f9 | unknown | — | — | unknown |
3664 | iexplore.exe | GET | 200 | 80.239.138.112:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a08f35fbea17b647 | unknown | compressed | 65.2 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 80.239.138.112:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b150b552b216e1f4 | unknown | compressed | 65.2 Kb | unknown |
3664 | iexplore.exe | GET | 200 | 2.22.41.69:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2160 | iexplore.exe | GET | 304 | 80.239.138.112:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?76ad697231f9b13b | unknown | — | — | unknown |
2160 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
2160 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3664 | iexplore.exe | 165.232.158.154:443 | files.dinolite.us | DIGITALOCEAN-ASN | US | unknown |
3664 | iexplore.exe | 80.239.138.112:80 | ctldl.windowsupdate.com | Telia Company AB | DE | unknown |
3664 | iexplore.exe | 2.22.41.69:80 | x1.c.lencr.org | Telia Company AB | SE | unknown |
2160 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2160 | iexplore.exe | 80.239.138.112:80 | ctldl.windowsupdate.com | Telia Company AB | DE | unknown |
2160 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2160 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
files.dinolite.us |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |