| File name: | 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos |
| Full analysis: | https://app.any.run/tasks/4889e20d-22cb-4712-ad01-5ed903b16e3f |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 11:29:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 2D38073A40EEF1369F1D8CB7BD4EFBCF |
| SHA1: | 55160E2BB9A0A3C546F1A3A2A7F0453E80B5AE20 |
| SHA256: | A222448CF6AF5437A4E0BA52C7987F7D63B10669B177D9AD08E8DC675F10C870 |
| SSDEEP: | 98304:zSYpVEQ4lksFIANxrg/rE4WNQ2YvS+cKH44SZqGXIzHCmKIcik8QTBrqPS4cAfAd:VGmA4nU |
MALICIOUS
CANBIS mutex has been found
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
SUSPICIOUS
Reads security settings of Internet Explorer
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
Executable content was dropped or overwritten
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
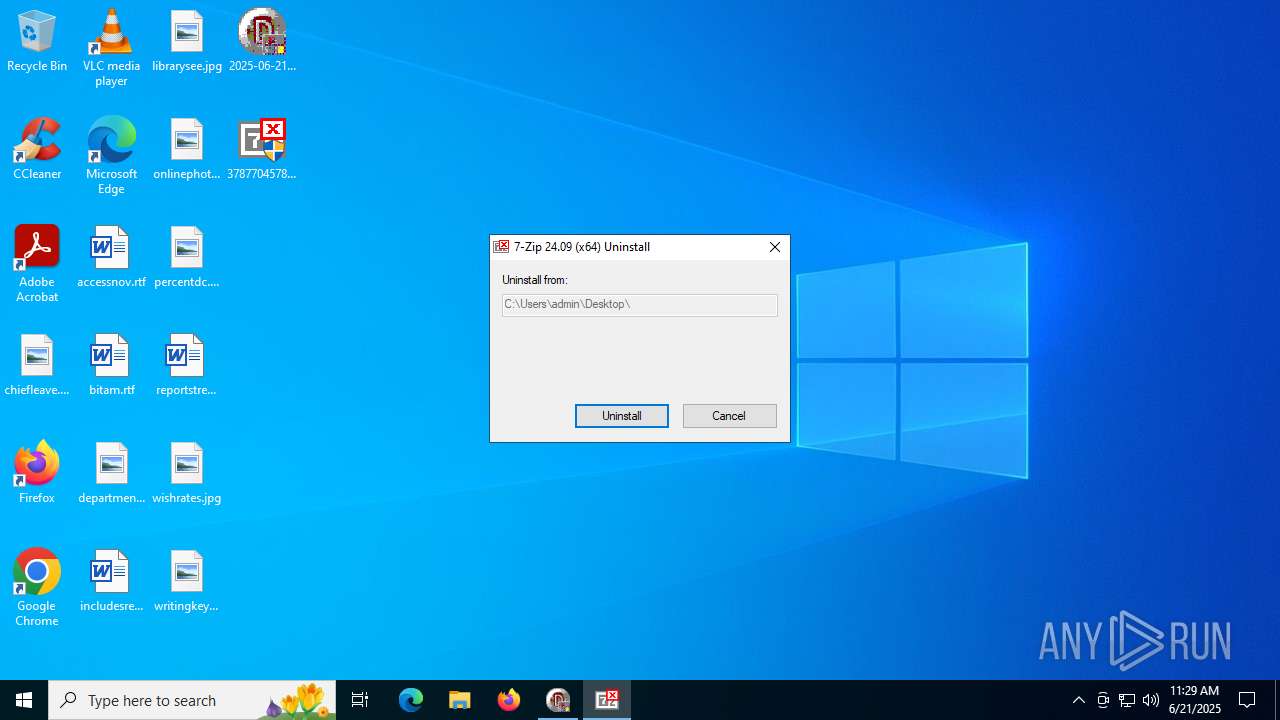
Drops 7-zip archiver for unpacking
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
There is functionality for communication over UDP network (YARA)
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
INFO
Checks supported languages
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
- 3787704578.exe (PID: 5116)
Reads the computer name
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
- 3787704578.exe (PID: 5116)
The sample compiled with english language support
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
Process checks computer location settings
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
Failed to create an executable file in Windows directory
- 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe (PID: 1720)
Checks proxy server information
- slui.exe (PID: 1800)
Reads the software policy settings
- slui.exe (PID: 1800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (57.2) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (38.8) |
| .exe | | | Win32 Executable Delphi generic (1.2) |
| .scr | | | Windows screen saver (1.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 46080 |
| InitializedDataSize: | 7680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc254 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
138
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1720 | "C:\Users\admin\Desktop\2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe" | C:\Users\admin\Desktop\2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1800 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\Desktop\3787704578.exe" | C:\Users\admin\Desktop\3787704578.exe | — | 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Uninstaller Exit code: 3221226540 Version: 24.09 Modules
| |||||||||||||||
| 5116 | "C:\Users\admin\Desktop\3787704578.exe" | C:\Users\admin\Desktop\3787704578.exe | 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Uninstaller Version: 24.09 Modules
| |||||||||||||||
Total events
4 096
Read events
4 096
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1720 | 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe | C:\Users\admin\Desktop\3787704578.exe | executable | |
MD5:E03115EE7530777231A0051667AB23D3 | SHA256:CCCF6F489961BB78C5C4BAECD964442B14593799403E2B6E4D50082C3E64803A | |||
| 1720 | 2025-06-21_2d38073a40eef1369f1d8cb7bd4efbcf_akira_black-basta_elex_gcleaner_hijackloader_luca-stealer_remcos.exe | C:\Users\admin\Desktop\7679611053.exe | executable | |
MD5:2D38073A40EEF1369F1D8CB7BD4EFBCF | SHA256:A222448CF6AF5437A4E0BA52C7987F7D63B10669B177D9AD08E8DC675F10C870 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
42
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6732 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6732 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 304 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
6292 | SIHClient.exe | GET | 200 | 184.25.50.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6732 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6732 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
uk.undernet.org |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |