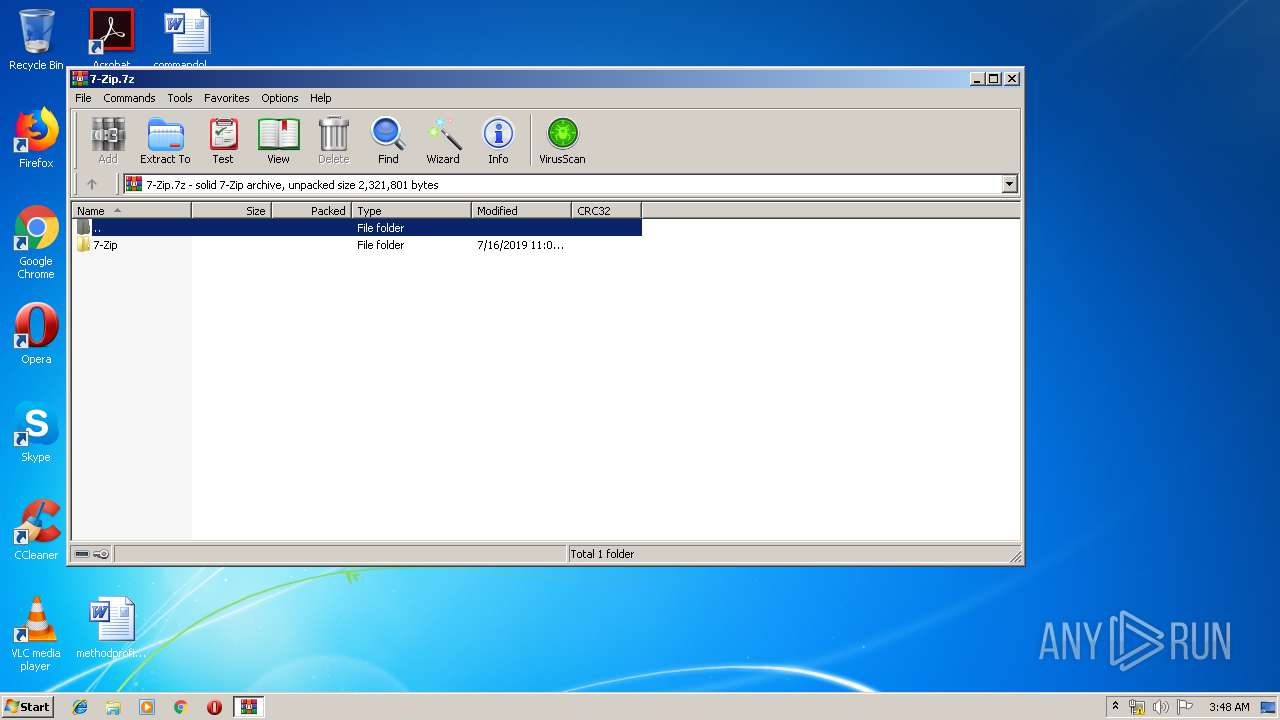
| File name: | 7-Zip.7z |
| Full analysis: | https://app.any.run/tasks/8824ff3d-2663-4c57-a811-41c1d3cb3bb6 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 02:47:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
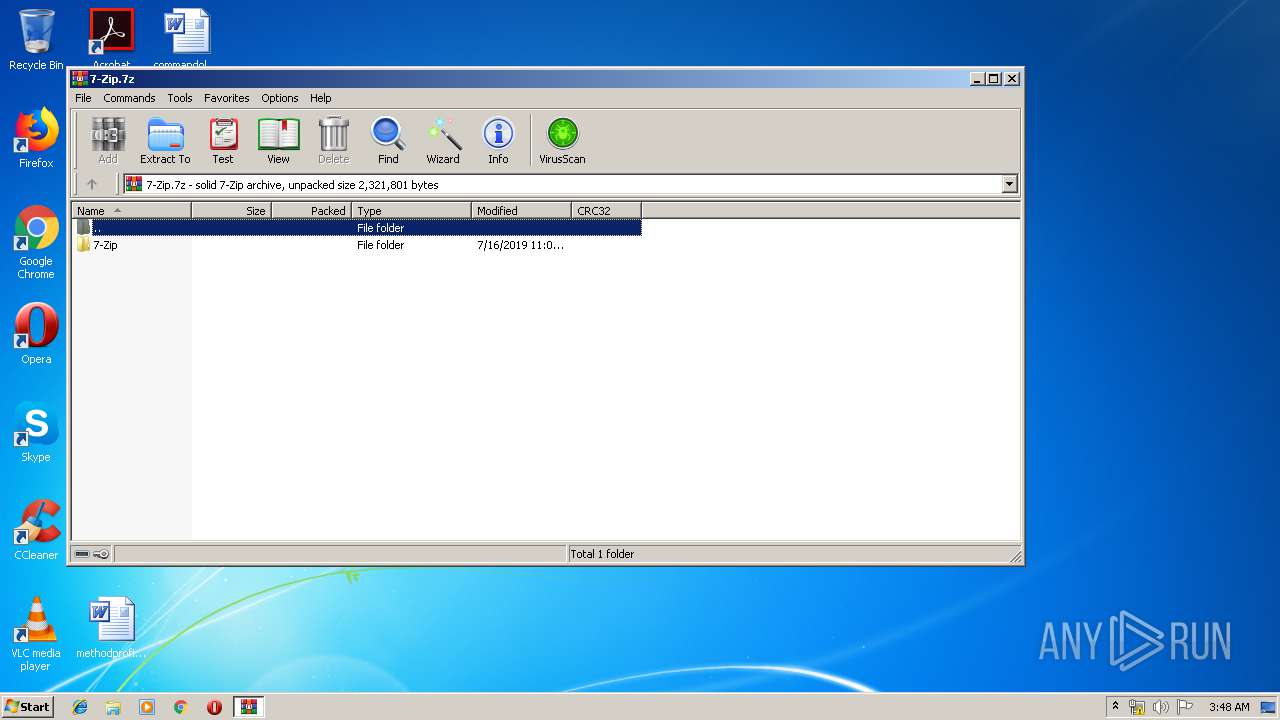
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 709AA1C065F623E89CC25A8D449D24A9 |
| SHA1: | 1E1E384DDD59AFA3BD3AACDC963B199BA3977AFF |
| SHA256: | A2202E06A1A2E3D5802E1D80CB7B32D82BC6EBB37D7C18309C76B5D3E80E7682 |
| SSDEEP: | 12288:oR/Ff0tkRPYUqqfdrn4T5ixBwR8PaWh9s4qR8ynEmrMG0:oR1RAUBn4TQxBVhqZ8A0 |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 292)
- explorer.exe (PID: 284)
- DllHost.exe (PID: 3220)
- WinRAR.exe (PID: 2948)
- 7zFMmgr.exe (PID: 1708)
- iexplore.exe (PID: 2988)
- DllHost.exe (PID: 3032)
- DllHost.exe (PID: 4044)
- DllHost.exe (PID: 2624)
- SearchProtocolHost.exe (PID: 3456)
- 7zFM.exe (PID: 3416)
Application was dropped or rewritten from another process
- 7zFM.exe (PID: 3416)
- 7zFMmgr.exe (PID: 1708)
Writes to a start menu file
- iexplore.exe (PID: 2988)
Changes the login/logoff helper path in the registry
- iexplore.exe (PID: 2988)
SUSPICIOUS
Reads Internet Cache Settings
- explorer.exe (PID: 284)
Creates files in the user directory
- explorer.exe (PID: 284)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2948)
- explorer.exe (PID: 284)
- 7zFM.exe (PID: 3416)
- 7zFMmgr.exe (PID: 1708)
Starts Internet Explorer
- 7zFMmgr.exe (PID: 1708)
Creates files in the program directory
- iexplore.exe (PID: 2988)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2988)
Reads Microsoft Office registry keys
- SearchProtocolHost.exe (PID: 3456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
40
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
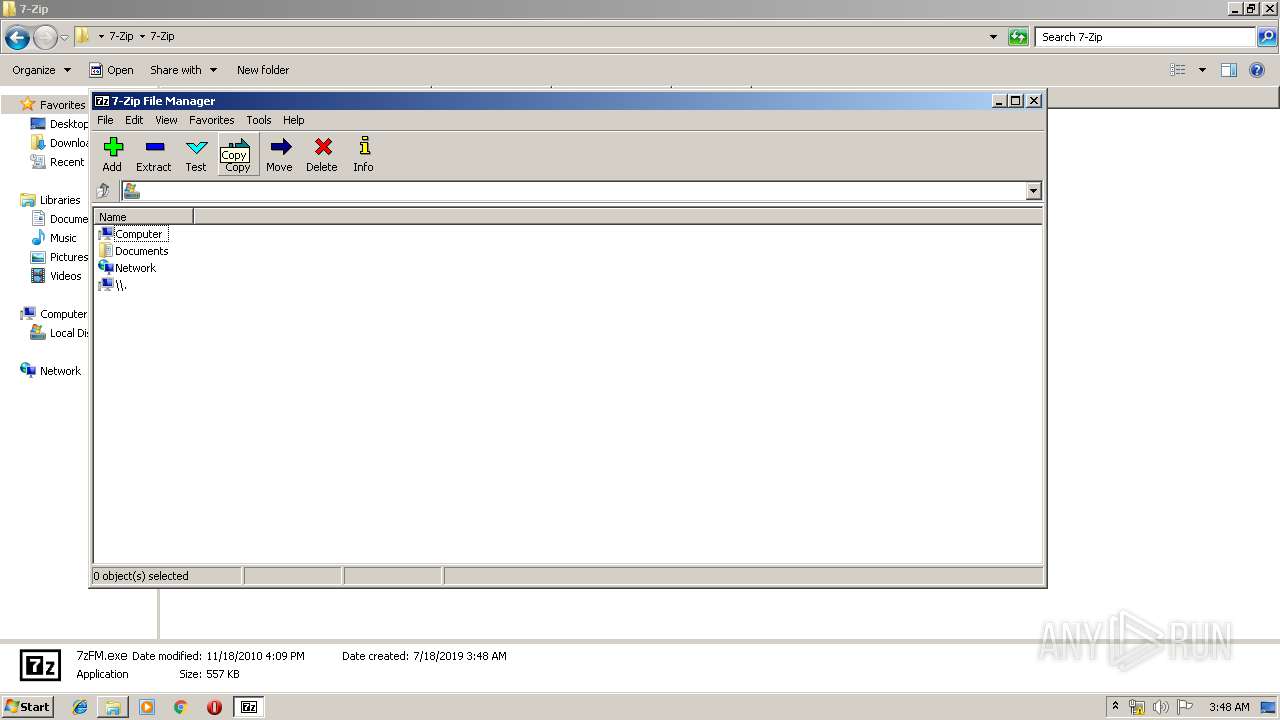
| 1708 | C:\Users\admin\Desktop\7-Zip\7-Zip\7zFMmgr.exe | C:\Users\admin\Desktop\7-Zip\7-Zip\7zFMmgr.exe | 7zFM.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2624 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\7-Zip.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2988 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | 7zFMmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
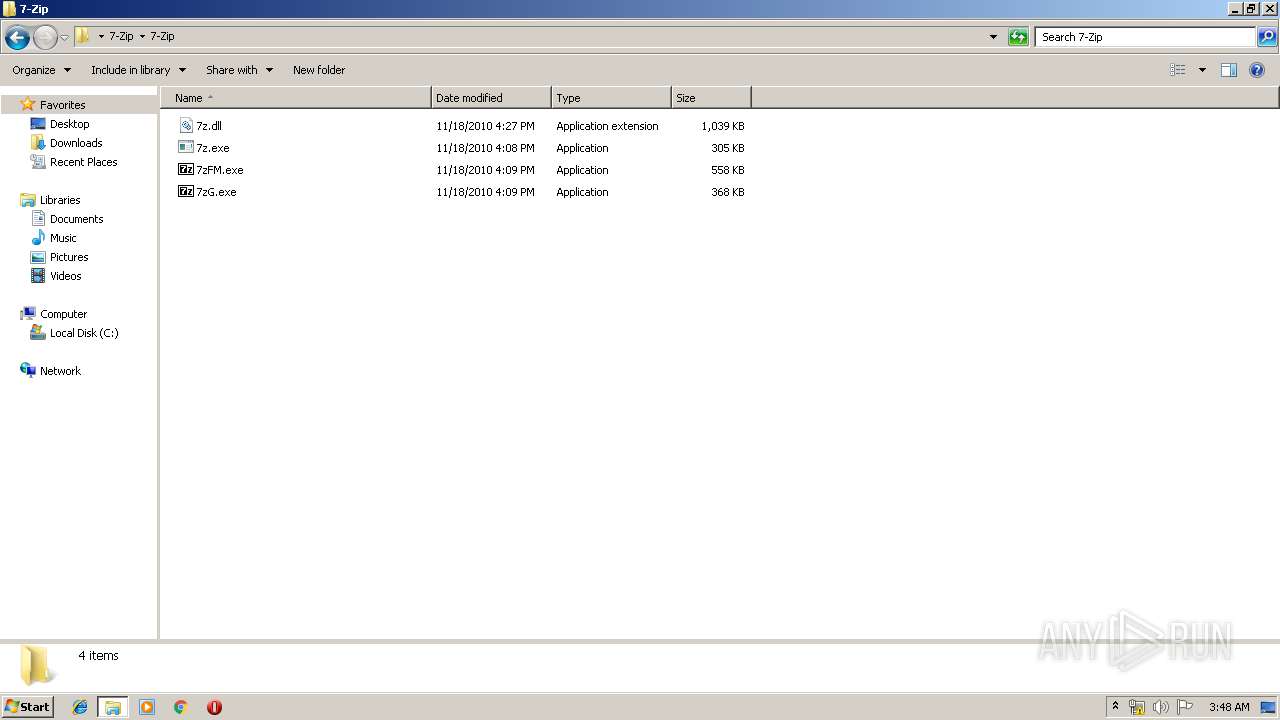
| 3416 | "C:\Users\admin\Desktop\7-Zip\7-Zip\7zFM.exe" | C:\Users\admin\Desktop\7-Zip\7-Zip\7zFM.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 3456 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10007_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10007 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 397
Read events
5 229
Write events
166
Delete events
2
Modification events
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\7-Zip.7z | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2948) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (284) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.7z\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (284) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.7z\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
7
Suspicious files
1
Text files
0
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1708 | 7zFMmgr.exe | C:\Users\admin\AppData\Local\Temp\~TM1605.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\enbfqohg.exe | — | |
MD5:— | SHA256:— | |||
| 284 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019071820190719\index.dat | dat | |
MD5:— | SHA256:— | |||
| 284 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 284 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
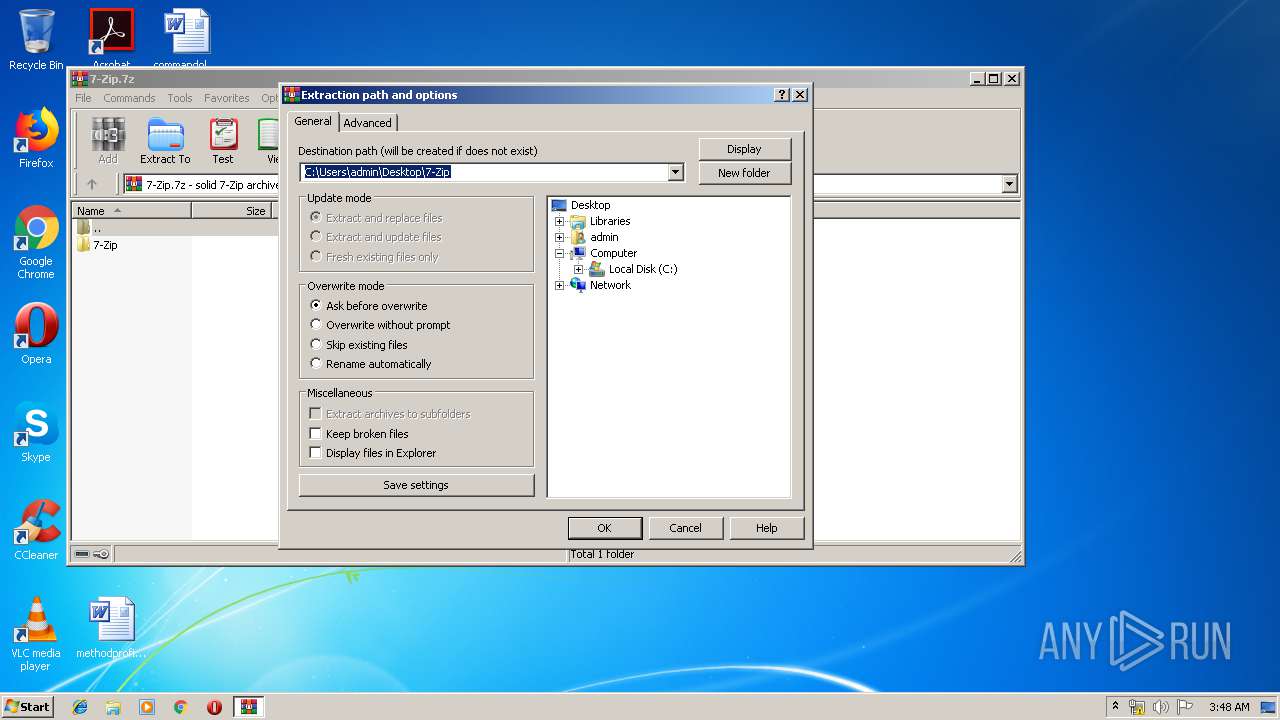
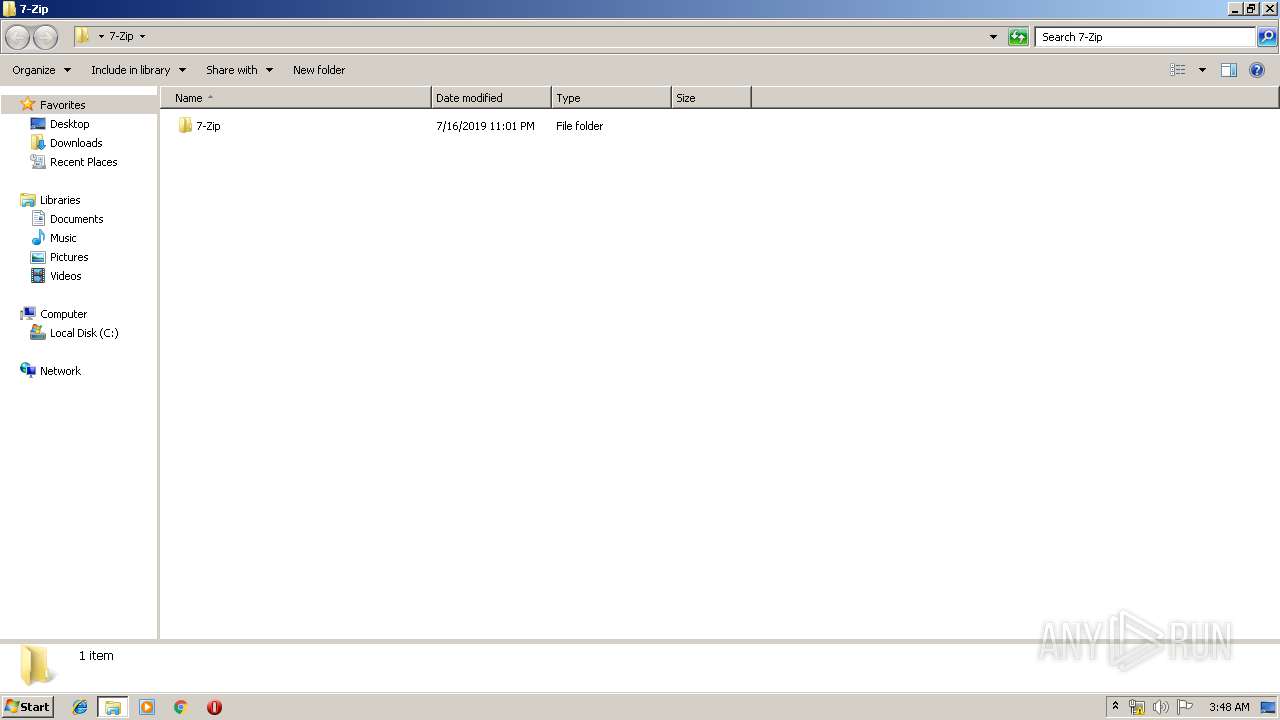
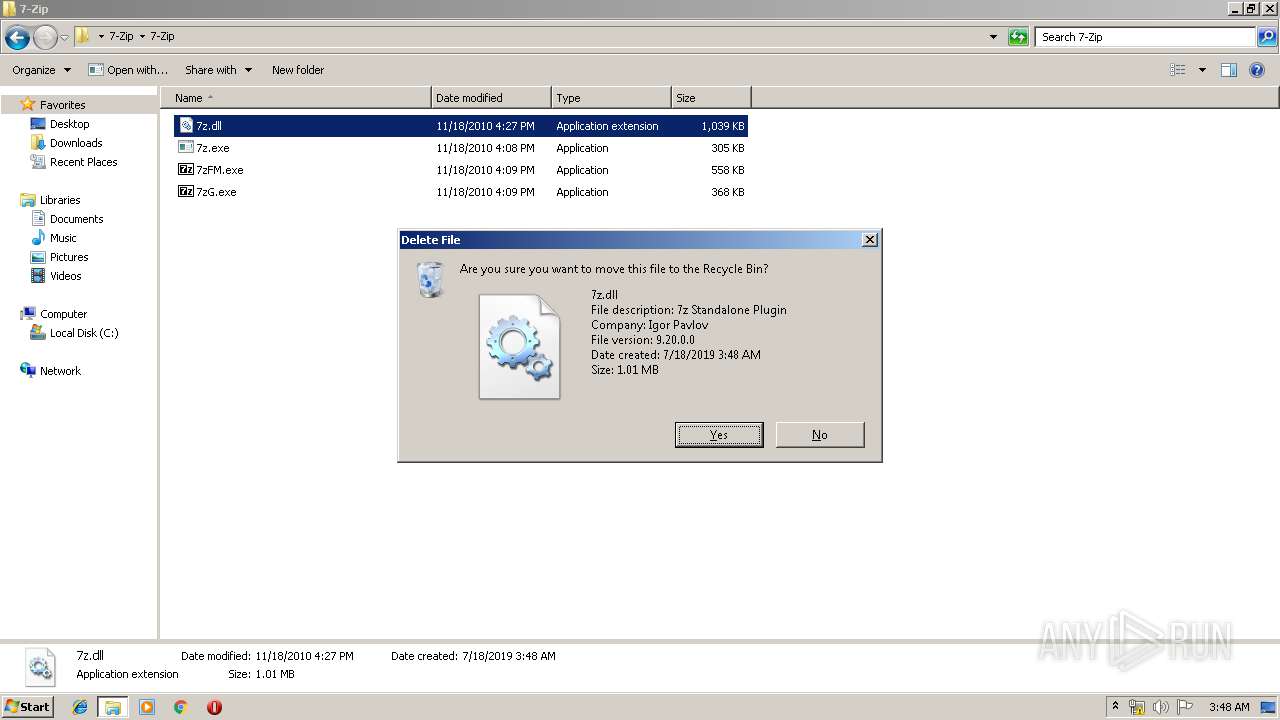
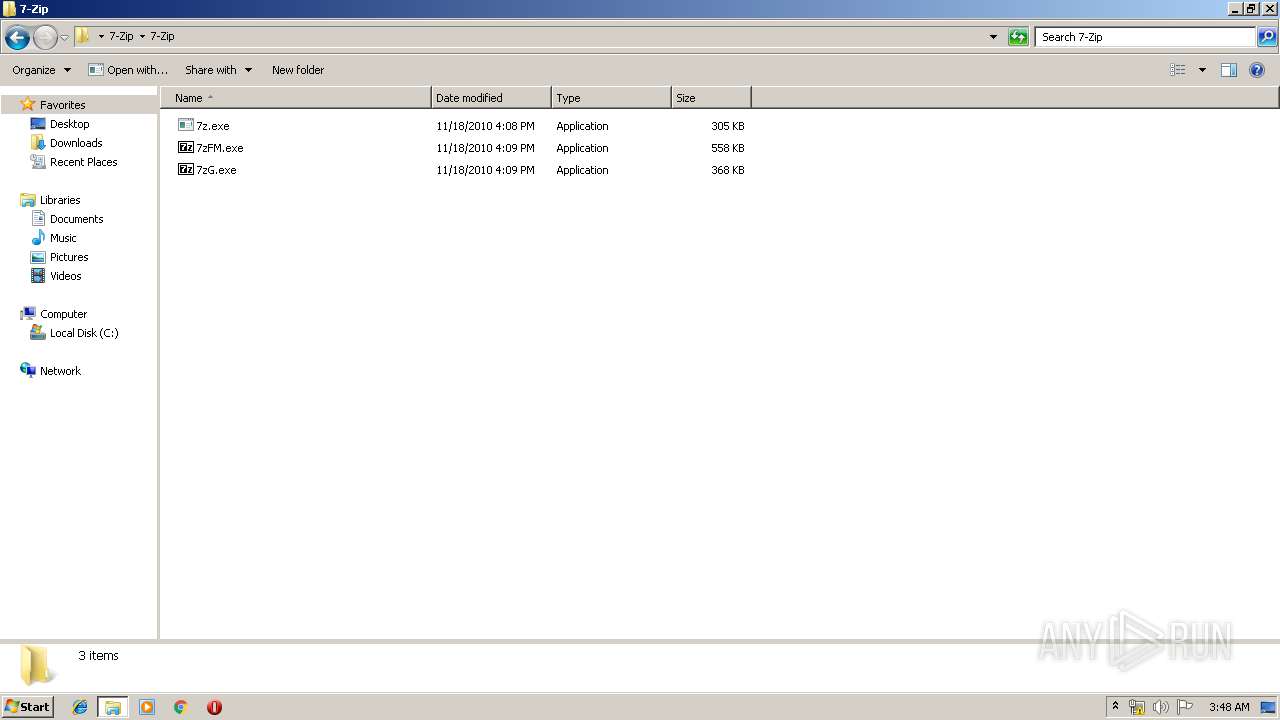
| 2948 | WinRAR.exe | C:\Users\admin\Desktop\7-Zip\7-Zip\7z.dll | executable | |
MD5:— | SHA256:— | |||
| 284 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\7-Zip.7z.lnk | lnk | |
MD5:— | SHA256:— | |||
| 284 | explorer.exe | C:\$RECYCLE.BIN\S-1-5-21-1302019708-1500728564-335382590-1000\$REBWMN3.dll | executable | |
MD5:— | SHA256:— | |||
| 2948 | WinRAR.exe | C:\Users\admin\Desktop\7-Zip\7-Zip\7zG.exe | executable | |
MD5:— | SHA256:— | |||
| 3416 | 7zFM.exe | C:\Users\admin\Desktop\7-Zip\7-Zip\7zFMmgr.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
12
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | iexplore.exe | 172.217.22.14:80 | google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stromoliks.com |
| malicious |
google.com |
| malicious |
promoliks.com |
| malicious |