| File name: | ViraBot.exe |
| Full analysis: | https://app.any.run/tasks/c8ee9f3b-5f8c-4081-beaf-bc488e562147 |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2025, 22:36:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 542694DE0AABA68D6CB6CAFE98C3C16A |
| SHA1: | 203759E383E1DF23EA3BC159854C467662CC66CE |
| SHA256: | A2126D25B90A475540BC4F9096608856A84ED5CE2D02ABCBB816643B16383B79 |
| SSDEEP: | 6144:d0Saa2HiYOxOHhTXU52osO2LnT25qndIjjVV+:d0Saa2HiYOxOw2LfLnT25qndIPVV+ |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 2148)
- powershell.exe (PID: 436)
- powershell.exe (PID: 8604)
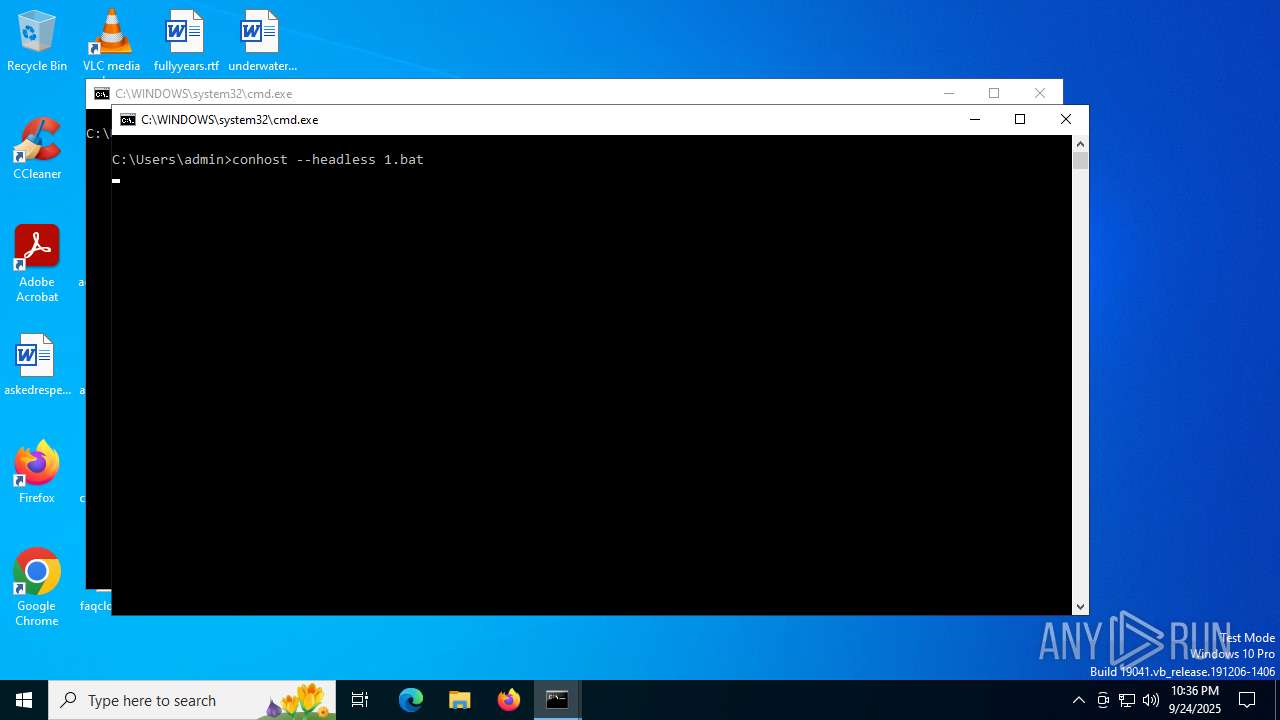
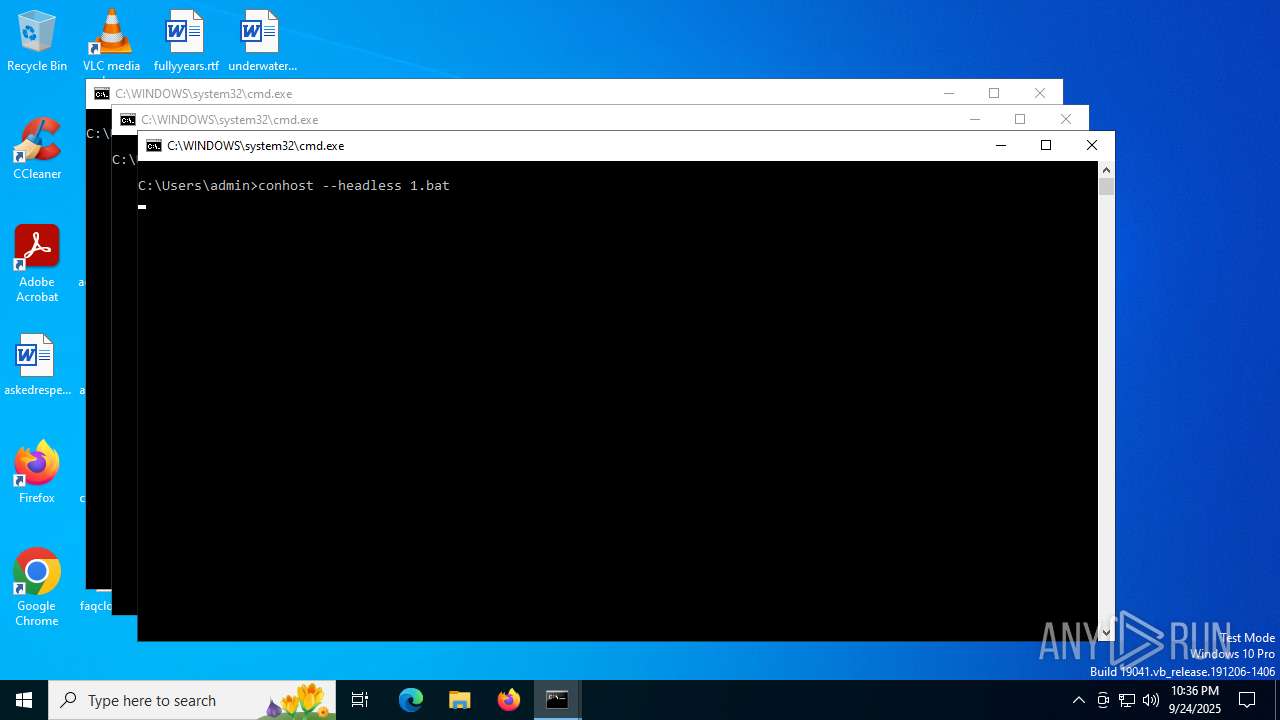
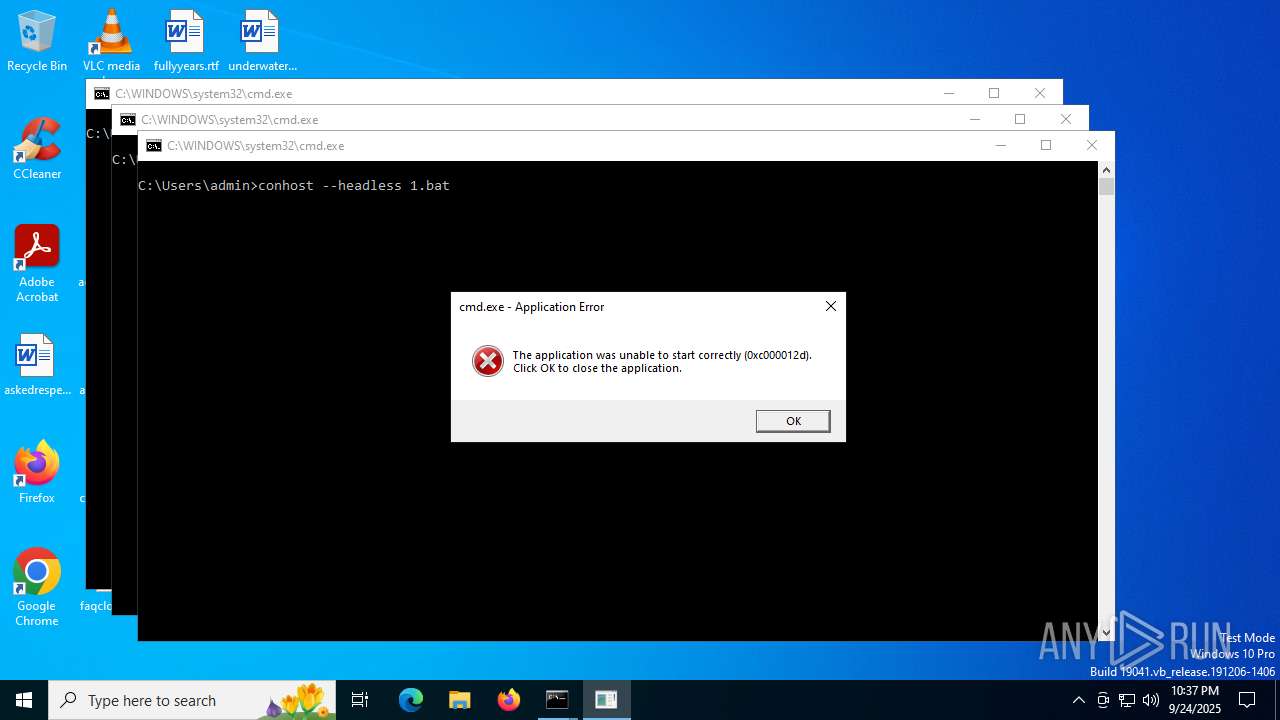
Execute application with conhost.exe as parent process
- cmd.exe (PID: 768)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 2220)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7856)
- cmd.exe (PID: 7900)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 8220)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 8264)
- cmd.exe (PID: 8304)
- cmd.exe (PID: 8352)
- cmd.exe (PID: 8404)
- cmd.exe (PID: 8180)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 8452)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8584)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 8772)
- cmd.exe (PID: 8820)
- cmd.exe (PID: 8868)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 8960)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 9060)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 9156)
- cmd.exe (PID: 9212)
- cmd.exe (PID: 9080)
- cmd.exe (PID: 9296)
- cmd.exe (PID: 9228)
- cmd.exe (PID: 8388)
- cmd.exe (PID: 8564)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 9460)
- cmd.exe (PID: 9568)
- cmd.exe (PID: 9708)
- cmd.exe (PID: 9680)
- cmd.exe (PID: 9604)
- cmd.exe (PID: 9344)
- cmd.exe (PID: 9396)
- cmd.exe (PID: 9496)
- cmd.exe (PID: 9920)
- cmd.exe (PID: 9956)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 10064)
- cmd.exe (PID: 10132)
- cmd.exe (PID: 10188)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 9812)
- cmd.exe (PID: 9864)
- cmd.exe (PID: 9692)
- cmd.exe (PID: 9592)
- cmd.exe (PID: 10004)
- cmd.exe (PID: 10100)
- cmd.exe (PID: 10260)
- cmd.exe (PID: 10216)
- cmd.exe (PID: 9320)
- cmd.exe (PID: 10484)
- cmd.exe (PID: 10560)
- cmd.exe (PID: 10640)
- cmd.exe (PID: 10660)
- cmd.exe (PID: 10320)
- cmd.exe (PID: 10348)
- cmd.exe (PID: 10412)
- cmd.exe (PID: 10452)
- cmd.exe (PID: 10568)
- cmd.exe (PID: 10760)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 10864)
- cmd.exe (PID: 10880)
- cmd.exe (PID: 10948)
- cmd.exe (PID: 10720)
- cmd.exe (PID: 10792)
- cmd.exe (PID: 10736)
- cmd.exe (PID: 11148)
- cmd.exe (PID: 11216)
- cmd.exe (PID: 11252)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 11032)
- cmd.exe (PID: 11060)
- cmd.exe (PID: 11120)
- cmd.exe (PID: 11632)
- cmd.exe (PID: 11428)
- cmd.exe (PID: 11476)
- cmd.exe (PID: 11568)
- cmd.exe (PID: 11688)
- cmd.exe (PID: 11272)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 11376)
- cmd.exe (PID: 11840)
- cmd.exe (PID: 11924)
- cmd.exe (PID: 11952)
- cmd.exe (PID: 12000)
- cmd.exe (PID: 12108)
- cmd.exe (PID: 11756)
- cmd.exe (PID: 11804)
- cmd.exe (PID: 12076)
- cmd.exe (PID: 11292)
- cmd.exe (PID: 8708)
- cmd.exe (PID: 11548)
- cmd.exe (PID: 10980)
- cmd.exe (PID: 12160)
- cmd.exe (PID: 12216)
- cmd.exe (PID: 12260)
- cmd.exe (PID: 12128)
- cmd.exe (PID: 12296)
- cmd.exe (PID: 12348)
- cmd.exe (PID: 12360)
- cmd.exe (PID: 12452)
- cmd.exe (PID: 12496)
- cmd.exe (PID: 12524)
- cmd.exe (PID: 12592)
- cmd.exe (PID: 11900)
- cmd.exe (PID: 12148)
- cmd.exe (PID: 12648)
- cmd.exe (PID: 12676)
- cmd.exe (PID: 12752)
- cmd.exe (PID: 12832)
- cmd.exe (PID: 12900)
- cmd.exe (PID: 12984)
- cmd.exe (PID: 13004)
- cmd.exe (PID: 12820)
- cmd.exe (PID: 13064)
- cmd.exe (PID: 13128)
- cmd.exe (PID: 13152)
- cmd.exe (PID: 13228)
- cmd.exe (PID: 13284)
- cmd.exe (PID: 13300)
- cmd.exe (PID: 12508)
- cmd.exe (PID: 8604)
- cmd.exe (PID: 12656)
- cmd.exe (PID: 12308)
- cmd.exe (PID: 3588)
- cmd.exe (PID: 13348)
- cmd.exe (PID: 13444)
- cmd.exe (PID: 13496)
- cmd.exe (PID: 13552)
- cmd.exe (PID: 13584)
- cmd.exe (PID: 13644)
- cmd.exe (PID: 13696)
- cmd.exe (PID: 13144)
- cmd.exe (PID: 13396)
- cmd.exe (PID: 13800)
- cmd.exe (PID: 13868)
- cmd.exe (PID: 13948)
- cmd.exe (PID: 14000)
- cmd.exe (PID: 14052)
- cmd.exe (PID: 14104)
- cmd.exe (PID: 14160)
- cmd.exe (PID: 14212)
- cmd.exe (PID: 13748)
- cmd.exe (PID: 13900)
- cmd.exe (PID: 14320)
- cmd.exe (PID: 13464)
- cmd.exe (PID: 13980)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 5468)
- cmd.exe (PID: 14400)
- cmd.exe (PID: 14268)
- cmd.exe (PID: 13988)
- cmd.exe (PID: 14368)
- cmd.exe (PID: 14564)
- cmd.exe (PID: 14608)
- cmd.exe (PID: 14712)
- cmd.exe (PID: 14720)
- cmd.exe (PID: 14764)
- cmd.exe (PID: 14876)
- cmd.exe (PID: 14884)
- cmd.exe (PID: 14468)
- cmd.exe (PID: 14516)
- cmd.exe (PID: 15020)
- cmd.exe (PID: 15060)
- cmd.exe (PID: 15076)
- cmd.exe (PID: 15188)
- cmd.exe (PID: 15220)
- cmd.exe (PID: 15348)
- cmd.exe (PID: 15228)
- cmd.exe (PID: 828)
- cmd.exe (PID: 14356)
- cmd.exe (PID: 14912)
- cmd.exe (PID: 14824)
- cmd.exe (PID: 15012)
- cmd.exe (PID: 14688)
- cmd.exe (PID: 15032)
- cmd.exe (PID: 14872)
- cmd.exe (PID: 15384)
- cmd.exe (PID: 15472)
- cmd.exe (PID: 15496)
- cmd.exe (PID: 15536)
- cmd.exe (PID: 15652)
- cmd.exe (PID: 15688)
- cmd.exe (PID: 15784)
- cmd.exe (PID: 15804)
- cmd.exe (PID: 15844)
- cmd.exe (PID: 15948)
- cmd.exe (PID: 16000)
- cmd.exe (PID: 15964)
- cmd.exe (PID: 16084)
- cmd.exe (PID: 15636)
- cmd.exe (PID: 16112)
- cmd.exe (PID: 16152)
- cmd.exe (PID: 16248)
- cmd.exe (PID: 16276)
- cmd.exe (PID: 16312)
- cmd.exe (PID: 15448)
- cmd.exe (PID: 15852)
- cmd.exe (PID: 15600)
- cmd.exe (PID: 16124)
- cmd.exe (PID: 16380)
- cmd.exe (PID: 16432)
- cmd.exe (PID: 16480)
- cmd.exe (PID: 16548)
- cmd.exe (PID: 16576)
- cmd.exe (PID: 16720)
- cmd.exe (PID: 16620)
- cmd.exe (PID: 16740)
- cmd.exe (PID: 16776)
- cmd.exe (PID: 16260)
- cmd.exe (PID: 16888)
- cmd.exe (PID: 16928)
- cmd.exe (PID: 17008)
- cmd.exe (PID: 17044)
- cmd.exe (PID: 17136)
- cmd.exe (PID: 17192)
- cmd.exe (PID: 17248)
- cmd.exe (PID: 16872)
- cmd.exe (PID: 17124)
- cmd.exe (PID: 16464)
- cmd.exe (PID: 17404)
- cmd.exe (PID: 16860)
- cmd.exe (PID: 17184)
- cmd.exe (PID: 17260)
- cmd.exe (PID: 17420)
- cmd.exe (PID: 17468)
- cmd.exe (PID: 17476)
- cmd.exe (PID: 17360)
- cmd.exe (PID: 17276)
- cmd.exe (PID: 17576)
- cmd.exe (PID: 17632)
- cmd.exe (PID: 17612)
- cmd.exe (PID: 17724)
- cmd.exe (PID: 17752)
- cmd.exe (PID: 17776)
- cmd.exe (PID: 17872)
- cmd.exe (PID: 17900)
- cmd.exe (PID: 17936)
- cmd.exe (PID: 18072)
- cmd.exe (PID: 18104)
- cmd.exe (PID: 18260)
- cmd.exe (PID: 18212)
- cmd.exe (PID: 18268)
- cmd.exe (PID: 18380)
- cmd.exe (PID: 18400)
- cmd.exe (PID: 18428)
- cmd.exe (PID: 18012)
- cmd.exe (PID: 18032)
- cmd.exe (PID: 18056)
- cmd.exe (PID: 18088)
- cmd.exe (PID: 17740)
- cmd.exe (PID: 18440)
- cmd.exe (PID: 18528)
- cmd.exe (PID: 18576)
- cmd.exe (PID: 18584)
- cmd.exe (PID: 18680)
- cmd.exe (PID: 17884)
- cmd.exe (PID: 18752)
- cmd.exe (PID: 18856)
- cmd.exe (PID: 18896)
- cmd.exe (PID: 19000)
- cmd.exe (PID: 19020)
- cmd.exe (PID: 19040)
- cmd.exe (PID: 19180)
- cmd.exe (PID: 19172)
- cmd.exe (PID: 18708)
- cmd.exe (PID: 18828)
- cmd.exe (PID: 19208)
- cmd.exe (PID: 19324)
- cmd.exe (PID: 19356)
- cmd.exe (PID: 18544)
- cmd.exe (PID: 19340)
- cmd.exe (PID: 19520)
- cmd.exe (PID: 19532)
- cmd.exe (PID: 19680)
- cmd.exe (PID: 19548)
- cmd.exe (PID: 18692)
- cmd.exe (PID: 18668)
- cmd.exe (PID: 19144)
- cmd.exe (PID: 19308)
- cmd.exe (PID: 19300)
- cmd.exe (PID: 19860)
- cmd.exe (PID: 20004)
- cmd.exe (PID: 20016)
- cmd.exe (PID: 20028)
- cmd.exe (PID: 20152)
- cmd.exe (PID: 19696)
- cmd.exe (PID: 19704)
- cmd.exe (PID: 19844)
- cmd.exe (PID: 19852)
- cmd.exe (PID: 20332)
- cmd.exe (PID: 20348)
- cmd.exe (PID: 20440)
- cmd.exe (PID: 19484)
- cmd.exe (PID: 19540)
- cmd.exe (PID: 19984)
- cmd.exe (PID: 20176)
- cmd.exe (PID: 20184)
- cmd.exe (PID: 20292)
- cmd.exe (PID: 20164)
- cmd.exe (PID: 20132)
- cmd.exe (PID: 20524)
- cmd.exe (PID: 20620)
- cmd.exe (PID: 20640)
- cmd.exe (PID: 20692)
- cmd.exe (PID: 19992)
- cmd.exe (PID: 20276)
- cmd.exe (PID: 20768)
- cmd.exe (PID: 20832)
- cmd.exe (PID: 20984)
- cmd.exe (PID: 20968)
- cmd.exe (PID: 21080)
- cmd.exe (PID: 21240)
- cmd.exe (PID: 21088)
- cmd.exe (PID: 20820)
- cmd.exe (PID: 20916)
- cmd.exe (PID: 21248)
- cmd.exe (PID: 21380)
- cmd.exe (PID: 21396)
- cmd.exe (PID: 21428)
- cmd.exe (PID: 20600)
- cmd.exe (PID: 20660)
- cmd.exe (PID: 20752)
- cmd.exe (PID: 21256)
- cmd.exe (PID: 21216)
- cmd.exe (PID: 21392)
- cmd.exe (PID: 21536)
- cmd.exe (PID: 21544)
- cmd.exe (PID: 21556)
- cmd.exe (PID: 21672)
- cmd.exe (PID: 21688)
- cmd.exe (PID: 21700)
- cmd.exe (PID: 21824)
- cmd.exe (PID: 21804)
- cmd.exe (PID: 21352)
- cmd.exe (PID: 21948)
- cmd.exe (PID: 21964)
- cmd.exe (PID: 21988)
- cmd.exe (PID: 22104)
- cmd.exe (PID: 22084)
- cmd.exe (PID: 22124)
- cmd.exe (PID: 22208)
- cmd.exe (PID: 22252)
- cmd.exe (PID: 22272)
- cmd.exe (PID: 21840)
- cmd.exe (PID: 22400)
- cmd.exe (PID: 22388)
- cmd.exe (PID: 22608)
- cmd.exe (PID: 22412)
- cmd.exe (PID: 21812)
- cmd.exe (PID: 21684)
- cmd.exe (PID: 21788)
- cmd.exe (PID: 22536)
- cmd.exe (PID: 22596)
- cmd.exe (PID: 22776)
- cmd.exe (PID: 22804)
- cmd.exe (PID: 22912)
- cmd.exe (PID: 23116)
- cmd.exe (PID: 22928)
- cmd.exe (PID: 22968)
- cmd.exe (PID: 23084)
- cmd.exe (PID: 23144)
- cmd.exe (PID: 22708)
- cmd.exe (PID: 23260)
- cmd.exe (PID: 23496)
- cmd.exe (PID: 23320)
- cmd.exe (PID: 23452)
- cmd.exe (PID: 23360)
- cmd.exe (PID: 23460)
- cmd.exe (PID: 22900)
- cmd.exe (PID: 23044)
- cmd.exe (PID: 23204)
- cmd.exe (PID: 23236)
- cmd.exe (PID: 23572)
- cmd.exe (PID: 23628)
- cmd.exe (PID: 23696)
- cmd.exe (PID: 23844)
- cmd.exe (PID: 23864)
- cmd.exe (PID: 23996)
- cmd.exe (PID: 23676)
- cmd.exe (PID: 23832)
- cmd.exe (PID: 24140)
- cmd.exe (PID: 24176)
- cmd.exe (PID: 24188)
- cmd.exe (PID: 24308)
- cmd.exe (PID: 24344)
- cmd.exe (PID: 24016)
- cmd.exe (PID: 24028)
- cmd.exe (PID: 23796)
- cmd.exe (PID: 24288)
- cmd.exe (PID: 24372)
- cmd.exe (PID: 24460)
- cmd.exe (PID: 24524)
- cmd.exe (PID: 24516)
- cmd.exe (PID: 24316)
- cmd.exe (PID: 24612)
- cmd.exe (PID: 24632)
- cmd.exe (PID: 24688)
- cmd.exe (PID: 24888)
- cmd.exe (PID: 24896)
- cmd.exe (PID: 24904)
- cmd.exe (PID: 25072)
- cmd.exe (PID: 25088)
- cmd.exe (PID: 25080)
- cmd.exe (PID: 25264)
- cmd.exe (PID: 25284)
- cmd.exe (PID: 25316)
- cmd.exe (PID: 25444)
- cmd.exe (PID: 25460)
- cmd.exe (PID: 25496)
- cmd.exe (PID: 25740)
- cmd.exe (PID: 25760)
- cmd.exe (PID: 25776)
- cmd.exe (PID: 25584)
- cmd.exe (PID: 24160)
- cmd.exe (PID: 25612)
- cmd.exe (PID: 24840)
- cmd.exe (PID: 25628)
- cmd.exe (PID: 25960)
- cmd.exe (PID: 26108)
- cmd.exe (PID: 26064)
- cmd.exe (PID: 26128)
- cmd.exe (PID: 26256)
- cmd.exe (PID: 25920)
- cmd.exe (PID: 25948)
- cmd.exe (PID: 25888)
- cmd.exe (PID: 26540)
- cmd.exe (PID: 26512)
- cmd.exe (PID: 26040)
- cmd.exe (PID: 26312)
- cmd.exe (PID: 26384)
- cmd.exe (PID: 26504)
- cmd.exe (PID: 26696)
- cmd.exe (PID: 26120)
- cmd.exe (PID: 26664)
- cmd.exe (PID: 26688)
- cmd.exe (PID: 26852)
- cmd.exe (PID: 26864)
- cmd.exe (PID: 26872)
- cmd.exe (PID: 27036)
- cmd.exe (PID: 27052)
- cmd.exe (PID: 27044)
- cmd.exe (PID: 27456)
- cmd.exe (PID: 27592)
- cmd.exe (PID: 27184)
- cmd.exe (PID: 27216)
- cmd.exe (PID: 27232)
- cmd.exe (PID: 27384)
- cmd.exe (PID: 27404)
- cmd.exe (PID: 27356)
- cmd.exe (PID: 27756)
- cmd.exe (PID: 27608)
- cmd.exe (PID: 25712)
- cmd.exe (PID: 27684)
- cmd.exe (PID: 27160)
- cmd.exe (PID: 27772)
- cmd.exe (PID: 27920)
- cmd.exe (PID: 27968)
- cmd.exe (PID: 27860)
- cmd.exe (PID: 28044)
- cmd.exe (PID: 28160)
- cmd.exe (PID: 28108)
- cmd.exe (PID: 28256)
- cmd.exe (PID: 28368)
- cmd.exe (PID: 28440)
- cmd.exe (PID: 28472)
- cmd.exe (PID: 28544)
- cmd.exe (PID: 28612)
- cmd.exe (PID: 28628)
- cmd.exe (PID: 28788)
- cmd.exe (PID: 28888)
- cmd.exe (PID: 27932)
- cmd.exe (PID: 28432)
- cmd.exe (PID: 28516)
- cmd.exe (PID: 28684)
- cmd.exe (PID: 28780)
- cmd.exe (PID: 29200)
- cmd.exe (PID: 29264)
- cmd.exe (PID: 28960)
- cmd.exe (PID: 28952)
- cmd.exe (PID: 29136)
- cmd.exe (PID: 29156)
- cmd.exe (PID: 29348)
- cmd.exe (PID: 29560)
- cmd.exe (PID: 29580)
- cmd.exe (PID: 28940)
- cmd.exe (PID: 29392)
- cmd.exe (PID: 29432)
- cmd.exe (PID: 29544)
- cmd.exe (PID: 28876)
- cmd.exe (PID: 29076)
- cmd.exe (PID: 29760)
- cmd.exe (PID: 29788)
- cmd.exe (PID: 29940)
- cmd.exe (PID: 29804)
- cmd.exe (PID: 29956)
- cmd.exe (PID: 29992)
- cmd.exe (PID: 30072)
- cmd.exe (PID: 30140)
- cmd.exe (PID: 30220)
- cmd.exe (PID: 30292)
- cmd.exe (PID: 30244)
- cmd.exe (PID: 30404)
- cmd.exe (PID: 30640)
- cmd.exe (PID: 30000)
- cmd.exe (PID: 30052)
- cmd.exe (PID: 30060)
- cmd.exe (PID: 30468)
- cmd.exe (PID: 30428)
- cmd.exe (PID: 30580)
- cmd.exe (PID: 30620)
- cmd.exe (PID: 30740)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 30772)
- cmd.exe (PID: 30908)
- cmd.exe (PID: 30972)
- cmd.exe (PID: 30956)
- cmd.exe (PID: 31096)
- cmd.exe (PID: 31116)
- cmd.exe (PID: 31132)
- cmd.exe (PID: 31244)
- cmd.exe (PID: 31276)
- cmd.exe (PID: 31452)
- cmd.exe (PID: 31628)
- cmd.exe (PID: 31316)
- cmd.exe (PID: 31436)
- cmd.exe (PID: 31524)
- cmd.exe (PID: 30756)
- cmd.exe (PID: 31840)
- cmd.exe (PID: 31872)
- cmd.exe (PID: 31640)
- cmd.exe (PID: 31700)
- cmd.exe (PID: 31092)
- cmd.exe (PID: 30948)
- cmd.exe (PID: 31600)
- cmd.exe (PID: 32080)
- cmd.exe (PID: 32100)
- cmd.exe (PID: 31928)
- cmd.exe (PID: 32040)
- cmd.exe (PID: 32232)
- cmd.exe (PID: 32256)
- cmd.exe (PID: 32292)
- cmd.exe (PID: 32416)
- cmd.exe (PID: 32432)
- cmd.exe (PID: 32472)
- cmd.exe (PID: 32564)
- cmd.exe (PID: 32584)
- cmd.exe (PID: 32636)
- cmd.exe (PID: 32764)
- cmd.exe (PID: 32060)
- cmd.exe (PID: 32740)
- cmd.exe (PID: 32216)
- cmd.exe (PID: 32032)
- cmd.exe (PID: 32816)
- cmd.exe (PID: 32936)
- cmd.exe (PID: 32944)
- cmd.exe (PID: 32992)
- cmd.exe (PID: 33156)
- cmd.exe (PID: 33164)
- cmd.exe (PID: 33184)
- cmd.exe (PID: 33300)
- cmd.exe (PID: 33476)
- cmd.exe (PID: 33340)
- cmd.exe (PID: 33372)
- cmd.exe (PID: 33124)
- cmd.exe (PID: 33508)
- cmd.exe (PID: 33560)
- cmd.exe (PID: 33708)
- cmd.exe (PID: 33684)
- cmd.exe (PID: 33728)
- cmd.exe (PID: 32932)
- cmd.exe (PID: 33172)
- cmd.exe (PID: 33800)
- cmd.exe (PID: 33884)
- cmd.exe (PID: 33820)
- cmd.exe (PID: 34124)
- cmd.exe (PID: 33968)
- cmd.exe (PID: 34000)
- cmd.exe (PID: 34200)
- cmd.exe (PID: 34232)
- cmd.exe (PID: 33640)
- cmd.exe (PID: 34308)
- cmd.exe (PID: 34372)
- cmd.exe (PID: 34408)
- cmd.exe (PID: 34552)
- cmd.exe (PID: 34484)
- cmd.exe (PID: 34564)
- cmd.exe (PID: 34688)
- cmd.exe (PID: 34696)
- cmd.exe (PID: 34736)
- cmd.exe (PID: 33936)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 34464)
- cmd.exe (PID: 34844)
- cmd.exe (PID: 35284)
- cmd.exe (PID: 34892)
- cmd.exe (PID: 34928)
- cmd.exe (PID: 35048)
- cmd.exe (PID: 35092)
- cmd.exe (PID: 35104)
- cmd.exe (PID: 35220)
- cmd.exe (PID: 35336)
- cmd.exe (PID: 35736)
- cmd.exe (PID: 35652)
- cmd.exe (PID: 35824)
- cmd.exe (PID: 35476)
- cmd.exe (PID: 35492)
- cmd.exe (PID: 35520)
- cmd.exe (PID: 35700)
- cmd.exe (PID: 35024)
- cmd.exe (PID: 35900)
- cmd.exe (PID: 36072)
- cmd.exe (PID: 35920)
- cmd.exe (PID: 36000)
- cmd.exe (PID: 35204)
- cmd.exe (PID: 35248)
- cmd.exe (PID: 1052)
- cmd.exe (PID: 36252)
- cmd.exe (PID: 36324)
- cmd.exe (PID: 36428)
- cmd.exe (PID: 36108)
- cmd.exe (PID: 36164)
- cmd.exe (PID: 36228)
- cmd.exe (PID: 36420)
- cmd.exe (PID: 36664)
- cmd.exe (PID: 36788)
- cmd.exe (PID: 36844)
- cmd.exe (PID: 36472)
- cmd.exe (PID: 36588)
- cmd.exe (PID: 36608)
- cmd.exe (PID: 36772)
- cmd.exe (PID: 36916)
- cmd.exe (PID: 1816)
- cmd.exe (PID: 36924)
- cmd.exe (PID: 37056)
- cmd.exe (PID: 36992)
- cmd.exe (PID: 35956)
- cmd.exe (PID: 36044)
- cmd.exe (PID: 36400)
- cmd.exe (PID: 37512)
- cmd.exe (PID: 37320)
- cmd.exe (PID: 37236)
- cmd.exe (PID: 37368)
- cmd.exe (PID: 37416)
- cmd.exe (PID: 37068)
- cmd.exe (PID: 37180)
- cmd.exe (PID: 37220)
- cmd.exe (PID: 37712)
- cmd.exe (PID: 37772)
- cmd.exe (PID: 37848)
- cmd.exe (PID: 37884)
- cmd.exe (PID: 37200)
- cmd.exe (PID: 37540)
- cmd.exe (PID: 37576)
- cmd.exe (PID: 37724)
- cmd.exe (PID: 37896)
- cmd.exe (PID: 37944)
- cmd.exe (PID: 37964)
- cmd.exe (PID: 38064)
- cmd.exe (PID: 38124)
- cmd.exe (PID: 38136)
- cmd.exe (PID: 37468)
- cmd.exe (PID: 37680)
- cmd.exe (PID: 38324)
- cmd.exe (PID: 38444)
- cmd.exe (PID: 38496)
- cmd.exe (PID: 38488)
- cmd.exe (PID: 38640)
- cmd.exe (PID: 38596)
- cmd.exe (PID: 38664)
- cmd.exe (PID: 38240)
- cmd.exe (PID: 38312)
- cmd.exe (PID: 38800)
- cmd.exe (PID: 37916)
- cmd.exe (PID: 38820)
- cmd.exe (PID: 4116)
- cmd.exe (PID: 38112)
- cmd.exe (PID: 38212)
- cmd.exe (PID: 38780)
- cmd.exe (PID: 38756)
- cmd.exe (PID: 39040)
- cmd.exe (PID: 39032)
- cmd.exe (PID: 39180)
- cmd.exe (PID: 39212)
- cmd.exe (PID: 39228)
- cmd.exe (PID: 39356)
- cmd.exe (PID: 39404)
- cmd.exe (PID: 38100)
- cmd.exe (PID: 39004)
- cmd.exe (PID: 39380)
- cmd.exe (PID: 39492)
- cmd.exe (PID: 39540)
- cmd.exe (PID: 39568)
- cmd.exe (PID: 39728)
- cmd.exe (PID: 39740)
- cmd.exe (PID: 39896)
- cmd.exe (PID: 39672)
- cmd.exe (PID: 39920)
- cmd.exe (PID: 39828)
- cmd.exe (PID: 39520)
- cmd.exe (PID: 39708)
- cmd.exe (PID: 40004)
- cmd.exe (PID: 40072)
- cmd.exe (PID: 39784)
- cmd.exe (PID: 40120)
- cmd.exe (PID: 40152)
- cmd.exe (PID: 40188)
- cmd.exe (PID: 40296)
- cmd.exe (PID: 40312)
- cmd.exe (PID: 40332)
- cmd.exe (PID: 40424)
- cmd.exe (PID: 40576)
- cmd.exe (PID: 40464)
- cmd.exe (PID: 40508)
- cmd.exe (PID: 40652)
- cmd.exe (PID: 40668)
- cmd.exe (PID: 40792)
- cmd.exe (PID: 40728)
- cmd.exe (PID: 40824)
- cmd.exe (PID: 40916)
- cmd.exe (PID: 40136)
- cmd.exe (PID: 40092)
- cmd.exe (PID: 40988)
- cmd.exe (PID: 41016)
- cmd.exe (PID: 40976)
- cmd.exe (PID: 41128)
- cmd.exe (PID: 41160)
- cmd.exe (PID: 41184)
- cmd.exe (PID: 41304)
- cmd.exe (PID: 41348)
- cmd.exe (PID: 41548)
- cmd.exe (PID: 41424)
- cmd.exe (PID: 41792)
- cmd.exe (PID: 41464)
- cmd.exe (PID: 41608)
- cmd.exe (PID: 41624)
- cmd.exe (PID: 41748)
- cmd.exe (PID: 41704)
- cmd.exe (PID: 41316)
- cmd.exe (PID: 41912)
- cmd.exe (PID: 41920)
- cmd.exe (PID: 41888)
- cmd.exe (PID: 41948)
- cmd.exe (PID: 2532)
- cmd.exe (PID: 41760)
- cmd.exe (PID: 42104)
- cmd.exe (PID: 41616)
- cmd.exe (PID: 42148)
- cmd.exe (PID: 42244)
- cmd.exe (PID: 42316)
- cmd.exe (PID: 42364)
- cmd.exe (PID: 42428)
- cmd.exe (PID: 42460)
- cmd.exe (PID: 42512)
- cmd.exe (PID: 42592)
- cmd.exe (PID: 42612)
- cmd.exe (PID: 42688)
- cmd.exe (PID: 42732)
- cmd.exe (PID: 42752)
- cmd.exe (PID: 42848)
- cmd.exe (PID: 42900)
- cmd.exe (PID: 42912)
- cmd.exe (PID: 42568)
- cmd.exe (PID: 42724)
- cmd.exe (PID: 43200)
- cmd.exe (PID: 42444)
- cmd.exe (PID: 43232)
- cmd.exe (PID: 43244)
- cmd.exe (PID: 43420)
- cmd.exe (PID: 43440)
- cmd.exe (PID: 43548)
- cmd.exe (PID: 43604)
- cmd.exe (PID: 43624)
- cmd.exe (PID: 43720)
- cmd.exe (PID: 43768)
- cmd.exe (PID: 43808)
- cmd.exe (PID: 43364)
- cmd.exe (PID: 43880)
- cmd.exe (PID: 43940)
- cmd.exe (PID: 43992)
- cmd.exe (PID: 43176)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 43212)
- cmd.exe (PID: 43764)
- cmd.exe (PID: 44164)
- cmd.exe (PID: 44196)
- cmd.exe (PID: 44480)
- cmd.exe (PID: 44592)
- cmd.exe (PID: 44672)
- cmd.exe (PID: 44724)
- cmd.exe (PID: 44760)
- cmd.exe (PID: 44820)
- cmd.exe (PID: 44264)
- cmd.exe (PID: 44356)
- cmd.exe (PID: 44428)
- cmd.exe (PID: 44552)
- cmd.exe (PID: 44896)
- cmd.exe (PID: 45008)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 44216)
- cmd.exe (PID: 44716)
- cmd.exe (PID: 45088)
- cmd.exe (PID: 45080)
- cmd.exe (PID: 44944)
- cmd.exe (PID: 45312)
- cmd.exe (PID: 45440)
- cmd.exe (PID: 45476)
- cmd.exe (PID: 45628)
- cmd.exe (PID: 45672)
- cmd.exe (PID: 45176)
- cmd.exe (PID: 45252)
- cmd.exe (PID: 45336)
- cmd.exe (PID: 45504)
- cmd.exe (PID: 45660)
- cmd.exe (PID: 45840)
- cmd.exe (PID: 45756)
- cmd.exe (PID: 46000)
- cmd.exe (PID: 46008)
- cmd.exe (PID: 46024)
- cmd.exe (PID: 45968)
- cmd.exe (PID: 46016)
- cmd.exe (PID: 45812)
- cmd.exe (PID: 45820)
- cmd.exe (PID: 46172)
- cmd.exe (PID: 46196)
- cmd.exe (PID: 46336)
- cmd.exe (PID: 46368)
- cmd.exe (PID: 46420)
- cmd.exe (PID: 46532)
- cmd.exe (PID: 46552)
- cmd.exe (PID: 46564)
- cmd.exe (PID: 46152)
- cmd.exe (PID: 46916)
- cmd.exe (PID: 46756)
- cmd.exe (PID: 46880)
- cmd.exe (PID: 46900)
- cmd.exe (PID: 47032)
- cmd.exe (PID: 47064)
- cmd.exe (PID: 46708)
- cmd.exe (PID: 46724)
- cmd.exe (PID: 46864)
- cmd.exe (PID: 47364)
- cmd.exe (PID: 47184)
- cmd.exe (PID: 47176)
- cmd.exe (PID: 47292)
- cmd.exe (PID: 47376)
- cmd.exe (PID: 47444)
- cmd.exe (PID: 47092)
- cmd.exe (PID: 46844)
- cmd.exe (PID: 47048)
- cmd.exe (PID: 47540)
- cmd.exe (PID: 47588)
- cmd.exe (PID: 47756)
- cmd.exe (PID: 47656)
- cmd.exe (PID: 47740)
- cmd.exe (PID: 47912)
- cmd.exe (PID: 47808)
- cmd.exe (PID: 48008)
- cmd.exe (PID: 47508)
- cmd.exe (PID: 48088)
- cmd.exe (PID: 48028)
- cmd.exe (PID: 47576)
- cmd.exe (PID: 47636)
- cmd.exe (PID: 47248)
- cmd.exe (PID: 48024)
- cmd.exe (PID: 48228)
- cmd.exe (PID: 48040)
- cmd.exe (PID: 47356)
- cmd.exe (PID: 48240)
- cmd.exe (PID: 48404)
- cmd.exe (PID: 48456)
- cmd.exe (PID: 48516)
- cmd.exe (PID: 48660)
- cmd.exe (PID: 48616)
- cmd.exe (PID: 48680)
- cmd.exe (PID: 48288)
- cmd.exe (PID: 48880)
- cmd.exe (PID: 48964)
- cmd.exe (PID: 49124)
- cmd.exe (PID: 49044)
- cmd.exe (PID: 49136)
- cmd.exe (PID: 48504)
- cmd.exe (PID: 48824)
- cmd.exe (PID: 48796)
- cmd.exe (PID: 48812)
- cmd.exe (PID: 48948)
- cmd.exe (PID: 49008)
- cmd.exe (PID: 49224)
- cmd.exe (PID: 49372)
- cmd.exe (PID: 49256)
- cmd.exe (PID: 49504)
- cmd.exe (PID: 49496)
- cmd.exe (PID: 49524)
- cmd.exe (PID: 49636)
- cmd.exe (PID: 49660)
- cmd.exe (PID: 49164)
- cmd.exe (PID: 49700)
- cmd.exe (PID: 49800)
- cmd.exe (PID: 50012)
- cmd.exe (PID: 49844)
- cmd.exe (PID: 49884)
- cmd.exe (PID: 49992)
- cmd.exe (PID: 50108)
- cmd.exe (PID: 50168)
- cmd.exe (PID: 49356)
- cmd.exe (PID: 6680)
- cmd.exe (PID: 50412)
- cmd.exe (PID: 50192)
- cmd.exe (PID: 50260)
- cmd.exe (PID: 50348)
- cmd.exe (PID: 50456)
- cmd.exe (PID: 49648)
- cmd.exe (PID: 6732)
- cmd.exe (PID: 50304)
- cmd.exe (PID: 50600)
- cmd.exe (PID: 50652)
- cmd.exe (PID: 50764)
- cmd.exe (PID: 50812)
- cmd.exe (PID: 50868)
- cmd.exe (PID: 50924)
- cmd.exe (PID: 50968)
- cmd.exe (PID: 51016)
- cmd.exe (PID: 50544)
- cmd.exe (PID: 51196)
- cmd.exe (PID: 50296)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 50784)
- cmd.exe (PID: 50944)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 50376)
- cmd.exe (PID: 51076)
- cmd.exe (PID: 51128)
- cmd.exe (PID: 51360)
- cmd.exe (PID: 51520)
- cmd.exe (PID: 51396)
- cmd.exe (PID: 51532)
- cmd.exe (PID: 51564)
- cmd.exe (PID: 51712)
- cmd.exe (PID: 51732)
- cmd.exe (PID: 51216)
- cmd.exe (PID: 51348)
- cmd.exe (PID: 51756)
- cmd.exe (PID: 52068)
- cmd.exe (PID: 51904)
- cmd.exe (PID: 51912)
- cmd.exe (PID: 52020)
- cmd.exe (PID: 52076)
- cmd.exe (PID: 52216)
- cmd.exe (PID: 50404)
- cmd.exe (PID: 51880)
- cmd.exe (PID: 52244)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 8296)
- cmd.exe (PID: 52212)
- cmd.exe (PID: 8600)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 8256)
- cmd.exe (PID: 52372)
- cmd.exe (PID: 52440)
- cmd.exe (PID: 52464)
- cmd.exe (PID: 52520)
- cmd.exe (PID: 52572)
- cmd.exe (PID: 52644)
- cmd.exe (PID: 52236)
- cmd.exe (PID: 52872)
- cmd.exe (PID: 52916)
- cmd.exe (PID: 53008)
- cmd.exe (PID: 53060)
- cmd.exe (PID: 53072)
- cmd.exe (PID: 53196)
- cmd.exe (PID: 53224)
- cmd.exe (PID: 52696)
- cmd.exe (PID: 52752)
- cmd.exe (PID: 52808)
- cmd.exe (PID: 8924)
- cmd.exe (PID: 8928)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 52544)
- cmd.exe (PID: 52844)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 9292)
- cmd.exe (PID: 9416)
- cmd.exe (PID: 53232)
- cmd.exe (PID: 52852)
- cmd.exe (PID: 53252)
- cmd.exe (PID: 10080)
- cmd.exe (PID: 53300)
- cmd.exe (PID: 53292)
- cmd.exe (PID: 53460)
- cmd.exe (PID: 53400)
- cmd.exe (PID: 53444)
- cmd.exe (PID: 9552)
- cmd.exe (PID: 52708)
- cmd.exe (PID: 53588)
- cmd.exe (PID: 53616)
- cmd.exe (PID: 53764)
- cmd.exe (PID: 53952)
- cmd.exe (PID: 53824)
- cmd.exe (PID: 53780)
- cmd.exe (PID: 53960)
- cmd.exe (PID: 53988)
- cmd.exe (PID: 53600)
- cmd.exe (PID: 54112)
- cmd.exe (PID: 54144)
- cmd.exe (PID: 54260)
- cmd.exe (PID: 53372)
- cmd.exe (PID: 54060)
- cmd.exe (PID: 54196)
- cmd.exe (PID: 9856)
- cmd.exe (PID: 11088)
- cmd.exe (PID: 53900)
- cmd.exe (PID: 10544)
- cmd.exe (PID: 10440)
- cmd.exe (PID: 53568)
- cmd.exe (PID: 11092)
- cmd.exe (PID: 11452)
- cmd.exe (PID: 11580)
- cmd.exe (PID: 12116)
- cmd.exe (PID: 12240)
- cmd.exe (PID: 54456)
- cmd.exe (PID: 54532)
- cmd.exe (PID: 54556)
- cmd.exe (PID: 54608)
- cmd.exe (PID: 11584)
- cmd.exe (PID: 54312)
- cmd.exe (PID: 54436)
- cmd.exe (PID: 54832)
- cmd.exe (PID: 54860)
- cmd.exe (PID: 54952)
- cmd.exe (PID: 54984)
- cmd.exe (PID: 55008)
- cmd.exe (PID: 54696)
- cmd.exe (PID: 54704)
- cmd.exe (PID: 54780)
- cmd.exe (PID: 55156)
- cmd.exe (PID: 55284)
- cmd.exe (PID: 11460)
- cmd.exe (PID: 55292)
- cmd.exe (PID: 12200)
- cmd.exe (PID: 12768)
- cmd.exe (PID: 12700)
- cmd.exe (PID: 55136)
- cmd.exe (PID: 54804)
- cmd.exe (PID: 54768)
- cmd.exe (PID: 13452)
- cmd.exe (PID: 55112)
- cmd.exe (PID: 55240)
- cmd.exe (PID: 12396)
- cmd.exe (PID: 14304)
- cmd.exe (PID: 54588)
- cmd.exe (PID: 54928)
- cmd.exe (PID: 15208)
- cmd.exe (PID: 15112)
- cmd.exe (PID: 14808)
- cmd.exe (PID: 15572)
- cmd.exe (PID: 14128)
- cmd.exe (PID: 54648)
- cmd.exe (PID: 12968)
- cmd.exe (PID: 15152)
- cmd.exe (PID: 6152)
- cmd.exe (PID: 55540)
- cmd.exe (PID: 15412)
- cmd.exe (PID: 55368)
- cmd.exe (PID: 55396)
- cmd.exe (PID: 55416)
- cmd.exe (PID: 55560)
- cmd.exe (PID: 15560)
- cmd.exe (PID: 15888)
- cmd.exe (PID: 55716)
- cmd.exe (PID: 55740)
- cmd.exe (PID: 55784)
- cmd.exe (PID: 55888)
- cmd.exe (PID: 55948)
- cmd.exe (PID: 55904)
- cmd.exe (PID: 56052)
- cmd.exe (PID: 55604)
- cmd.exe (PID: 56216)
- cmd.exe (PID: 56240)
- cmd.exe (PID: 55404)
- cmd.exe (PID: 55340)
- cmd.exe (PID: 16516)
- cmd.exe (PID: 15916)
- cmd.exe (PID: 56100)
- cmd.exe (PID: 56172)
- cmd.exe (PID: 17108)
- cmd.exe (PID: 17384)
- cmd.exe (PID: 55756)
- cmd.exe (PID: 17544)
- cmd.exe (PID: 16652)
- cmd.exe (PID: 16696)
- cmd.exe (PID: 17340)
- cmd.exe (PID: 17512)
- cmd.exe (PID: 56228)
- cmd.exe (PID: 56428)
- cmd.exe (PID: 56452)
- cmd.exe (PID: 56532)
- cmd.exe (PID: 56600)
- cmd.exe (PID: 17920)
- cmd.exe (PID: 18144)
- cmd.exe (PID: 17744)
- cmd.exe (PID: 56756)
- cmd.exe (PID: 56780)
- cmd.exe (PID: 56928)
- cmd.exe (PID: 56948)
- cmd.exe (PID: 57068)
- cmd.exe (PID: 56616)
- cmd.exe (PID: 56688)
- cmd.exe (PID: 56896)
- cmd.exe (PID: 57124)
- cmd.exe (PID: 57300)
- cmd.exe (PID: 57308)
- cmd.exe (PID: 56516)
- cmd.exe (PID: 18760)
- cmd.exe (PID: 57116)
- cmd.exe (PID: 57236)
- cmd.exe (PID: 19264)
- cmd.exe (PID: 19380)
- cmd.exe (PID: 19404)
- cmd.exe (PID: 18568)
- cmd.exe (PID: 18864)
- cmd.exe (PID: 19112)
- cmd.exe (PID: 18604)
- cmd.exe (PID: 57624)
- cmd.exe (PID: 57684)
- cmd.exe (PID: 57196)
- cmd.exe (PID: 19776)
- cmd.exe (PID: 20044)
- cmd.exe (PID: 57452)
- cmd.exe (PID: 57500)
- cmd.exe (PID: 57524)
- cmd.exe (PID: 57876)
- cmd.exe (PID: 57996)
- cmd.exe (PID: 58008)
- cmd.exe (PID: 58016)
- cmd.exe (PID: 57808)
- cmd.exe (PID: 57836)
- cmd.exe (PID: 57716)
- cmd.exe (PID: 58208)
- cmd.exe (PID: 58292)
- cmd.exe (PID: 58356)
- cmd.exe (PID: 19920)
- cmd.exe (PID: 20412)
- cmd.exe (PID: 57672)
- cmd.exe (PID: 58144)
- cmd.exe (PID: 58152)
- cmd.exe (PID: 57972)
- cmd.exe (PID: 57944)
- cmd.exe (PID: 21168)
- cmd.exe (PID: 21284)
- cmd.exe (PID: 57788)
- cmd.exe (PID: 20556)
- cmd.exe (PID: 21160)
- cmd.exe (PID: 21500)
- cmd.exe (PID: 21496)
- cmd.exe (PID: 58464)
- cmd.exe (PID: 58532)
- cmd.exe (PID: 58608)
- cmd.exe (PID: 58640)
- cmd.exe (PID: 58664)
- cmd.exe (PID: 20956)
- cmd.exe (PID: 58484)
- cmd.exe (PID: 58836)
- cmd.exe (PID: 58936)
- cmd.exe (PID: 58976)
- cmd.exe (PID: 59016)
- cmd.exe (PID: 59136)
- cmd.exe (PID: 58792)
- cmd.exe (PID: 58844)
- cmd.exe (PID: 59284)
- cmd.exe (PID: 59312)
- cmd.exe (PID: 59380)
- cmd.exe (PID: 58804)
- cmd.exe (PID: 58460)
- cmd.exe (PID: 21888)
- cmd.exe (PID: 59148)
- cmd.exe (PID: 59212)
- cmd.exe (PID: 59396)
- cmd.exe (PID: 59468)
- cmd.exe (PID: 59604)
- cmd.exe (PID: 59656)
- cmd.exe (PID: 44040)
- cmd.exe (PID: 47680)
- cmd.exe (PID: 59484)
- cmd.exe (PID: 59816)
- cmd.exe (PID: 59872)
- cmd.exe (PID: 60032)
- cmd.exe (PID: 60176)
- cmd.exe (PID: 59756)
- cmd.exe (PID: 59672)
- cmd.exe (PID: 59996)
- cmd.exe (PID: 60048)
- cmd.exe (PID: 22644)
- cmd.exe (PID: 60384)
- cmd.exe (PID: 60376)
- cmd.exe (PID: 22848)
- cmd.exe (PID: 60204)
- cmd.exe (PID: 60224)
- cmd.exe (PID: 60364)
- cmd.exe (PID: 59616)
- cmd.exe (PID: 60360)
- cmd.exe (PID: 60520)
- cmd.exe (PID: 60556)
- cmd.exe (PID: 60600)
- cmd.exe (PID: 60316)
- cmd.exe (PID: 59740)
- cmd.exe (PID: 60464)
- cmd.exe (PID: 60888)
- cmd.exe (PID: 60840)
- cmd.exe (PID: 60924)
- cmd.exe (PID: 61008)
- cmd.exe (PID: 60676)
- cmd.exe (PID: 60700)
- cmd.exe (PID: 60752)
- cmd.exe (PID: 61240)
- cmd.exe (PID: 61068)
- cmd.exe (PID: 61120)
- cmd.exe (PID: 61188)
- cmd.exe (PID: 61280)
- cmd.exe (PID: 61404)
- cmd.exe (PID: 23936)
- cmd.exe (PID: 24272)
- cmd.exe (PID: 24548)
- cmd.exe (PID: 60872)
- cmd.exe (PID: 60548)
- cmd.exe (PID: 60732)
- cmd.exe (PID: 60972)
- cmd.exe (PID: 61208)
- cmd.exe (PID: 61724)
- cmd.exe (PID: 61700)
- cmd.exe (PID: 61716)
- cmd.exe (PID: 61876)
- cmd.exe (PID: 61868)
- cmd.exe (PID: 61452)
- cmd.exe (PID: 61512)
- cmd.exe (PID: 61560)
- cmd.exe (PID: 62048)
- cmd.exe (PID: 62060)
- cmd.exe (PID: 62160)
- cmd.exe (PID: 62196)
- cmd.exe (PID: 62232)
- cmd.exe (PID: 61884)
- cmd.exe (PID: 62032)
- cmd.exe (PID: 24988)
- cmd.exe (PID: 62040)
- cmd.exe (PID: 62148)
- cmd.exe (PID: 62224)
- cmd.exe (PID: 62276)
- cmd.exe (PID: 62312)
- cmd.exe (PID: 62392)
- cmd.exe (PID: 62444)
- cmd.exe (PID: 62640)
- cmd.exe (PID: 62632)
- cmd.exe (PID: 62704)
- cmd.exe (PID: 62776)
- cmd.exe (PID: 62812)
- cmd.exe (PID: 62480)
- cmd.exe (PID: 62520)
- cmd.exe (PID: 63016)
- cmd.exe (PID: 63116)
- cmd.exe (PID: 63152)
- cmd.exe (PID: 62960)
- cmd.exe (PID: 62968)
- cmd.exe (PID: 63216)
- cmd.exe (PID: 62700)
- cmd.exe (PID: 62580)
- cmd.exe (PID: 62772)
- cmd.exe (PID: 26596)
- cmd.exe (PID: 63340)
- cmd.exe (PID: 63272)
- cmd.exe (PID: 63396)
- cmd.exe (PID: 63460)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 27976)
- cmd.exe (PID: 26764)
- cmd.exe (PID: 26940)
- cmd.exe (PID: 27124)
- cmd.exe (PID: 2184)
- cmd.exe (PID: 62492)
- cmd.exe (PID: 28652)
- cmd.exe (PID: 28608)
- cmd.exe (PID: 28868)
- cmd.exe (PID: 63536)
- cmd.exe (PID: 63808)
- cmd.exe (PID: 63896)
- cmd.exe (PID: 63584)
- cmd.exe (PID: 63616)
- cmd.exe (PID: 63748)
- cmd.exe (PID: 63732)
- cmd.exe (PID: 64108)
- cmd.exe (PID: 64152)
- cmd.exe (PID: 63864)
- cmd.exe (PID: 64000)
- cmd.exe (PID: 63952)
- cmd.exe (PID: 64032)
- cmd.exe (PID: 64332)
- cmd.exe (PID: 64444)
- cmd.exe (PID: 64420)
- cmd.exe (PID: 29476)
- cmd.exe (PID: 64172)
- cmd.exe (PID: 64264)
- cmd.exe (PID: 64280)
- cmd.exe (PID: 64472)
- cmd.exe (PID: 30628)
- cmd.exe (PID: 30604)
- cmd.exe (PID: 30540)
- cmd.exe (PID: 30984)
- cmd.exe (PID: 63780)
- cmd.exe (PID: 28248)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 30636)
- cmd.exe (PID: 64808)
- cmd.exe (PID: 64800)
- cmd.exe (PID: 64944)
- cmd.exe (PID: 64816)
- cmd.exe (PID: 64972)
- cmd.exe (PID: 64608)
- cmd.exe (PID: 64660)
- cmd.exe (PID: 65228)
- cmd.exe (PID: 65304)
- cmd.exe (PID: 65344)
- cmd.exe (PID: 65388)
- cmd.exe (PID: 65468)
- cmd.exe (PID: 65044)
- cmd.exe (PID: 65132)
- cmd.exe (PID: 65196)
- cmd.exe (PID: 31660)
- cmd.exe (PID: 64720)
- cmd.exe (PID: 32280)
- cmd.exe (PID: 65284)
- cmd.exe (PID: 65504)
- cmd.exe (PID: 31184)
- cmd.exe (PID: 64760)
- cmd.exe (PID: 32408)
- cmd.exe (PID: 65176)
- cmd.exe (PID: 33432)
- cmd.exe (PID: 65616)
- cmd.exe (PID: 65628)
- cmd.exe (PID: 65448)
- cmd.exe (PID: 32524)
- cmd.exe (PID: 65816)
- cmd.exe (PID: 65904)
- cmd.exe (PID: 65920)
- cmd.exe (PID: 65720)
- cmd.exe (PID: 65776)
- cmd.exe (PID: 66188)
- cmd.exe (PID: 33736)
- cmd.exe (PID: 33924)
- cmd.exe (PID: 66044)
- cmd.exe (PID: 66360)
- cmd.exe (PID: 66516)
- cmd.exe (PID: 55128)
- cmd.exe (PID: 66012)
- cmd.exe (PID: 34592)
- cmd.exe (PID: 65048)
- cmd.exe (PID: 66304)
- cmd.exe (PID: 63928)
- cmd.exe (PID: 32860)
- cmd.exe (PID: 66176)
- cmd.exe (PID: 31740)
- cmd.exe (PID: 66296)
- cmd.exe (PID: 63704)
- cmd.exe (PID: 34832)
- cmd.exe (PID: 63440)
- cmd.exe (PID: 62620)
- cmd.exe (PID: 63348)
- cmd.exe (PID: 66400)
- cmd.exe (PID: 63900)
- cmd.exe (PID: 61740)
- cmd.exe (PID: 62284)
- cmd.exe (PID: 61976)
- cmd.exe (PID: 66228)
- cmd.exe (PID: 35200)
- cmd.exe (PID: 62712)
- cmd.exe (PID: 25520)
- cmd.exe (PID: 24340)
- cmd.exe (PID: 59632)
- cmd.exe (PID: 34584)
- cmd.exe (PID: 22488)
- cmd.exe (PID: 66316)
- cmd.exe (PID: 60924)
- cmd.exe (PID: 60660)
- cmd.exe (PID: 59808)
- cmd.exe (PID: 35624)
- cmd.exe (PID: 30044)
- cmd.exe (PID: 58212)
- cmd.exe (PID: 21736)
- cmd.exe (PID: 64680)
- cmd.exe (PID: 58776)
- cmd.exe (PID: 57916)
- cmd.exe (PID: 56960)
- cmd.exe (PID: 57260)
- cmd.exe (PID: 56528)
- cmd.exe (PID: 63756)
- cmd.exe (PID: 57728)
- cmd.exe (PID: 64172)
- cmd.exe (PID: 19280)
- cmd.exe (PID: 55556)
- cmd.exe (PID: 14748)
- cmd.exe (PID: 27136)
- cmd.exe (PID: 17040)
- cmd.exe (PID: 16512)
- cmd.exe (PID: 28872)
- cmd.exe (PID: 56232)
- cmd.exe (PID: 12256)
- cmd.exe (PID: 36172)
- cmd.exe (PID: 54464)
- cmd.exe (PID: 11764)
- cmd.exe (PID: 65584)
- cmd.exe (PID: 13072)
- cmd.exe (PID: 54620)
- cmd.exe (PID: 62536)
- cmd.exe (PID: 53276)
- cmd.exe (PID: 32)
- cmd.exe (PID: 36388)
- cmd.exe (PID: 62652)
- cmd.exe (PID: 9716)
- cmd.exe (PID: 52620)
- cmd.exe (PID: 52208)
- cmd.exe (PID: 62032)
- cmd.exe (PID: 36700)
- cmd.exe (PID: 66124)
- cmd.exe (PID: 65548)
- cmd.exe (PID: 52904)
- cmd.exe (PID: 52496)
- cmd.exe (PID: 50908)
- cmd.exe (PID: 50720)
- cmd.exe (PID: 50360)
- cmd.exe (PID: 51268)
- cmd.exe (PID: 64764)
- cmd.exe (PID: 49620)
- cmd.exe (PID: 36052)
- cmd.exe (PID: 48788)
- cmd.exe (PID: 36216)
- cmd.exe (PID: 49676)
- cmd.exe (PID: 49220)
- cmd.exe (PID: 6140)
- cmd.exe (PID: 48724)
- cmd.exe (PID: 48084)
- cmd.exe (PID: 59608)
- cmd.exe (PID: 59476)
- cmd.exe (PID: 48496)
- cmd.exe (PID: 48276)
- cmd.exe (PID: 60020)
- cmd.exe (PID: 60720)
- cmd.exe (PID: 46748)
- cmd.exe (PID: 59264)
- cmd.exe (PID: 47264)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 46356)
- cmd.exe (PID: 46644)
- cmd.exe (PID: 64860)
- cmd.exe (PID: 58304)
- cmd.exe (PID: 44708)
- cmd.exe (PID: 45860)
- cmd.exe (PID: 37652)
- cmd.exe (PID: 45368)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 4032)
- cmd.exe (PID: 43472)
- cmd.exe (PID: 44676)
- cmd.exe (PID: 44472)
- cmd.exe (PID: 44288)
- cmd.exe (PID: 44740)
- cmd.exe (PID: 58308)
- cmd.exe (PID: 58040)
- cmd.exe (PID: 42816)
- cmd.exe (PID: 19560)
- cmd.exe (PID: 42380)
- cmd.exe (PID: 40956)
- cmd.exe (PID: 41852)
- cmd.exe (PID: 41712)
- cmd.exe (PID: 64068)
- cmd.exe (PID: 42840)
- cmd.exe (PID: 42656)
- cmd.exe (PID: 41168)
- cmd.exe (PID: 56996)
- cmd.exe (PID: 38560)
- cmd.exe (PID: 38676)
- cmd.exe (PID: 38736)
- cmd.exe (PID: 40024)
- cmd.exe (PID: 40216)
- cmd.exe (PID: 39264)
- cmd.exe (PID: 38636)
- cmd.exe (PID: 38352)
- cmd.exe (PID: 37952)
- cmd.exe (PID: 39100)
- cmd.exe (PID: 63604)
- cmd.exe (PID: 39468)
- cmd.exe (PID: 37924)
- cmd.exe (PID: 12604)
- cmd.exe (PID: 35820)
- cmd.exe (PID: 54600)
- cmd.exe (PID: 36232)
- cmd.exe (PID: 12196)
- cmd.exe (PID: 37412)
- cmd.exe (PID: 37080)
- cmd.exe (PID: 33116)
- cmd.exe (PID: 55188)
- cmd.exe (PID: 34724)
- cmd.exe (PID: 34560)
- cmd.exe (PID: 54844)
- cmd.exe (PID: 34064)
- cmd.exe (PID: 33496)
- cmd.exe (PID: 33388)
- cmd.exe (PID: 11920)
SUSPICIOUS
Starts process via Powershell
- powershell.exe (PID: 2148)
- powershell.exe (PID: 436)
- powershell.exe (PID: 8604)
Executing commands from a ".bat" file
- ViraBot.exe (PID: 4072)
- powershell.exe (PID: 2148)
- conhost.exe (PID: 6160)
- conhost.exe (PID: 7224)
- conhost.exe (PID: 7276)
- conhost.exe (PID: 2880)
- conhost.exe (PID: 1880)
- conhost.exe (PID: 3480)
- conhost.exe (PID: 7008)
- conhost.exe (PID: 7644)
- conhost.exe (PID: 7432)
- conhost.exe (PID: 7484)
- conhost.exe (PID: 7592)
- conhost.exe (PID: 7688)
- conhost.exe (PID: 7328)
- conhost.exe (PID: 7380)
- conhost.exe (PID: 7536)
- conhost.exe (PID: 7840)
- conhost.exe (PID: 7984)
- conhost.exe (PID: 7884)
- conhost.exe (PID: 8072)
- conhost.exe (PID: 8116)
- conhost.exe (PID: 7744)
- conhost.exe (PID: 7796)
- conhost.exe (PID: 7928)
- conhost.exe (PID: 8028)
- conhost.exe (PID: 7444)
- conhost.exe (PID: 7940)
- conhost.exe (PID: 8244)
- conhost.exe (PID: 8200)
- conhost.exe (PID: 8332)
- conhost.exe (PID: 8288)
- conhost.exe (PID: 8384)
- conhost.exe (PID: 8160)
- conhost.exe (PID: 7228)
- conhost.exe (PID: 7604)
- conhost.exe (PID: 8436)
- conhost.exe (PID: 8484)
- powershell.exe (PID: 436)
- conhost.exe (PID: 8656)
- conhost.exe (PID: 8740)
- conhost.exe (PID: 8788)
- conhost.exe (PID: 8840)
- conhost.exe (PID: 8552)
- conhost.exe (PID: 8892)
- conhost.exe (PID: 8980)
- conhost.exe (PID: 8936)
- conhost.exe (PID: 9032)
- conhost.exe (PID: 9076)
- conhost.exe (PID: 9180)
- conhost.exe (PID: 9128)
- conhost.exe (PID: 8344)
- conhost.exe (PID: 8336)
- conhost.exe (PID: 7596)
- conhost.exe (PID: 9264)
- conhost.exe (PID: 9316)
- conhost.exe (PID: 6648)
- conhost.exe (PID: 536)
- conhost.exe (PID: 8996)
- conhost.exe (PID: 8672)
- conhost.exe (PID: 9468)
- conhost.exe (PID: 9540)
- conhost.exe (PID: 9644)
- conhost.exe (PID: 9672)
- conhost.exe (PID: 9756)
- conhost.exe (PID: 9368)
- conhost.exe (PID: 9428)
- conhost.exe (PID: 9576)
- conhost.exe (PID: 9988)
- conhost.exe (PID: 9884)
- conhost.exe (PID: 10096)
- conhost.exe (PID: 10040)
- conhost.exe (PID: 10172)
- conhost.exe (PID: 9772)
- conhost.exe (PID: 9848)
- conhost.exe (PID: 9936)
- conhost.exe (PID: 9488)
- conhost.exe (PID: 9560)
- conhost.exe (PID: 9888)
- conhost.exe (PID: 10008)
- conhost.exe (PID: 10296)
- conhost.exe (PID: 10196)
- conhost.exe (PID: 9280)
- conhost.exe (PID: 9944)
- conhost.exe (PID: 10432)
- conhost.exe (PID: 10468)
- conhost.exe (PID: 10528)
- conhost.exe (PID: 10536)
- conhost.exe (PID: 10612)
- conhost.exe (PID: 10304)
- conhost.exe (PID: 10396)
- conhost.exe (PID: 10624)
- conhost.exe (PID: 10844)
- conhost.exe (PID: 10836)
- conhost.exe (PID: 10920)
- conhost.exe (PID: 10932)
- conhost.exe (PID: 11012)
- conhost.exe (PID: 10704)
- conhost.exe (PID: 10732)
- conhost.exe (PID: 10776)
- conhost.exe (PID: 11184)
- conhost.exe (PID: 11224)
- conhost.exe (PID: 10848)
- conhost.exe (PID: 11044)
- conhost.exe (PID: 11104)
- conhost.exe (PID: 11128)
- conhost.exe (PID: 10472)
- conhost.exe (PID: 11240)
- conhost.exe (PID: 11348)
- conhost.exe (PID: 11456)
- powershell.exe (PID: 8604)
- conhost.exe (PID: 11600)
- conhost.exe (PID: 11288)
- conhost.exe (PID: 11400)
- conhost.exe (PID: 11536)
- conhost.exe (PID: 11876)
- conhost.exe (PID: 11908)
- conhost.exe (PID: 11964)
- conhost.exe (PID: 11656)
- conhost.exe (PID: 11712)
- conhost.exe (PID: 11796)
- conhost.exe (PID: 11768)
- conhost.exe (PID: 12040)
- conhost.exe (PID: 12188)
- conhost.exe (PID: 12232)
- conhost.exe (PID: 12276)
- conhost.exe (PID: 8648)
- conhost.exe (PID: 11504)
- conhost.exe (PID: 8716)
- conhost.exe (PID: 12056)
- conhost.exe (PID: 12124)
- conhost.exe (PID: 11736)
- conhost.exe (PID: 12320)
- conhost.exe (PID: 12408)
- conhost.exe (PID: 12468)
- conhost.exe (PID: 12476)
- conhost.exe (PID: 11936)
- conhost.exe (PID: 11912)
- conhost.exe (PID: 10332)
- conhost.exe (PID: 12304)
- conhost.exe (PID: 12708)
- conhost.exe (PID: 12632)
- conhost.exe (PID: 12776)
- conhost.exe (PID: 12784)
- conhost.exe (PID: 13028)
- conhost.exe (PID: 13096)
- conhost.exe (PID: 12548)
- conhost.exe (PID: 12616)
- conhost.exe (PID: 12864)
- conhost.exe (PID: 12936)
- conhost.exe (PID: 12948)
- conhost.exe (PID: 13192)
- conhost.exe (PID: 13240)
- conhost.exe (PID: 13256)
- conhost.exe (PID: 12328)
- conhost.exe (PID: 12552)
- conhost.exe (PID: 12724)
- conhost.exe (PID: 13196)
- conhost.exe (PID: 13104)
- conhost.exe (PID: 13404)
- conhost.exe (PID: 13320)
- conhost.exe (PID: 13372)
- conhost.exe (PID: 13520)
- conhost.exe (PID: 13460)
- conhost.exe (PID: 13544)
- conhost.exe (PID: 13620)
- conhost.exe (PID: 12624)
- conhost.exe (PID: 12980)
- conhost.exe (PID: 13652)
- conhost.exe (PID: 13716)
- conhost.exe (PID: 13764)
- conhost.exe (PID: 13832)
- conhost.exe (PID: 13916)
- conhost.exe (PID: 13976)
- conhost.exe (PID: 14016)
- conhost.exe (PID: 14060)
- conhost.exe (PID: 14132)
- conhost.exe (PID: 14168)
- conhost.exe (PID: 13844)
- conhost.exe (PID: 14232)
- conhost.exe (PID: 14296)
- conhost.exe (PID: 13332)
- conhost.exe (PID: 13576)
- conhost.exe (PID: 14032)
- conhost.exe (PID: 14252)
- conhost.exe (PID: 2040)
- conhost.exe (PID: 2112)
- conhost.exe (PID: 14420)
- conhost.exe (PID: 14524)
- conhost.exe (PID: 14580)
- conhost.exe (PID: 14648)
- conhost.exe (PID: 14736)
- conhost.exe (PID: 14660)
- conhost.exe (PID: 14820)
- conhost.exe (PID: 14832)
- conhost.exe (PID: 14348)
- conhost.exe (PID: 14484)
- conhost.exe (PID: 14868)
- conhost.exe (PID: 14972)
- conhost.exe (PID: 15028)
- conhost.exe (PID: 15140)
- conhost.exe (PID: 15168)
- conhost.exe (PID: 15176)
- conhost.exe (PID: 15316)
- conhost.exe (PID: 15308)
- conhost.exe (PID: 15324)
- conhost.exe (PID: 14996)
- conhost.exe (PID: 14836)
- conhost.exe (PID: 14696)
- conhost.exe (PID: 5288)
- conhost.exe (PID: 15340)
- conhost.exe (PID: 14740)
- conhost.exe (PID: 15444)
- conhost.exe (PID: 15428)
- conhost.exe (PID: 15492)
- conhost.exe (PID: 14664)
- conhost.exe (PID: 15748)
- conhost.exe (PID: 15740)
- conhost.exe (PID: 15812)
- conhost.exe (PID: 15896)
- conhost.exe (PID: 15912)
- conhost.exe (PID: 15956)
- conhost.exe (PID: 16056)
- conhost.exe (PID: 15596)
- conhost.exe (PID: 15588)
- conhost.exe (PID: 15660)
- conhost.exe (PID: 16120)
- conhost.exe (PID: 16220)
- conhost.exe (PID: 15676)
- conhost.exe (PID: 15984)
- conhost.exe (PID: 16100)
- conhost.exe (PID: 16048)
- conhost.exe (PID: 16204)
- conhost.exe (PID: 16264)
- conhost.exe (PID: 16368)
- conhost.exe (PID: 16360)
- conhost.exe (PID: 16364)
- conhost.exe (PID: 16388)
- conhost.exe (PID: 16444)
- conhost.exe (PID: 16504)
- conhost.exe (PID: 16536)
- conhost.exe (PID: 16584)
- conhost.exe (PID: 16668)
- conhost.exe (PID: 16676)
- conhost.exe (PID: 16712)
- conhost.exe (PID: 16832)
- conhost.exe (PID: 16896)
- conhost.exe (PID: 16980)
- conhost.exe (PID: 17084)
- conhost.exe (PID: 17148)
- conhost.exe (PID: 17072)
- conhost.exe (PID: 17208)
- conhost.exe (PID: 16824)
- conhost.exe (PID: 16972)
- conhost.exe (PID: 17216)
- conhost.exe (PID: 17308)
- conhost.exe (PID: 17376)
- conhost.exe (PID: 17368)
- conhost.exe (PID: 16604)
- conhost.exe (PID: 16984)
- conhost.exe (PID: 16900)
- conhost.exe (PID: 16060)
- conhost.exe (PID: 17428)
- conhost.exe (PID: 17412)
- conhost.exe (PID: 17592)
- conhost.exe (PID: 17704)
- conhost.exe (PID: 17696)
- conhost.exe (PID: 17732)
- conhost.exe (PID: 17844)
- conhost.exe (PID: 17836)
- conhost.exe (PID: 17888)
- conhost.exe (PID: 17536)
- conhost.exe (PID: 17584)
- conhost.exe (PID: 18016)
- conhost.exe (PID: 18064)
- conhost.exe (PID: 18192)
- conhost.exe (PID: 18220)
- conhost.exe (PID: 18328)
- conhost.exe (PID: 18360)
- conhost.exe (PID: 18348)
- conhost.exe (PID: 17700)
- conhost.exe (PID: 17992)
- conhost.exe (PID: 18164)
- conhost.exe (PID: 17860)
- conhost.exe (PID: 15052)
- conhost.exe (PID: 18412)
- conhost.exe (PID: 18392)
- conhost.exe (PID: 18508)
- conhost.exe (PID: 18536)
- conhost.exe (PID: 18500)
- conhost.exe (PID: 18644)
- conhost.exe (PID: 17708)
- conhost.exe (PID: 18724)
- conhost.exe (PID: 18800)
- conhost.exe (PID: 18868)
- conhost.exe (PID: 18944)
- conhost.exe (PID: 18968)
- conhost.exe (PID: 18980)
- conhost.exe (PID: 19132)
- conhost.exe (PID: 19120)
- conhost.exe (PID: 18664)
- conhost.exe (PID: 18792)
- conhost.exe (PID: 15408)
- conhost.exe (PID: 19272)
- conhost.exe (PID: 19288)
- conhost.exe (PID: 19296)
- conhost.exe (PID: 19444)
- conhost.exe (PID: 19140)
- conhost.exe (PID: 19480)
- conhost.exe (PID: 19464)
- conhost.exe (PID: 19628)
- conhost.exe (PID: 19636)
- conhost.exe (PID: 19436)
- conhost.exe (PID: 19156)
- conhost.exe (PID: 19148)
- conhost.exe (PID: 19028)
- conhost.exe (PID: 19496)
- conhost.exe (PID: 19644)
- conhost.exe (PID: 19784)
- conhost.exe (PID: 19960)
- conhost.exe (PID: 19792)
- conhost.exe (PID: 19952)
- conhost.exe (PID: 20108)
- conhost.exe (PID: 20116)
- conhost.exe (PID: 19800)
- conhost.exe (PID: 19944)
- conhost.exe (PID: 20124)
- conhost.exe (PID: 20256)
- conhost.exe (PID: 20280)
- conhost.exe (PID: 20304)
- conhost.exe (PID: 20404)
- conhost.exe (PID: 20456)
- conhost.exe (PID: 20448)
- conhost.exe (PID: 19648)
- conhost.exe (PID: 20408)
- conhost.exe (PID: 20500)
- conhost.exe (PID: 20572)
- conhost.exe (PID: 20588)
- conhost.exe (PID: 20656)
- conhost.exe (PID: 19976)
- conhost.exe (PID: 20136)
- conhost.exe (PID: 20460)
- conhost.exe (PID: 20776)
- conhost.exe (PID: 20932)
- conhost.exe (PID: 21040)
- conhost.exe (PID: 20940)
- conhost.exe (PID: 21188)
- conhost.exe (PID: 21048)
- conhost.exe (PID: 21180)
- conhost.exe (PID: 20724)
- conhost.exe (PID: 20784)
- conhost.exe (PID: 20880)
- conhost.exe (PID: 21340)
- conhost.exe (PID: 21356)
- conhost.exe (PID: 21348)
- conhost.exe (PID: 19812)
- conhost.exe (PID: 19492)
- conhost.exe (PID: 20512)
- conhost.exe (PID: 21056)
- conhost.exe (PID: 21044)
- conhost.exe (PID: 21196)
- conhost.exe (PID: 21192)
- conhost.exe (PID: 21052)
- conhost.exe (PID: 21212)
- conhost.exe (PID: 21624)
- conhost.exe (PID: 21640)
- conhost.exe (PID: 21632)
- conhost.exe (PID: 21760)
- conhost.exe (PID: 21768)
- conhost.exe (PID: 21068)
- conhost.exe (PID: 22048)
- conhost.exe (PID: 21920)
- conhost.exe (PID: 21932)
- conhost.exe (PID: 21912)
- conhost.exe (PID: 22056)
- conhost.exe (PID: 22068)
- conhost.exe (PID: 22180)
- conhost.exe (PID: 22216)
- conhost.exe (PID: 22228)
- conhost.exe (PID: 21784)
- conhost.exe (PID: 22340)
- conhost.exe (PID: 22348)
- conhost.exe (PID: 22508)
- conhost.exe (PID: 22516)
- conhost.exe (PID: 22500)
- conhost.exe (PID: 22504)
- conhost.exe (PID: 22544)
- conhost.exe (PID: 22332)
- conhost.exe (PID: 21764)
- conhost.exe (PID: 22648)
- conhost.exe (PID: 22732)
- conhost.exe (PID: 22724)
- conhost.exe (PID: 22872)
- conhost.exe (PID: 22864)
- conhost.exe (PID: 23048)
- conhost.exe (PID: 22884)
- conhost.exe (PID: 23040)
- conhost.exe (PID: 23104)
- conhost.exe (PID: 23336)
- conhost.exe (PID: 23424)
- conhost.exe (PID: 23468)
- conhost.exe (PID: 23412)
- conhost.exe (PID: 22700)
- conhost.exe (PID: 22960)
- conhost.exe (PID: 22868)
- conhost.exe (PID: 23216)
- conhost.exe (PID: 23200)
- conhost.exe (PID: 23280)
- conhost.exe (PID: 22896)
- conhost.exe (PID: 23600)
- conhost.exe (PID: 23644)
- conhost.exe (PID: 23792)
- conhost.exe (PID: 23652)
- conhost.exe (PID: 23808)
- conhost.exe (PID: 23960)
- conhost.exe (PID: 23968)
- conhost.exe (PID: 23784)
- conhost.exe (PID: 24116)
- conhost.exe (PID: 24108)
- conhost.exe (PID: 24124)
- conhost.exe (PID: 24276)
- conhost.exe (PID: 24296)
- conhost.exe (PID: 24324)
- conhost.exe (PID: 23980)
- conhost.exe (PID: 23608)
- conhost.exe (PID: 24432)
- conhost.exe (PID: 24476)
- conhost.exe (PID: 24468)
- conhost.exe (PID: 23972)
- conhost.exe (PID: 24112)
- conhost.exe (PID: 24588)
- conhost.exe (PID: 24648)
- conhost.exe (PID: 24824)
- conhost.exe (PID: 24836)
- conhost.exe (PID: 24780)
- conhost.exe (PID: 25012)
- conhost.exe (PID: 25028)
- conhost.exe (PID: 25224)
- conhost.exe (PID: 25020)
- conhost.exe (PID: 25208)
- conhost.exe (PID: 25232)
- conhost.exe (PID: 25384)
- conhost.exe (PID: 25408)
- conhost.exe (PID: 25416)
- conhost.exe (PID: 25552)
- conhost.exe (PID: 25716)
- conhost.exe (PID: 25544)
- conhost.exe (PID: 24676)
- conhost.exe (PID: 25440)
- conhost.exe (PID: 25228)
- conhost.exe (PID: 25708)
- conhost.exe (PID: 25884)
- conhost.exe (PID: 26084)
- conhost.exe (PID: 26204)
- conhost.exe (PID: 25684)
- conhost.exe (PID: 25900)
- conhost.exe (PID: 25892)
- conhost.exe (PID: 26036)
- conhost.exe (PID: 26052)
- conhost.exe (PID: 26464)
- conhost.exe (PID: 26480)
- conhost.exe (PID: 26616)
- conhost.exe (PID: 26292)
- conhost.exe (PID: 26348)
- conhost.exe (PID: 26456)
- conhost.exe (PID: 26636)
- conhost.exe (PID: 26804)
- conhost.exe (PID: 25420)
- conhost.exe (PID: 25720)
- conhost.exe (PID: 25896)
- conhost.exe (PID: 26628)
- conhost.exe (PID: 26984)
- conhost.exe (PID: 27140)
- conhost.exe (PID: 26796)
- conhost.exe (PID: 26812)
- conhost.exe (PID: 26976)
- conhost.exe (PID: 26992)
- conhost.exe (PID: 27352)
- conhost.exe (PID: 27164)
- conhost.exe (PID: 27176)
- conhost.exe (PID: 27360)
- conhost.exe (PID: 27396)
- conhost.exe (PID: 27536)
- conhost.exe (PID: 27032)
- conhost.exe (PID: 27196)
- conhost.exe (PID: 27732)
- conhost.exe (PID: 27696)
- conhost.exe (PID: 26816)
- conhost.exe (PID: 27624)
- conhost.exe (PID: 27552)
- conhost.exe (PID: 27928)
- conhost.exe (PID: 28004)
- conhost.exe (PID: 27824)
- conhost.exe (PID: 27876)
- conhost.exe (PID: 28052)
- conhost.exe (PID: 28116)
- conhost.exe (PID: 28192)
- conhost.exe (PID: 28332)
- conhost.exe (PID: 28056)
- conhost.exe (PID: 28404)
- conhost.exe (PID: 28388)
- conhost.exe (PID: 28500)
- conhost.exe (PID: 28576)
- conhost.exe (PID: 28588)
- conhost.exe (PID: 27664)
- conhost.exe (PID: 28848)
- conhost.exe (PID: 28904)
- conhost.exe (PID: 28148)
- conhost.exe (PID: 27892)
- conhost.exe (PID: 28732)
- conhost.exe (PID: 28724)
- conhost.exe (PID: 29228)
- conhost.exe (PID: 29172)
- conhost.exe (PID: 29312)
- conhost.exe (PID: 28896)
- conhost.exe (PID: 29104)
- conhost.exe (PID: 29072)
- conhost.exe (PID: 29508)
- conhost.exe (PID: 29676)
- conhost.exe (PID: 29368)
- conhost.exe (PID: 29400)
- conhost.exe (PID: 29492)
- conhost.exe (PID: 29500)
- conhost.exe (PID: 29668)
- conhost.exe (PID: 29692)
- conhost.exe (PID: 29712)
- conhost.exe (PID: 29740)
- conhost.exe (PID: 29772)
- conhost.exe (PID: 29900)
- conhost.exe (PID: 29892)
- conhost.exe (PID: 29908)
- conhost.exe (PID: 30048)
- conhost.exe (PID: 30112)
- conhost.exe (PID: 30172)
- conhost.exe (PID: 30212)
- conhost.exe (PID: 30352)
- conhost.exe (PID: 30268)
- conhost.exe (PID: 30368)
- conhost.exe (PID: 30560)
- conhost.exe (PID: 30572)
- conhost.exe (PID: 30716)
- conhost.exe (PID: 30420)
- conhost.exe (PID: 30544)
- conhost.exe (PID: 29776)
- conhost.exe (PID: 29744)
- conhost.exe (PID: 30596)
- conhost.exe (PID: 3688)
- conhost.exe (PID: 30728)
- conhost.exe (PID: 30864)
- conhost.exe (PID: 31216)
- conhost.exe (PID: 31224)
- conhost.exe (PID: 30920)
- conhost.exe (PID: 30872)
- conhost.exe (PID: 31052)
- conhost.exe (PID: 31064)
- conhost.exe (PID: 31072)
- conhost.exe (PID: 24120)
- conhost.exe (PID: 31388)
- conhost.exe (PID: 31568)
- conhost.exe (PID: 31576)
- conhost.exe (PID: 31252)
- conhost.exe (PID: 31484)
- conhost.exe (PID: 31488)
- conhost.exe (PID: 31808)
- conhost.exe (PID: 31832)
- conhost.exe (PID: 31668)
- conhost.exe (PID: 29768)
- conhost.exe (PID: 30724)
- conhost.exe (PID: 31400)
- conhost.exe (PID: 31888)
- conhost.exe (PID: 31988)
- conhost.exe (PID: 32012)
- conhost.exe (PID: 32048)
- conhost.exe (PID: 32176)
- conhost.exe (PID: 32204)
- conhost.exe (PID: 32248)
- conhost.exe (PID: 32360)
- conhost.exe (PID: 32384)
- conhost.exe (PID: 32400)
- conhost.exe (PID: 32528)
- conhost.exe (PID: 32548)
- conhost.exe (PID: 32600)
- conhost.exe (PID: 32708)
- conhost.exe (PID: 32736)
- conhost.exe (PID: 32440)
- conhost.exe (PID: 32776)
- conhost.exe (PID: 32556)
- conhost.exe (PID: 32876)
- conhost.exe (PID: 32896)
- conhost.exe (PID: 32956)
- conhost.exe (PID: 33084)
- conhost.exe (PID: 33112)
- conhost.exe (PID: 32028)
- conhost.exe (PID: 33128)
- conhost.exe (PID: 33268)
- conhost.exe (PID: 33316)
- conhost.exe (PID: 33328)
- conhost.exe (PID: 32984)
- conhost.exe (PID: 32912)
- conhost.exe (PID: 33448)
- conhost.exe (PID: 33460)
- conhost.exe (PID: 33500)
- conhost.exe (PID: 33636)
- conhost.exe (PID: 33652)
- conhost.exe (PID: 33660)
- conhost.exe (PID: 33780)
- conhost.exe (PID: 33144)
- conhost.exe (PID: 33848)
- conhost.exe (PID: 33932)
- conhost.exe (PID: 34084)
- conhost.exe (PID: 34156)
- conhost.exe (PID: 33488)
- conhost.exe (PID: 32552)
- conhost.exe (PID: 33952)
- conhost.exe (PID: 34360)
- conhost.exe (PID: 34440)
- conhost.exe (PID: 34496)
- conhost.exe (PID: 34164)
- conhost.exe (PID: 34276)
- conhost.exe (PID: 34340)
- conhost.exe (PID: 34528)
- conhost.exe (PID: 34616)
- conhost.exe (PID: 34656)
- conhost.exe (PID: 34648)
- conhost.exe (PID: 32880)
- conhost.exe (PID: 32960)
- conhost.exe (PID: 34112)
- conhost.exe (PID: 34108)
- conhost.exe (PID: 35236)
- conhost.exe (PID: 33980)
- conhost.exe (PID: 34864)
- conhost.exe (PID: 34964)
- conhost.exe (PID: 35040)
- conhost.exe (PID: 35056)
- conhost.exe (PID: 35156)
- conhost.exe (PID: 35228)
- conhost.exe (PID: 35372)
- conhost.exe (PID: 35572)
- conhost.exe (PID: 35668)
- conhost.exe (PID: 34828)
- conhost.exe (PID: 35768)
- conhost.exe (PID: 35660)
- conhost.exe (PID: 35448)
- conhost.exe (PID: 35440)
- conhost.exe (PID: 35856)
- conhost.exe (PID: 35692)
- conhost.exe (PID: 35952)
- conhost.exe (PID: 36048)
- conhost.exe (PID: 35232)
- conhost.exe (PID: 34912)
- conhost.exe (PID: 35872)
- conhost.exe (PID: 36280)
- conhost.exe (PID: 36196)
- conhost.exe (PID: 36188)
- conhost.exe (PID: 36372)
- conhost.exe (PID: 36380)
- conhost.exe (PID: 36040)
- conhost.exe (PID: 36120)
- conhost.exe (PID: 36636)
- conhost.exe (PID: 36724)
- conhost.exe (PID: 36808)
- conhost.exe (PID: 36732)
- conhost.exe (PID: 1472)
- conhost.exe (PID: 36556)
- conhost.exe (PID: 36572)
- conhost.exe (PID: 31396)
- conhost.exe (PID: 36728)
- conhost.exe (PID: 36956)
- conhost.exe (PID: 36876)
- conhost.exe (PID: 36868)
- conhost.exe (PID: 35912)
- conhost.exe (PID: 36236)
- conhost.exe (PID: 36436)
- conhost.exe (PID: 37016)
- conhost.exe (PID: 37188)
- conhost.exe (PID: 37288)
- conhost.exe (PID: 37328)
- conhost.exe (PID: 37376)
- conhost.exe (PID: 37464)
- conhost.exe (PID: 37032)
- conhost.exe (PID: 37128)
- conhost.exe (PID: 37172)
- conhost.exe (PID: 37740)
- conhost.exe (PID: 37660)
- conhost.exe (PID: 37816)
- conhost.exe (PID: 36872)
- conhost.exe (PID: 37836)
- conhost.exe (PID: 37520)
- conhost.exe (PID: 37552)
- conhost.exe (PID: 37668)
- conhost.exe (PID: 38012)
- conhost.exe (PID: 38072)
- conhost.exe (PID: 37920)
- conhost.exe (PID: 38080)
- conhost.exe (PID: 37352)
- conhost.exe (PID: 37360)
- conhost.exe (PID: 37744)
- conhost.exe (PID: 37912)
- conhost.exe (PID: 38408)
- conhost.exe (PID: 38280)
- conhost.exe (PID: 38432)
- conhost.exe (PID: 38424)
- conhost.exe (PID: 38604)
- conhost.exe (PID: 38564)
- conhost.exe (PID: 38612)
- conhost.exe (PID: 38208)
- conhost.exe (PID: 38272)
- conhost.exe (PID: 38772)
- conhost.exe (PID: 38040)
- conhost.exe (PID: 38904)
- conhost.exe (PID: 37932)
- conhost.exe (PID: 38608)
- conhost.exe (PID: 38632)
- conhost.exe (PID: 38720)
- conhost.exe (PID: 38764)
- conhost.exe (PID: 38568)
- conhost.exe (PID: 38964)
- conhost.exe (PID: 39168)
- conhost.exe (PID: 39160)
- conhost.exe (PID: 39336)
- conhost.exe (PID: 39328)
- conhost.exe (PID: 39364)
- conhost.exe (PID: 39452)
- conhost.exe (PID: 38956)
- conhost.exe (PID: 38968)
- conhost.exe (PID: 39128)
- conhost.exe (PID: 39684)
- conhost.exe (PID: 39700)
- conhost.exe (PID: 39500)
- conhost.exe (PID: 39516)
- conhost.exe (PID: 39628)
- conhost.exe (PID: 39780)
- conhost.exe (PID: 39852)
- conhost.exe (PID: 39844)
- conhost.exe (PID: 39480)
- conhost.exe (PID: 39484)
- conhost.exe (PID: 39528)
- conhost.exe (PID: 39968)
- conhost.exe (PID: 40052)
- conhost.exe (PID: 40088)
- conhost.exe (PID: 40108)
- conhost.exe (PID: 40160)
- conhost.exe (PID: 40256)
- conhost.exe (PID: 40264)
- conhost.exe (PID: 40276)
- conhost.exe (PID: 40400)
- conhost.exe (PID: 40556)
- conhost.exe (PID: 40604)
- conhost.exe (PID: 40632)
- conhost.exe (PID: 40684)
- conhost.exe (PID: 40764)
- conhost.exe (PID: 40800)
- conhost.exe (PID: 40876)
- conhost.exe (PID: 40472)
- conhost.exe (PID: 40436)
- conhost.exe (PID: 40924)
- conhost.exe (PID: 40940)
- conhost.exe (PID: 40904)
- conhost.exe (PID: 40180)
- conhost.exe (PID: 40880)
- conhost.exe (PID: 41096)
- conhost.exe (PID: 41084)
- conhost.exe (PID: 41104)
- conhost.exe (PID: 41268)
- conhost.exe (PID: 41284)
- conhost.exe (PID: 41716)
- conhost.exe (PID: 41440)
- conhost.exe (PID: 41520)
- conhost.exe (PID: 41580)
- conhost.exe (PID: 41572)
- conhost.exe (PID: 41668)
- conhost.exe (PID: 41756)
- conhost.exe (PID: 41276)
- conhost.exe (PID: 41392)
- conhost.exe (PID: 41876)
- conhost.exe (PID: 41828)
- conhost.exe (PID: 40896)
- conhost.exe (PID: 41412)
- conhost.exe (PID: 41872)
- conhost.exe (PID: 41576)
- conhost.exe (PID: 42028)
- conhost.exe (PID: 42068)
- conhost.exe (PID: 42180)
- conhost.exe (PID: 41868)
- conhost.exe (PID: 42280)
- conhost.exe (PID: 42344)
- conhost.exe (PID: 42392)
- conhost.exe (PID: 42636)
- conhost.exe (PID: 42468)
- conhost.exe (PID: 42556)
- conhost.exe (PID: 42564)
- conhost.exe (PID: 42704)
- conhost.exe (PID: 42400)
- conhost.exe (PID: 42800)
- conhost.exe (PID: 42856)
- conhost.exe (PID: 42864)
- conhost.exe (PID: 42452)
- conhost.exe (PID: 42860)
- conhost.exe (PID: 43156)
- conhost.exe (PID: 42696)
- conhost.exe (PID: 42136)
- conhost.exe (PID: 43412)
- conhost.exe (PID: 43584)
- conhost.exe (PID: 43568)
- conhost.exe (PID: 43500)
- conhost.exe (PID: 43688)
- conhost.exe (PID: 43732)
- conhost.exe (PID: 43752)
- conhost.exe (PID: 43336)
- conhost.exe (PID: 43380)
- conhost.exe (PID: 43192)
- conhost.exe (PID: 43172)
- conhost.exe (PID: 43844)
- conhost.exe (PID: 43692)
- conhost.exe (PID: 44000)
- conhost.exe (PID: 43352)
- conhost.exe (PID: 43356)
- conhost.exe (PID: 44116)
- conhost.exe (PID: 44212)
- conhost.exe (PID: 43892)
- conhost.exe (PID: 43912)
- conhost.exe (PID: 44132)
- conhost.exe (PID: 44364)
- conhost.exe (PID: 44328)
- conhost.exe (PID: 44452)
- conhost.exe (PID: 44508)
- conhost.exe (PID: 44516)
- conhost.exe (PID: 44624)
- conhost.exe (PID: 44696)
- conhost.exe (PID: 44712)
- conhost.exe (PID: 44788)
- conhost.exe (PID: 44884)
- conhost.exe (PID: 44952)
- conhost.exe (PID: 45052)
- conhost.exe (PID: 44512)
- conhost.exe (PID: 4912)
- conhost.exe (PID: 44920)
- conhost.exe (PID: 45124)
- conhost.exe (PID: 44860)
- conhost.exe (PID: 45000)
- conhost.exe (PID: 45284)
- conhost.exe (PID: 45296)
- conhost.exe (PID: 45416)
- conhost.exe (PID: 45448)
- conhost.exe (PID: 45456)
- conhost.exe (PID: 45608)
- conhost.exe (PID: 45600)
- conhost.exe (PID: 45592)
- conhost.exe (PID: 45224)
- conhost.exe (PID: 45752)
- conhost.exe (PID: 45772)
- conhost.exe (PID: 45780)
- conhost.exe (PID: 45944)
- conhost.exe (PID: 45952)
- conhost.exe (PID: 45960)
- conhost.exe (PID: 45492)
- conhost.exe (PID: 45612)
- conhost.exe (PID: 46124)
- conhost.exe (PID: 46160)
- conhost.exe (PID: 46312)
- conhost.exe (PID: 46388)
- conhost.exe (PID: 46484)
- conhost.exe (PID: 46500)
- conhost.exe (PID: 46492)
- conhost.exe (PID: 45648)
- conhost.exe (PID: 46116)
- conhost.exe (PID: 46300)
- conhost.exe (PID: 46664)
- conhost.exe (PID: 46692)
- conhost.exe (PID: 47040)
- conhost.exe (PID: 46852)
- conhost.exe (PID: 46840)
- conhost.exe (PID: 46832)
- conhost.exe (PID: 47016)
- conhost.exe (PID: 47000)
- conhost.exe (PID: 46672)
- conhost.exe (PID: 46680)
- conhost.exe (PID: 47116)
- conhost.exe (PID: 47132)
- conhost.exe (PID: 47244)
- conhost.exe (PID: 47312)
- conhost.exe (PID: 47316)
- conhost.exe (PID: 47408)
- conhost.exe (PID: 46436)
- conhost.exe (PID: 46516)
- conhost.exe (PID: 47500)
- conhost.exe (PID: 47784)
- conhost.exe (PID: 47620)
- conhost.exe (PID: 47560)
- conhost.exe (PID: 47696)
- conhost.exe (PID: 47704)
- conhost.exe (PID: 47860)
- conhost.exe (PID: 47480)
- conhost.exe (PID: 48052)
- conhost.exe (PID: 47324)
- conhost.exe (PID: 47320)
- conhost.exe (PID: 48080)
- conhost.exe (PID: 48032)
- conhost.exe (PID: 48192)
- conhost.exe (PID: 47984)
- conhost.exe (PID: 48020)
- conhost.exe (PID: 47276)
- conhost.exe (PID: 47348)
- conhost.exe (PID: 48252)
- conhost.exe (PID: 48360)
- conhost.exe (PID: 48352)
- conhost.exe (PID: 48412)
- conhost.exe (PID: 48556)
- conhost.exe (PID: 48600)
- conhost.exe (PID: 48772)
- conhost.exe (PID: 48636)
- conhost.exe (PID: 48184)
- conhost.exe (PID: 48820)
- conhost.exe (PID: 48920)
- conhost.exe (PID: 49004)
- conhost.exe (PID: 49072)
- conhost.exe (PID: 49080)
- conhost.exe (PID: 48260)
- conhost.exe (PID: 48416)
- conhost.exe (PID: 48764)
- conhost.exe (PID: 48912)
- conhost.exe (PID: 49100)
- conhost.exe (PID: 49200)
- conhost.exe (PID: 49192)
- conhost.exe (PID: 49444)
- conhost.exe (PID: 49452)
- conhost.exe (PID: 49468)
- conhost.exe (PID: 49608)
- conhost.exe (PID: 48676)
- conhost.exe (PID: 49304)
- conhost.exe (PID: 49668)
- conhost.exe (PID: 49784)
- conhost.exe (PID: 49812)
- conhost.exe (PID: 49828)
- conhost.exe (PID: 49948)
- conhost.exe (PID: 49960)
- conhost.exe (PID: 50072)
- conhost.exe (PID: 50136)
- conhost.exe (PID: 49616)
- conhost.exe (PID: 49876)
- conhost.exe (PID: 49832)
- conhost.exe (PID: 5744)
- conhost.exe (PID: 50268)
- conhost.exe (PID: 50312)
- conhost.exe (PID: 50372)
- conhost.exe (PID: 50420)
- conhost.exe (PID: 50496)
- conhost.exe (PID: 50144)
- conhost.exe (PID: 49448)
- conhost.exe (PID: 50224)
- conhost.exe (PID: 50608)
- conhost.exe (PID: 50728)
- conhost.exe (PID: 50780)
- conhost.exe (PID: 50832)
- conhost.exe (PID: 50892)
- conhost.exe (PID: 50912)
- conhost.exe (PID: 50992)
- conhost.exe (PID: 51036)
- conhost.exe (PID: 50552)
- conhost.exe (PID: 51160)
- conhost.exe (PID: 51088)
- conhost.exe (PID: 51188)
- conhost.exe (PID: 50340)
- conhost.exe (PID: 50520)
- conhost.exe (PID: 7320)
- conhost.exe (PID: 7428)
- conhost.exe (PID: 7720)
- conhost.exe (PID: 51192)
- conhost.exe (PID: 51484)
- conhost.exe (PID: 51308)
- conhost.exe (PID: 51320)
- conhost.exe (PID: 51476)
- conhost.exe (PID: 51500)
- conhost.exe (PID: 51652)
- conhost.exe (PID: 51672)
- conhost.exe (PID: 50244)
- conhost.exe (PID: 51304)
- conhost.exe (PID: 52168)
- conhost.exe (PID: 51848)
- conhost.exe (PID: 51984)
- conhost.exe (PID: 51996)
- conhost.exe (PID: 52004)
- conhost.exe (PID: 52160)
- conhost.exe (PID: 51692)
- conhost.exe (PID: 51840)
- conhost.exe (PID: 51860)
- conhost.exe (PID: 51488)
- conhost.exe (PID: 52012)
- conhost.exe (PID: 52032)
- conhost.exe (PID: 51988)
- conhost.exe (PID: 8108)
- conhost.exe (PID: 52176)
- conhost.exe (PID: 51508)
- conhost.exe (PID: 8112)
- conhost.exe (PID: 52612)
- conhost.exe (PID: 52428)
- conhost.exe (PID: 52488)
- conhost.exe (PID: 52536)
- conhost.exe (PID: 52656)
- conhost.exe (PID: 8412)
- conhost.exe (PID: 8432)
- conhost.exe (PID: 52324)
- conhost.exe (PID: 52404)
- conhost.exe (PID: 52772)
- conhost.exe (PID: 52964)
- conhost.exe (PID: 53016)
- conhost.exe (PID: 53148)
- conhost.exe (PID: 53024)
- conhost.exe (PID: 53164)
- conhost.exe (PID: 52704)
- conhost.exe (PID: 52840)
- conhost.exe (PID: 52860)
- conhost.exe (PID: 52884)
- conhost.exe (PID: 52448)
- conhost.exe (PID: 8888)
- conhost.exe (PID: 52412)
- conhost.exe (PID: 52724)
- conhost.exe (PID: 52728)
- conhost.exe (PID: 53192)
- conhost.exe (PID: 53172)
- conhost.exe (PID: 53180)
- conhost.exe (PID: 9732)
- conhost.exe (PID: 53368)
- conhost.exe (PID: 52732)
- conhost.exe (PID: 9908)
- conhost.exe (PID: 1392)
- conhost.exe (PID: 9748)
- conhost.exe (PID: 53408)
- conhost.exe (PID: 53416)
- conhost.exe (PID: 9436)
- conhost.exe (PID: 52408)
- conhost.exe (PID: 53544)
- conhost.exe (PID: 53720)
- conhost.exe (PID: 53536)
- conhost.exe (PID: 53560)
- conhost.exe (PID: 53904)
- conhost.exe (PID: 53740)
- conhost.exe (PID: 53800)
- conhost.exe (PID: 53920)
- conhost.exe (PID: 53896)
- conhost.exe (PID: 54080)
- conhost.exe (PID: 54124)
- conhost.exe (PID: 54228)
- conhost.exe (PID: 54156)
- conhost.exe (PID: 53260)
- conhost.exe (PID: 54040)
- conhost.exe (PID: 10916)
- conhost.exe (PID: 54240)
- conhost.exe (PID: 10292)
- conhost.exe (PID: 10252)
- conhost.exe (PID: 53452)
- conhost.exe (PID: 10936)
- conhost.exe (PID: 10608)
- conhost.exe (PID: 10940)
- conhost.exe (PID: 11280)
- conhost.exe (PID: 11324)
- conhost.exe (PID: 12020)
- conhost.exe (PID: 11960)
- conhost.exe (PID: 12156)
- conhost.exe (PID: 54420)
- conhost.exe (PID: 54500)
- conhost.exe (PID: 54508)
- conhost.exe (PID: 54572)
- conhost.exe (PID: 54412)
- conhost.exe (PID: 54736)
- conhost.exe (PID: 54796)
- conhost.exe (PID: 54824)
- conhost.exe (PID: 54924)
- conhost.exe (PID: 54916)
- conhost.exe (PID: 54960)
- conhost.exe (PID: 55072)
- conhost.exe (PID: 54644)
- conhost.exe (PID: 54652)
- conhost.exe (PID: 55092)
- conhost.exe (PID: 12600)
- conhost.exe (PID: 12432)
- conhost.exe (PID: 55252)
- conhost.exe (PID: 55244)
- conhost.exe (PID: 11940)
- conhost.exe (PID: 55084)
- conhost.exe (PID: 55236)
- conhost.exe (PID: 54668)
- conhost.exe (PID: 13036)
- conhost.exe (PID: 13736)
- conhost.exe (PID: 13420)
- conhost.exe (PID: 13956)
- conhost.exe (PID: 12428)
- conhost.exe (PID: 54512)
- conhost.exe (PID: 13180)
- conhost.exe (PID: 54828)
- conhost.exe (PID: 15100)
- conhost.exe (PID: 13216)
- conhost.exe (PID: 14544)
- conhost.exe (PID: 55256)
- conhost.exe (PID: 2168)
- conhost.exe (PID: 14224)
- conhost.exe (PID: 14256)
- conhost.exe (PID: 14220)
- conhost.exe (PID: 13024)
- conhost.exe (PID: 15736)
- conhost.exe (PID: 15980)
- conhost.exe (PID: 16024)
- conhost.exe (PID: 55328)
- conhost.exe (PID: 55336)
- conhost.exe (PID: 55344)
- conhost.exe (PID: 55528)
- conhost.exe (PID: 55512)
- conhost.exe (PID: 55840)
- conhost.exe (PID: 56016)
- conhost.exe (PID: 55692)
- conhost.exe (PID: 55732)
- conhost.exe (PID: 55852)
- conhost.exe (PID: 55916)
- conhost.exe (PID: 56068)
- conhost.exe (PID: 55576)
- conhost.exe (PID: 55680)
- conhost.exe (PID: 56308)
- conhost.exe (PID: 56192)
- conhost.exe (PID: 56180)
- conhost.exe (PID: 16348)
- conhost.exe (PID: 55708)
- conhost.exe (PID: 55332)
- conhost.exe (PID: 16468)
- conhost.exe (PID: 56144)
- conhost.exe (PID: 16956)
- conhost.exe (PID: 17300)
- conhost.exe (PID: 17692)
- conhost.exe (PID: 56188)
- conhost.exe (PID: 16988)
- conhost.exe (PID: 17088)
- conhost.exe (PID: 17336)
- conhost.exe (PID: 55768)
- conhost.exe (PID: 16588)
- conhost.exe (PID: 18304)
- conhost.exe (PID: 56400)
- conhost.exe (PID: 56564)
- conhost.exe (PID: 56512)
- conhost.exe (PID: 55696)
- conhost.exe (PID: 56416)
- conhost.exe (PID: 56732)
- conhost.exe (PID: 56848)
- conhost.exe (PID: 56860)
- conhost.exe (PID: 56868)
- conhost.exe (PID: 56572)
- conhost.exe (PID: 56636)
- conhost.exe (PID: 56724)
- conhost.exe (PID: 56404)
- conhost.exe (PID: 57252)
- conhost.exe (PID: 57244)
- conhost.exe (PID: 18628)
- conhost.exe (PID: 57032)
- conhost.exe (PID: 57056)
- conhost.exe (PID: 57052)
- conhost.exe (PID: 57192)
- conhost.exe (PID: 57036)
- conhost.exe (PID: 57088)
- conhost.exe (PID: 57220)
- conhost.exe (PID: 56420)
- conhost.exe (PID: 19012)
- conhost.exe (PID: 19572)
- conhost.exe (PID: 18616)
- conhost.exe (PID: 18936)
- conhost.exe (PID: 19780)
- conhost.exe (PID: 57412)
- conhost.exe (PID: 57460)
- conhost.exe (PID: 57476)
- conhost.exe (PID: 57584)
- conhost.exe (PID: 57648)
- conhost.exe (PID: 18784)
- conhost.exe (PID: 57940)
- conhost.exe (PID: 57828)
- conhost.exe (PID: 57948)
- conhost.exe (PID: 58104)
- conhost.exe (PID: 57664)
- conhost.exe (PID: 57772)
- conhost.exe (PID: 57792)
- conhost.exe (PID: 58300)
- conhost.exe (PID: 20228)
- conhost.exe (PID: 57956)
- conhost.exe (PID: 58112)
- conhost.exe (PID: 58096)
- conhost.exe (PID: 58240)
- conhost.exe (PID: 58348)
- conhost.exe (PID: 20476)
- conhost.exe (PID: 20488)
- conhost.exe (PID: 21024)
- conhost.exe (PID: 58336)
- conhost.exe (PID: 58276)
- conhost.exe (PID: 20380)
- conhost.exe (PID: 57604)
- conhost.exe (PID: 20284)
- conhost.exe (PID: 58340)
- conhost.exe (PID: 58392)
- conhost.exe (PID: 58456)
- conhost.exe (PID: 58568)
- conhost.exe (PID: 58508)
- conhost.exe (PID: 58584)
- conhost.exe (PID: 20608)
- conhost.exe (PID: 21176)
- conhost.exe (PID: 58776)
- conhost.exe (PID: 59088)
- conhost.exe (PID: 58784)
- conhost.exe (PID: 58948)
- conhost.exe (PID: 58964)
- conhost.exe (PID: 58648)
- conhost.exe (PID: 58752)
- conhost.exe (PID: 58900)
- conhost.exe (PID: 59252)
- conhost.exe (PID: 59276)
- conhost.exe (PID: 21740)
- conhost.exe (PID: 59096)
- conhost.exe (PID: 59176)
- conhost.exe (PID: 59356)
- conhost.exe (PID: 21208)
- conhost.exe (PID: 22464)
- conhost.exe (PID: 59420)
- conhost.exe (PID: 59432)
- conhost.exe (PID: 59576)
- conhost.exe (PID: 59620)
- conhost.exe (PID: 58756)
- conhost.exe (PID: 58952)
- conhost.exe (PID: 22028)
- conhost.exe (PID: 59776)
- conhost.exe (PID: 59984)
- conhost.exe (PID: 59948)
- conhost.exe (PID: 60136)
- conhost.exe (PID: 59972)
- conhost.exe (PID: 59612)
- conhost.exe (PID: 59728)
- conhost.exe (PID: 59828)
- conhost.exe (PID: 60312)
- conhost.exe (PID: 60320)
- conhost.exe (PID: 60304)
- conhost.exe (PID: 59476)
- conhost.exe (PID: 59628)
- conhost.exe (PID: 60156)
- conhost.exe (PID: 60164)
- conhost.exe (PID: 59436)
- conhost.exe (PID: 60200)
- conhost.exe (PID: 60480)
- conhost.exe (PID: 60564)
- conhost.exe (PID: 60508)
- conhost.exe (PID: 22696)
- conhost.exe (PID: 60168)
- conhost.exe (PID: 60440)
- conhost.exe (PID: 60720)
- conhost.exe (PID: 60792)
- conhost.exe (PID: 60824)
- conhost.exe (PID: 60968)
- conhost.exe (PID: 60868)
- conhost.exe (PID: 61028)
- conhost.exe (PID: 60632)
- conhost.exe (PID: 60644)
- conhost.exe (PID: 61152)
- conhost.exe (PID: 61204)
- conhost.exe (PID: 61228)
- conhost.exe (PID: 61344)
- conhost.exe (PID: 61076)
- conhost.exe (PID: 60636)
- conhost.exe (PID: 24132)
- conhost.exe (PID: 24424)
- conhost.exe (PID: 24208)
- conhost.exe (PID: 61420)
- conhost.exe (PID: 23636)
- conhost.exe (PID: 60896)
- conhost.exe (PID: 61040)
- conhost.exe (PID: 61224)
- conhost.exe (PID: 61468)
- conhost.exe (PID: 61656)
- conhost.exe (PID: 61672)
- conhost.exe (PID: 61664)
- conhost.exe (PID: 61804)
- conhost.exe (PID: 61820)
- conhost.exe (PID: 61484)
- conhost.exe (PID: 61992)
- conhost.exe (PID: 62136)
- conhost.exe (PID: 62204)
- conhost.exe (PID: 61812)
- conhost.exe (PID: 61984)
- conhost.exe (PID: 62000)
- conhost.exe (PID: 62168)
- conhost.exe (PID: 61840)
- conhost.exe (PID: 25348)
- conhost.exe (PID: 62140)
- conhost.exe (PID: 62272)
- conhost.exe (PID: 62332)
- conhost.exe (PID: 62400)
- conhost.exe (PID: 62424)
- conhost.exe (PID: 62672)
- conhost.exe (PID: 62588)
- conhost.exe (PID: 62748)
- conhost.exe (PID: 62340)
- conhost.exe (PID: 25696)
- conhost.exe (PID: 62488)
- conhost.exe (PID: 62576)
- conhost.exe (PID: 62768)
- conhost.exe (PID: 63088)
- conhost.exe (PID: 63184)
- conhost.exe (PID: 63252)
- conhost.exe (PID: 62888)
- conhost.exe (PID: 62916)
- conhost.exe (PID: 62988)
- conhost.exe (PID: 63080)
- conhost.exe (PID: 63420)
- conhost.exe (PID: 62756)
- conhost.exe (PID: 26020)
- conhost.exe (PID: 63084)
- conhost.exe (PID: 63304)
- conhost.exe (PID: 63380)
- conhost.exe (PID: 26016)
- conhost.exe (PID: 26952)
- conhost.exe (PID: 5072)
- conhost.exe (PID: 5828)
- conhost.exe (PID: 63264)
- conhost.exe (PID: 26784)
- conhost.exe (PID: 27572)
- conhost.exe (PID: 63256)
- conhost.exe (PID: 4076)
- conhost.exe (PID: 5856)
- conhost.exe (PID: 28660)
- conhost.exe (PID: 27672)
- conhost.exe (PID: 63704)
- conhost.exe (PID: 63504)
- conhost.exe (PID: 63560)
- conhost.exe (PID: 63544)
- conhost.exe (PID: 63712)
- conhost.exe (PID: 63776)
- conhost.exe (PID: 64016)
- conhost.exe (PID: 64120)
- conhost.exe (PID: 64092)
- conhost.exe (PID: 63848)
- conhost.exe (PID: 63832)
- conhost.exe (PID: 63924)
- conhost.exe (PID: 63976)
- conhost.exe (PID: 64140)
- conhost.exe (PID: 64404)
- conhost.exe (PID: 64396)
- conhost.exe (PID: 29420)
- conhost.exe (PID: 64232)
- conhost.exe (PID: 64304)
- conhost.exe (PID: 64256)
- conhost.exe (PID: 64380)
- conhost.exe (PID: 30480)
- conhost.exe (PID: 30516)
- conhost.exe (PID: 30484)
- conhost.exe (PID: 63980)
- conhost.exe (PID: 31180)
- conhost.exe (PID: 29300)
- conhost.exe (PID: 63792)
- conhost.exe (PID: 29324)
- conhost.exe (PID: 64716)
- conhost.exe (PID: 64920)
- conhost.exe (PID: 64756)
- conhost.exe (PID: 64928)
- conhost.exe (PID: 65016)
- conhost.exe (PID: 64580)
- conhost.exe (PID: 64616)
- conhost.exe (PID: 64748)
- conhost.exe (PID: 65184)
- conhost.exe (PID: 65264)
- conhost.exe (PID: 65328)
- conhost.exe (PID: 65100)
- conhost.exe (PID: 65160)
- conhost.exe (PID: 65356)
- conhost.exe (PID: 31560)
- conhost.exe (PID: 64752)
- conhost.exe (PID: 65180)
- conhost.exe (PID: 65428)
- conhost.exe (PID: 65456)
- conhost.exe (PID: 65512)
- conhost.exe (PID: 64624)
- conhost.exe (PID: 31616)
- conhost.exe (PID: 32720)
- conhost.exe (PID: 32428)
- conhost.exe (PID: 32156)
- conhost.exe (PID: 65492)
- conhost.exe (PID: 32904)
- conhost.exe (PID: 65580)
- conhost.exe (PID: 65800)
- conhost.exe (PID: 66020)
- conhost.exe (PID: 65572)
- conhost.exe (PID: 65680)
- conhost.exe (PID: 65752)
- conhost.exe (PID: 65856)
- conhost.exe (PID: 65692)
- conhost.exe (PID: 34116)
- conhost.exe (PID: 65932)
- conhost.exe (PID: 66132)
- conhost.exe (PID: 66300)
- conhost.exe (PID: 66484)
- conhost.exe (PID: 65596)
- conhost.exe (PID: 65524)
- conhost.exe (PID: 65416)
- conhost.exe (PID: 65184)
- conhost.exe (PID: 65044)
- conhost.exe (PID: 32288)
- conhost.exe (PID: 32024)
- conhost.exe (PID: 66376)
- conhost.exe (PID: 26608)
- conhost.exe (PID: 63496)
- conhost.exe (PID: 64780)
- conhost.exe (PID: 26016)
- conhost.exe (PID: 64340)
- conhost.exe (PID: 66412)
- conhost.exe (PID: 63752)
- conhost.exe (PID: 25692)
- conhost.exe (PID: 23648)
- conhost.exe (PID: 65684)
- conhost.exe (PID: 62852)
- conhost.exe (PID: 24492)
- conhost.exe (PID: 62096)
- conhost.exe (PID: 61704)
- conhost.exe (PID: 22220)
- conhost.exe (PID: 60176)
- conhost.exe (PID: 64720)
- conhost.exe (PID: 65276)
- conhost.exe (PID: 60884)
- conhost.exe (PID: 61176)
- conhost.exe (PID: 60804)
- conhost.exe (PID: 65348)
- conhost.exe (PID: 64800)
- conhost.exe (PID: 20224)
- conhost.exe (PID: 57964)
- conhost.exe (PID: 57444)
- conhost.exe (PID: 64412)
- conhost.exe (PID: 57752)
- conhost.exe (PID: 66328)
- conhost.exe (PID: 59008)
- conhost.exe (PID: 18376)
- conhost.exe (PID: 57096)
- conhost.exe (PID: 56324)
- conhost.exe (PID: 57544)
- conhost.exe (PID: 19032)
- conhost.exe (PID: 56740)
- conhost.exe (PID: 56152)
- conhost.exe (PID: 4076)
- conhost.exe (PID: 15732)
- conhost.exe (PID: 17668)
- conhost.exe (PID: 56196)
- conhost.exe (PID: 34292)
- conhost.exe (PID: 55760)
- conhost.exe (PID: 63296)
- conhost.exe (PID: 54492)
- conhost.exe (PID: 54752)
- conhost.exe (PID: 11640)
- conhost.exe (PID: 14208)
- conhost.exe (PID: 54920)
- conhost.exe (PID: 63432)
- conhost.exe (PID: 54052)
- conhost.exe (PID: 62540)
- conhost.exe (PID: 65884)
- conhost.exe (PID: 53184)
- conhost.exe (PID: 10824)
- conhost.exe (PID: 36360)
- conhost.exe (PID: 52284)
- conhost.exe (PID: 51908)
- conhost.exe (PID: 8548)
- conhost.exe (PID: 51992)
- conhost.exe (PID: 52932)
- conhost.exe (PID: 61780)
- conhost.exe (PID: 51852)
- conhost.exe (PID: 51012)
- conhost.exe (PID: 61132)
- conhost.exe (PID: 50416)
- conhost.exe (PID: 34480)
- conhost.exe (PID: 32720)
- conhost.exe (PID: 61104)
- conhost.exe (PID: 51068)
- conhost.exe (PID: 49076)
- conhost.exe (PID: 48840)
- conhost.exe (PID: 50128)
- conhost.exe (PID: 66280)
- conhost.exe (PID: 59636)
- conhost.exe (PID: 36096)
- conhost.exe (PID: 36932)
- conhost.exe (PID: 43560)
- conhost.exe (PID: 47896)
- conhost.exe (PID: 59884)
- conhost.exe (PID: 47820)
- conhost.exe (PID: 48536)
- conhost.exe (PID: 60216)
- conhost.exe (PID: 47628)
- conhost.exe (PID: 46768)
- conhost.exe (PID: 46444)
- conhost.exe (PID: 60136)
- conhost.exe (PID: 22368)
- conhost.exe (PID: 46504)
- conhost.exe (PID: 46932)
- conhost.exe (PID: 45340)
- conhost.exe (PID: 37736)
- conhost.exe (PID: 58432)
- conhost.exe (PID: 58408)
- conhost.exe (PID: 46240)
- conhost.exe (PID: 46020)
- conhost.exe (PID: 58884)
- conhost.exe (PID: 37656)
- conhost.exe (PID: 19816)
- conhost.exe (PID: 43984)
- conhost.exe (PID: 43188)
- conhost.exe (PID: 43576)
- conhost.exe (PID: 44476)
- conhost.exe (PID: 44260)
- conhost.exe (PID: 20384)
- conhost.exe (PID: 41536)
- conhost.exe (PID: 42388)
- conhost.exe (PID: 57372)
- conhost.exe (PID: 64168)
- conhost.exe (PID: 20976)
- conhost.exe (PID: 43052)
- conhost.exe (PID: 38044)
- conhost.exe (PID: 57748)
- conhost.exe (PID: 18972)
- conhost.exe (PID: 57012)
- conhost.exe (PID: 38528)
- conhost.exe (PID: 40580)
- conhost.exe (PID: 40528)
- conhost.exe (PID: 38844)
- conhost.exe (PID: 40080)
- conhost.exe (PID: 41256)
- conhost.exe (PID: 39892)
- conhost.exe (PID: 38164)
- conhost.exe (PID: 55796)
- conhost.exe (PID: 37500)
- conhost.exe (PID: 39660)
- conhost.exe (PID: 56304)
- conhost.exe (PID: 38428)
- conhost.exe (PID: 38416)
- conhost.exe (PID: 13428)
- conhost.exe (PID: 35672)
- conhost.exe (PID: 37508)
- conhost.exe (PID: 37252)
- conhost.exe (PID: 36792)
- conhost.exe (PID: 36484)
- conhost.exe (PID: 33812)
- conhost.exe (PID: 34412)
- conhost.exe (PID: 39692)
- conhost.exe (PID: 32572)
- conhost.exe (PID: 39428)
- conhost.exe (PID: 35484)
- conhost.exe (PID: 34980)
- conhost.exe (PID: 55044)
- conhost.exe (PID: 32988)
- conhost.exe (PID: 33304)
- conhost.exe (PID: 65876)
Starts a Microsoft application from unusual location
- ViraBot.exe (PID: 4072)
Process drops legitimate windows executable
- ViraBot.exe (PID: 4072)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1576)
INFO
The sample compiled with english language support
- ViraBot.exe (PID: 4072)
Checks supported languages
- ViraBot.exe (PID: 4072)
Reads the computer name
- ViraBot.exe (PID: 4072)
Create files in a temporary directory
- ViraBot.exe (PID: 4072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2001:11:17 14:11:13+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 40960 |
| InitializedDataSize: | 139264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1300 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.26100.1 |
| ProductVersionNumber: | 11.0.26100.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.26100.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.26100.1 |
Total processes
3 287
Monitored processes
3 154
Malicious processes
1 529
Suspicious processes
1 546
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\WINDOWS\system32\cmd.exe /c 1.bat | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | powershell -WindowStyle Hidden -Command "& {Start-Process 'C:\Users\admin\1.bat'}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | conhost --headless 1.bat | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | C:\WINDOWS\system32\cmd.exe /c 1.bat | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | C:\WINDOWS\system32\cmd.exe /c 1.bat | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | C:\WINDOWS\system32\cmd.exe /c 1.bat | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1392 | conhost --headless 1.bat | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | conhost --headless 1.bat | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1576 | cmd /c main.bat | C:\Windows\System32\cmd.exe | — | ViraBot.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1816 | C:\WINDOWS\system32\cmd.exe /c 1.bat | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
50 796
Read events
50 796
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4072 | ViraBot.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\main.bat | text | |
MD5:92039EC0BB849975D09F83B0377333D9 | SHA256:9CA7F91CB7893927C19494AEC1523D5217650673DC657FF915E057A97DF837E5 | |||
| 2148 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_udyrmoae.u2q.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2148 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B74B2BF3AF92B172D424C5848CC70210 | SHA256:237B9014A63A1537CD29A96E313D8EE732396BFD0453F5C8FFBDDE4877371657 | |||
| 2148 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ejaeoltj.bmq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1576 | cmd.exe | C:\Users\admin\1.bat | text | |
MD5:ABD16D70AD03629282B104C183F1A3B5 | SHA256:E713845B09EF58C7A0E10AB7723087A9966766E5827CB39544EDBD29EE28429F | |||
| 8604 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_azwprq3o.adf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8604 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5q3utbz2.yea.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 436 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_clrsfxgd.haj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 436 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tewn5lpp.hix.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
21
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
43312 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
43312 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
43312 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | DE | binary | 824 b | whitelisted |
43312 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | DE | binary | 400 b | whitelisted |
43312 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | DE | binary | 813 b | whitelisted |
43312 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | DE | binary | 401 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
43312 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
6760 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6760 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6760 | svchost.exe | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |