| File name: | NL DB.zip |
| Full analysis: | https://app.any.run/tasks/d7a1ec6b-eb48-4d14-8c52-9934c7ea0087 |
| Verdict: | Malicious activity |
| Analysis date: | December 28, 2020, 08:23:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 159527885D529407044A91E6545FB10A |
| SHA1: | 4F2C21B6D3E33507C86D9527D47E04554B1EFF60 |
| SHA256: | A2105BBDB272093DB7F95AC41BD88716D3A727D112A3C20BCD7387BE363352D0 |
| SSDEEP: | 393216:RsBYrENFxIeFVYZ0KiUwdN8Pl1fxR37Y2fG6w8dVk:2BY0JWZ0Kipdazh+juy |
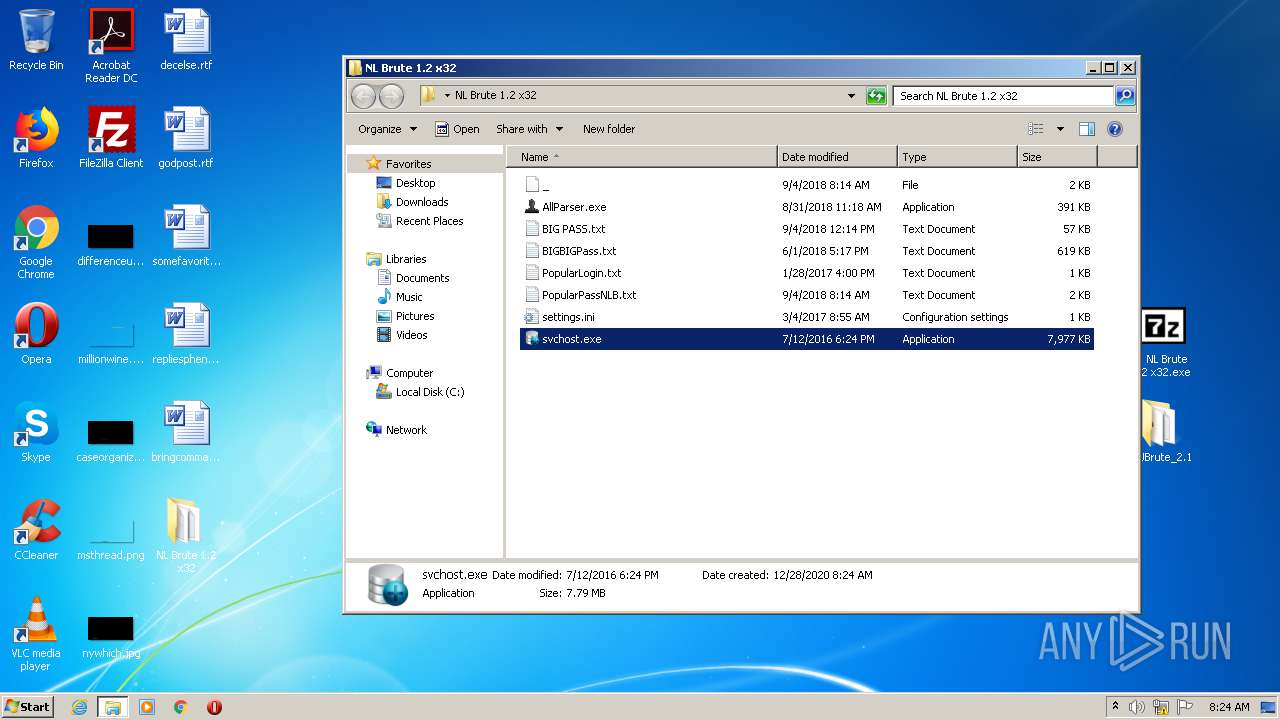
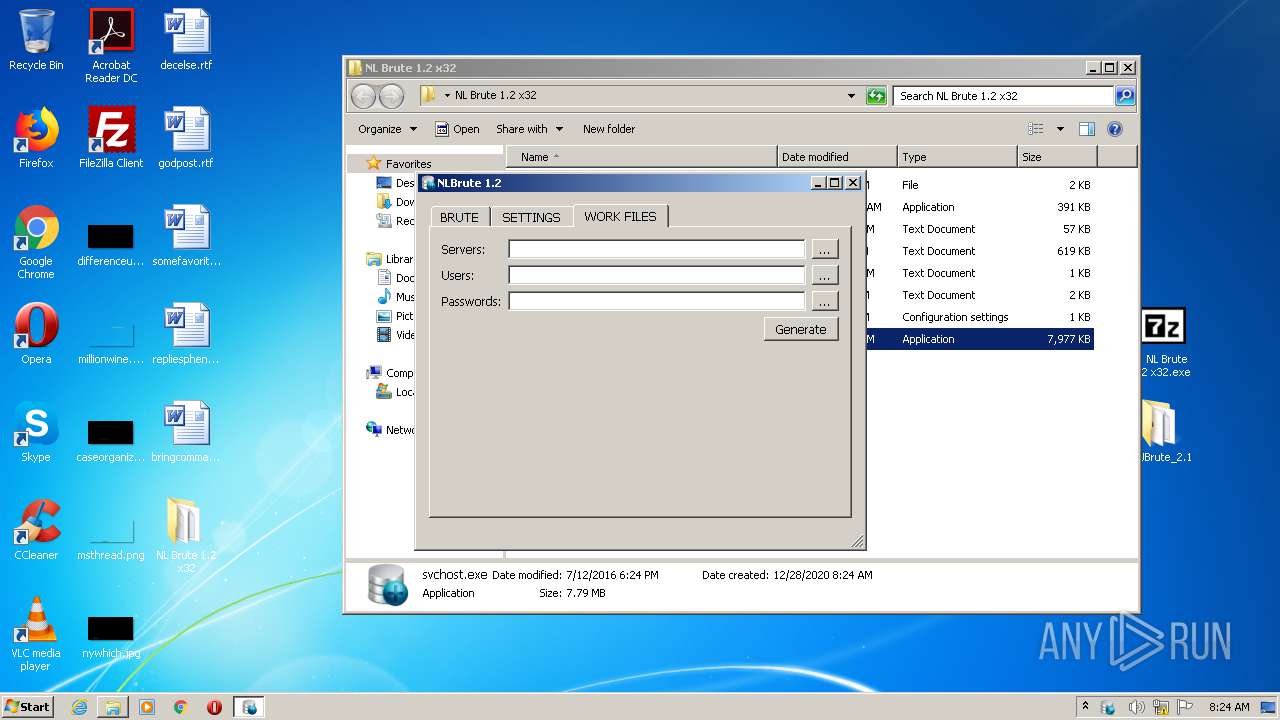
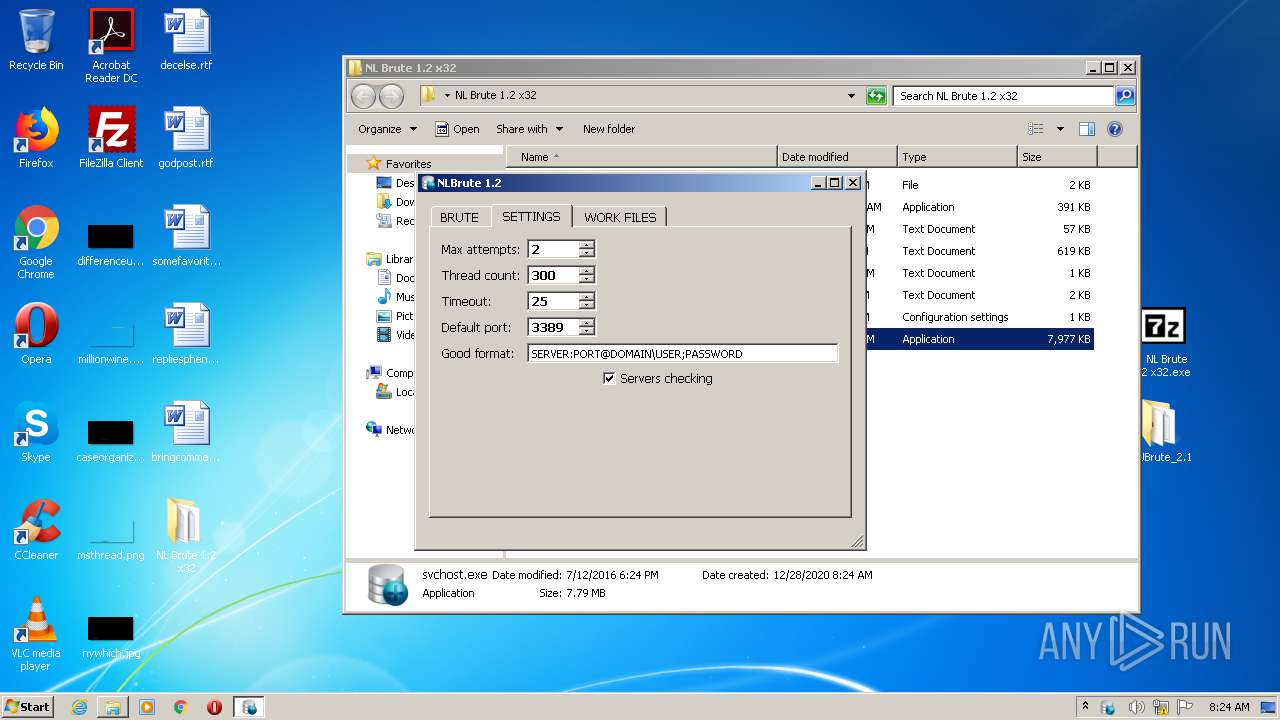
MALICIOUS
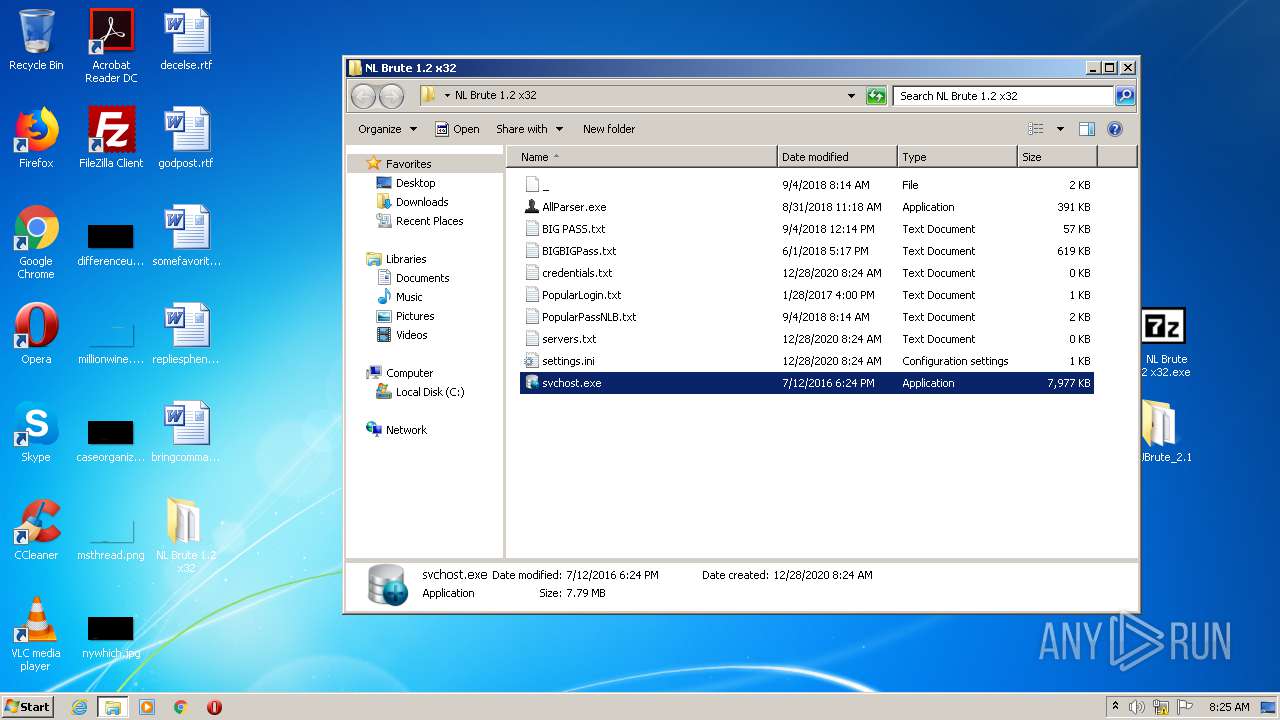
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3536)
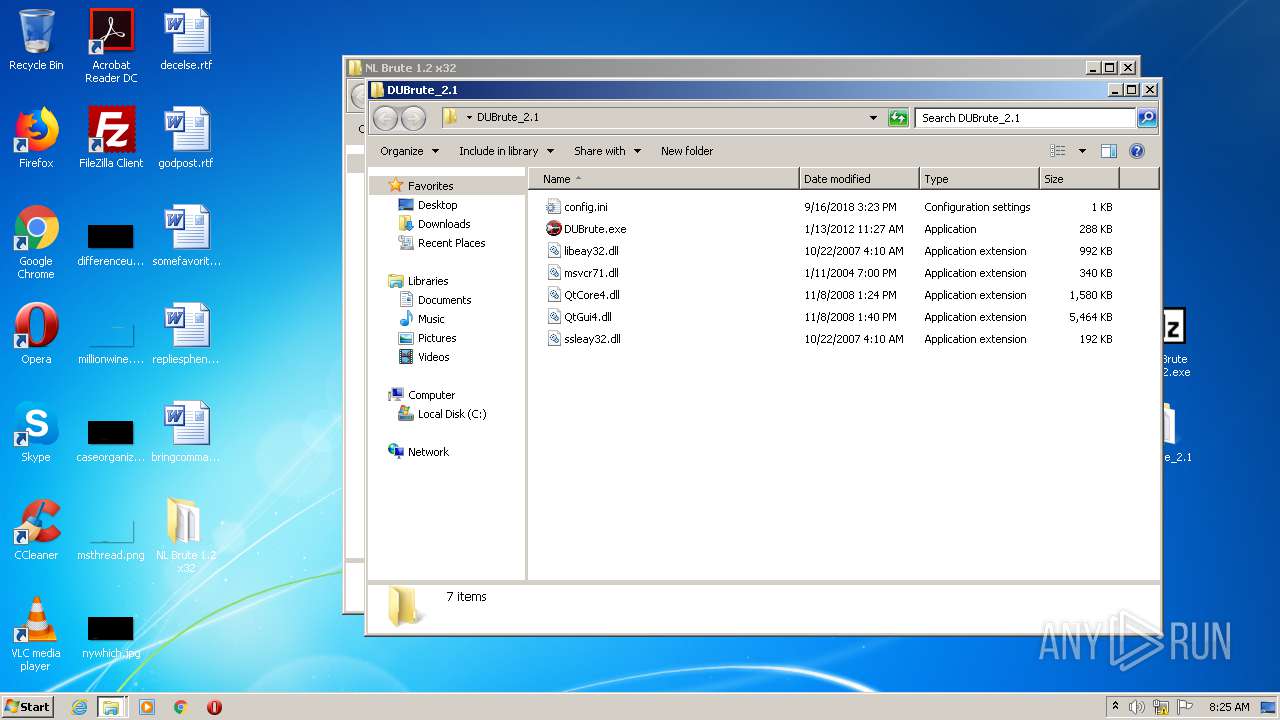
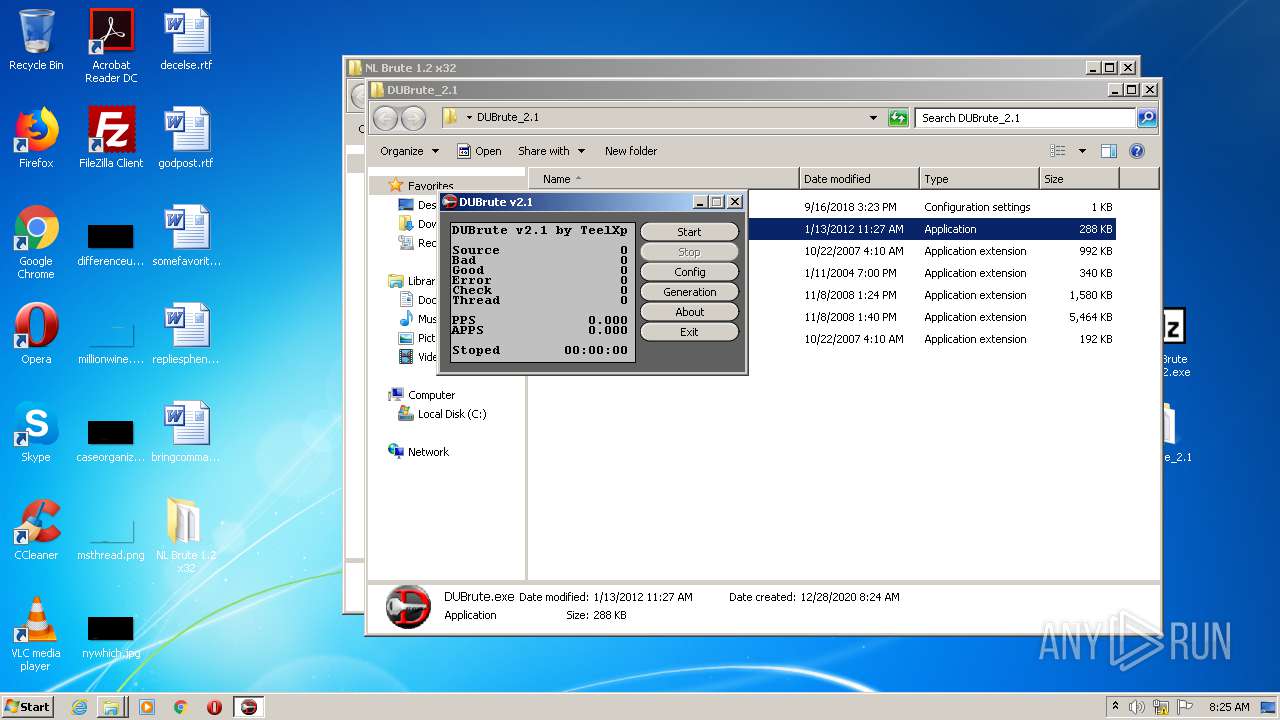
- DUBrute.exe (PID: 1844)
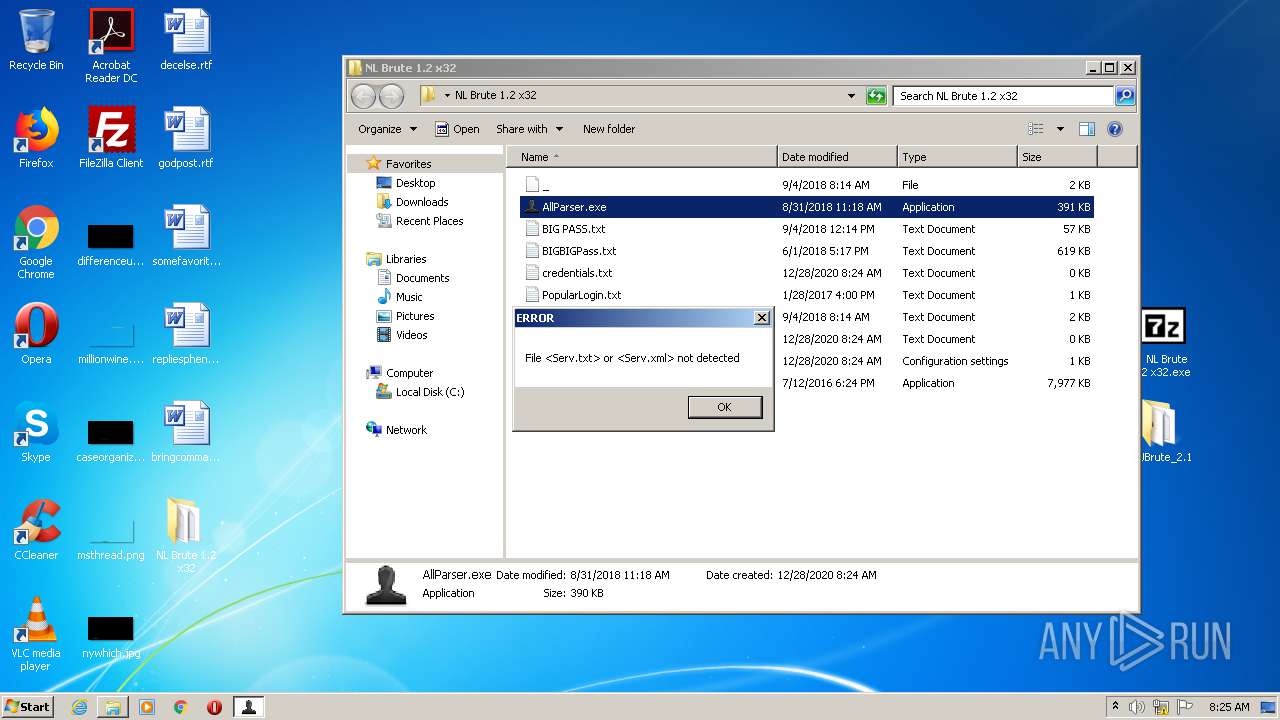
Application was dropped or rewritten from another process
- AllParser.exe (PID: 2576)
- svchost.exe (PID: 3664)
- 4. NL Brute 1.2 x32.exe (PID: 312)
- DUBrute.exe (PID: 1844)
SUSPICIOUS
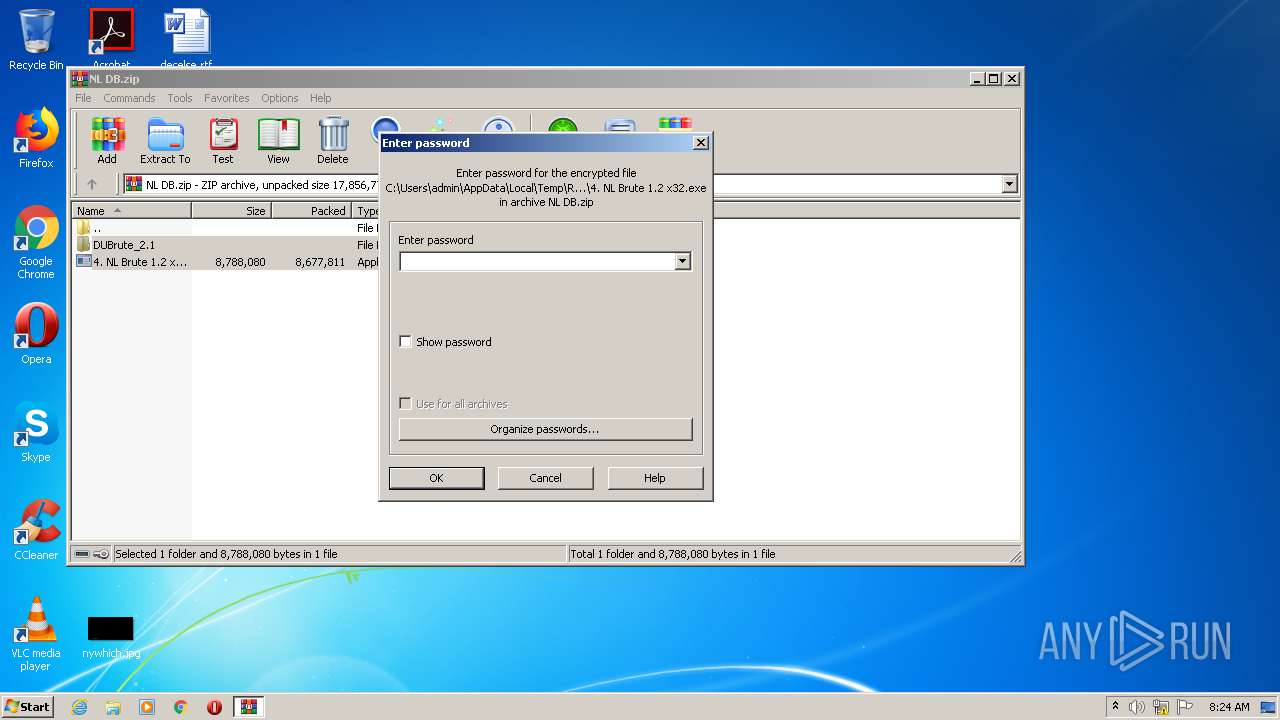
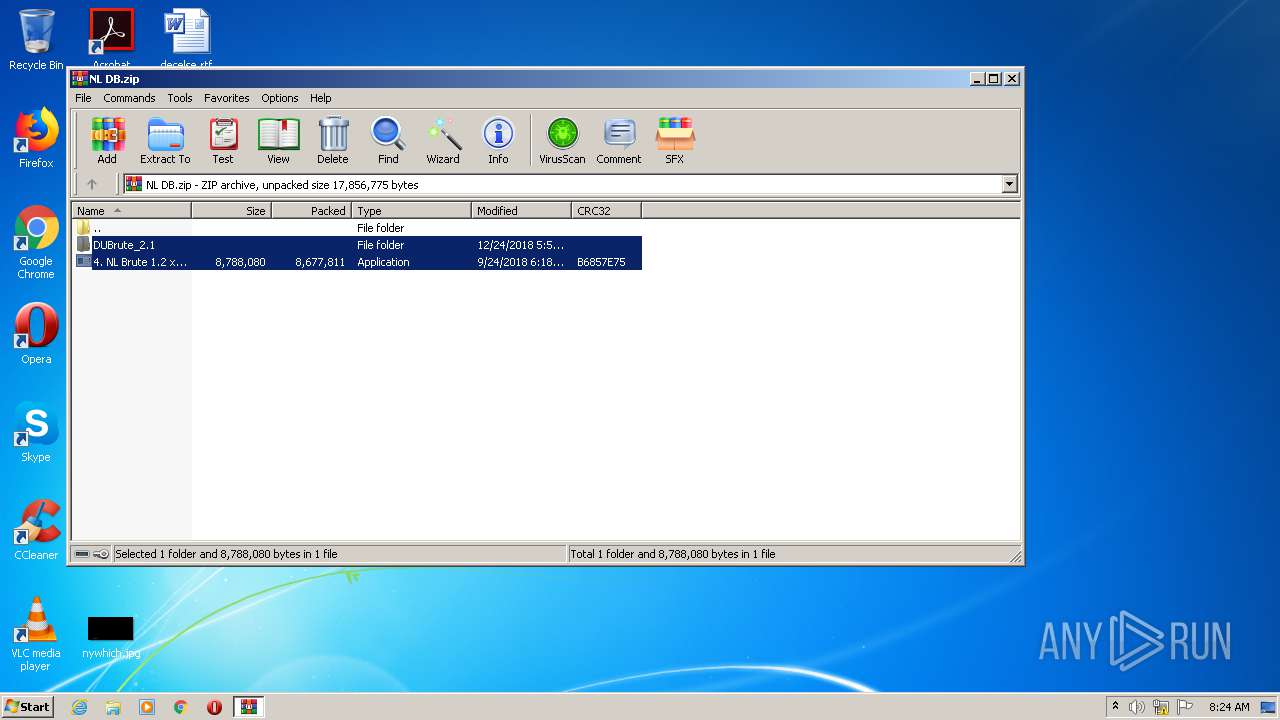
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2568)
- 4. NL Brute 1.2 x32.exe (PID: 312)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2568)
Drops a file with too old compile date
- WinRAR.exe (PID: 2568)
Creates executable files which already exist in Windows
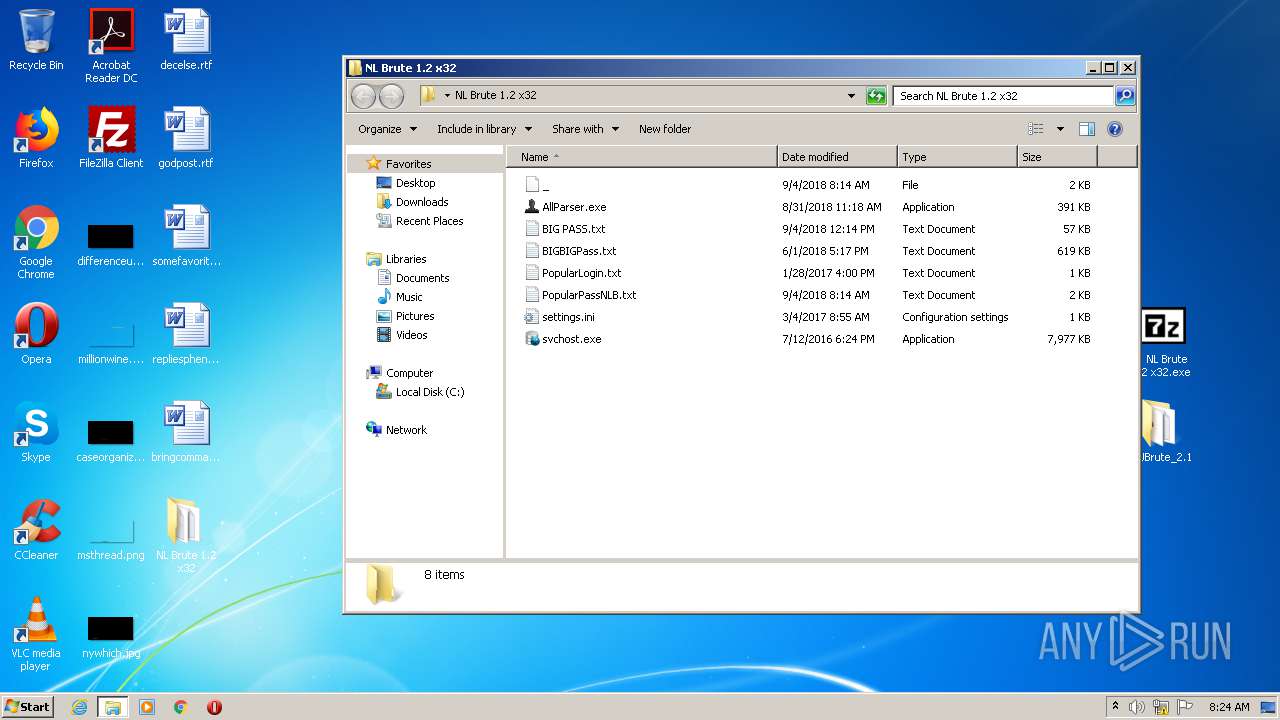
- 4. NL Brute 1.2 x32.exe (PID: 312)
INFO
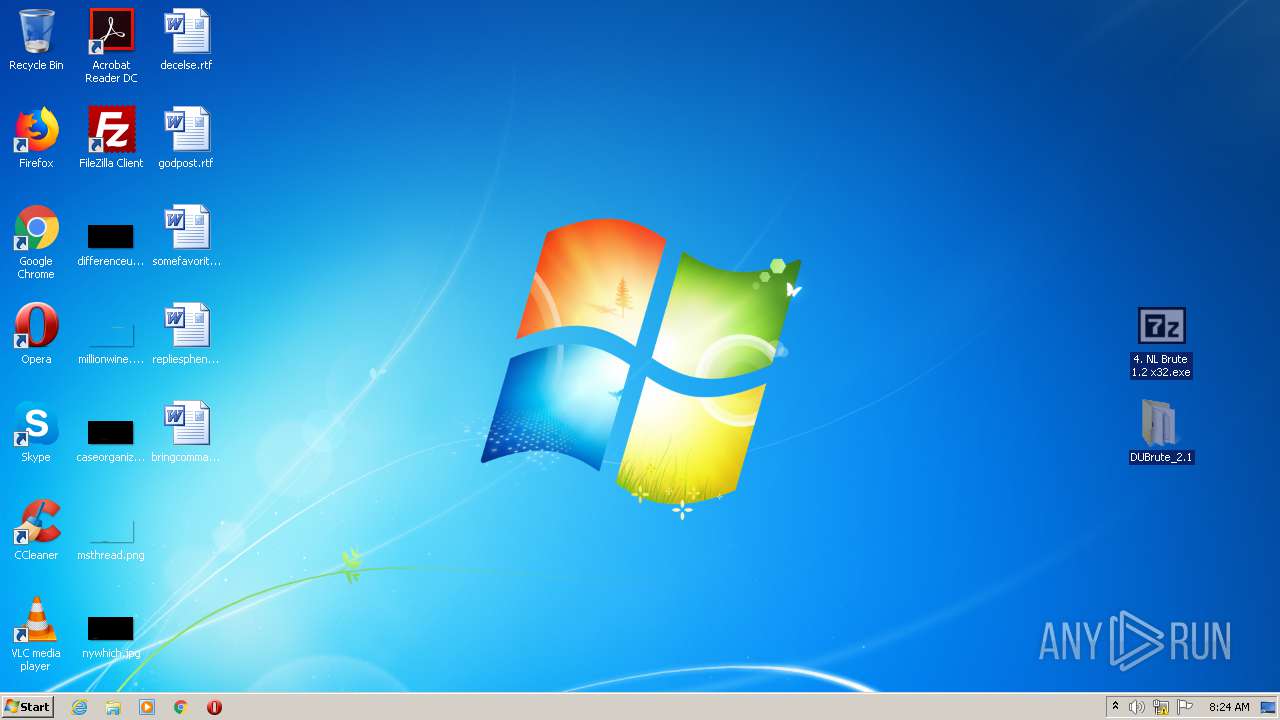
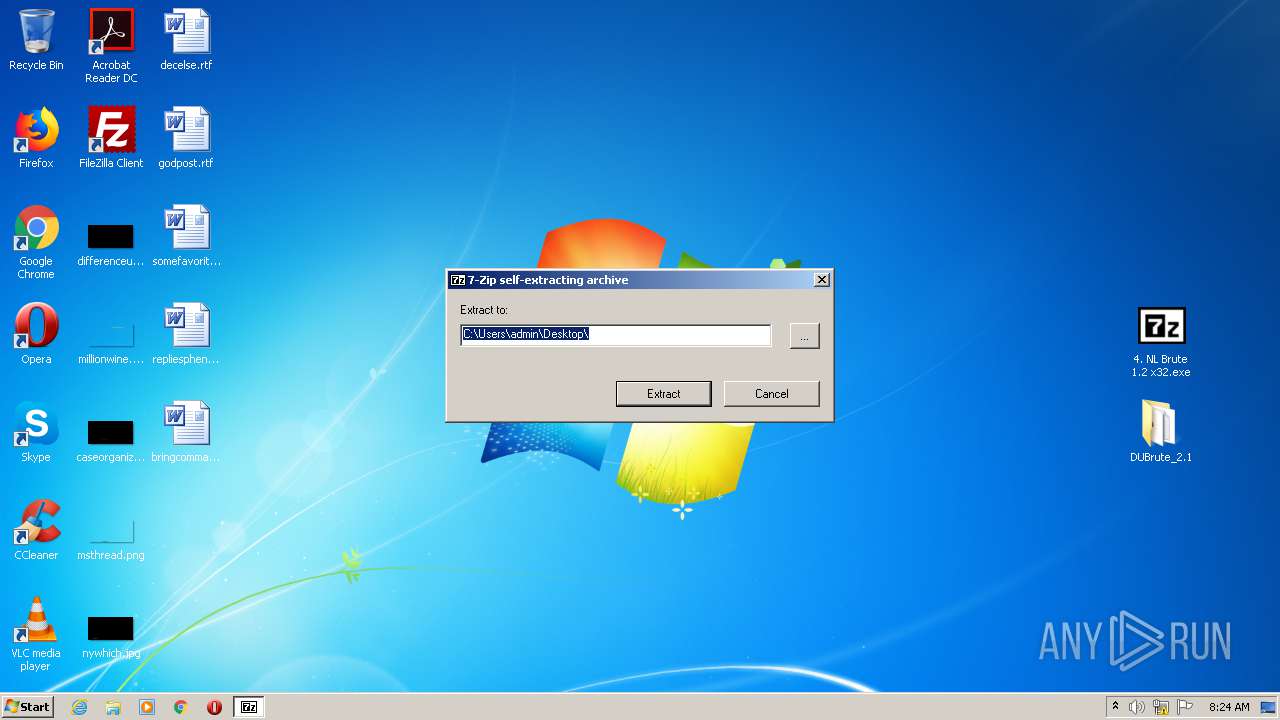
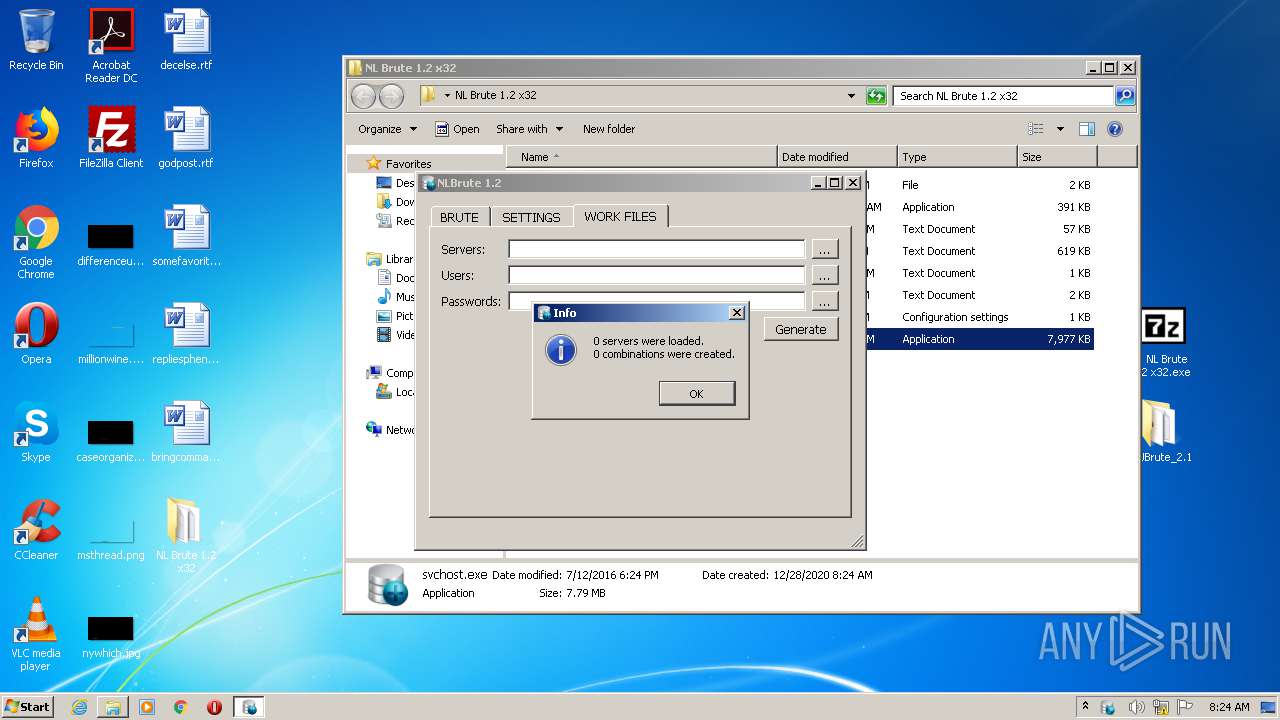
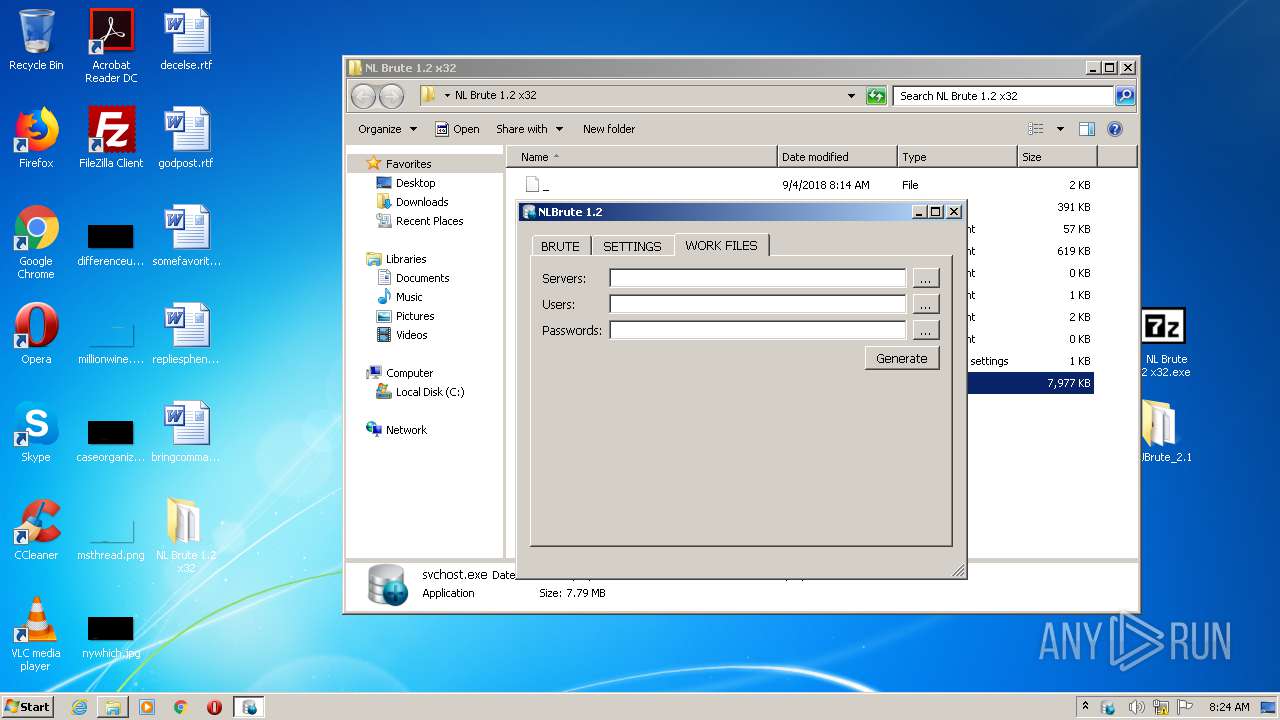
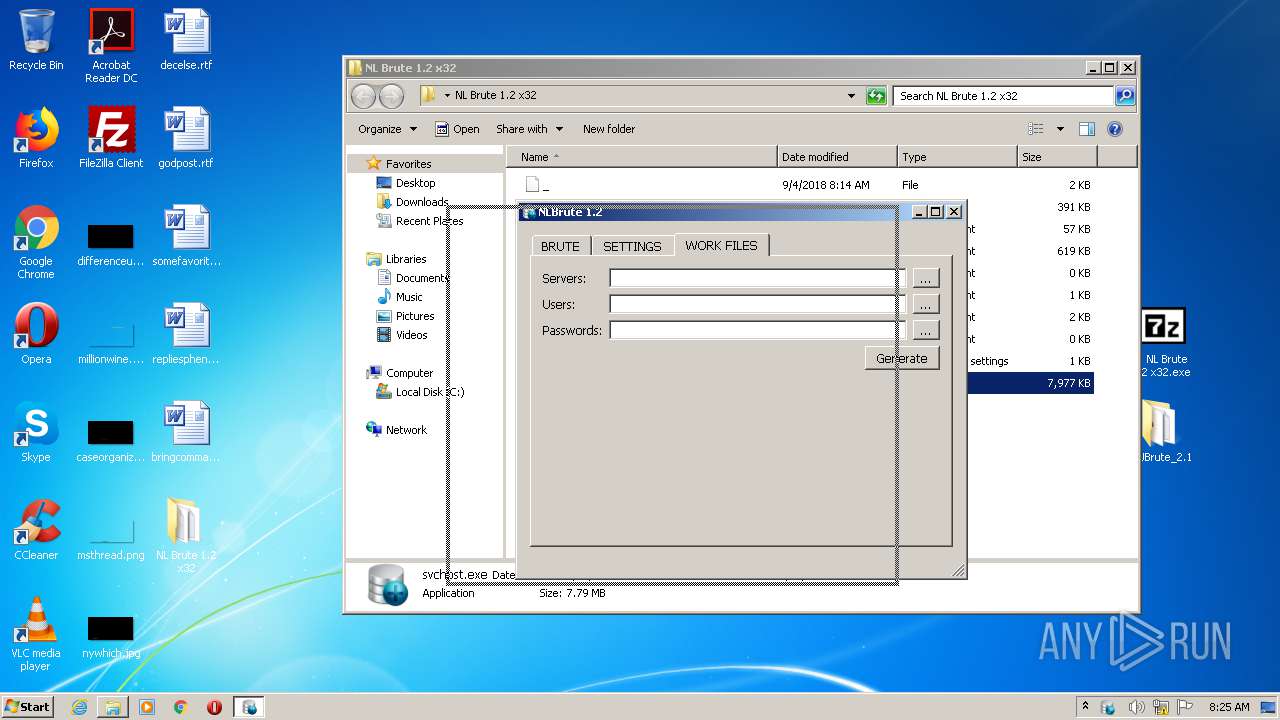
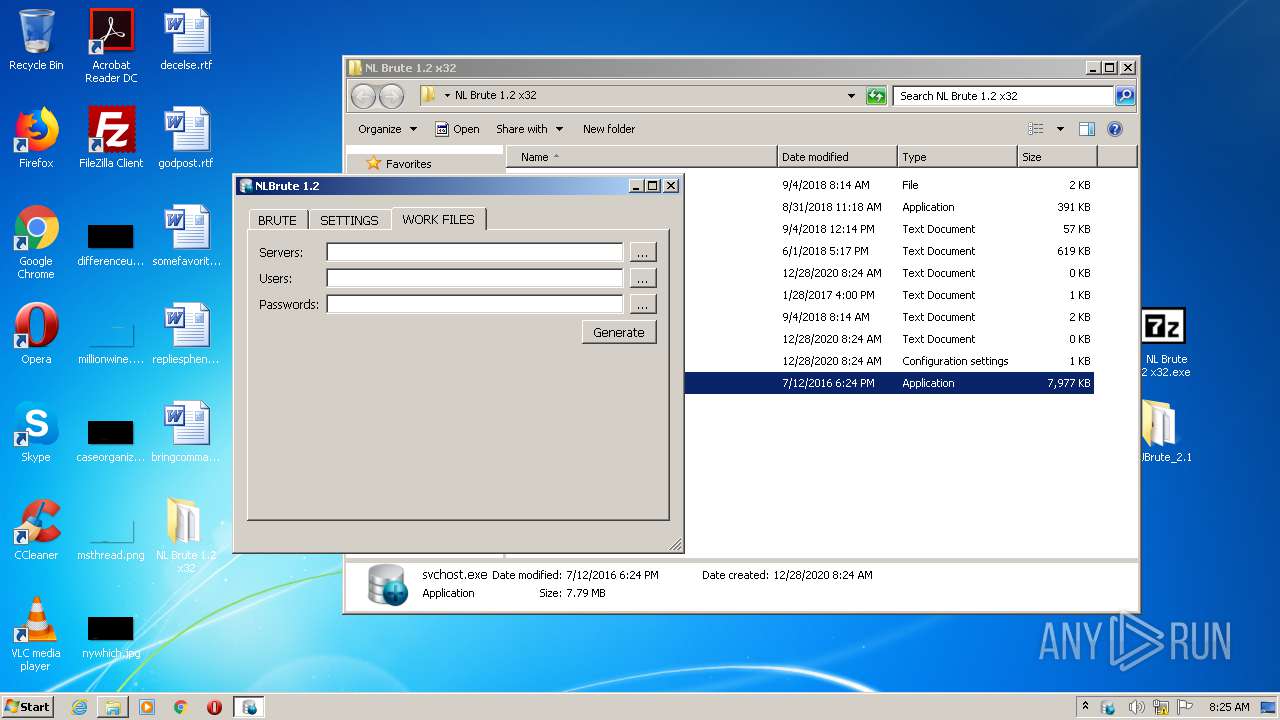
Manual execution by user
- 4. NL Brute 1.2 x32.exe (PID: 312)
- svchost.exe (PID: 3664)
- DUBrute.exe (PID: 1844)
- AllParser.exe (PID: 2576)
Dropped object may contain Bitcoin addresses
- 4. NL Brute 1.2 x32.exe (PID: 312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
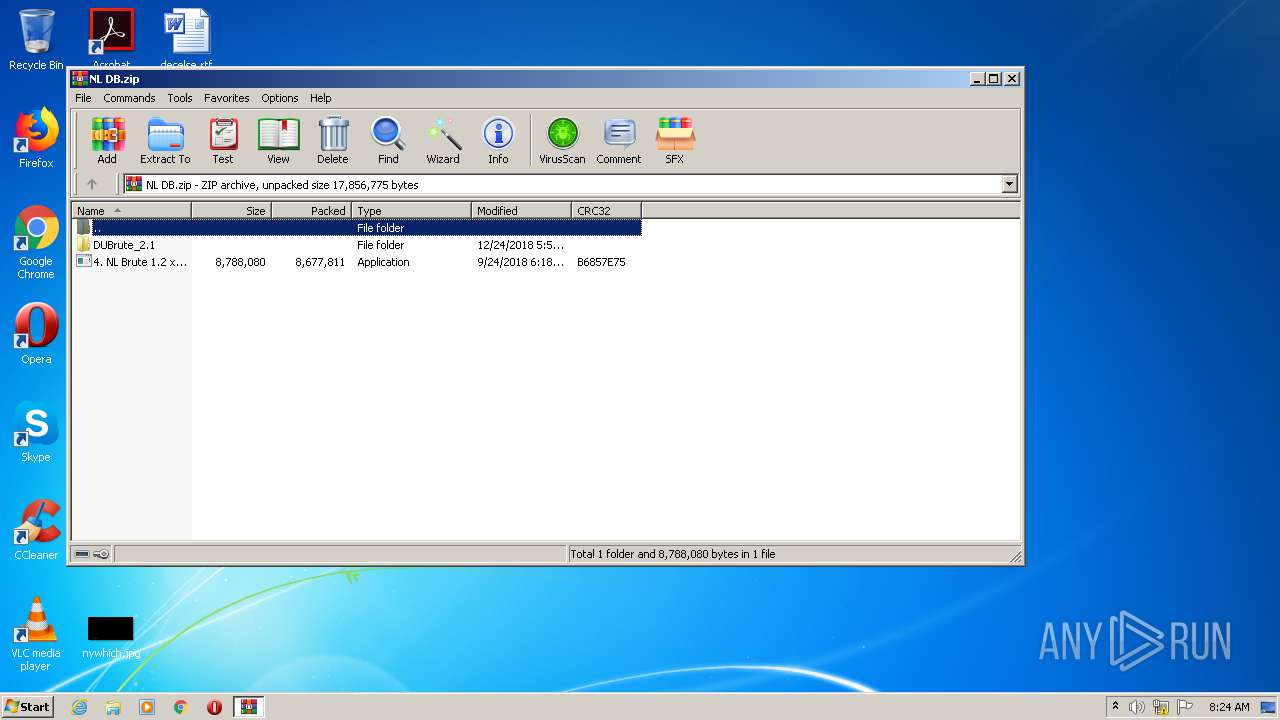
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:09:24 20:18:02 |
| ZipCRC: | 0xb6857e75 |
| ZipCompressedSize: | 8677811 |
| ZipUncompressedSize: | 8788080 |
| ZipFileName: | 4. NL Brute 1.2 x32.exe |
Total processes
44
Monitored processes
6
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\Desktop\4. NL Brute 1.2 x32.exe" | C:\Users\admin\Desktop\4. NL Brute 1.2 x32.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z SFX Exit code: 0 Version: 18.05 Modules
| |||||||||||||||
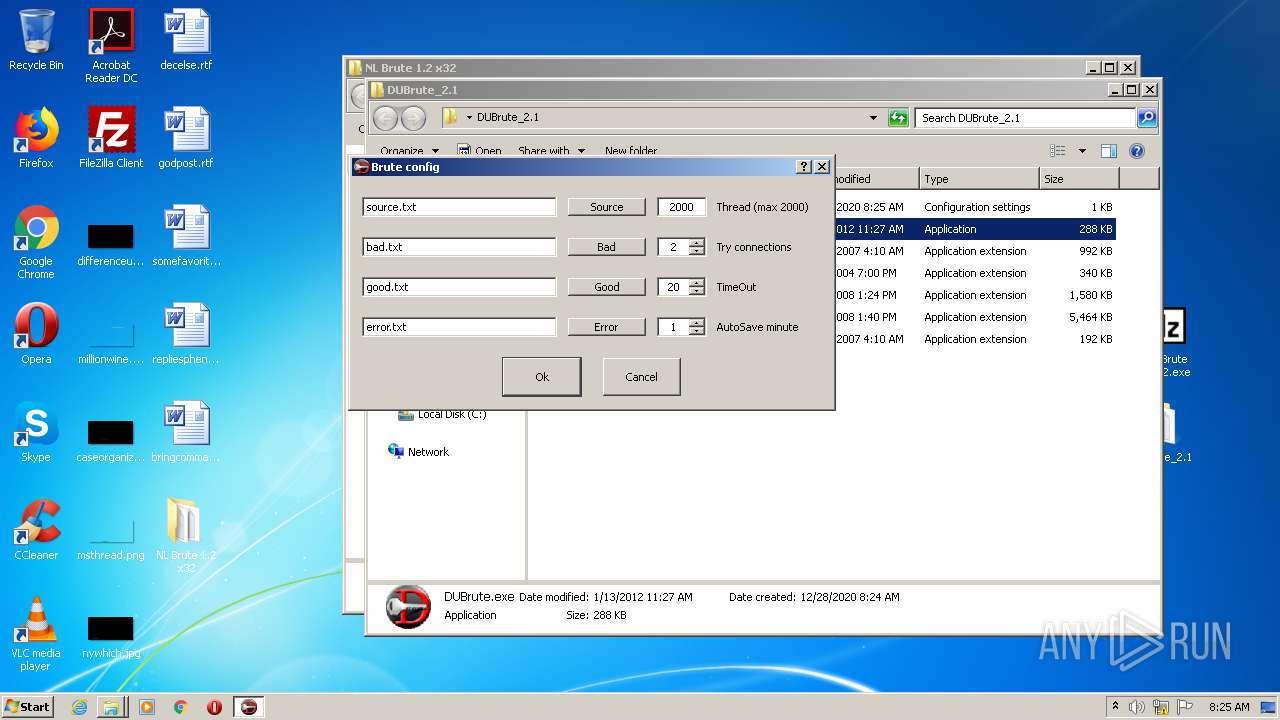
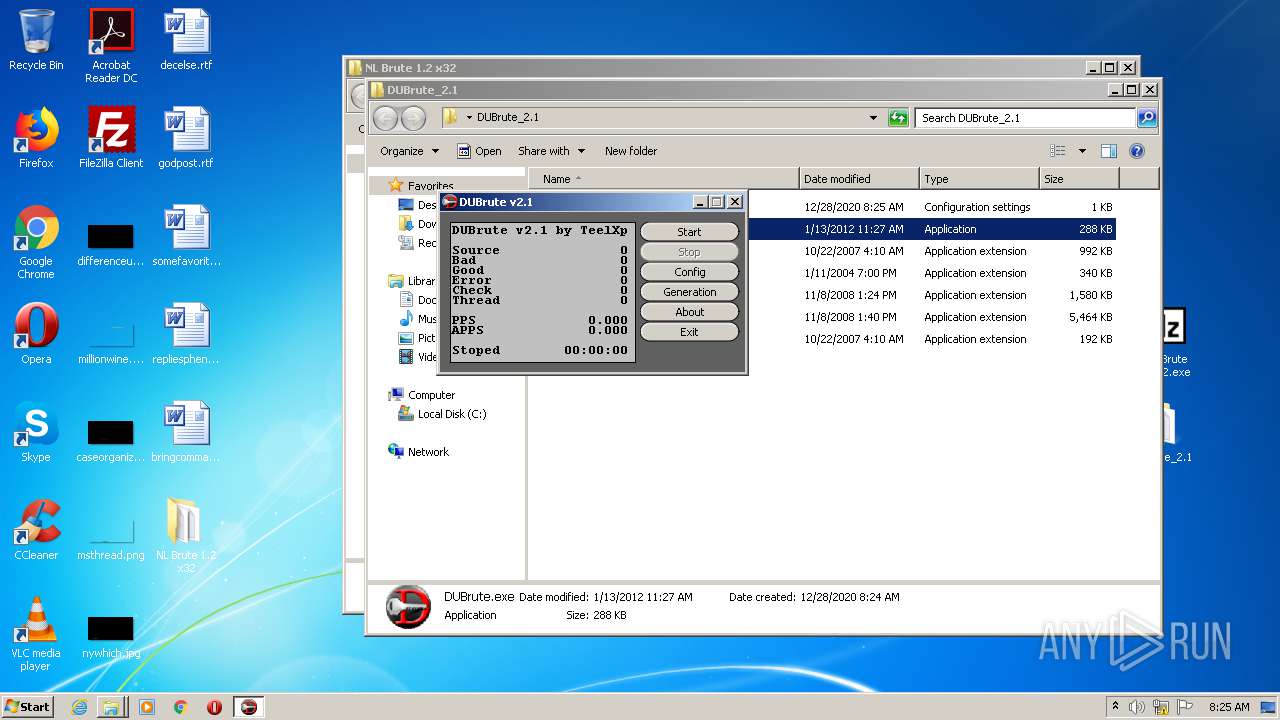
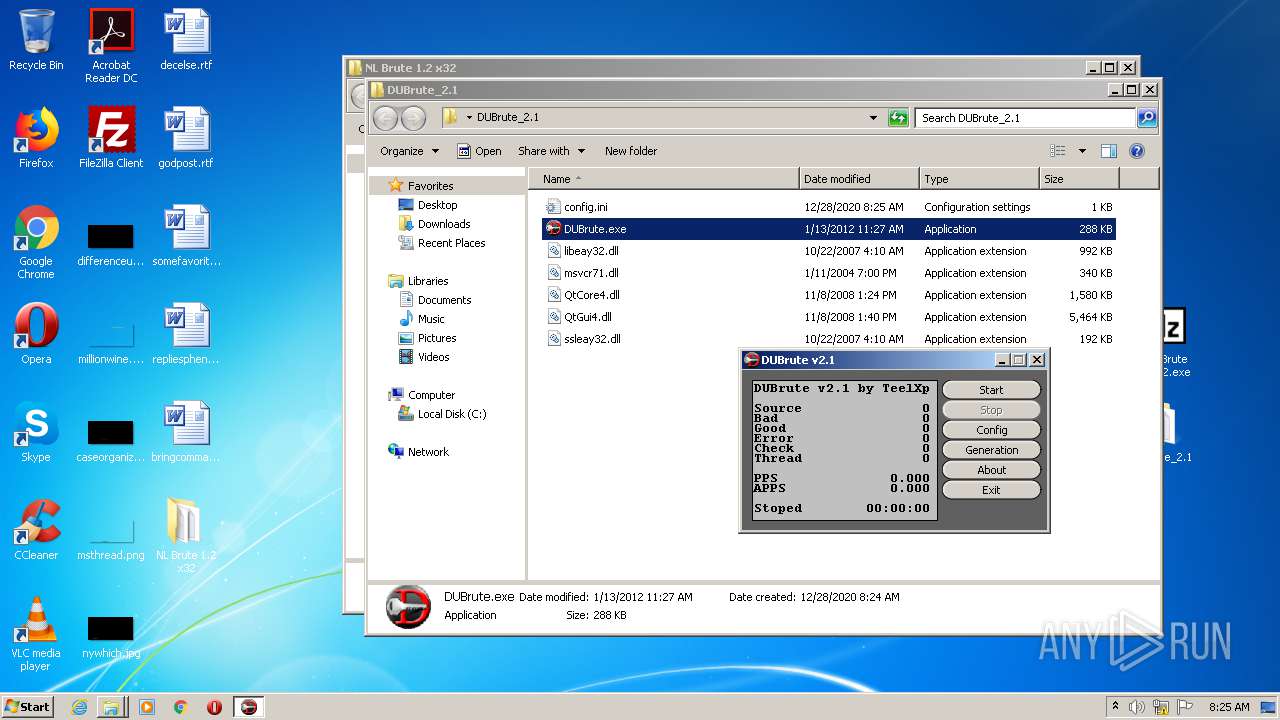
| 1844 | "C:\Users\admin\Desktop\DUBrute_2.1\DUBrute.exe" | C:\Users\admin\Desktop\DUBrute_2.1\DUBrute.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NL DB.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\Desktop\NL Brute 1.2 x32\AllParser.exe" | C:\Users\admin\Desktop\NL Brute 1.2 x32\AllParser.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Server Parser Exit code: 0 Version: 6.3.9600.16385 Modules
| |||||||||||||||
| 3536 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Users\admin\Desktop\NL Brute 1.2 x32\svchost.exe" | C:\Users\admin\Desktop\NL Brute 1.2 x32\svchost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
Total events
809
Read events
787
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NL DB.zip | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2568) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
7
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2568.17622\DUBrute_2.1\QtGui4.dll | — | |
MD5:— | SHA256:— | |||
| 2568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2568.17622\DUBrute_2.1\ssleay32.dll | — | |
MD5:— | SHA256:— | |||
| 3664 | svchost.exe | C:\Users\admin\Desktop\NL Brute 1.2 x32\servers.txt | — | |
MD5:— | SHA256:— | |||
| 3664 | svchost.exe | C:\Users\admin\Desktop\NL Brute 1.2 x32\credentials.txt | — | |
MD5:— | SHA256:— | |||
| 2568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2568.17622\DUBrute_2.1\DUBrute.exe | executable | |
MD5:— | SHA256:— | |||
| 312 | 4. NL Brute 1.2 x32.exe | C:\Users\admin\Desktop\NL Brute 1.2 x32\_ | text | |
MD5:— | SHA256:— | |||
| 312 | 4. NL Brute 1.2 x32.exe | C:\Users\admin\Desktop\NL Brute 1.2 x32\settings.ini | text | |
MD5:— | SHA256:— | |||
| 312 | 4. NL Brute 1.2 x32.exe | C:\Users\admin\Desktop\NL Brute 1.2 x32\BIGBIGPass.txt | binary | |
MD5:— | SHA256:— | |||
| 312 | 4. NL Brute 1.2 x32.exe | C:\Users\admin\Desktop\NL Brute 1.2 x32\BIG PASS.txt | text | |
MD5:— | SHA256:— | |||
| 2568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2568.17622\DUBrute_2.1\msvcr71.dll | executable | |
MD5:86F1895AE8C5E8B17D99ECE768A70732 | SHA256:8094AF5EE310714CAEBCCAEEE7769FFB08048503BA478B879EDFEF5F1A24FEFE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
svchost.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
svchost.exe | QFSFileEngine::open: No file name specified
|
svchost.exe | QFSFileEngine::open: No file name specified
|
svchost.exe | QFSFileEngine::open: No file name specified
|