| File name: | TouchEn_nxKey_32bit.exe |
| Full analysis: | https://app.any.run/tasks/6d69aa81-be36-409d-9388-d20eaf2f22aa |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2020, 07:24:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | ABE9C96947DBE01AD7AF198154FC01C2 |
| SHA1: | 0F6BD02FE0E46F9477D5E3A1EA2ABEF21CD61B8E |
| SHA256: | A2046714E298B526EFC2E253D8BCD60253437E136AF7A1B3A78076C2214D96AB |
| SSDEEP: | 196608:KPbZGfoeKOf6ivvcCkd/AN18lYFCEseQ4+8Yk4TLRqzha20bRSa11/bRiUdfhNeI:KDZneKY7vMo18uFT64ZILRf20bZ11TRb |
MALICIOUS
Changes settings of System certificates
- CrossEX_LocalService_Install.exe (PID: 916)
Changes the autorun value in the registry
- CrossEX_LocalService_Install.exe (PID: 916)
Loads dropped or rewritten executable
- raon_touchenex_Install.exe (PID: 536)
- TouchEn_nxKey_32bit.exe (PID: 2936)
- certutil.exe (PID: 1232)
- CrossEX_LocalService_Install.exe (PID: 916)
- certutil.exe (PID: 2520)
Application was dropped or rewritten from another process
- CrossEX_LocalService_Install.exe (PID: 916)
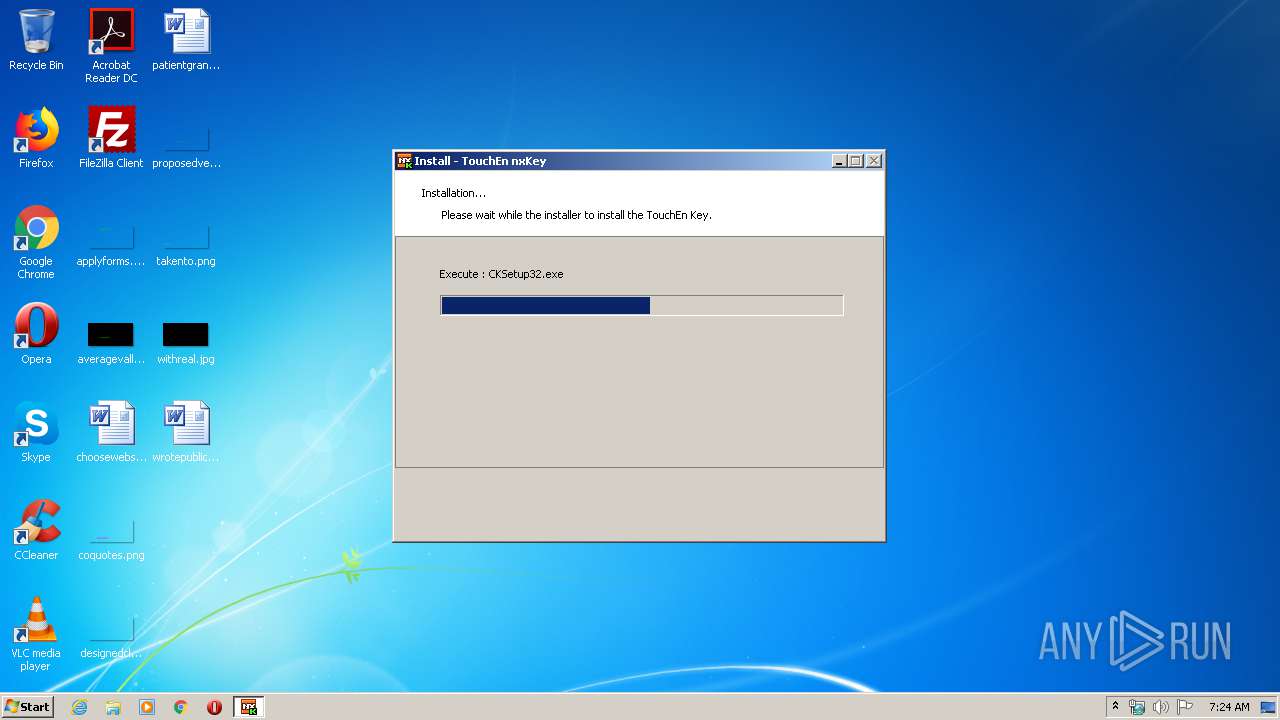
- CKSetup32.exe (PID: 3472)
- ObCrossEXService.exe (PID: 2672)
- raon_touchenex_Install.exe (PID: 536)
- CrossEXService.exe (PID: 2872)
- Firefox_CertUtil.exe (PID: 4004)
- certutil.exe (PID: 2520)
- FFCert.exe (PID: 3964)
- certutil.exe (PID: 1232)
SUSPICIOUS
Creates a software uninstall entry
- CKSetup32.exe (PID: 3472)
- CrossEX_LocalService_Install.exe (PID: 916)
- TouchEn_nxKey_32bit.exe (PID: 2936)
Creates files in the Windows directory
- TouchEn_nxKey_32bit.exe (PID: 2936)
- CKSetup32.exe (PID: 3472)
Executable content was dropped or overwritten
- CKSetup32.exe (PID: 3472)
- TouchEn_nxKey_32bit.exe (PID: 2936)
- raon_touchenex_Install.exe (PID: 536)
- CrossEX_LocalService_Install.exe (PID: 916)
- FFCert.exe (PID: 3964)
Removes files from Windows directory
- CKSetup32.exe (PID: 3472)
Creates files in the program directory
- CrossEX_LocalService_Install.exe (PID: 916)
- raon_touchenex_Install.exe (PID: 536)
- TouchEn_nxKey_32bit.exe (PID: 2936)
Creates COM task schedule object
- raon_touchenex_Install.exe (PID: 536)
- TouchEn_nxKey_32bit.exe (PID: 2936)
Starts application with an unusual extension
- CrossEX_LocalService_Install.exe (PID: 916)
Starts SC.EXE for service management
- ns849B.tmp (PID: 3148)
- ns8587.tmp (PID: 1696)
- ns85F5.tmp (PID: 3684)
Creates files in the user directory
- certutil.exe (PID: 1232)
Executed as Windows Service
- ObCrossEXService.exe (PID: 2672)
INFO
Reads settings of System Certificates
- TouchEn_nxKey_32bit.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (28.6) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (28) |
| .exe | | | Win32 EXE Yoda's Crypter (27.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.8) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:22 09:31:39+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 11472896 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 3657728 |
| EntryPoint: | 0xe6e870 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.73 |
| ProductVersionNumber: | 1.0.0.73 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | TouchEn nxKey Keyboard Protector Installer |
| CompanyName: | RaonSecure Co., Ltd. |
| FileDescription: | TouchEn nxKey Keyboard Protector Installer |
| FileVersion: | 1, 0, 0, 73 |
| InternalName: | TouchEn nxKey Installer |
| LegalCopyright: | Copyright(C)2013 RaonSecure Co., Ltd. |
| OriginalFileName: | TouchEn nxKey Installer.exe |
| ProductName: | TouchEn nxKey Installer |
| ProductVersion: | 1, 0, 0, 73 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Nov-2018 08:31:39 |
| Detected languages: |
|
| Comments: | TouchEn nxKey Keyboard Protector Installer |
| CompanyName: | RaonSecure Co., Ltd. |
| FileDescription: | TouchEn nxKey Keyboard Protector Installer |
| FileVersion: | 1, 0, 0, 73 |
| InternalName: | TouchEn nxKey Installer |
| LegalCopyright: | Copyright(C)2013 RaonSecure Co., Ltd. |
| OriginalFilename: | TouchEn nxKey Installer.exe |
| ProductName: | TouchEn nxKey Installer |
| ProductVersion: | 1, 0, 0, 73 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Nov-2018 08:31:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0037D000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0037E000 | 0x00AF1000 | 0x00AF0C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.81292 |
.rsrc | 0x00E6F000 | 0x00002000 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.54715 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05265 | 1397 | UNKNOWN | Korean - Korea | RT_MANIFEST |
12 | 7.61451 | 1274 | UNKNOWN | Korean - Korea | RT_STRING |
13 | 7.48088 | 654 | UNKNOWN | Korean - Korea | RT_STRING |
108 | 1.91924 | 20 | UNKNOWN | Korean - Korea | RT_GROUP_ICON |
109 | 6.97286 | 340 | UNKNOWN | Korean - Korea | RT_DIALOG |
218 | 7.93718 | 16224 | UNKNOWN | Korean - Korea | RT_BITMAP |
219 | 0 | 14231804 | UNKNOWN | Korean - Korea | BIN |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
58
Monitored processes
17
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Users\admin\AppData\Local\Temp\~RAPack1911078\raon_touchenex_Install.exe" /S | C:\Users\admin\AppData\Local\Temp\~RAPack1911078\raon_touchenex_Install.exe | TouchEn_nxKey_32bit.exe | ||||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: HIGH Description: iniLINE CrossEX 32bit Exit code: 0 Version: 1.0.1.1243 Modules
| |||||||||||||||
| 916 | "C:\Users\admin\AppData\Local\Temp\~RAPack1911078\CrossEX_LocalService_Install.exe" /S | C:\Users\admin\AppData\Local\Temp\~RAPack1911078\CrossEX_LocalService_Install.exe | TouchEn_nxKey_32bit.exe | ||||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: HIGH Description: iniLINE CrossEX Service Exit code: 0 Version: 1.0.2.8 Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe" -A -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default" -i "C:\Program Files\iniLINE\CrossEX\crossex\rootCA.crt" -n "iniLINE CrossEX RootCA2" -t "CT,C,C" | C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe | — | Firefox_CertUtil.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\AppData\Local\Temp\nsj845C.tmp\ns8587.tmp" sc description "CrossEX Live Checker" "checking live status of CrossEXService" | C:\Users\admin\AppData\Local\Temp\nsj845C.tmp\ns8587.tmp | — | CrossEX_LocalService_Install.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2012 | "C:\Users\admin\AppData\Local\Temp\TouchEn_nxKey_32bit.exe" | C:\Users\admin\AppData\Local\Temp\TouchEn_nxKey_32bit.exe | — | explorer.exe | |||||||||||
User: admin Company: RaonSecure Co., Ltd. Integrity Level: MEDIUM Description: TouchEn nxKey Keyboard Protector Installer Exit code: 3221226540 Version: 1, 0, 0, 73 Modules
| |||||||||||||||
| 2288 | sc start "CrossEX Live Checker" | C:\Windows\system32\sc.exe | — | ns85F5.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe" -L -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default" | C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe | — | Firefox_CertUtil.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\iniLINE\CrossEX\crossex\ObCrossEXService.exe" | C:\Program Files\iniLINE\CrossEX\crossex\ObCrossEXService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: iniLINE Co., Ltd. Integrity Level: SYSTEM Description: CrossEX Live Checker Exit code: 0 Version: 1.0.2.8 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\iniLINE\CrossEX\crossex\CrossEXService.exe" | C:\Program Files\iniLINE\CrossEX\crossex\CrossEXService.exe | CrossEX_LocalService_Install.exe | ||||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: HIGH Description: CrossEX Service Exit code: 0 Version: 1.0.2.8 Modules
| |||||||||||||||
| 2936 | "C:\Users\admin\AppData\Local\Temp\TouchEn_nxKey_32bit.exe" | C:\Users\admin\AppData\Local\Temp\TouchEn_nxKey_32bit.exe | explorer.exe | ||||||||||||
User: admin Company: RaonSecure Co., Ltd. Integrity Level: HIGH Description: TouchEn nxKey Keyboard Protector Installer Exit code: 0 Version: 1, 0, 0, 73 Modules
| |||||||||||||||
Total events
492
Read events
405
Write events
80
Delete events
7
Modification events
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\ActiveX Compatibility\{6CE20149-ABE3-462E-A1B4-5B549971AA38} |
| Operation: | write | Name: | Compatibility Flags |
Value: 0 | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_CLASSES_ROOT\VirtualStore\MACHINE\SOFTWARE\Microsoft\Internet Explorer\ActiveX Compatibility\{6CE20149-ABE3-462E-A1B4-5B549971AA38} |
| Operation: | write | Name: | Compatibility Flags |
Value: 0 | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\ActiveX Compatibility\{8FD68F8A-641E-4204-AE47-DD835C1AE756} |
| Operation: | write | Name: | Compatibility Flags |
Value: 0 | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_CLASSES_ROOT\VirtualStore\MACHINE\SOFTWARE\Microsoft\Internet Explorer\ActiveX Compatibility\{8FD68F8A-641E-4204-AE47-DD835C1AE756} |
| Operation: | write | Name: | Compatibility Flags |
Value: 0 | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{6CE20149-ABE3-462E-A1B4-5B549971AA39} |
| Operation: | write | Name: | AppName |
Value: CKAgentNXE.exe | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{6CE20149-ABE3-462E-A1B4-5B549971AA39} |
| Operation: | write | Name: | AppPath |
Value: C:\Windows\system32 | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{6CE20149-ABE3-462E-A1B4-5B549971AA39} |
| Operation: | write | Name: | Policy |
Value: 3 | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TouchEn\Key |
| Operation: | write | Name: | ucount |
Value: 0 | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TouchEn nxKey |
| Operation: | write | Name: | DisplayName |
Value: TouchEn nxKey with E2E for 32bit | |||
| (PID) Process: | (3472) CKSetup32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TouchEn nxKey |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\system32\CKSetup32.exe /uninstall appm | |||
Executable files
40
Suspicious files
1
Text files
6
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3472 | CKSetup32.exe | C:\Windows\system32\CKAgentNXE_t.exe | — | |
MD5:— | SHA256:— | |||
| 3472 | CKSetup32.exe | C:\Windows\system32\CKAgent_t.exe | — | |
MD5:— | SHA256:— | |||
| 3472 | CKSetup32.exe | C:\Windows\system32\temp_JRSKD24.SYS | — | |
MD5:— | SHA256:— | |||
| 3472 | CKSetup32.exe | C:\Windows\system32\temp_JRSUKD25.SYS | — | |
MD5:— | SHA256:— | |||
| 536 | raon_touchenex_Install.exe | C:\Users\admin\AppData\Local\Temp\nst8314.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 2936 | TouchEn_nxKey_32bit.exe | C:\Users\admin\AppData\Local\Temp\~RAPack1911078\_Chunk.zip | compressed | |
MD5:— | SHA256:— | |||
| 3472 | CKSetup32.exe | C:\Windows\system32\JRSKD24.SYS | executable | |
MD5:— | SHA256:— | |||
| 3472 | CKSetup32.exe | C:\Windows\system32\CKAgentNXE.exe | executable | |
MD5:01903B5143FB2F6959AF247D16C6F768 | SHA256:B459518A087ABD2F758A8B5E284A49DCDBCCC4343A35C2480EB242CD1E68AB2A | |||
| 2936 | TouchEn_nxKey_32bit.exe | C:\Users\admin\AppData\Local\Temp\~RAPack1911078\_Install.ini | ini | |
MD5:— | SHA256:— | |||
| 3472 | CKSetup32.exe | C:\Windows\system32\JRSUKD25.SYS | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
TouchEn_nxKey_32bit.exe | 20141130 fn : C:\Users\admin\AppData\Local\Temp\~RAPack1911078\_Chunk.zip, C:\Users\admin\AppData\Local\Temp\~RAPack1911078 333
|
TouchEn_nxKey_32bit.exe | 20141130 fn : C:\Windows\system32\CKSetup32.exe, C:\Windows\system32(size=2868896) 565
|
TouchEn_nxKey_32bit.exe | C:\Windows\system32\CKSetup32.exe /install appm
|
TouchEn_nxKey_32bit.exe | 20141130 1240_.\TouchEn_nxKey_Installer.cpp
|
TouchEn_nxKey_32bit.exe | 20141211 1.szResVersion : 3,1,1,43
|
CKSetup32.exe | [TK] KillProcessByImageName = CKAgentNXE.exe
|
CKSetup32.exe | [TK] KillProcessByImageName return = 0
|
CKSetup32.exe | [TK] KillProcessByImageName = CKAgent.exe
|
CKSetup32.exe | [TK] KillProcessByImageName return = 0
|
CKSetup32.exe | [TK] [CKSETUP 20130627 DOSPathFileName] C:\Windows\system32\wininit.exe
|