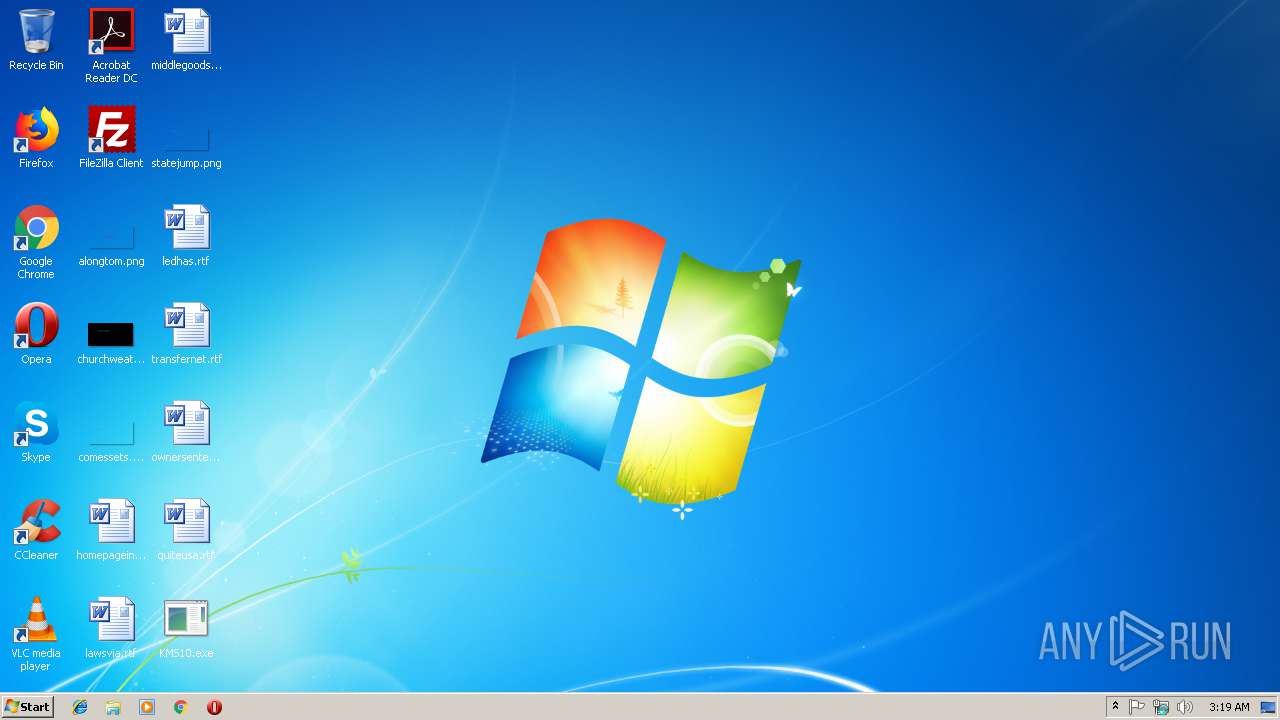
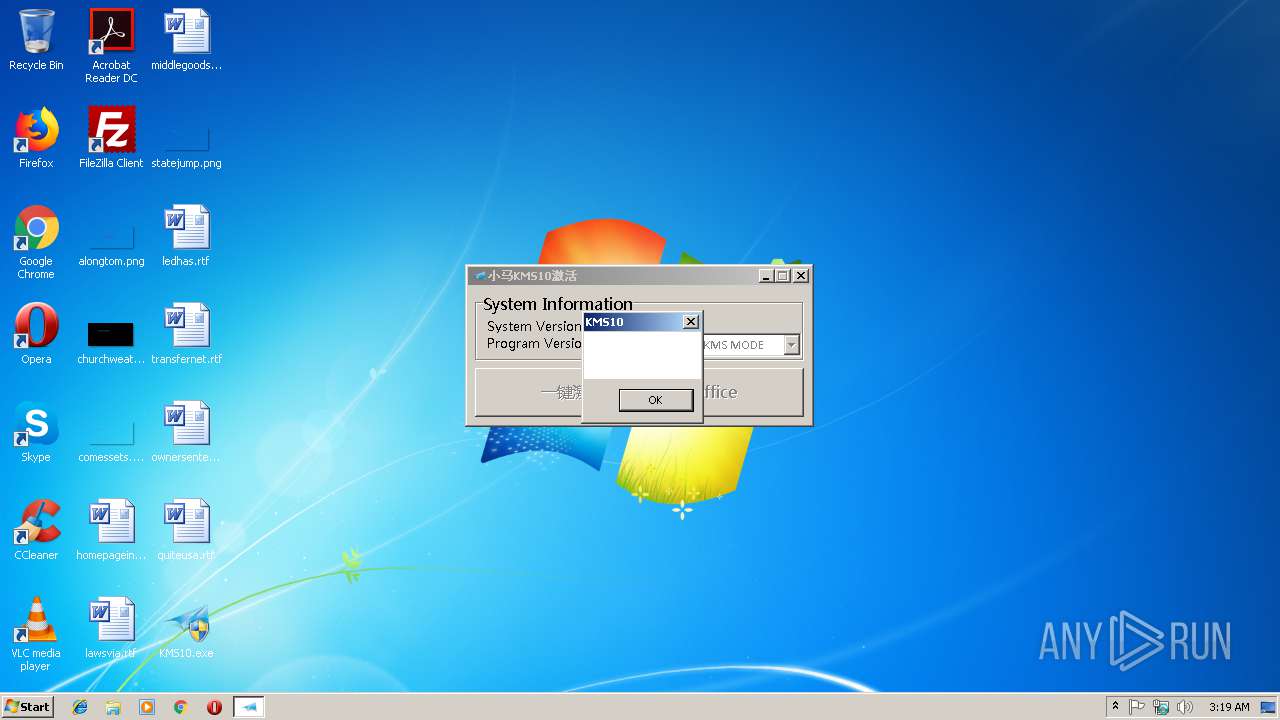
| File name: | KMS10.exe |
| Full analysis: | https://app.any.run/tasks/920b73a5-e918-4050-aee2-e2f7c879c70f |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2018, 03:18:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1B754FD414DC0A1AADF8B917872A27DB |
| SHA1: | 82B93809EFFDFCD0207201A02A58C4328E7F757A |
| SHA256: | A1F3473A4E6BA6450C61C89EC5DE2C9B8DE60DBD74FCC09EBA13DF4DE3219317 |
| SSDEEP: | 49152:zCoFqWbHnfmJimyUNDdOx1GbwkaNndZSrtW54EeEz4hglsP8V/usnFjv1vGNwz4l:zdHf8JOL8FaNndQrA4EeY4+Gy/3p1qO4 |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 2880)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 2492)
- cmd.exe (PID: 3572)
Changes Image File Execution Options
- KMS10.exe (PID: 2504)
Loads the Task Scheduler COM API
- KMS10.exe (PID: 2504)
SUSPICIOUS
Starts CMD.EXE for commands execution
- KMS10.exe (PID: 2504)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2360)
- cmd.exe (PID: 3424)
- cmd.exe (PID: 3600)
- cmd.exe (PID: 2744)
Reads Environment values
- KMS10.exe (PID: 2504)
Creates files in the Windows directory
- KMS10.exe (PID: 2504)
Executable content was dropped or overwritten
- KMS10.exe (PID: 2504)
Removes files from Windows directory
- KMS10.exe (PID: 2504)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:10:21 09:00:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2207232 |
| InitializedDataSize: | 1154048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7aa000 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Oct-2016 07:00:49 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 21-Oct-2016 07:00:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x00277000 | 0x000C2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91873 | |
.rsrc | 0x00278000 | 0x000CA000 | 0x00067200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.993 |
.idata | 0x00342000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.30872 |
0x00343000 | 0x00302000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.256865 | |
inkptteo | 0x00645000 | 0x00165000 | 0x00164600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93868 |
tisacgei | 0x007AA000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.98727 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13923 | 1848 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.3213 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 2.15895 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 3.87169 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 3.7079 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 1.94228 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 7.97998 | 40546 | UNKNOWN | English - United States | RT_ICON |
8 | 3.31182 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 3.4796 | 4264 | UNKNOWN | English - United States | RT_ICON |
10 | 3.62921 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
comctl32.dll |
kernel32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x00239C5C |
__dbk_fcall_wrapper | 2 | 0x0000DCE4 |
TMethodImplementationIntercept | 3 | 0x00055D5C |
Total processes
78
Monitored processes
29
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2228 | tasklist /FI "IMAGENAME eq osppsvc.exe" | C:\Windows\system32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2324 | C:\Windows\system32\net1 stop sppsvc /y | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2360 | cmd /C tasklist /FI "IMAGENAME eq sppsvc.exe" 2>nul | find /i "sppsvc.exe" 1>nul && taskkill /t /f /IM KMS8Load.exe >nul 2>&1 | C:\Windows\system32\cmd.exe | — | KMS10.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2404 | wmic path SoftwareLicensingProduct where '(Description like "%%Windows%%" and not(Description like "%%KMSCLIENT%%") and LicenseStatus="1")' get ID /format:list | C:\Windows\System32\Wbem\wmic.exe | — | KMS10.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | find /i "osppsvc.exe" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | net stop osppsvc /y | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | cmd /C net stop sppsvc /y >nul 2>&1 | C:\Windows\system32\cmd.exe | — | KMS10.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
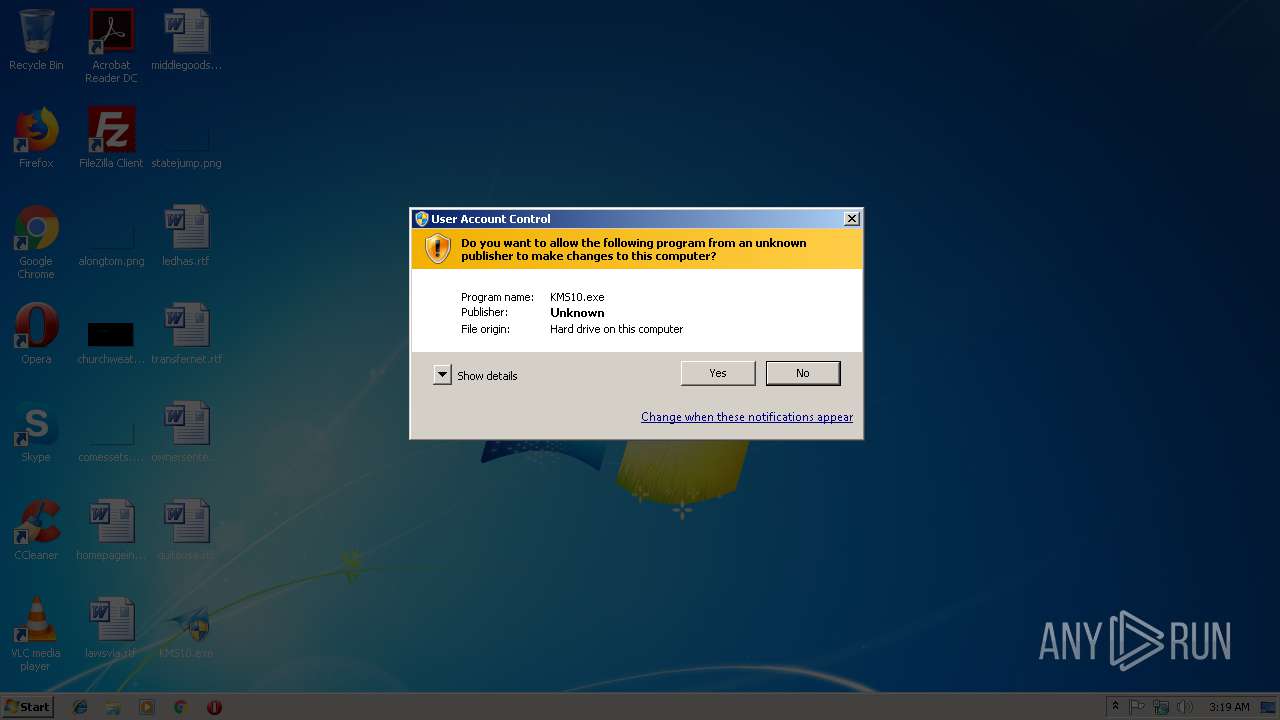
| 2504 | "C:\Users\admin\Desktop\KMS10.exe" | C:\Users\admin\Desktop\KMS10.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2584 | wmic path SoftwareLicensingProduct where (Description like "%%KMSCLIENT%%") get ID /format:list | C:\Windows\System32\Wbem\wmic.exe | — | KMS10.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2668 | net stop sppsvc /y | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
142
Read events
136
Write events
5
Delete events
1
Modification events
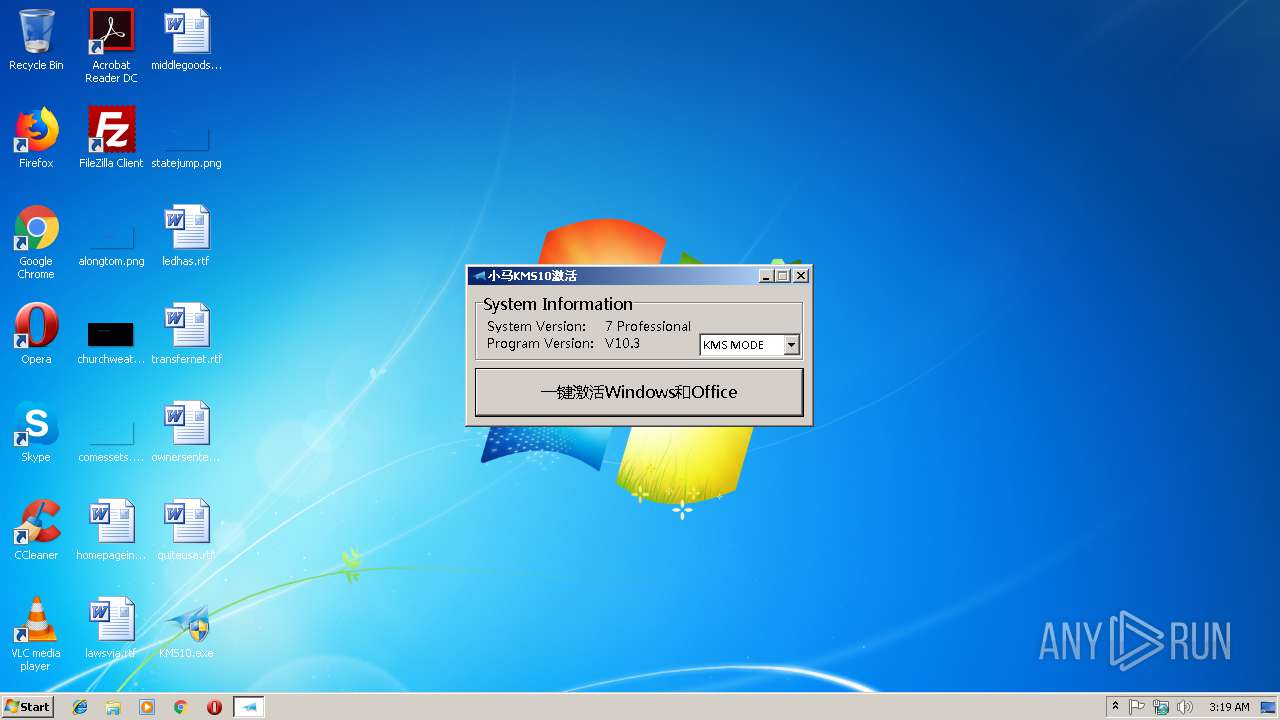
| (PID) Process: | (2504) KMS10.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | write | Name: | KeyManagementServiceName |
Value: 127.111.32.185 | |||
| (PID) Process: | (2504) KMS10.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | write | Name: | KeyManagementServicePort |
Value: 1688 | |||
| (PID) Process: | (2504) KMS10.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe |
| Operation: | write | Name: | Debugger |
Value: KMS8Load.exe | |||
| (PID) Process: | (2504) KMS10.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2504) KMS10.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | write | Name: | KeyManagementServiceName |
Value: | |||
| (PID) Process: | (2504) KMS10.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | write | Name: | KeyManagementServicePort |
Value: | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | KMS10.exe | C:\Windows\system32\KMS8Load.exe | executable | |
MD5:— | SHA256:— | |||
| 2504 | KMS10.exe | C:\Windows\system32\KMS8Core.dll | executable | |
MD5:— | SHA256:— | |||
| 2504 | KMS10.exe | C:\Windows\KMS10\KMS10.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report