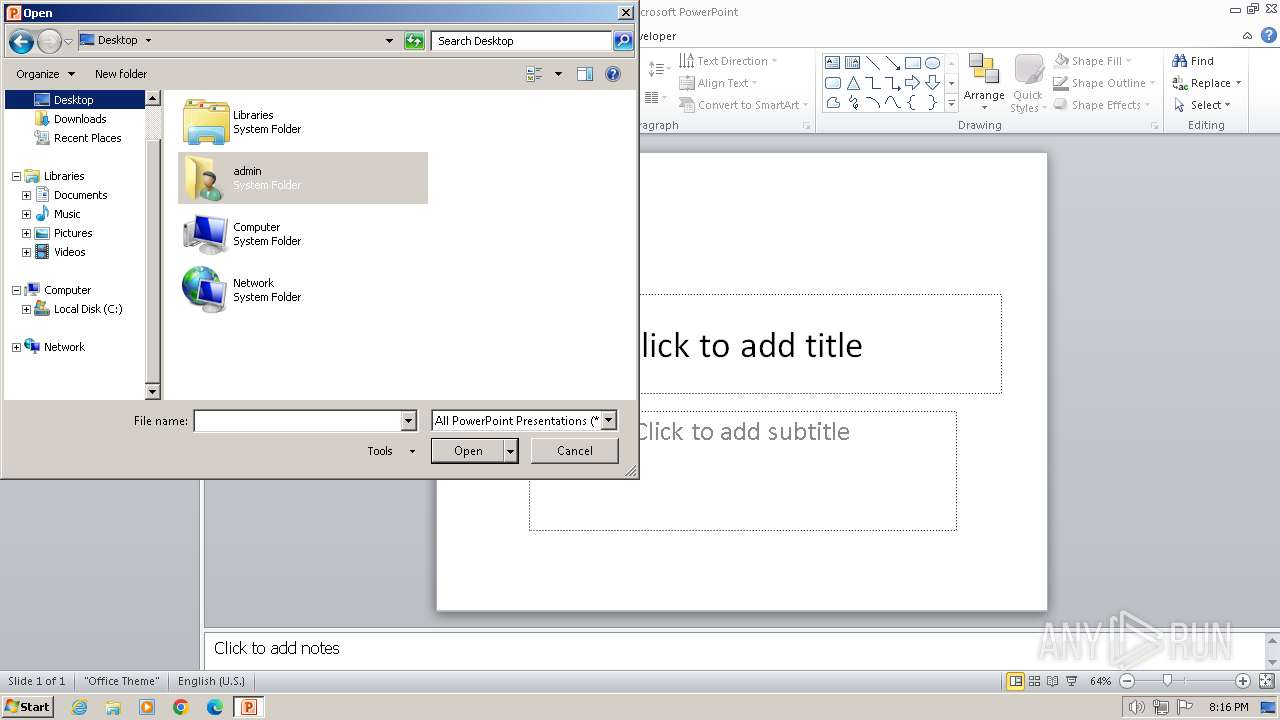
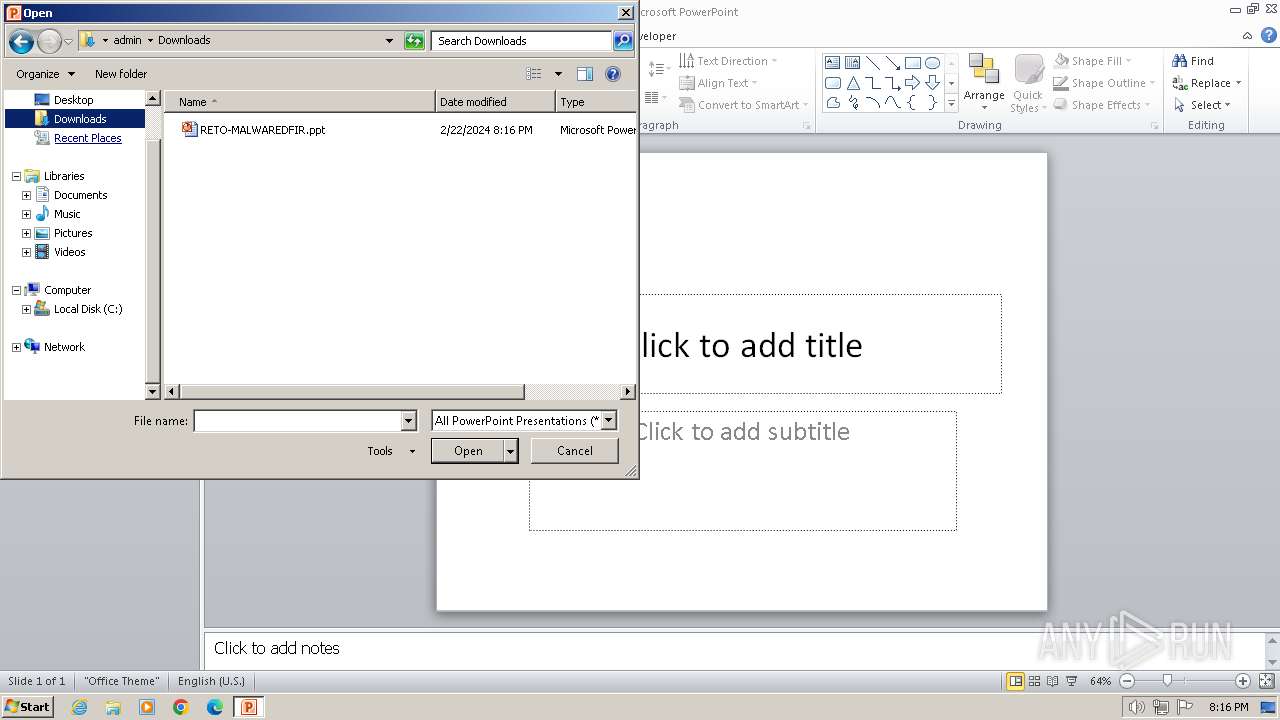
| File name: | RETO-MALWAREDFIR.ppt |
| Full analysis: | https://app.any.run/tasks/7e9e1028-fbdd-4063-a63f-ef916634522c |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2024, 20:12:20 |
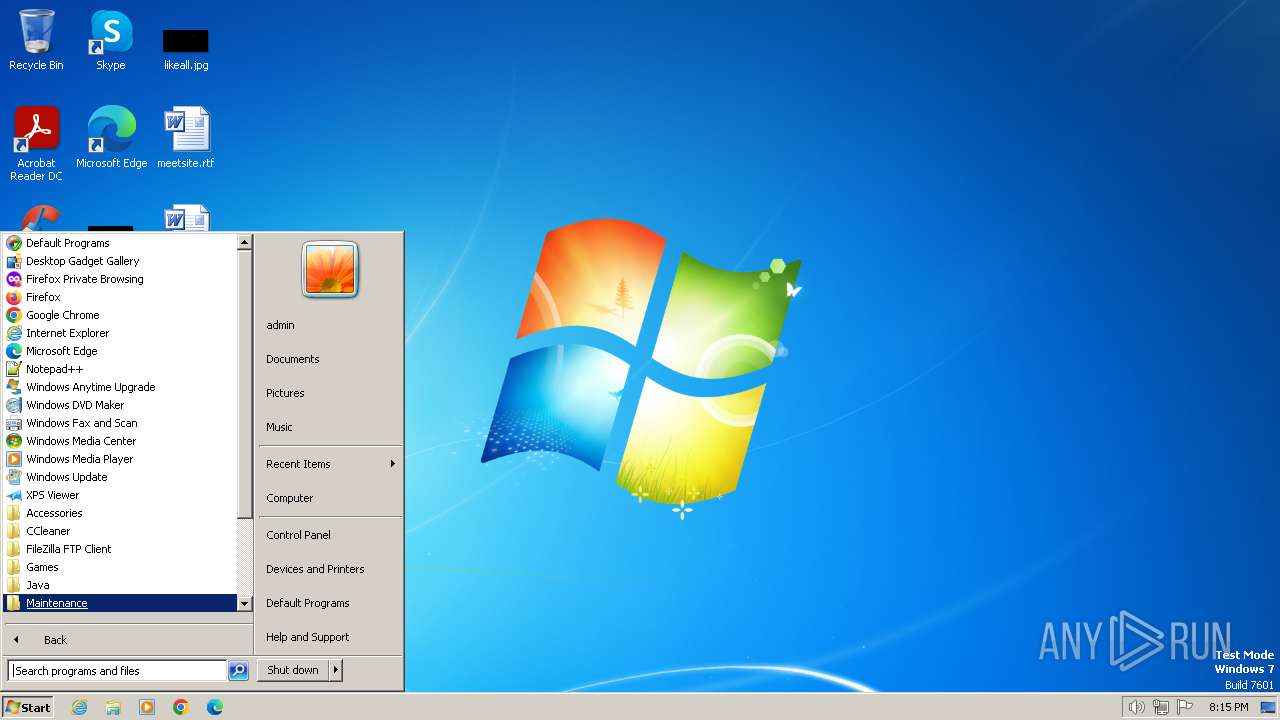
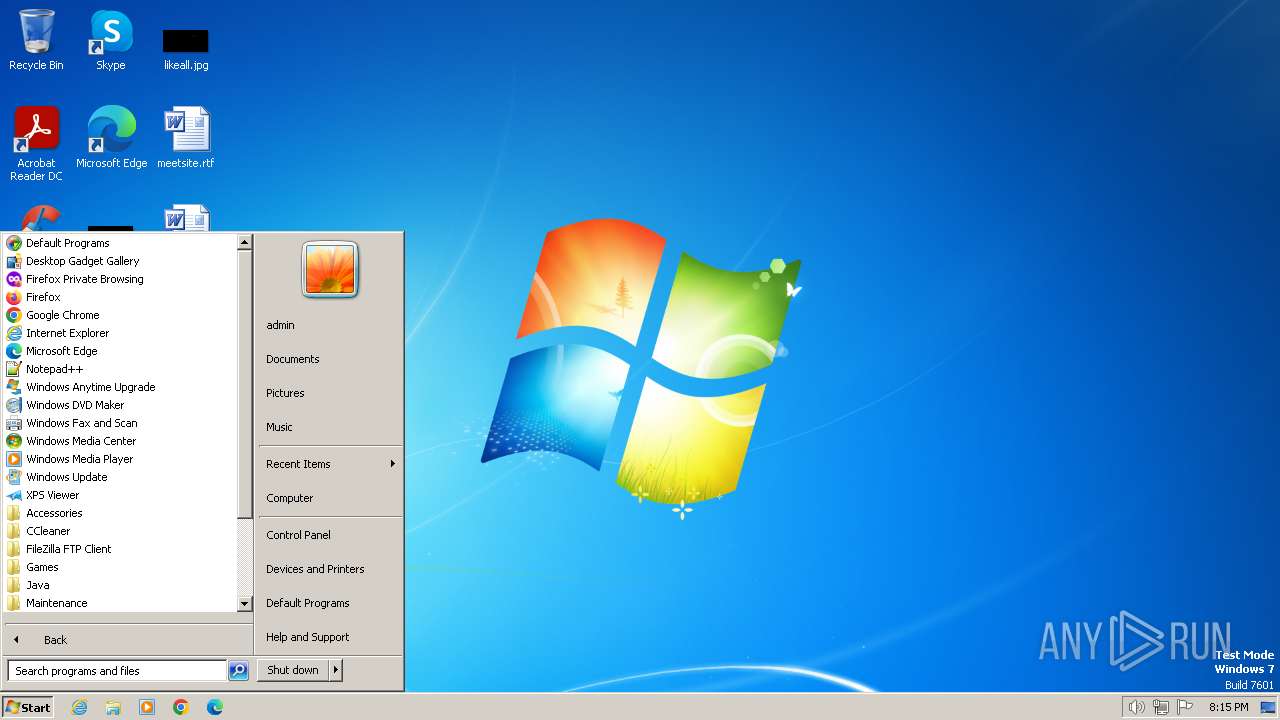
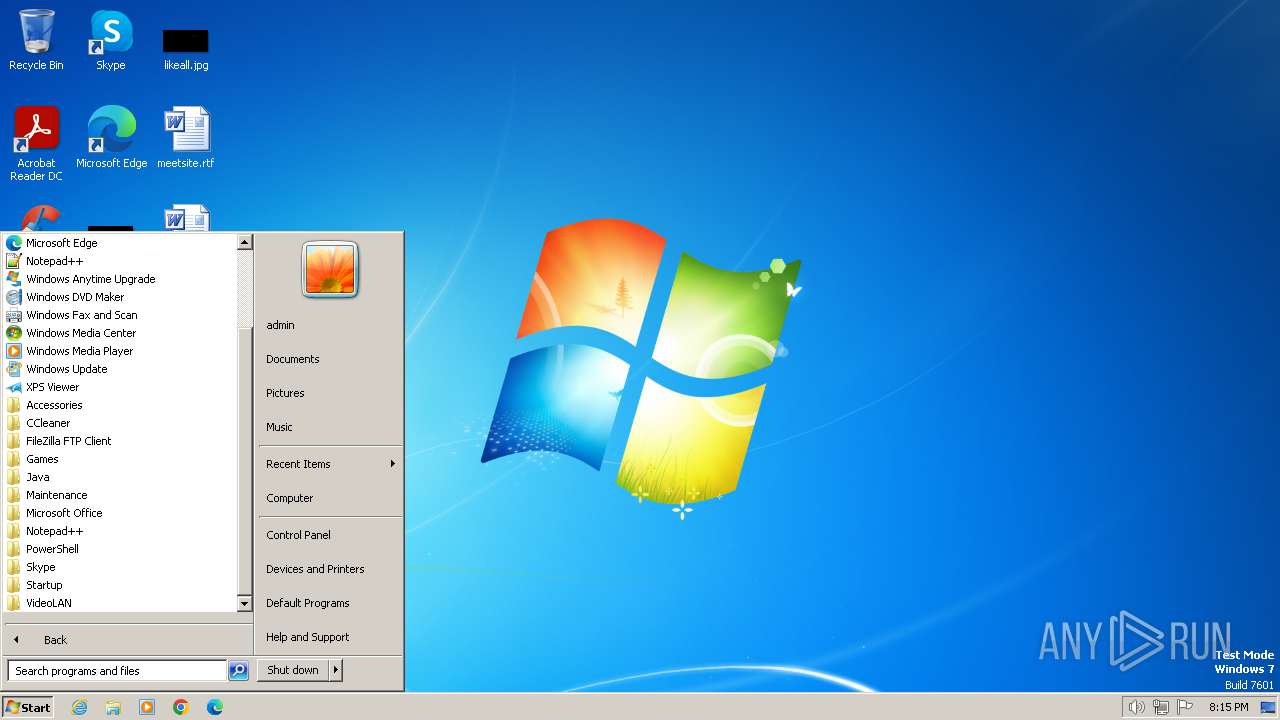
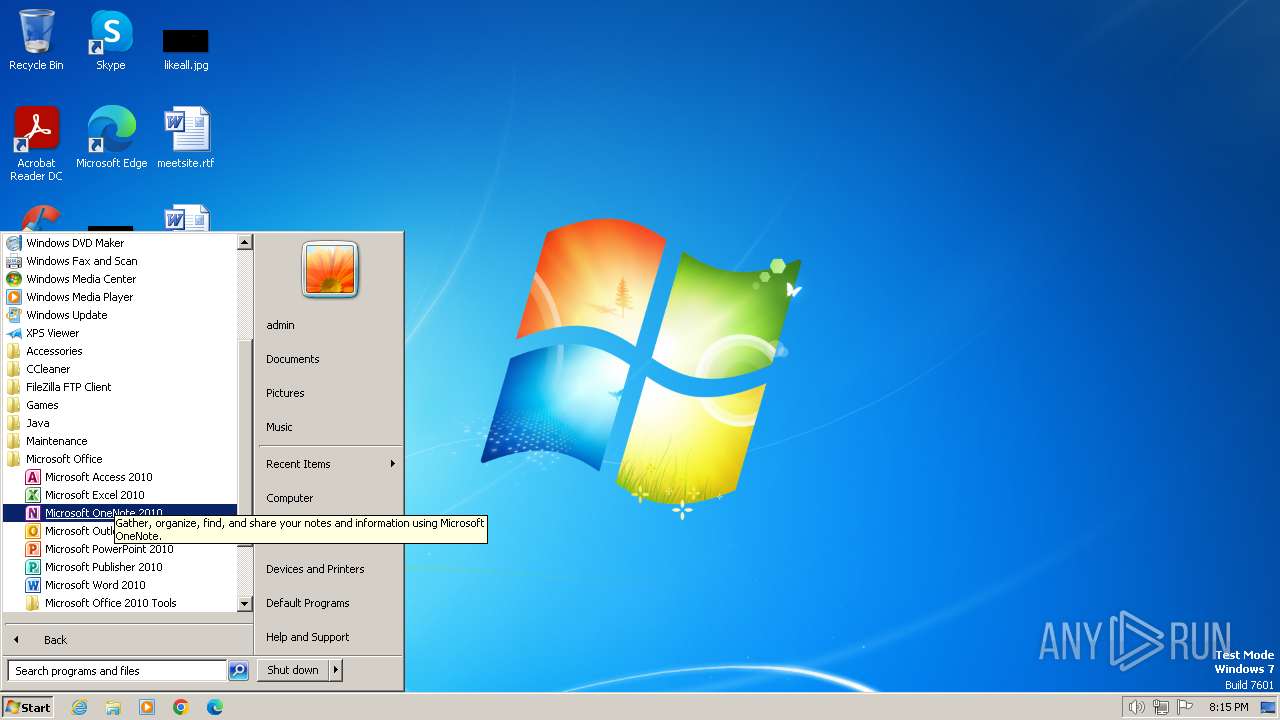
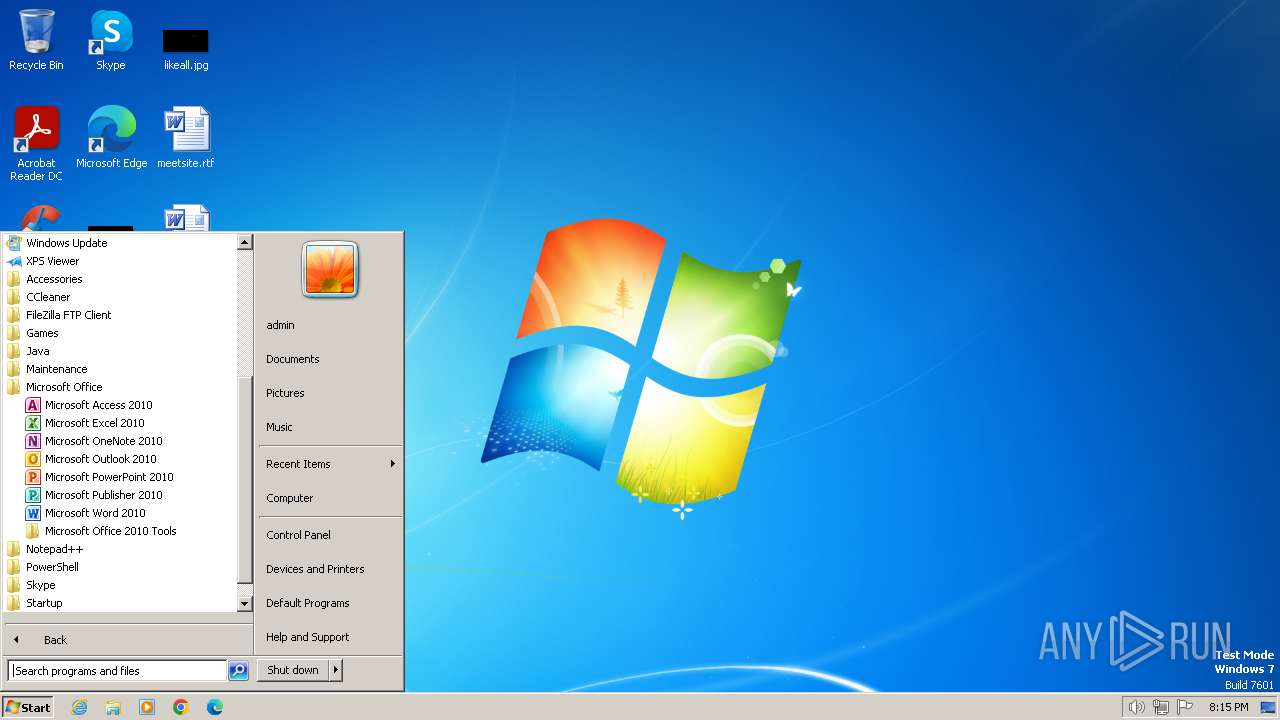
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-powerpoint |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: yazeed, Keywords: maviya, Last Saved By: Master Mana, Revision Number: 4, Name of Creating Application: Microsoft Office PowerPoint, Total Editing Time: 22:02, Create Time/Date: Wed Feb 24 17:17:23 2021, Last Saved Time/Date: Wed Feb 24 17:39:25 2021, Number of Words: 0 |
| MD5: | 00D7A6D6029559FA2FB656D906F7C5E4 |
| SHA1: | 42EB2E085BA018868C8A4018341516D843154B30 |
| SHA256: | A1E8DA85D99CFB4C8569EA850691CF6C565B6083114198E17369F3013E4016B5 |
| SSDEEP: | 1536:7333zMF4VlO20PZTVReP7zX1eBuyCSj/0f1p4C:7333+20xTVM31eBuyB/Op4C |
MALICIOUS
Unusual execution from MS Office
- POWERPNT.EXE (PID: 3940)
SUSPICIOUS
Reads the Internet Settings
- rundll32.exe (PID: 2472)
- mshta.exe (PID: 2728)
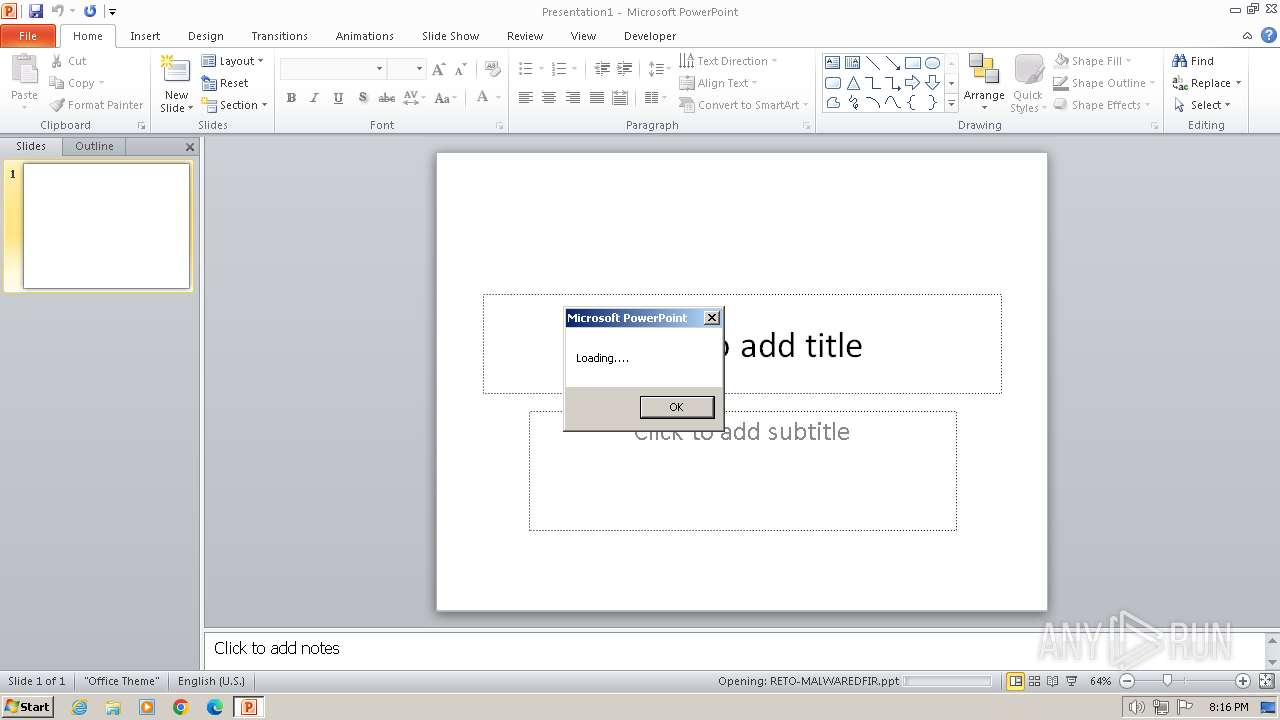
Runs shell command (SCRIPT)
- POWERPNT.EXE (PID: 3940)
INFO
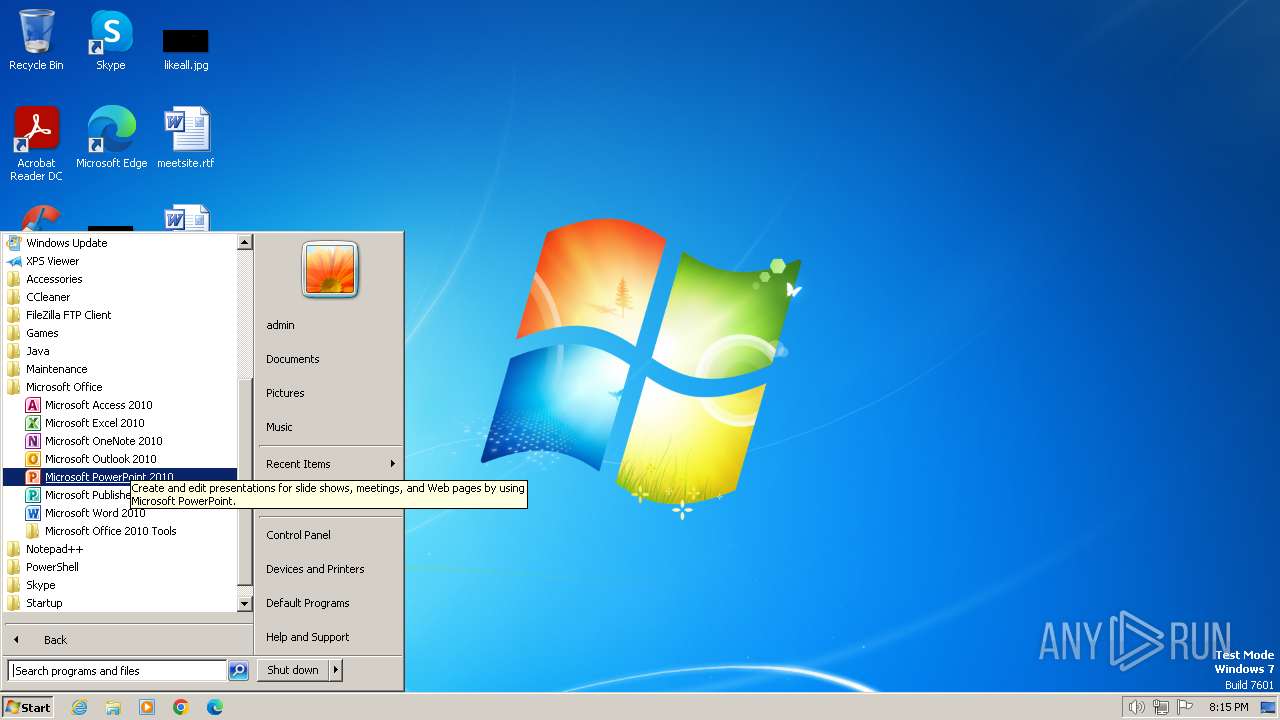
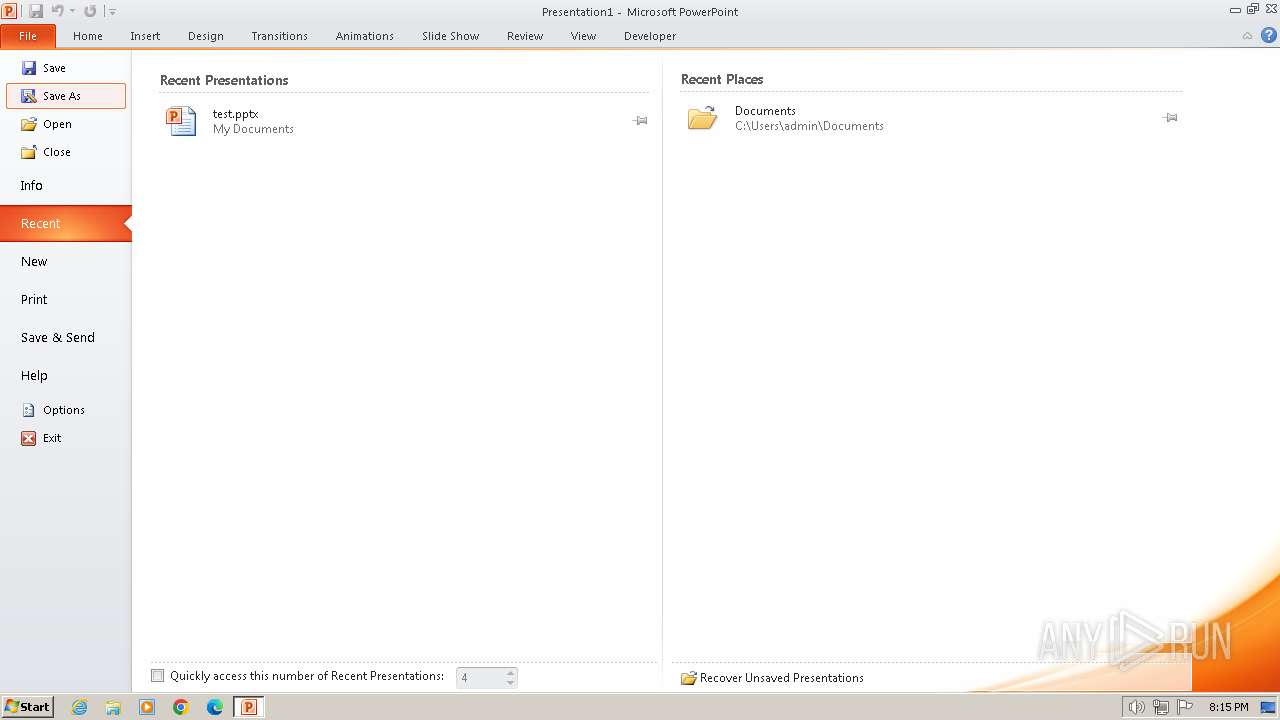
Manual execution by a user
- POWERPNT.EXE (PID: 3940)
Checks proxy server information
- mshta.exe (PID: 2728)
Reads Internet Explorer settings
- mshta.exe (PID: 2728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pps/ppt | | | Microsoft PowerPoint document (79.7) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Author: | yazeed |
| Keywords: | maviya |
| LastModifiedBy: | Master Mana |
| RevisionNumber: | 4 |
| Software: | Microsoft Office PowerPoint |
| TotalEditTime: | 22.0 minutes |
| CreateDate: | 2021:02:24 17:17:23 |
| ModifyDate: | 2021:02:24 17:39:25 |
| Words: | - |
| ThumbnailClip: | (Binary data 43336 bytes, use -b option to extract) |
| CodePage: | Windows Latin 1 (Western European) |
| PresentationTarget: | Widescreen |
| Bytes: | - |
| Paragraphs: | - |
| Slides: | - |
| Notes: | - |
| HiddenSlides: | - |
| MMClips: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
45
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
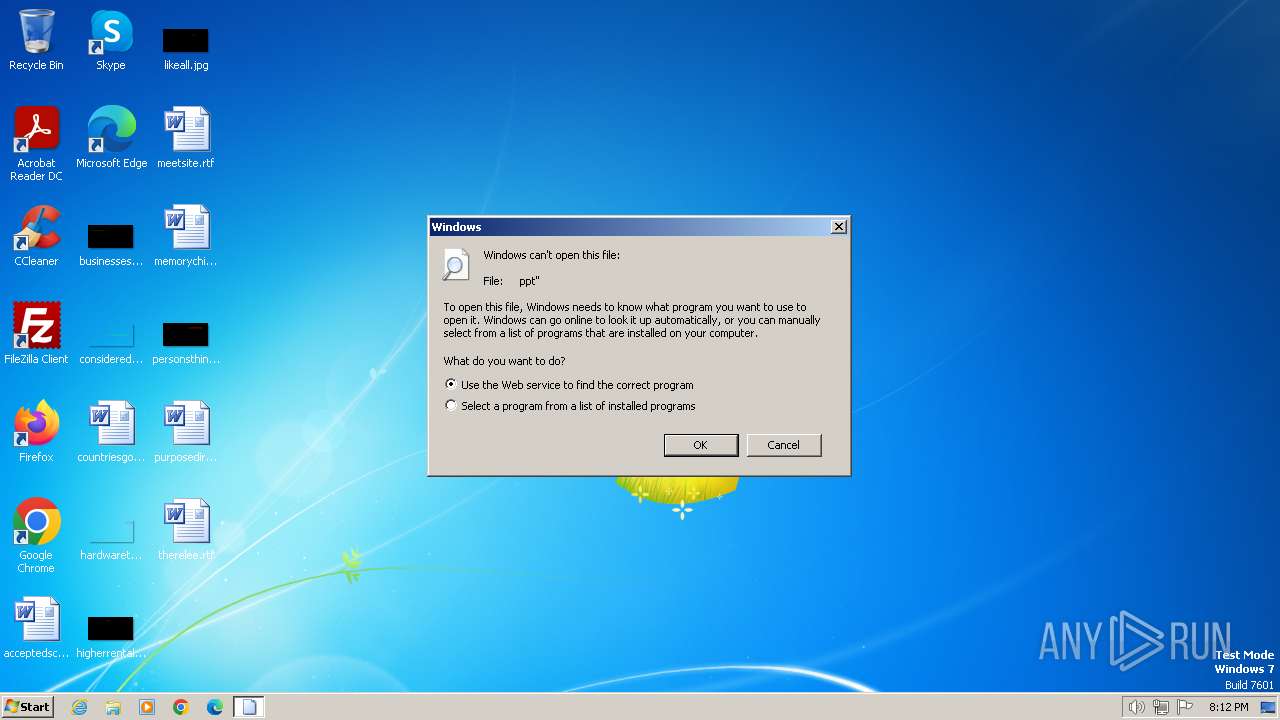
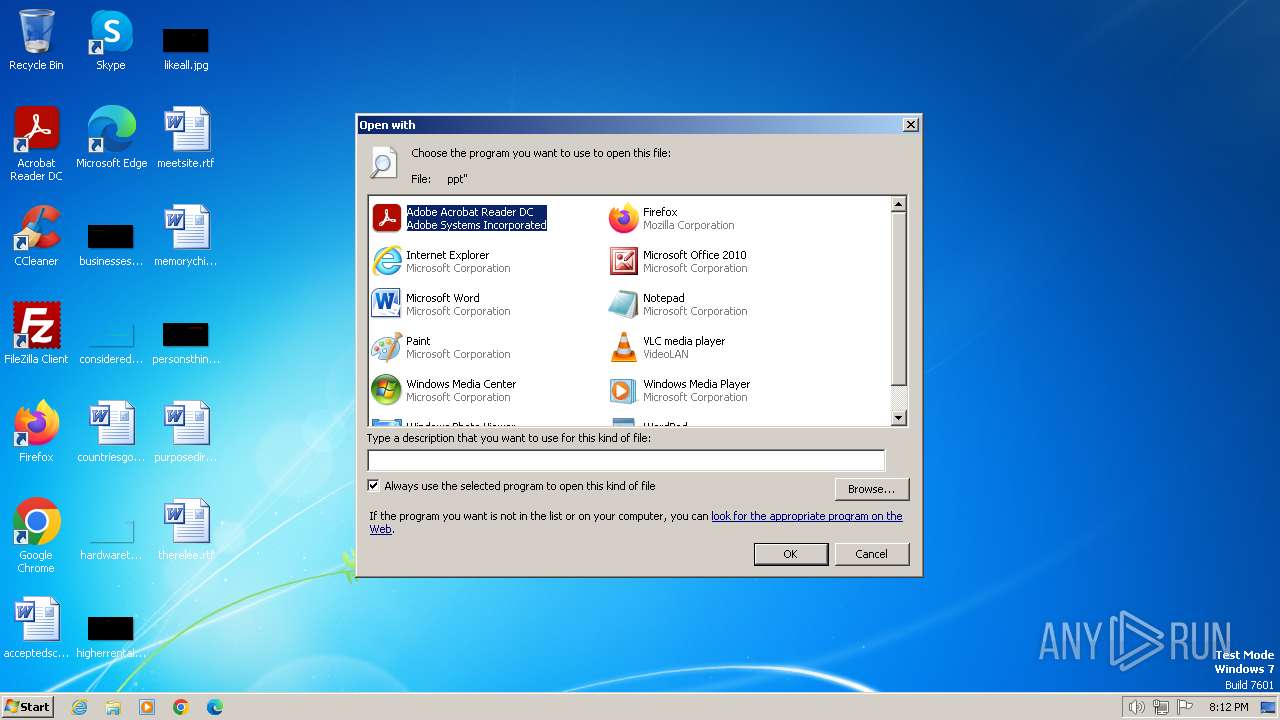
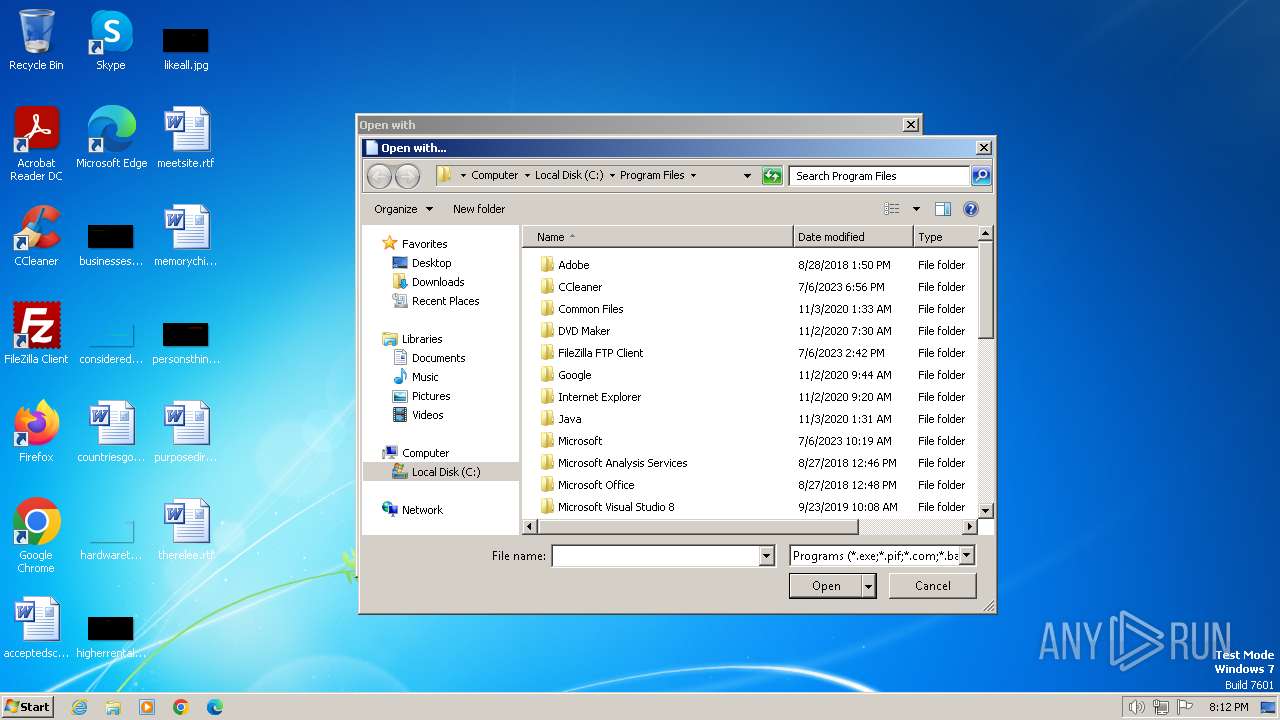
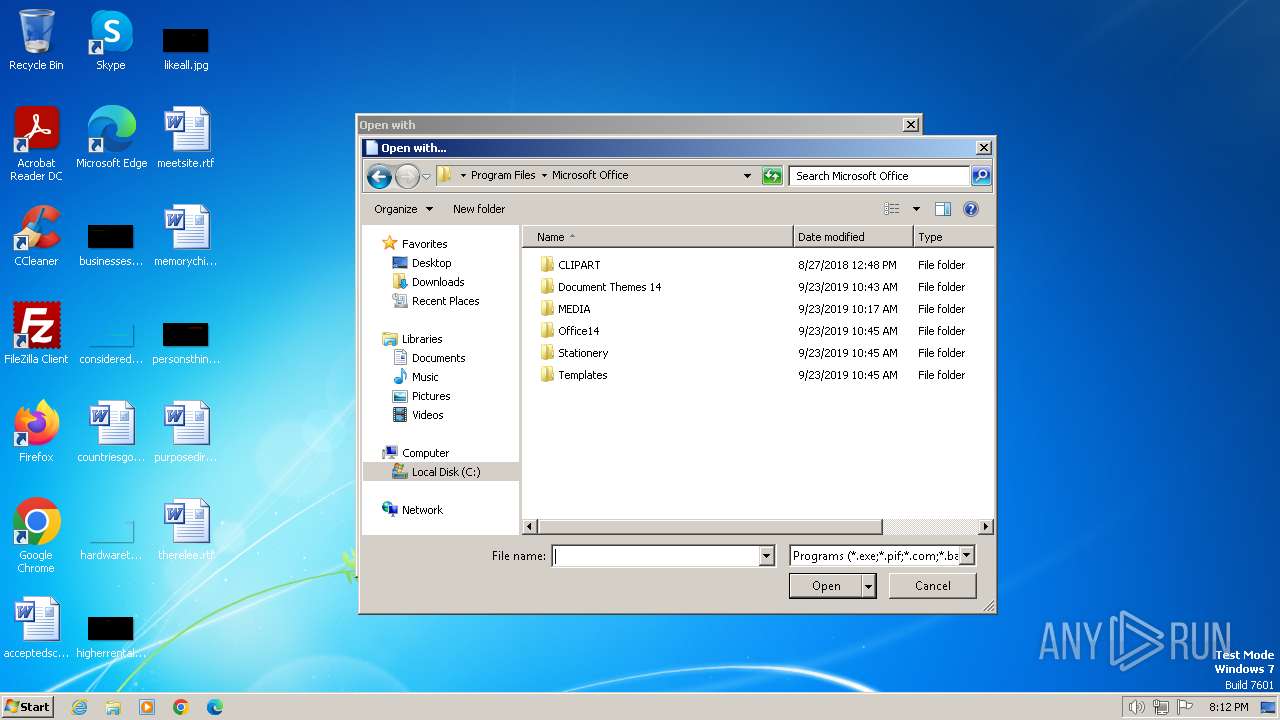
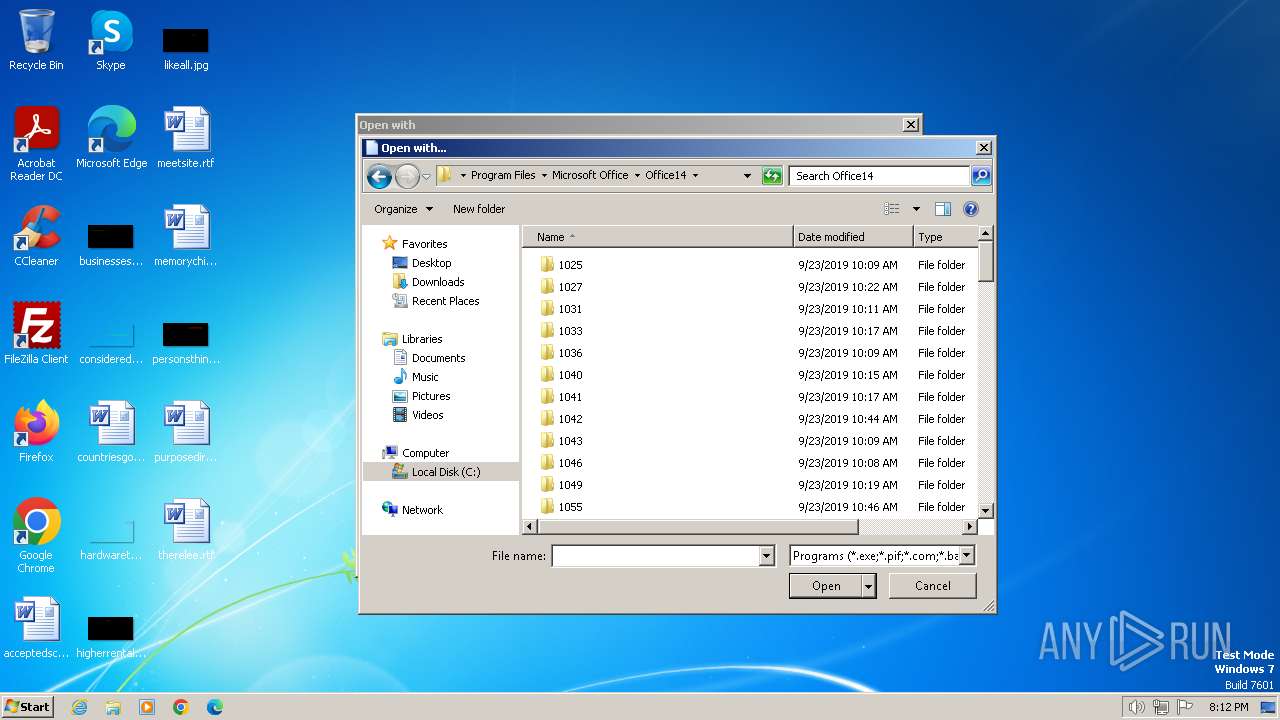
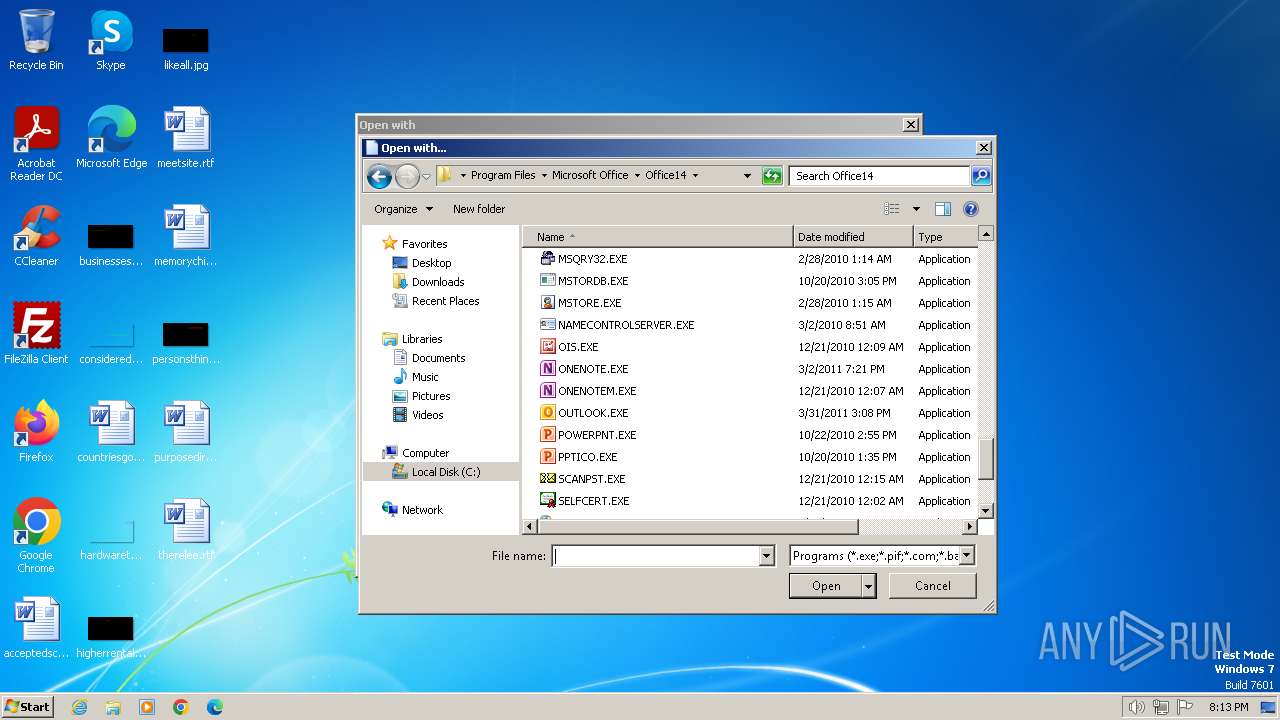
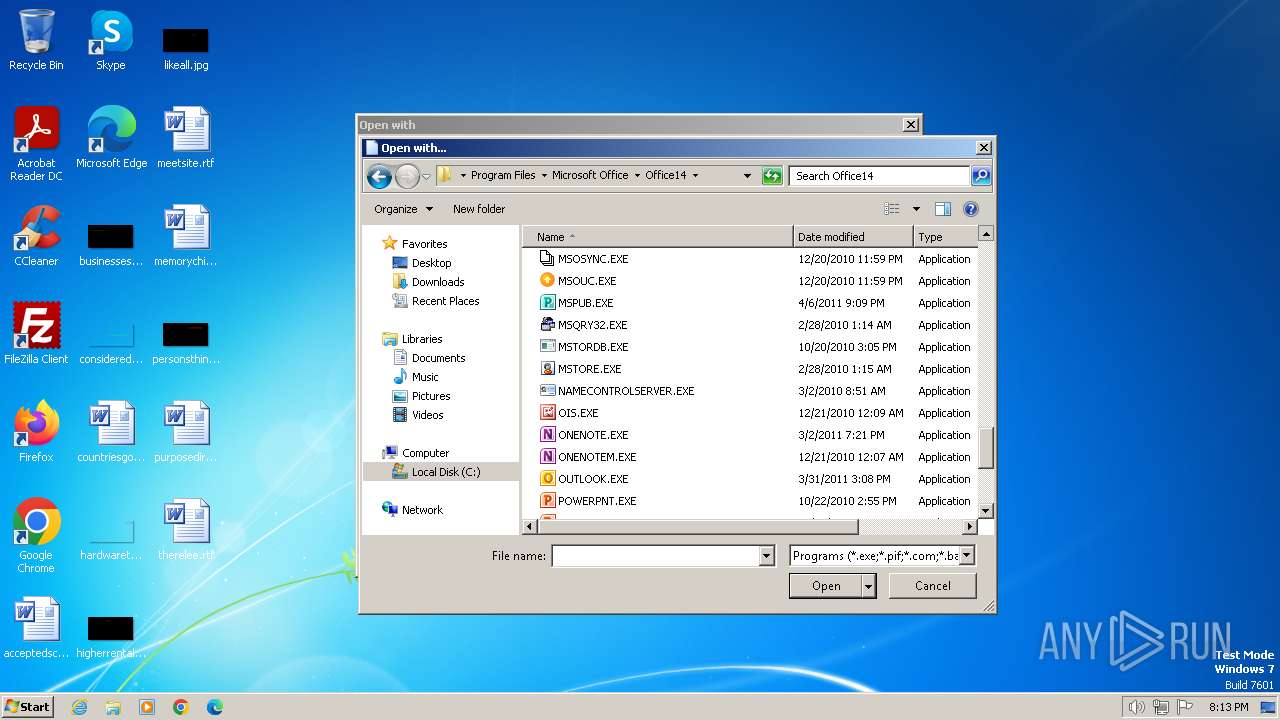
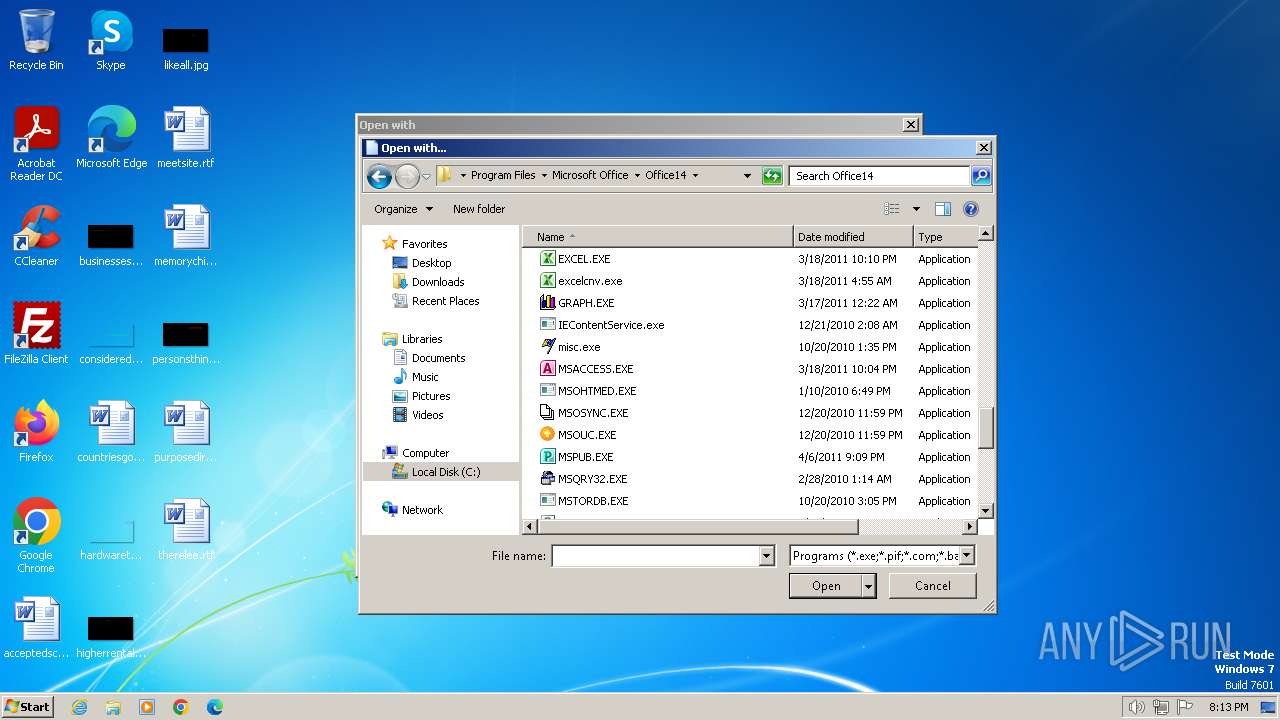
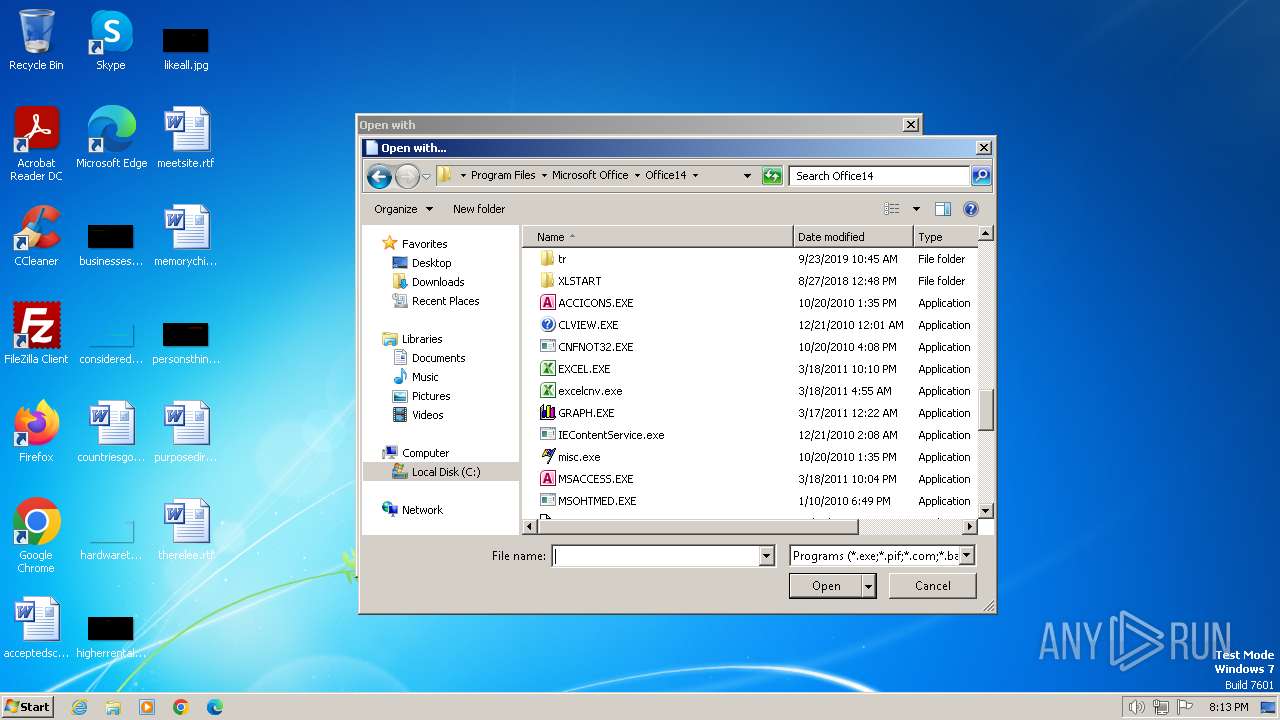
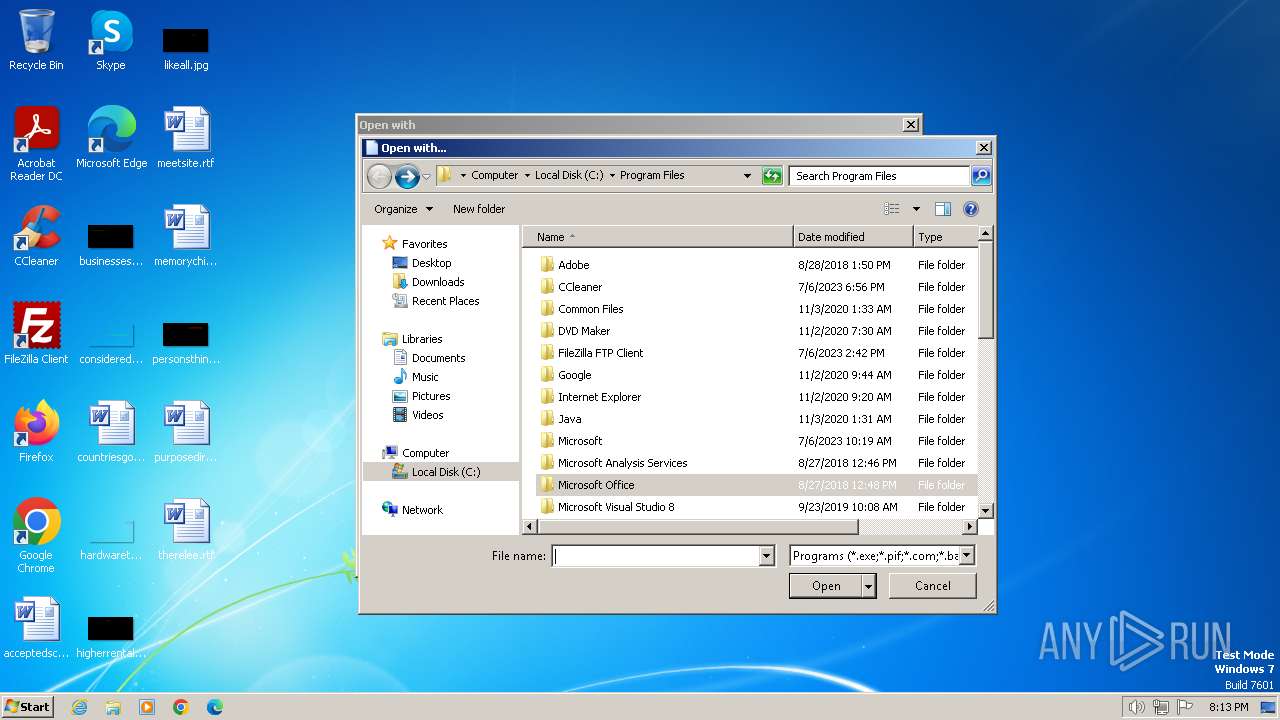
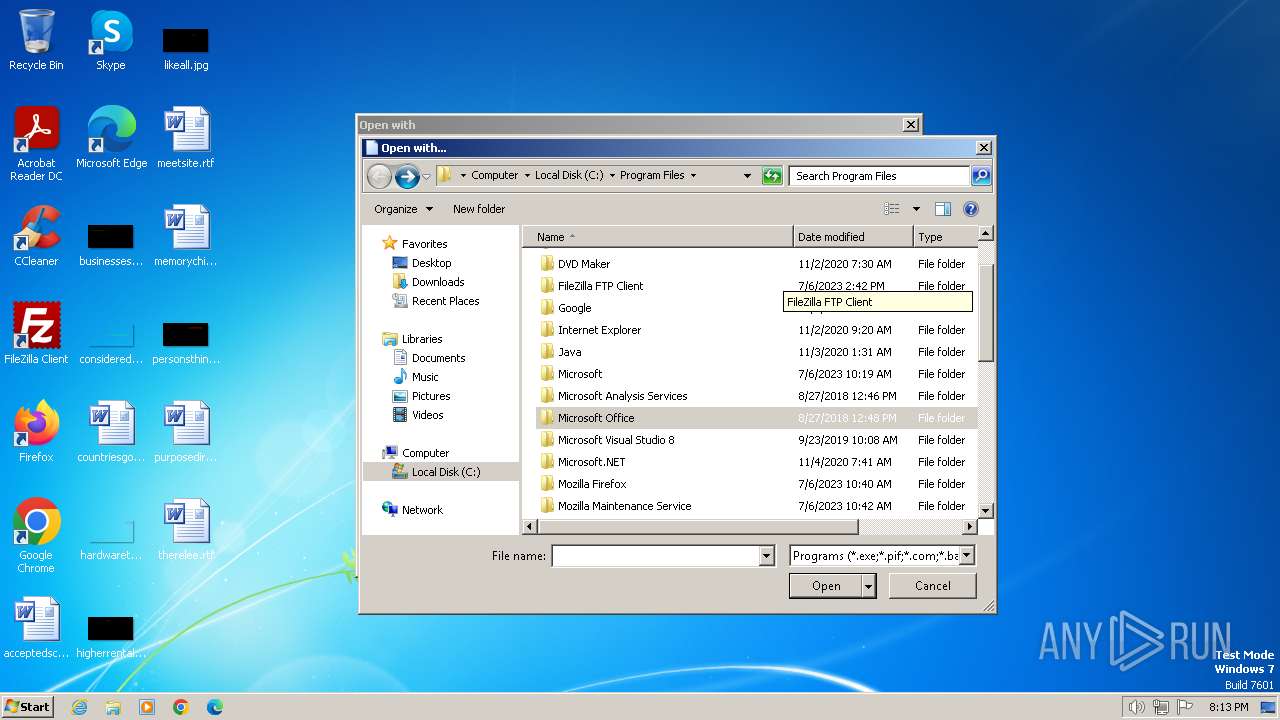
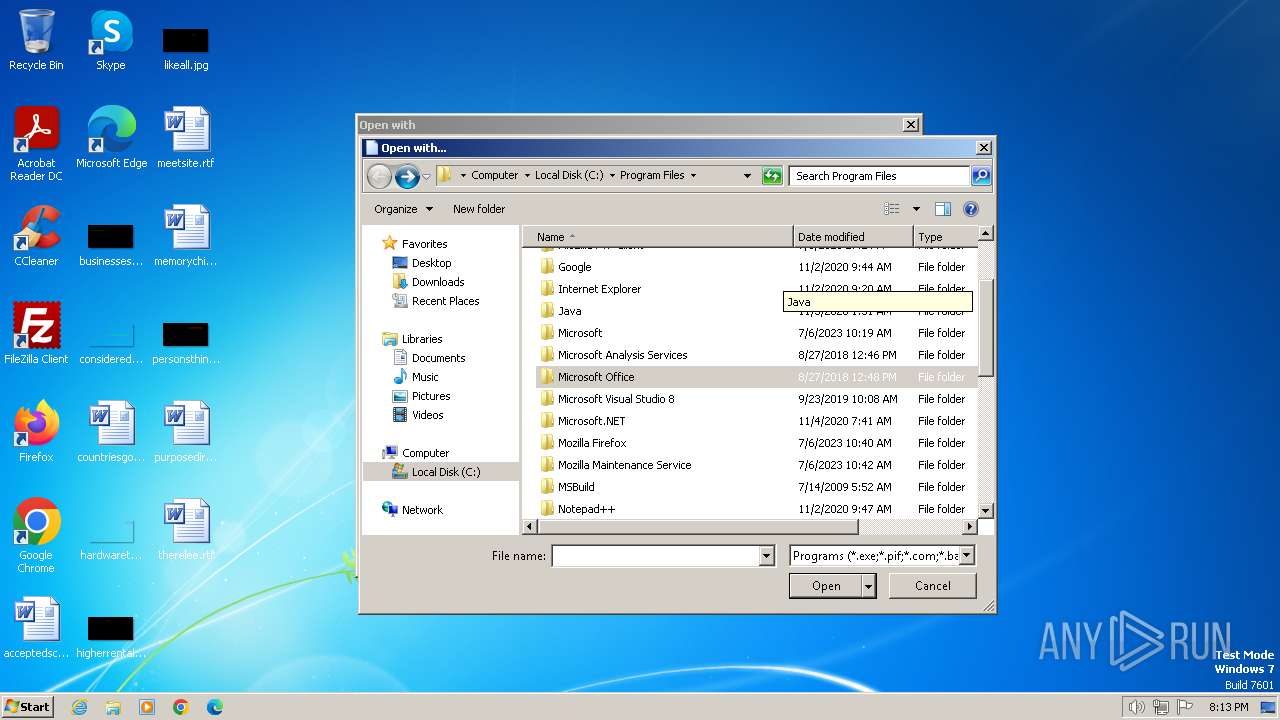
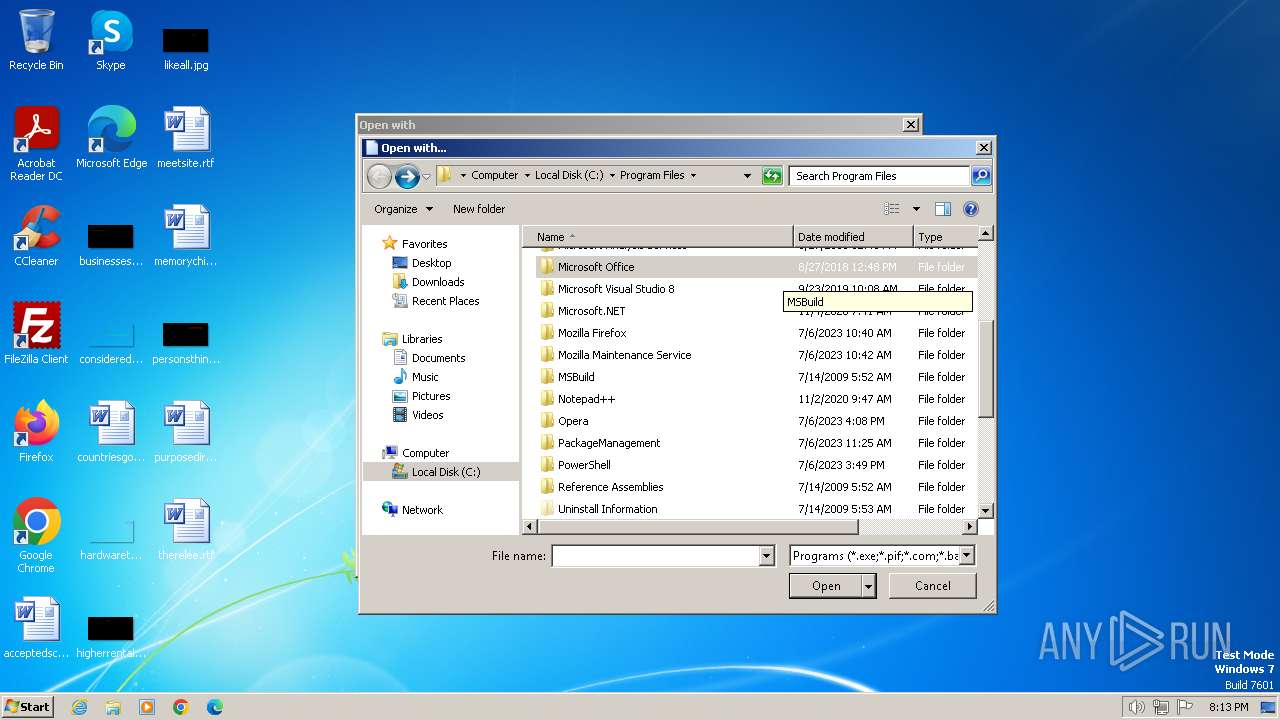
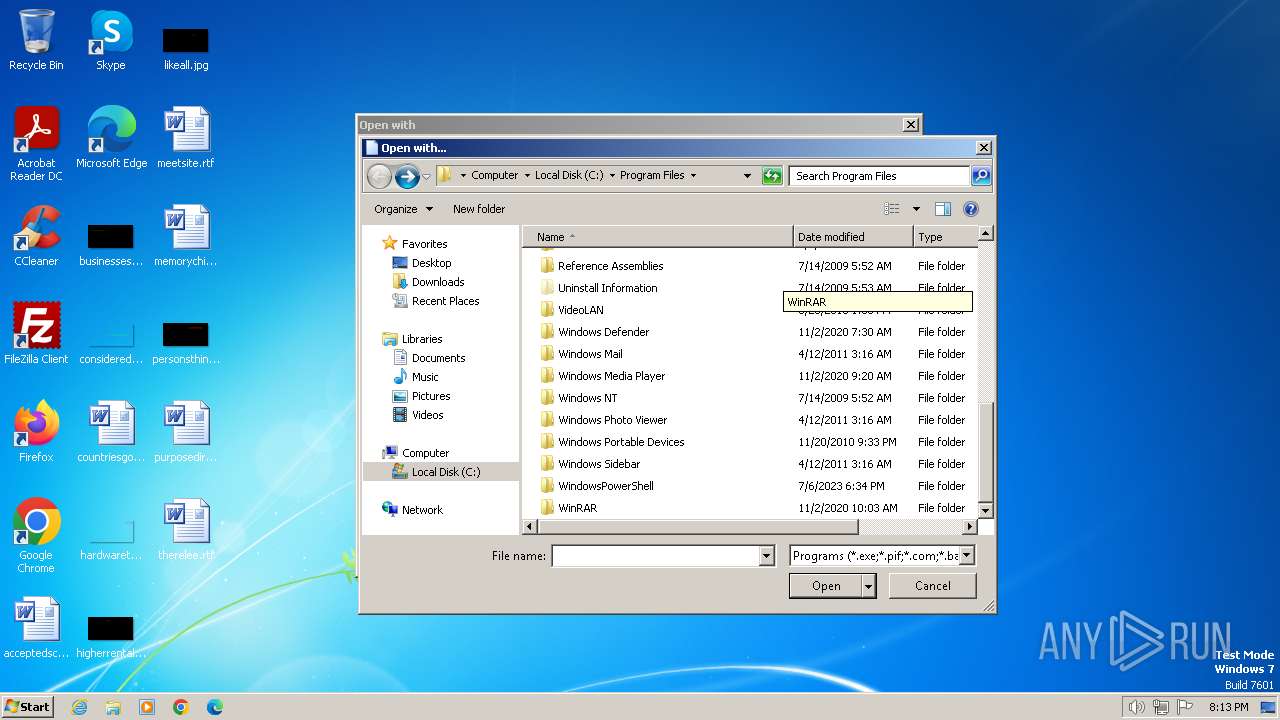
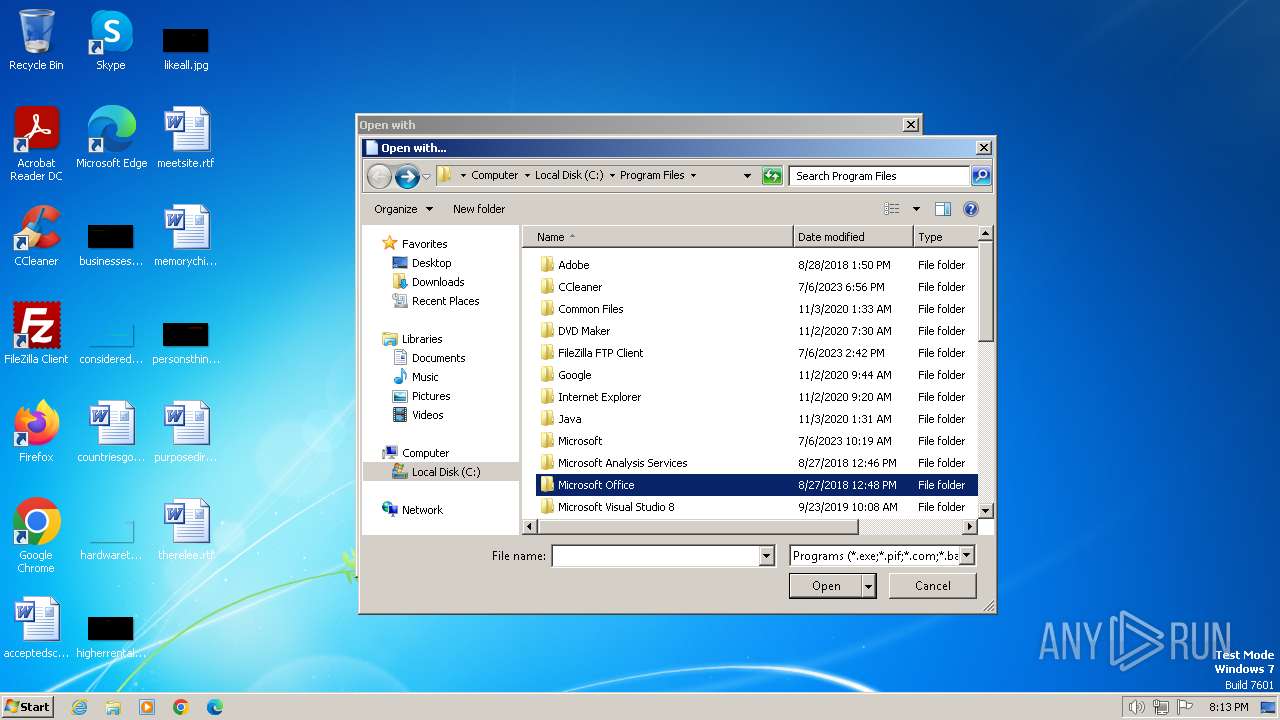
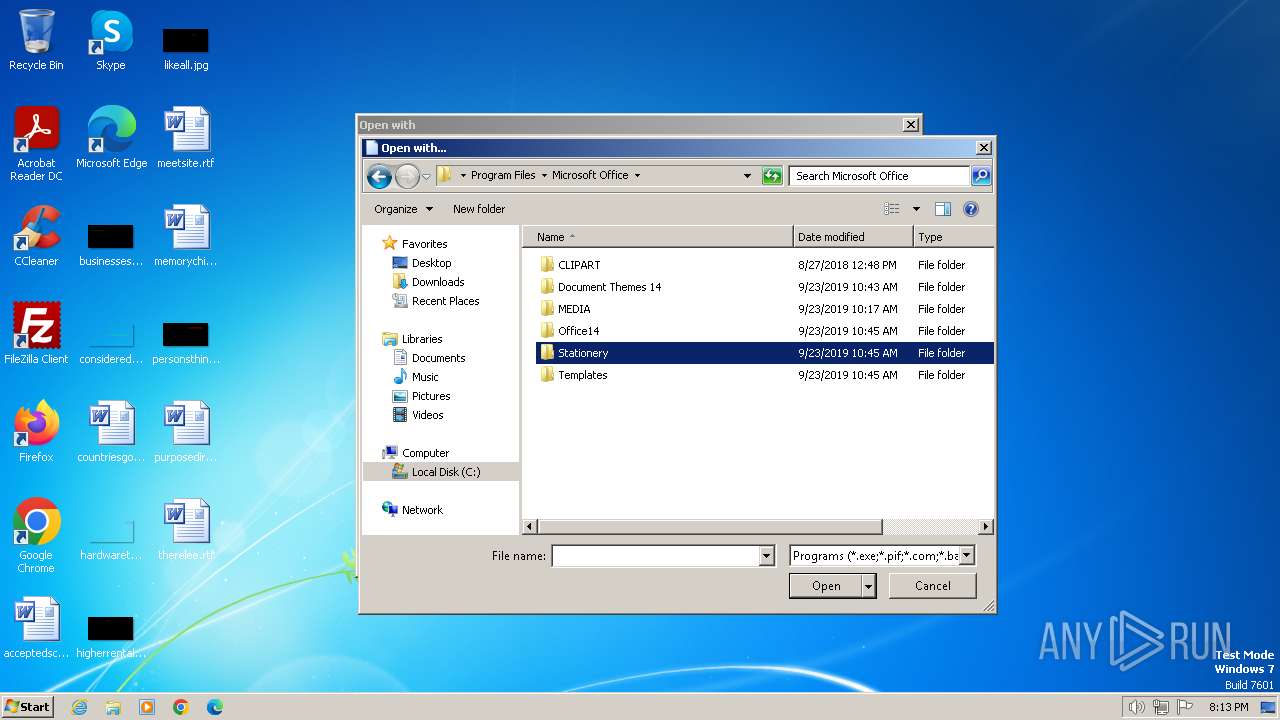
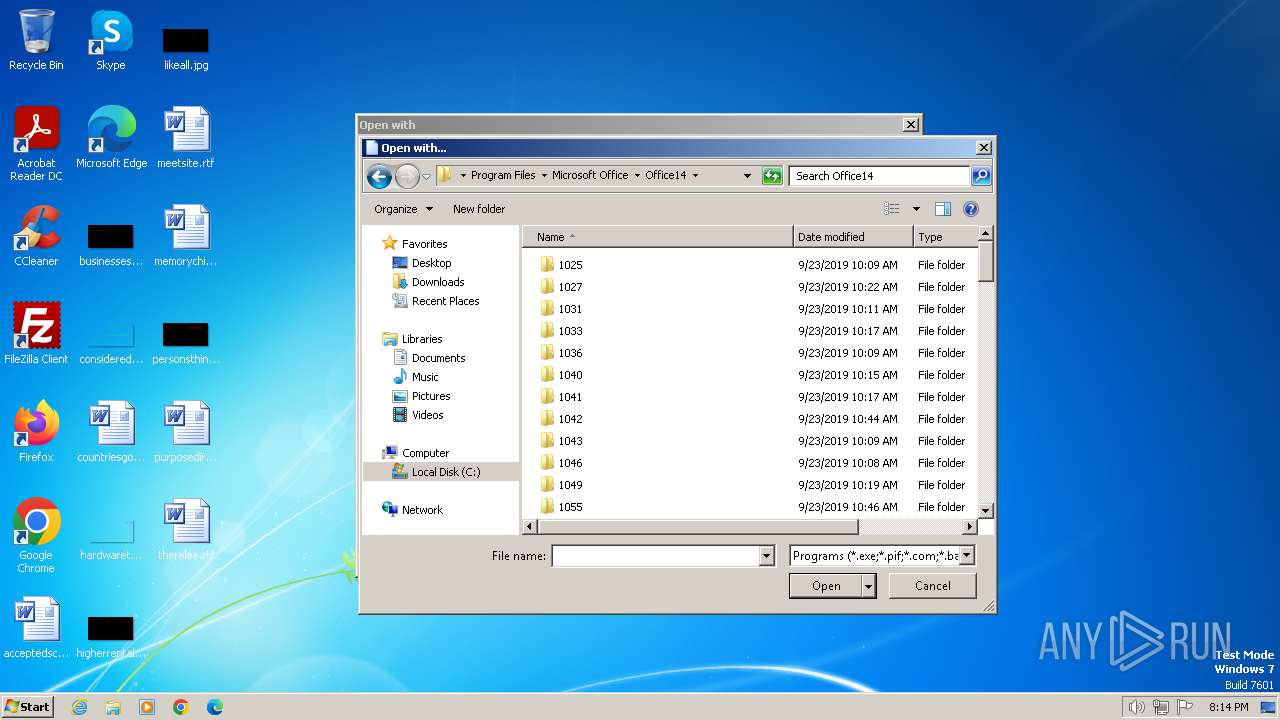
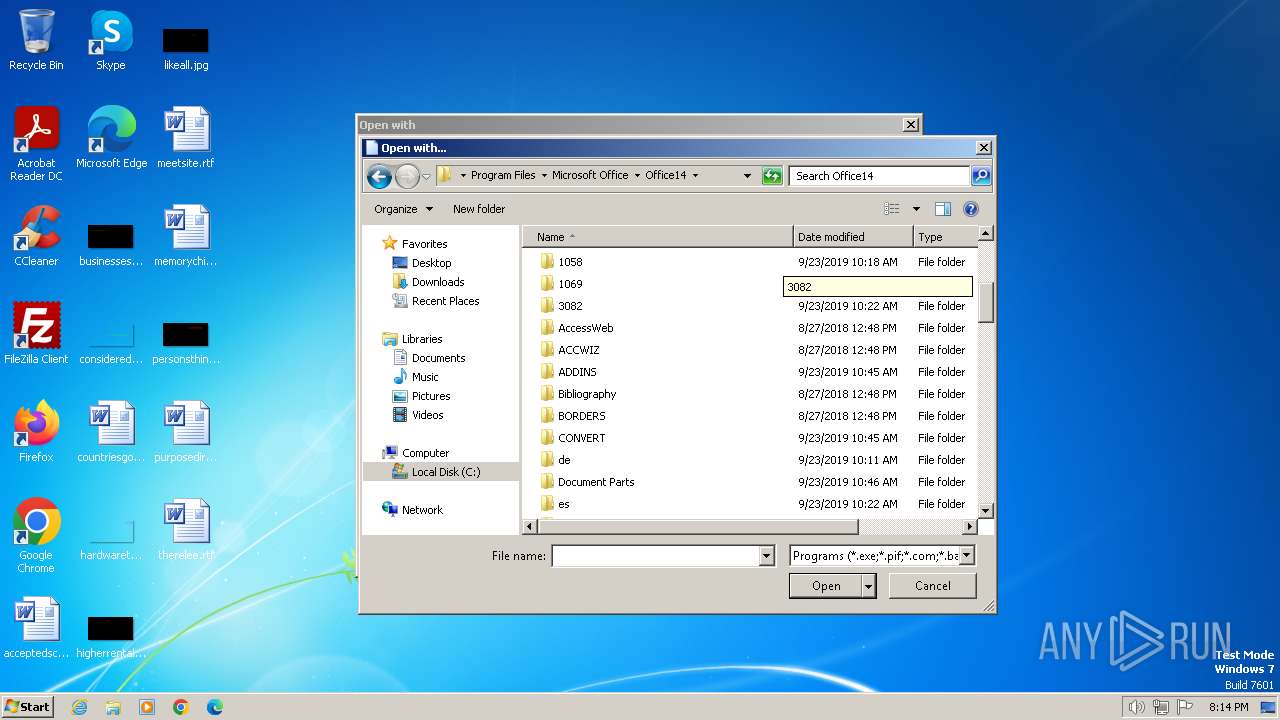
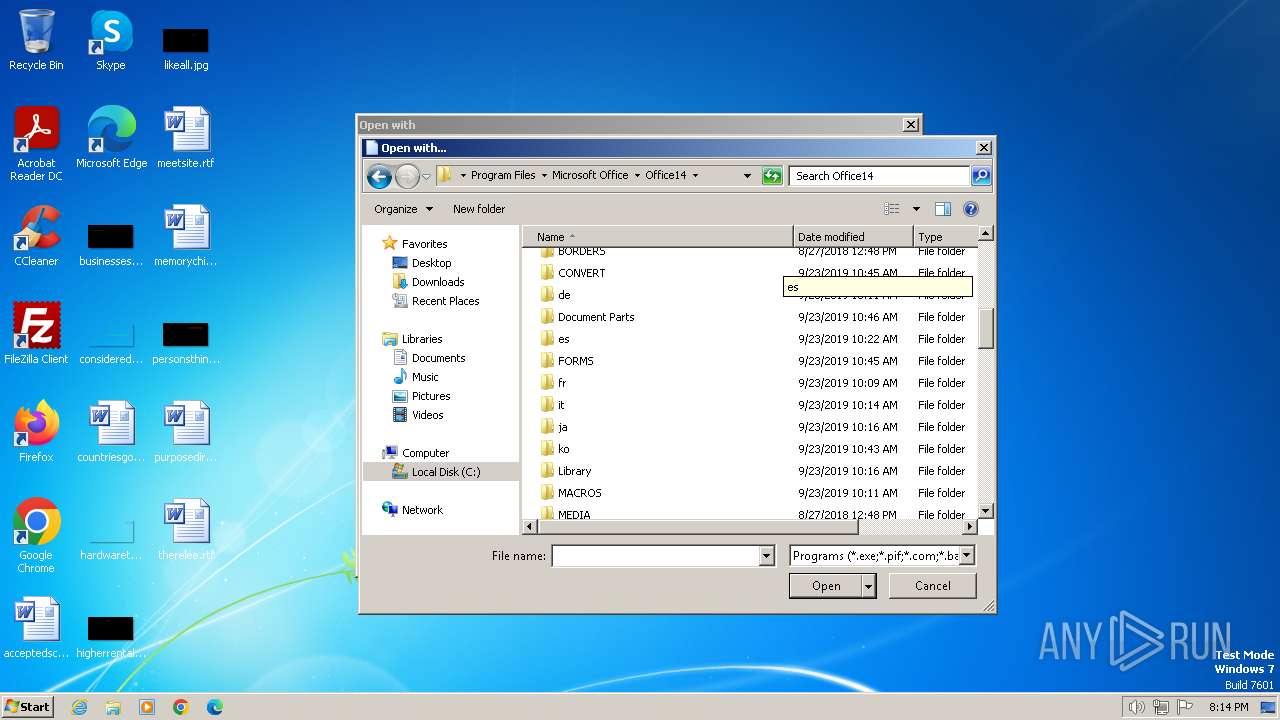
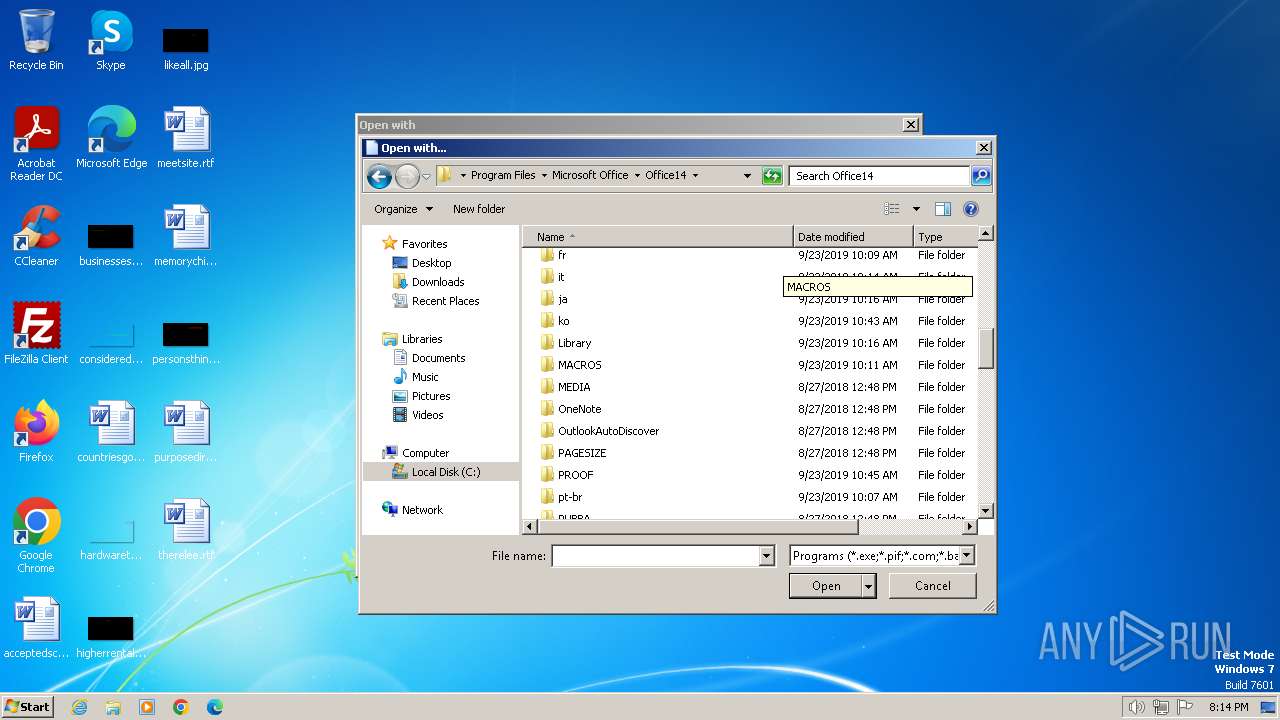
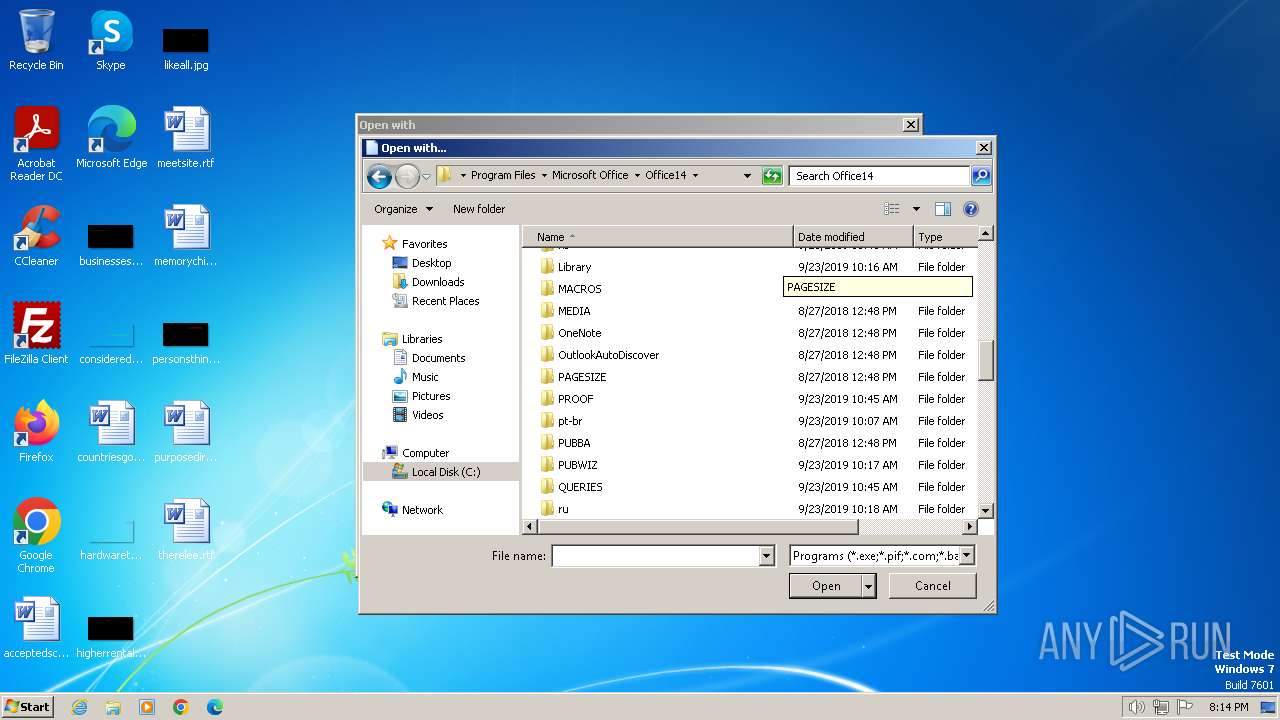
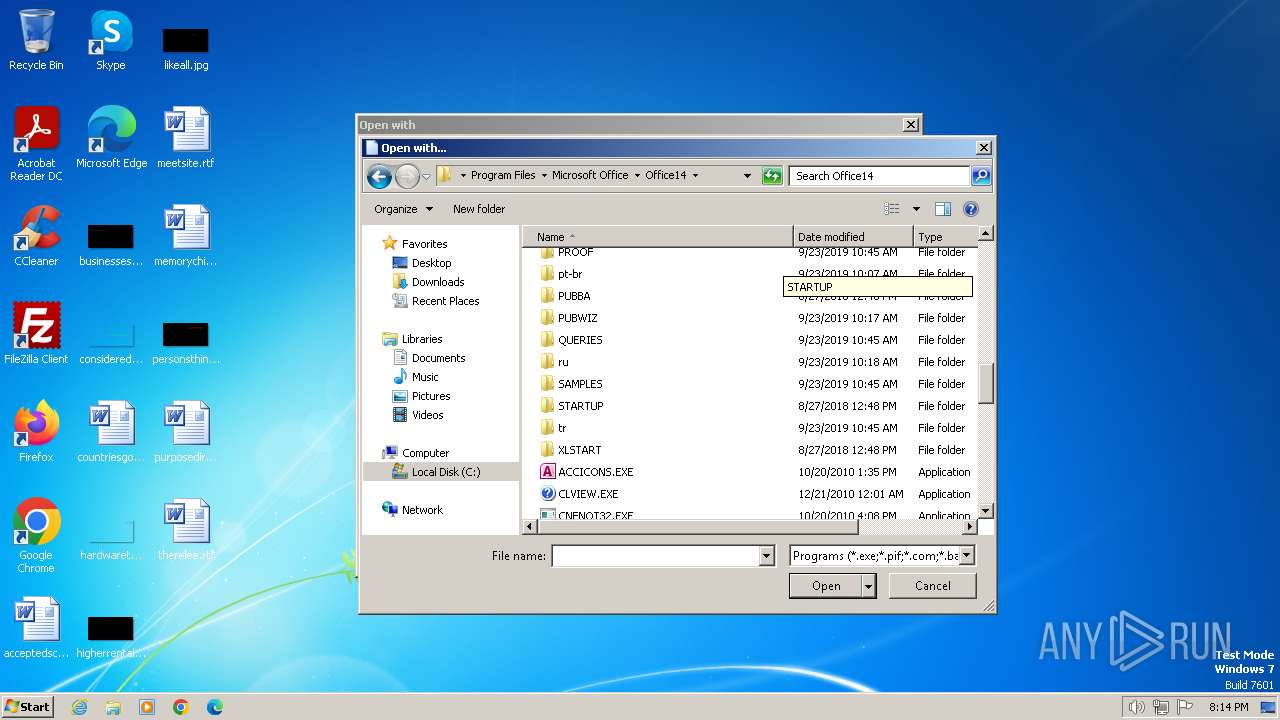
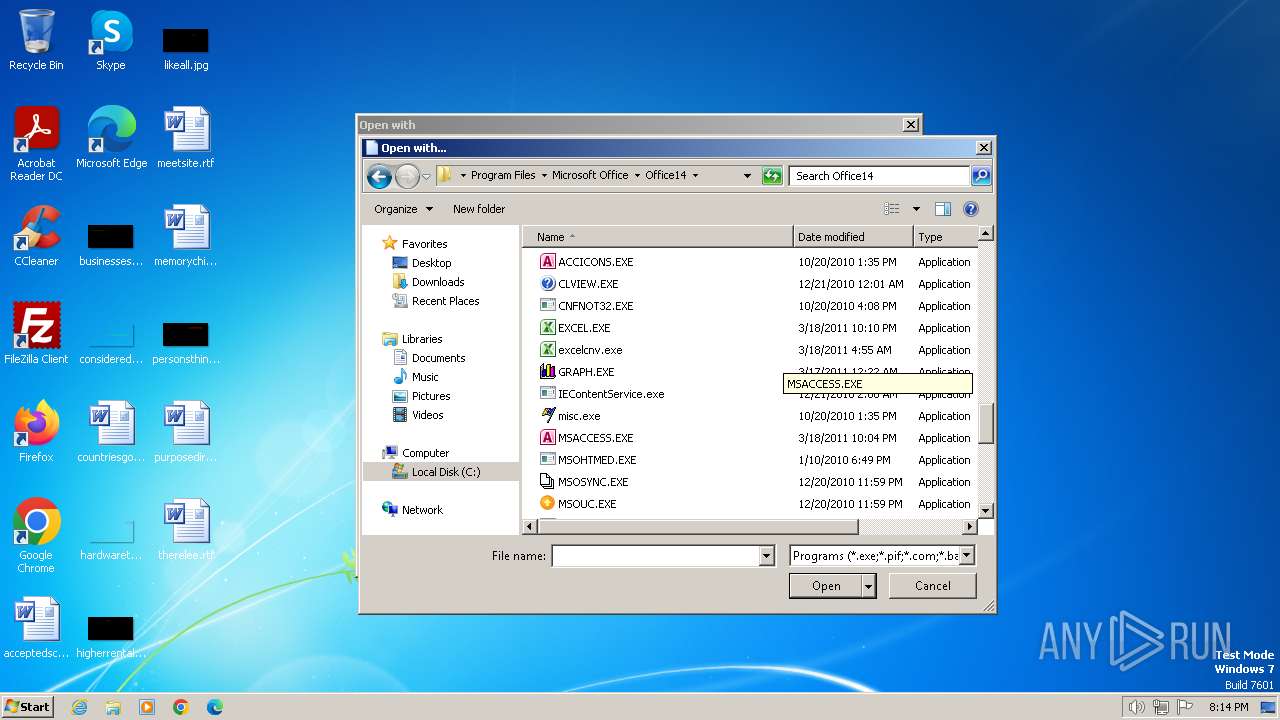
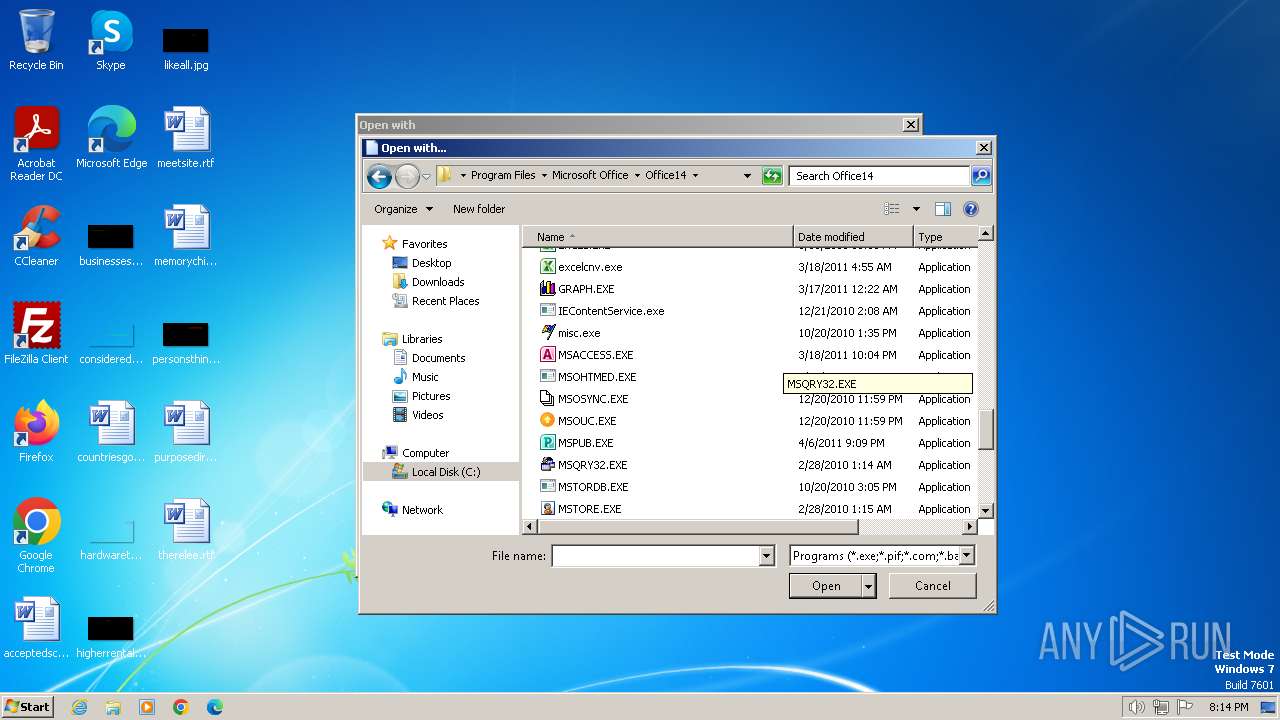
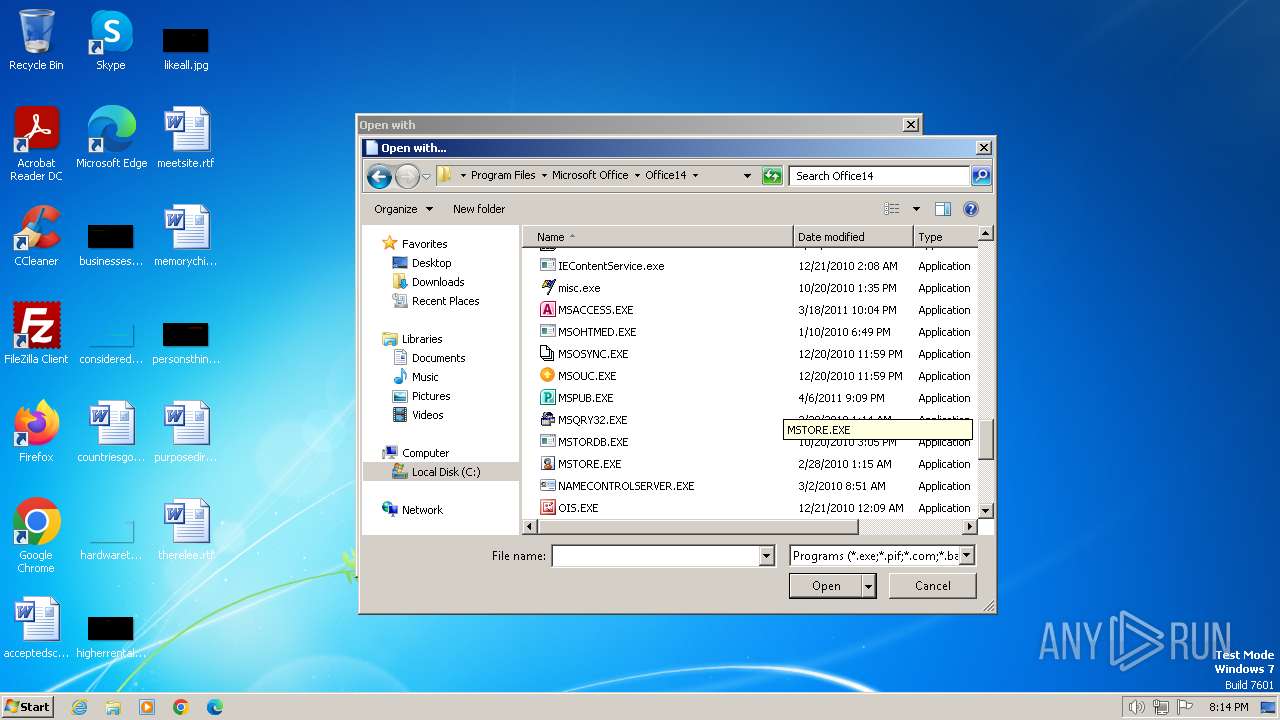
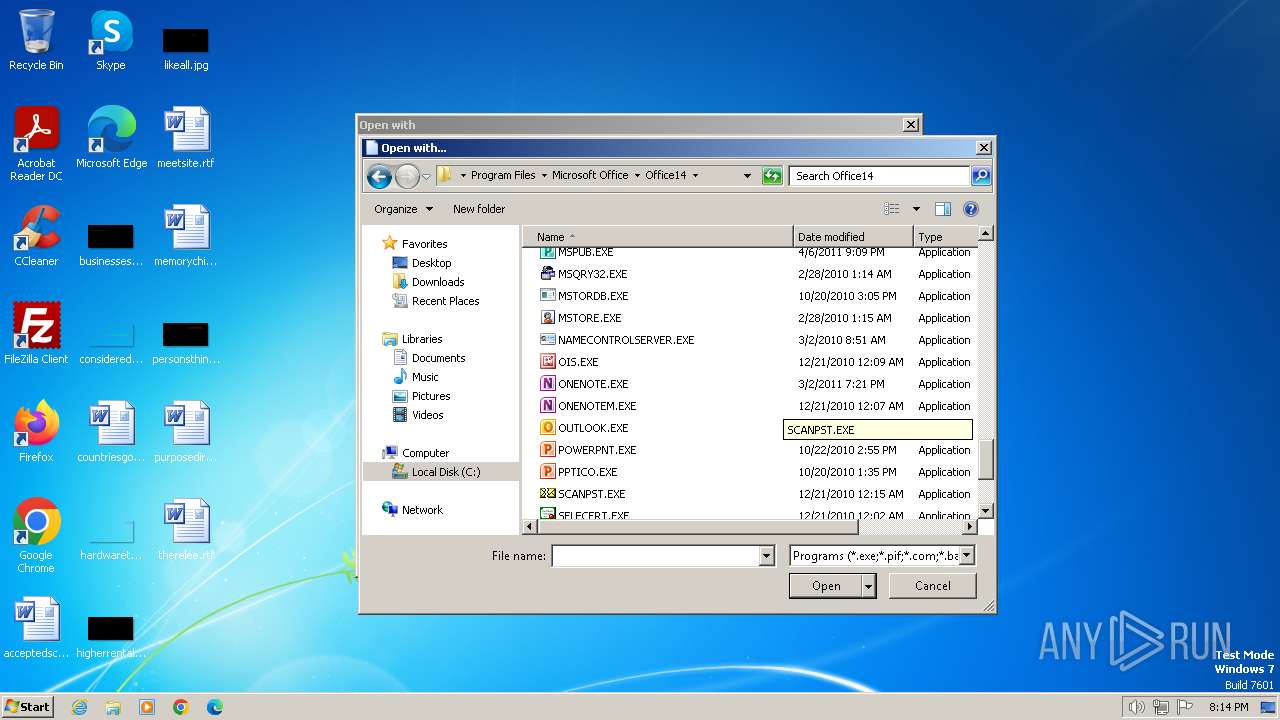
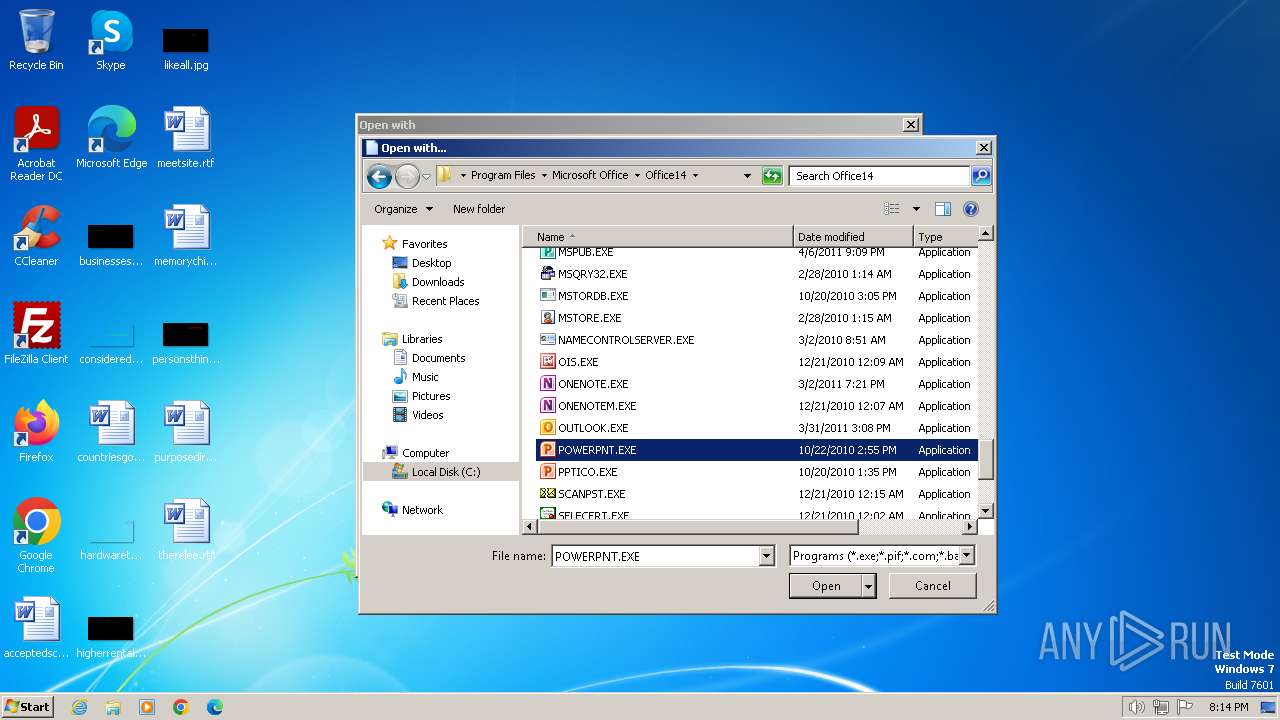
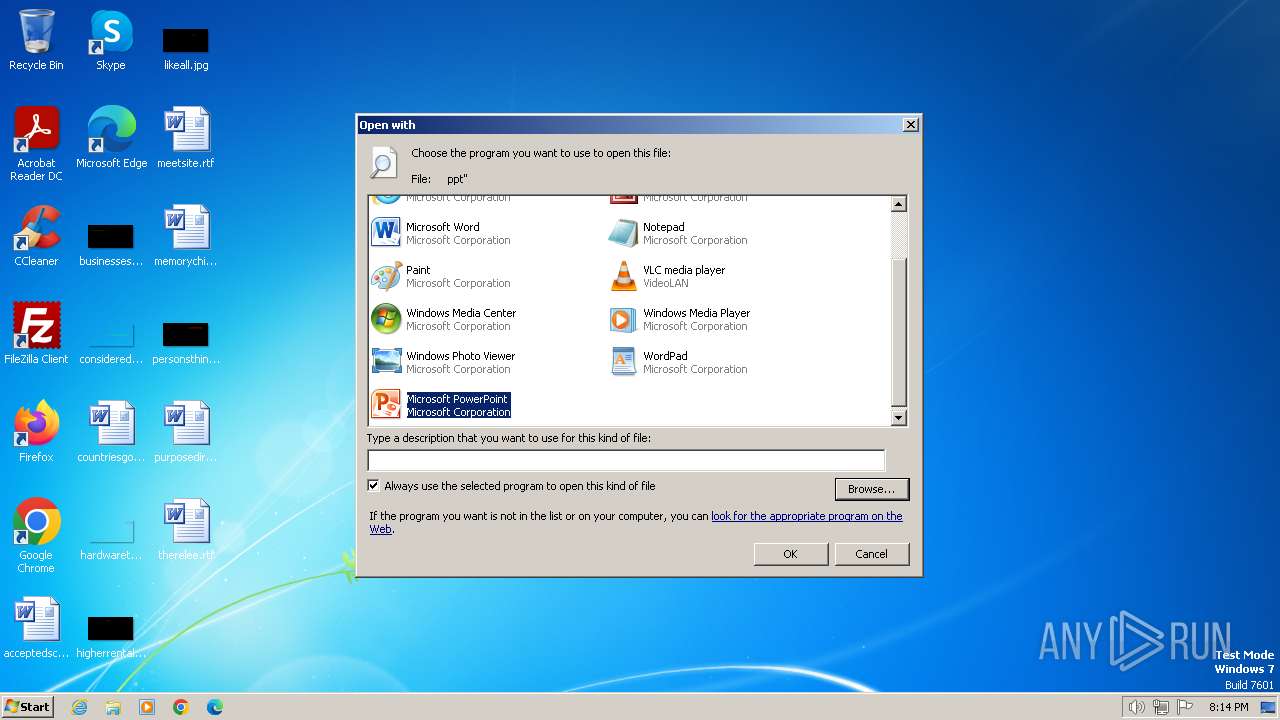
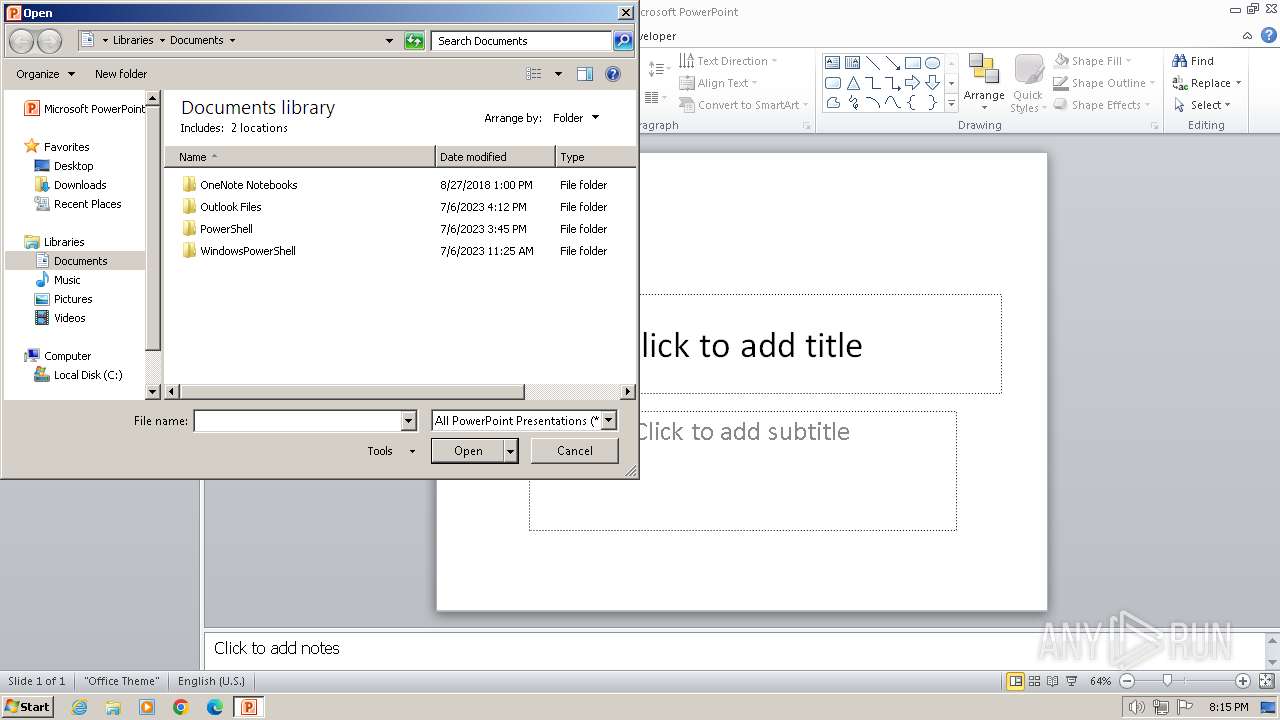
| 2472 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\AppData\Local\Temp\RETO-MALWAREDFIR.ppt.pps/ppt" | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2728 | mSHtA http://12384928198391823%12384928198391823@j.mp/hdkjashdkasbctdgjsa | C:\Windows\System32\mshta.exe | POWERPNT.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2780 | ping | C:\Windows\System32\PING.EXE | — | POWERPNT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
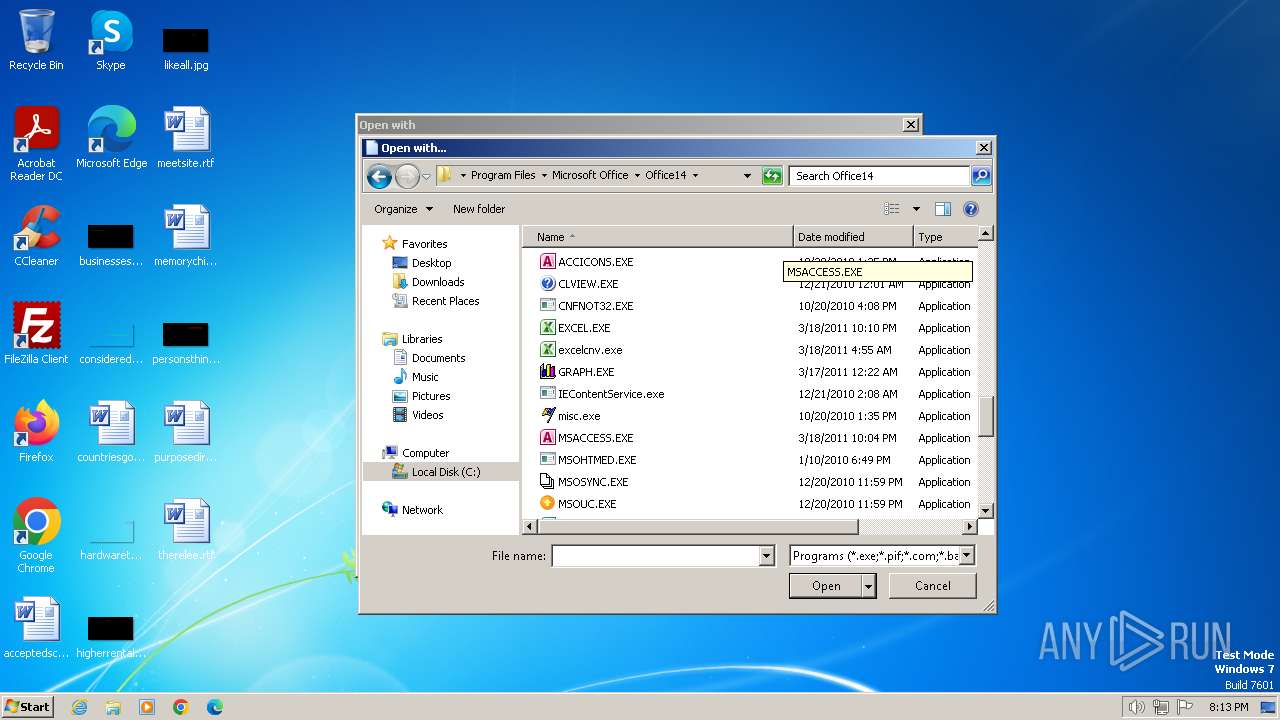
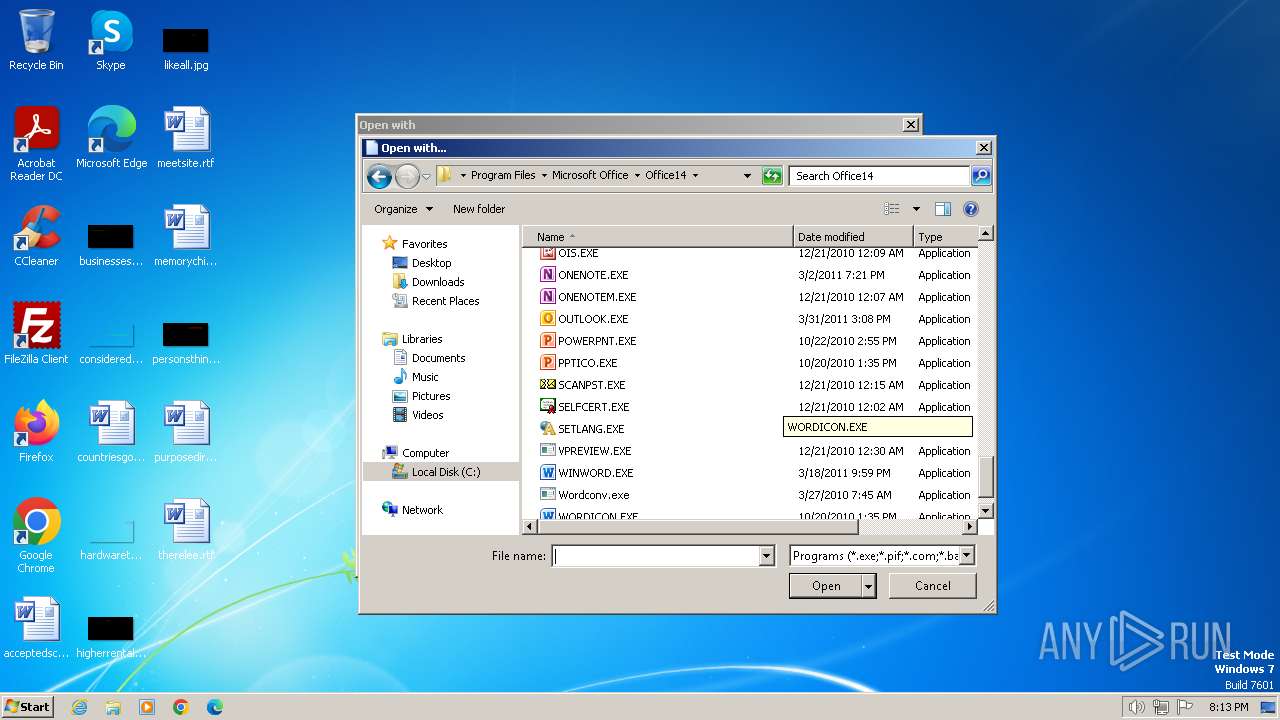
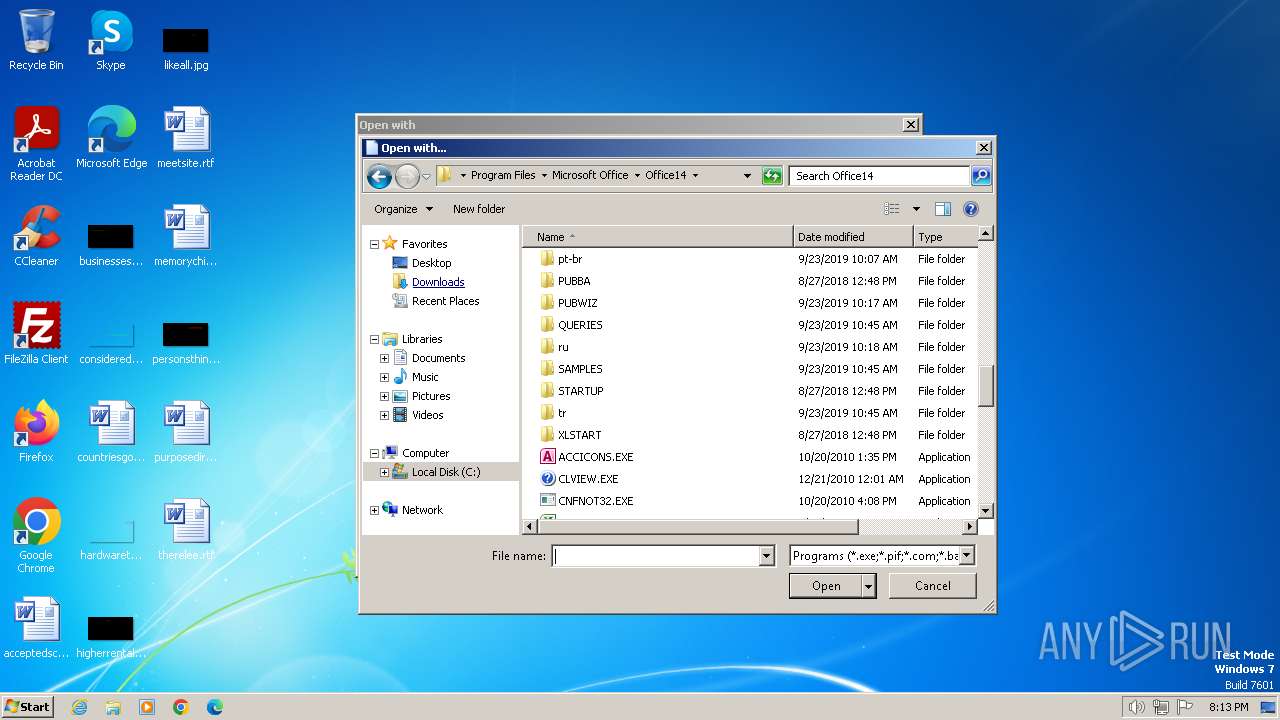
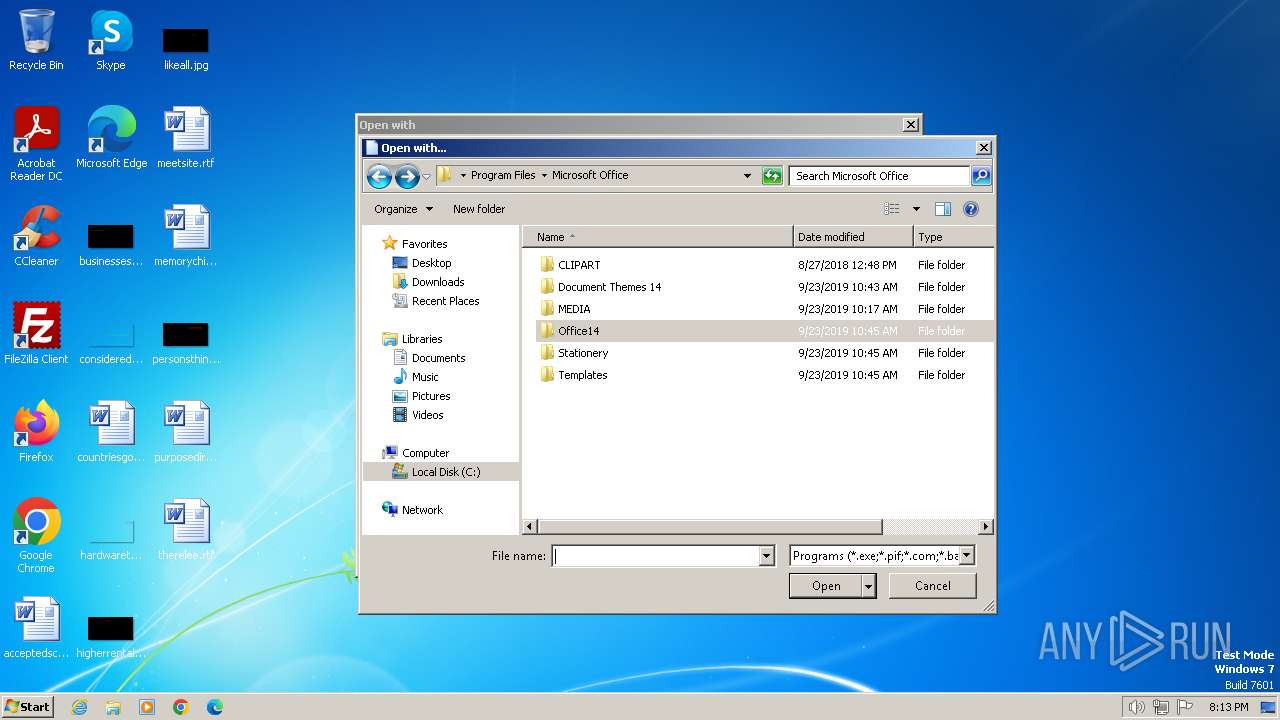
| 3540 | winword | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | POWERPNT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
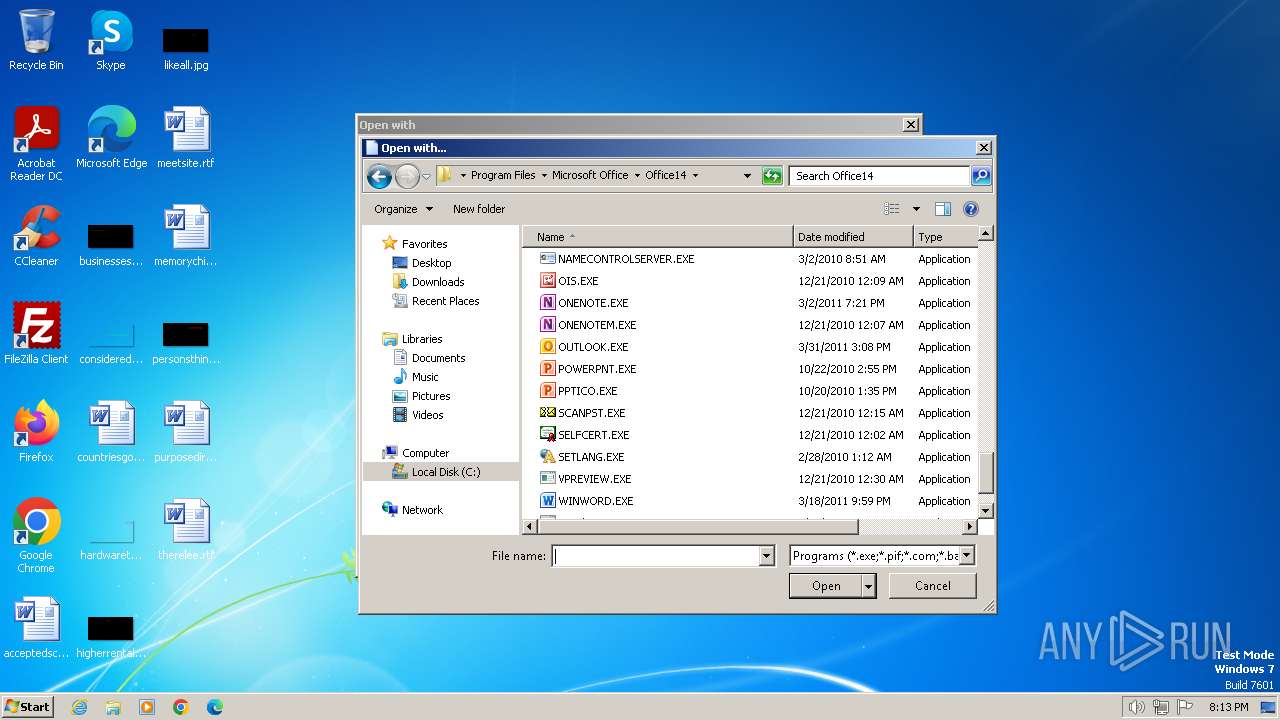
| 3940 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
Total events
27 687
Read events
26 641
Write events
879
Delete events
167
Modification events
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: Firefox | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (2472) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
Executable files
1
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3940 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVR95F8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3540 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR61DE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3940 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:25E5389F6EF0DD19C6AC207B5CCB80EC | SHA256:BDAD20D48E4F875A30F29B4DE3ABAAD05BA56D0ACF60C70490BFA6974A4A8870 | |||
| 3940 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\RETO-MALWAREDFIR.ppt.LNK | binary | |
MD5:85DF4D685F4E2E22EC2CCEC182FC8479 | SHA256:3B0148E989C8B75A91E68194BFA5155265A26D29A435BE55530FF70D0D5AC402 | |||
| 3540 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:41AC11F53F39CAAA866B3F1EA277D584 | SHA256:24B879A7808F59D9222DFC2AA5F5D19AA0D8329ACBBE6FBF421493C3CDEDC8A5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2728 | mshta.exe | GET | — | 67.199.248.17:80 | http://j.mp/hdkjashdkasbctdgjsa | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2728 | mshta.exe | 67.199.248.17:80 | j.mp | GOOGLE-CLOUD-PLATFORM | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
j.mp |
| shared |