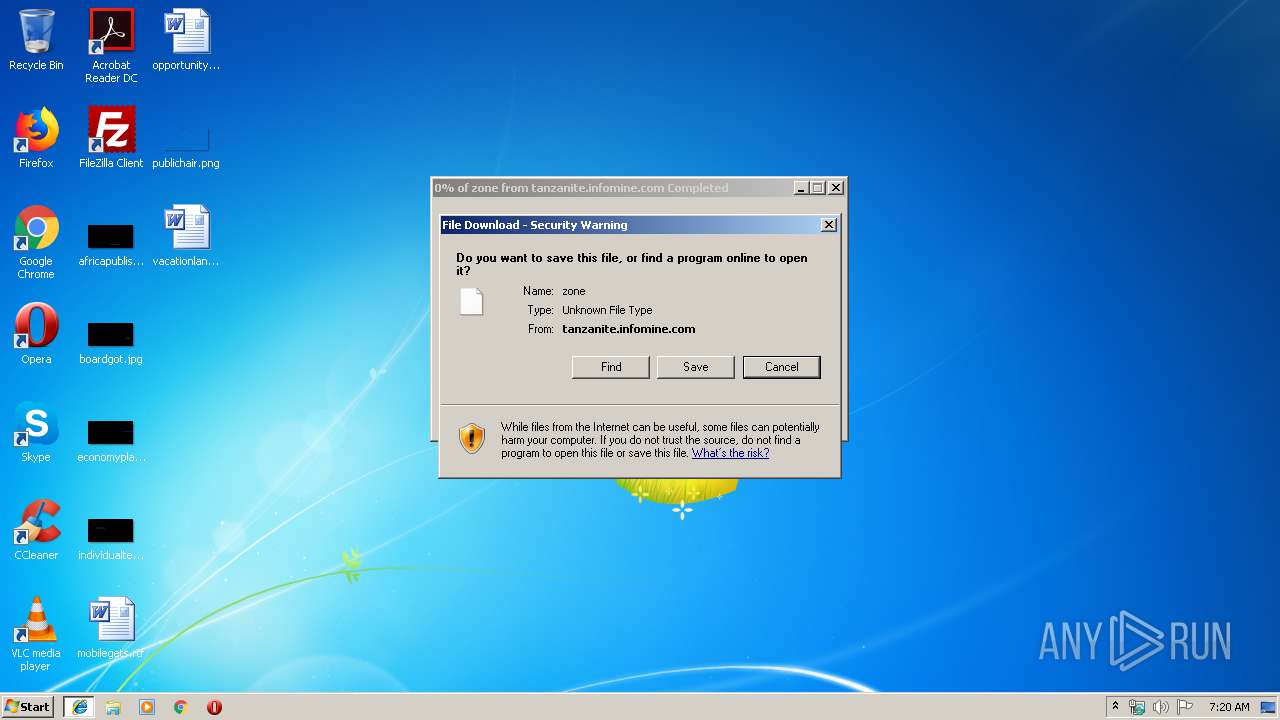
| URL: | http://tanzanite.infomine.com:80/servlet/view/dynamic/javascript/zone?cookied=yes&position=0&os=11&test=false&random=41439723&hostname=192.168.128.14&pid=0&resolution=unsupported&agent=Mozilla/5.0+(Windows+NT+10.0;+Win64;+x64)+AppleWebKit/537.36+(KHTML,+like+Gecko)+Chrome/73.0.3683.103+Safari/537.36&millis=1555303063837&cid=0&lookup=false&ip=192.53.82.13×tamp=20190414213744&referrer=http://mining.com/las-bambas-copper-markets-68-day-blockade/?utm_source=digest-en-mining-190414&utm_medium=email&utm_campaign=digest&default=false&zid=747&browser=17&language=en&mid=0&refresh=0 |
| Full analysis: | https://app.any.run/tasks/d8b93b21-b673-4b5f-a849-723184cf68bd |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 06:20:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F297FDE4D37890C214520303CE41BBD5 |
| SHA1: | 58A3FF08F8ADF22027FC97ED674052F461368E53 |
| SHA256: | A1D7CC91521829618B7681A86EA915DFD8484EB215A9101402A66E82FA83B414 |
| SSDEEP: | 12:DlPnEVQiWMwLmOmRMZ0Y/jucKlgrdSFFTeEf7lU7Q3m4cHRAK:1R4OmquY/SllIQTJf7lZxcH1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3456)
Creates files in the user directory
- firefox.exe (PID: 2464)
- iexplore.exe (PID: 3456)
Changes internet zones settings
- iexplore.exe (PID: 2964)
Reads settings of System Certificates
- pingsender.exe (PID: 2404)
Application launched itself
- firefox.exe (PID: 2464)
- iexplore.exe (PID: 2964)
Adds / modifies Windows certificates
- pingsender.exe (PID: 2404)
Changes settings of System certificates
- pingsender.exe (PID: 2404)
Reads CPU info
- firefox.exe (PID: 2464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 704 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2464.6.1075069060\1533341948" -childID 1 -isForBrowser -prefsHandle 1600 -prefMapHandle 1560 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2464 "\\.\pipe\gecko-crash-server-pipe.2464" 1612 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2464.13.168114783\1927527248" -childID 2 -isForBrowser -prefsHandle 2568 -prefMapHandle 2572 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2464 "\\.\pipe\gecko-crash-server-pipe.2464" 2584 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/649a5ec6-9d55-45e4-8b8e-6fafc595d59a/main/Firefox/65.0.2/release/20190225143501?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\649a5ec6-9d55-45e4-8b8e-6fafc595d59a | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Internet Explorer\iexplore.exe" http://tanzanite.infomine.com:80/servlet/view/dynamic/javascript/zone?cookied=yes&position=0&os=11&test=false&random=41439723&hostname=192.168.128.14&pid=0&resolution=unsupported&agent=Mozilla/5.0+(Windows+NT+10.0;+Win64;+x64)+AppleWebKit/537.36+(KHTML,+like+Gecko)+Chrome/73.0.3683.103+Safari/537.36&millis=1555303063837&cid=0&lookup=false&ip=192.53.82.13×tamp=20190414213744&referrer=http://mining.com/las-bambas-copper-markets-68-day-blockade/?utm_source=digest-en-mining-190414&utm_medium=email&utm_campaign=digest&default=false&zid=747&browser=17&language=en&mid=0&refresh=0 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2464.20.1517770722\1154489706" -childID 3 -isForBrowser -prefsHandle 3424 -prefMapHandle 3428 -prefsLen 5882 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2464 "\\.\pipe\gecko-crash-server-pipe.2464" 3440 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2464.0.70399848\501835576" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 2464 "\\.\pipe\gecko-crash-server-pipe.2464" 1092 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3456 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2964 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
938
Read events
881
Write events
54
Delete events
3
Modification events
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {927D54EF-5F46-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307040001000F00060014002100B401 | |||
Executable files
0
Suspicious files
215
Text files
80
Unknown types
112
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0A5A09505F731452.TMP | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFE8AE0ECAAA82E593.TMP | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{927D54EF-5F46-11E9-B3B3-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2464 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2464 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2464 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\trash17166 | — | |
MD5:— | SHA256:— | |||
| 2464 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2464 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
115
TCP/UDP connections
137
DNS requests
224
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
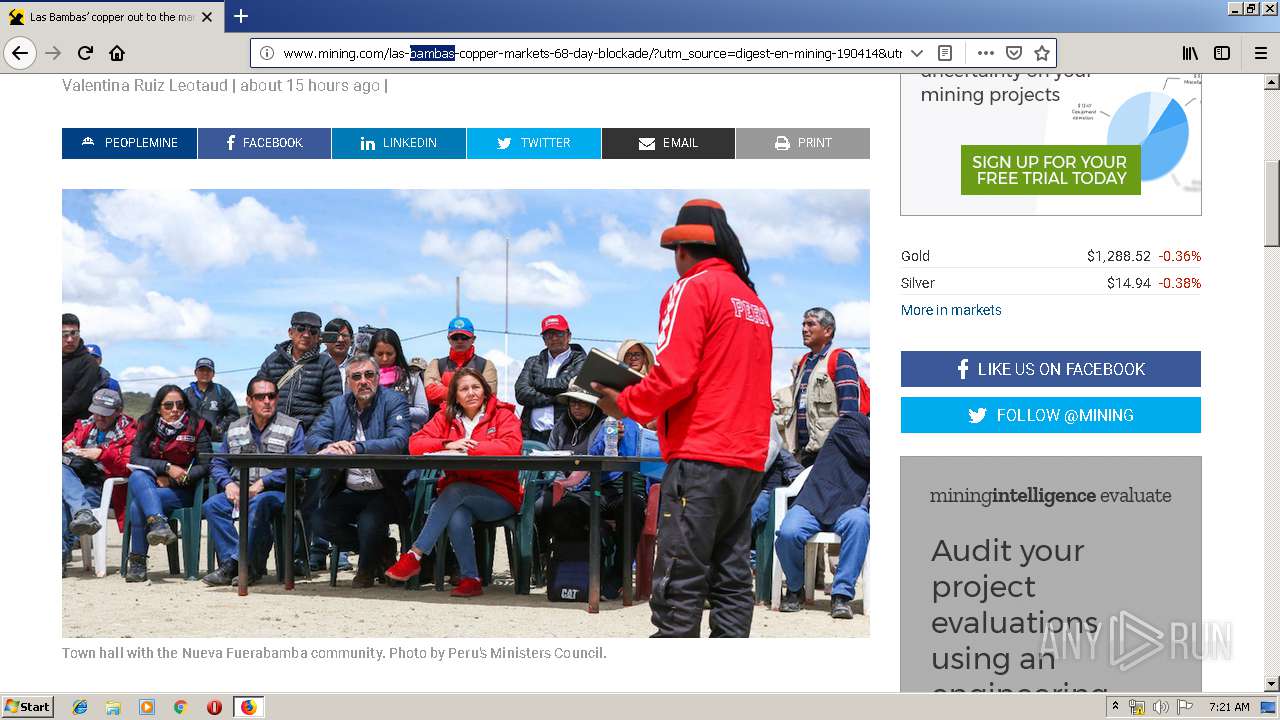
2464 | firefox.exe | GET | 200 | 104.16.108.75:80 | http://www.mining.com/las-bambas-copper-markets-68-day-blockade/?utm_source=digest-en-mining-190414&utm_medium=email&utm_campaign=digest | US | html | 15.5 Kb | shared |
2464 | firefox.exe | POST | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | GET | 200 | 104.16.108.75:80 | http://www.mining.com/wp-content/themes/Kessel/css/style.css | US | text | 7.91 Kb | shared |
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | GET | 200 | 216.58.205.228:80 | http://www.google.com/jsapi?ver=4.9.8 | US | html | 6.12 Kb | malicious |
2464 | firefox.exe | GET | 200 | 104.16.108.75:80 | http://www.mining.com/wp-content/themes/Kessel/css/bootstrap.min.css | US | text | 27.1 Kb | shared |
2964 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2464 | firefox.exe | GET | 200 | 104.16.108.75:80 | http://www.mining.com/wp-content/themes/Kessel/css/theme.min.css | US | text | 21.4 Kb | shared |
2464 | firefox.exe | GET | 200 | 104.16.108.75:80 | http://www.mining.com/wp-content/plugins/inline-google-spreadsheet-viewer/igsv-datatables.js?ver=4.9.8 | US | text | 1.02 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2464 | firefox.exe | 52.222.173.224:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2464 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2464 | firefox.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2464 | firefox.exe | 173.223.11.150:80 | detectportal.firefox.com | Akamai International B.V. | NL | whitelisted |
2464 | firefox.exe | 52.222.162.48:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2464 | firefox.exe | 172.217.18.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2464 | firefox.exe | 104.20.42.93:443 | cdn.datatables.net | Cloudflare Inc | US | shared |
2464 | firefox.exe | 216.58.205.228:80 | www.google.com | Google Inc. | US | whitelisted |
2464 | firefox.exe | 54.186.163.246:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tanzanite.infomine.com |
| unknown |
www.bing.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |