| File name: | malsample |
| Full analysis: | https://app.any.run/tasks/b229c904-131d-454a-b023-b34b2351485e |
| Verdict: | Malicious activity |
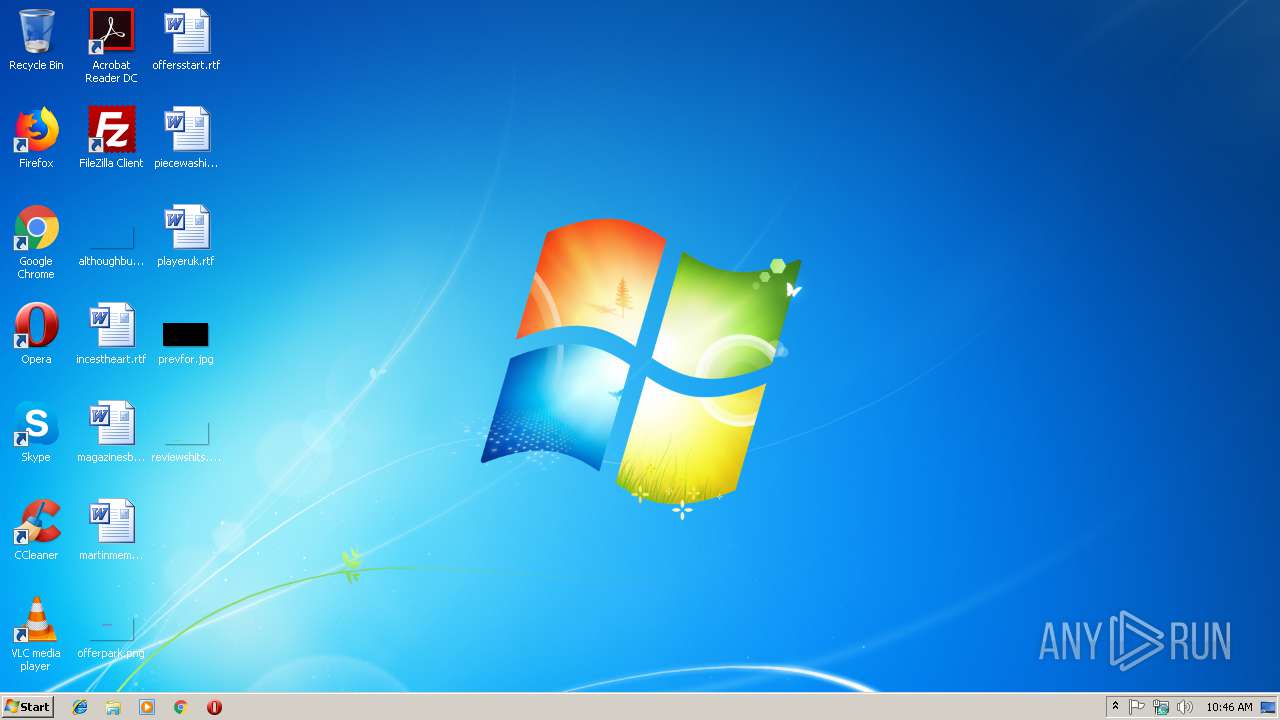
| Analysis date: | December 06, 2018, 10:46:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 73386CFDC45A6862BE0D29C2AC9B85C6 |
| SHA1: | B68ABB20D2A18311363D3D5DC33B11EAB62A9773 |
| SHA256: | A1D64E4BF423CFD50B1F8F82B835F1DCE31B2BD3EEDEC5E1D241AA71DB6AE89F |
| SSDEEP: | 24576:e8RLtIMLlqYumQvYEYEol6iSFWMXOg+/EGZCrv8s7eja:b9xpqYumNE2l6NFWM+5HgkA |
MALICIOUS
Application was dropped or rewritten from another process
- remover.exe (PID: 2940)
- MisoFileDown.exe (PID: 4012)
Changes the autorun value in the registry
- malsample.exe (PID: 2300)
SUSPICIOUS
Creates files in the program directory
- MisoFileDown.exe (PID: 4012)
- malsample.exe (PID: 2300)
Creates files in the user directory
- MisoFileDown.exe (PID: 4012)
Connects to unusual port
- MisoFileDown.exe (PID: 4012)
Creates files in the Windows directory
- malsample.exe (PID: 2300)
Executable content was dropped or overwritten
- malsample.exe (PID: 2300)
Reads internet explorer settings
- MisoFileDown.exe (PID: 4012)
Creates a software uninstall entry
- malsample.exe (PID: 2300)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:06:06 23:43:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 308224 |
| UninitializedDataSize: | 8192 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jun-2009 21:43:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Jun-2009 21:43:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4388 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00048C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.79628 |
.ndata | 0x00052000 | 0x00040000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00092000 | 0x000006A8 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14628 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10609 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.06096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2300 | "C:\Users\admin\AppData\Local\Temp\malsample.exe" | C:\Users\admin\AppData\Local\Temp\malsample.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2940 | C:\Windows\system32\remover.exe C:\Users\admin\AppData\Local\Temp\malsample.exe | C:\Windows\system32\remover.exe | — | malsample.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2968 | "C:\Users\admin\AppData\Local\Temp\malsample.exe" | C:\Users\admin\AppData\Local\Temp\malsample.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4012 | "C:\Program Files\MisoFile\MisoFileDown.exe" malsample.exe first | C:\Program Files\MisoFile\MisoFileDown.exe | malsample.exe | ||||||||||||
User: admin Company: TODO: <회사 이름> Integrity Level: HIGH Description: TODO: <파일 설명> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
492
Read events
463
Write events
29
Delete events
0
Modification events
| (PID) Process: | (2300) malsample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MisoFileService |
Value: C:\Program Files\MisoFile\MisoFileService.exe run | |||
| (PID) Process: | (2300) malsample.exe | Key: | HKEY_CURRENT_USER\Software\MisoFile |
| Operation: | write | Name: | SetUpService |
Value: true | |||
| (PID) Process: | (2300) malsample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MisoFile |
| Operation: | write | Name: | DisplayName |
Value: ¹Ì¼ÒÆÄÀÏ | |||
| (PID) Process: | (2300) malsample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MisoFile |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\MisoFile\Uninstall.exe | |||
| (PID) Process: | (2300) malsample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MisoFile |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Windows\system32\misofile.ico | |||
| (PID) Process: | (2300) malsample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MisoFile |
| Operation: | write | Name: | Publisher |
Value: MediaSave | |||
| (PID) Process: | (2300) malsample.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-500\Software\MisoFile |
| Operation: | write | Name: | SetUpService |
Value: true | |||
| (PID) Process: | (4012) MisoFileDown.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4012) MisoFileDown.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4012) MisoFileDown.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MisoFileDown_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4012 | MisoFileDown.exe | C:\Program Files\MisoFile\bundle.ini | — | |
MD5:— | SHA256:— | |||
| 2300 | malsample.exe | C:\Program Files\MisoFile\MisoFileDown.exe | executable | |
MD5:— | SHA256:— | |||
| 2300 | malsample.exe | C:\Windows\system32\remover.exe | executable | |
MD5:— | SHA256:— | |||
| 2300 | malsample.exe | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 4012 | MisoFileDown.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\ww1_misofile_com[1].txt | html | |
MD5:— | SHA256:— | |||
| 2300 | malsample.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 2300 | malsample.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | log | |
MD5:— | SHA256:— | |||
| 4012 | MisoFileDown.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@misofile[1].txt | text | |
MD5:— | SHA256:— | |||
| 4012 | MisoFileDown.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\install[1].php | html | |
MD5:— | SHA256:— | |||
| 2300 | malsample.exe | C:\Program Files\MisoFile\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4012 | MisoFileDown.exe | GET | 200 | 72.52.4.90:80 | http://ww1.misofile.com/?sub1=287d59c4-f944-11e8-ac94-00c48f9f556d | US | html | 19.8 Kb | malicious |
4012 | MisoFileDown.exe | GET | 200 | 72.52.4.90:80 | http://ww1.misofile.com/?sub1=287d59c4-f944-11e8-ac94-00c48f9f556d | US | html | 19.8 Kb | malicious |
4012 | MisoFileDown.exe | GET | 302 | 151.106.5.168:80 | http://misofile.com/app/bundle/bundle.ini | US | text | 11 b | malicious |
4012 | MisoFileDown.exe | GET | 302 | 151.106.5.168:80 | http://misofile.com/log/install.php?js=eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJqcyI6MX0.fADWc9hUOlh58R9UzufQBROmie3I7c7vE835oE6YmU4&pds_no=&uuid=287d8200-f944-11e8-8bf7-00c4971753bd | US | text | 11 b | malicious |
4012 | MisoFileDown.exe | GET | 200 | 151.106.5.168:80 | http://misofile.com/log/install.php?pds_no= | US | html | 313 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4012 | MisoFileDown.exe | 151.106.5.168:80 | misofile.com | — | US | unknown |
4012 | MisoFileDown.exe | 72.52.4.90:80 | ww1.misofile.com | Akamai Technologies, Inc. | US | whitelisted |
4012 | MisoFileDown.exe | 218.146.255.198:4011 | — | Korea Telecom | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
misofile.com |
| unknown |
ww1.misofile.com |
| malicious |