| File name: | neta_run.exe |
| Full analysis: | https://app.any.run/tasks/a051928e-6095-4525-b9fb-449f601e4b68 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 17:14:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 52E60FE418B2905FB1BD002D739E58EF |
| SHA1: | 141A31F34FC83AC6B09B121079954ECE39133EA6 |
| SHA256: | A1C57628D78FCD6E627FD6D06508710CBC6FBC4D5C612A6C2BBD260DDB71E168 |
| SSDEEP: | 24576:ATTSLVxMMyK//+CMLt8MXtDC6ZdZKK1pJSj:yTQVwK3+pyMXNC4ZKqA |
MALICIOUS
Application was dropped or rewritten from another process
- cort.exe (PID: 4068)
- w2c.exe (PID: 3720)
- down.exe (PID: 2944)
- down.exe (PID: 4024)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2948)
- cmd.exe (PID: 3828)
SUSPICIOUS
Executable content was dropped or overwritten
- xcopy.exe (PID: 3332)
- neta_run.exe (PID: 1352)
- xcopy.exe (PID: 2868)
- xcopy.exe (PID: 3920)
Creates files in the Windows directory
- xcopy.exe (PID: 2868)
- xcopy.exe (PID: 3332)
Creates files in the user directory
- xcopy.exe (PID: 3920)
Starts CMD.EXE for commands execution
- w2c.exe (PID: 3720)
- neta_run.exe (PID: 1352)
- cort.exe (PID: 4068)
Executes scripts
- cmd.exe (PID: 2948)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3828)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 3828)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:18:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 67584 |
| InitializedDataSize: | 863744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 12.23.72 |
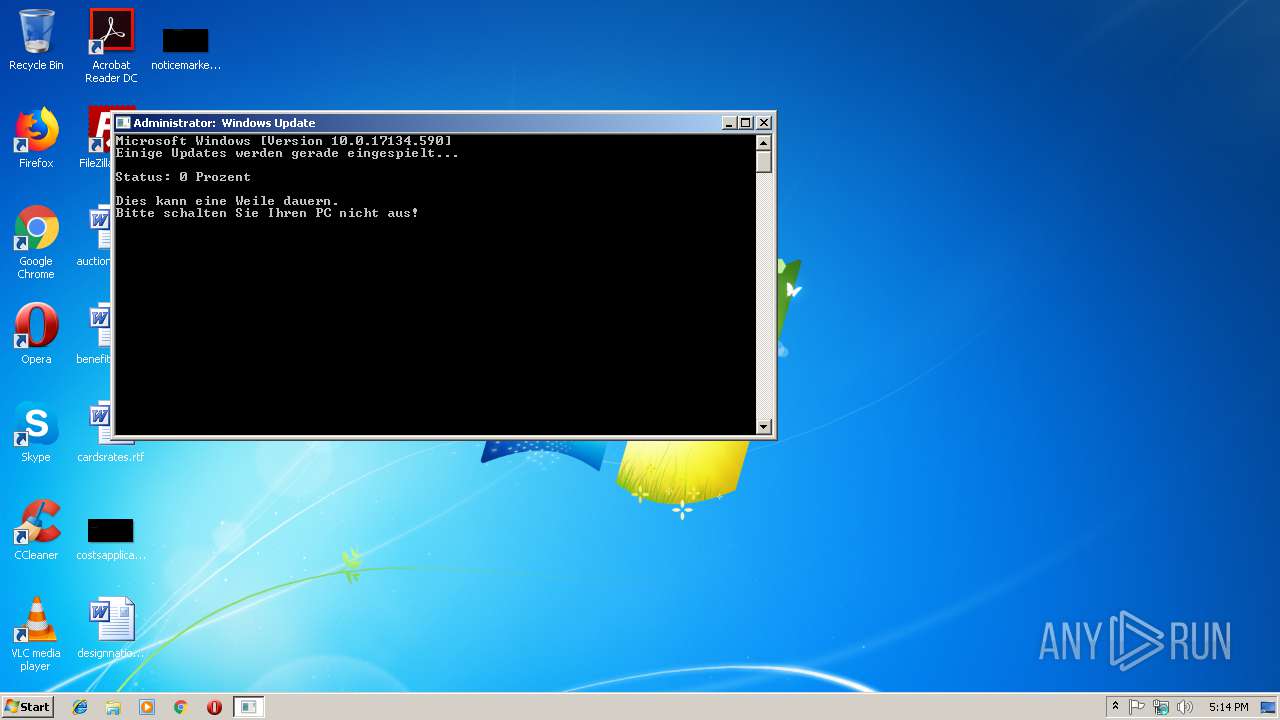
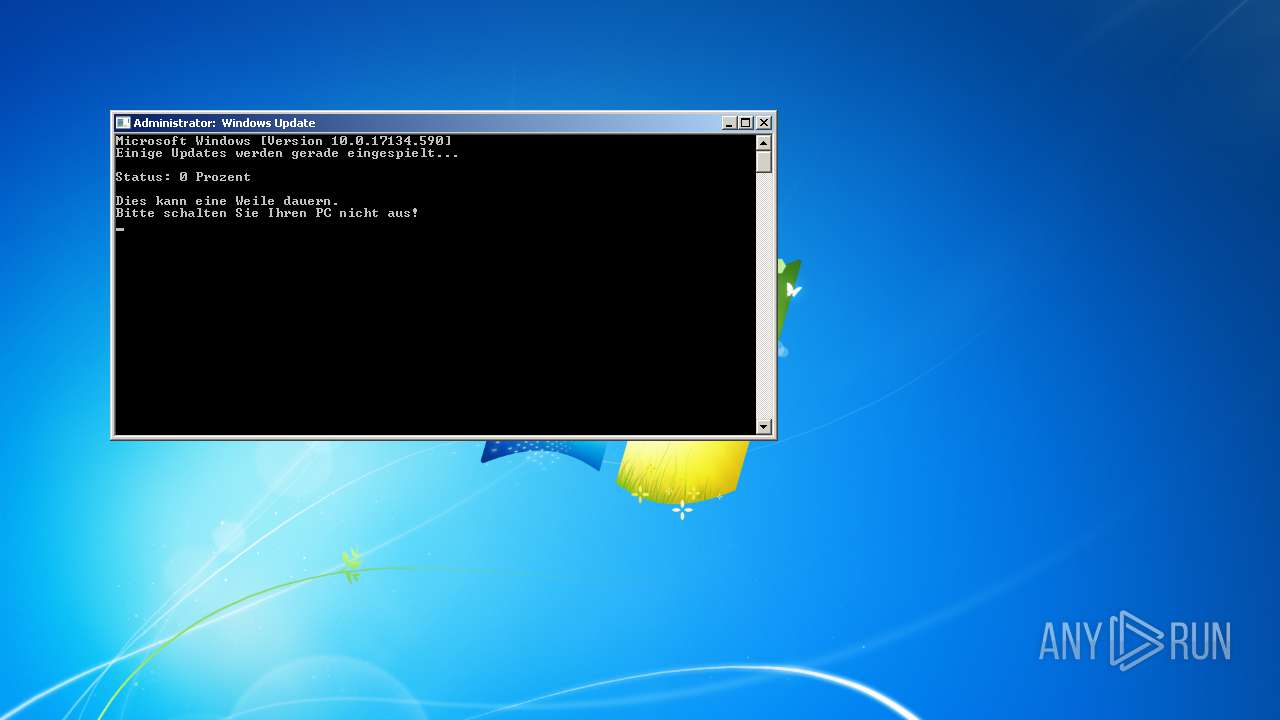
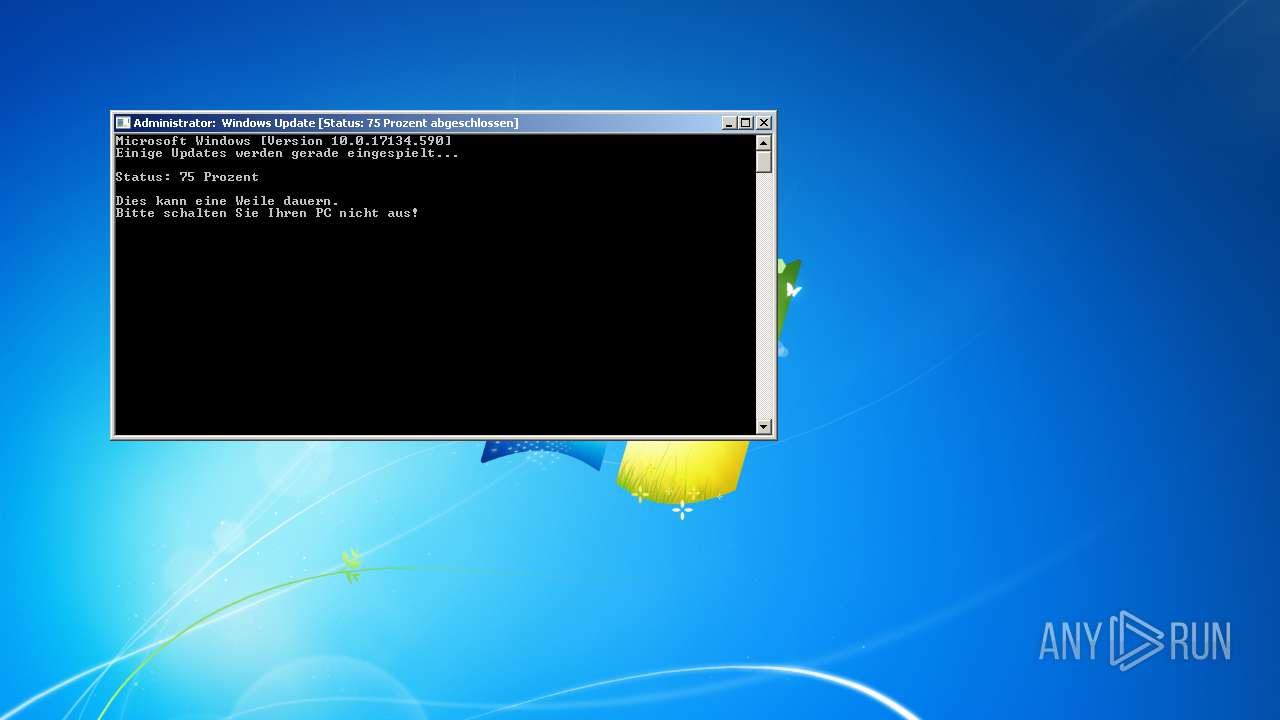
| ProductName: | Windows Update Service |
| OriginalFileName: | wus.exe |
| FileDescription: | Windows Update Service |
| CompanyName: | Microsoft Corp. |
| LegalCopyright: | (c) Microsoft Corp. 2019 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2018 20:18:00 |
| Detected languages: |
|
| FileVersion: | 12.23.72 |
| ProductName: | Windows Update Service |
| OriginalFilename: | wus.exe |
| FileDescription: | Windows Update Service |
| CompanyName: | Microsoft Corp. |
| LegalCopyright: | (c) Microsoft Corp. 2019 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2018 20:18:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x000037F0 | 0x00003800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.61236 |
.text | 0x00005000 | 0x0000CFA2 | 0x0000D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58582 |
.rdata | 0x00012000 | 0x000033A0 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11024 |
.data | 0x00016000 | 0x00001724 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93394 |
.rsrc | 0x00018000 | 0x000CE618 | 0x000CE800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.6938 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.00696 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.07409 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.07276 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.09169 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.16097 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.27367 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.36761 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 5.452 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
29E8553651EDA745D2772D6DD83CDECADB322CF0 | 7.99907 | 224426 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
784
Monitored processes
740
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | taskkill /im firefox.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 124 | taskkill /im iexplore.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 128 | ping localhost -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 252 | taskkill /im firefox.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | taskkill /im searchui.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | taskkill /im chrome.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 280 | taskkill /im chrome.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | taskkill /im firefox.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 308 | taskkill /im firefox.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | taskkill /im svchost.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
2 544
Read events
2 532
Write events
12
Delete events
0
Modification events
| (PID) Process: | (1352) neta_run.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1352) neta_run.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4068) cort.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4068) cort.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2948) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2948) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
21
Suspicious files
24
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1352 | neta_run.exe | C:\Users\admin\AppData\Local\Temp\cort.exe | executable | |
MD5:— | SHA256:— | |||
| 1352 | neta_run.exe | C:\Users\admin\AppData\Local\Temp\down.exe | executable | |
MD5:— | SHA256:— | |||
| 1352 | neta_run.exe | C:\Users\admin\AppData\Local\Temp\playr.exe | executable | |
MD5:— | SHA256:— | |||
| 1352 | neta_run.exe | C:\Users\admin\AppData\Local\Temp\graph.exe | executable | |
MD5:— | SHA256:— | |||
| 1352 | neta_run.exe | C:\Users\admin\AppData\Local\Temp\D3DB.tmp\D3DC.tmp\D3DD.bat | text | |
MD5:— | SHA256:— | |||
| 3920 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\1sh3sw4j.wv0 | binary | |
MD5:— | SHA256:— | |||
| 3920 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\2ofa1nk4.0i4 | binary | |
MD5:— | SHA256:— | |||
| 3920 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\4tswsxn1.den | binary | |
MD5:— | SHA256:— | |||
| 3920 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\3gvuer3j.2jb | binary | |
MD5:— | SHA256:— | |||
| 3920 | xcopy.exe | C:\Users\admin\AppData\Roaming\.mmd\55gsgd51.m3w | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4024 | down.exe | GET | — | 157.7.144.5:80 | http://www.music-note.jp/bgm/mp3/0801/radionoise.mp3 | JP | — | — | malicious |
— | — | GET | 200 | 188.121.36.239:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | NL | der | 1.69 Kb | whitelisted |
— | — | GET | 200 | 188.121.36.237:80 | http://crl.godaddy.com/gdroot.crl | NL | der | 429 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | down.exe | 192.0.77.2:443 | i1.wp.com | Automattic, Inc | US | suspicious |
— | — | 188.121.36.237:80 | crl.godaddy.com | GoDaddy.com, LLC | NL | suspicious |
— | — | 188.121.36.239:80 | ocsp.godaddy.com | GoDaddy.com, LLC | NL | unknown |
4024 | down.exe | 157.7.144.5:80 | www.music-note.jp | GMO Internet,Inc | JP | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
i1.wp.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
crl.godaddy.com |
| whitelisted |
www.music-note.jp |
| malicious |