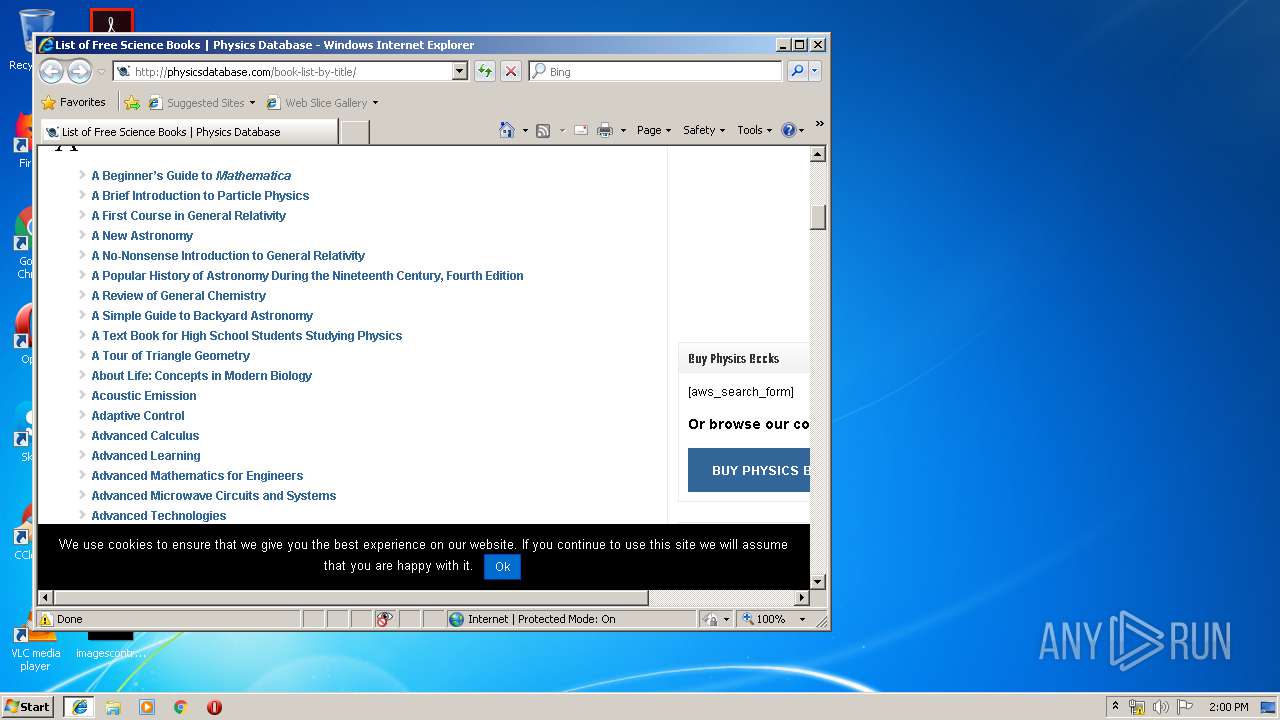
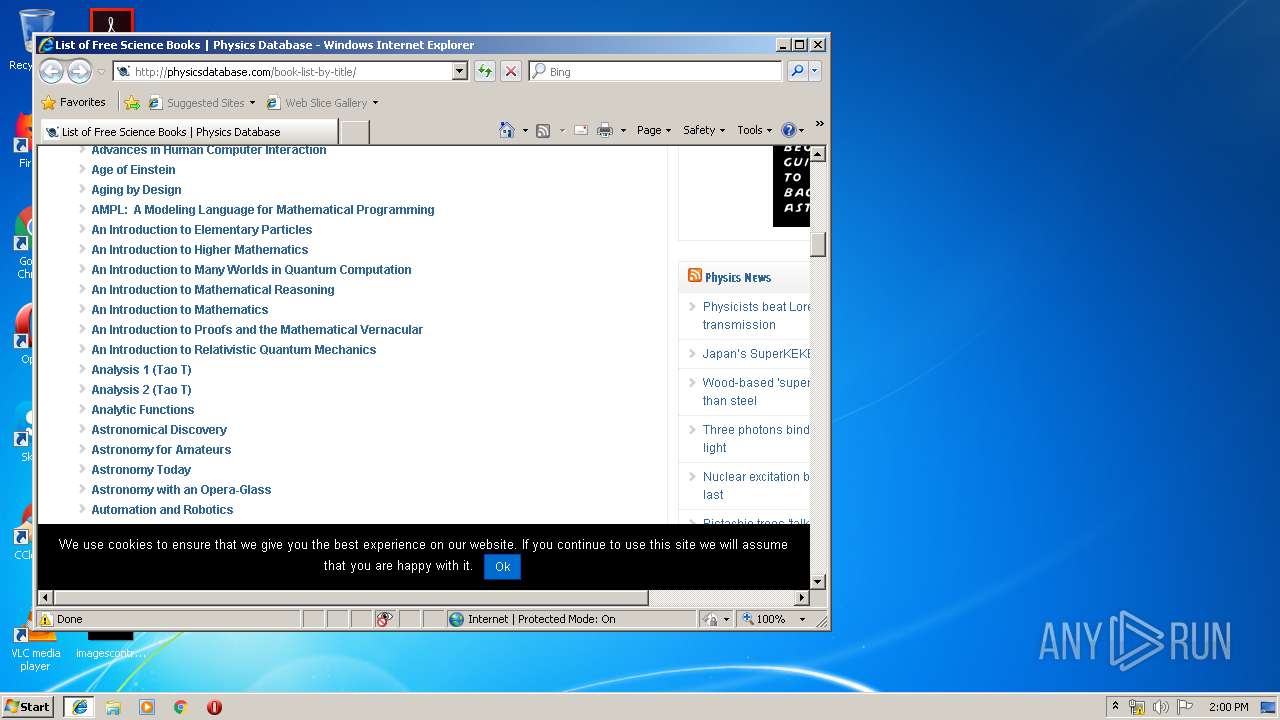
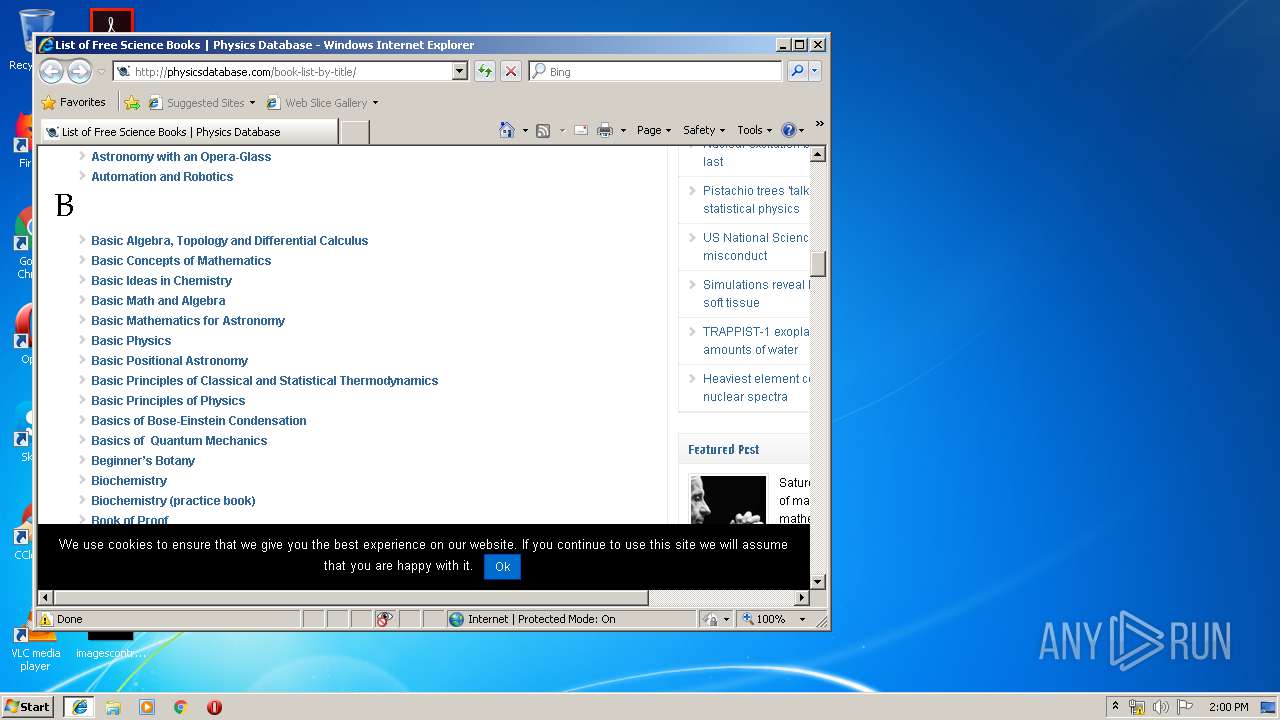
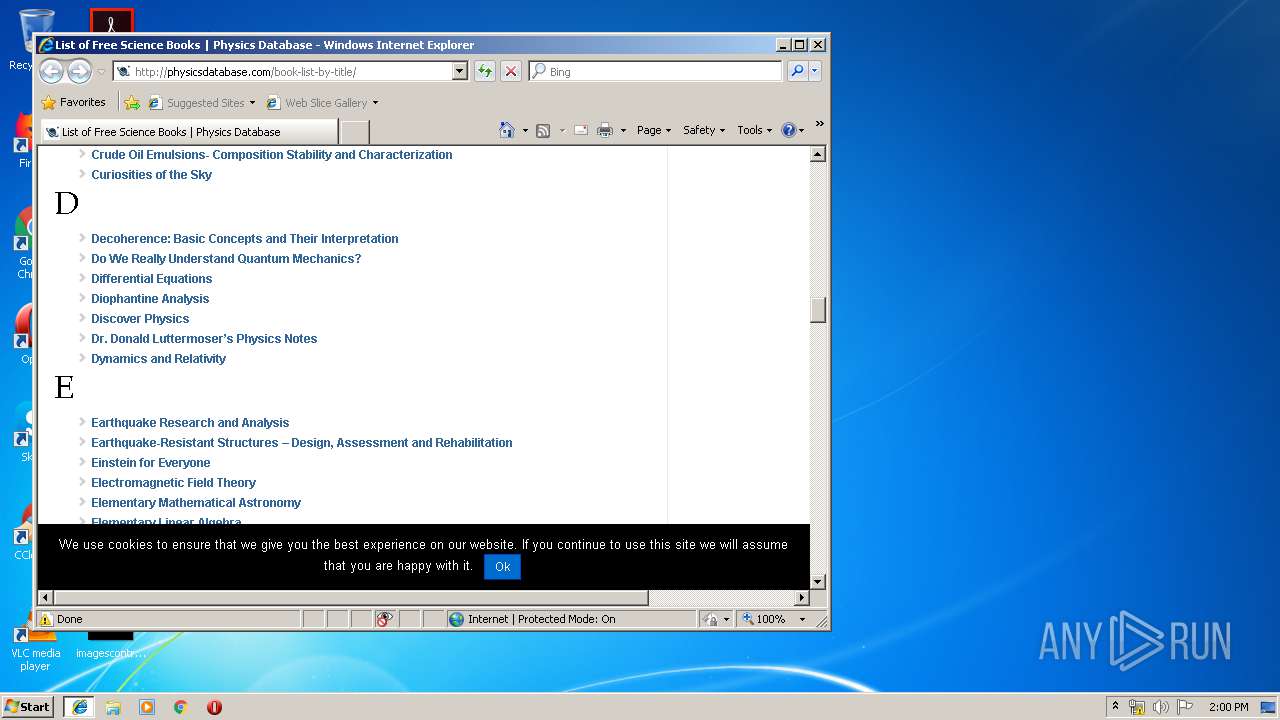
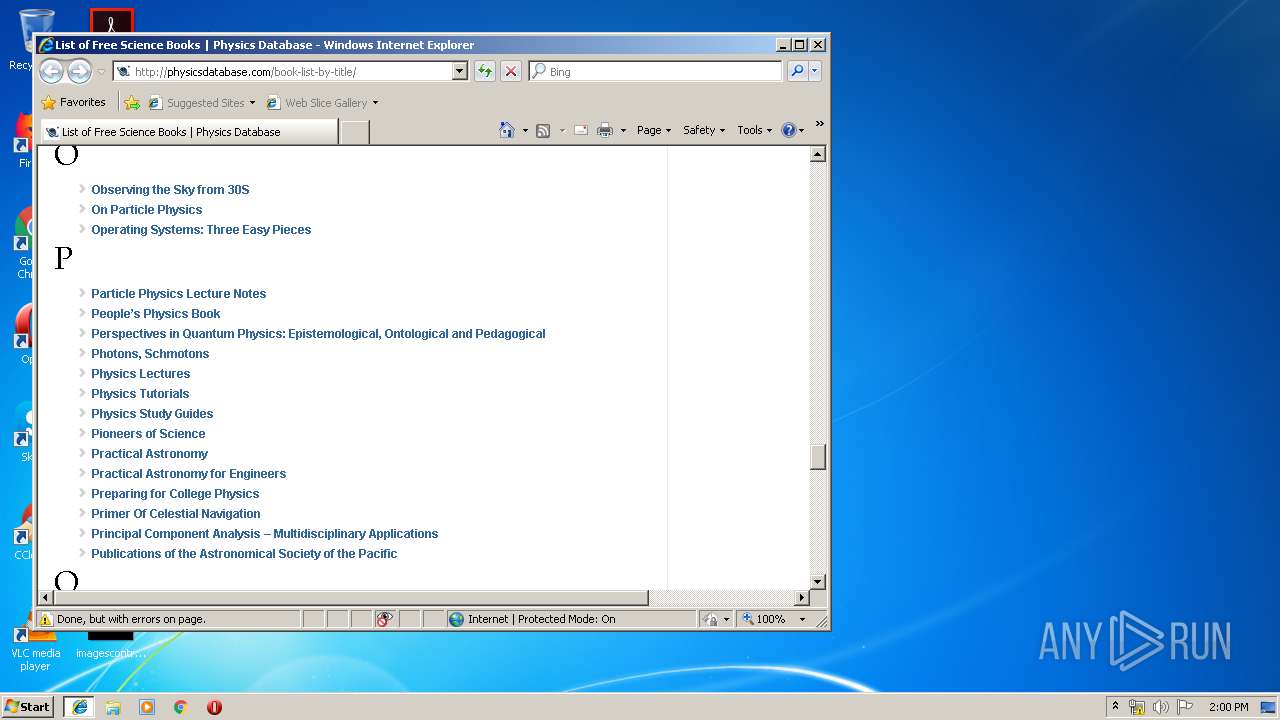
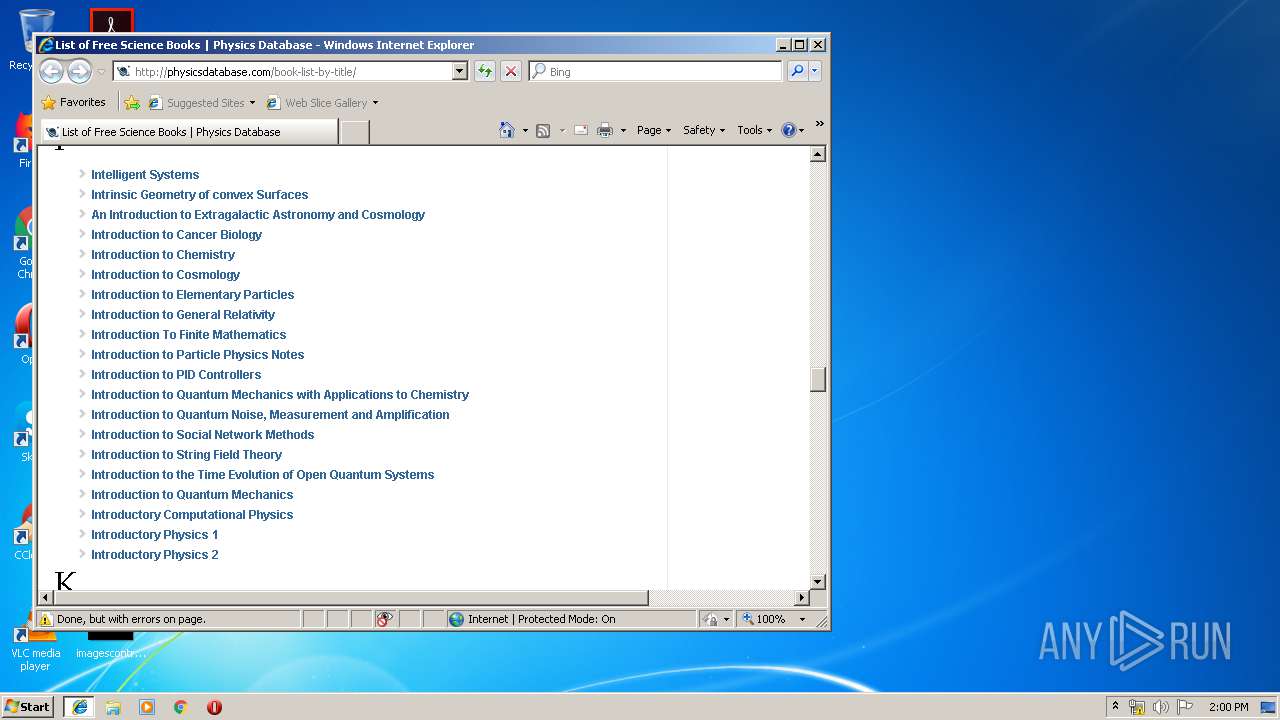
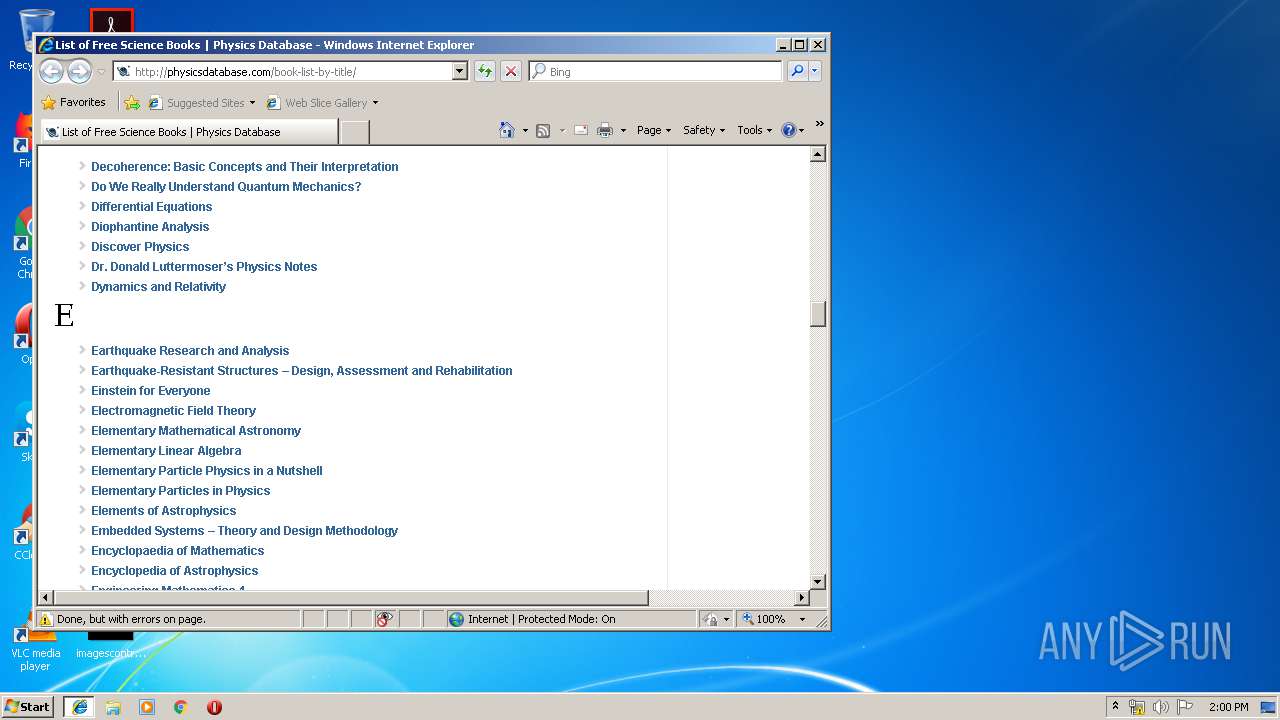
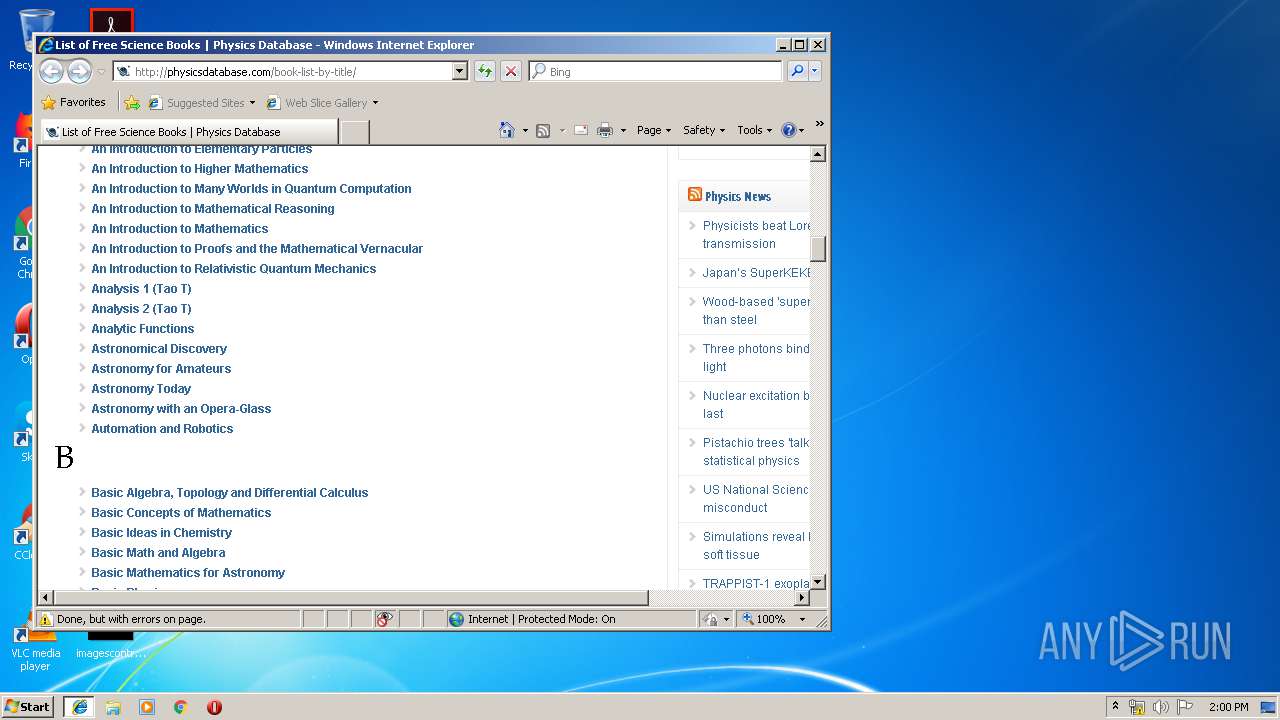
| download: | book-list-by-title |
| Full analysis: | https://app.any.run/tasks/4f0b12a1-0022-4d04-b63e-96c6cd4a3366 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 12:59:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | C742D99CA2B4F8EB670349208BEB3187 |
| SHA1: | 9455651897FD40A84FC7A52E07149DA25C27AF26 |
| SHA256: | A1A10092BF25EAC0935AA1A1C6A1BCAE99BBCFFE5A1D093E8B5F2C8C3EC0CA09 |
| SSDEEP: | 1536:ScRDeh/r/QWFgVmwngopkl3h7w04mjkZ9UDgS0cZ+kKNd/wILAPMyUDn0/Di+FlC:SF/DQWFwmwngopkR91BjkHUDxZ+kKnwS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Internet Explorer
- MSOXMLED.EXE (PID: 3676)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3632)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1136)
Application launched itself
- iexplore.exe (PID: 1136)
Reads Internet Cache Settings
- iexplore.exe (PID: 388)
- iexplore.exe (PID: 1724)
- iexplore.exe (PID: 1136)
Creates files in the user directory
- iexplore.exe (PID: 1724)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3632)
Reads internet explorer settings
- iexplore.exe (PID: 1724)
- iexplore.exe (PID: 388)
Reads settings of System Certificates
- iexplore.exe (PID: 1724)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 1724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml/atom | | | Atom web feed (54.1) |
|---|---|---|
| .aiml | | | Artificial Intelligence Markup Language (22.1) |
| .htm/html | | | HyperText Markup Language with DOCTYPE (19) |
| .html | | | HyperText Markup Language (4.5) |
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| ContentType: | text/html; charset=UTF-8 |
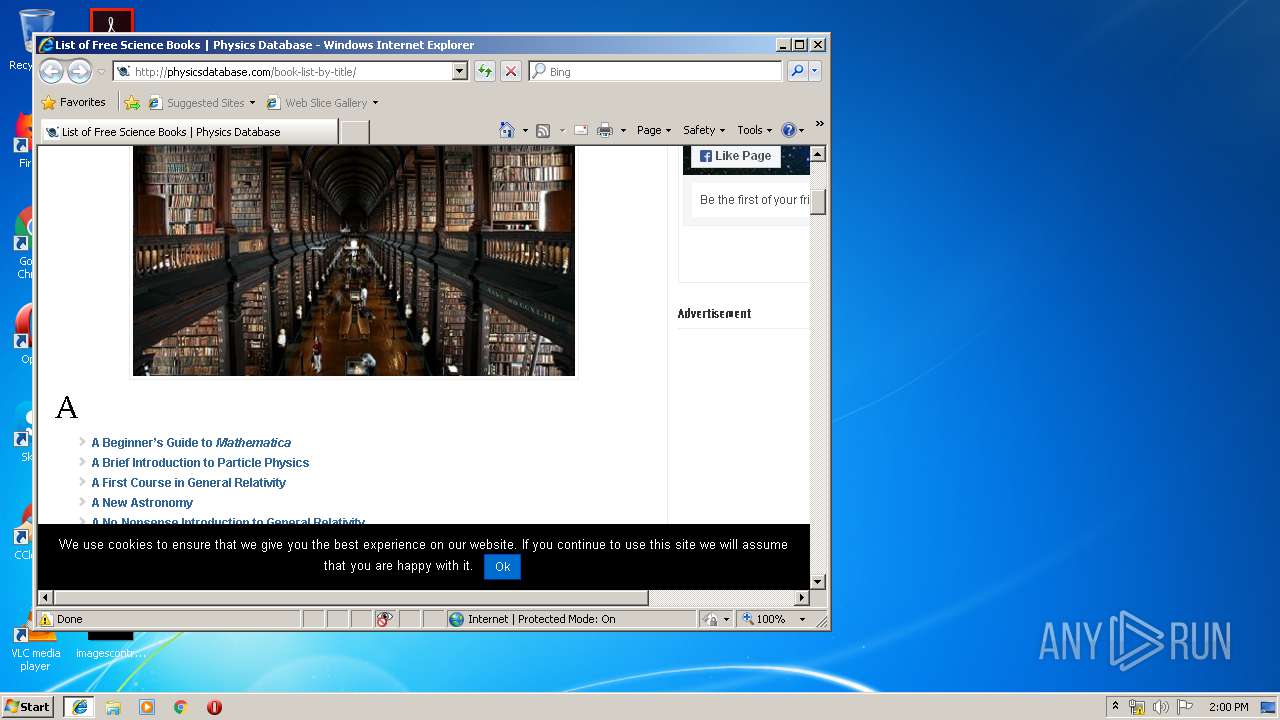
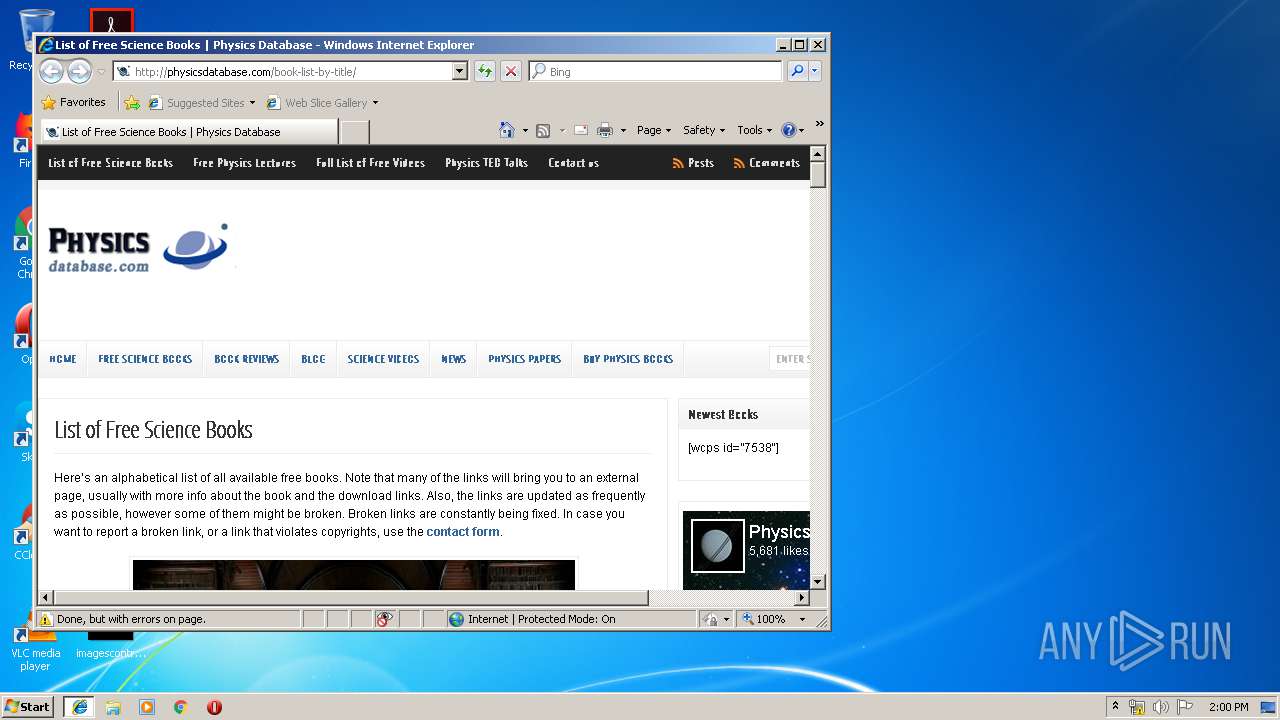
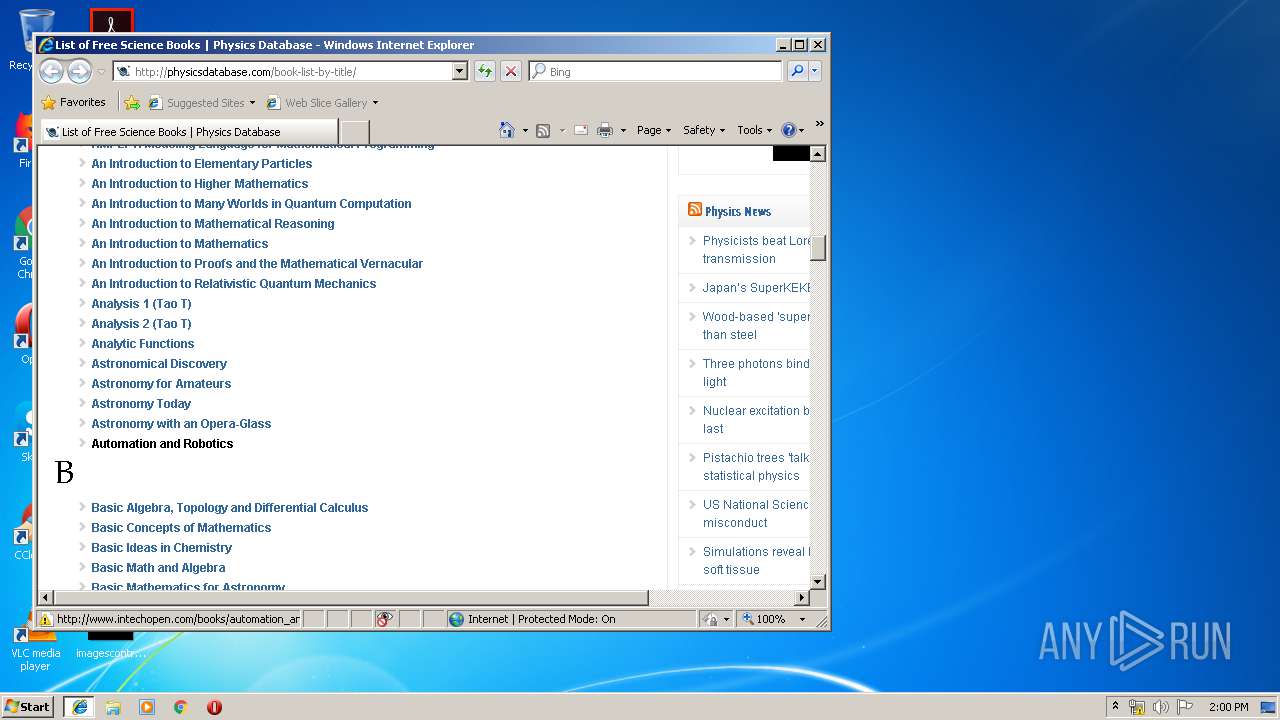
| Title: | List of Free Science Books | Physics Database |
| viewport: | width=device-width,initial-scale=1 |
| Description: | Loads of free science books, including books on physics, chemistry, biology, astronomy and mathematics. Most books are available in pdf format for download. Enjoy! |
| Keywords: | books,ebooks,free,list,science,math,physics,astronomy,mathematics,free pdf books,free physics textbooks,physics textbook pdf, |
| Generator: | Custom Login v3.2.8 |
| twitterTextTitle: | List of Free Science Books |
| twitterCard: | summary |
Total processes
37
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1136 CREDAT:14337 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | MSOXMLED.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1136 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3632 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3676 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open "C:\Users\admin\AppData\Local\Temp\book-list-by-title.xml" | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
Total events
1 027
Read events
909
Write events
116
Delete events
2
Modification events
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {3309FCD7-7AFF-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (1136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070500010014000D0000000B00F602 | |||
Executable files
0
Suspicious files
3
Text files
106
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDBC66FB4FA9D7210.TMP | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF17410DE29894F059.TMP | — | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{3309FCD8-7AFF-11E9-A09E-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 1724 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\JV7F4Q7L\book-list-by-title[1].htm | html | |
MD5:— | SHA256:— | |||
| 1724 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1136 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{3309FCD9-7AFF-11E9-A09E-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 1724 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5MOJ494T\jquery-ui-1.10.4.custom.min[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
54
DNS requests
31
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1724 | iexplore.exe | GET | 301 | 151.101.1.140:80 | http://www.reddit.com/static/button/button2.js | US | — | — | whitelisted |
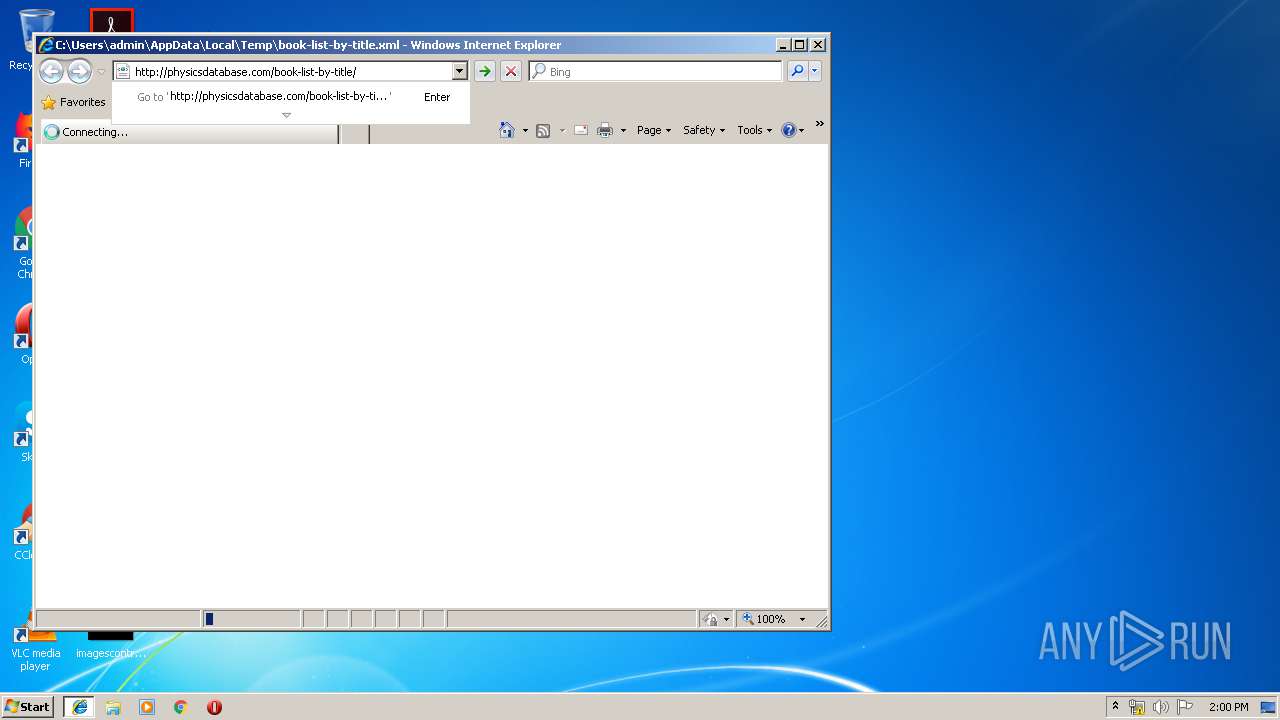
1724 | iexplore.exe | GET | 200 | 192.254.235.140:80 | http://physicsdatabase.com/book-list-by-title/ | US | html | 24.3 Kb | suspicious |
1724 | iexplore.exe | GET | 200 | 192.254.235.140:80 | http://physicsdatabase.com/wp-content/themes/wp-clear321/style.css | US | text | 10.0 Kb | suspicious |
1724 | iexplore.exe | GET | 200 | 192.254.235.140:80 | http://physicsdatabase.com/wp-content/themes/wp-clear321/style-responsive.css | US | text | 1.15 Kb | suspicious |
1724 | iexplore.exe | GET | 200 | 192.254.235.140:80 | http://physicsdatabase.com/wp-content/plugins/wicakhp-wp-fats/jquery-ui-1.10.4.custom.min.css?ver=4.9.8 | US | text | 4.83 Kb | suspicious |
1724 | iexplore.exe | GET | 200 | 192.254.235.140:80 | http://physicsdatabase.com/?sccss=1&ver=4.9.8 | US | text | 1.40 Kb | suspicious |
1724 | iexplore.exe | GET | 200 | 93.184.220.66:80 | http://platform.twitter.com/widgets.js | US | text | 92.7 Kb | whitelisted |
1724 | iexplore.exe | GET | 200 | 192.254.235.140:80 | http://physicsdatabase.com/wp-content/plugins/blockalyzer-adblock-counter/js/banner.js?ver=1.3 | US | text | 93 b | suspicious |
1724 | iexplore.exe | GET | 200 | 192.254.235.140:80 | http://physicsdatabase.com/wp-content/themes/wp-clear321/js/suckerfish.js?ver=4.9.8 | US | text | 252 b | suspicious |
1136 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1136 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1724 | iexplore.exe | 192.254.235.140:80 | physicsdatabase.com | Unified Layer | US | suspicious |
1724 | iexplore.exe | 172.217.16.206:443 | apis.google.com | Google Inc. | US | whitelisted |
1724 | iexplore.exe | 172.217.22.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 151.101.1.140:80 | www.reddit.com | Fastly | US | suspicious |
— | — | 74.125.140.82:80 | css3-mediaqueries-js.googlecode.com | Google Inc. | US | whitelisted |
— | — | 93.184.220.66:80 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1724 | iexplore.exe | 151.101.1.140:443 | www.reddit.com | Fastly | US | suspicious |
— | — | 192.0.78.17:443 | wordpress.com | Automattic, Inc | US | unknown |
1724 | iexplore.exe | 157.240.20.19:80 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
physicsdatabase.com |
| suspicious |
apis.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.reddit.com |
| whitelisted |
platform.twitter.com |
| whitelisted |
css3-mediaqueries-js.googlecode.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
wordpress.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report