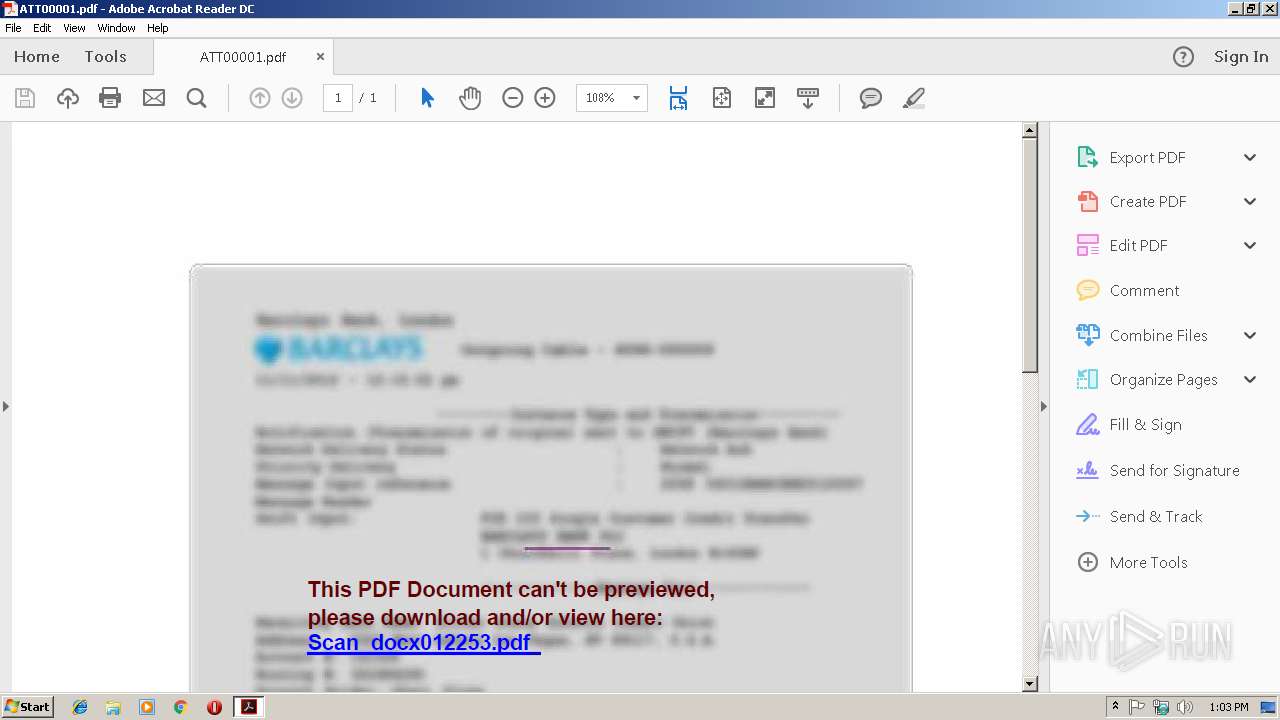
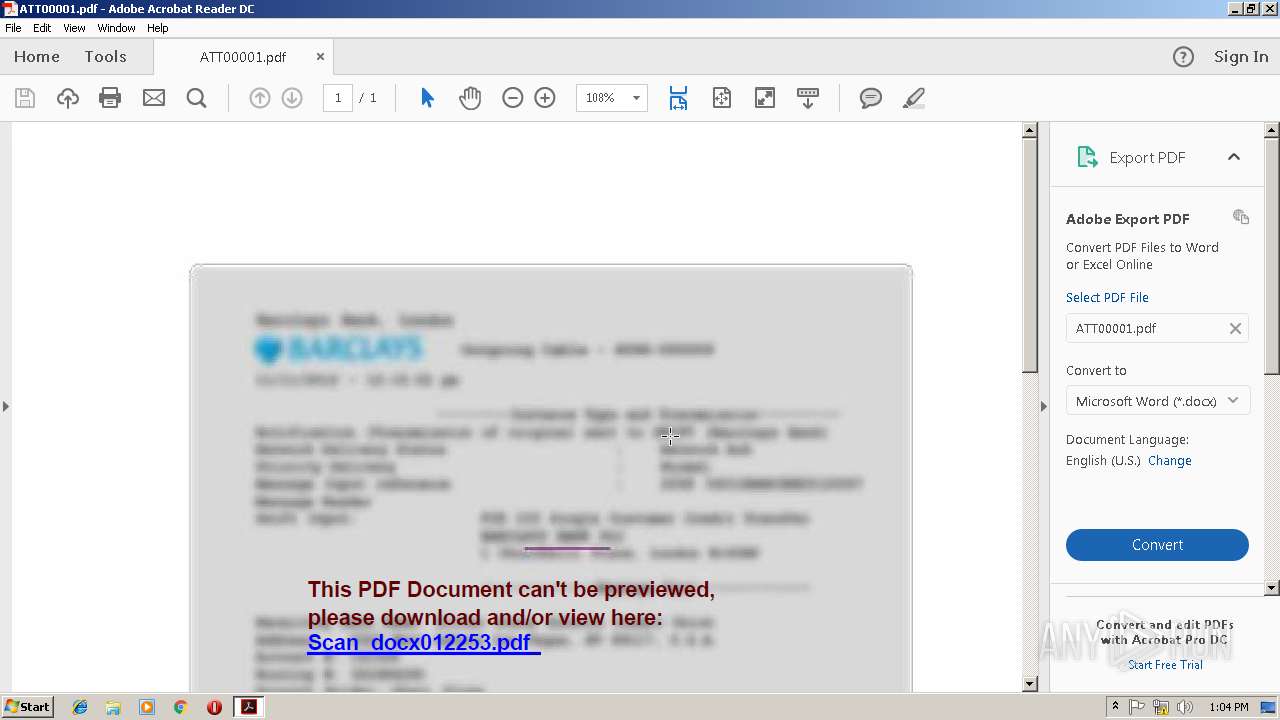
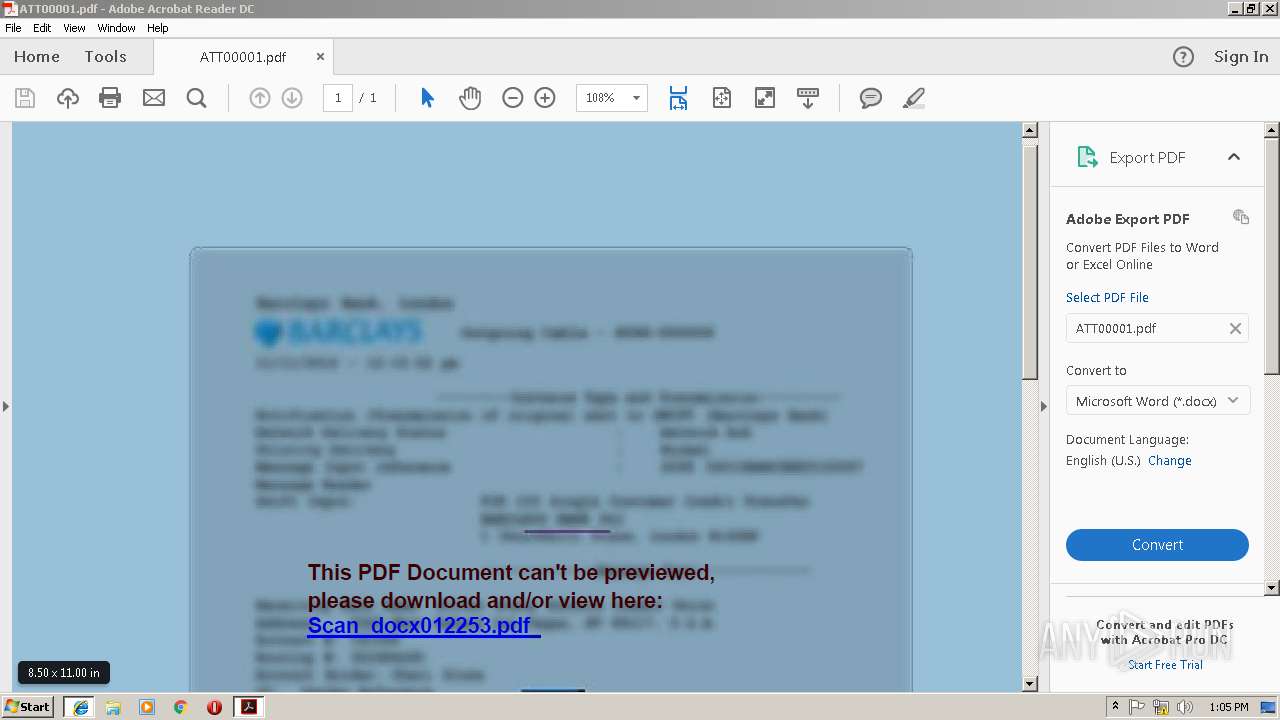
| File name: | ATT00001.pdf |
| Full analysis: | https://app.any.run/tasks/84d4d928-84ae-4072-9164-729d3383d87f |
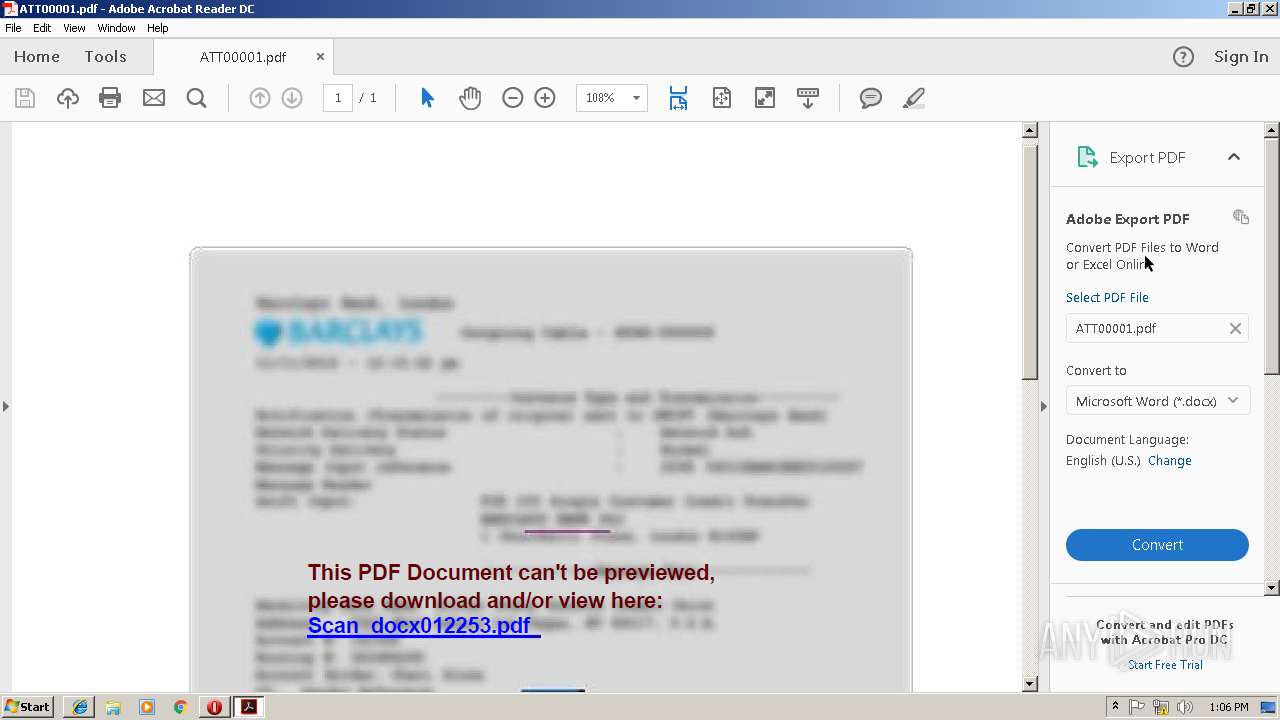
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 13:02:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.6 |
| MD5: | 0E1B187AD7E52251D9BD001F47D0FEA6 |
| SHA1: | 05C6BA486FF6EA0EA5723180440B1D017F8F7D14 |
| SHA256: | A17A28409E0512E75370B5D5CB56A6D7A435C68CCEDF646EECACC31E60A759B7 |
| SSDEEP: | 1536:DG8CS3iJbt4BxqvqZZ9liCIwa0/ZJ/TOFVeL9XzYb:aBS3wbt4BEcGwBJ/aFVeLhM |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- AdobeARM.exe (PID: 3116)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 3116)
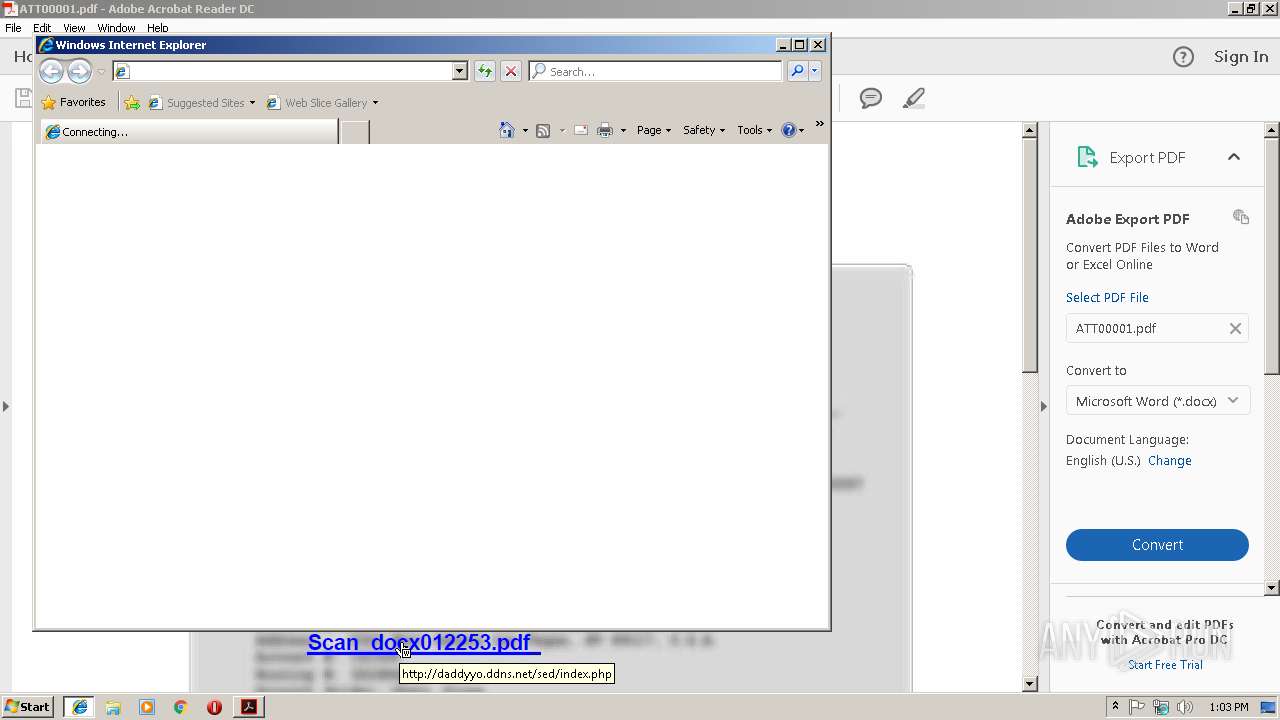
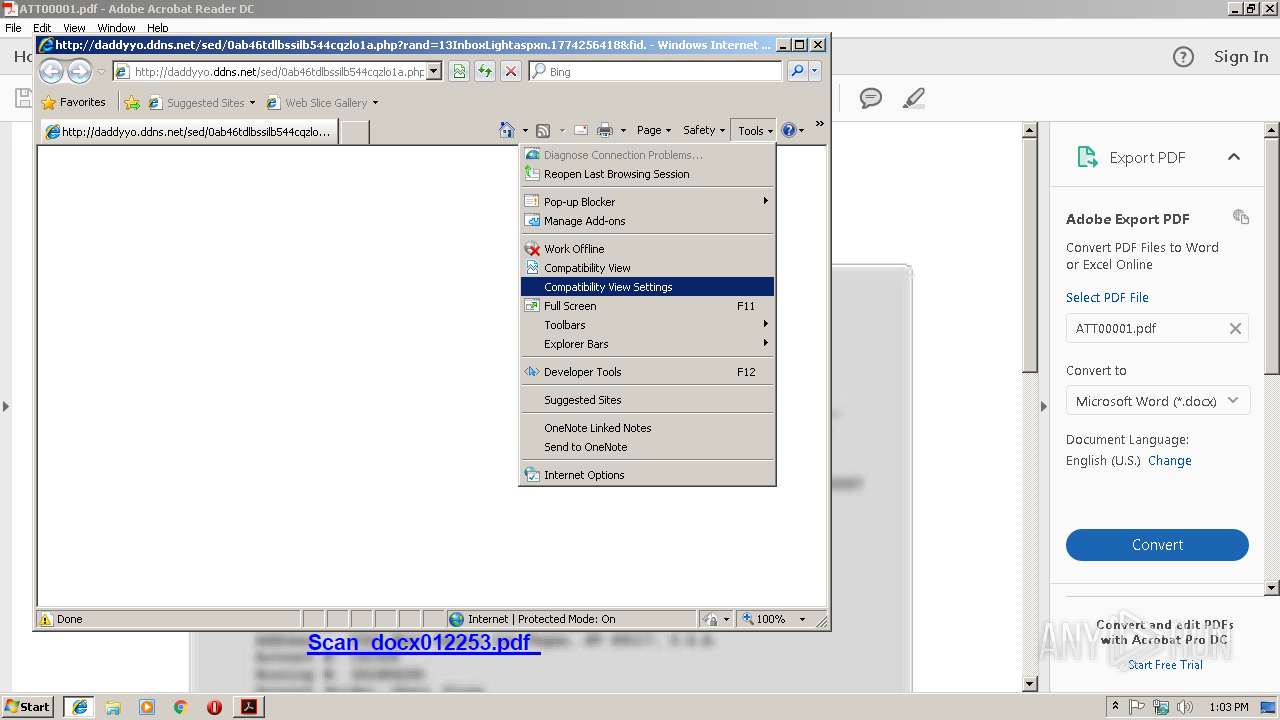
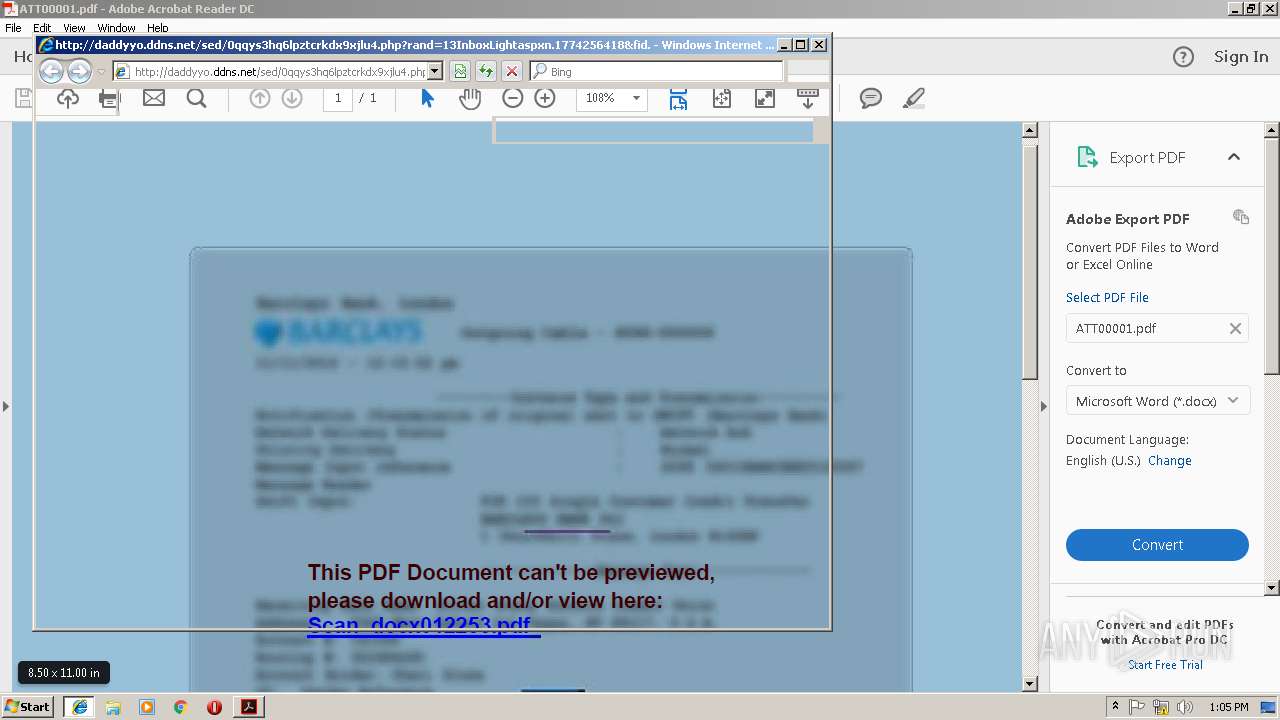
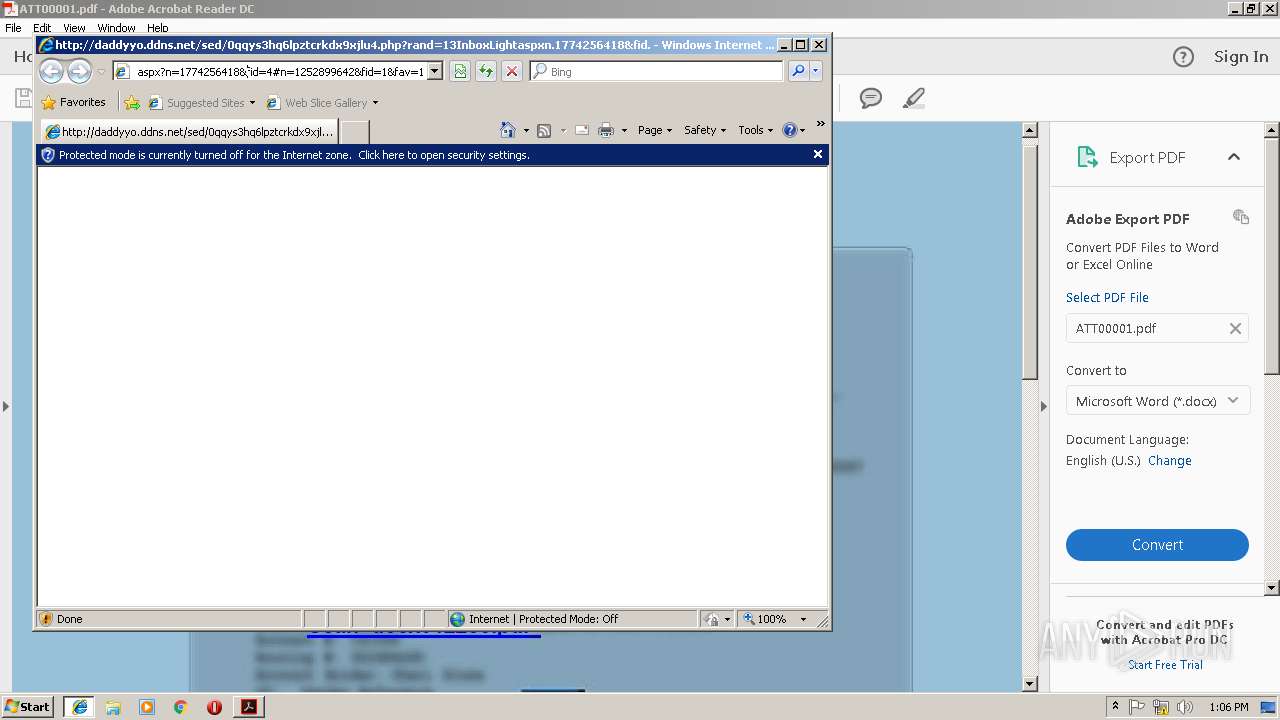
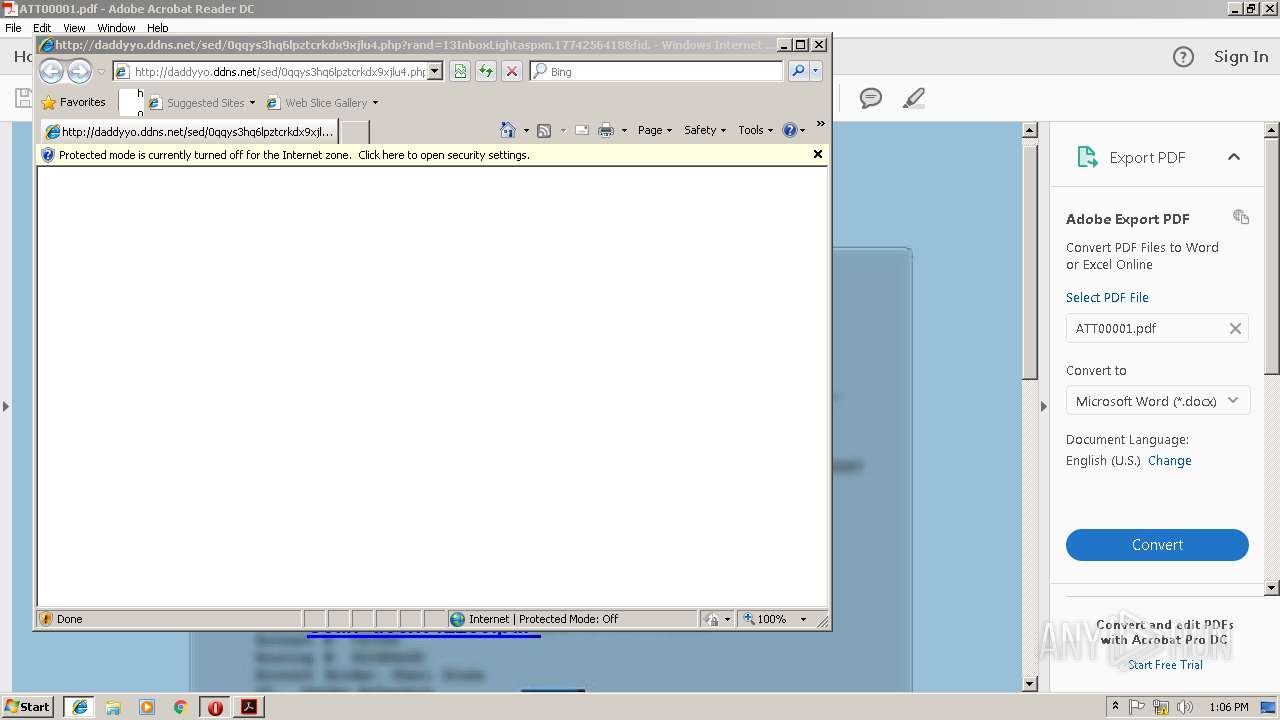
Starts Internet Explorer
- AcroRd32.exe (PID: 2896)
INFO
Application launched itself
- AcroRd32.exe (PID: 2896)
- RdrCEF.exe (PID: 2792)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 3200)
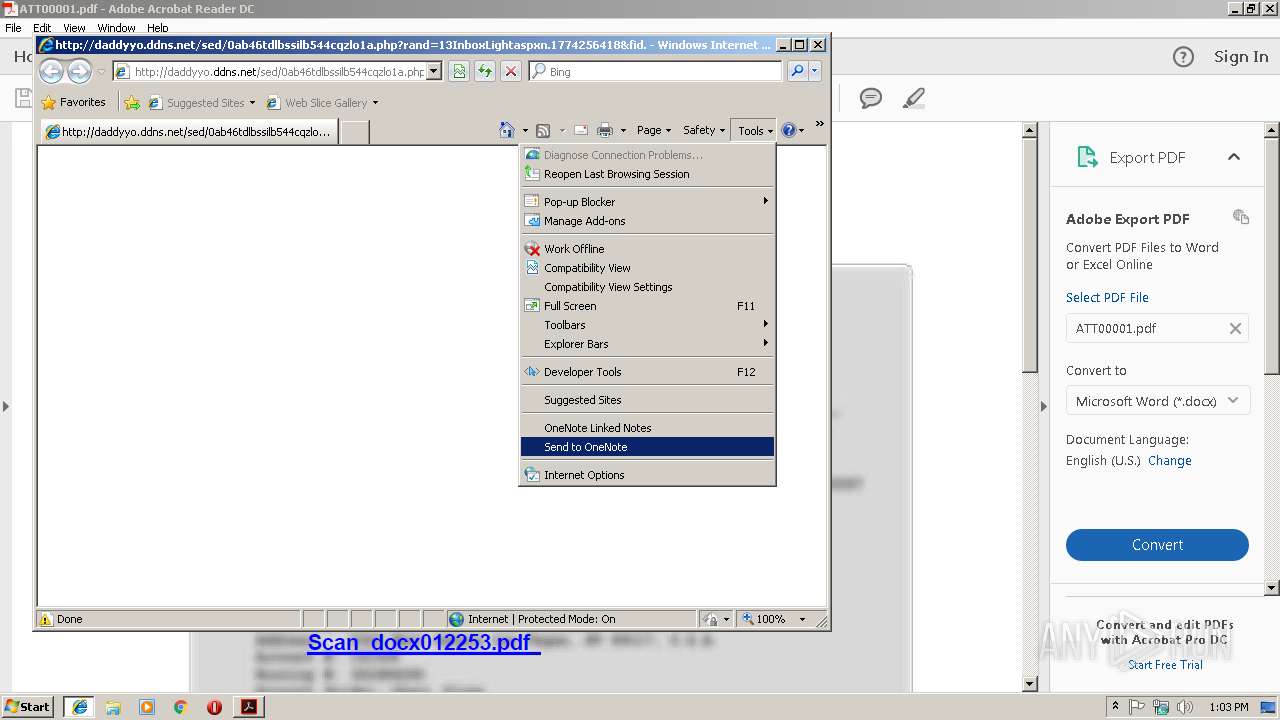
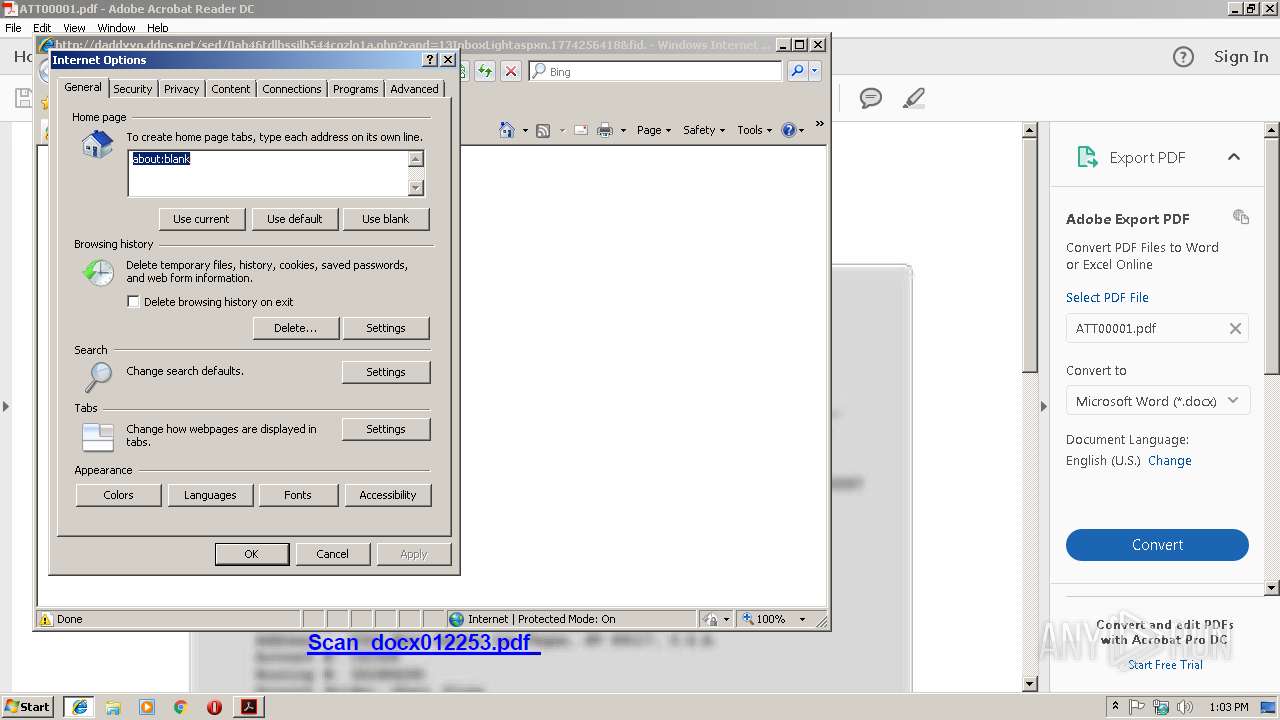
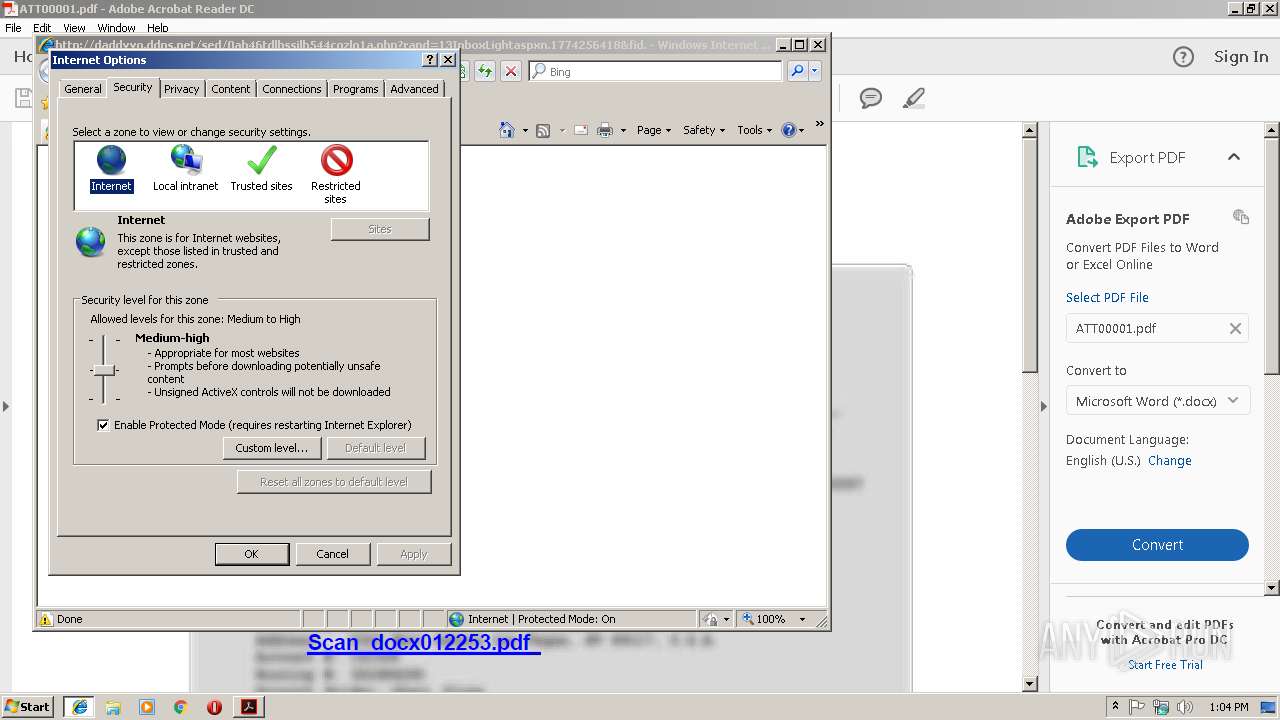
Reads internet explorer settings
- iexplore.exe (PID: 3244)
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 1584)
Creates files in the user directory
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 3096)
- opera.exe (PID: 2384)
Reads Internet Cache Settings
- iexplore.exe (PID: 3244)
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 1584)
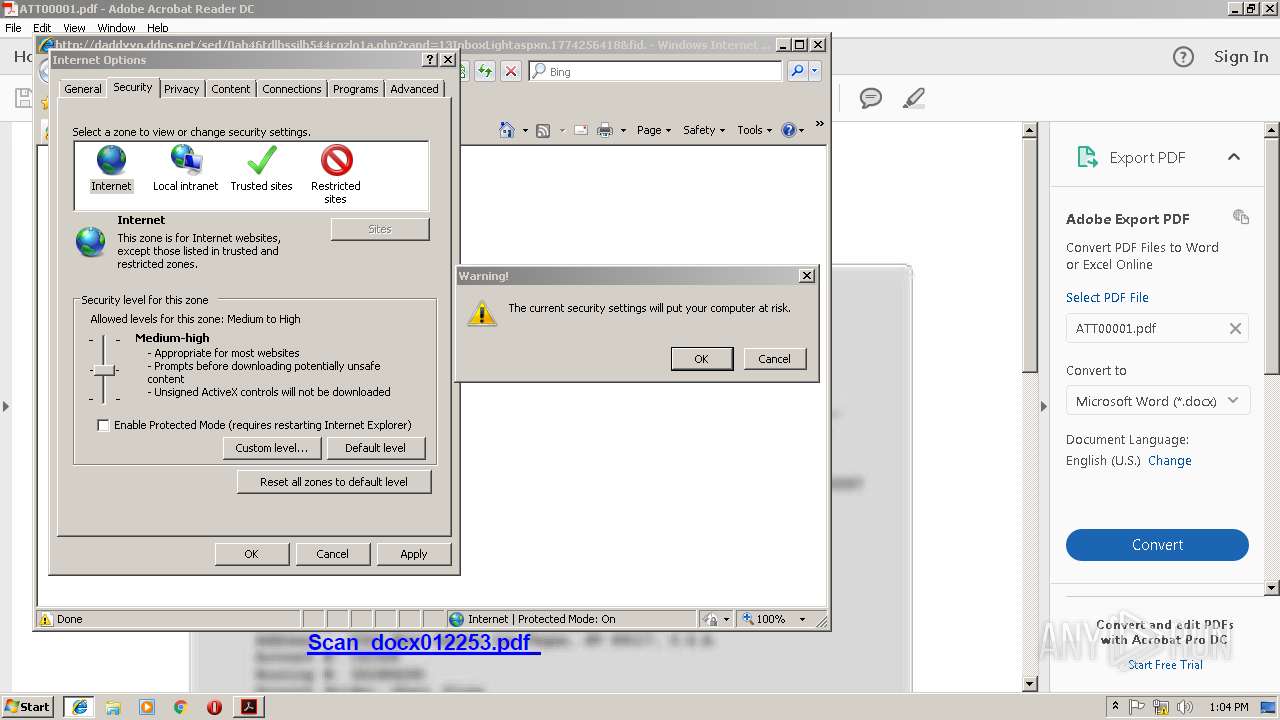
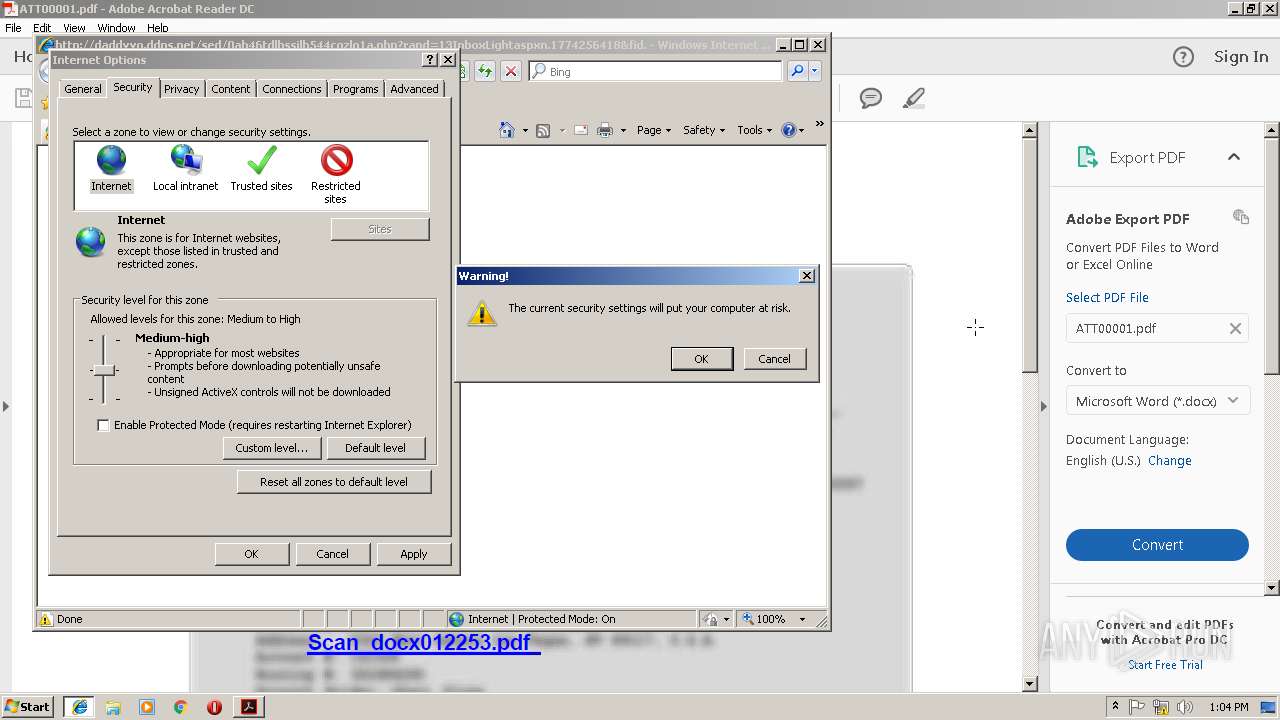
Changes internet zones settings
- iexplore.exe (PID: 3200)
- iexplore.exe (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.6 |
|---|---|
| Linearized: | Yes |
| CreateDate: | 2015:12:08 04:45:12-06:00 |
| Creator: | Microsoft® Word 2010 |
| ModifyDate: | 2019:01:21 18:19:46-08:00 |
| Producer: | Microsoft® Word 2010 |
| Language: | en-US |
| TaggedPDF: | Yes |
| PageCount: | 1 |
XMP
| XMPToolkit: | Adobe XMP Core 5.4-c006 80.159825, 2016/09/16-03:31:08 |
|---|---|
| CreateDate: | 2015:12:08 04:45:12-06:00 |
| CreatorTool: | Microsoft® Word 2010 |
| ModifyDate: | 2019:01:21 18:19:46-08:00 |
| MetadataDate: | 2019:01:21 18:19:46-08:00 |
| Producer: | Microsoft® Word 2010 |
| DocumentID: | uuid:491c3bae-9a2a-4f2f-b6af-7a8f845147b9 |
| InstanceID: | uuid:a3d291c0-9a7f-4f96-8fa3-10268f12c554 |
| Format: | application/pdf |
Total processes
45
Monitored processes
13
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1584 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3200 CREDAT:14344 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2792.0.1250518880\519353697" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\Desktop\ATT00001.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2792 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Desktop\ATT00001.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 3096 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3200 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3116 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
Total events
1 703
Read events
1 195
Write events
504
Delete events
4
Modification events
| (PID) Process: | (2352) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2352) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (2352) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (2896) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | aFS |
Value: DOS | |||
| (PID) Process: | (2896) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tDIText |
Value: /C/Users/admin/Desktop/ATT00001.pdf | |||
| (PID) Process: | (2896) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tFileName |
Value: ATT00001.pdf | |||
| (PID) Process: | (2896) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tFileSource |
Value: local | |||
| (PID) Process: | (2896) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | sFileAncestors |
Value: 5B5D00 | |||
| (PID) Process: | (2896) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | sDI |
Value: 2F432F55736572732F61646D696E2F4465736B746F702F41545430303030312E70646600 | |||
| (PID) Process: | (2896) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | sDate |
Value: 443A32303139303132323133303332305A00 | |||
Executable files
2
Suspicious files
21
Text files
69
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2352 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\0ab46tdlbssilb544cqzlo1a[1].php | — | |
MD5:— | SHA256:— | |||
| 2352 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R4j0aea_1iryhfy_1tc.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1uuqiwx_1iryhfx_1tc.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1pmlu76_1iryhg0_1tc.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1wclbu4_1iryhfz_1tc.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R9yyowz_1iryhg1_1tc.tmp | — | |
MD5:— | SHA256:— | |||
| 3116 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp3048.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
39
DNS requests
17
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
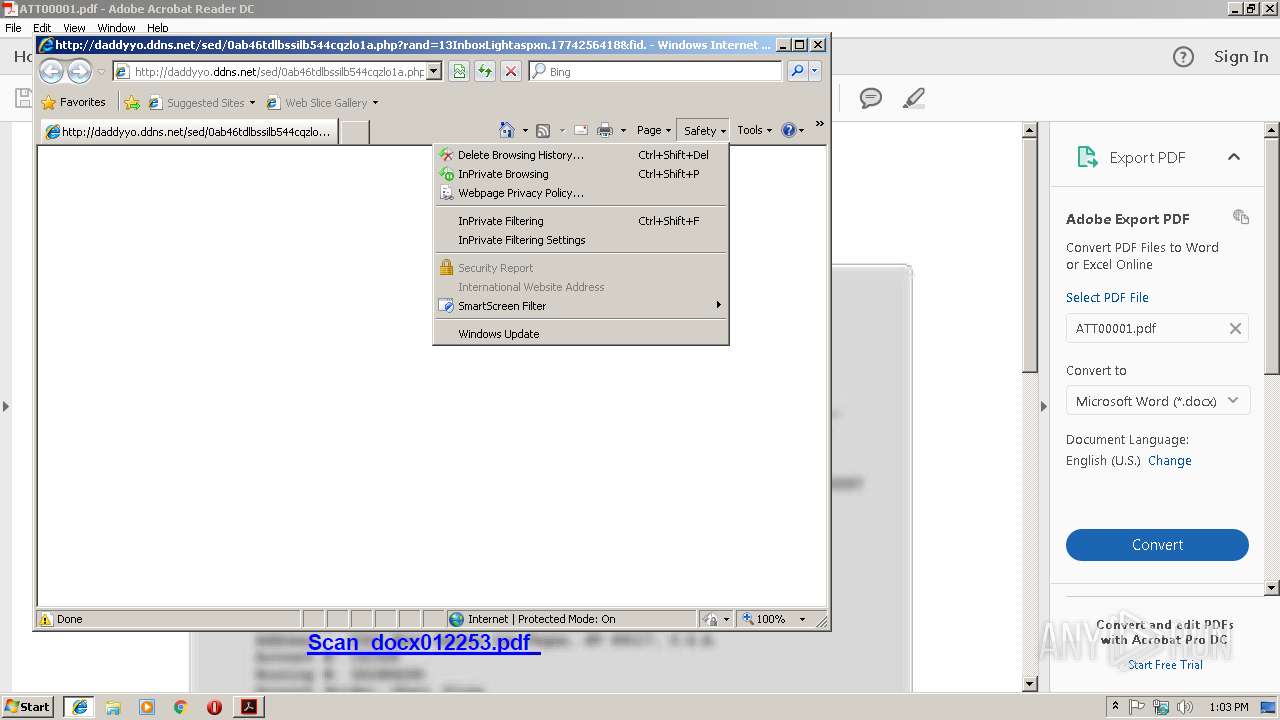
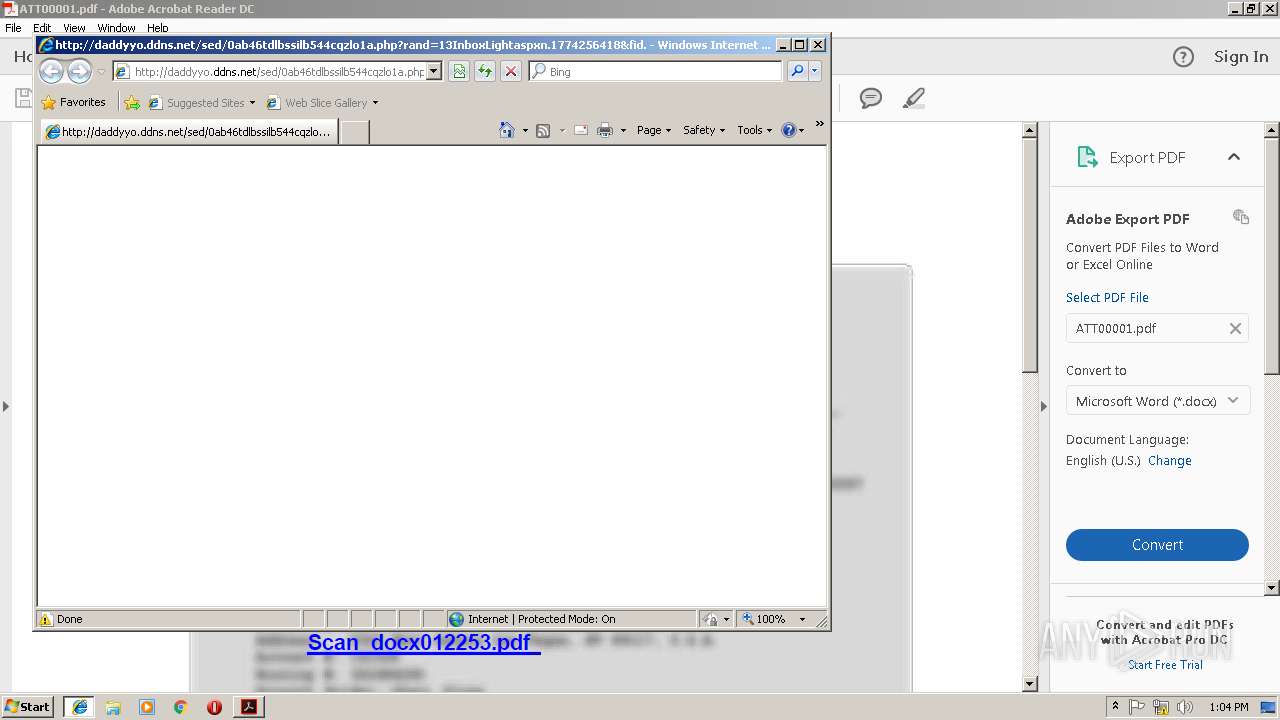
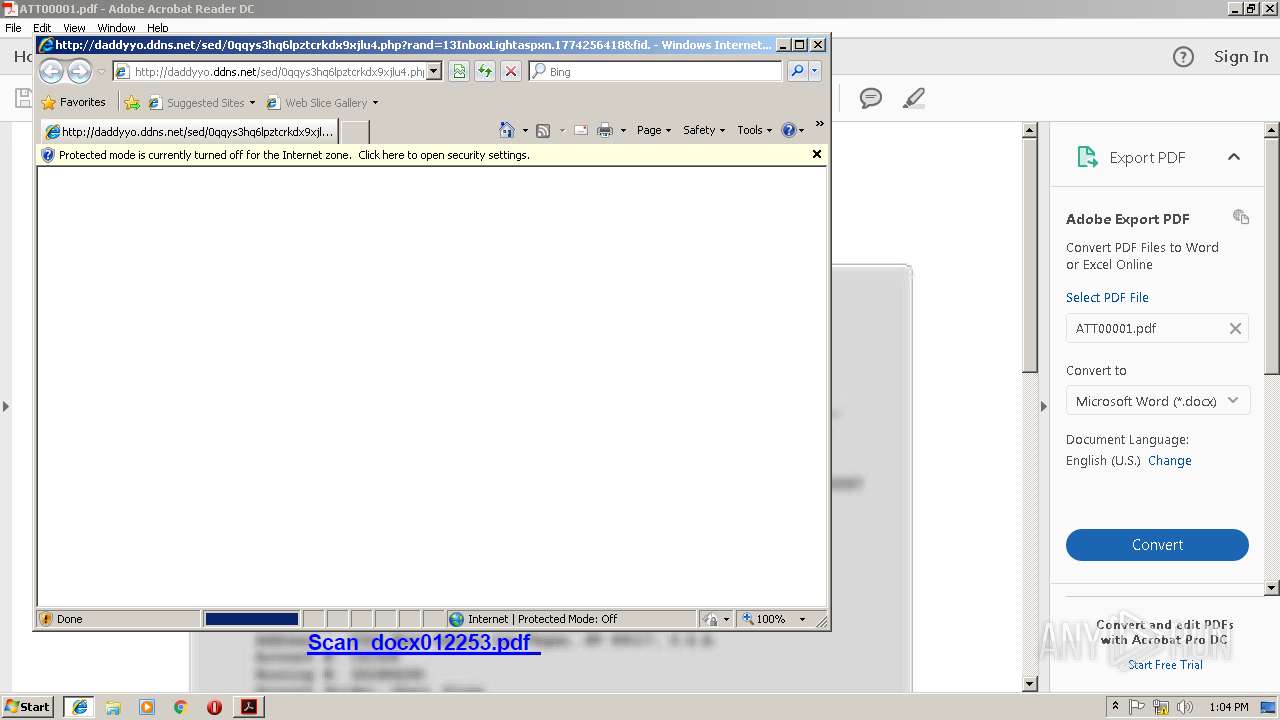
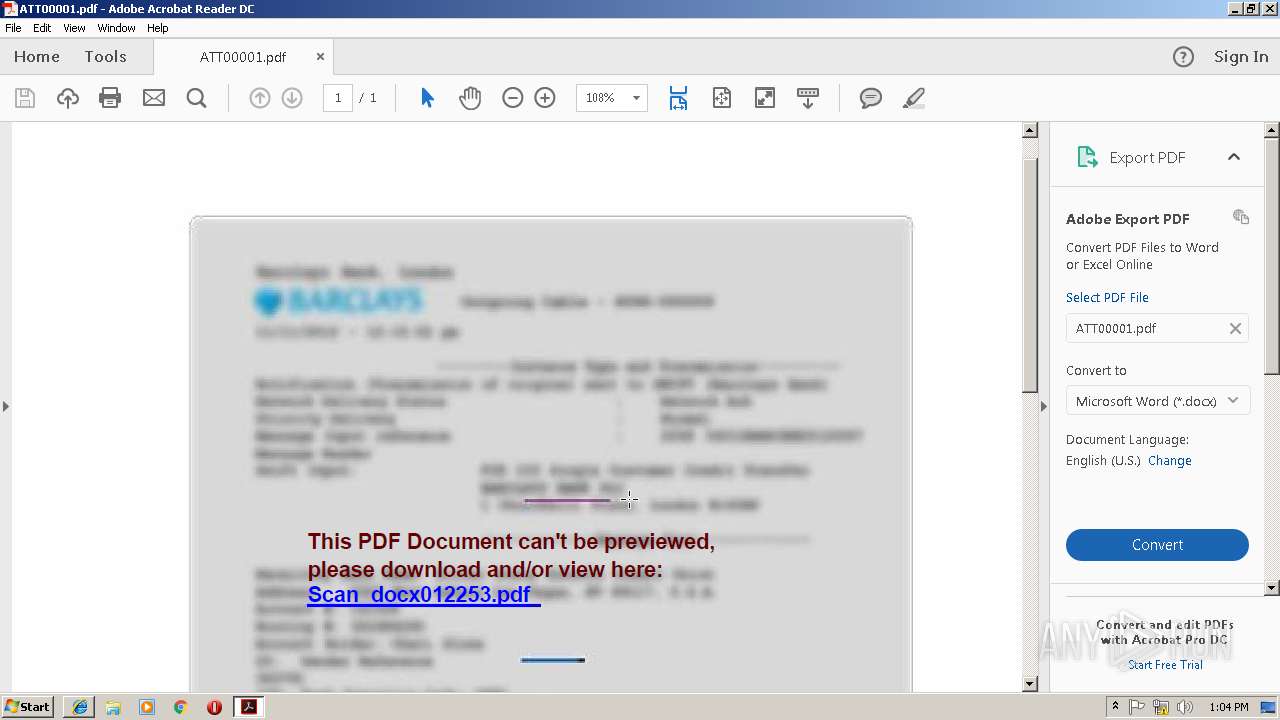
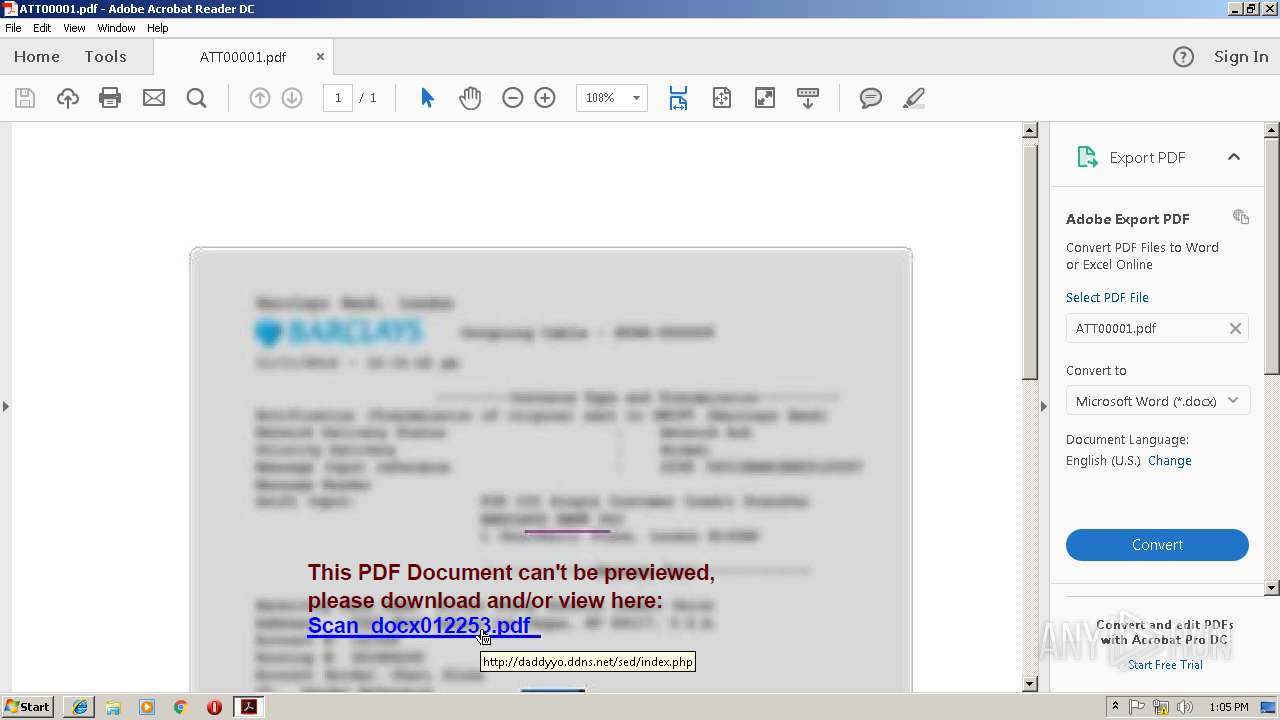
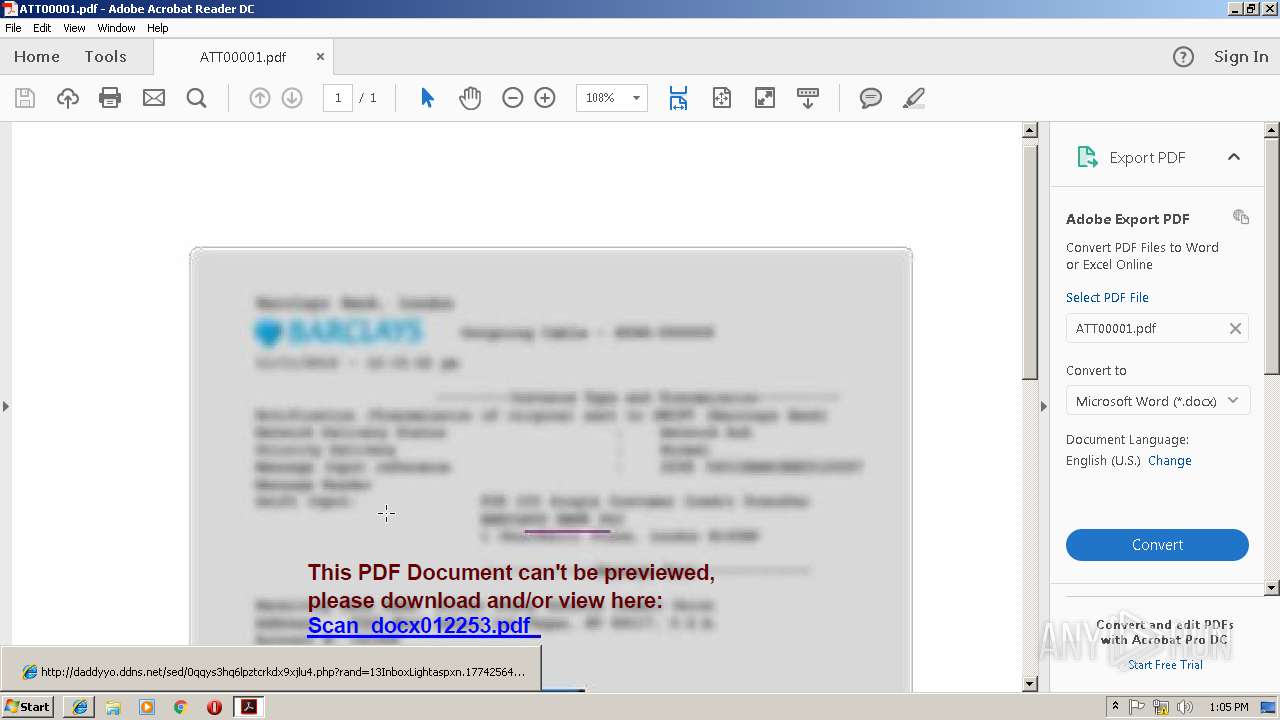
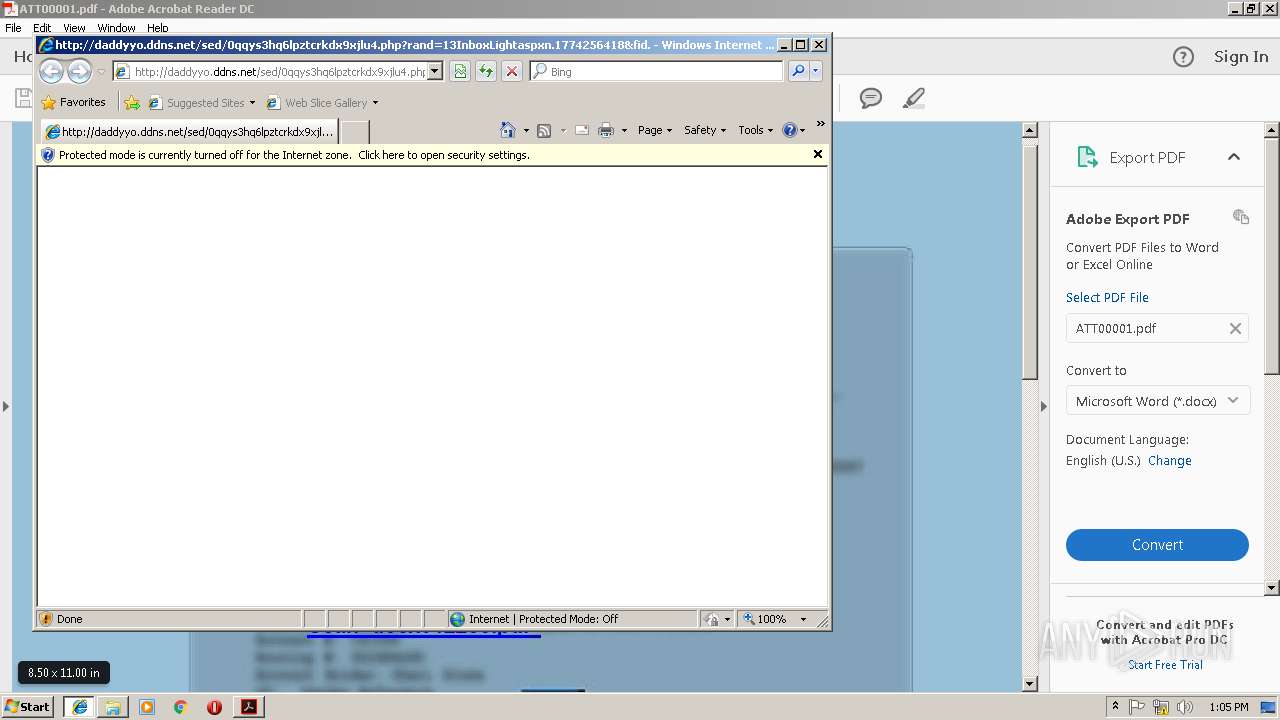
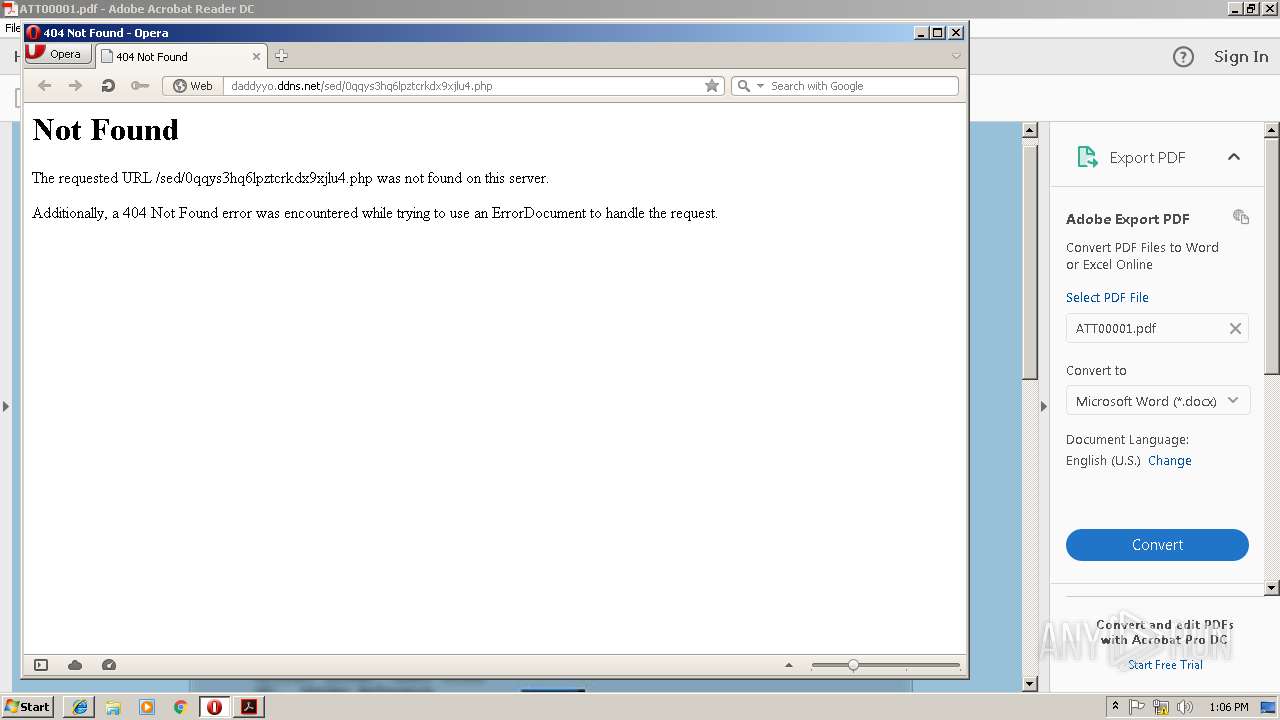
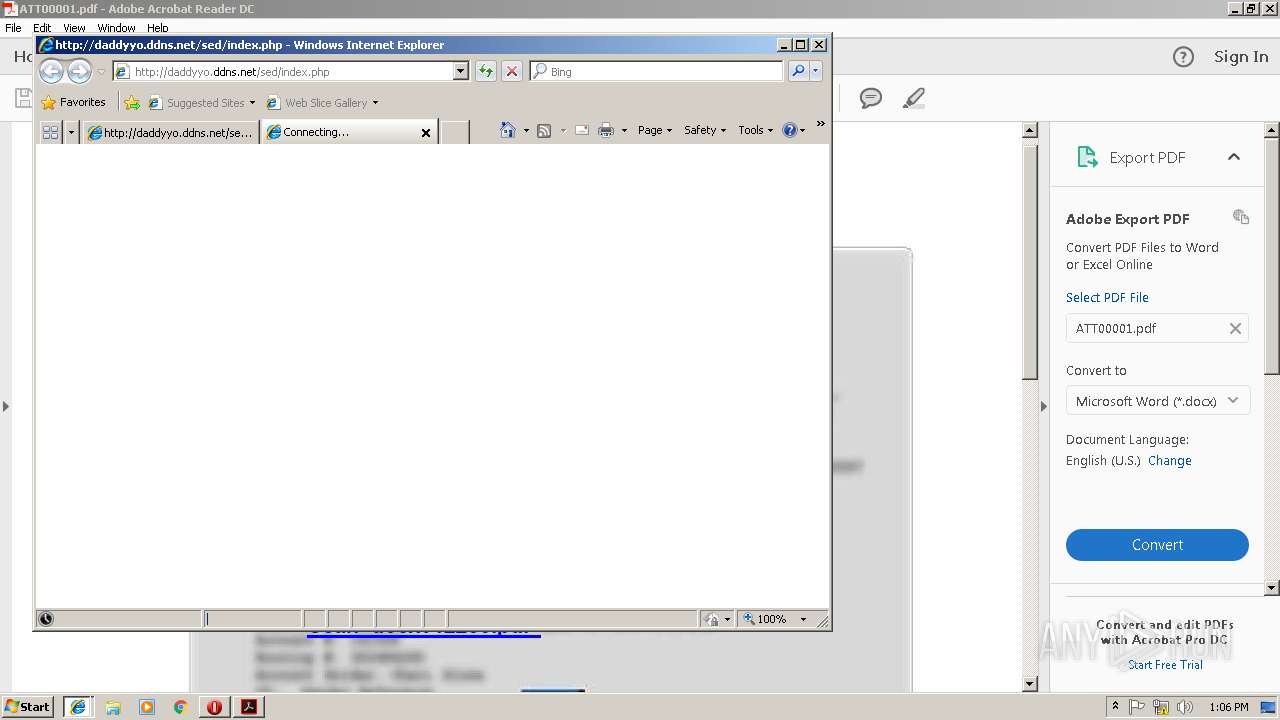
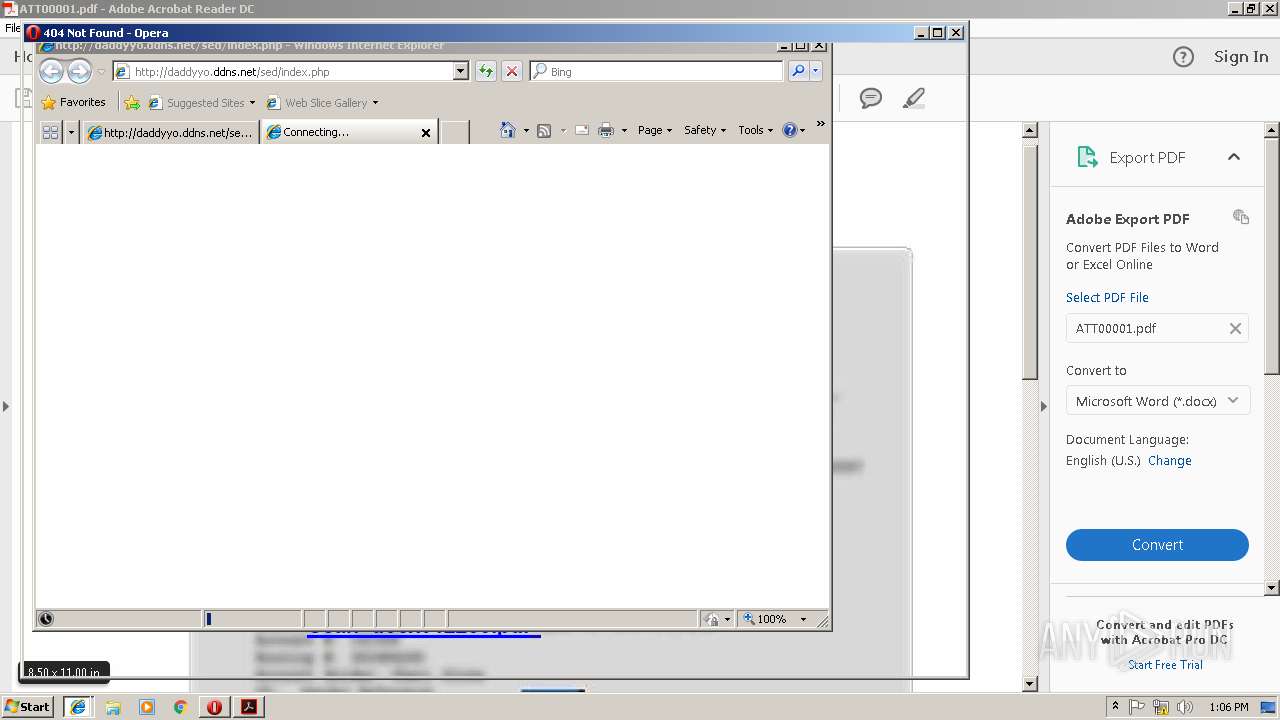
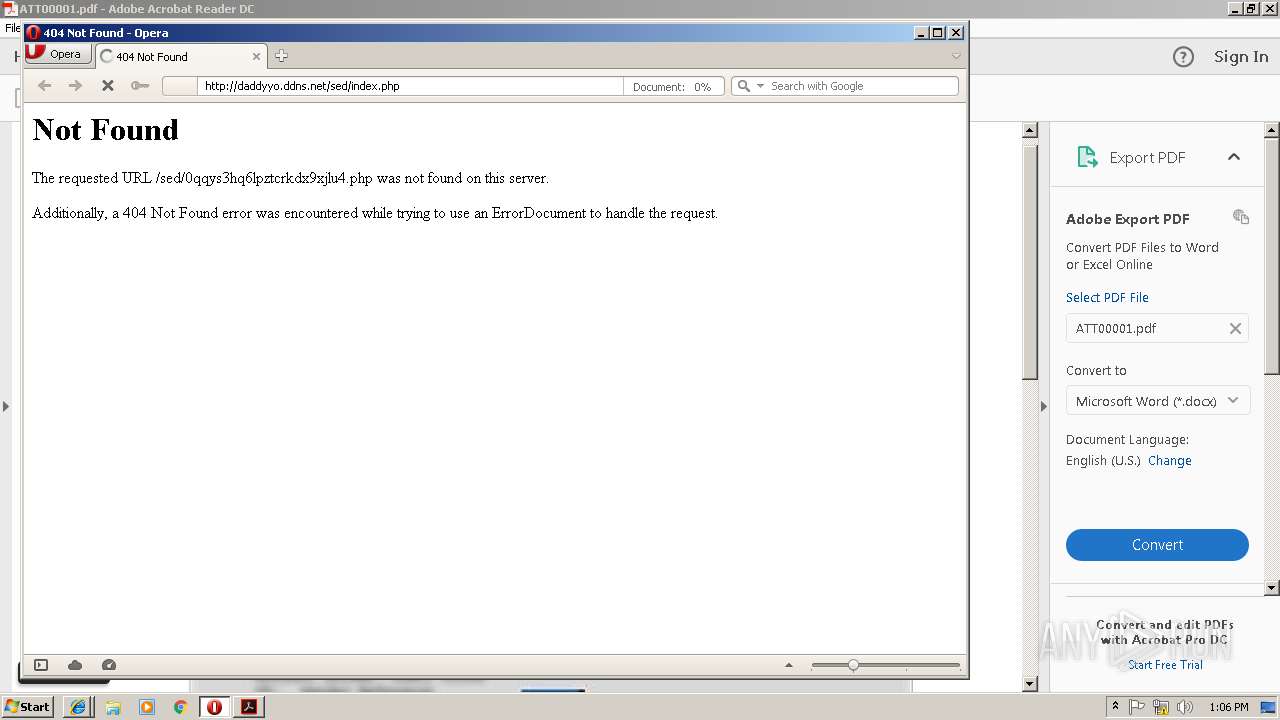
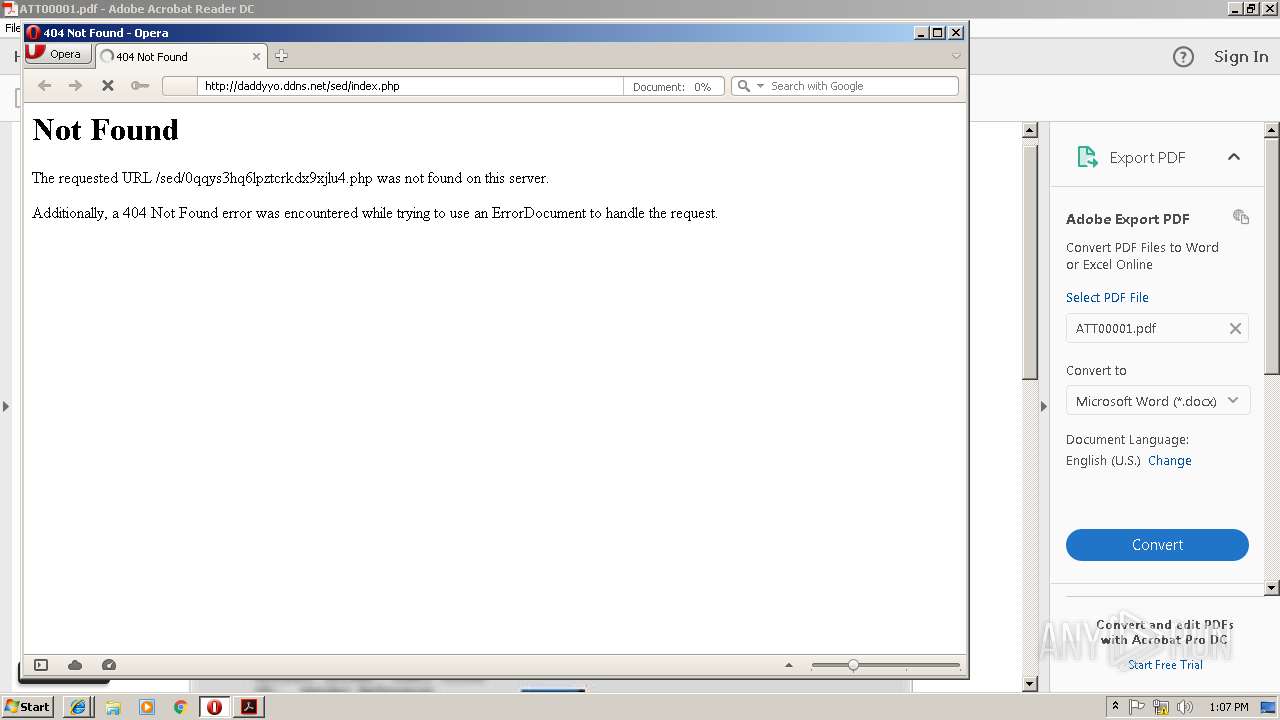
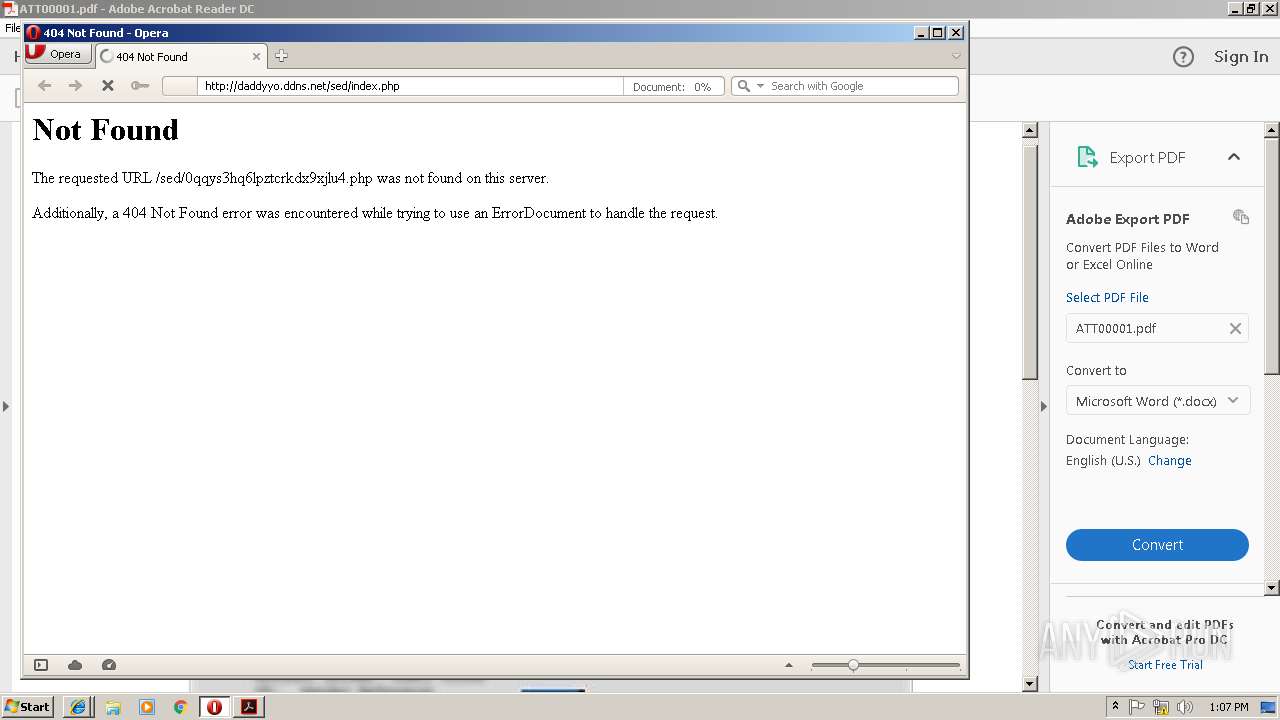
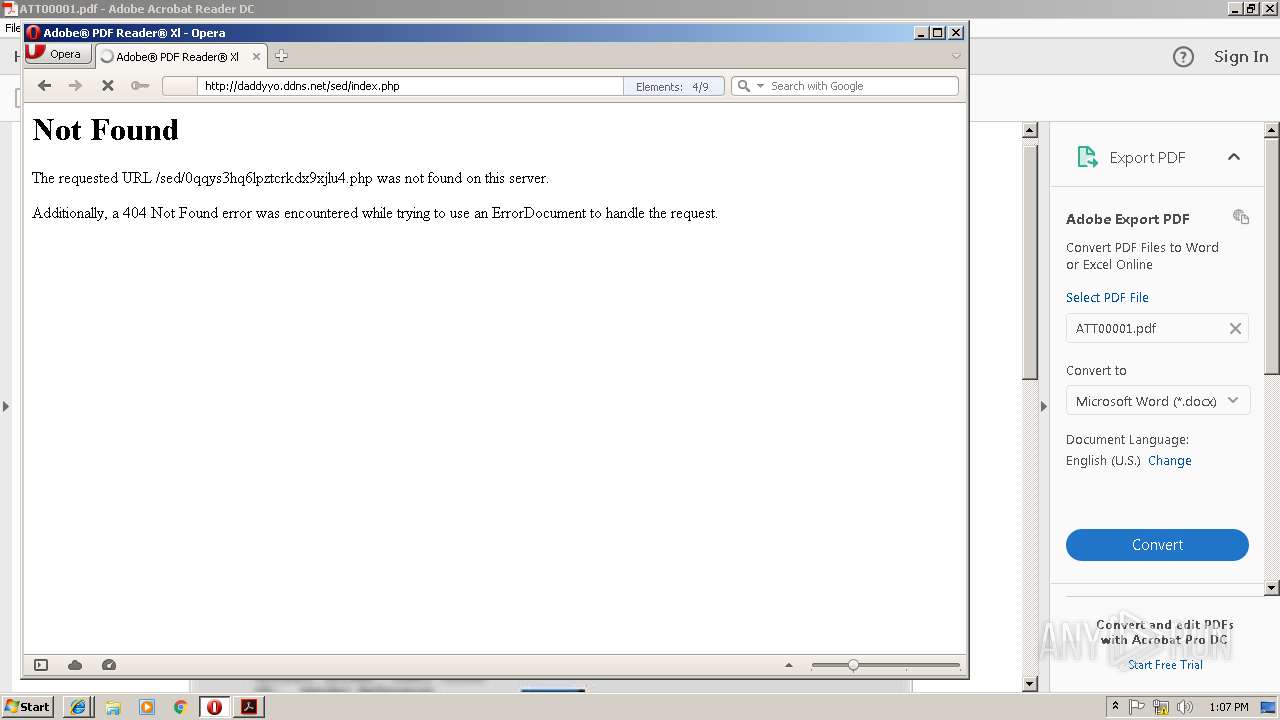
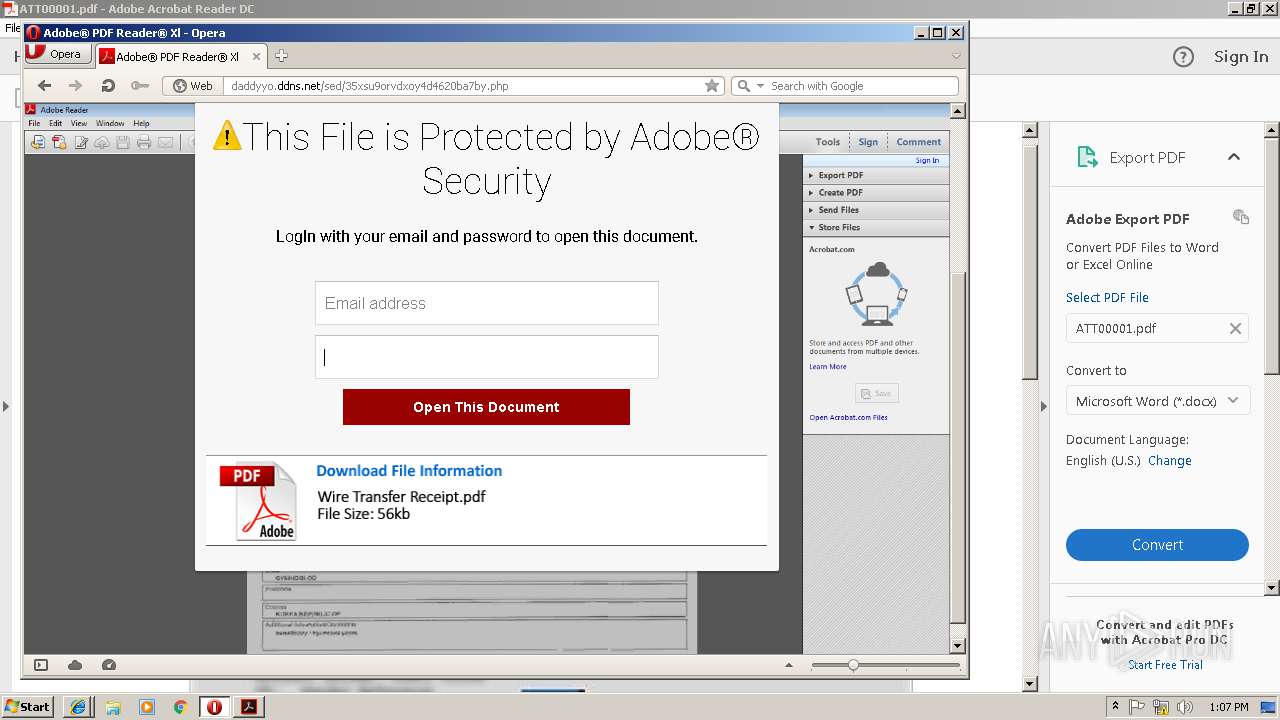
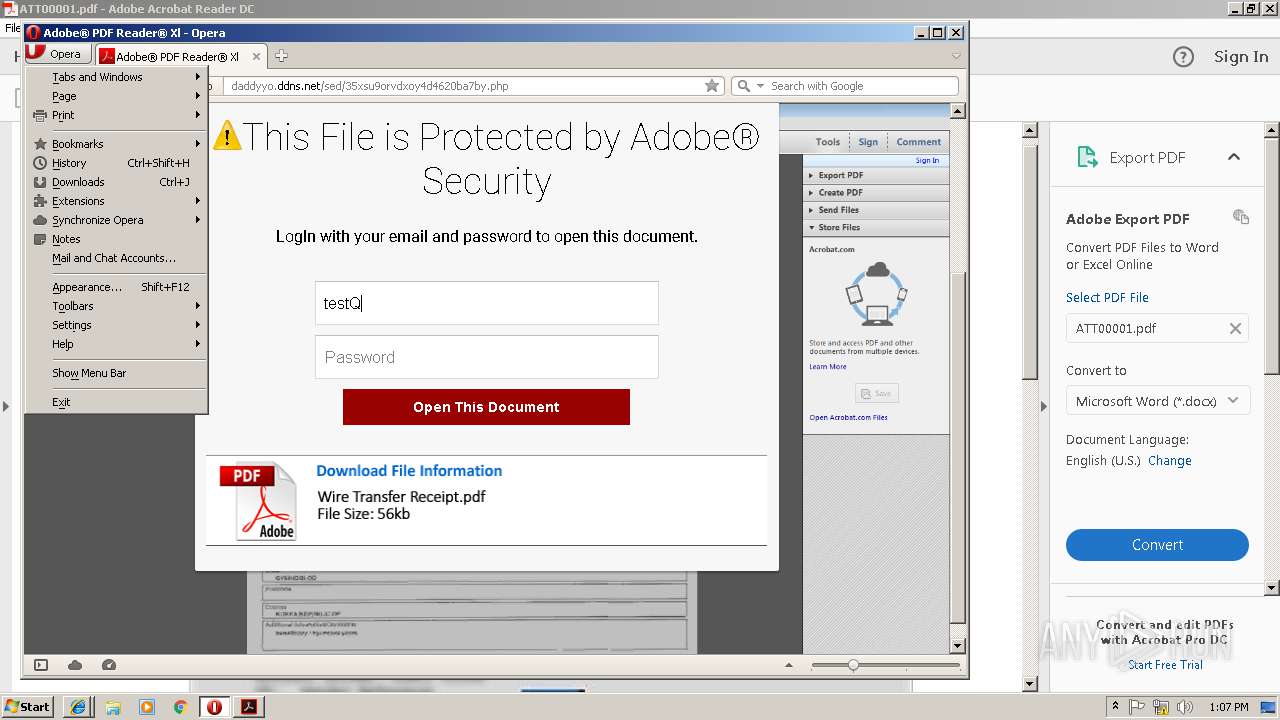
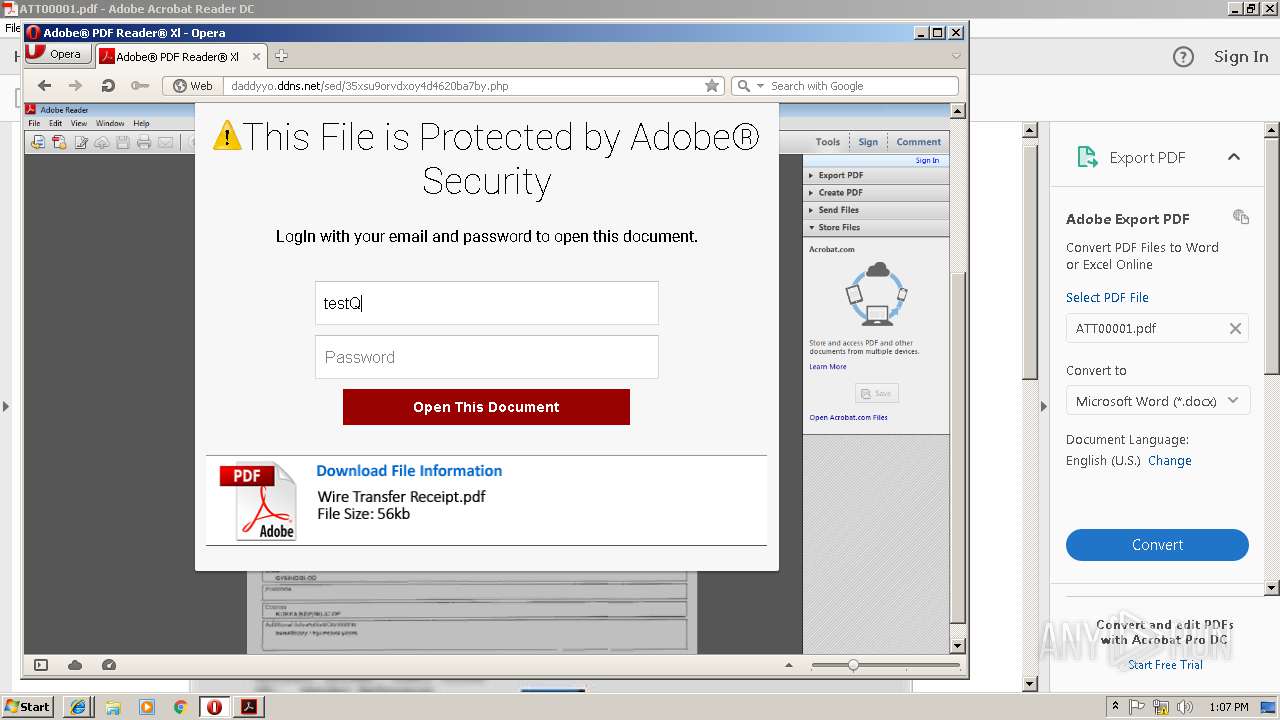
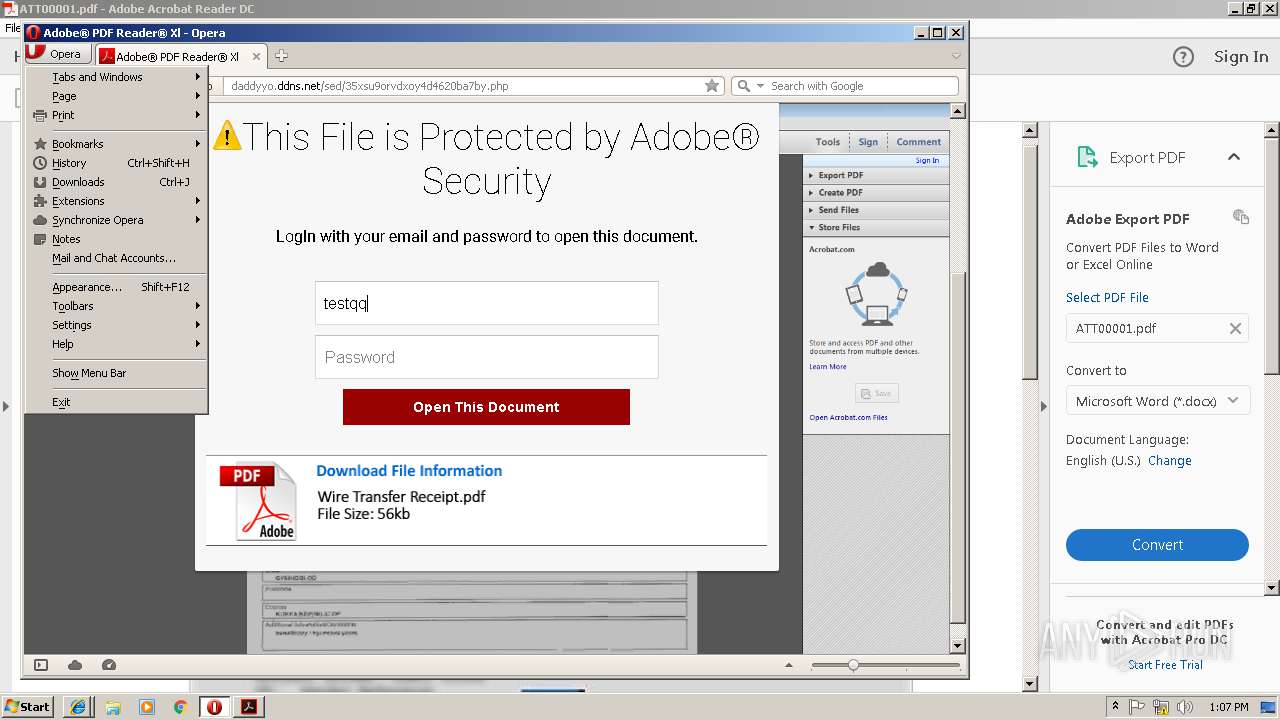
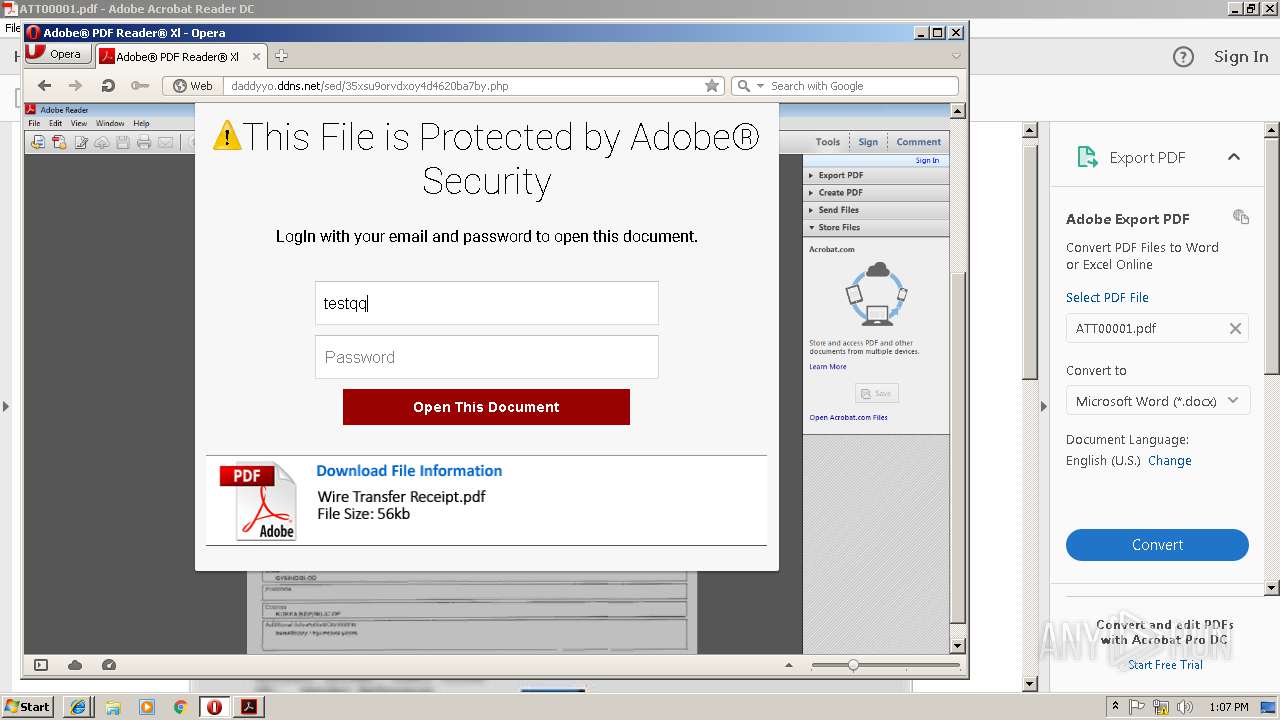
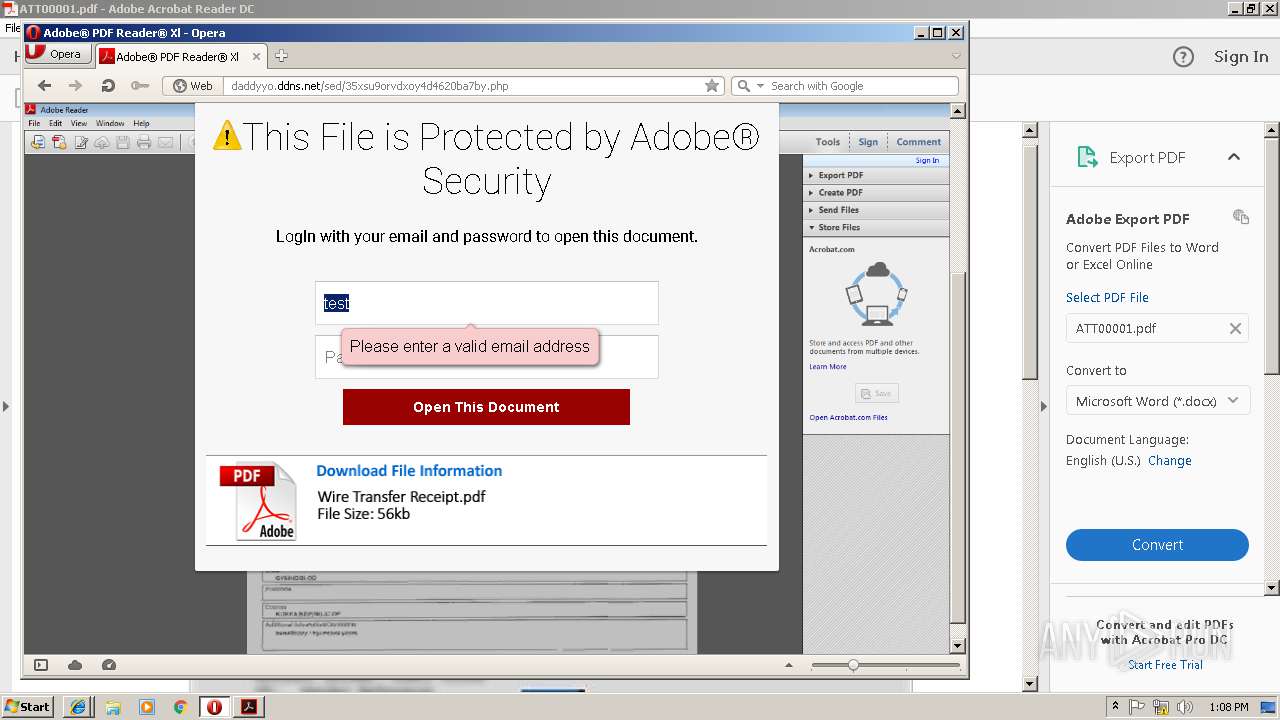
3244 | iexplore.exe | GET | 302 | 45.122.138.17:80 | http://daddyyo.ddns.net/sed/index.php | HK | — | — | malicious |
3096 | iexplore.exe | GET | 302 | 45.122.138.17:80 | http://daddyyo.ddns.net/sed/index.php | HK | — | — | malicious |
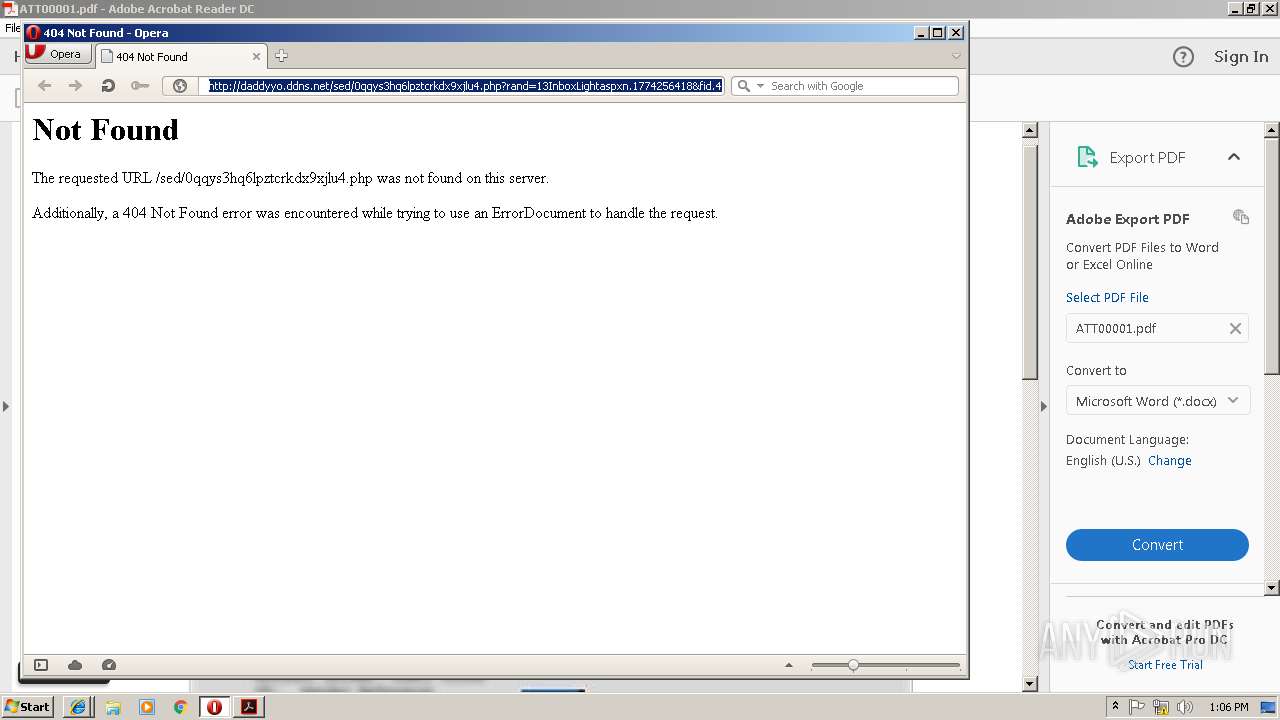
2384 | opera.exe | GET | — | 45.122.138.17:80 | http://daddyyo.ddns.net/sed/0qqys3hq6lpztcrkdx9xjlu4.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=&.rand=13InboxLight.aspx?n=1774256418&fid=4 | HK | — | — | malicious |
2896 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2896 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
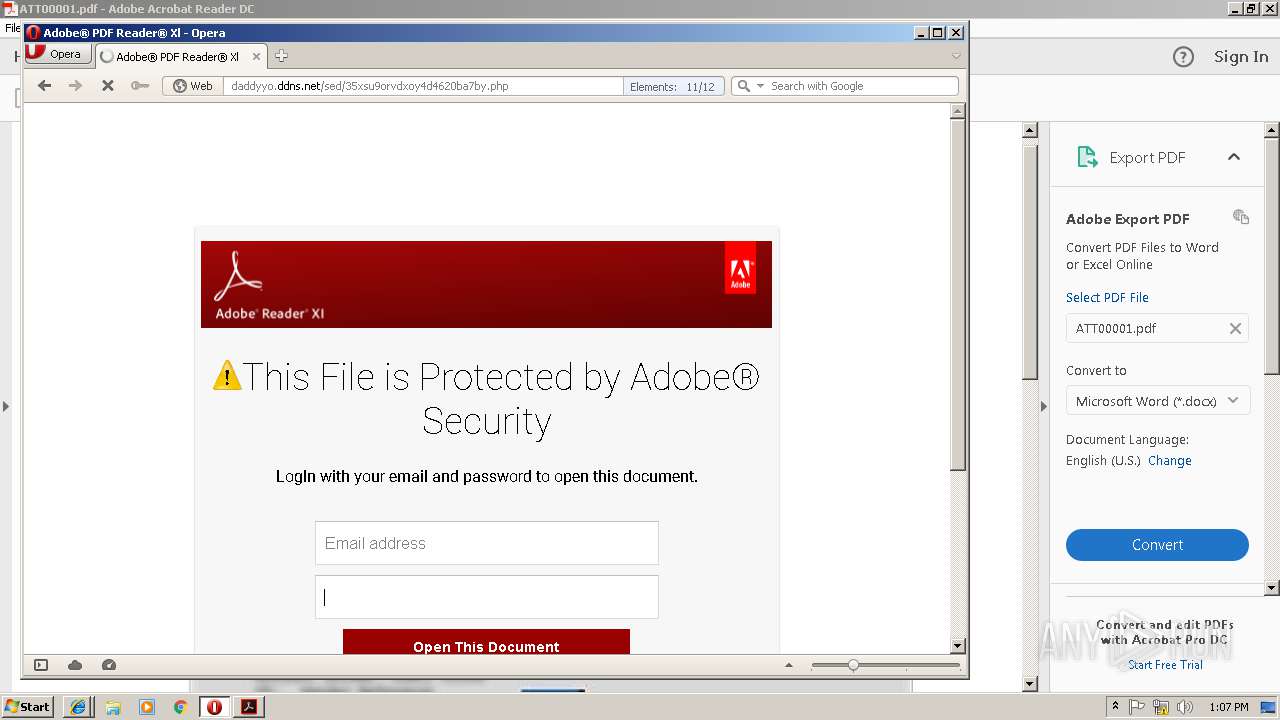
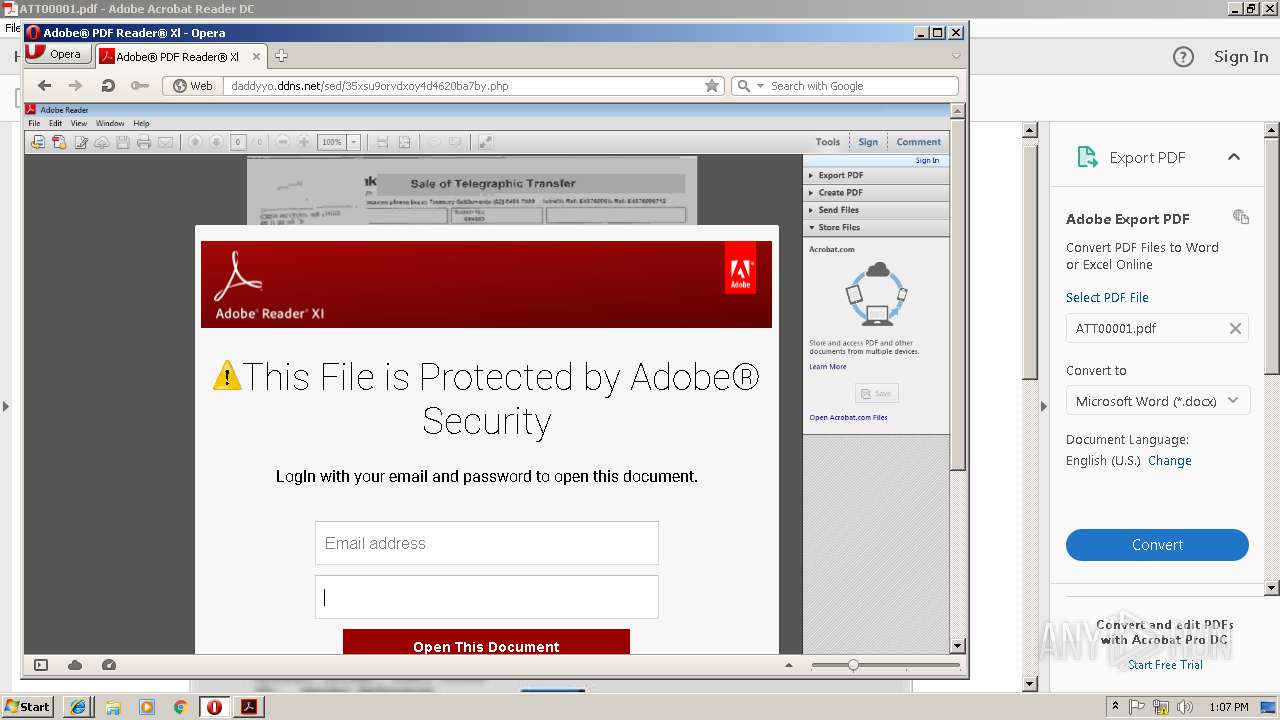
3244 | iexplore.exe | GET | 200 | 45.122.138.17:80 | http://daddyyo.ddns.net/sed/0ab46tdlbssilb544cqzlo1a.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=&.rand=13InboxLight.aspx?n=1774256418&fid=4 | HK | html | 3.38 Kb | malicious |
2384 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
3096 | iexplore.exe | GET | 200 | 45.122.138.17:80 | http://daddyyo.ddns.net/sed/0qqys3hq6lpztcrkdx9xjlu4.php?rand=13InboxLightaspxn.1774256418&fid.4.1252899642&fid=1&fav.1&rand.13InboxLight.aspxn.1774256418&fid.1252899642&fid.1&fav.1&email=&.rand=13InboxLight.aspx?n=1774256418&fid=4 | HK | html | 3.38 Kb | malicious |
2384 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
1584 | iexplore.exe | GET | — | 45.122.138.17:80 | http://daddyyo.ddns.net/sed/index.php | HK | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2384 | opera.exe | 172.217.18.170:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3244 | iexplore.exe | 45.122.138.17:80 | daddyyo.ddns.net | Guochao Group limited | HK | malicious |
2632 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2896 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3244 | iexplore.exe | 172.217.22.74:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2896 | AcroRd32.exe | 2.16.186.33:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
2632 | iexplore.exe | 45.122.138.17:80 | daddyyo.ddns.net | Guochao Group limited | HK | malicious |
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3096 | iexplore.exe | 45.122.138.17:80 | daddyyo.ddns.net | Guochao Group limited | HK | malicious |
— | — | 23.54.113.182:443 | ardownload2.adobe.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
daddyyo.ddns.net |
| malicious |
www.bing.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3244 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
3096 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
2384 | opera.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
1584 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
2384 | opera.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
2384 | opera.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |
4 ETPRO signatures available at the full report