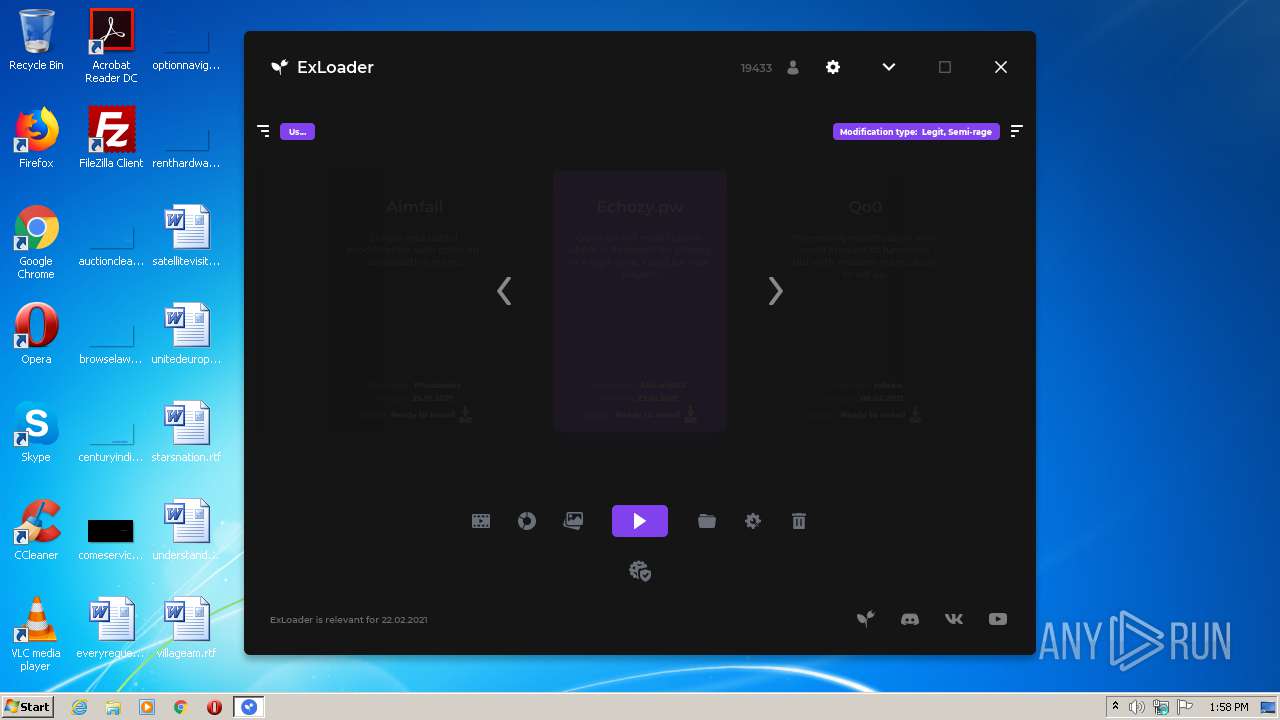
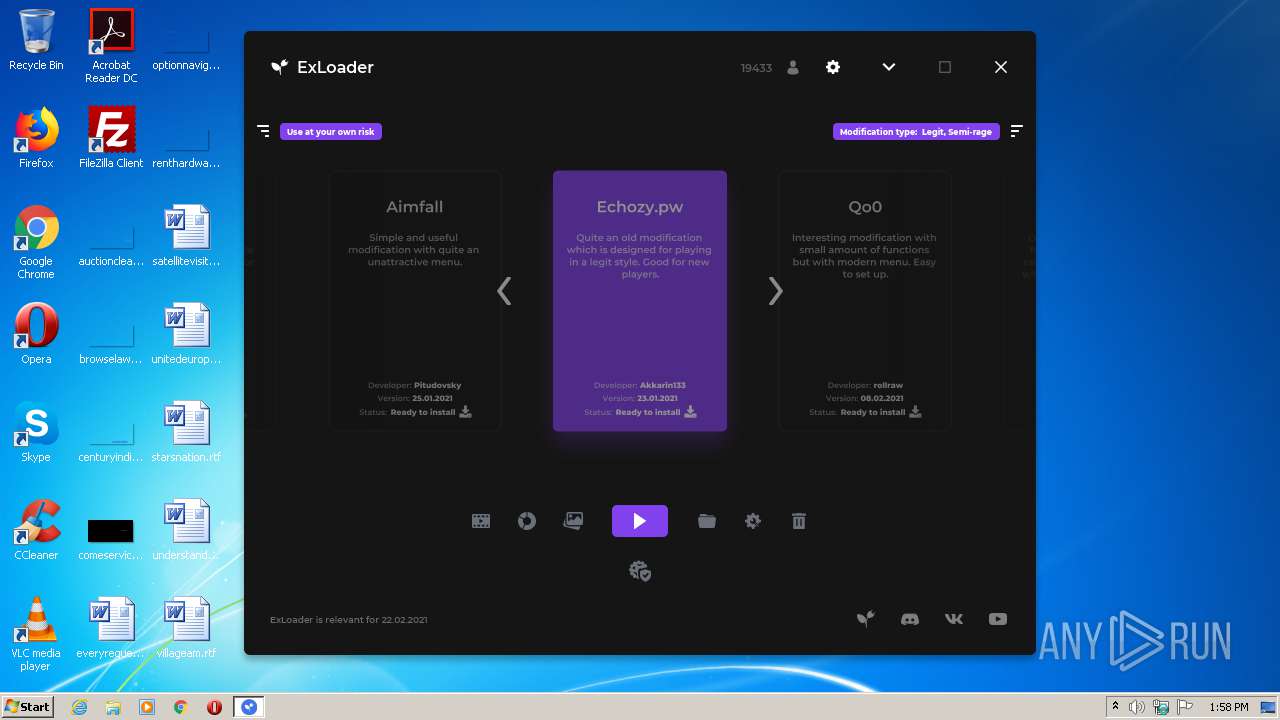
| File name: | ExLoader.exe |
| Full analysis: | https://app.any.run/tasks/8a208e97-aa58-466d-8810-ca30d5d91fdb |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2021, 13:57:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 6B8D4A6FE634501BB85E2E1507D46E32 |
| SHA1: | 64884341F5AFA812B8C8CAE40664940A86A7E8E7 |
| SHA256: | A176E914F8C97804BAFD4C619CC0E3986EA2B8B3FDBA793884906B6D6EF0D124 |
| SSDEEP: | 196608:H9i9sq7aUM2+6hhZdroXhfRRwaaFgchipDCwZblO9etcPNvseI:diMU75PZZoXlRRwa5co1NZh9cPo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 2496)
- cmd.exe (PID: 1836)
- cmd.exe (PID: 2768)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 2404)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 4080)
- cmd.exe (PID: 440)
- cmd.exe (PID: 560)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 892)
- cmd.exe (PID: 3136)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 988)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 2640)
Creates files in the user directory
- javaw.exe (PID: 1796)
- powershell.exe (PID: 1572)
Executes PowerShell scripts
- javaw.exe (PID: 1796)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 1796)
- javaw.exe (PID: 376)
- java.exe (PID: 2252)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1836)
- cmd.exe (PID: 2496)
- cmd.exe (PID: 2768)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 2404)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2640)
- cmd.exe (PID: 3840)
Executes JAVA applets
- ExLoader.exe (PID: 2800)
- ExLoader.exe (PID: 1624)
- javaw.exe (PID: 376)
Creates files in the program directory
- javaw.exe (PID: 376)
Checks Windows language
- reg.exe (PID: 3900)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 4080)
- cmd.exe (PID: 440)
- cmd.exe (PID: 560)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 892)
- cmd.exe (PID: 3136)
- cmd.exe (PID: 988)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 3136)
- cmd.exe (PID: 988)
INFO
Checks supported languages
- reg.exe (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:02:14 21:28:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 19968 |
| InitializedDataSize: | 15872 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.5.21.0 |
| ProductVersionNumber: | 2.5.21.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | SwiftSoft |
| FileDescription: | Unified library of game modifications |
| FileVersion: | 2.5.21.0 |
| InternalName: | ExLoader |
| LegalCopyright: | SwiftSoft |
| LegalTrademarks: | ExLoader |
| OriginalFileName: | ExLoader.exe |
| ProductName: | ExLoader |
| ProductVersion: | 2.5.21.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Feb-2021 20:28:14 |
| Detected languages: |
|
| CompanyName: | SwiftSoft |
| FileDescription: | Unified library of game modifications |
| FileVersion: | 2.5.21.0 |
| InternalName: | ExLoader |
| LegalCopyright: | SwiftSoft |
| LegalTrademarks: | ExLoader |
| OriginalFilename: | ExLoader.exe |
| ProductName: | ExLoader |
| ProductVersion: | 2.5.21.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Feb-2021 20:28:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004CE0 | 0x00004E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03278 |
.data | 0x00006000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00007000 | 0x00000680 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92317 |
.bss | 0x00008000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65099 |
.rsrc | 0x00012000 | 0x000027A4 | 0x00002800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.4416 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.31167 | 784 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
13 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 2 | 4 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 5.36446 | 74 | UNKNOWN | Process Default Language | RT_RCDATA |
22 | 4.10539 | 24 | UNKNOWN | Process Default Language | RT_RCDATA |
30 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
131
Monitored processes
70
Malicious processes
6
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | C:\Windows\System32\reg.exe query "HKEY_LOCAL_MACHINE\SOFTWARE\Valve\Steam" /v "InstallPath" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | C:\Windows\System32\chcp.com 866 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\ExLoader.exe" %* %* | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | ExLoader.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 440 | C:\Windows\System32\cmd.exe /c "C:\Windows\System32\chcp.com 866>nul & C:\Windows\System32\wbem\wmic.exe path Win32_ComputerSystem get TotalPhysicalMemory /Format:List | C:\Windows\System32\more.com" | C:\Windows\System32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 464 | C:\Windows\System32\wbem\wmic.exe Path Win32_VideoController Get AdapterRAM /Format:List | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | C:\Windows\System32\cmd.exe /c "C:\Windows\System32\chcp.com 866>nul & C:\Windows\System32\wbem\wmic.exe CPU get CurrentVoltage /Format:List | C:\Windows\System32\more.com" | C:\Windows\System32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 756 | C:\Windows\System32\chcp.com 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | C:\Windows\System32\cmd.exe /c "C:\Windows\System32\chcp.com 866>nul & C:\Windows\System32\wbem\wmic.exe CPU get Name /Format:List | C:\Windows\System32\more.com" | C:\Windows\System32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 940 | C:\Windows\System32\reg.exe query "HKU\S-1-5-19" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | C:\Windows\System32\more.com | C:\Windows\System32\more.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: More Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
762
Read events
700
Write events
62
Delete events
0
Modification events
| (PID) Process: | (1796) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (1572) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1572) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1572) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (376) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2252) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
Executable files
0
Suspicious files
2
Text files
13
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1572 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RHC3EZ3EC7Y5VRXKR8B5.temp | — | |
MD5:— | SHA256:— | |||
| 2252 | java.exe | C:\ProgramData\ExLoader\config.json | text | |
MD5:1685C4495C0414197F8C595239F7106C | SHA256:5BC7AF02756C3AC58DB8F117105AEA6EF76423EDFA61ECE209DA2300F4B563B6 | |||
| 1572 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFe8067.TMP | binary | |
MD5:7B952B5577A4BF89CB200BCB001DED0E | SHA256:EC6C30933C10130474F9D3C9282E83DC6F18DA0596621B30330ACBBCBD43FBC4 | |||
| 1572 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:7B952B5577A4BF89CB200BCB001DED0E | SHA256:EC6C30933C10130474F9D3C9282E83DC6F18DA0596621B30330ACBBCBD43FBC4 | |||
| 1796 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:5CE879506632807C021BAB43C5428EBA | SHA256:4C5F476F4000BA5DD6B2B1B75A1A2C3F697D0D4C2160BE2724265BE01C2702C6 | |||
| 376 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:B78F2DE28D7714036644FEEED6B9328A | SHA256:091FF6F07EFA49266994EC1B0140D7BC3D025F3779A3427562844C9B1E21E0A7 | |||
| 376 | javaw.exe | C:\ProgramData\ExLoader\config.json | text | |
MD5:3BF3DF175F80B7DFD1BEE32332DE66A2 | SHA256:A99A5D06CB8E6AE6CE1336DDBAA638439C231BAE0C54BE1B9298F90CCEE10BC1 | |||
| 2252 | java.exe | C:\Users\admin\AppData\Local\Temp\+JXF5416633896044370958.tmp | ttf | |
MD5:6D1796A9F798CED8961BAF3C79F894B6 | SHA256:DA0B09317F1CEFFB9767876579B15DC4DC9F75784E678404AA80632B6771207D | |||
| 2252 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:3C61E17DF631E133233AB5AEF4F1D7B6 | SHA256:AC0CF1897AFBDCB5C62CD54F70E42C1A5E03DEF1FE3ECAE75CE8E318A1ECE390 | |||
| 376 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF5219504726503206330.tmp | ttf | |
MD5:88932DADC42E1BBA93B21A76DE60EF7A | SHA256:C4C8CB572A5A2C43D78B3701F4B2349684E6CA4D1557E469AF6065B1E099C26C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
376 | javaw.exe | 104.21.23.26:443 | exloader.net | Cloudflare Inc | US | unknown |
2252 | java.exe | 172.67.171.116:443 | exloader.ru | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
exloader.net |
| unknown |
exloader.ru |
| suspicious |