| File name: | register.cmd |
| Full analysis: | https://app.any.run/tasks/92db70aa-373f-4bfc-952d-3940d31ed95d |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2024, 14:14:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (340), with CRLF line terminators |
| MD5: | 69D7C77DA0C817B911E7FCBFEB1DD271 |
| SHA1: | 1DB8578EA39BB51AACA5D545D0F2F8524C52E8F0 |
| SHA256: | A171D3AE6B224D7C2AB8B778AA66311E2A91C91540DAB6606623B36C02F548CA |
| SSDEEP: | 24:/F8iY/NLCEotn1tyRVPRx8q8SJTfmsm4O:YOqlRxj8SJj9m4O |
MALICIOUS
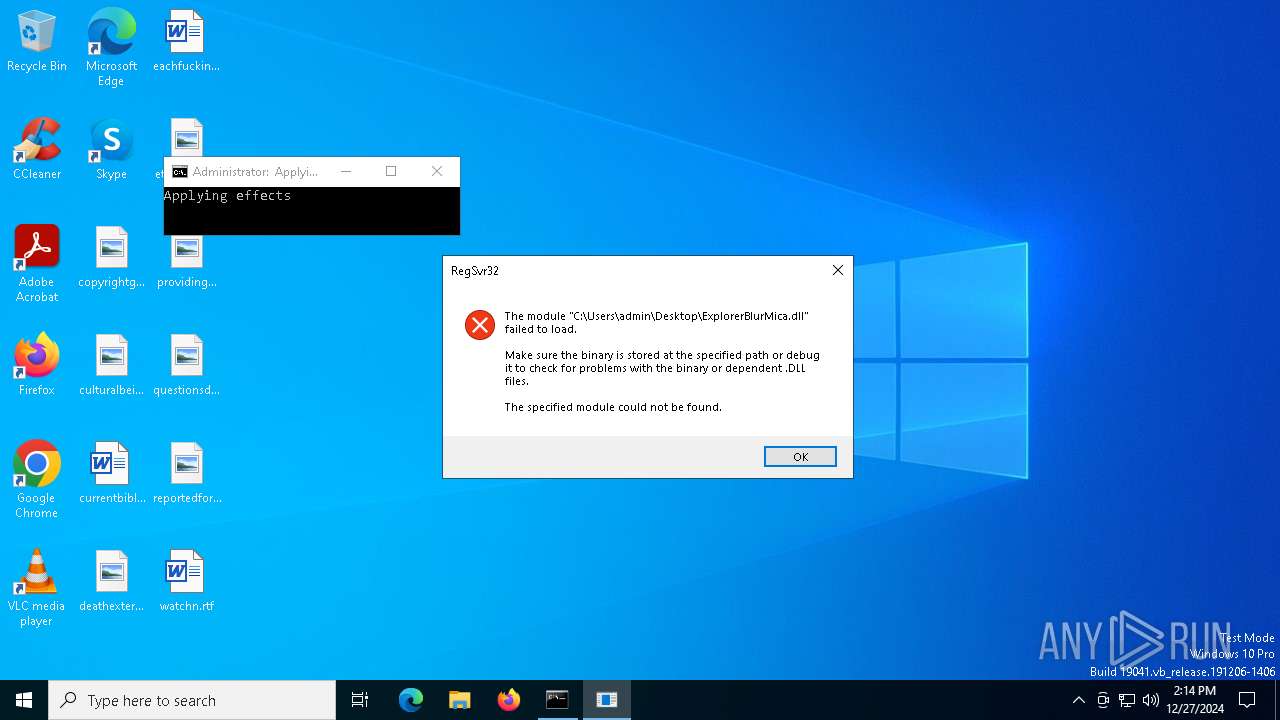
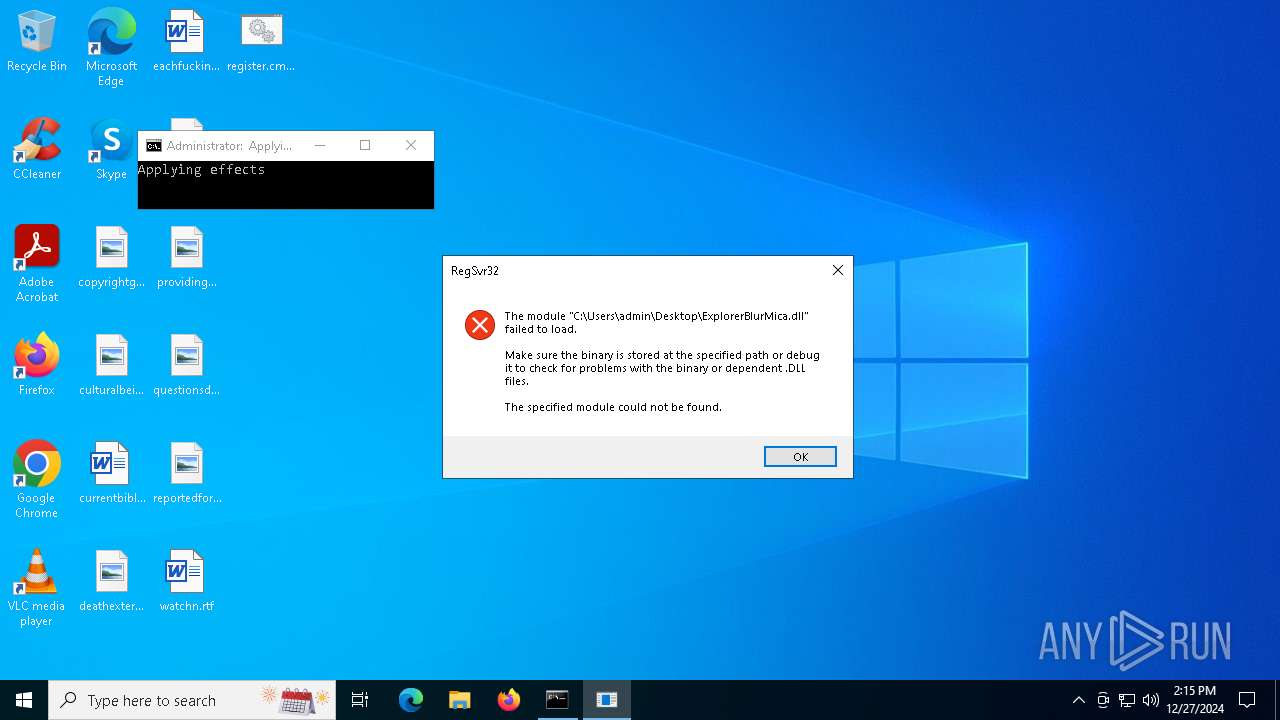
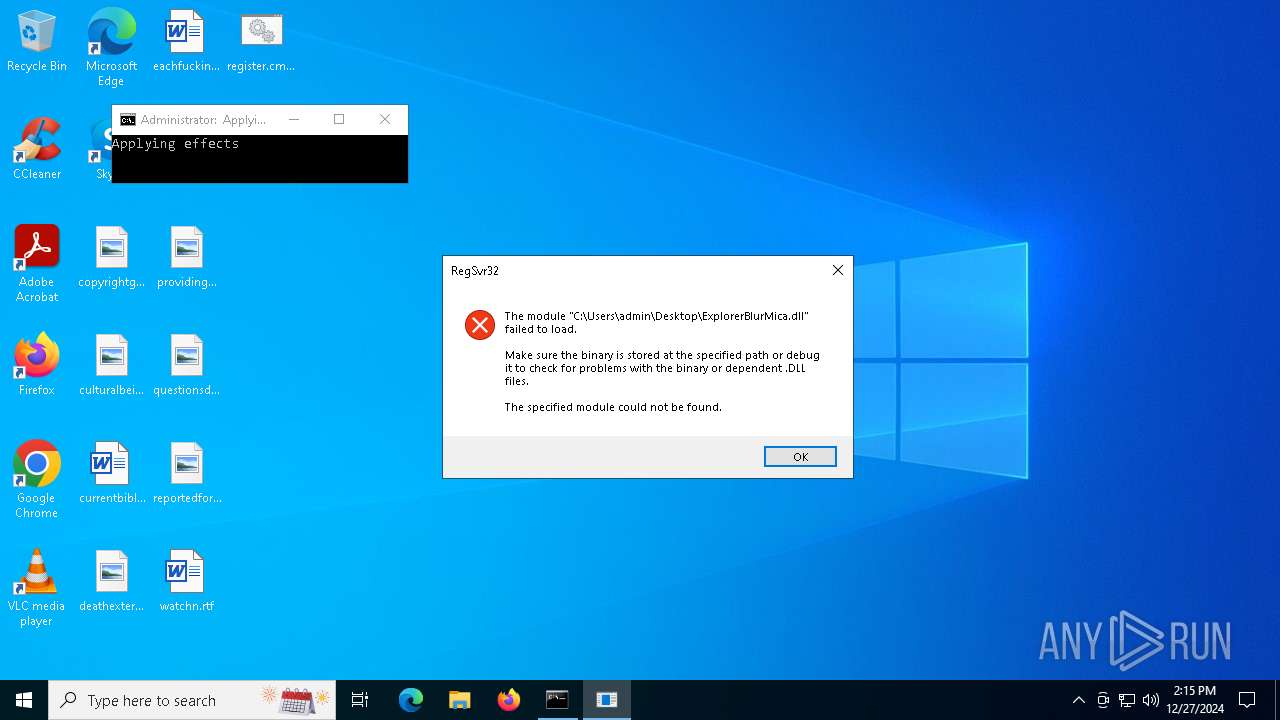
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 6480)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 4704)
SUSPICIOUS
The process executes VB scripts
- cmd.exe (PID: 5968)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 5048)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5968)
- wscript.exe (PID: 6148)
- explorer.exe (PID: 6468)
- cmd.exe (PID: 7104)
- wscript.exe (PID: 5116)
- explorer.exe (PID: 5288)
- cmd.exe (PID: 5048)
- wscript.exe (PID: 5208)
Executing commands from a ".bat" file
- cmd.exe (PID: 5968)
- wscript.exe (PID: 6148)
- explorer.exe (PID: 6468)
- cmd.exe (PID: 7104)
- wscript.exe (PID: 5116)
- explorer.exe (PID: 5288)
- cmd.exe (PID: 5048)
- wscript.exe (PID: 5208)
Application launched itself
- cmd.exe (PID: 5968)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 5048)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6148)
- wscript.exe (PID: 5116)
- wscript.exe (PID: 5208)
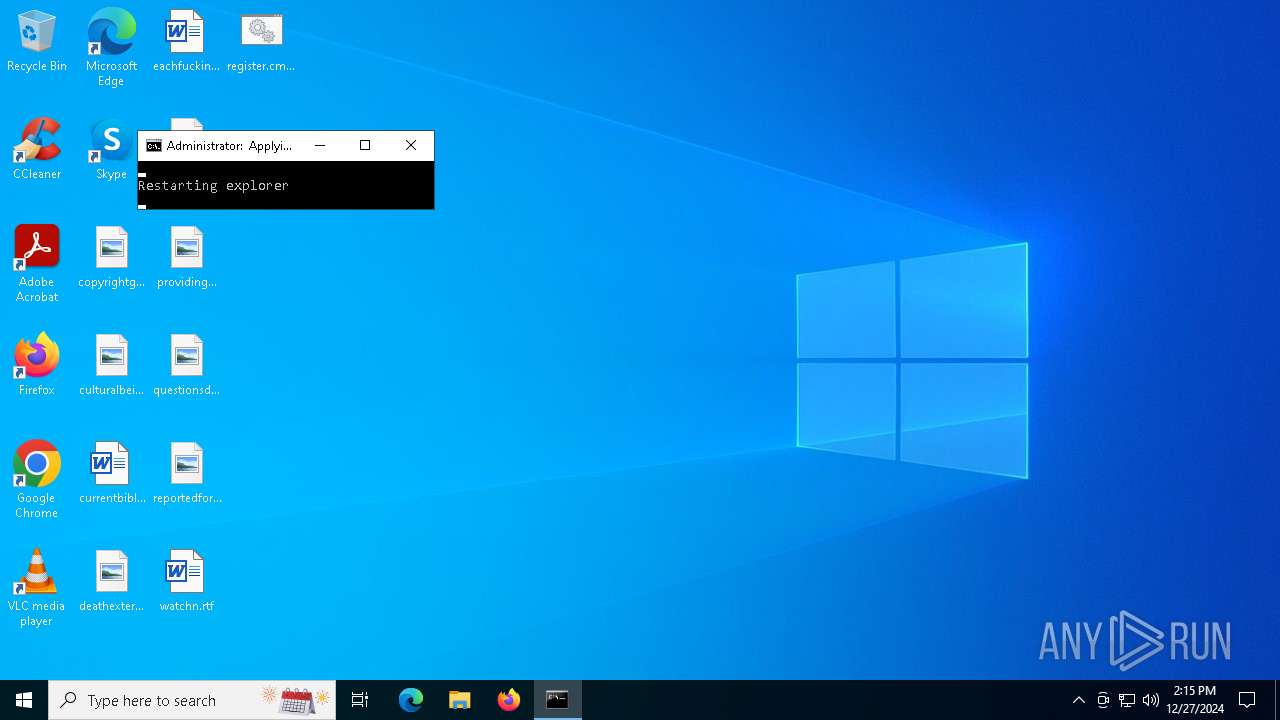
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6480)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 4704)
Executing commands from ".cmd" file
- explorer.exe (PID: 6468)
- explorer.exe (PID: 5288)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5084)
- cmd.exe (PID: 4704)
- cmd.exe (PID: 6480)
The process executes via Task Scheduler
- explorer.exe (PID: 5288)
- explorer.exe (PID: 6468)
- explorer.exe (PID: 6740)
Reads the date of Windows installation
- SearchApp.exe (PID: 2572)
- StartMenuExperienceHost.exe (PID: 6628)
INFO
Starts MODE.COM to configure console settings
- mode.com (PID: 3608)
- mode.com (PID: 6556)
- mode.com (PID: 3176)
- mode.com (PID: 1820)
- mode.com (PID: 4788)
- mode.com (PID: 3744)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 2972)
- SearchApp.exe (PID: 4164)
- StartMenuExperienceHost.exe (PID: 4112)
- SearchApp.exe (PID: 2572)
- StartMenuExperienceHost.exe (PID: 6628)
- SearchApp.exe (PID: 1856)
Checks supported languages
- mode.com (PID: 3608)
- mode.com (PID: 6556)
- TextInputHost.exe (PID: 1296)
- mode.com (PID: 3176)
- SearchApp.exe (PID: 4164)
- SearchApp.exe (PID: 2572)
- StartMenuExperienceHost.exe (PID: 4112)
- TextInputHost.exe (PID: 5300)
- mode.com (PID: 3744)
- StartMenuExperienceHost.exe (PID: 6628)
- GameBar.exe (PID: 2084)
- TextInputHost.exe (PID: 6084)
- SearchApp.exe (PID: 1856)
- StartMenuExperienceHost.exe (PID: 2972)
Reads the computer name
- TextInputHost.exe (PID: 1296)
- SearchApp.exe (PID: 4164)
- StartMenuExperienceHost.exe (PID: 4112)
- GameBar.exe (PID: 2084)
- StartMenuExperienceHost.exe (PID: 2972)
Sends debugging messages
- StartMenuExperienceHost.exe (PID: 2972)
- StartMenuExperienceHost.exe (PID: 6628)
The process uses the downloaded file
- explorer.exe (PID: 6468)
- explorer.exe (PID: 5288)
Reads the software policy settings
- SearchApp.exe (PID: 4164)
- SearchApp.exe (PID: 2572)
- BackgroundTransferHost.exe (PID: 6808)
Checks proxy server information
- SearchApp.exe (PID: 4164)
- explorer.exe (PID: 6468)
- SearchApp.exe (PID: 2572)
- explorer.exe (PID: 5288)
- BackgroundTransferHost.exe (PID: 6808)
Reads security settings of Internet Explorer
- explorer.exe (PID: 6468)
- explorer.exe (PID: 5288)
- BackgroundTransferHost.exe (PID: 4968)
- BackgroundTransferHost.exe (PID: 6520)
- BackgroundTransferHost.exe (PID: 6808)
- BackgroundTransferHost.exe (PID: 4544)
- BackgroundTransferHost.exe (PID: 2972)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 4164)
- SearchApp.exe (PID: 2572)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 6808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
66
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 1 Version: 123.26505.0.0 Modules
| |||||||||||||||
| 1516 | explorer.exe | C:\Windows\explorer.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 2 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1796 | cmd /u /c echo Set UAC = CreateObject("Shell.Application") : UAC.ShellExecute "cmd.exe", "/k cd ""C:\Users\admin\Desktop\"" && ""C:\Users\admin\Desktop\REGIST~1.BAT"" ", "", "runas", 1 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1820 | mode CON COLS=37 LINES=3 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1856 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | taskkill /F /IM explorer.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | fsutil dirty query C: | C:\Windows\System32\fsutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: fsutil.exe Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe" -ServerName:App.AppXbdkk0yrkwpcgeaem8zk81k8py1eaahny.mca | C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2572 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 1 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
72 354
Read events
71 736
Write events
557
Delete events
61
Modification events
| (PID) Process: | (5968) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (7100) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{eaf65672-68c3-4f99-8d5c-104b5f4d8fff} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7100) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e73-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7100) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e72-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7100) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e71-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7100) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6468) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | delete value | Name: | SearchboxTaskbarModeForceGlyph |
Value: | |||
| (PID) Process: | (6468) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | SearchGlyphType |
Value: 2 | |||
| (PID) Process: | (6468) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisible |
Value: 0 | |||
| (PID) Process: | (6468) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search |
| Operation: | write | Name: | TraySearchBoxVisibleOnAnyMonitor |
Value: 0 | |||
Executable files
4
Suspicious files
65
Text files
122
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5968 | cmd.exe | C:\Users\admin\AppData\Local\Temp\getadmin.vbs | binary | |
MD5:493D41C252F720B8C4507FBD9172C5A6 | SHA256:2AB723854690F484B379776029E4E19A068CC5163A1ED71C4A732FABE1E66182 | |||
| 4244 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:B68173CDDF95F3669993F254D36AE779 | SHA256:3EE100AD8A3A30946F2C2C72552F3209CB20E801070DDEB42FC6A1BE60F08701 | |||
| 4164 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\95d9a2a97a42f02325559b453ba7f8fe839baa18.tbres | binary | |
MD5:70947D7DF70A200134756ED823FE752C | SHA256:EB390689A9DD7567264E23EBB5B4A51112D1607A933A0CE4B926F10BDCDDB84C | |||
| 4164 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:F9CB4423A4A70A7F48525712D492EECC | SHA256:2E0EAAD778FF82A65D0514FA8974D3F79B8F7E51DA58B64ACDB30E8922226687 | |||
| 4164 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\INetCache\Q84V0JUH\6hU_LneafI_NFLeDvM367ebFaKQ[1].js | binary | |
MD5:C6C21B7634D82C53FB86080014D86E66 | SHA256:D39E9BA92B07F4D50B11A49965E9B162452D7B9C9F26D9DCB07825727E31057E | |||
| 4164 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\Swi4yFavETfuSZ9mHxnUvb4UdTw[1].js | binary | |
MD5:B2C3CBF8A1D940D6C83D59A67486675C | SHA256:08EA9109346E9018ED50567503D2C141F7A84CFDE80EB25E97FDDCFE270BAA67 | |||
| 4164 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\FgBbpIj0thGWZOh_xFnM9i4O7ek[1].css | text | |
MD5:908111EB0FFB1360D5DD61279C21703E | SHA256:1ED87CF425DED994B05A842271AB4D28A76F399E571688CF2E7B186F70DC3059 | |||
| 4164 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\_BjeFNPDJ-N9umMValublyrbq4Y[1].css | text | |
MD5:15DC838A1A66277F9F4D915124DFFBBC | SHA256:9C947D5F732431197DA9DB1F159CB3D4CDC5DBFE55FDC0A9513E571FF31236A1 | |||
| 4164 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\dg0bEoz0nxScOpJJ_JI0IxFBuTs[1].css | text | |
MD5:071CD9CDFB86B42F65CCD66A7413EAC1 | SHA256:C1D6F71AF2376013D3B3FC25DB91CC9DA8D961084641312CCB96B3045AD921D5 | |||
| 4164 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\67\0u2b9EXo8LdXut1MFm4AD0phBuM.br[1].js | binary | |
MD5:8C0F73D4C854DC52B555898FEF7EDB54 | SHA256:B652F917E744E7A4EADB5DF108D622FD18C793E80445FAA69B1BFFC97BE2529E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
61
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6256 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6552 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2572 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6256 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6552 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2572 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6808 | BackgroundTransferHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
372 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5564 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.182:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |