| File name: | sample3.pdf |
| Full analysis: | https://app.any.run/tasks/c9efd1b9-b6a8-42f3-bd43-2d4592c4b63a |
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2024, 09:01:37 |
| OS: | Windows 8.1 Professional (build: 9600, 64 bit) |
| Tags: | |
| Indicators: | |
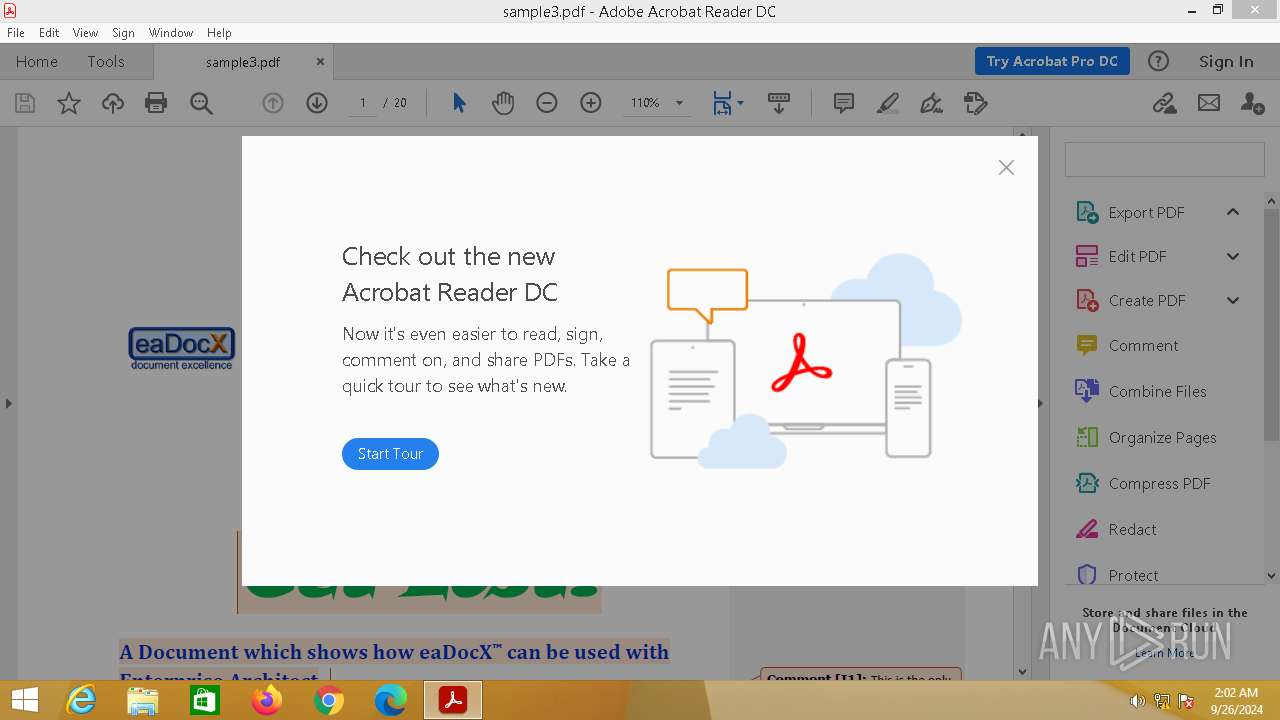
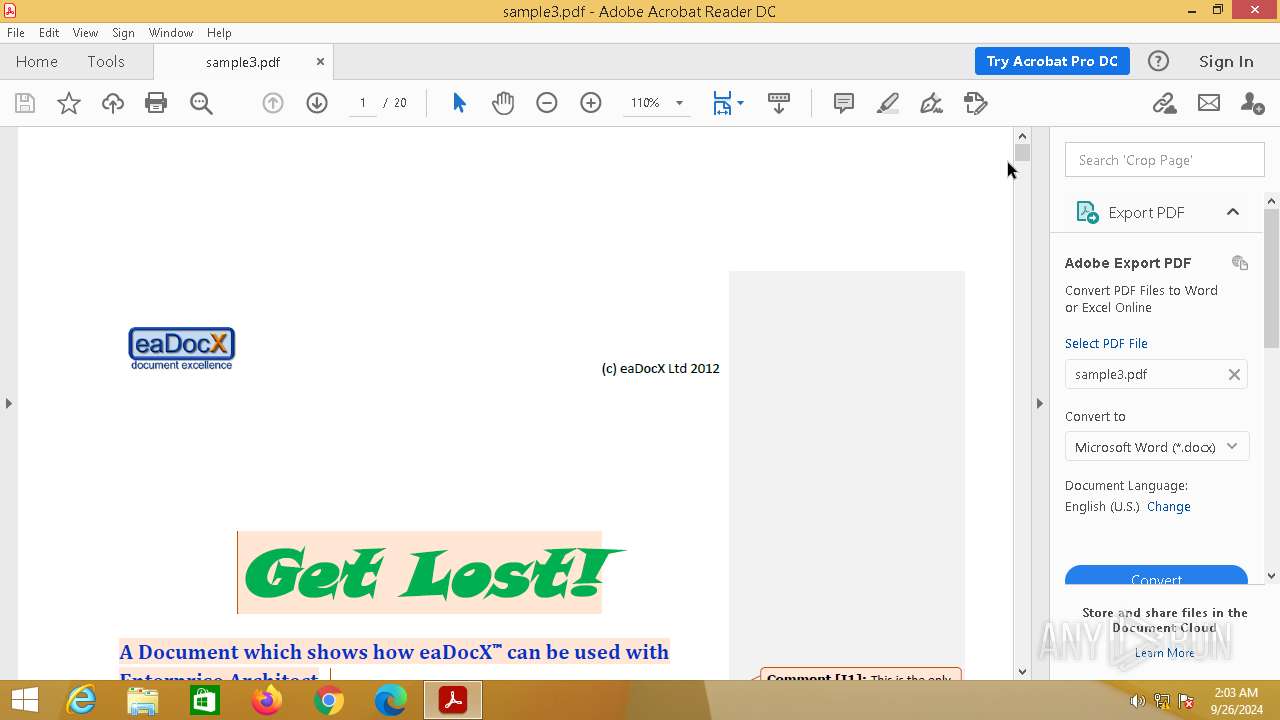
| MIME: | application/pdf |
| File info: | PDF document, version 1.5, 20 pages |
| MD5: | CA12EF7B9E7B41FDDE61D1CD60A6C41C |
| SHA1: | DD8774537C10C2610980361BCFC99D14DFDA235E |
| SHA256: | A16CFF406A7B806AD3B30803D46C413B13B6036AF4947847E0E30655C61B752A |
| SSDEEP: | 24576:snwGdjM6cJEpMcP+GIYSJONHVa7xJbGnSdh91RuSVrl1rbfyNPzB27Lh3p:Ak/cPjIYSKHQ7xJGnSrRhVjbyxzB2Z3p |
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 400)
SUSPICIOUS
Reads the Internet Settings
- slui.exe (PID: 944)
- slui.exe (PID: 3168)
Creates file in the systems drive root
- AcroRd32.exe (PID: 2416)
Reads settings of System Certificates
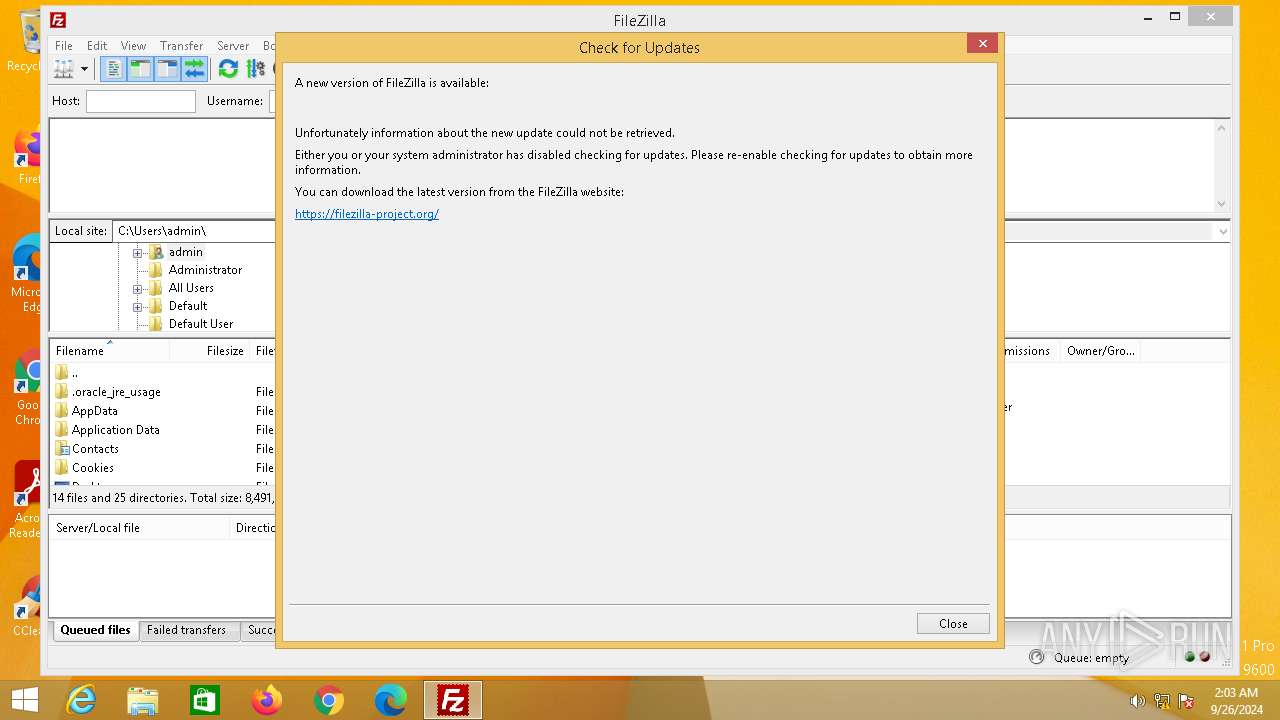
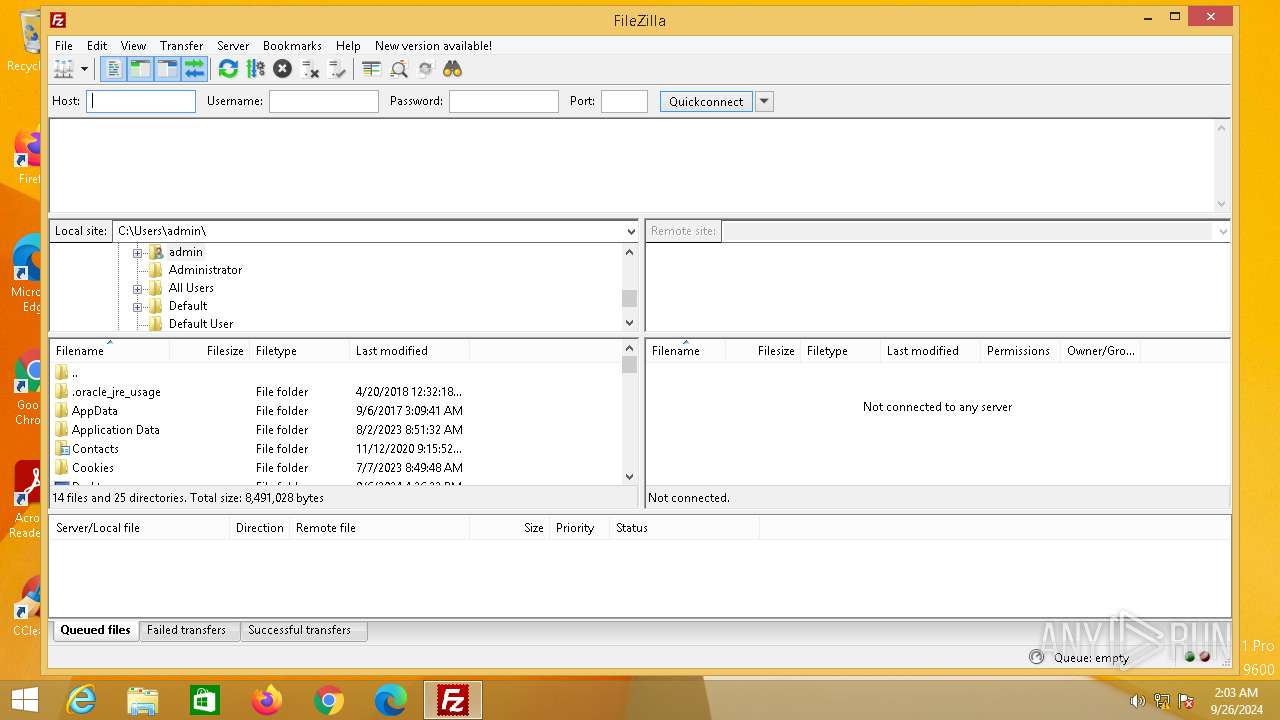
- filezilla.exe (PID: 3564)
INFO
An automatically generated document
- AcroRd32.exe (PID: 1752)
Application launched itself
- AcroRd32.exe (PID: 1752)
- RdrCEF.exe (PID: 2324)
- chrome.exe (PID: 3628)
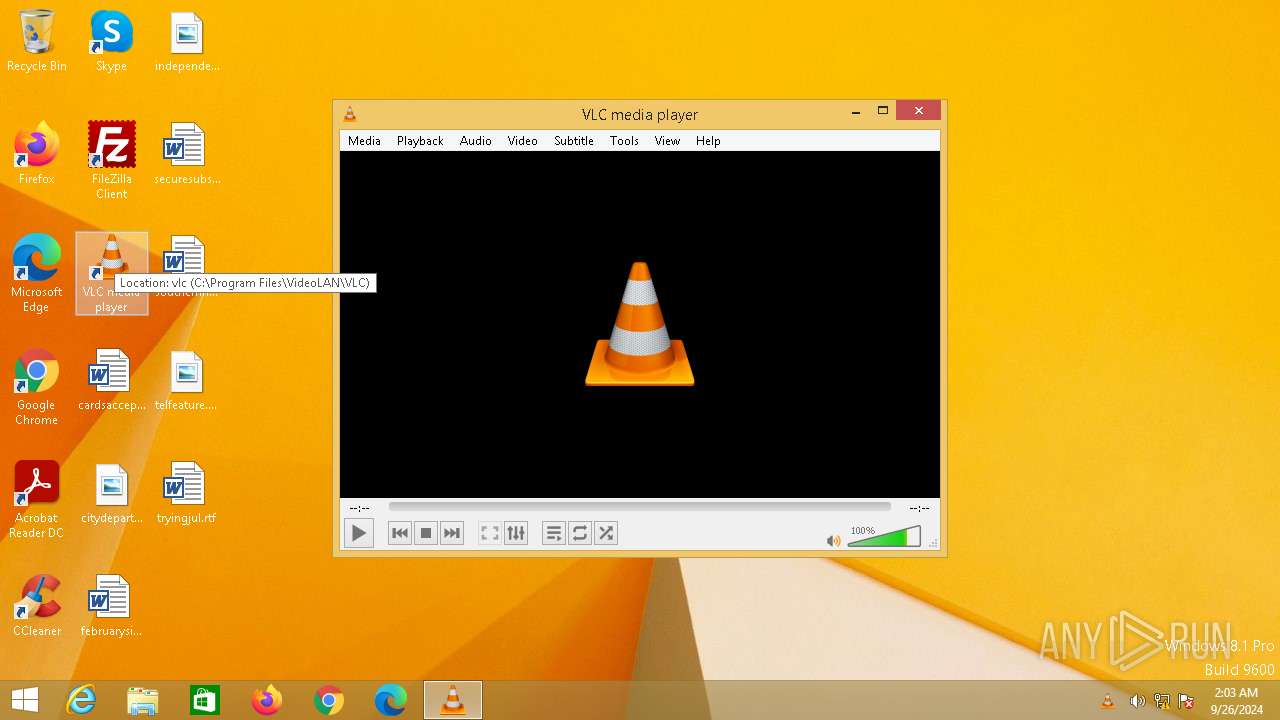
Sends debugging messages
- RdrCEF.exe (PID: 2324)
- vlc.exe (PID: 3448)
- AcroRd32.exe (PID: 2416)
Manual execution by a user
- vlc.exe (PID: 3448)
- filezilla.exe (PID: 3564)
- chrome.exe (PID: 3628)
The process uses the downloaded file
- AdobeARM.exe (PID: 3224)
- AcroRd32.exe (PID: 1752)
Checks supported languages
- vlc.exe (PID: 3448)
- filezilla.exe (PID: 3564)
Reads the computer name
- vlc.exe (PID: 3448)
- filezilla.exe (PID: 3564)
Creates files or folders in the user directory
- filezilla.exe (PID: 3564)
Reads the machine GUID from the registry
- filezilla.exe (PID: 3564)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 3224)
Reads Microsoft Office registry keys
- chrome.exe (PID: 2068)
- filezilla.exe (PID: 3564)
Reads the software policy settings
- slui.exe (PID: 3168)
- slui.exe (PID: 944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.5 |
|---|---|
| Linearized: | No |
| PageCount: | 20 |
| Language: | en-GB |
| TaggedPDF: | Yes |
| Title: | Sample #1 |
| Author: | Ian Mitchell |
| Creator: | Microsoft® Office Word 2007 |
| CreateDate: | 2012:05:21 12:33:16+01:00 |
| ModifyDate: | 2012:05:21 12:33:16+01:00 |
| Producer: | Microsoft® Office Word 2007 |
Total processes
84
Monitored processes
48
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 80 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1180,5207134956913206976,4129893501337599927,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --lang=en-US --service-sandbox-type=utility --disable-quic --mojo-platform-channel-handle=2348 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 388 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1180,5207134956913206976,4129893501337599927,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --lang=en-US --service-sandbox-type=utility --disable-quic --mojo-platform-channel-handle=3592 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 400 | C:\WINDOWS\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 508 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1180,5207134956913206976,4129893501337599927,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=2472 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 588 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1180,5207134956913206976,4129893501337599927,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --lang=en-US --service-sandbox-type=utility --disable-quic --mojo-platform-channel-handle=3576 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1180,5207134956913206976,4129893501337599927,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --lang=en-US --service-sandbox-type=utility --disable-quic --mojo-platform-channel-handle=3468 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 944 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 1256 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1180,5207134956913206976,4129893501337599927,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --lang=en-US --service-sandbox-type=utility --disable-quic --mojo-platform-channel-handle=3876 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1320 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1180,5207134956913206976,4129893501337599927,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --lang=en-US --service-sandbox-type=utility --disable-quic --mojo-platform-channel-handle=3448 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1420 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1180,5207134956913206976,4129893501337599927,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3860 /prefetch:1 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 105
Read events
22 652
Write events
433
Delete events
20
Modification events
| (PID) Process: | (1752) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934\Children |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1752) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1752) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934 |
| Operation: | write | Name: | DisplayName |
Value: Adobe Acrobat Reader DC Protected Mode | |||
| (PID) Process: | (1752) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934 |
| Operation: | write | Name: | Moniker |
Value: adobe.acrobatreaderdc.protectedmode | |||
| (PID) Process: | (2416) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2416) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | iNumReaderLaunches |
Value: 3 | |||
| (PID) Process: | (2416) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\FTEDialog |
| Operation: | write | Name: | bShowUpdateFTE |
Value: 1 | |||
| (PID) Process: | (2416) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcome |
| Operation: | write | Name: | bIsAcrobatUpdated |
Value: 1 | |||
| (PID) Process: | (2416) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcomeFirstMileReader |
| Operation: | write | Name: | iCardCountShown |
Value: 2 | |||
| (PID) Process: | (400) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Dnscache\Parameters\Probe\{365931fe-d1a0-4b53-9d15-7dd623d8a335} |
| Operation: | write | Name: | LastProbeTime |
Value: | |||
Executable files
160
Suspicious files
1 483
Text files
186
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\fd17b2d8331c91e8_0 | binary | |
MD5:6D80EFACBBC210D6994EBC78FBCEE12D | SHA256:0DF9CFA538437D6E2546194CB6E00E129BC772381DE534435C50A3D1ED3B182D | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\0786087c3c360803_0 | binary | |
MD5:3084671B7857DB0A4A1DBA7BDC84BC73 | SHA256:EB7D2189F692769A472996F1D3157B206ACDEE325A8D669FE56C6BD57A0A8B9C | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\aba6710fde0876af_0 | binary | |
MD5:5FC75734155D7A1D016A2F4A3110BE45 | SHA256:C8E09C763C15C3FDEDA0FA8D13E19A3C0A63B2AD43EE94C95F8EEE2968B591D2 | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\92c56fa2a6c4d5ba_0 | binary | |
MD5:04D8E357AA0522425D3BDB9CA27F9121 | SHA256:B50E0ABDFB9BF2251B37965E2CAF328BBF11584E47714DB1CC7C32B1CEAF9175 | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\983b7a3da8f39a46_0 | binary | |
MD5:672E049E5FEF9704CDF0B2317F70B91F | SHA256:833185C6DD1321C49DA98A2E0559476D08DFAFF6DE0ADA0F779F9D2E188B18E9 | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\946896ee27df7947_0 | binary | |
MD5:B99D233D60BC2A86DF2CCE16252888B0 | SHA256:5BA431A6F8FCA7960B5724E18B3DA4E92BFE916490FAD197AC98DE46EF953C22 | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\4a0e94571d979b3c_0 | binary | |
MD5:185EF619259BB0313C810E043A2EEC69 | SHA256:7D8704F2C48B741C9467B62396D9C2F4691C3A0C7A0A81F95060DF14812F9BEB | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\febb41df4ea2b63a_0 | binary | |
MD5:F91580DC775B2462E473A403FF57D414 | SHA256:938161DB67F4726676F12A3F1FF4B157E782669C4A4DB95580AC4A7ECF7AE037 | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\8e417e79df3bf0e9_0 | binary | |
MD5:34396F013C4917A6CC23F707D889F142 | SHA256:872054FC471E2948AD166399CAAB6AC3EA59B5BA5E954E9E2B4B1A8B957BFB95 | |||
| 2324 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\78bff3512887b83d_0 | binary | |
MD5:00B1020F6B50385DF187DBBE7F2DC37D | SHA256:33B3DFDDA763AADFCCA9E324694D4665C250862237B0F72C70B7CC5F7DCB269F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
988
TCP/UDP connections
209
DNS requests
119
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | OPTIONS | 204 | 23.22.254.206:443 | https://p13n.adobe.io/psdk/v2/content?surfaceId=DC_READER_LAUNCH_CARD&surfaceId=DC_Reader_RHP_Banner&surfaceId=DC_Reader_RHP_Retention&surfaceId=Edit_InApp_Aug2020&adcProductLanguage=en-us&adcVersion=20.13.20064&adcProductType=Reader&adcOSType=WIN&adcCountryCode=DE&adcXAPIClientID=api_reader_desktop_win_20.13.20064&encodingScheme=BASE_64 | unknown | — | — | unknown |
— | — | GET | 200 | 23.48.23.51:443 | https://acroipm2.adobe.com/20/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | unknown |
— | — | HEAD | 200 | 184.30.20.134:443 | https://armmf.adobe.com/arm-manifests/win/ReaderDCManifest3.msi | unknown | — | — | unknown |
— | — | HEAD | 200 | 23.48.23.39:443 | https://ardownload3.adobe.com/pub/adobe/reader/win/AcrobatDC/2400320112/AcroRdrDCUpd2400320112.msi | unknown | — | — | unknown |
— | — | GET | 200 | 23.213.164.167:443 | https://geo2.adobe.com/ | unknown | text | 59 b | whitelisted |
— | — | GET | 200 | 23.213.164.167:443 | https://geo2.adobe.com/ | unknown | text | 59 b | whitelisted |
— | — | GET | 206 | 184.30.20.134:443 | https://armmf.adobe.com/arm-manifests/win/ReaderDCManifest3.msi | unknown | binary | 5.45 Kb | whitelisted |
— | — | GET | 206 | 23.48.23.39:443 | https://ardownload3.adobe.com/pub/adobe/reader/win/AcrobatDC/2400320112/AcroRdrDCUpd2400320112.msi | unknown | binary | 5.56 Kb | whitelisted |
— | — | GET | 200 | 52.202.204.11:443 | https://p13n.adobe.io/psdk/v2/content?surfaceId=DC_READER_LAUNCH_CARD&surfaceId=DC_Reader_RHP_Banner&surfaceId=DC_Reader_RHP_Retention&surfaceId=Edit_InApp_Aug2020&adcProductLanguage=en-us&adcVersion=20.13.20064&adcProductType=Reader&adcOSType=WIN&adcCountryCode=DE&adcXAPIClientID=api_reader_desktop_win_20.13.20064&encodingScheme=BASE_64 | unknown | binary | 1.91 Kb | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2156 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
400 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2324 | RdrCEF.exe | 23.213.164.167:443 | geo2.adobe.com | AKAMAI-AS | DE | whitelisted |
944 | slui.exe | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2324 | RdrCEF.exe | 54.144.73.197:443 | p13n.adobe.io | AMAZON-AES | US | whitelisted |
3168 | slui.exe | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2324 | RdrCEF.exe | 184.30.20.134:443 | armmf.adobe.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
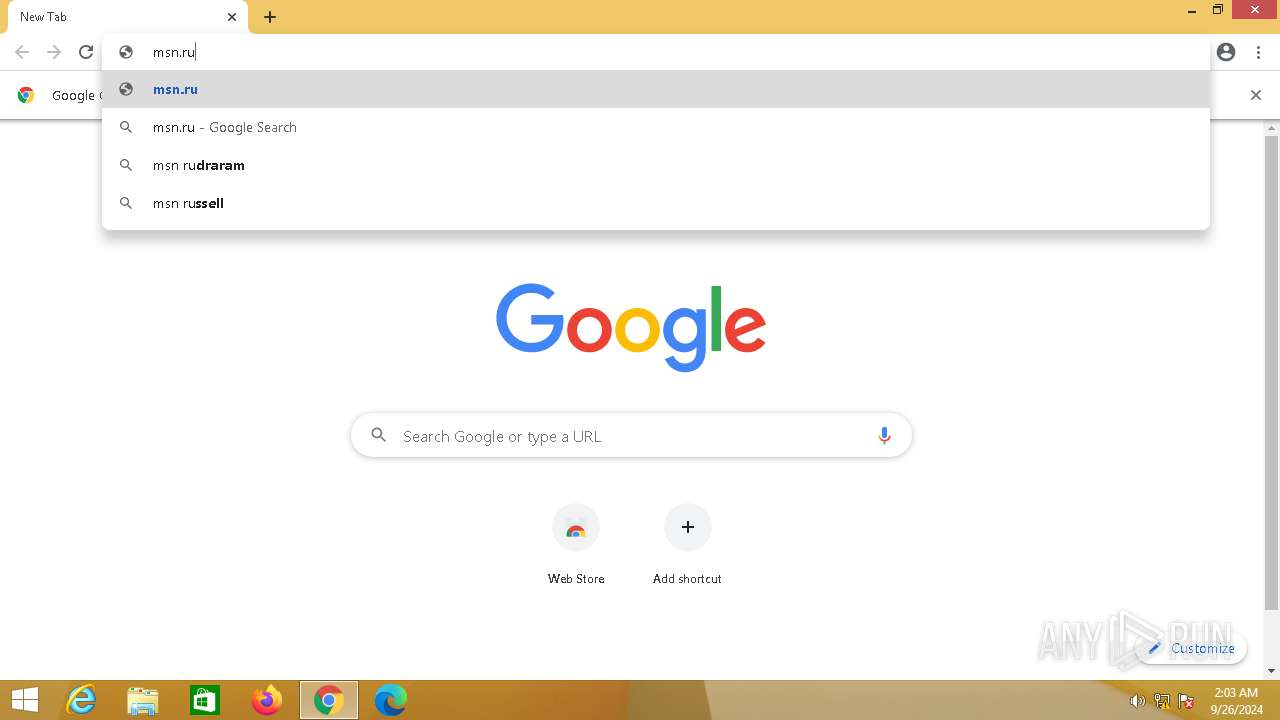
google.com |
| whitelisted |
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
ardownload3.adobe.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | A Network Trojan was detected | ET HUNTING Possible Obfuscator io JavaScript Obfuscation |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] JavaScript Obfuscation (ParseInt) |
400 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
400 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
— | — | Generic Protocol Command Decode | SURICATA HTTP request buffer too long |
400 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
400 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (aadzone) |
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc error: stale plugins cache: modified C:\Program Files\VideoLAN\VLC\plugins\access\libaccess_concat_plugin.dll
|