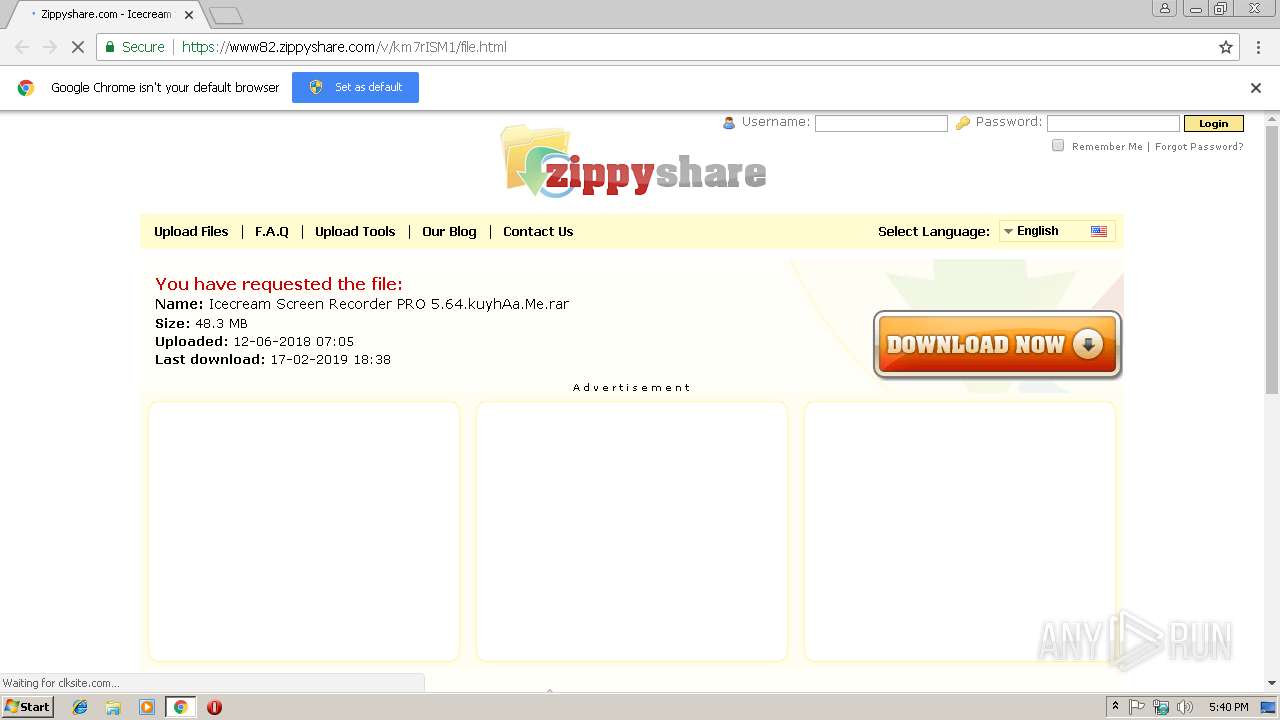
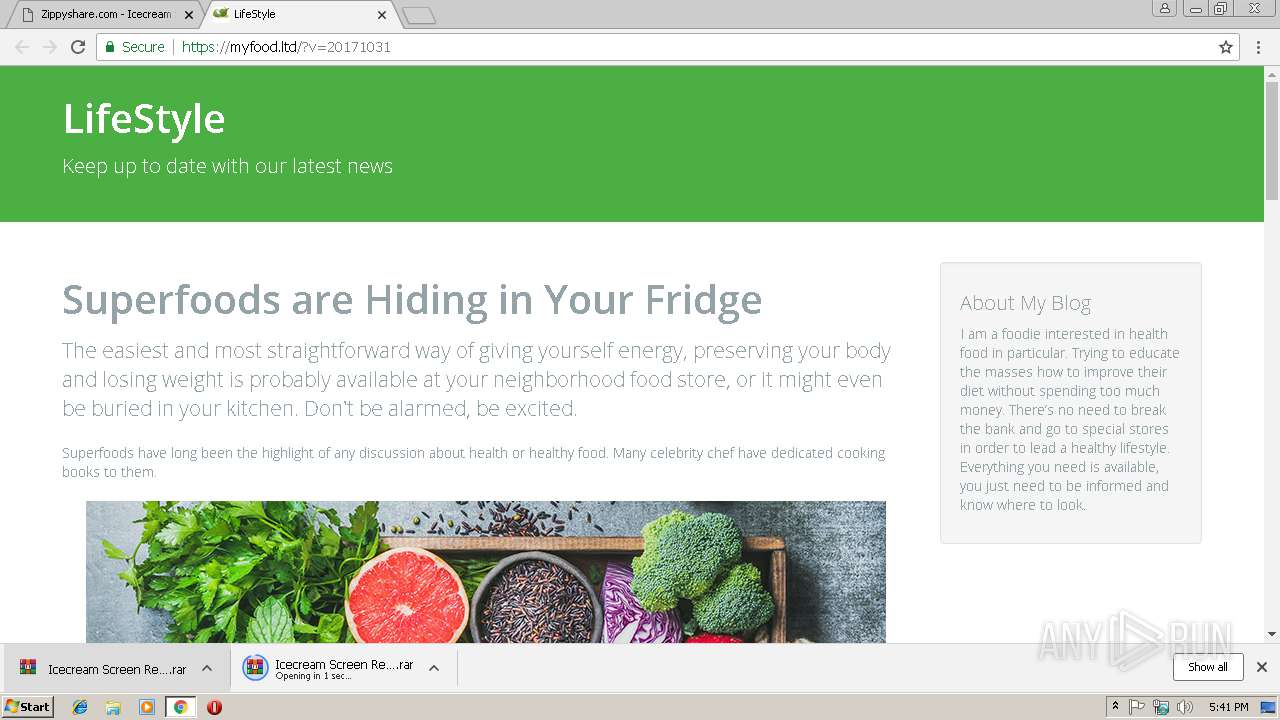
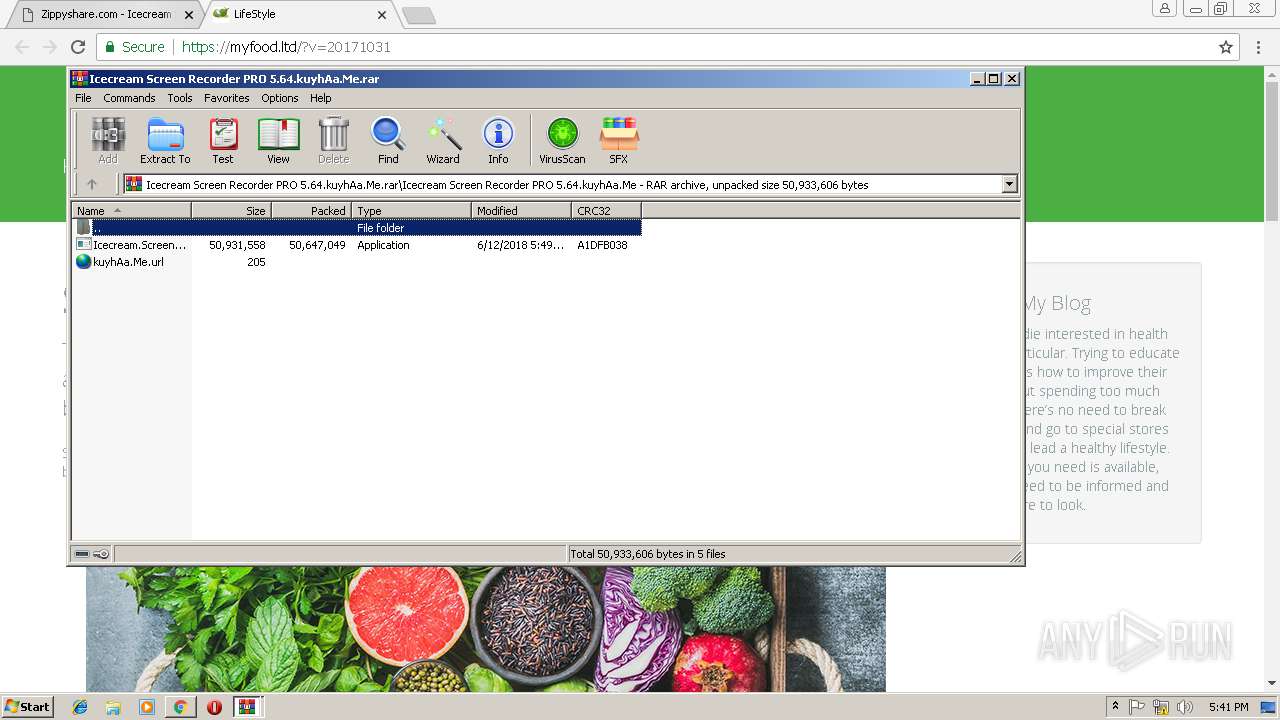
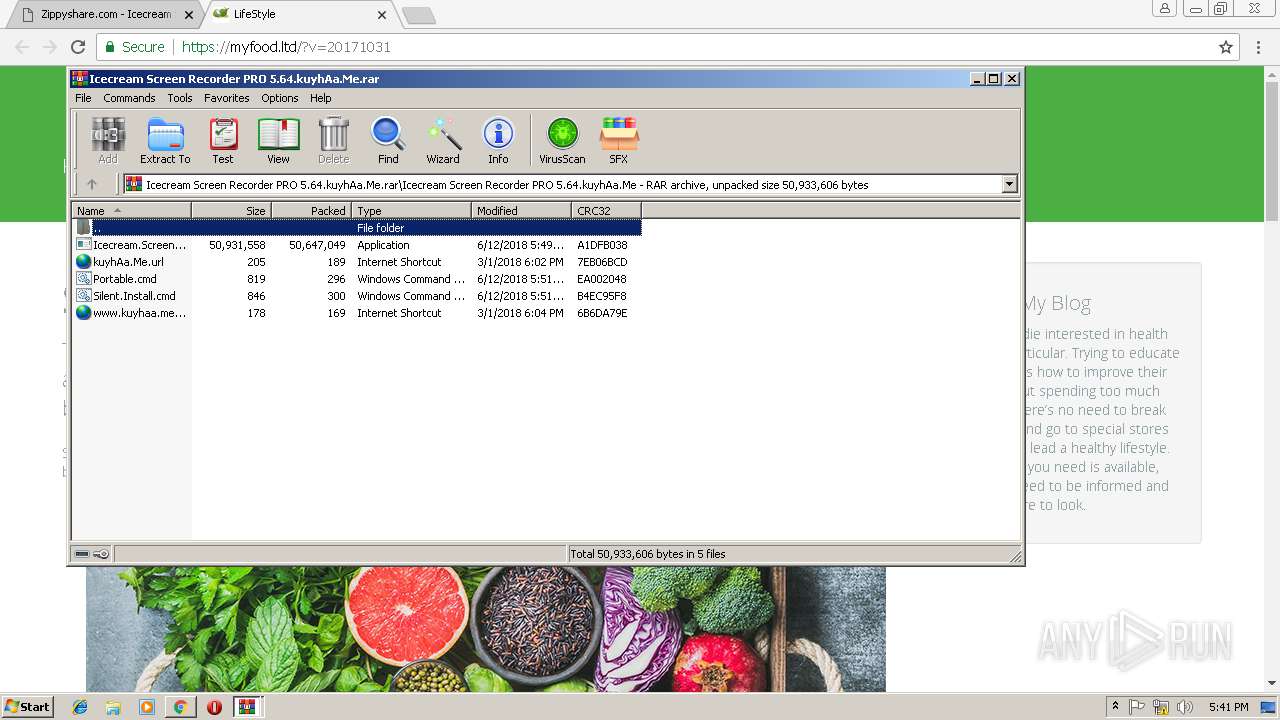
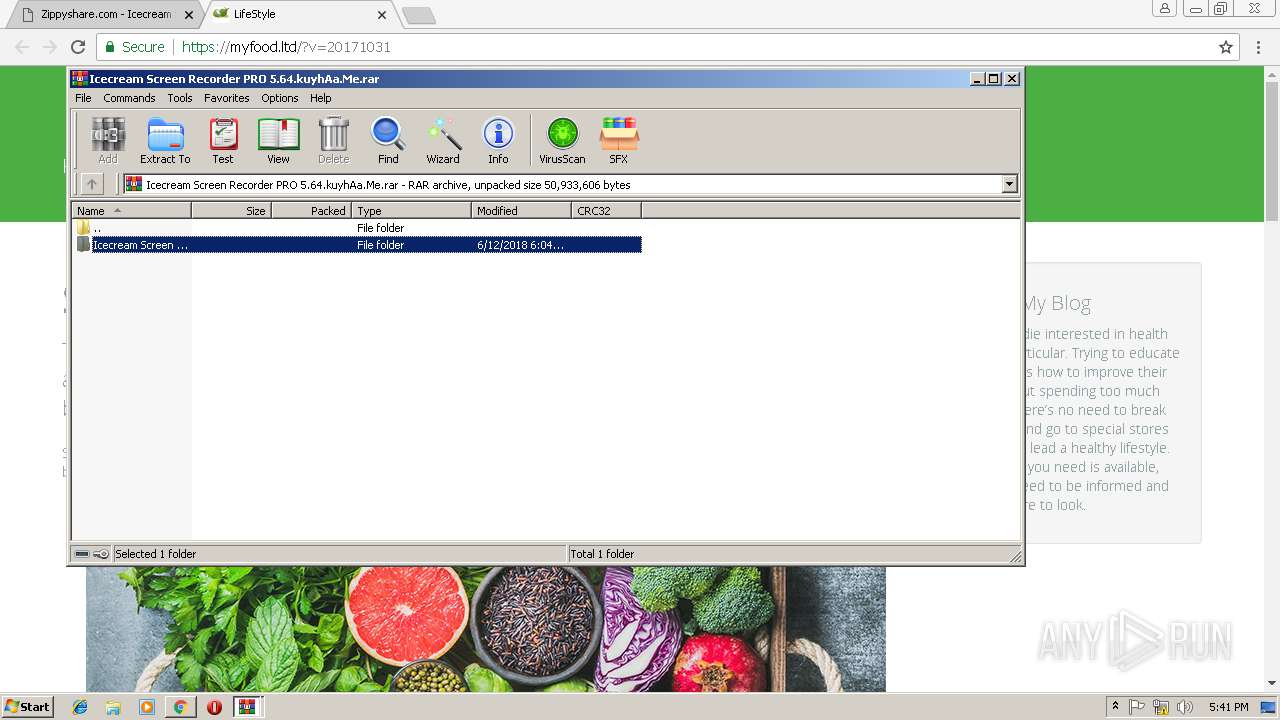
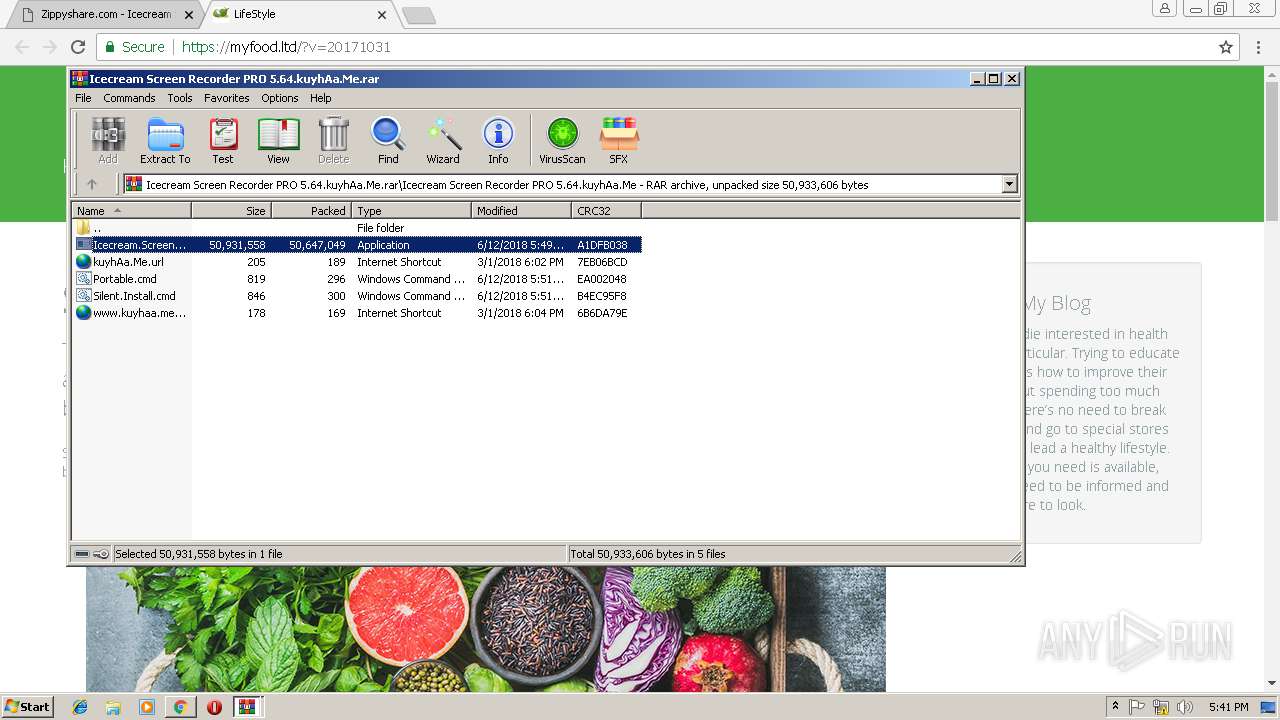
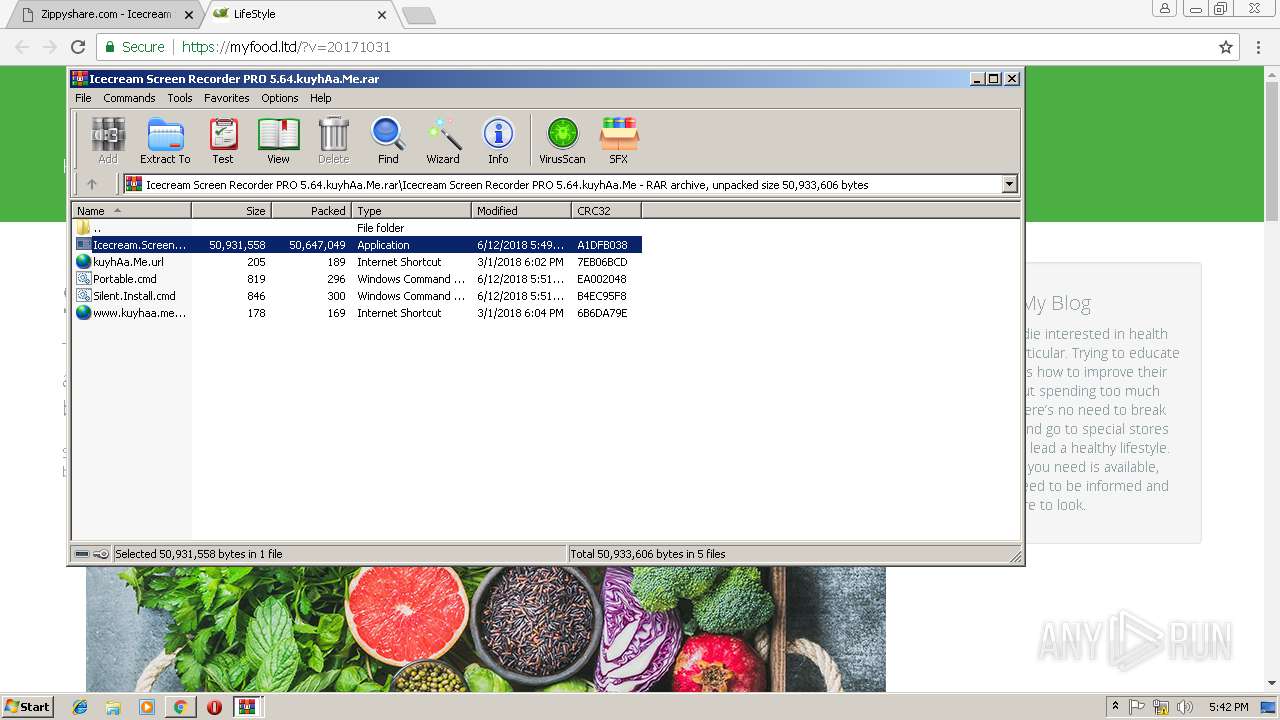
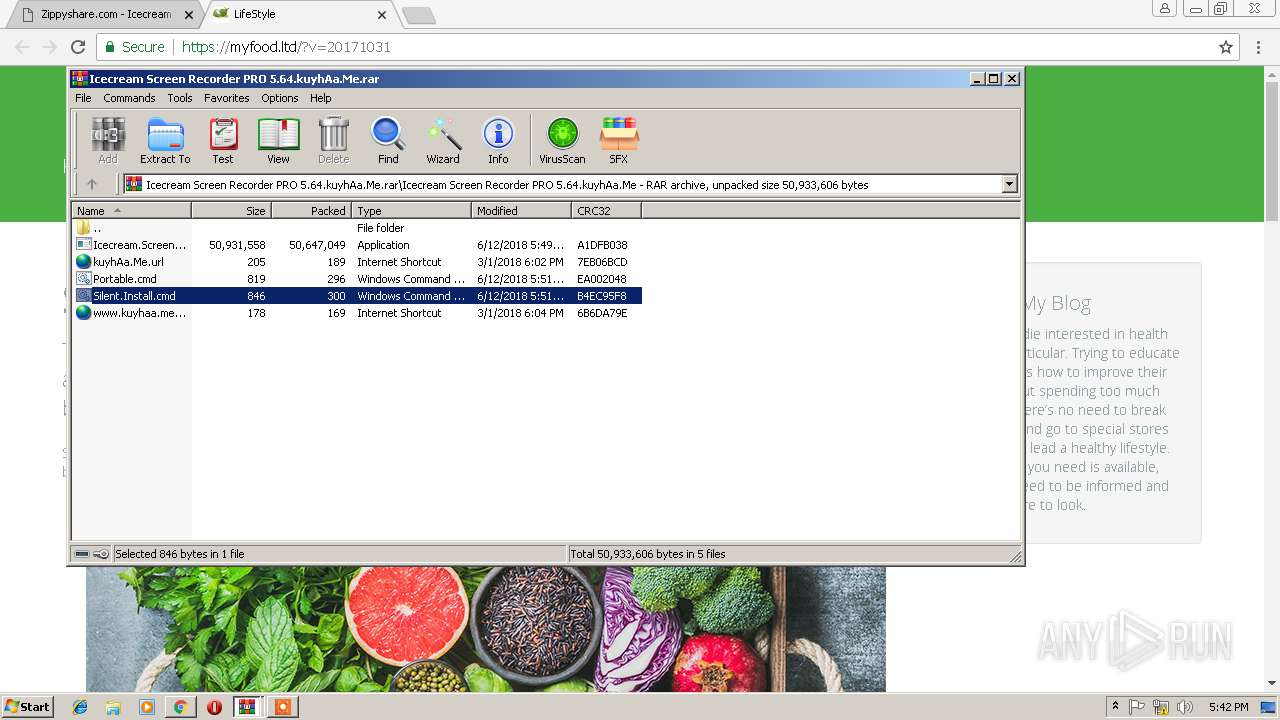
| URL: | https://www82.zippyshare.com/d/km7rISM1/857378/Icecream%20Screen%20Recorder%20PRO%205.64.kuyhAa.Me.rar |
| Full analysis: | https://app.any.run/tasks/e705ab1e-fc33-4e35-afd6-a530f3a9c075 |
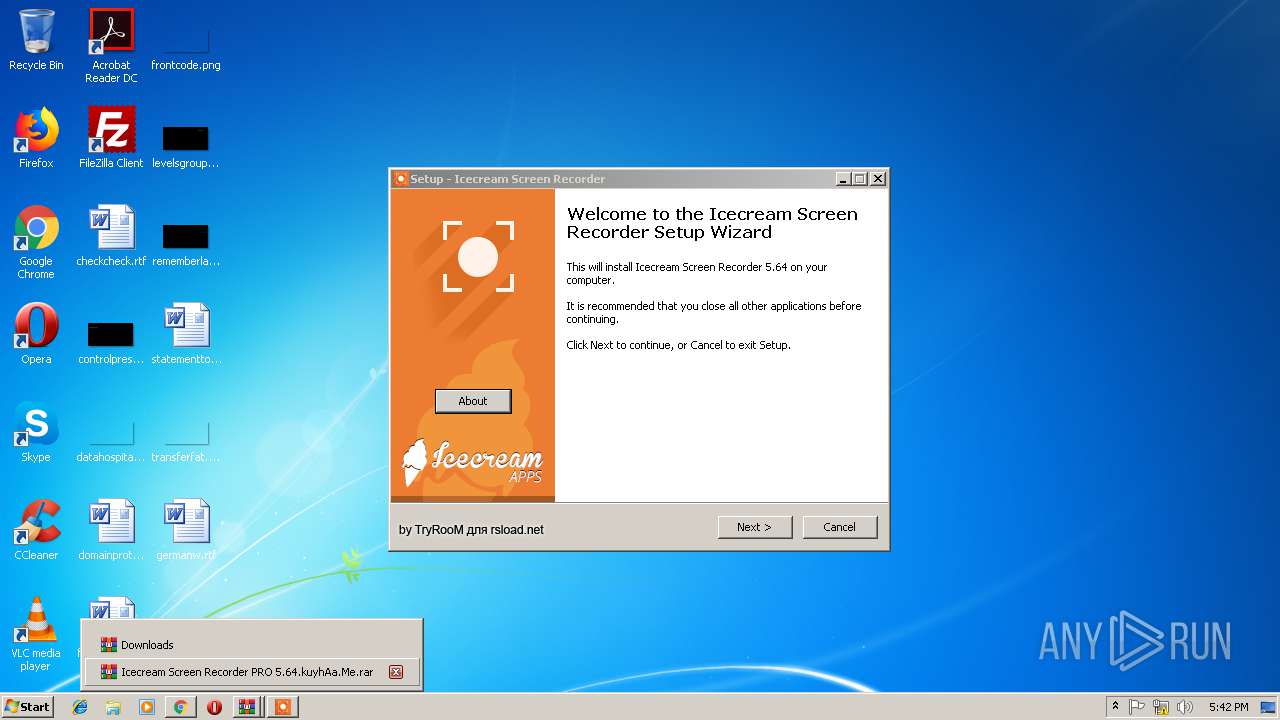
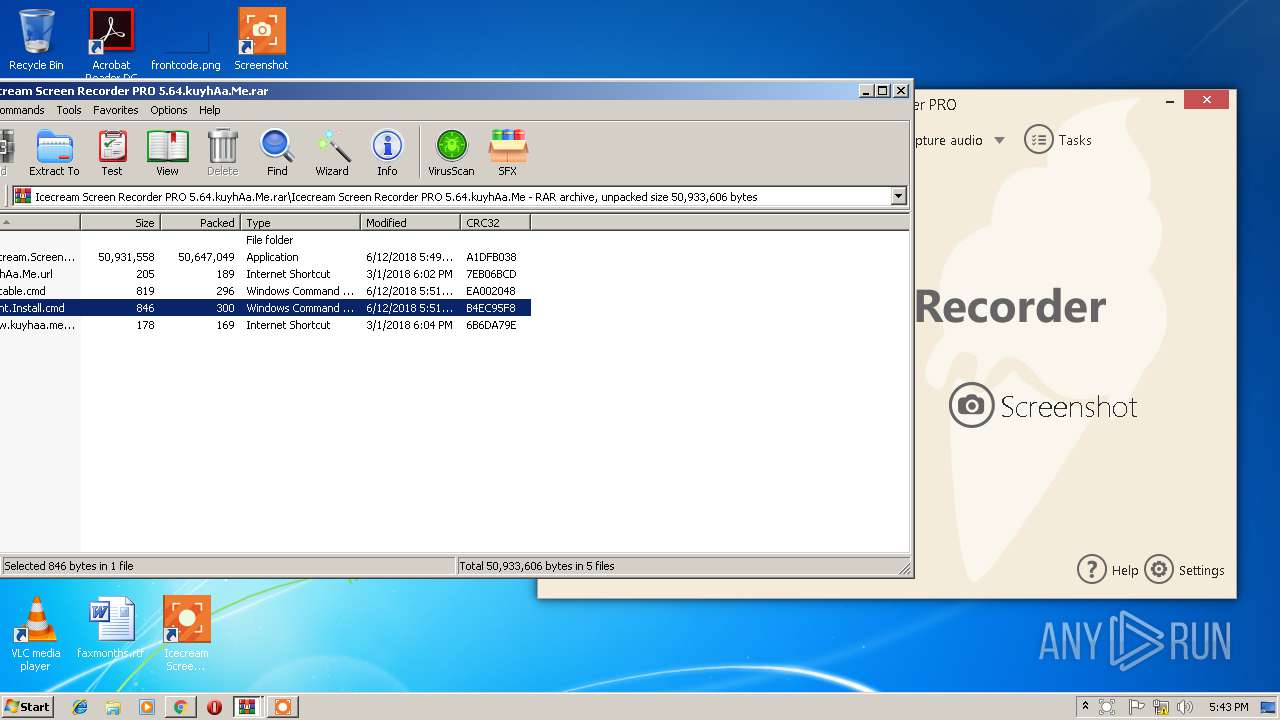
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2019, 17:40:33 |
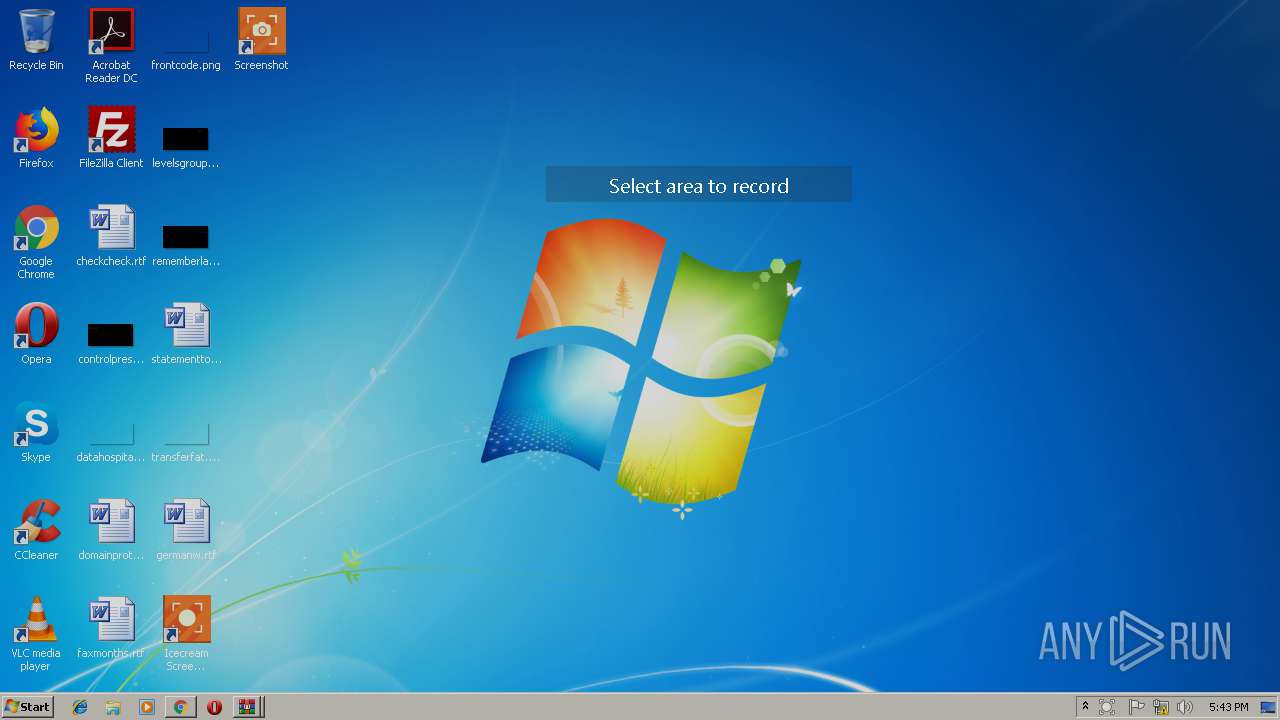
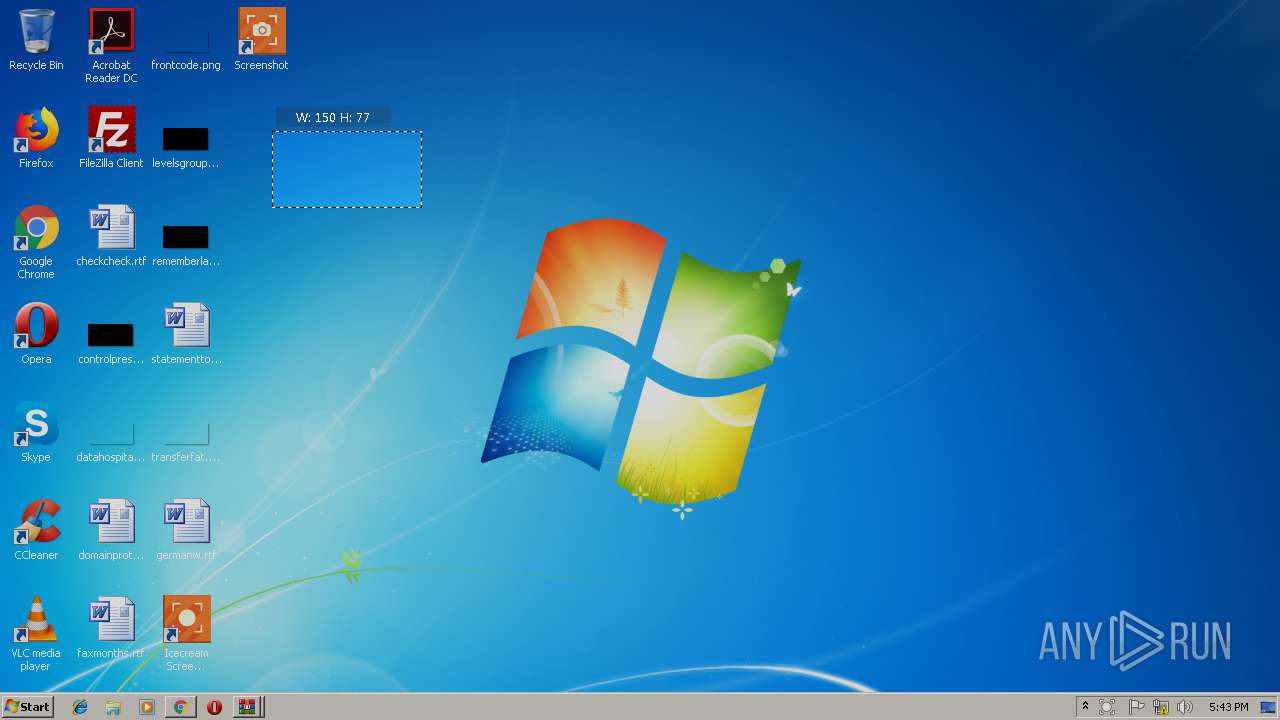
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 910DB4B4FE8574E9E1701630AE0C1837 |
| SHA1: | 4ED835372F71A20D48699E0BB1888A85FBA4821A |
| SHA256: | A15932A57984E5CD0D196A14DF687676EC6B93FC138E4A059DB5A8C5E9260A8E |
| SSDEEP: | 3:N8DSdIZGKxKnkX0H3KsXyAAui2kETfuUXn:2OdEGNnrah+zf5 |
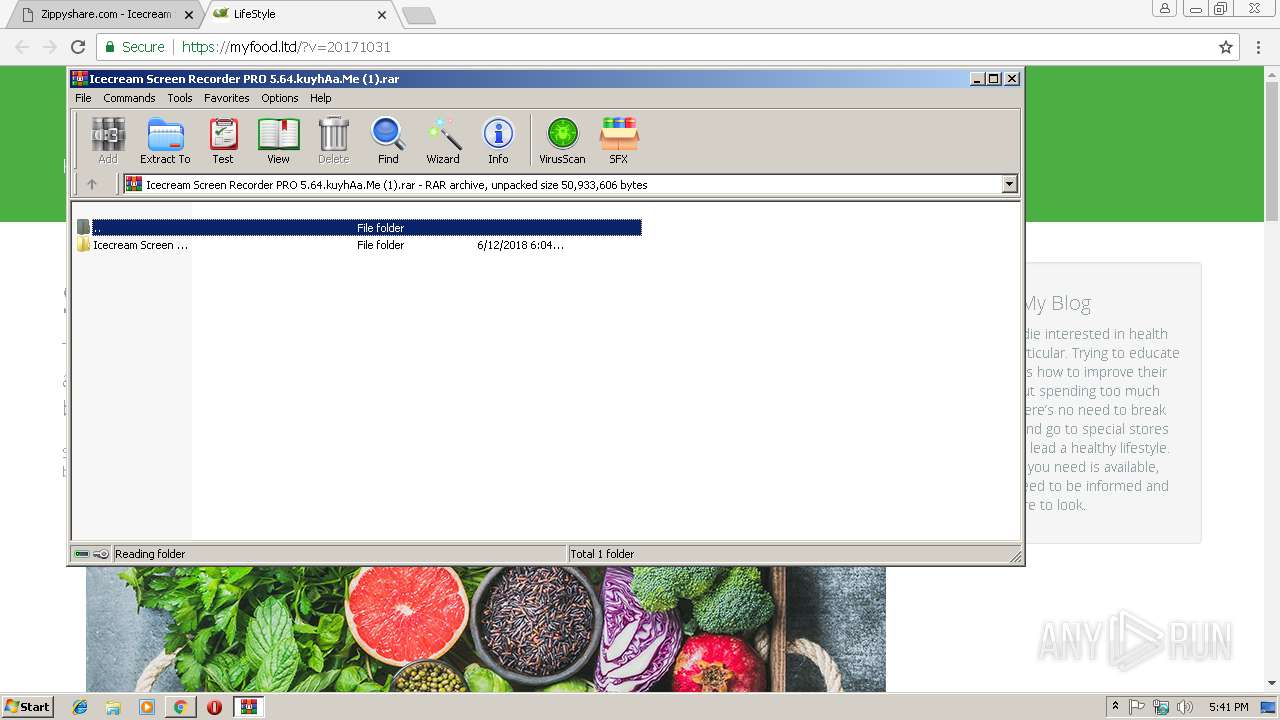
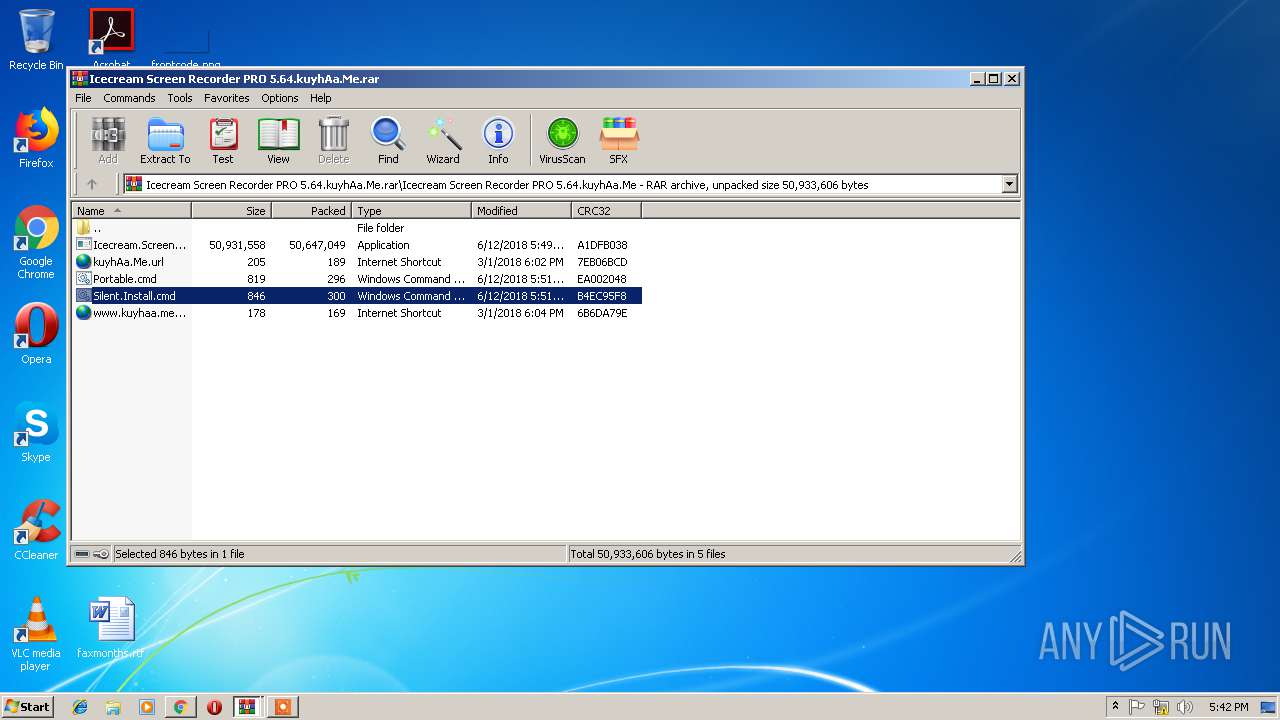
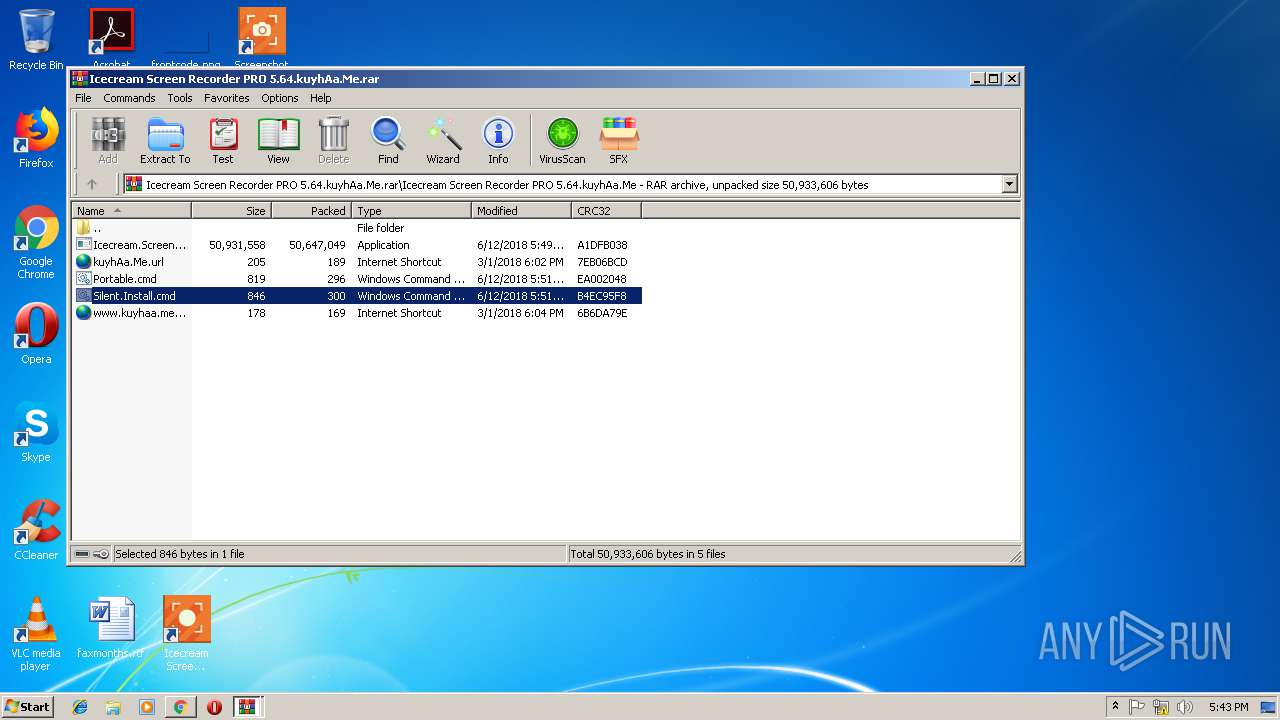
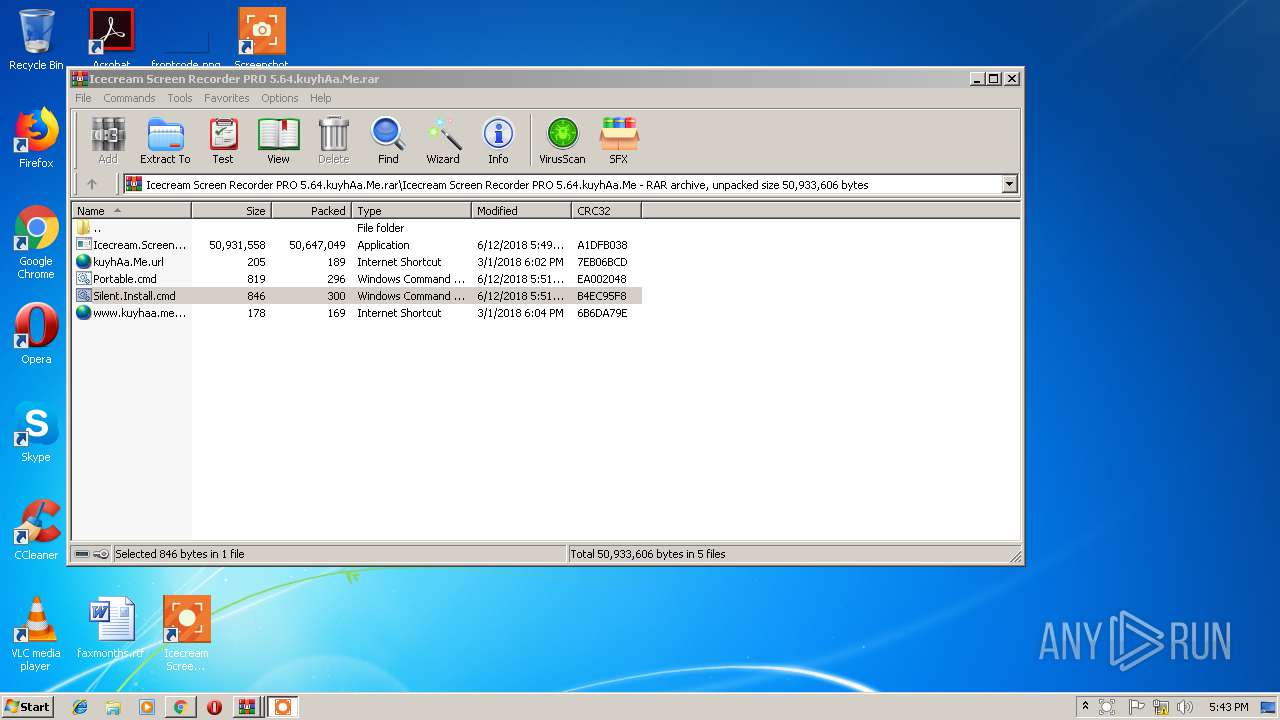
MALICIOUS
Loads dropped or rewritten executable
- recorder.exe (PID: 2980)
- ffmpeg.exe (PID: 336)
Application was dropped or rewritten from another process
- recorder.exe (PID: 2980)
- ffmpeg.exe (PID: 336)
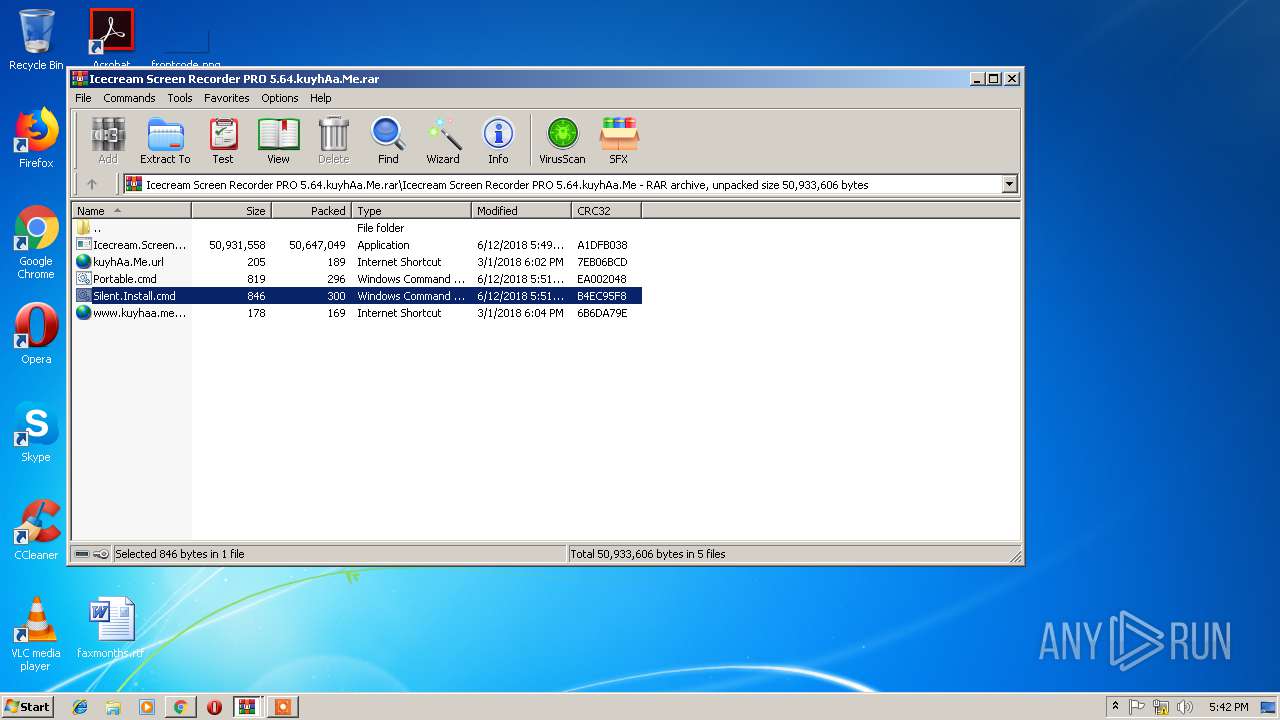
SUSPICIOUS
Executable content was dropped or overwritten
- Icecream.Screen.Recorder.5.64.exe (PID: 4060)
- Icecream.Screen.Recorder.5.64.tmp (PID: 1156)
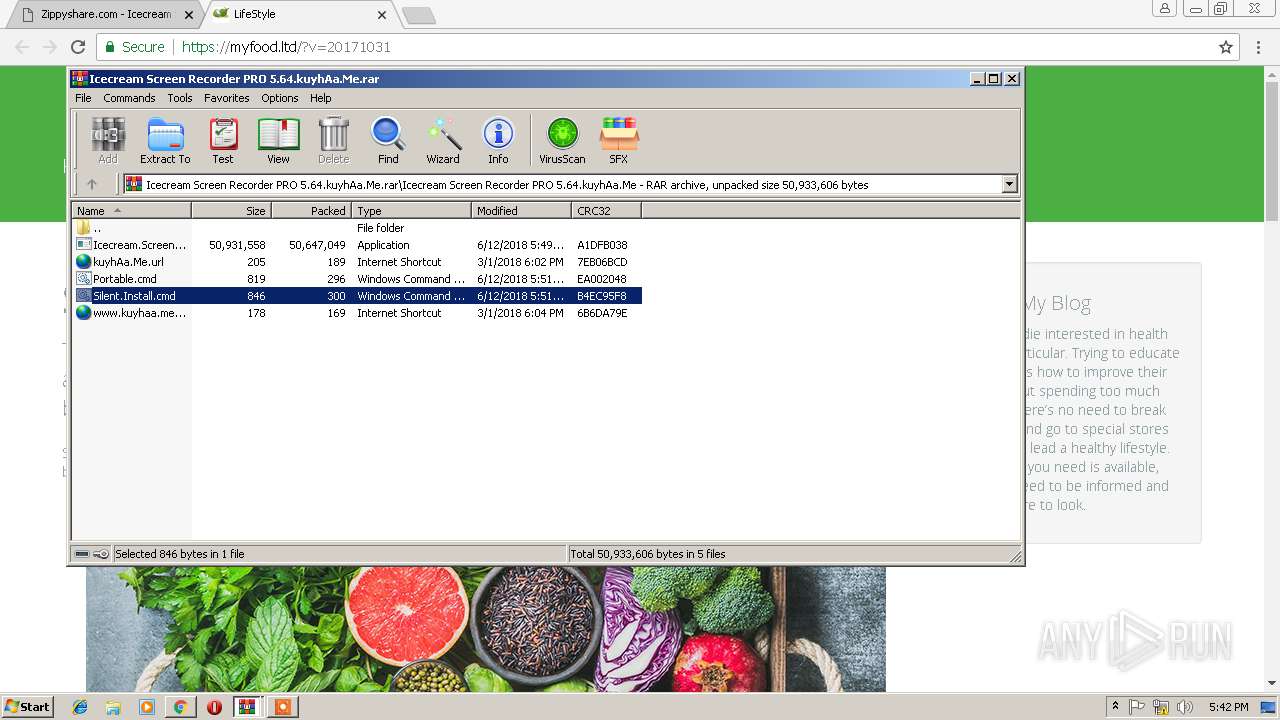
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3960)
Reads the machine GUID from the registry
- recorder.exe (PID: 2980)
INFO
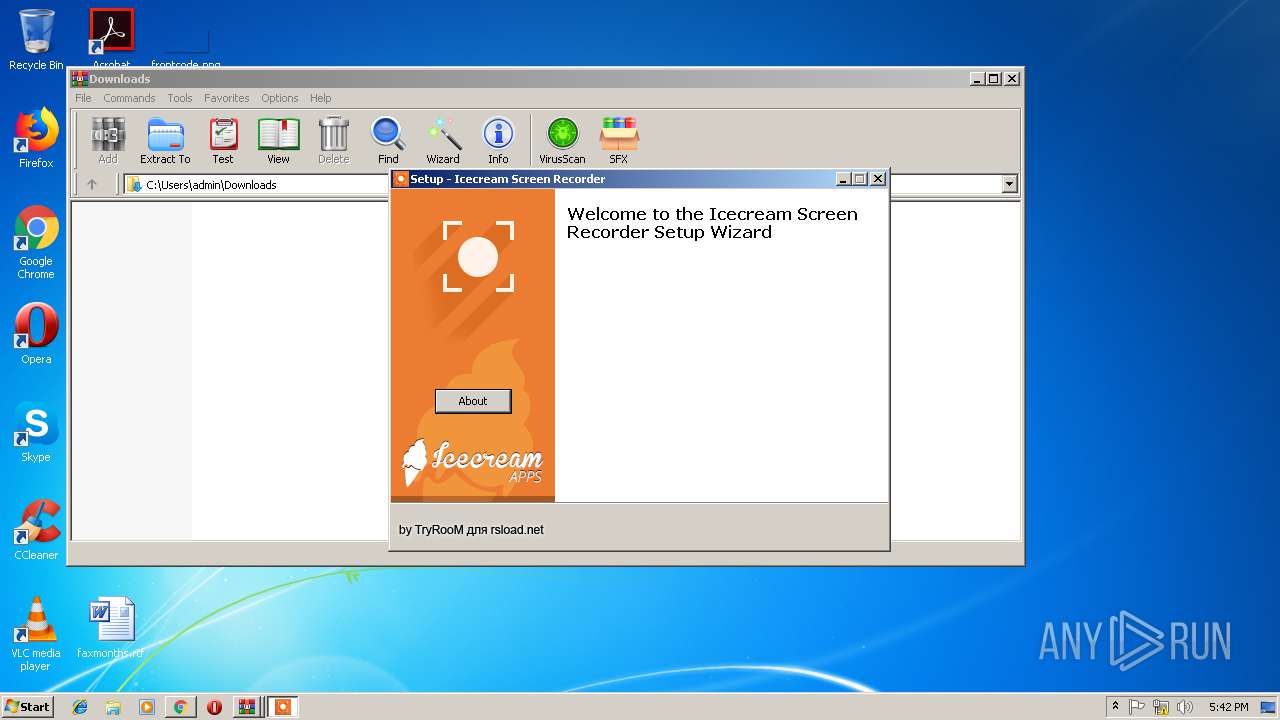
Application launched itself
- chrome.exe (PID: 2752)
Reads Internet Cache Settings
- chrome.exe (PID: 2752)
Reads settings of System Certificates
- chrome.exe (PID: 2752)
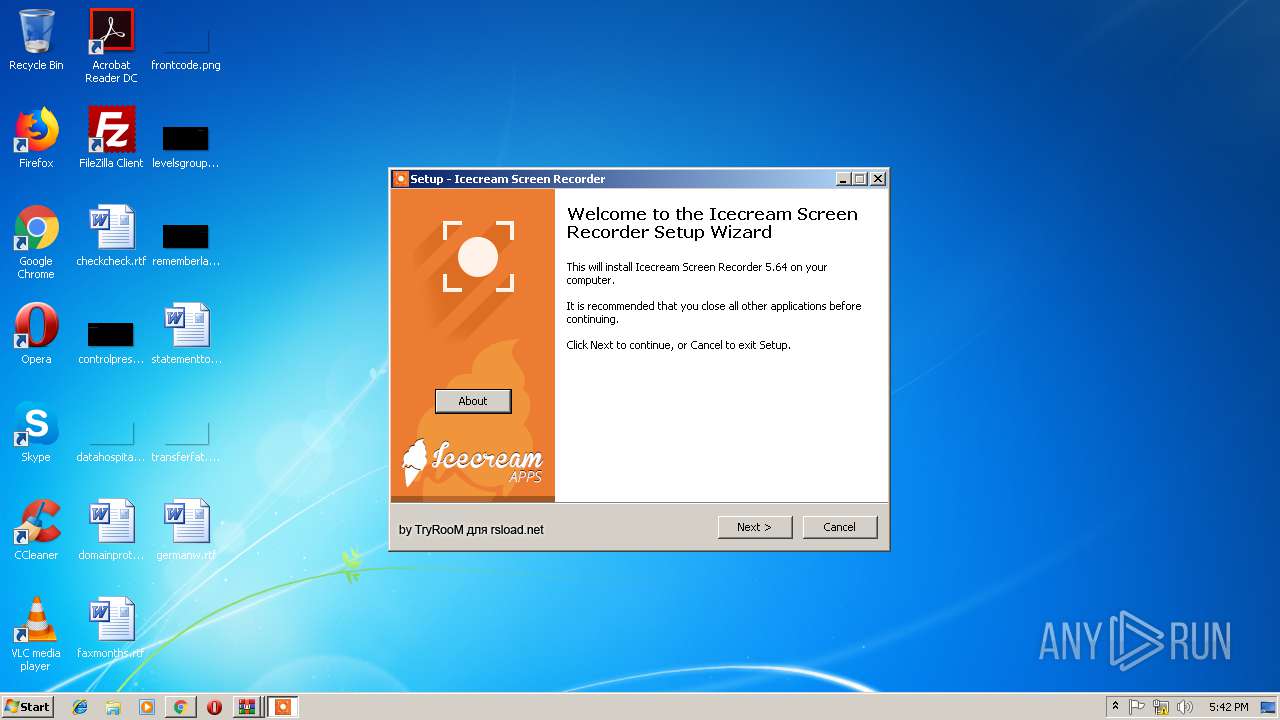
Application was dropped or rewritten from another process
- Icecream.Screen.Recorder.5.64.tmp (PID: 1156)
Loads dropped or rewritten executable
- Icecream.Screen.Recorder.5.64.tmp (PID: 1156)
Dropped object may contain Bitcoin addresses
- Icecream.Screen.Recorder.5.64.tmp (PID: 1156)
Creates a software uninstall entry
- Icecream.Screen.Recorder.5.64.tmp (PID: 1156)
Creates files in the program directory
- Icecream.Screen.Recorder.5.64.tmp (PID: 1156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
22
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
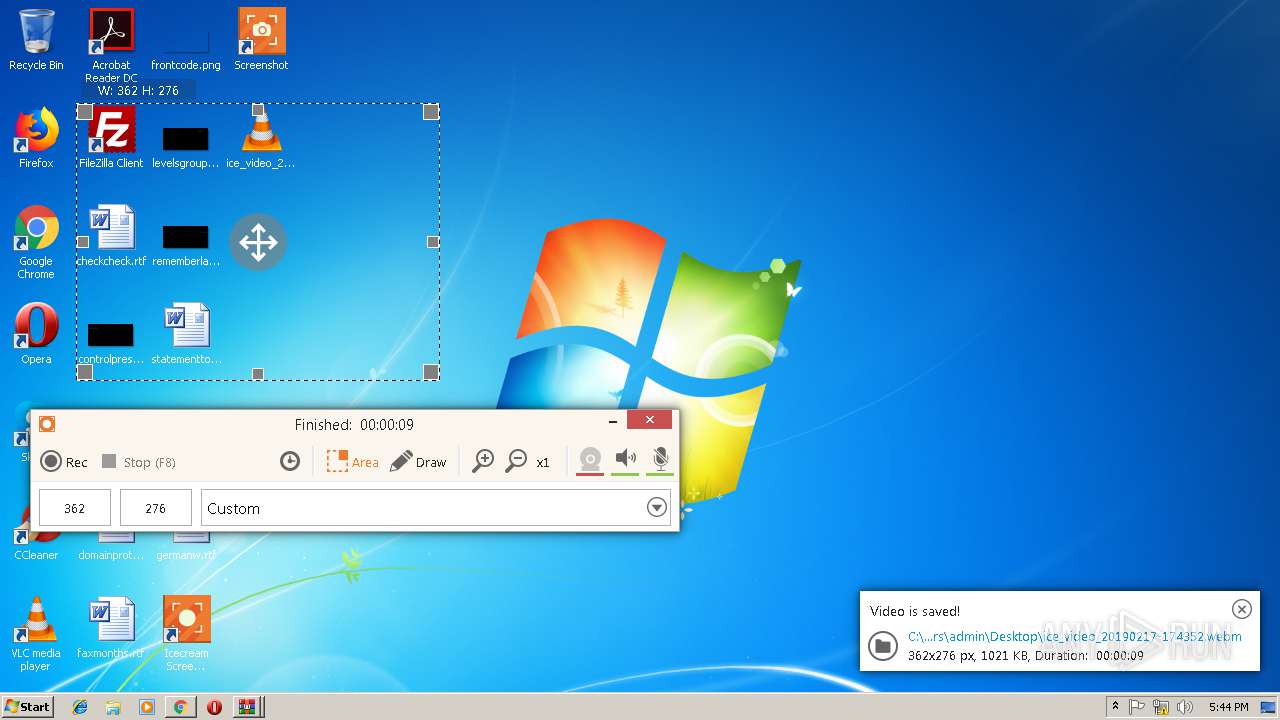
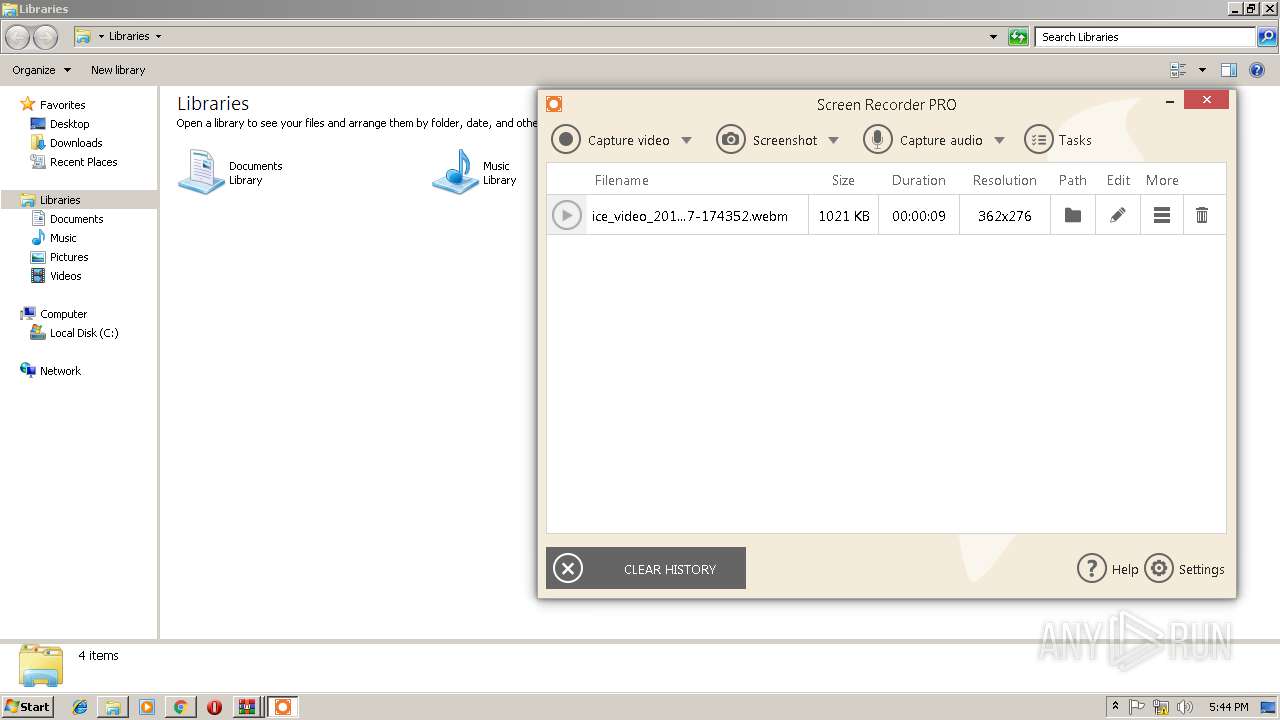
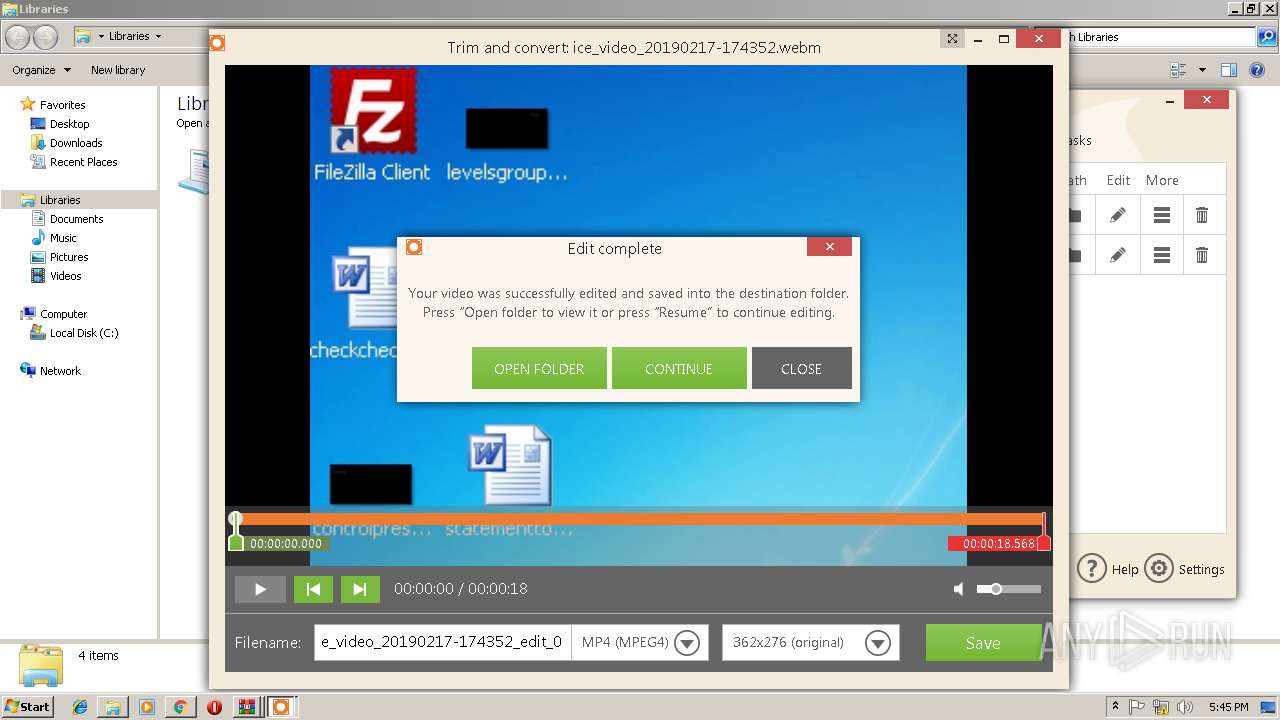
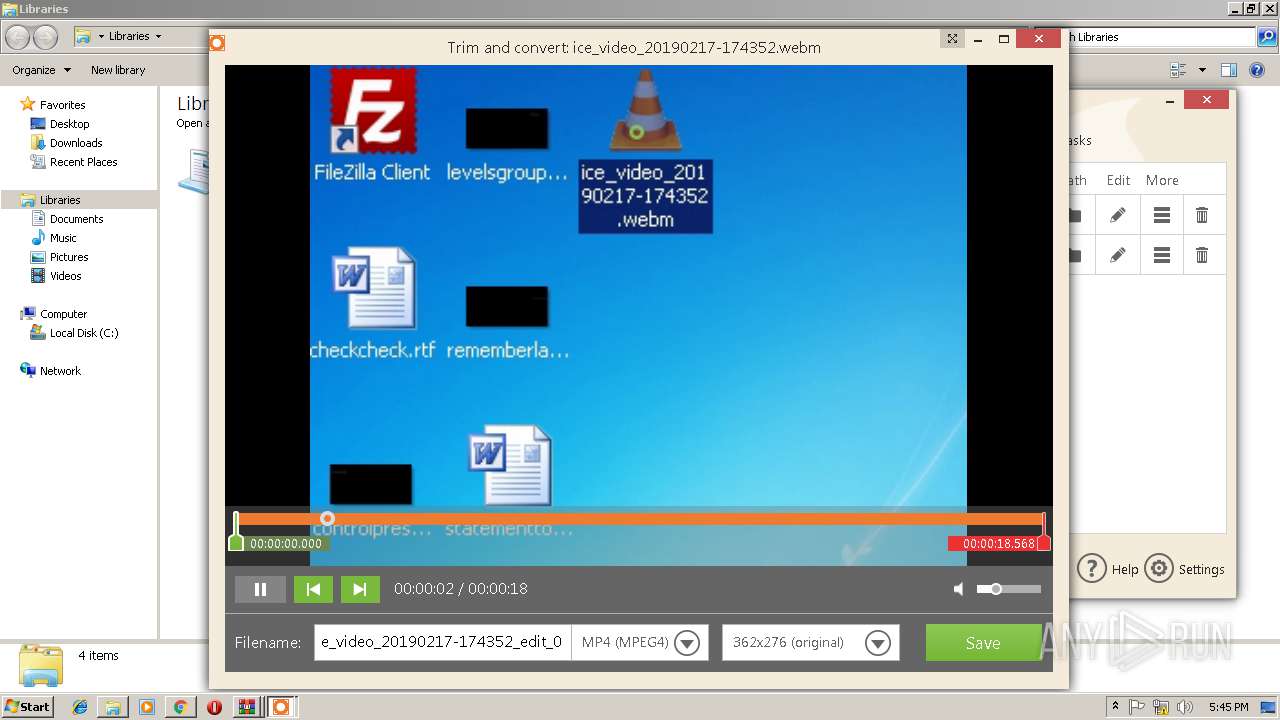
| 336 | ffmpeg.exe -y -i C:\Users\admin\Desktop\ice_video_20190217-174352.webm -ss 00:00:00.000 -to 00:00:18.568 -vcodec mpeg4 -b:v 1126675 -acodec mp3 C:\Users\admin\Desktop\ice_video_20190217-174352_edit_0.mp4 | C:\Program Files\Icecream Screen Recorder\ffmpeg.exe | — | recorder.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
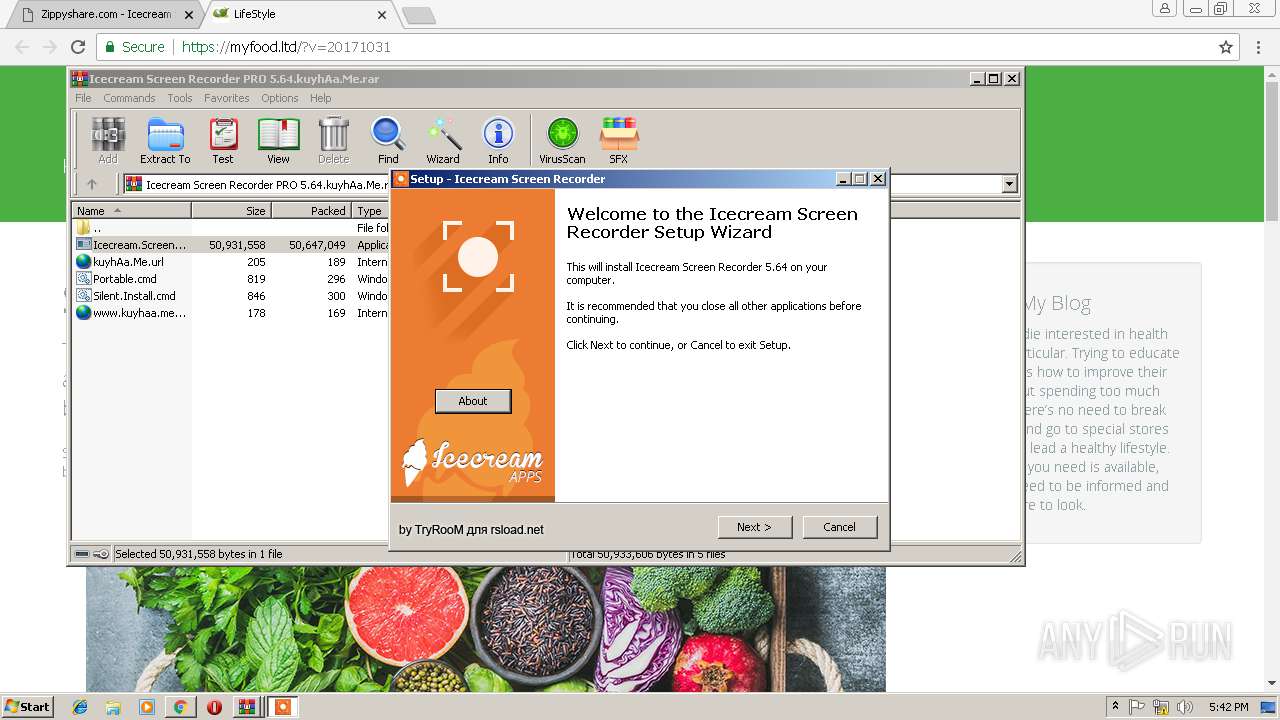
| 1156 | "C:\Users\admin\AppData\Local\Temp\is-NI102.tmp\Icecream.Screen.Recorder.5.64.tmp" /SL5="$60144,50588639,419840,C:\Users\admin\AppData\Local\Temp\Rar$EXa3960.32424\Icecream Screen Recorder PRO 5.64.kuyhAa.Me\Icecream.Screen.Recorder.5.64.exe" | C:\Users\admin\AppData\Local\Temp\is-NI102.tmp\Icecream.Screen.Recorder.5.64.tmp | Icecream.Screen.Recorder.5.64.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1520 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3960.33081\Silent.Install.cmd" " | C:\Windows\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1664 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1812 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3960.36050\Silent.Install.cmd" " | C:\Windows\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=912,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=46CD9AF4069A2FFD158F35DDEDC6AB6C --mojo-platform-channel-handle=3680 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3960.32424\Icecream Screen Recorder PRO 5.64.kuyhAa.Me\Icecream.Screen.Recorder.5.64.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3960.32424\Icecream Screen Recorder PRO 5.64.kuyhAa.Me\Icecream.Screen.Recorder.5.64.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Icecream Integrity Level: MEDIUM Description: Icecream Screen Recorder 5.64 Exit code: 3221226540 Version: 5.64 Modules
| |||||||||||||||
| 2352 | mode con:cols=110 lines=15 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
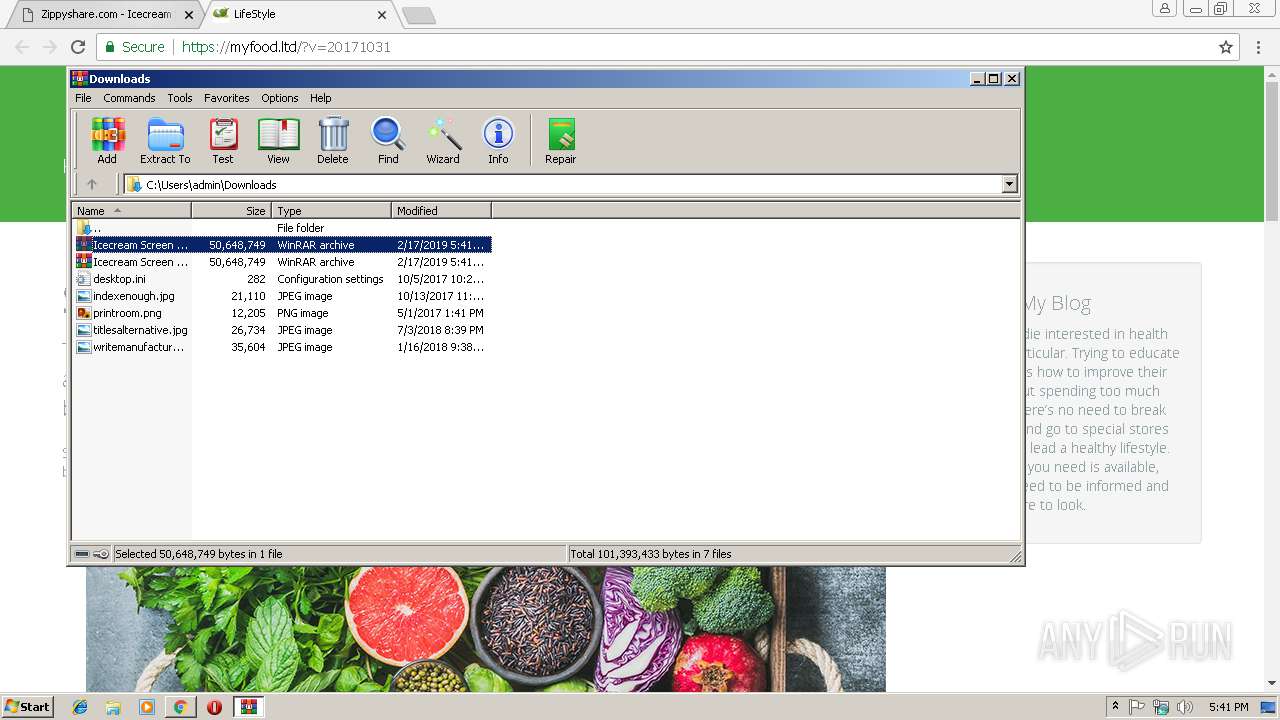
| 2628 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Icecream Screen Recorder PRO 5.64.kuyhAa.Me (1).rar" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=912,6782429653125926169,8958812780097232084,131072 --enable-features=PasswordImport --service-pipe-token=92805FB8D31BABF909838F305AE27533 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=92805FB8D31BABF909838F305AE27533 --renderer-client-id=4 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 148
Read events
2 004
Write events
134
Delete events
10
Modification events
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2752-13194898848960375 |
Value: 259 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2752-13194898848960375 |
Value: 259 | |||
| (PID) Process: | (2752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
64
Suspicious files
63
Text files
242
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\303e44fd-469f-44df-8e76-0a6566c14902.tmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ac1eb862-ddd0-49e0-9304-efbdc90ae340.tmp | — | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF246bab.TMP | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
61
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | chrome.exe | GET | 200 | 2.16.186.89:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
2752 | chrome.exe | GET | 200 | 13.32.222.109:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2752 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | chrome.exe | 173.192.101.24:443 | p232207.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
2752 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 35.190.68.123:443 | www.maxonclick.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 51.15.155.124:443 | makemyvids.com | Online S.a.s. | FR | unknown |
2752 | chrome.exe | 13.32.222.115:443 | d10lumateci472.cloudfront.net | Amazon.com, Inc. | US | malicious |
2752 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 46.166.139.215:443 | www82.zippyshare.com | NForce Entertainment B.V. | NL | unknown |
2752 | chrome.exe | 198.134.112.244:443 | gz06x5tqlj.com | Webair Internet Development Company Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www82.zippyshare.com |
| unknown |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
p232207.clksite.com |
| whitelisted |
www.maxonclick.com |
| whitelisted |
www.google.com |
| malicious |
d10lumateci472.cloudfront.net |
| whitelisted |
makemyvids.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
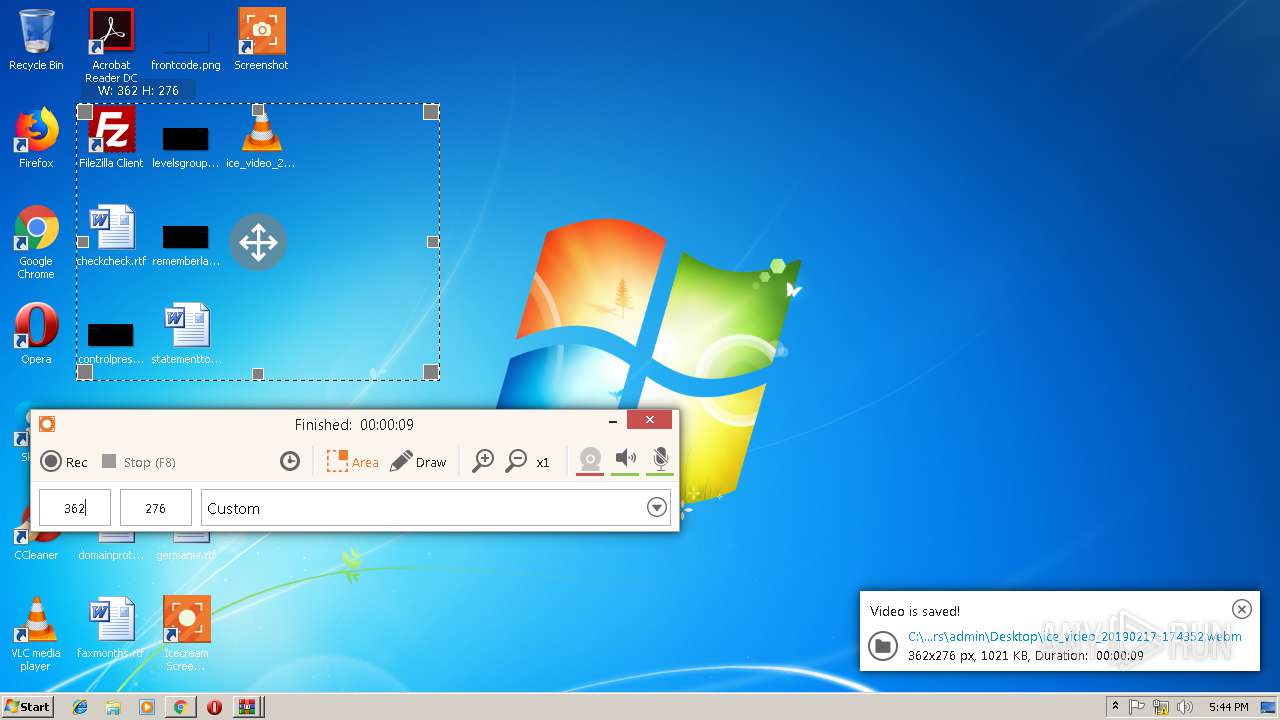
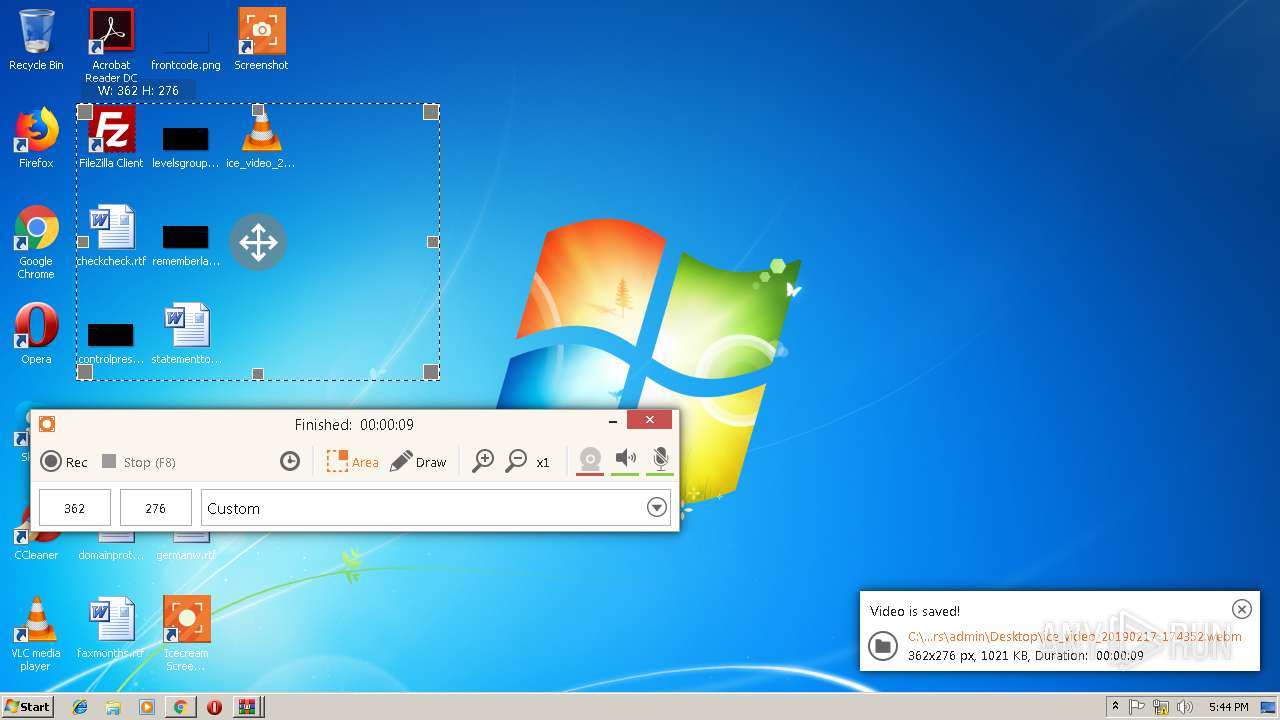
recorder.exe | [5.6.4][Windows 7][32bit][17:43:11] DEBUG: Get serial number for win v2. Root path:'C:/Users/admin/AppData/Local/Icecream/Icecream Screen Recorder' Drive path:'\\.\C:'
|
recorder.exe | [5.6.4][Windows 7][32bit][17:43:11] DEBUG: HDD OS ID V3:4d51303030302031202020202020202020202020
|
recorder.exe | Load translation: "C:/Program Files/Icecream Screen Recorder/translations/lang_en.qm"
|
recorder.exe | class QString __thiscall LicenseService::licenseFile(void) const Full path: "C:\\Users\\admin\\AppData\\Local\\Icecream\\Icecream Screen Recorder\\\u0000icense.lic"
|
recorder.exe | [5.6.4][Windows 7][32bit][17:43:11] DEBUG: License file found [OK]
|
recorder.exe | class QString __thiscall LicenseService::licenseFile(void) const Full path: "C:\\Users\\admin\\AppData\\Local\\Icecream\\Icecream Screen Recorder\\\u0000icense.lic"
|
recorder.exe | [5.6.4][Windows 7][32bit][17:43:11] ERROR: Loading license file [FAILED]: C:\Users\admin\AppData\Local\Icecream\Icecream Screen Recorder\
|
recorder.exe | __thiscall CrashInstaller::CrashInstaller(void) [BEGIN]
|
recorder.exe | __thiscall CrashInstaller::CrashInstaller(void) [END]
|
recorder.exe | [5.6.4][Windows 7][32bit][17:43:11] DEBUG: History file:'C:\Users\admin\AppData\Local\Icecream\Icecream Screen Recorder\history.ini'
|