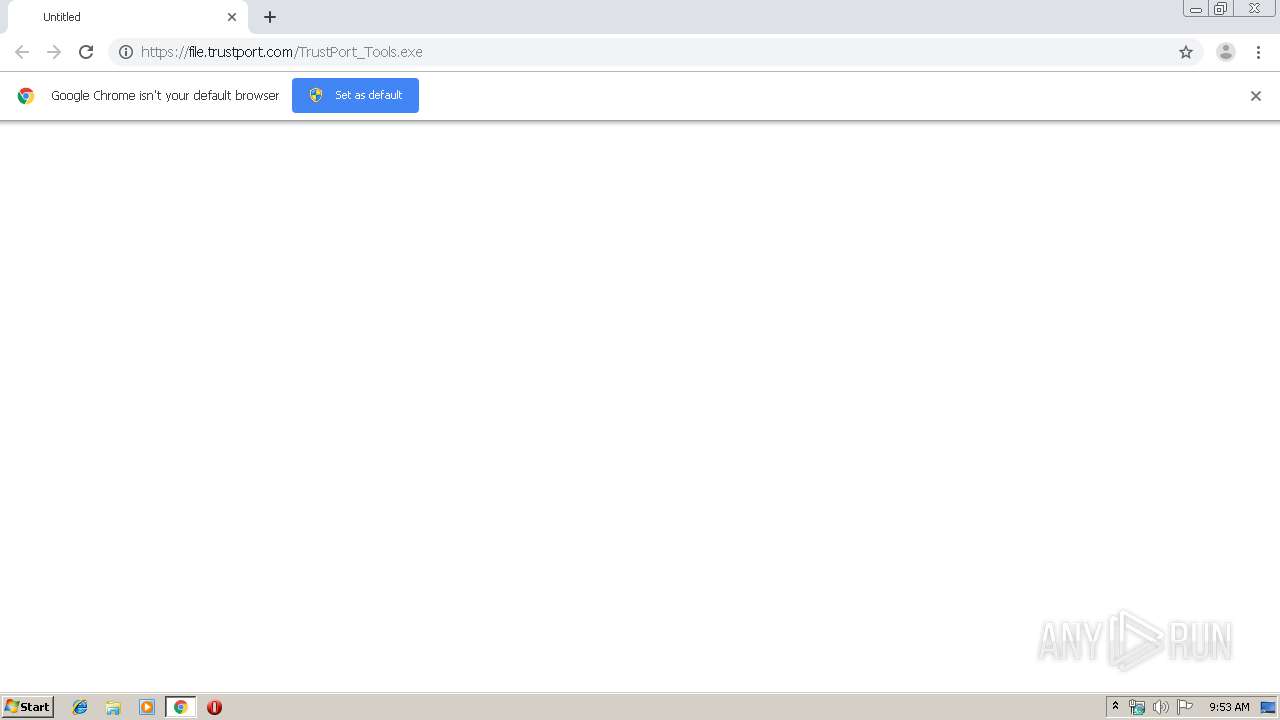
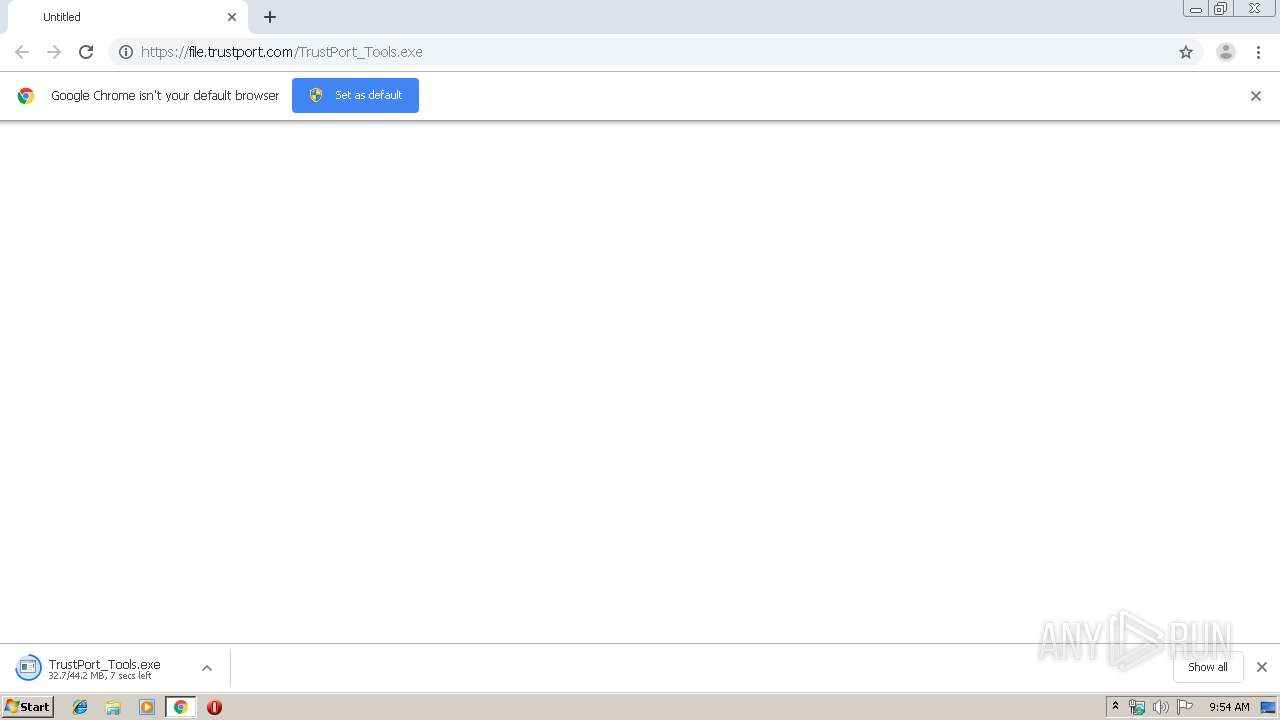
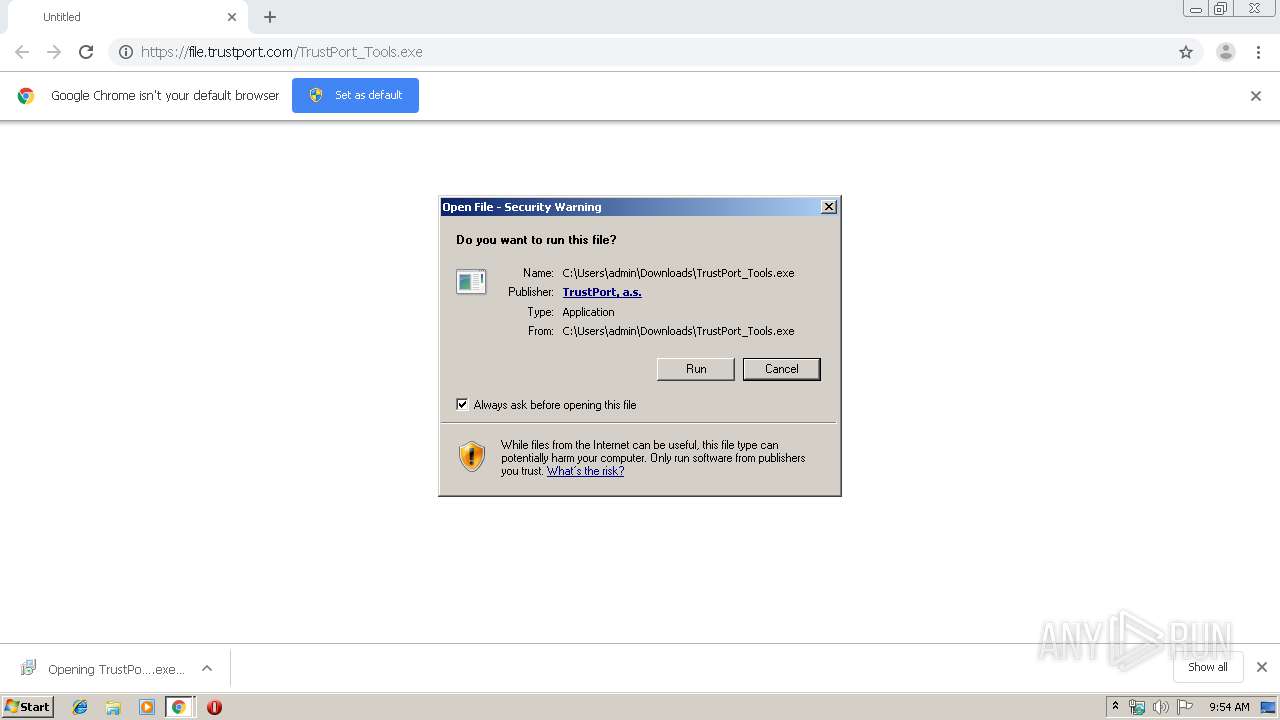
| URL: | https://file.trustport.com/TrustPort_Tools.exe |
| Full analysis: | https://app.any.run/tasks/8db379af-5acb-4369-a0dc-b8700982e21b |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 09:53:39 |
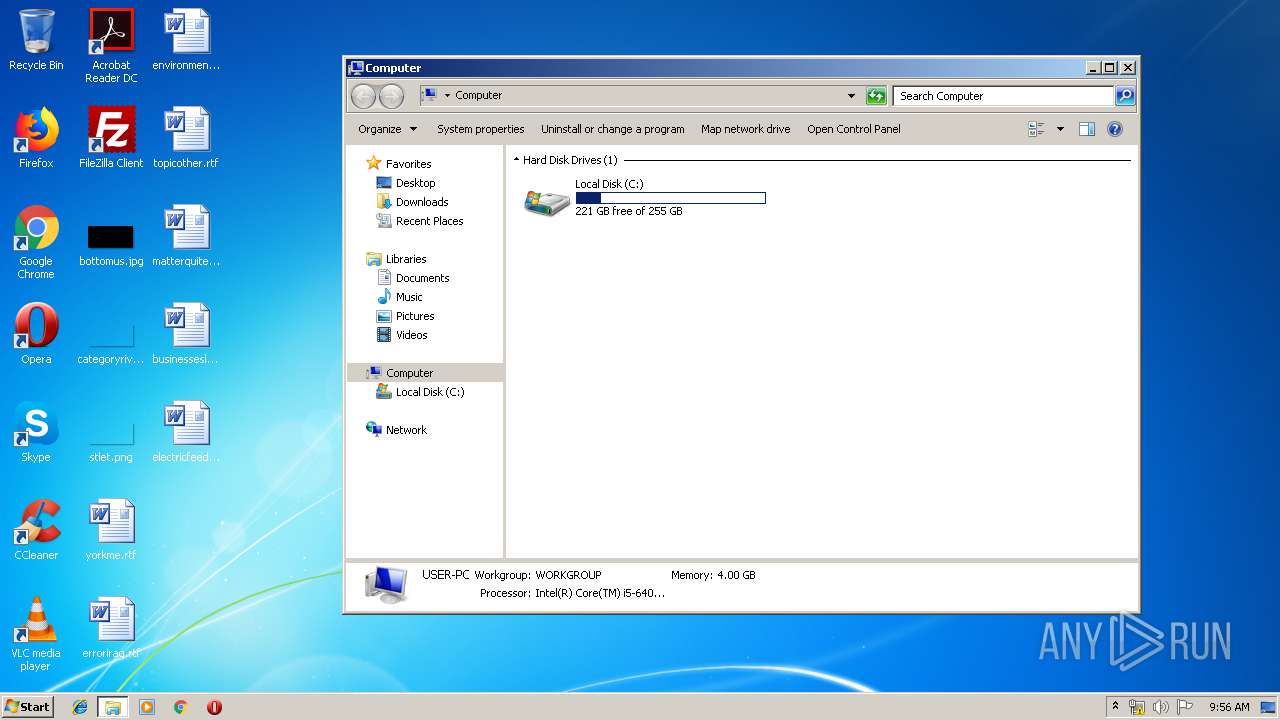
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B089A9465A4837DC9A6A8AD2677C71F9 |
| SHA1: | ABD862E7C9C71D45ECB457F74B3C106E8C450CDA |
| SHA256: | A147A43C4ABF69E4556F0929A90762399E35663CF0F38571F28A0CA62BF84E1F |
| SSDEEP: | 3:N82DxR1KB8JM4An:2GxTQ8JrAn |
MALICIOUS
Application was dropped or rewritten from another process
- TrustPort_Tools.exe (PID: 2836)
- TrustPort_Tools.exe (PID: 2760)
- tpsctrl.exe (PID: 2416)
- tpsctrl.exe (PID: 3356)
- tpsctrl.exe (PID: 3924)
- tpsctrl.exe (PID: 2580)
- tpmgma.exe (PID: 1152)
- tpsctrl.exe (PID: 776)
- tpmgma.exe (PID: 3084)
- tpmgma.exe (PID: 792)
- tpupdate.exe (PID: 2748)
- tpsctrl.exe (PID: 3040)
- tpsctrl.exe (PID: 688)
- tpsctrl.exe (PID: 3504)
- tpsctrl.exe (PID: 2396)
- tpsctrl.exe (PID: 1028)
- tpsctrl.exe (PID: 856)
- tpsctrl.exe (PID: 1608)
- tpsctrl.exe (PID: 2980)
- tpsctrl.exe (PID: 3140)
- tpsctrl.exe (PID: 2788)
- tpsctrl.exe (PID: 2744)
- tpsctrl.exe (PID: 1216)
- tpsctrl.exe (PID: 3008)
- tpsctrl.exe (PID: 4064)
- tpsctrl.exe (PID: 2708)
- tpsctrl.exe (PID: 2416)
- tpsctrl.exe (PID: 3172)
- tpsctrl.exe (PID: 2004)
- tpsctrl.exe (PID: 4032)
- tpsctrl.exe (PID: 2724)
- tpsctrl.exe (PID: 4044)
- tpsctrl.exe (PID: 3664)
- tpsctrl.exe (PID: 436)
- tpupdate.exe (PID: 3504)
- tpsctrl.exe (PID: 3228)
- tpsctrl.exe (PID: 4040)
- tpsctrl.exe (PID: 2668)
- tpmgma.exe (PID: 2924)
- tpmgma.exe (PID: 2740)
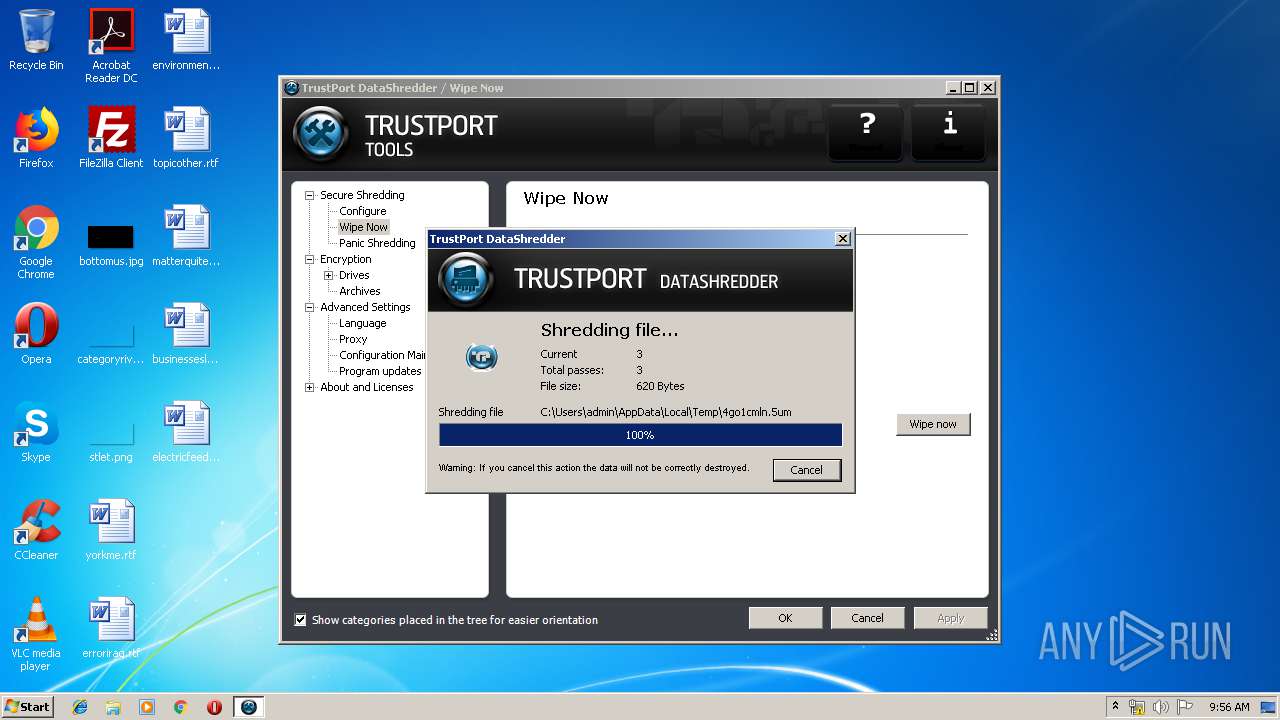
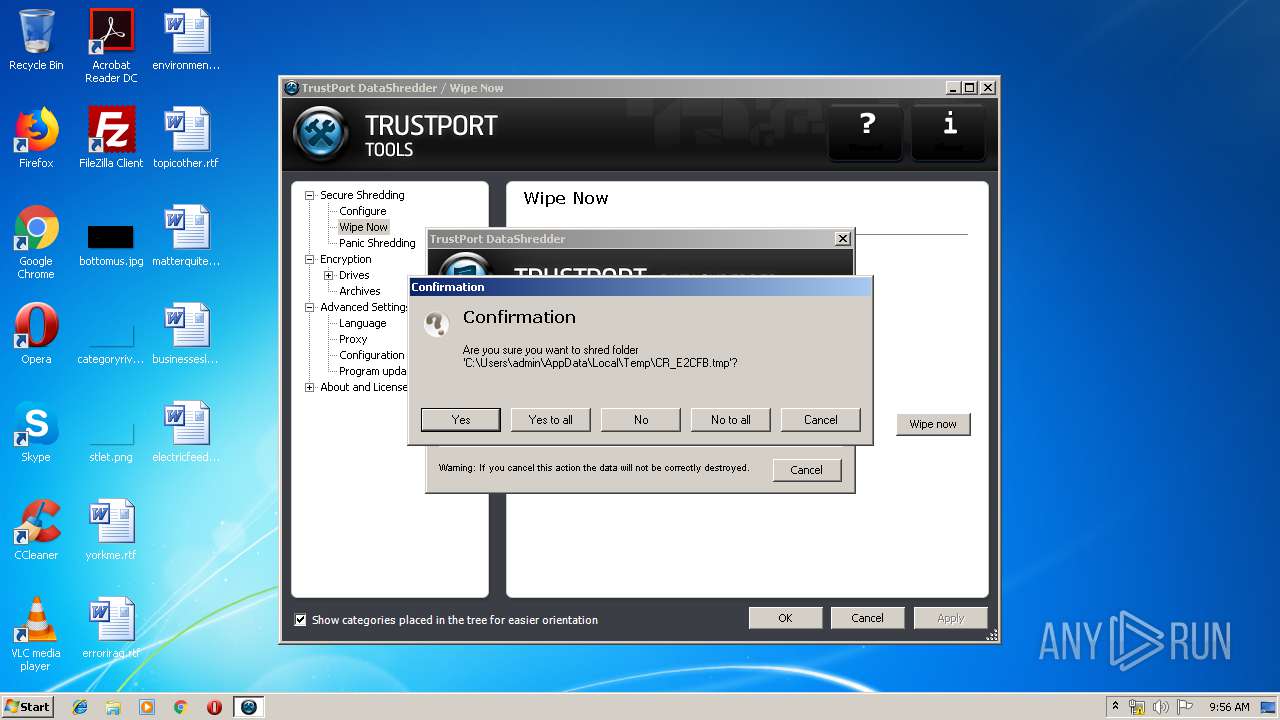
- wipesrv.exe (PID: 4004)
- wipesrv.exe (PID: 736)
- wipesrv.exe (PID: 3832)
- tpcfg.exe (PID: 2196)
- reglickey.exe (PID: 2164)
- reglickey.exe (PID: 2680)
- tpcfg.exe (PID: 1740)
- tpmgma.exe (PID: 748)
- tpcfg.exe (PID: 3248)
- reglickey.exe (PID: 2708)
- skytale.exe (PID: 2828)
- tptray.exe (PID: 3904)
- tptray.exe (PID: 2780)
- tptray.exe (PID: 3228)
- tpcfg.exe (PID: 2952)
Changes settings of System certificates
- AecCaImp.exe (PID: 748)
- tpupdate.exe (PID: 3504)
Loads dropped or rewritten executable
- tpmgma.exe (PID: 1152)
- tpmgma.exe (PID: 3084)
- tpmgma.exe (PID: 792)
- regsvr32.exe (PID: 996)
- tpupdate.exe (PID: 2748)
- regsvr32.exe (PID: 3100)
- regsvr32.exe (PID: 504)
- regsvr32.exe (PID: 2912)
- tpupdate.exe (PID: 3504)
- wipesrv.exe (PID: 4004)
- wipesrv.exe (PID: 736)
- wipesrv.exe (PID: 3832)
- skytale.exe (PID: 2828)
- tpmgma.exe (PID: 2924)
- tpmgma.exe (PID: 2740)
- tpcfg.exe (PID: 2196)
- tpcfg.exe (PID: 1740)
- tpmgma.exe (PID: 748)
- tptray.exe (PID: 3904)
- tptray.exe (PID: 2780)
- tpcfg.exe (PID: 3248)
- tptray.exe (PID: 3228)
- tpcfg.exe (PID: 2952)
Registers / Runs the DLL via REGSVR32.EXE
- TrustPort_Tools.tmp (PID: 3872)
Changes the autorun value in the registry
- regsvr32.exe (PID: 3100)
- tptray.exe (PID: 3904)
- tptray.exe (PID: 3228)
Loads the Task Scheduler COM API
- tpupdate.exe (PID: 2748)
- tpupdate.exe (PID: 3504)
- tpmgma.exe (PID: 748)
Changes the login/logoff helper path in the registry
- tpmgma.exe (PID: 748)
SUSPICIOUS
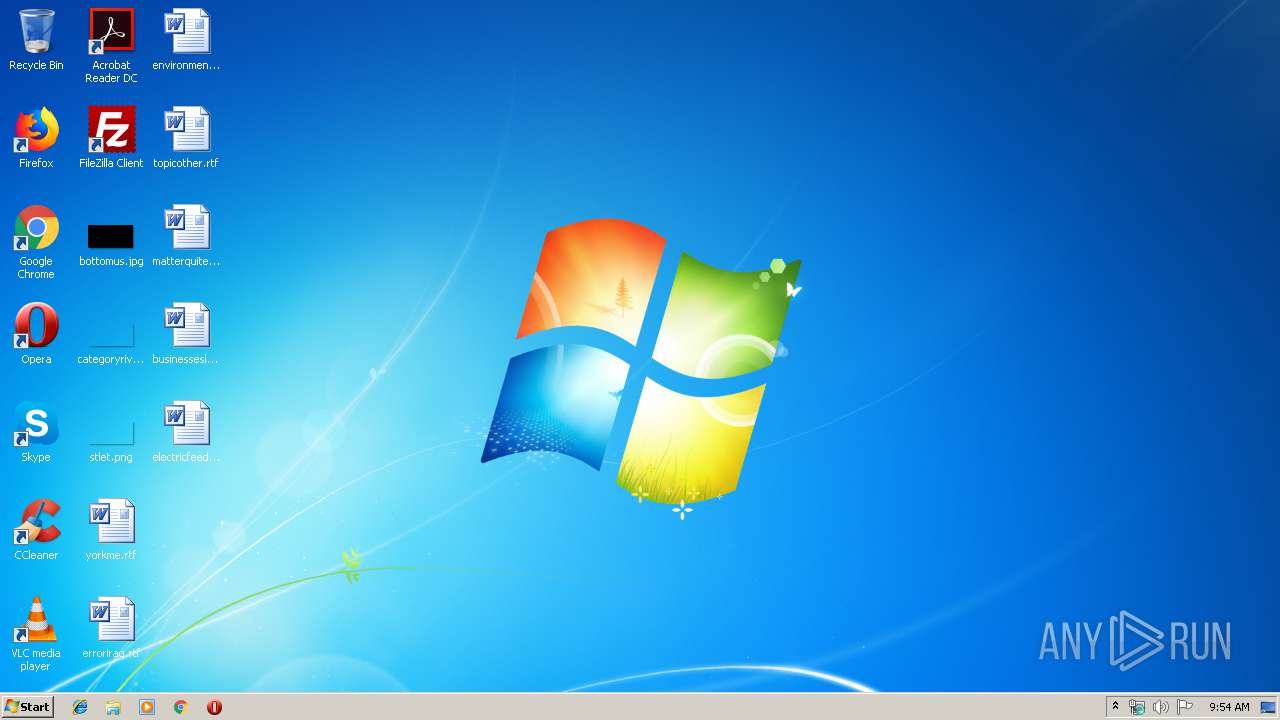
Executable content was dropped or overwritten
- chrome.exe (PID: 2552)
- TrustPort_Tools.exe (PID: 2836)
- TrustPort_Tools.exe (PID: 2760)
- TrustPort_Tools.tmp (PID: 3872)
Reads Windows owner or organization settings
- TrustPort_Tools.tmp (PID: 3872)
Reads the Windows organization settings
- TrustPort_Tools.tmp (PID: 3872)
Creates files in the Windows directory
- TrustPort_Tools.tmp (PID: 3872)
Creates or modifies windows services
- tpsctrl.exe (PID: 3924)
Creates files in the program directory
- tpmgma.exe (PID: 3084)
- regsvr32.exe (PID: 3100)
- tpupdate.exe (PID: 2748)
- skytale.exe (PID: 2828)
- tpcfg.exe (PID: 2196)
- tpcfg.exe (PID: 1740)
- tptray.exe (PID: 3228)
- tpmgma.exe (PID: 748)
- tptray.exe (PID: 2780)
- tpcfg.exe (PID: 2952)
Creates files in the driver directory
- TrustPort_Tools.tmp (PID: 3872)
Modifies the open verb of a shell class
- regsvr32.exe (PID: 504)
- regsvr32.exe (PID: 3100)
- skytale.exe (PID: 2828)
Creates COM task schedule object
- regsvr32.exe (PID: 504)
- regsvr32.exe (PID: 996)
- regsvr32.exe (PID: 3100)
- regsvr32.exe (PID: 2912)
Writes to a desktop.ini file (may be used to cloak folders)
- regsvr32.exe (PID: 3100)
Searches for installed software
- tpupdate.exe (PID: 2748)
- TrustPort_Tools.tmp (PID: 3872)
- tptray.exe (PID: 2780)
Executed as Windows Service
- wipesrv.exe (PID: 3832)
- tpmgma.exe (PID: 748)
Creates a software uninstall entry
- reglickey.exe (PID: 2680)
- reglickey.exe (PID: 2708)
Removes files from Windows directory
- wipesrv.exe (PID: 3832)
Reads the cookies of Mozilla Firefox
- wipesrv.exe (PID: 3832)
INFO
Application launched itself
- chrome.exe (PID: 2552)
Reads Internet Cache Settings
- chrome.exe (PID: 2552)
Reads the hosts file
- chrome.exe (PID: 2552)
- chrome.exe (PID: 4008)
Application was dropped or rewritten from another process
- TrustPort_Tools.tmp (PID: 1944)
- ResTool.exe (PID: 4056)
- TrustPort_Tools.tmp (PID: 3872)
- tpsctrl.exe (PID: 2536)
- AecCaImp.exe (PID: 748)
- zip.exe (PID: 2764)
- zip.exe (PID: 1892)
- zip.exe (PID: 2404)
- zip.exe (PID: 3740)
- zip.exe (PID: 3956)
- zip.exe (PID: 3924)
Loads dropped or rewritten executable
- TrustPort_Tools.tmp (PID: 3872)
Creates files in the program directory
- TrustPort_Tools.tmp (PID: 3872)
- zip.exe (PID: 3924)
- zip.exe (PID: 1892)
- zip.exe (PID: 2404)
- zip.exe (PID: 3740)
Creates a software uninstall entry
- TrustPort_Tools.tmp (PID: 3872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
126
Monitored processes
79
Malicious processes
21
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,11946932337148009740,5686277694788970784,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9871109345691879623 --mojo-platform-channel-handle=3376 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Common Files\TrustPort\bin\tpsctrl.exe" --addpathex "C:\Program Files\TrustPort\Skytale\tmp" | C:\Program Files\Common Files\TrustPort\bin\tpsctrl.exe | — | TrustPort_Tools.tmp | |||||||||||
User: admin Company: TrustPort, a.s. Integrity Level: HIGH Description: TrustPort Security Control Exit code: 0 Version: 17.0.5.7060 Modules
| |||||||||||||||
| 504 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\TrustPort\ArchiveEnc\CARReg.dll" | C:\Windows\system32\regsvr32.exe | — | TrustPort_Tools.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 688 | "C:\Program Files\Common Files\TrustPort\bin\tpsctrl.exe" --addpathex "C:\Program Files\TrustPort\ArchiveEnc\dmp" | C:\Program Files\Common Files\TrustPort\bin\tpsctrl.exe | — | TrustPort_Tools.tmp | |||||||||||
User: admin Company: TrustPort, a.s. Integrity Level: HIGH Description: TrustPort Security Control Exit code: 0 Version: 17.0.5.7060 Modules
| |||||||||||||||
| 736 | "C:\Program Files\TrustPort\DataShredder\bin\wipesrv.exe" --start | C:\Program Files\TrustPort\DataShredder\bin\wipesrv.exe | — | TrustPort_Tools.tmp | |||||||||||
User: admin Company: TrustPort, a.s. Integrity Level: HIGH Description: TrustPort DataShredder - Wiping Service Exit code: 0 Version: 17.0.5.7060 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Common Files\TrustPort\bin\tpmgma.exe" --svc=tpmgma_service | C:\Program Files\Common Files\TrustPort\bin\tpmgma.exe | services.exe | ||||||||||||
User: SYSTEM Company: TrustPort, a.s. Integrity Level: SYSTEM Description: TrustPort Antivirus Management Agent Exit code: 0 Version: 17.0.5.7060 Modules
| |||||||||||||||
| 748 | "C:\Users\admin\AppData\Local\Temp\is-MK307.tmp\AecCaImp.exe" C:\Users\admin\AppData\Local\Temp\is-MK307.tmp\aecroot.cer | C:\Users\admin\AppData\Local\Temp\is-MK307.tmp\AecCaImp.exe | — | TrustPort_Tools.tmp | |||||||||||
User: admin Company: TrustPort, a.s. Integrity Level: HIGH Description: AecCaImp Exit code: 0 Version: 17.0.5.7060 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Common Files\TrustPort\bin\tpsctrl.exe" --addpathex "C:\Program Files\Common Files\TrustPort\Tmp" | C:\Program Files\Common Files\TrustPort\bin\tpsctrl.exe | — | TrustPort_Tools.tmp | |||||||||||
User: admin Company: TrustPort, a.s. Integrity Level: HIGH Description: TrustPort Security Control Exit code: 0 Version: 17.0.5.7060 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Common Files\TrustPort\bin\tpmgma.exe" --execute -im "C:\Program Files\TrustPort\DiskProtection\bin\dpmgma.dll" | C:\Program Files\Common Files\TrustPort\bin\tpmgma.exe | — | TrustPort_Tools.tmp | |||||||||||
User: admin Company: TrustPort, a.s. Integrity Level: HIGH Description: TrustPort Antivirus Management Agent Exit code: 0 Version: 17.0.5.7060 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Common Files\TrustPort\bin\tpsctrl.exe" --addpathex "C:\Program Files\TrustPort\DataShredder\tmp" | C:\Program Files\Common Files\TrustPort\bin\tpsctrl.exe | — | TrustPort_Tools.tmp | |||||||||||
User: admin Company: TrustPort, a.s. Integrity Level: HIGH Description: TrustPort Security Control Exit code: 0 Version: 17.0.5.7060 Modules
| |||||||||||||||
Total events
2 575
Read events
2 211
Write events
342
Delete events
22
Modification events
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2552-13223814836340500 |
Value: 259 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2552-13223814836340500 |
Value: 259 | |||
Executable files
184
Suspicious files
55
Text files
182
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\52aa218c-ef17-4a03-ae2c-909b4154e1f3.tmp | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39ab8c.TMP | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
15
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2748 | tpupdate.exe | GET | 301 | 89.185.240.197:80 | http://download2.trustport.com/update/tpupdate/v5/tpupdate.xml | CZ | html | 189 b | unknown |
2748 | tpupdate.exe | GET | 200 | 54.39.105.61:80 | http://download15.trustport.com/update/16/tpupdate/v5/tpupdate.xml | FR | xml | 12.3 Kb | unknown |
2780 | tptray.exe | GET | 403 | 91.239.200.70:80 | http://www.trustport.com/app/wkst/licbox/default/update.lck | CZ | html | 326 b | unknown |
2780 | tptray.exe | GET | 403 | 91.239.200.70:80 | http://www.trustport.com/app/wkst/licbox/default/ | CZ | html | 326 b | unknown |
2780 | tptray.exe | GET | 403 | 91.239.200.70:80 | http://www.trustport.com/app/wkst/licbox/default/update.lck | CZ | html | 326 b | unknown |
2780 | tptray.exe | GET | 403 | 91.239.200.70:80 | http://www.trustport.com/app/wkst/licbox/default/update.lck | CZ | html | 326 b | unknown |
2780 | tptray.exe | GET | 403 | 91.239.200.70:80 | http://www.trustport.com/app/wkst/licbox/default/update.lck | CZ | html | 326 b | unknown |
2780 | tptray.exe | GET | 403 | 91.239.200.70:80 | http://www.trustport.com/app/wkst/licbox/default/update.lck | CZ | html | 326 b | unknown |
2780 | tptray.exe | GET | 403 | 89.185.240.197:80 | http://license.trustport.com/news_check.php?client=X6YBBgEBDzz/EP9wzEiOboCysvYUvwQBAIBKIl5FTlUAAAAAAAAAAAAAAAAAAAAAlBsAAAUDgEoiXkVOVaTdJU9SbEquZky2AkiGCm2UGwEABwOASiJeRU5VpN0lT1JsSq5mTLYCSIYKbZQbAQAGA4BKIl5FTlWk3SVPUmxKrmZMtgJIhgptlBsBAA== | CZ | html | 1.20 Kb | unknown |
2552 | chrome.exe | GET | 200 | 72.21.81.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4008 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 89.185.239.36:443 | file.trustport.com | Master Internet s.r.o. | CZ | suspicious |
4008 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 172.217.22.110:443 | clients4.google.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4008 | chrome.exe | 172.217.21.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2552 | chrome.exe | 72.21.81.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2748 | tpupdate.exe | 89.185.240.197:80 | download2.trustport.com | Master Internet s.r.o. | CZ | unknown |
2748 | tpupdate.exe | 54.39.105.61:80 | download15.trustport.com | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
file.trustport.com |
| suspicious |
accounts.google.com |
| shared |
clients4.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
download2.trustport.com |
| unknown |
download15.trustport.com |
| unknown |