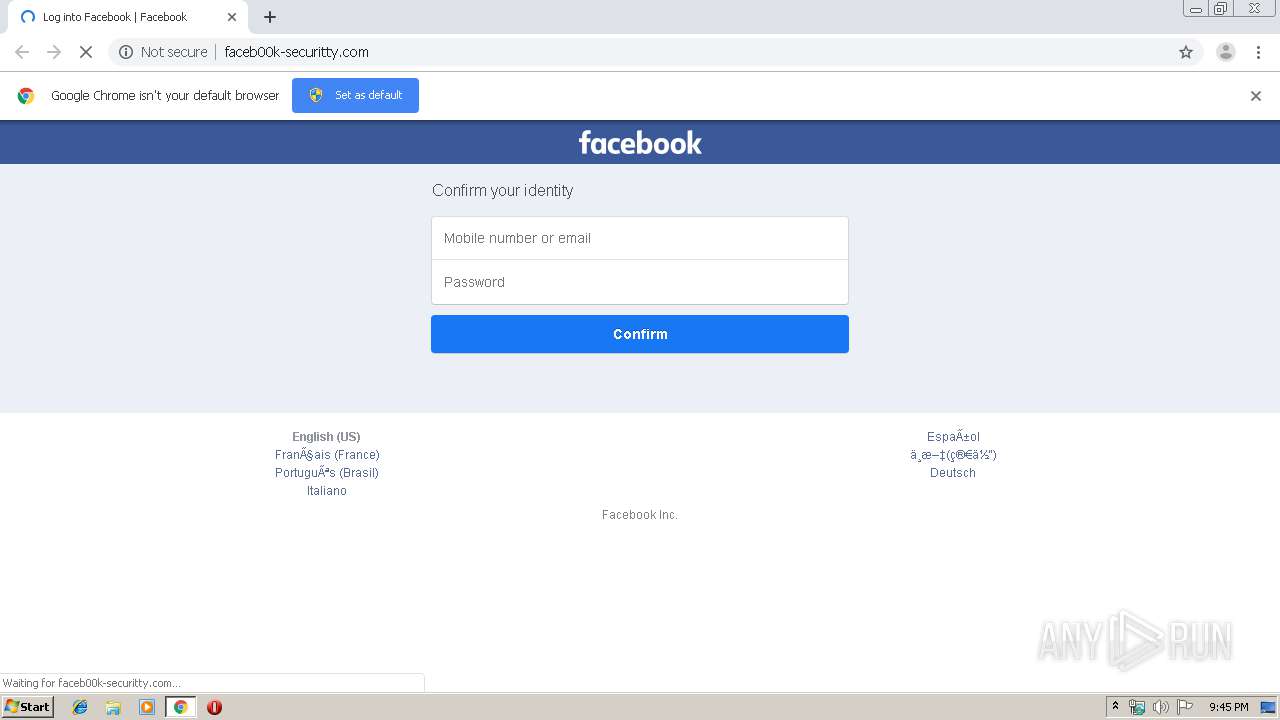
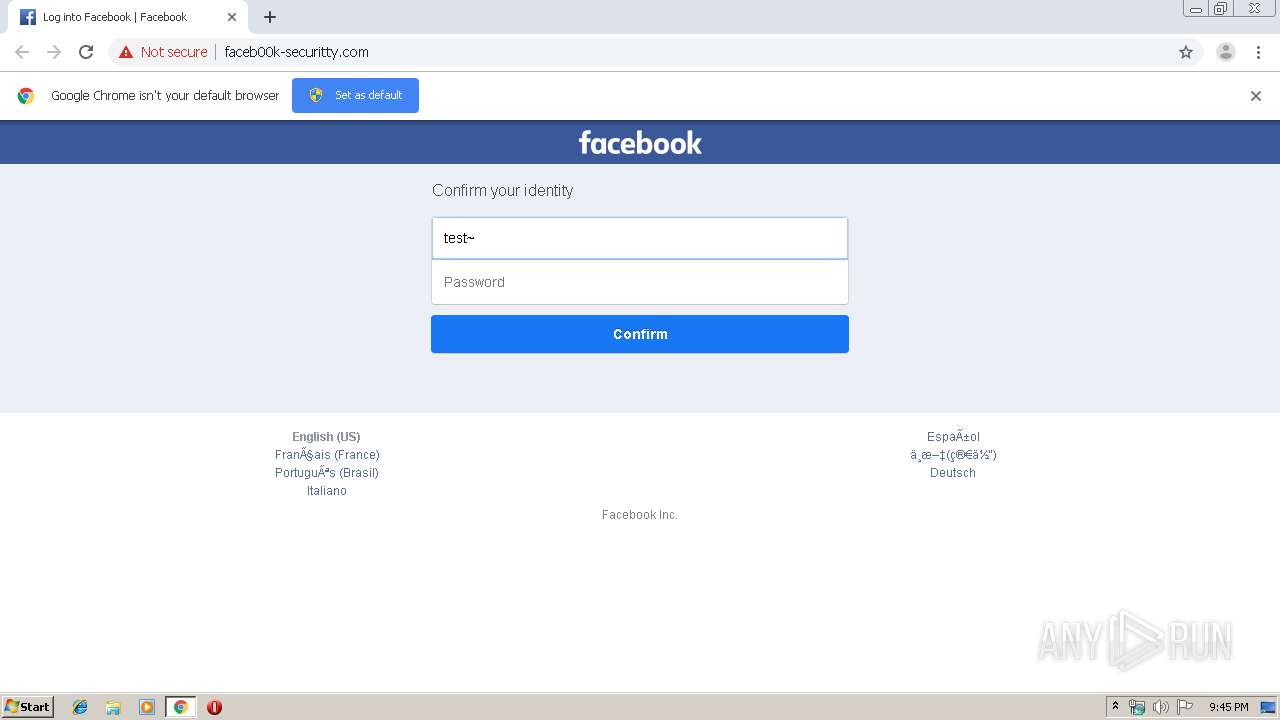
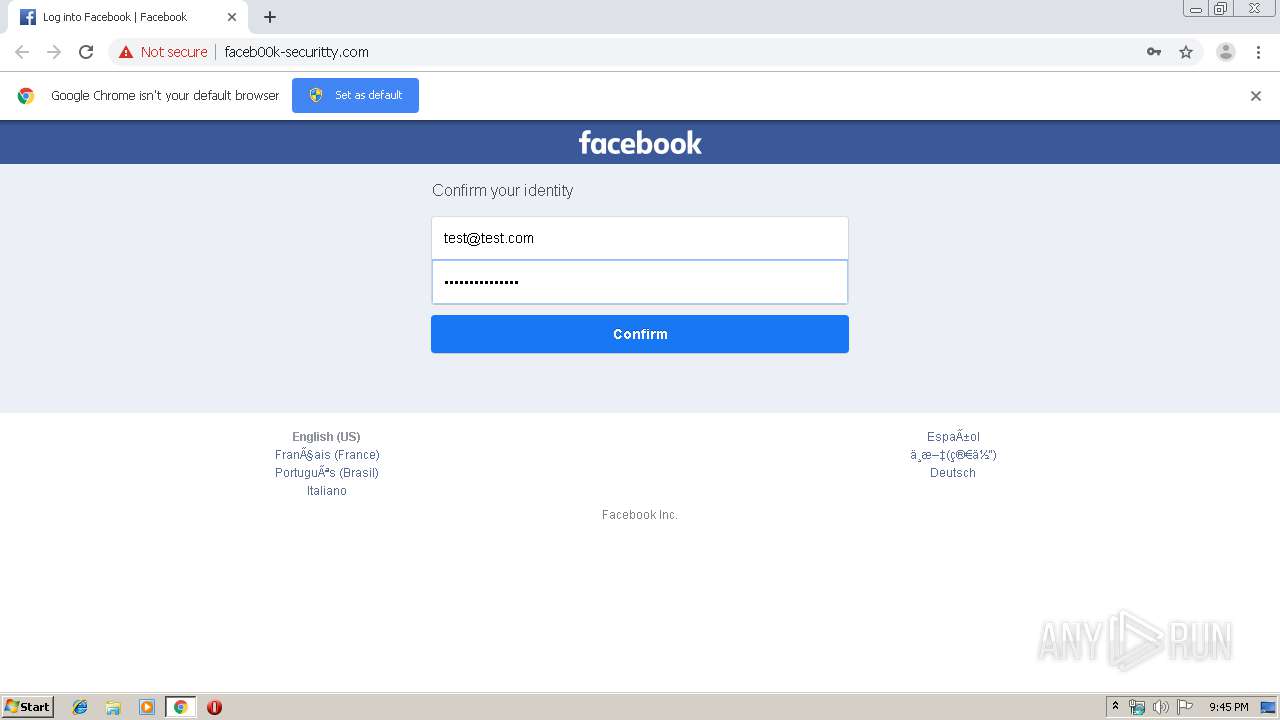
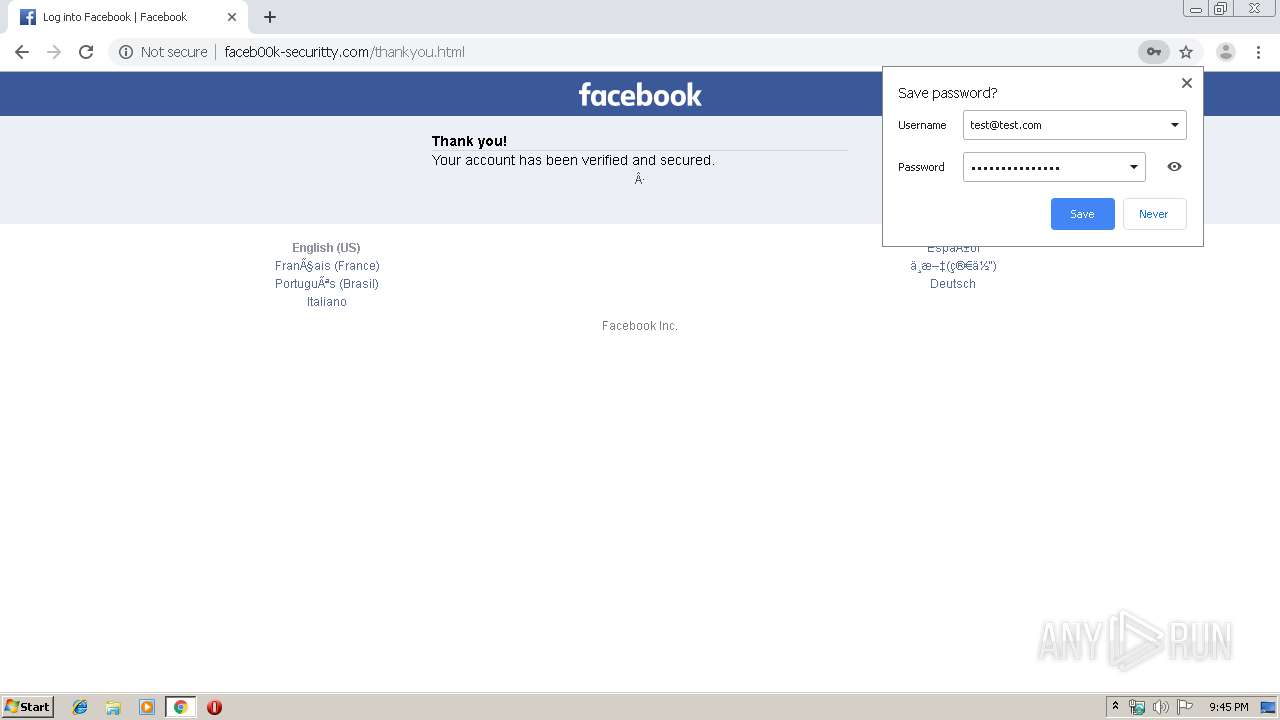
| URL: | http://faceb00k-securitty.com/ |
| Full analysis: | https://app.any.run/tasks/9163f006-7a24-4207-a60d-528004c98315 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 20:45:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BB1597C752EE027218A2CD9661A75F0A |
| SHA1: | ABE2B81D2B3B60358C83E438467B7C4768B8ED04 |
| SHA256: | A1437EB1E4F9F8A674A32262DD7DA546F918A4AD204C9115F24F8D22B02017A0 |
| SSDEEP: | 3:N1KYY1VOUHcR6tn:CYY1F8R6t |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2140)
INFO
Reads the hosts file
- chrome.exe (PID: 2140)
- chrome.exe (PID: 1552)
Reads settings of System Certificates
- chrome.exe (PID: 1552)
Application launched itself
- chrome.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
25
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11819599662134913979,1681326637078664038,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8438755026993037297 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1316 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11819599662134913979,1681326637078664038,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16367148966400965821 --mojo-platform-channel-handle=3804 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11819599662134913979,1681326637078664038,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6579229739602395255 --mojo-platform-channel-handle=1608 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11819599662134913979,1681326637078664038,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9644974856427377175 --mojo-platform-channel-handle=3568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11819599662134913979,1681326637078664038,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17337193438980119718 --mojo-platform-channel-handle=4008 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,11819599662134913979,1681326637078664038,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6261013946026383072 --mojo-platform-channel-handle=4100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://faceb00k-securitty.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,11819599662134913979,1681326637078664038,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11216439594463780471 --mojo-platform-channel-handle=4392 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,11819599662134913979,1681326637078664038,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7858517339302080154 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
616
Read events
522
Write events
89
Delete events
5
Modification events
| (PID) Process: | (1516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2140-13215559519960500 |
Value: 259 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
Executable files
0
Suspicious files
15
Text files
213
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1be35b18-c6c1-42a4-b6b7-6750818715db.tmp | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2140 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a8cd.TMP | text | |
MD5:— | SHA256:— | |||
| 3368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
24
DNS requests
12
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1552 | chrome.exe | GET | 200 | 107.180.44.125:80 | http://faceb00k-securitty.com/rsrc.php/v3/js/main.js | US | text | 425 b | malicious |
1552 | chrome.exe | GET | 200 | 107.180.44.125:80 | http://faceb00k-securitty.com/rsrc.php/v3/yK/l/bxrgh5LjyGF.css?_nc_x=Ij3Xr9lg0Kz | US | text | 11.0 Kb | malicious |
1552 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
1552 | chrome.exe | GET | 200 | 107.180.44.125:80 | http://faceb00k-securitty.com/ | US | html | 3.17 Kb | malicious |
1552 | chrome.exe | GET | 200 | 107.180.44.125:80 | http://faceb00k-securitty.com/rsrc.php/v3/ya/r/O2aKM2iSbOw.png | US | image | 6.63 Kb | malicious |
1552 | chrome.exe | GET | 200 | 107.180.44.125:80 | http://faceb00k-securitty.com/rsrc.php/v3/ye/r/-2_e3ML2w0e.png | US | image | 27.7 Kb | malicious |
1552 | chrome.exe | POST | — | 107.180.44.125:80 | http://faceb00k-securitty.com/confirm.php | US | — | — | malicious |
1552 | chrome.exe | GET | 200 | 107.180.44.125:80 | http://faceb00k-securitty.com/thankyou.html | US | html | 2.84 Kb | malicious |
1552 | chrome.exe | GET | 200 | 107.180.44.125:80 | http://faceb00k-securitty.com/rsrc.php/v3/yH/l/8gq-vs7Rs9q.css?_nc_x=Ij3Wp8lg5Kz | US | text | 9.96 Kb | malicious |
1552 | chrome.exe | GET | 200 | 107.180.44.125:80 | http://faceb00k-securitty.com/rsrc.php/v3/yK/l/bxrgh5LjyGF.css?_nc_x=Ij3Wp8lg5Kz | US | text | 11.0 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1552 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1552 | chrome.exe | 107.180.44.125:80 | faceb00k-securitty.com | GoDaddy.com, LLC | US | malicious |
1552 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1552 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1552 | chrome.exe | 172.217.18.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1552 | chrome.exe | 173.194.183.169:80 | r4---sn-aigl6ney.gvt1.com | Google Inc. | US | whitelisted |
1552 | chrome.exe | 185.60.216.35:443 | facebook.com | Facebook, Inc. | IE | whitelisted |
1552 | chrome.exe | 74.125.4.216:80 | r2---sn-aigzrney.gvt1.com | Google Inc. | US | whitelisted |
1552 | chrome.exe | 172.217.22.110:80 | clients1.google.com | Google Inc. | US | whitelisted |
1552 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
faceb00k-securitty.com |
| malicious |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-aigzrney.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
r4---sn-aigl6ney.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1552 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
1552 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
4 ETPRO signatures available at the full report