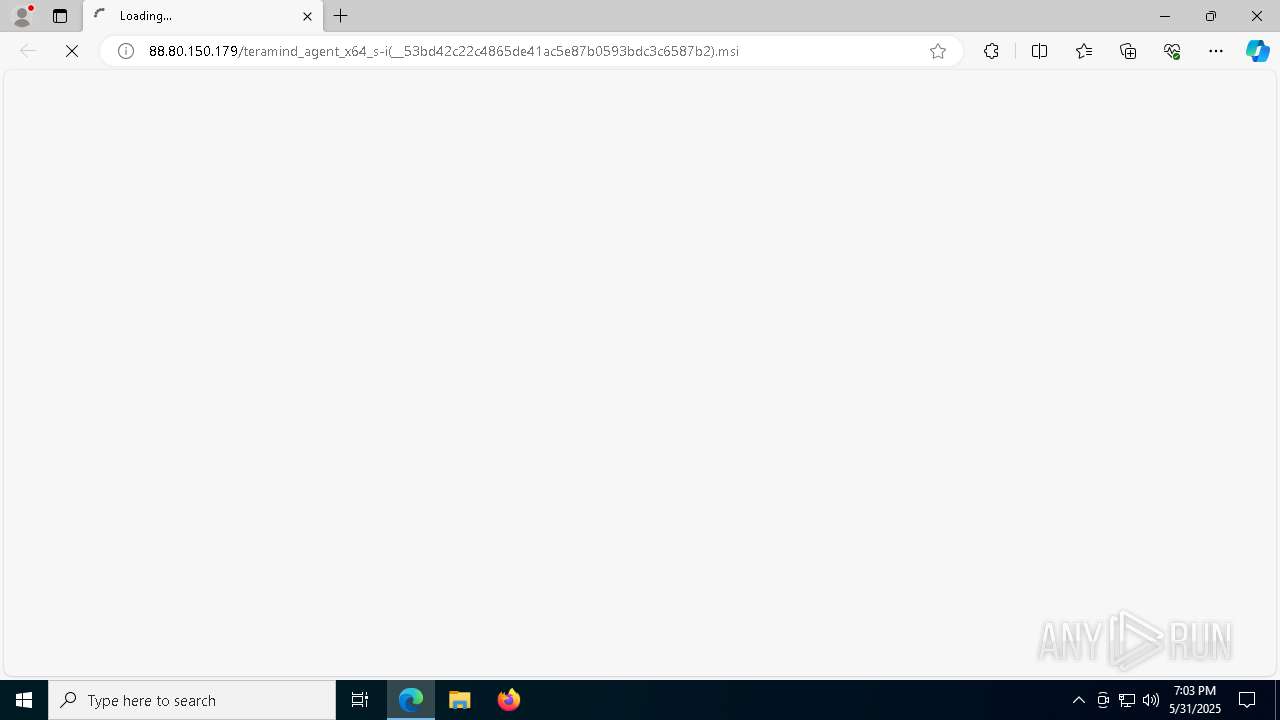
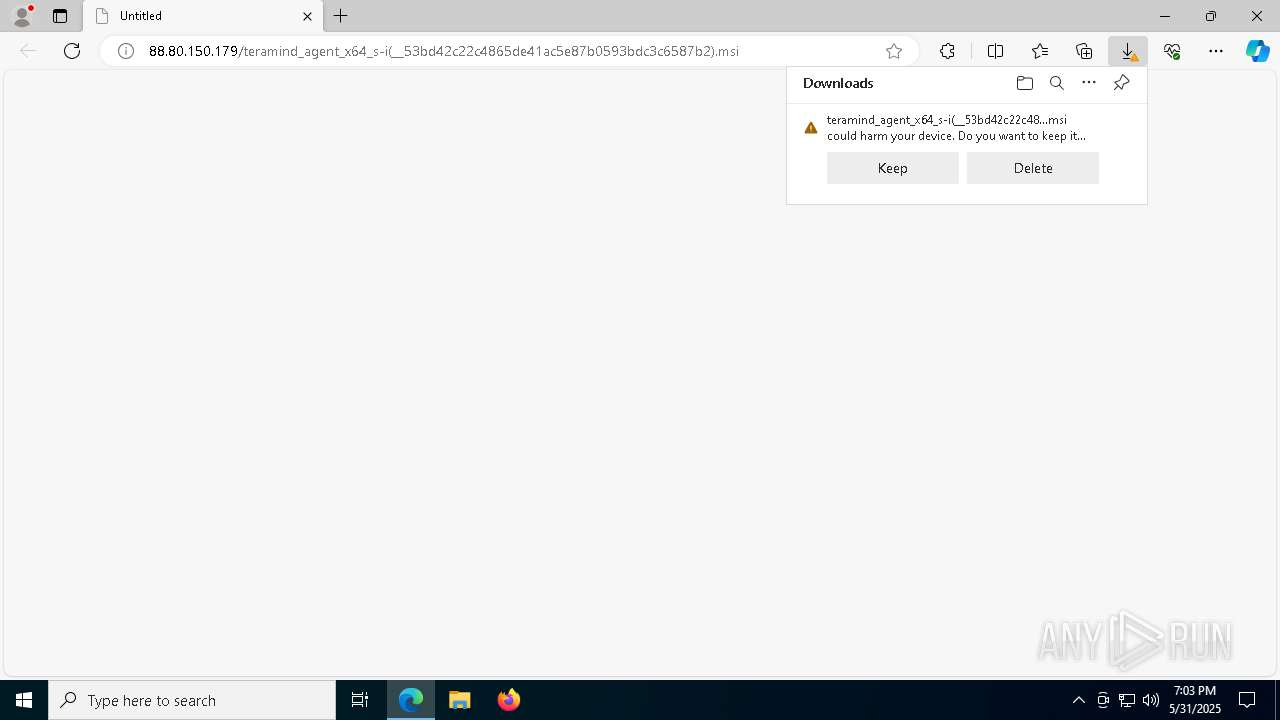
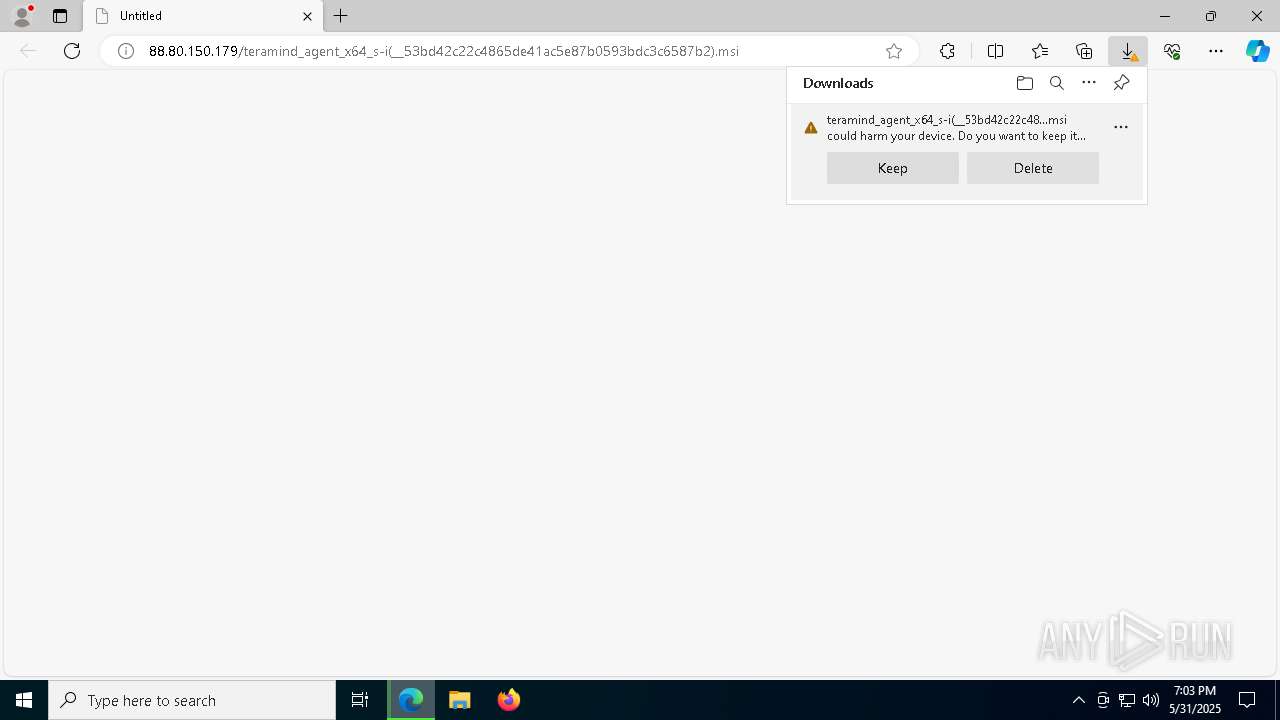
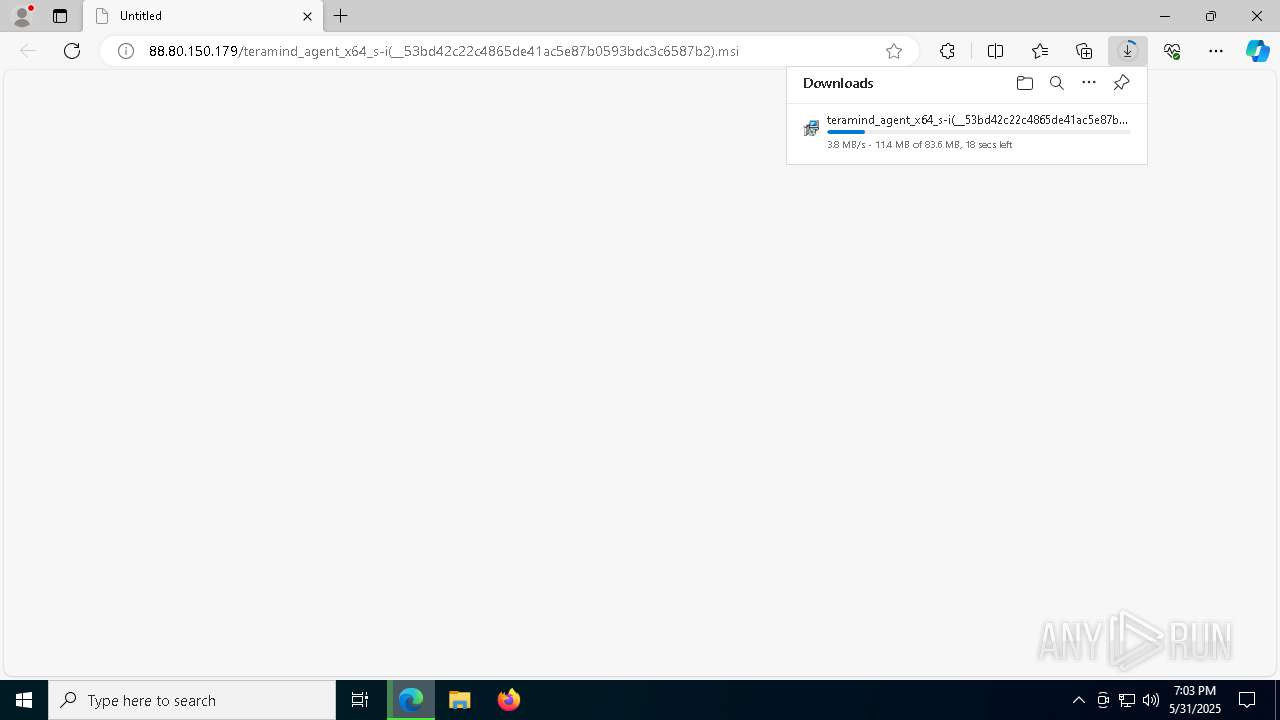
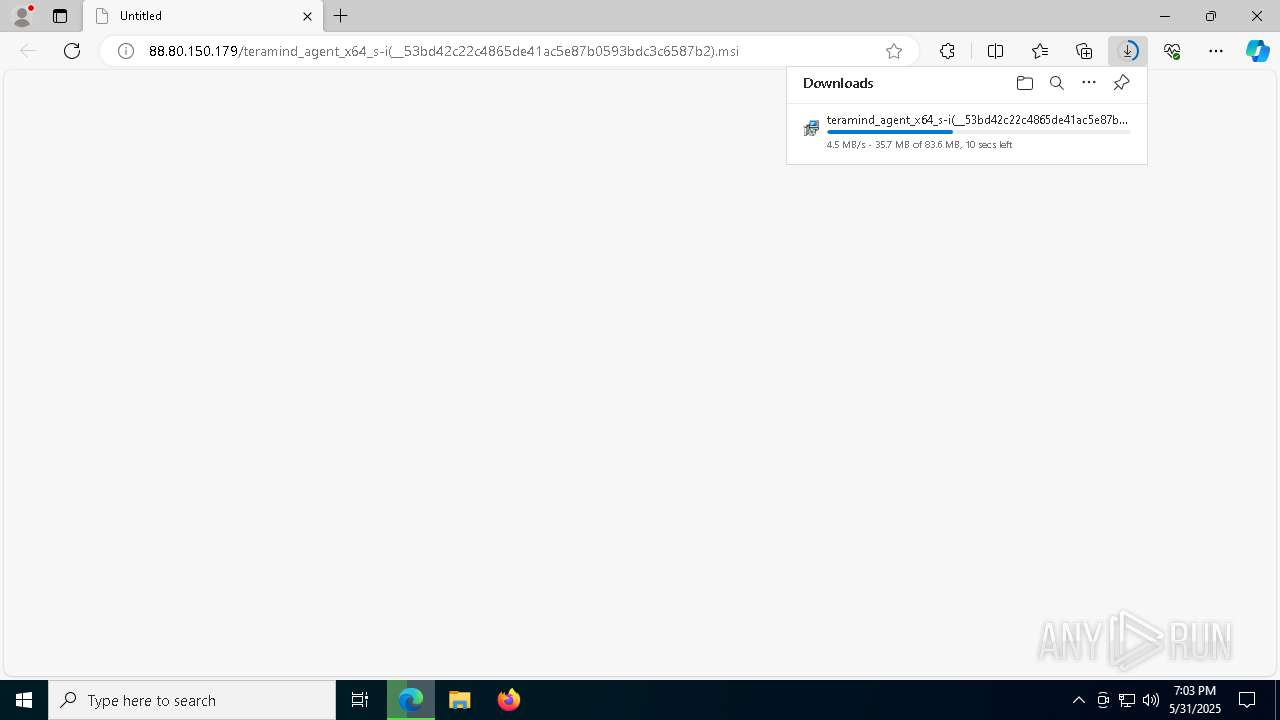
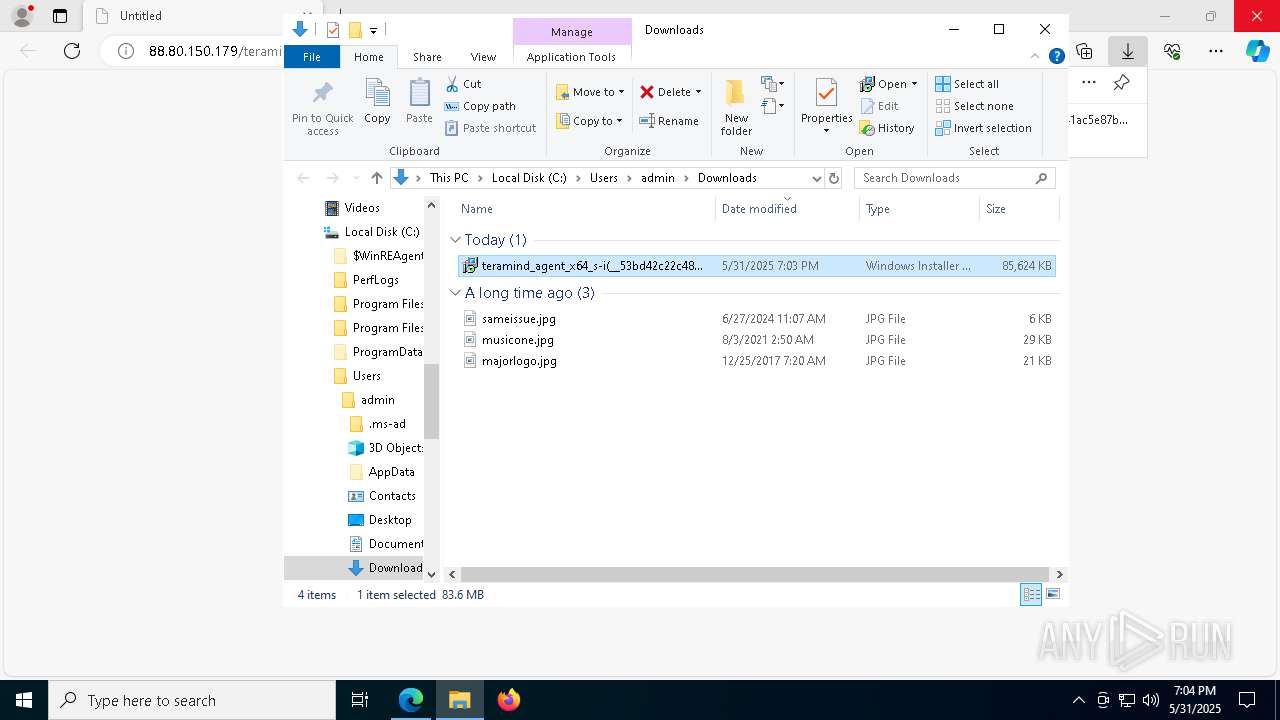
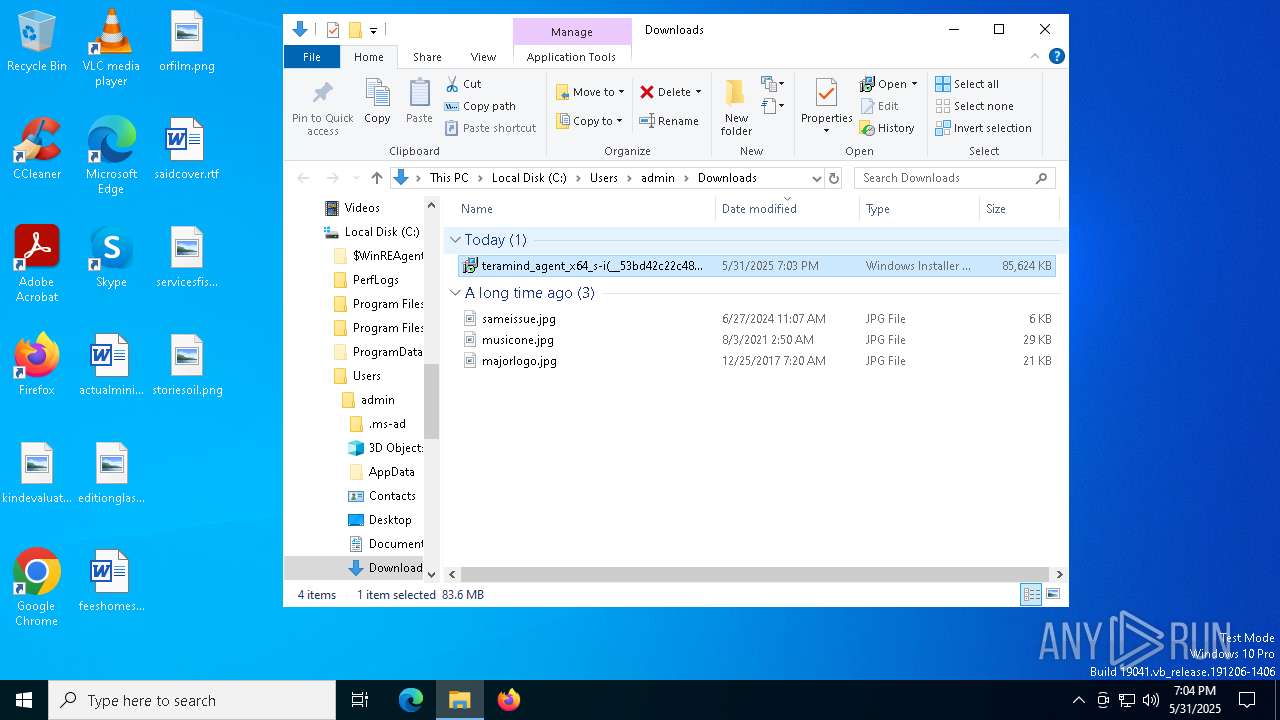
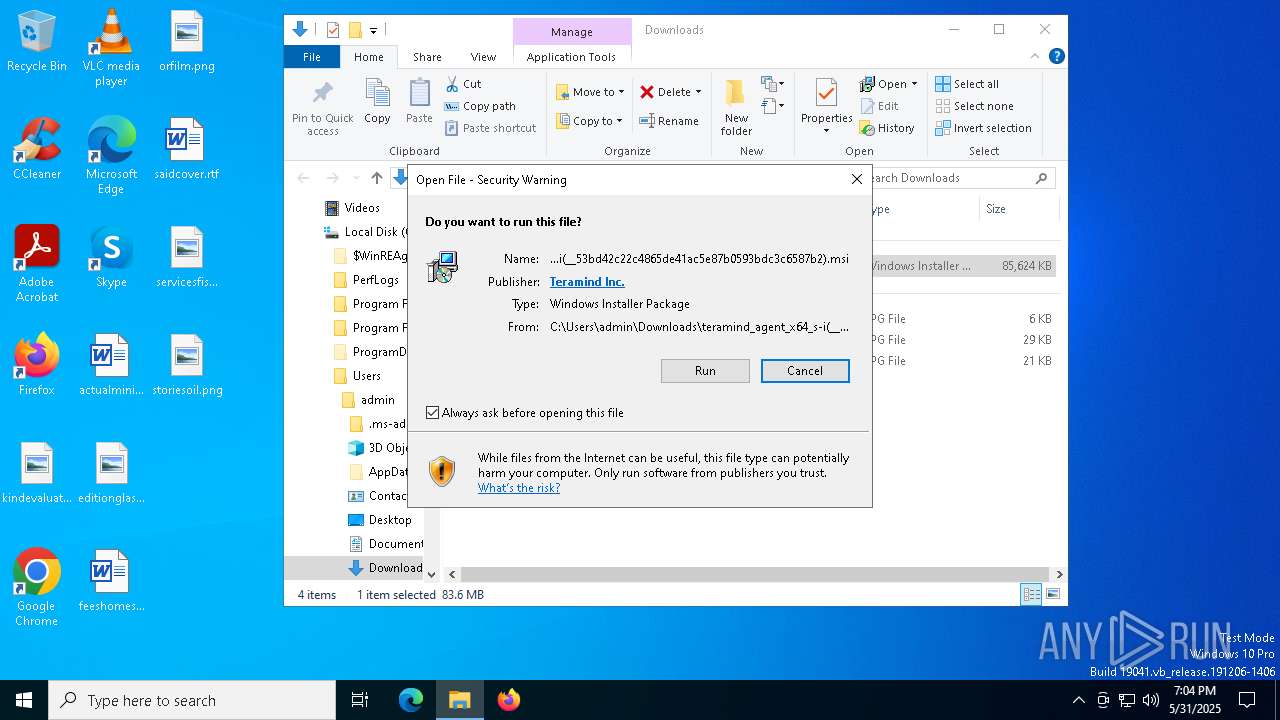
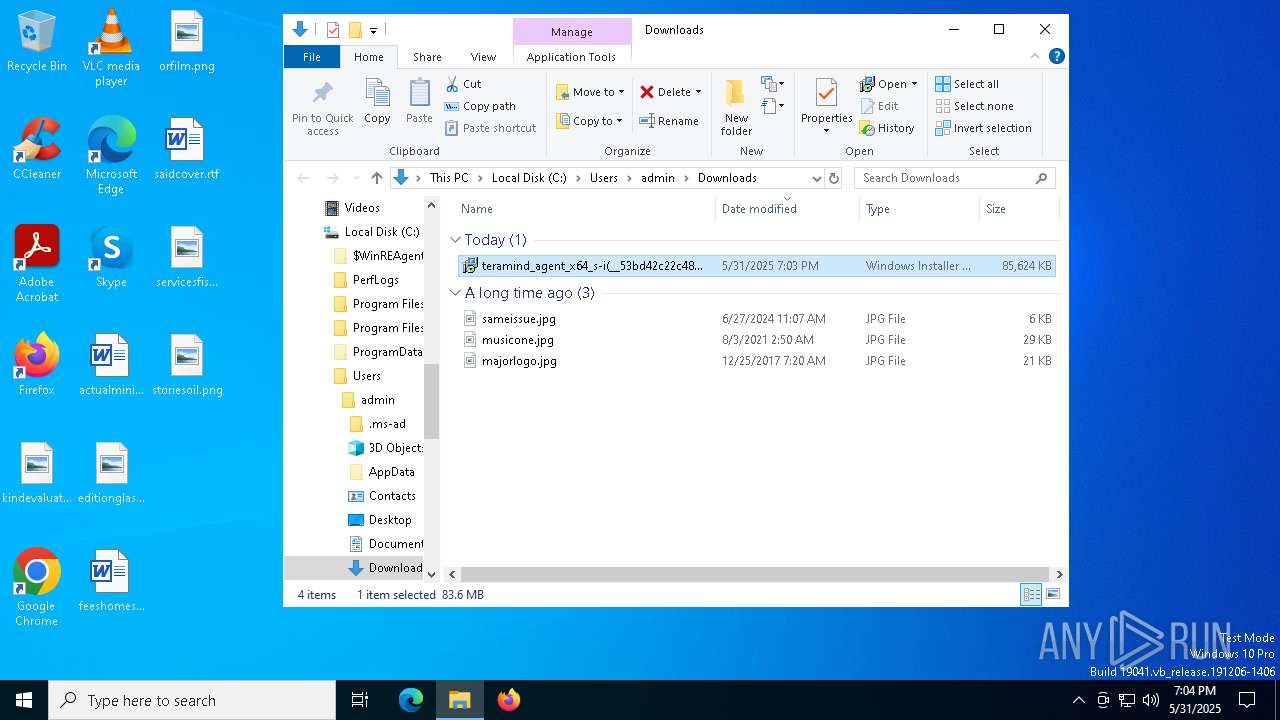
| URL: | http://88.80.150.179/teramind_agent_x64_s-i(__53bd42c22c4865de41ac5e87b0593bdc3c6587b2).msi |
| Full analysis: | https://app.any.run/tasks/65b39219-fc4f-4014-a203-944767dfa48f |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 31, 2025, 19:03:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FED864FE961954DD0305B0BBEBDB571B |
| SHA1: | 8A77B45691771533F22C04F4F0645274C3A9D915 |
| SHA256: | A13901875270411C6F551E0FA32FD913A2FB24D8AB14110C1E41B6B2FFECB954 |
| SSDEEP: | 3:N1KXruRo3NxHByYFHASwBGWEISH3:CXr938Y2S0GWD03 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 5492)
Process drops legitimate windows executable
- msedge.exe (PID: 2772)
- msiexec.exe (PID: 4408)
- kgxfngke.ovp.exe (PID: 5304)
- VC_redist.x86.exe (PID: 2064)
- VC_redist.x64.exe (PID: 716)
Executable content was dropped or overwritten
- rundll32.exe (PID: 7708)
- rundll32.exe (PID: 7712)
- rundll32.exe (PID: 7520)
- rundll32.exe (PID: 7728)
- rundll32.exe (PID: 4736)
- rundll32.exe (PID: 7512)
- rundll32.exe (PID: 456)
- rundll32.exe (PID: 4560)
- rundll32.exe (PID: 7392)
- rundll32.exe (PID: 928)
- rundll32.exe (PID: 7768)
- rundll32.exe (PID: 5568)
- VC_redist.x86.exe (PID: 2064)
- svc.exe (PID: 7052)
- kgxfngke.ovp.exe (PID: 5304)
- VC_redist.x64.exe (PID: 716)
- VC_redist.x64.exe (PID: 8184)
- VC_redist.x86.exe (PID: 8108)
- bundle.exe (PID: 6208)
- rundll32.exe (PID: 8136)
- bundle.exe (PID: 6240)
- rundll32.exe (PID: 7592)
- bundle.exe (PID: 5364)
- rundll32.exe (PID: 4276)
- rundll32.exe (PID: 4424)
- rundll32.exe (PID: 3176)
- rundll32.exe (PID: 7988)
- rundll32.exe (PID: 2084)
- rundll32.exe (PID: 6496)
- rundll32.exe (PID: 3028)
- rundll32.exe (PID: 760)
- rundll32.exe (PID: 4220)
- rundll32.exe (PID: 1804)
- rundll32.exe (PID: 7364)
- rundll32.exe (PID: 7612)
- rundll32.exe (PID: 8024)
- rundll32.exe (PID: 3012)
- rundll32.exe (PID: 2040)
- rundll32.exe (PID: 7632)
- rundll32.exe (PID: 6900)
Executes as Windows Service
- VSSVC.exe (PID: 7404)
- svc.exe (PID: 7052)
- svc.exe (PID: 7368)
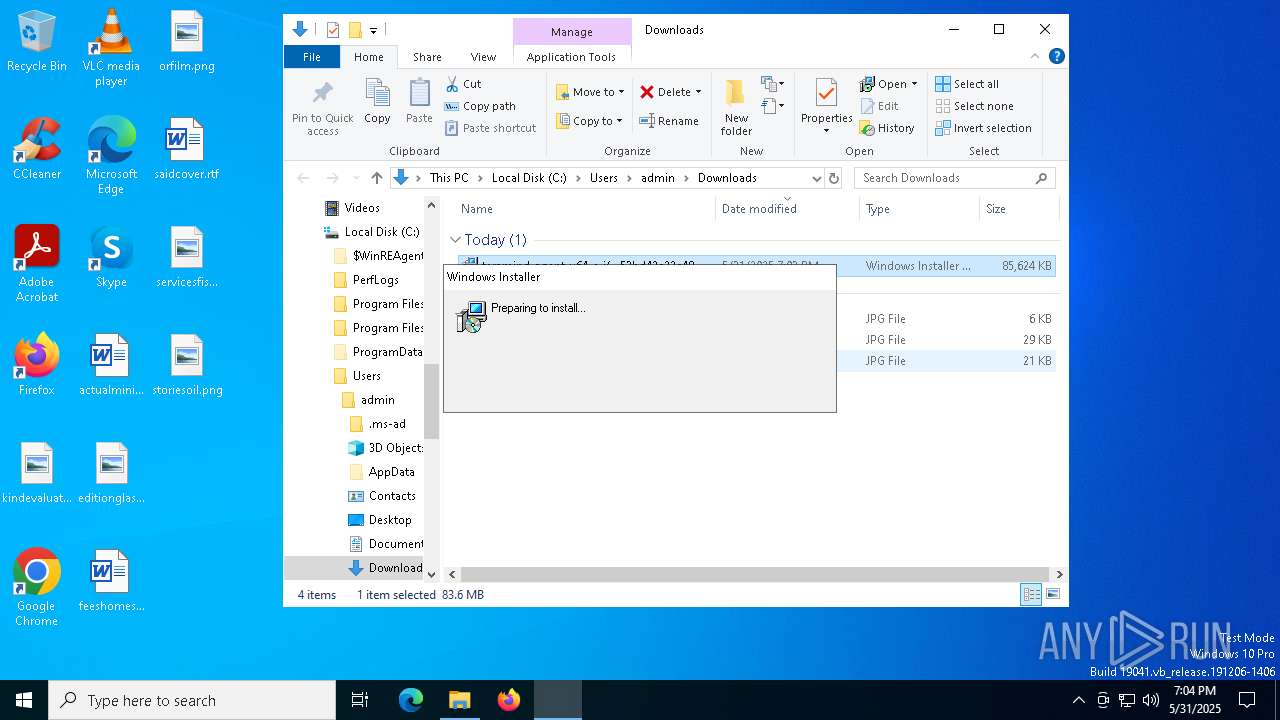
Application launched itself
- msiexec.exe (PID: 4408)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 4408)
- msiexec.exe (PID: 5364)
- msiexec.exe (PID: 4724)
The process drops C-runtime libraries
- msiexec.exe (PID: 4408)
Connects to unusual port
- dwm.exe (PID: 2088)
- dwm.exe (PID: 5408)
Starts a Microsoft application from unusual location
- VC_redist.x86.exe (PID: 8108)
- VC_redist.x64.exe (PID: 8184)
Starts itself from another location
- bundle.exe (PID: 6208)
INFO
Application launched itself
- msedge.exe (PID: 7360)
- msedge.exe (PID: 7240)
The sample compiled with czech language support
- msedge.exe (PID: 2772)
- msiexec.exe (PID: 4408)
Reads Environment values
- identity_helper.exe (PID: 7436)
- identity_helper.exe (PID: 1240)
Checks supported languages
- identity_helper.exe (PID: 7436)
- identity_helper.exe (PID: 1240)
- msiexec.exe (PID: 4408)
- msiexec.exe (PID: 7296)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
- msiexec.exe (PID: 8052)
- rundll32.exe (PID: 7708)
Reads the computer name
- identity_helper.exe (PID: 7436)
- identity_helper.exe (PID: 1240)
- msiexec.exe (PID: 4408)
- msiexec.exe (PID: 7296)
Reads the software policy settings
- explorer.exe (PID: 5492)
- msiexec.exe (PID: 8052)
- rundll32.exe (PID: 7708)
Reads Microsoft Office registry keys
- explorer.exe (PID: 5492)
Checks proxy server information
- explorer.exe (PID: 5492)
- rundll32.exe (PID: 7708)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8052)
- msiexec.exe (PID: 4408)
- msiexec.exe (PID: 5364)
- msiexec.exe (PID: 4724)
- msedge.exe (PID: 6028)
Creates files or folders in the user directory
- explorer.exe (PID: 5492)
- rundll32.exe (PID: 7708)
Create files in a temporary directory
- rundll32.exe (PID: 7708)
Manages system restore points
- SrTasks.exe (PID: 6980)
The sample compiled with english language support
- msiexec.exe (PID: 4408)
- msiexec.exe (PID: 5364)
- kgxfngke.ovp.exe (PID: 5304)
- VC_redist.x86.exe (PID: 2064)
- VC_redist.x86.exe (PID: 8108)
- VC_redist.x64.exe (PID: 8184)
- VC_redist.x64.exe (PID: 716)
- bundle.exe (PID: 6240)
- bundle.exe (PID: 6208)
- bundle.exe (PID: 5364)
- msiexec.exe (PID: 4724)
- msedge.exe (PID: 6028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
273
Monitored processes
133
Malicious processes
2
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5304 --field-trial-handle=2284,i,14030800855928329152,13191728509274436034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5728 --field-trial-handle=2284,i,14030800855928329152,13191728509274436034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 456 | rundll32.exe "C:\WINDOWS\Installer\MSIDB9B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1235875 101 Teramind.Setup.Actions!Teramind.Setup.Actions.CustomActions.ValidateAdmin | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | "C:\ProgramData\{4CEC2908-5CE4-48F0-A717-8FC833D8017A}\updates\yxfdq5k5.xeg\VC_redist.x64.exe" /quiet /norestart | C:\ProgramData\{4CEC2908-5CE4-48F0-A717-8FC833D8017A}\updates\yxfdq5k5.xeg\VC_redist.x64.exe | kgxfngke.ovp.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.32.31332 Exit code: 1638 Version: 14.32.31332.0 Modules
| |||||||||||||||
| 760 | rundll32.exe "C:\WINDOWS\Installer\MSI7CD8.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1277140 564 Teramind.Setup.Actions!Teramind.Setup.Actions.CustomActions.ValidateAdmin | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | C:\Windows\syswow64\MsiExec.exe -Embedding 0DA045557066E3EE7428FA5C199FDF10 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1324 --field-trial-handle=2284,i,14030800855928329152,13191728509274436034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 928 | rundll32.exe "C:\WINDOWS\Installer\MSIE775.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1238906 154 Teramind.Setup.Actions!Teramind.Setup.Actions.CustomActions.CleanupAgent | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3380 --field-trial-handle=2212,i,7898356220233356893,2577297539228592842,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4888 --field-trial-handle=2284,i,14030800855928329152,13191728509274436034,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
157 632
Read events
156 141
Write events
1 128
Delete events
363
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:000000000005025C |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:000000000005024A |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (7360) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7360) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7360) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7360) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7360) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 10ED227809952F00 | |||
| (PID) Process: | (7360) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328266 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A3889E61-12A3-479E-8040-69D03C7F14C3} | |||
| (PID) Process: | (7360) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DD912D7809952F00 | |||
| (PID) Process: | (7360) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
334
Suspicious files
597
Text files
212
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f097.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f0c6.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f0c6.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f0d5.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f0d5.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f0d5.TMP | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7360 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
106
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7964 | svchost.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2772 | msedge.exe | GET | 200 | 88.80.150.179:80 | http://88.80.150.179/teramind_agent_x64_s-i(__53bd42c22c4865de41ac5e87b0593bdc3c6587b2).msi | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7996 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7996 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7184 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7964 | svchost.exe | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7964 | svchost.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7360 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2772 | msedge.exe | 88.80.150.179:80 | — | S3 Company Ltd | BG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
kgxfngke.ovp.exe | Setup mutex successfully held
|
kgxfngke.ovp.exe | Application started
|
kgxfngke.ovp.exe | Existing config file:
|
kgxfngke.ovp.exe | Unpacking0
|
kgxfngke.ovp.exe | Exe file path: C:\ProgramData\{4CEC2908-5CE4-48F0-A717-8FC833D8017A}\updates\yxfdq5k5.xeg\bundle.exe
|
kgxfngke.ovp.exe | Mutex with name 'Global\{44EAB652-6600-48F4-A3AE-E0211E1046B3}-bundle-25.17.2584' is going to be locked
|
kgxfngke.ovp.exe | Install redis
|
kgxfngke.ovp.exe | Installing Visual Studio redistributable10
|
kgxfngke.ovp.exe | Installing Visual Studio redistributable35
|
kgxfngke.ovp.exe | Installing packages50
|