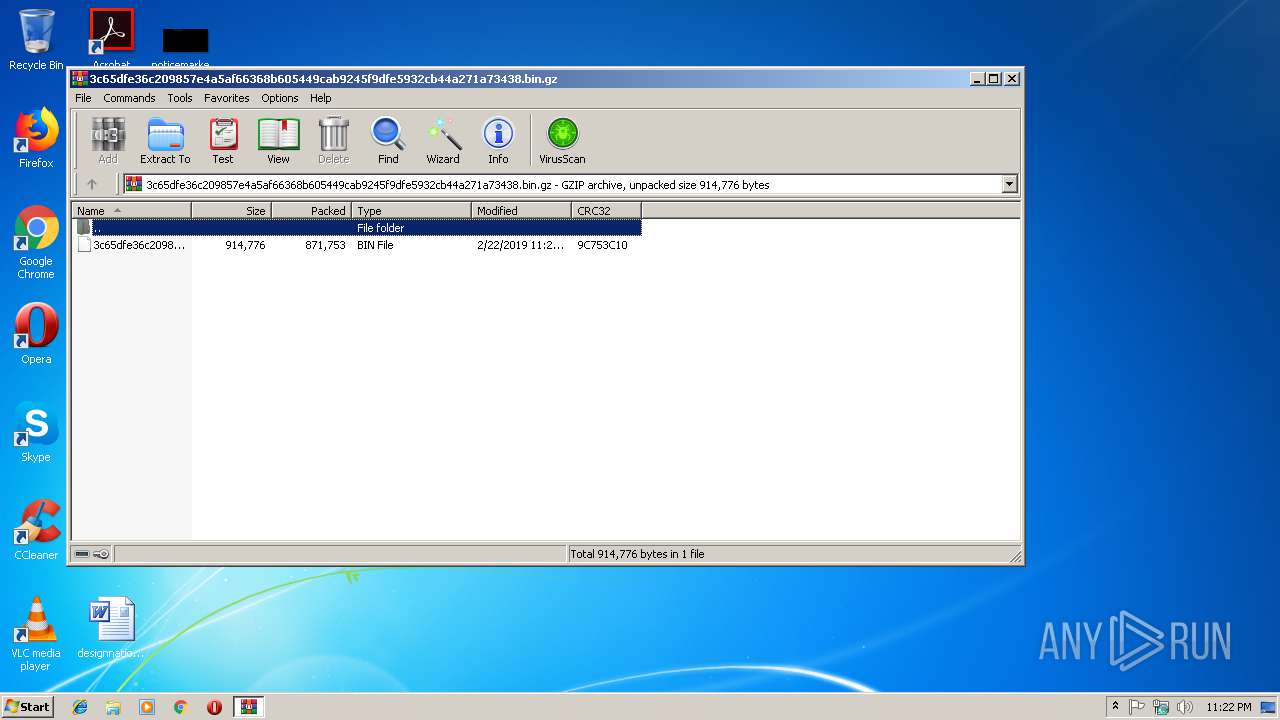
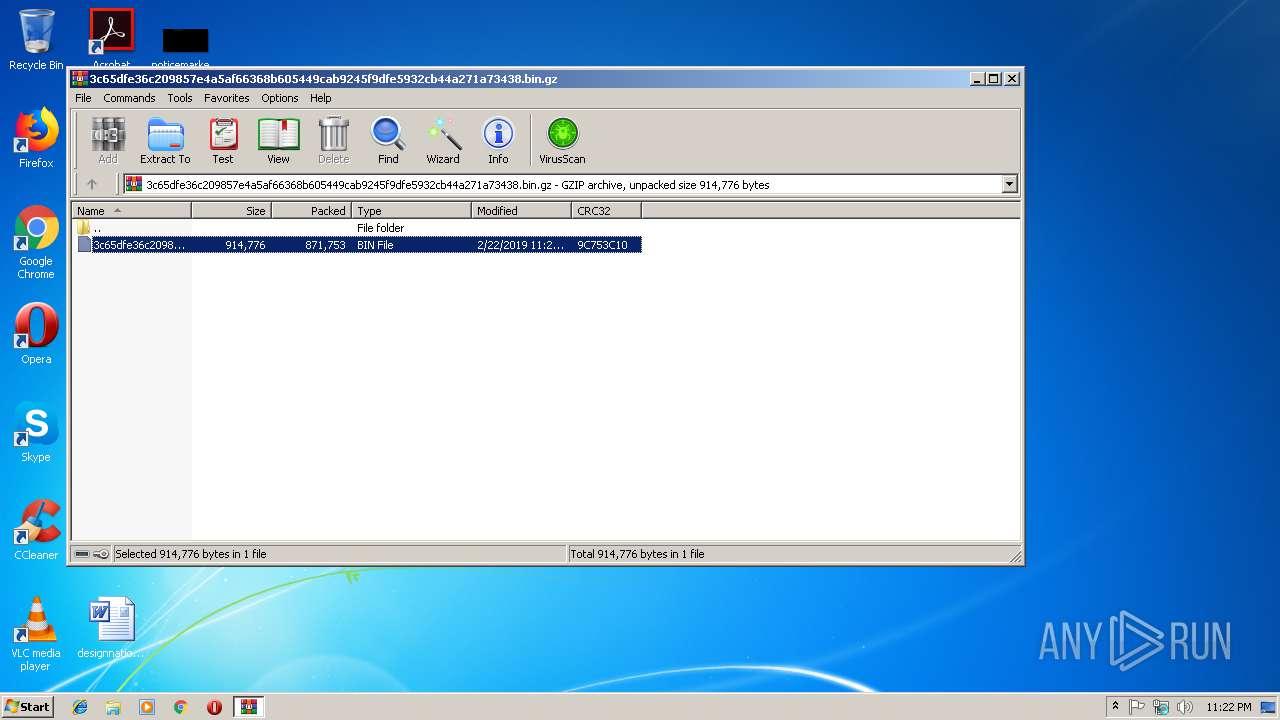
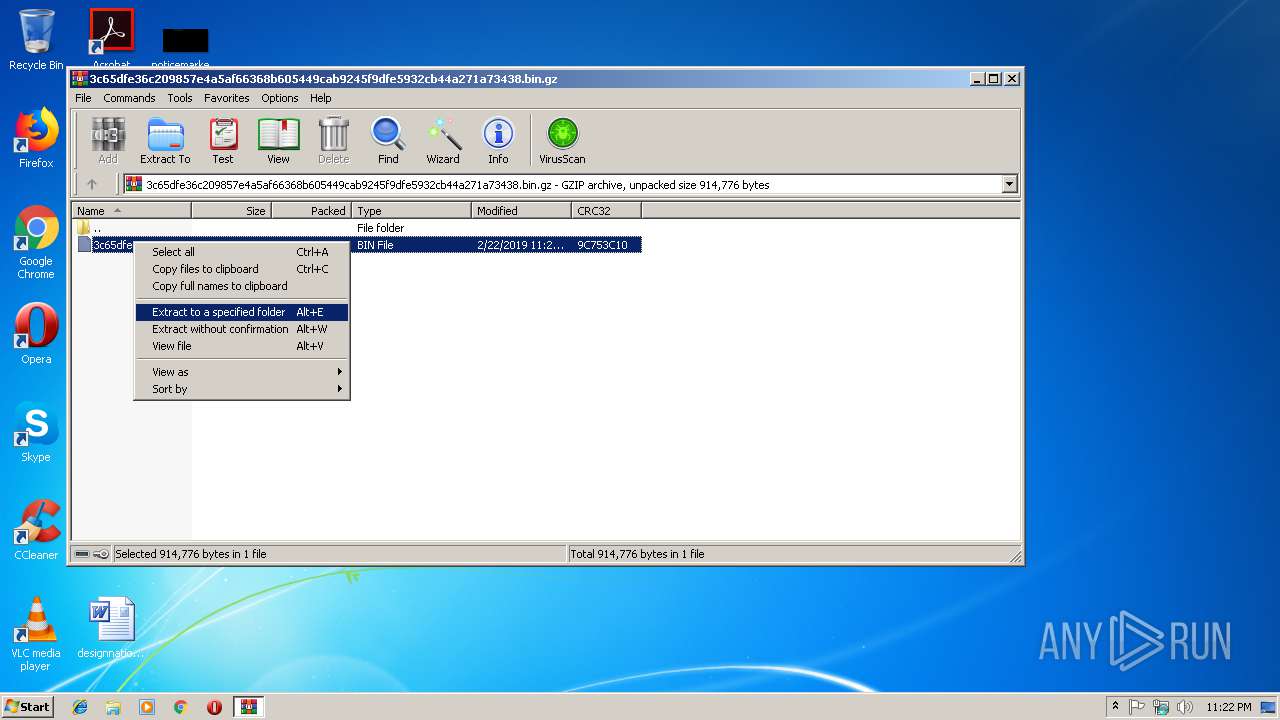
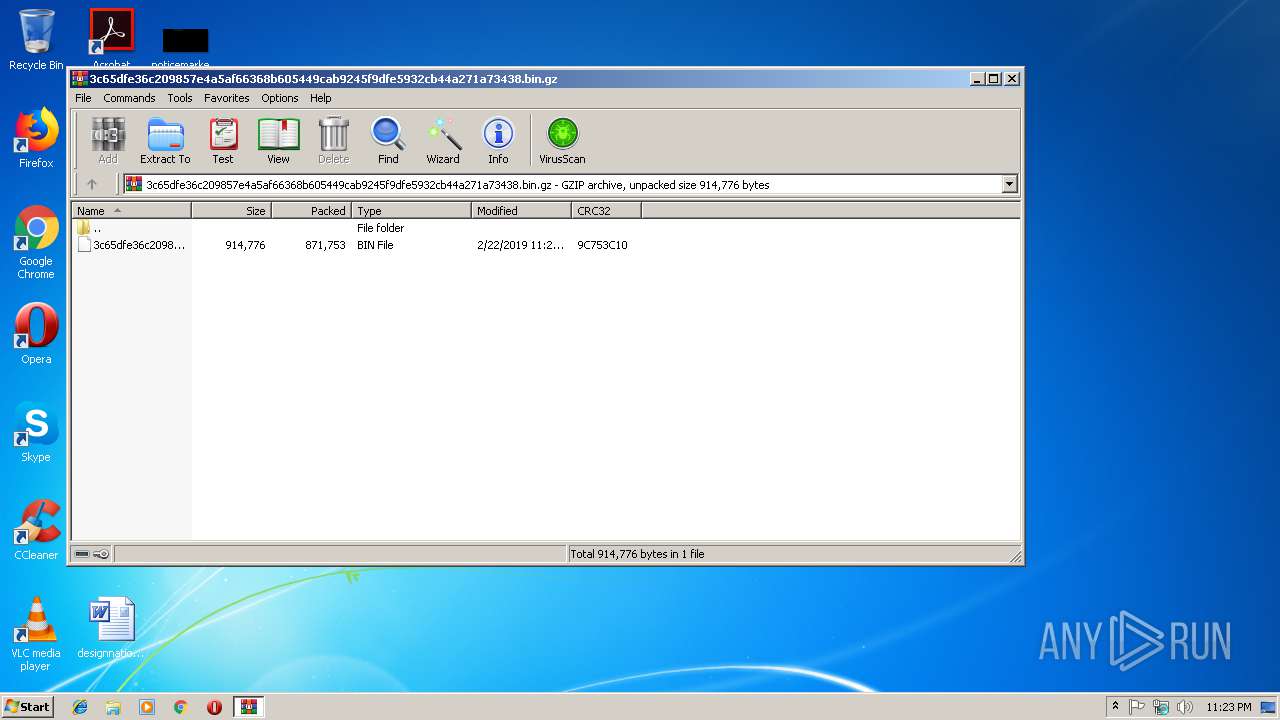
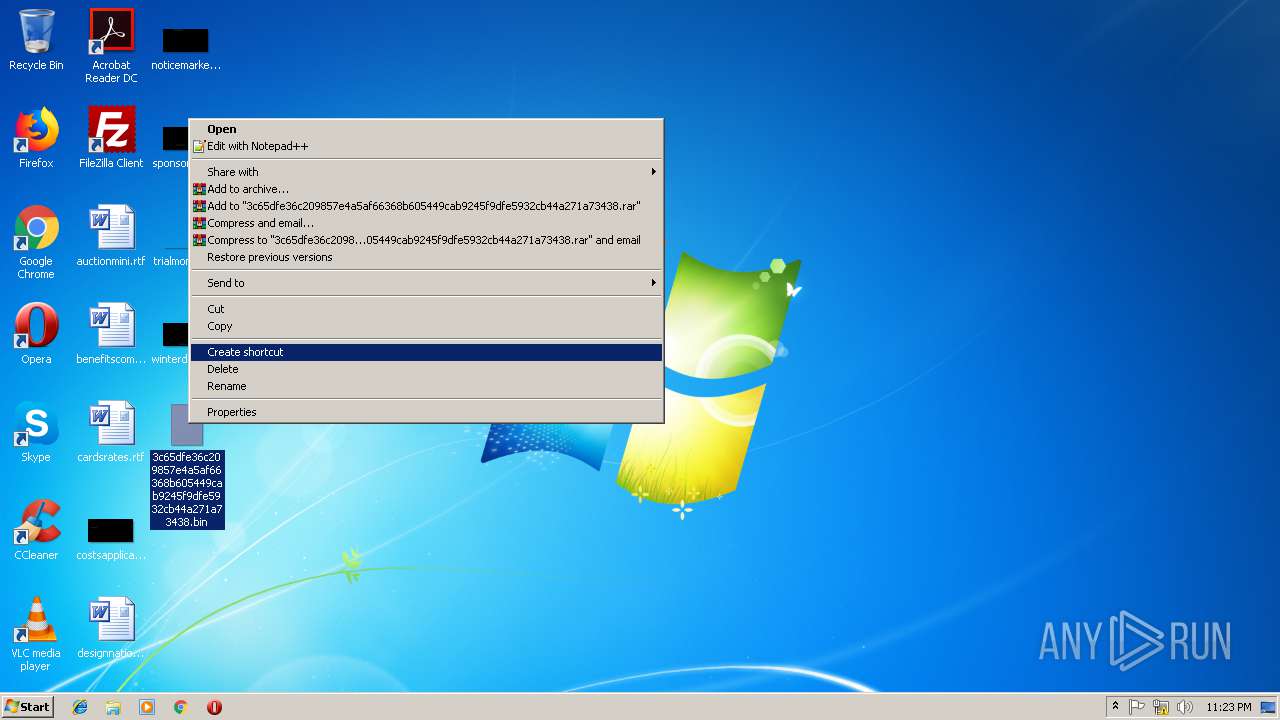
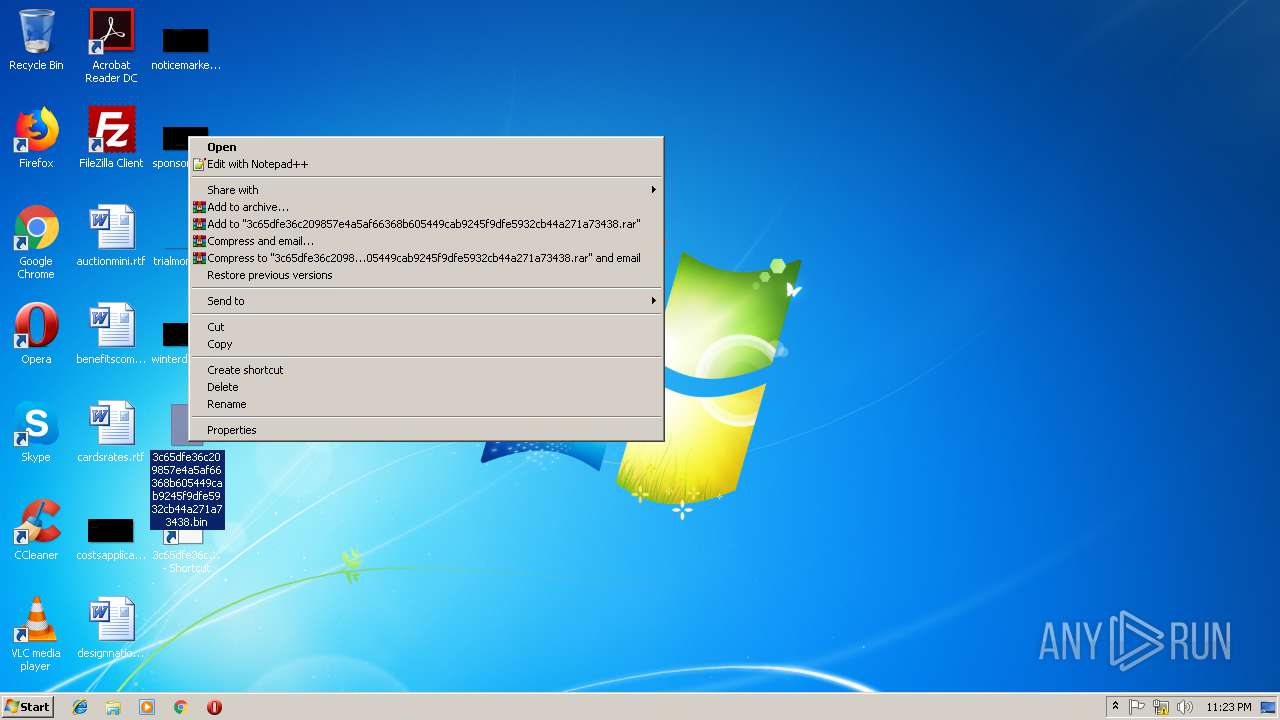
| File name: | 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.bin.gz |
| Full analysis: | https://app.any.run/tasks/12980ade-c12e-445b-af1e-837bbc11f4d5 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2019, 23:22:09 |
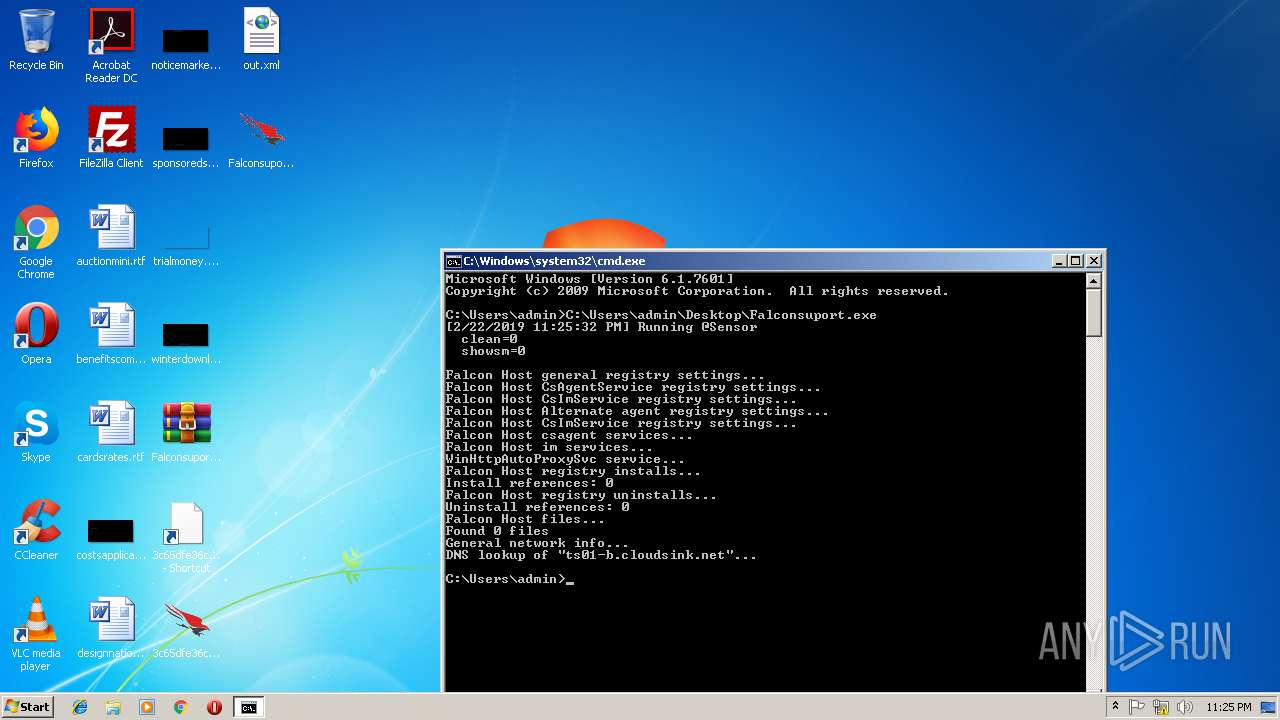
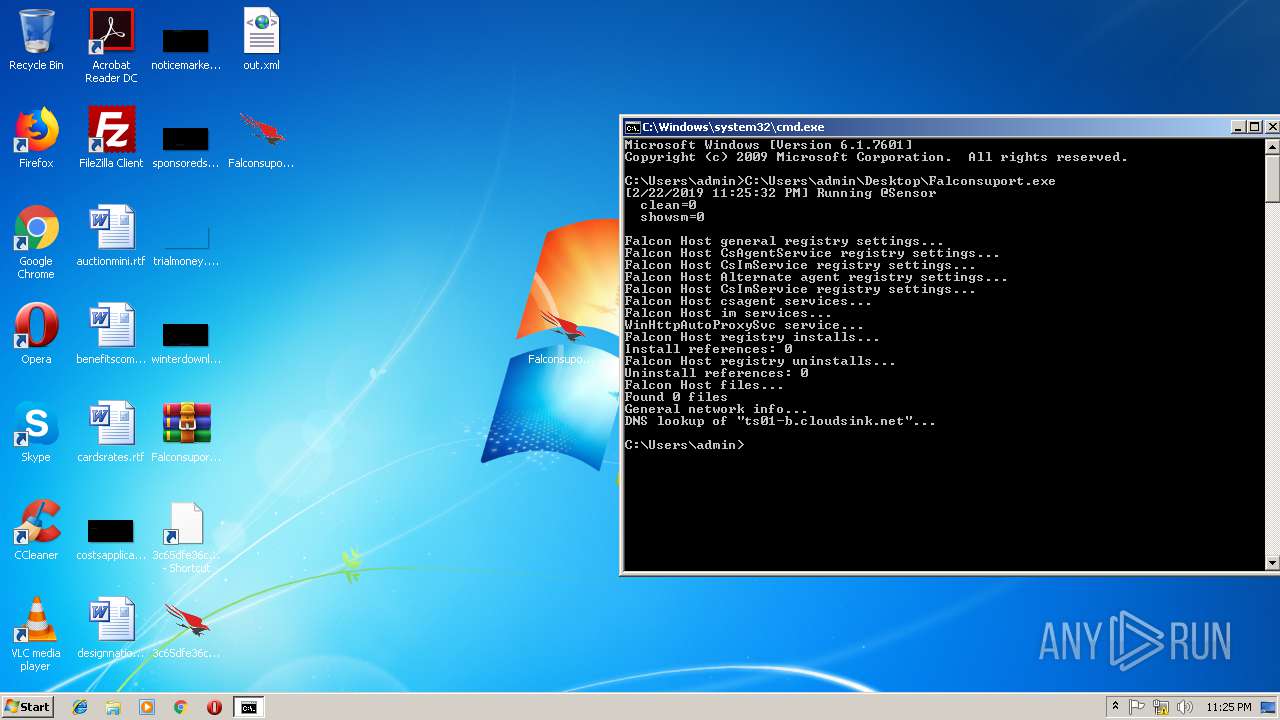
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/gzip |
| File info: | gzip compressed data, max compression, from Unix |
| MD5: | 1D915E6ECE58B162AF6F19BEFCCD51CC |
| SHA1: | CFDF46E5C3BA327AB0CB36CF560FF53CB605D59F |
| SHA256: | A131492971470E2F698BDE7DF6D8F71CCA6E20765B609A02276325302F0B0BC1 |
| SSDEEP: | 24576:kvPBCnE2VstZcYnxquN6I5lwek3nFLD+qDduzdOom:kn+5aMsxr6mlan1D+qDdu4om |
MALICIOUS
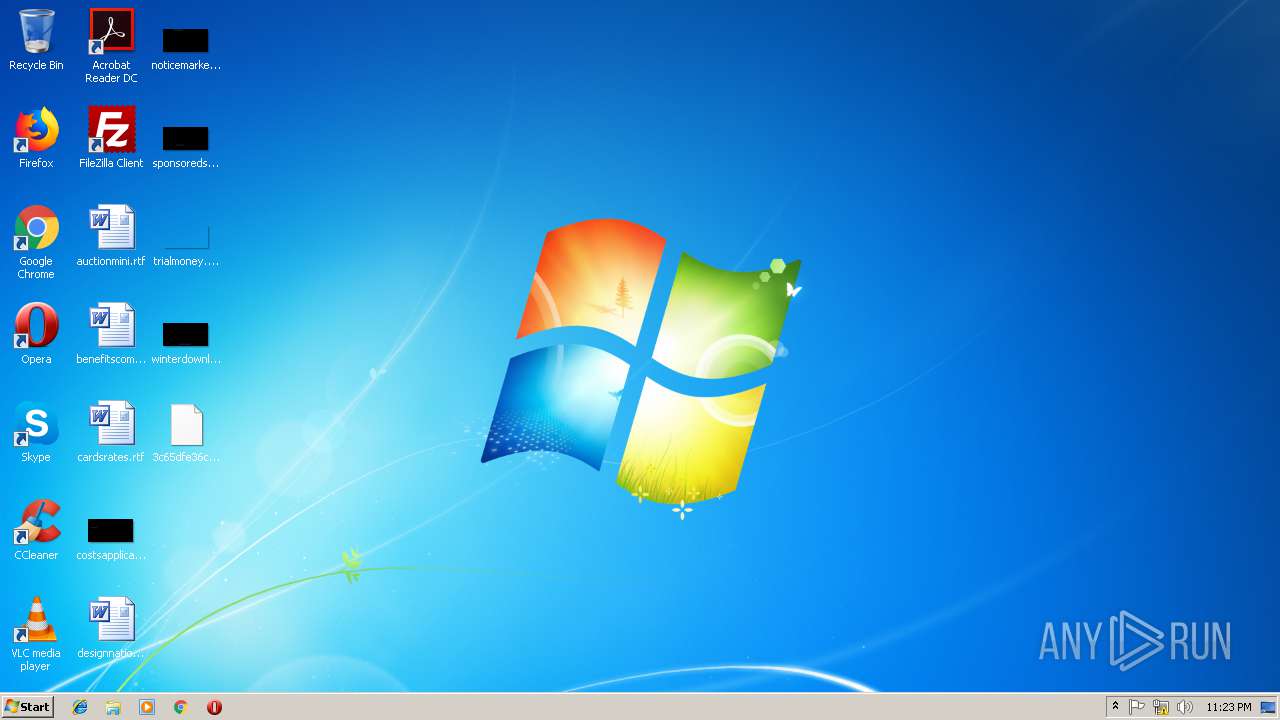
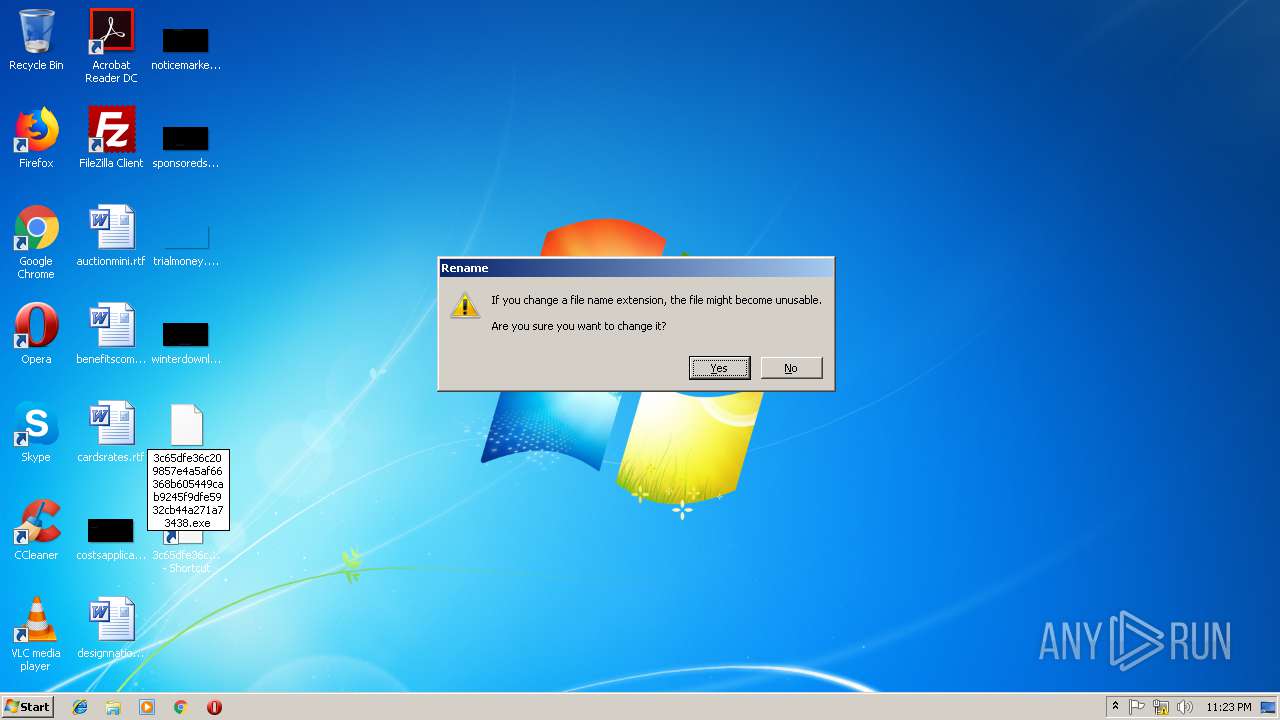
Application was dropped or rewritten from another process
- 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe (PID: 3024)
- 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe (PID: 1016)
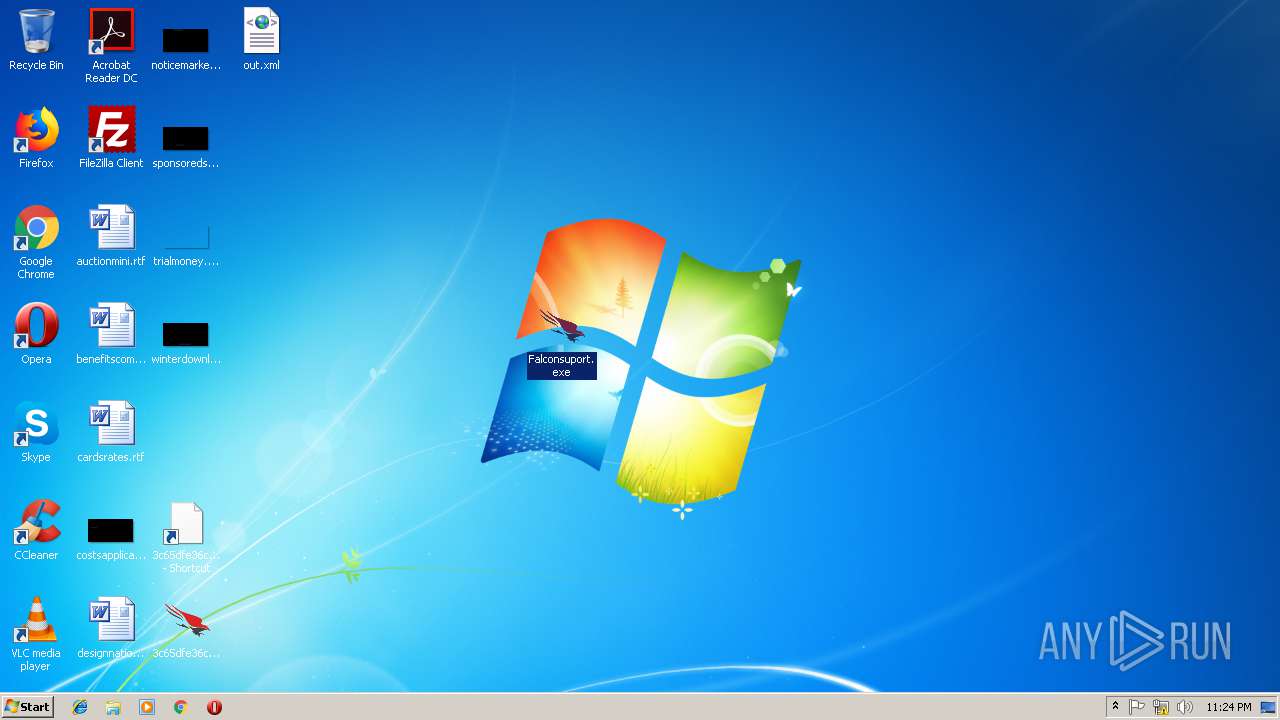
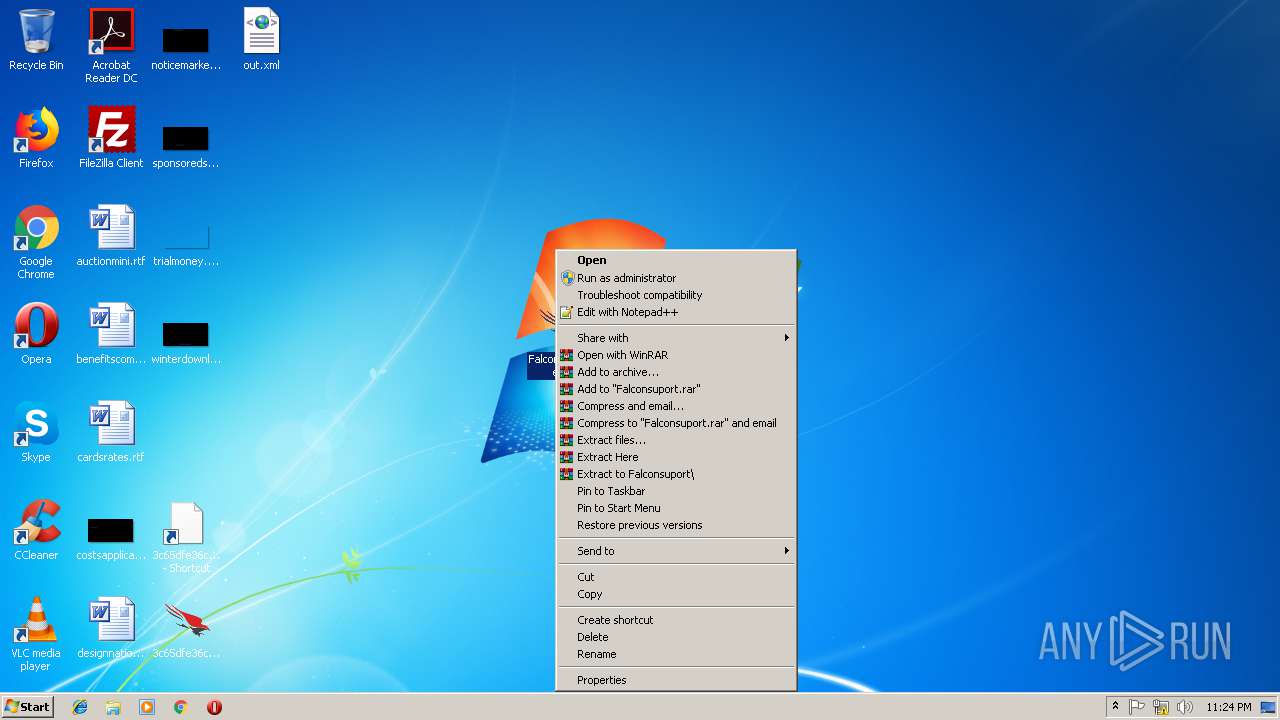
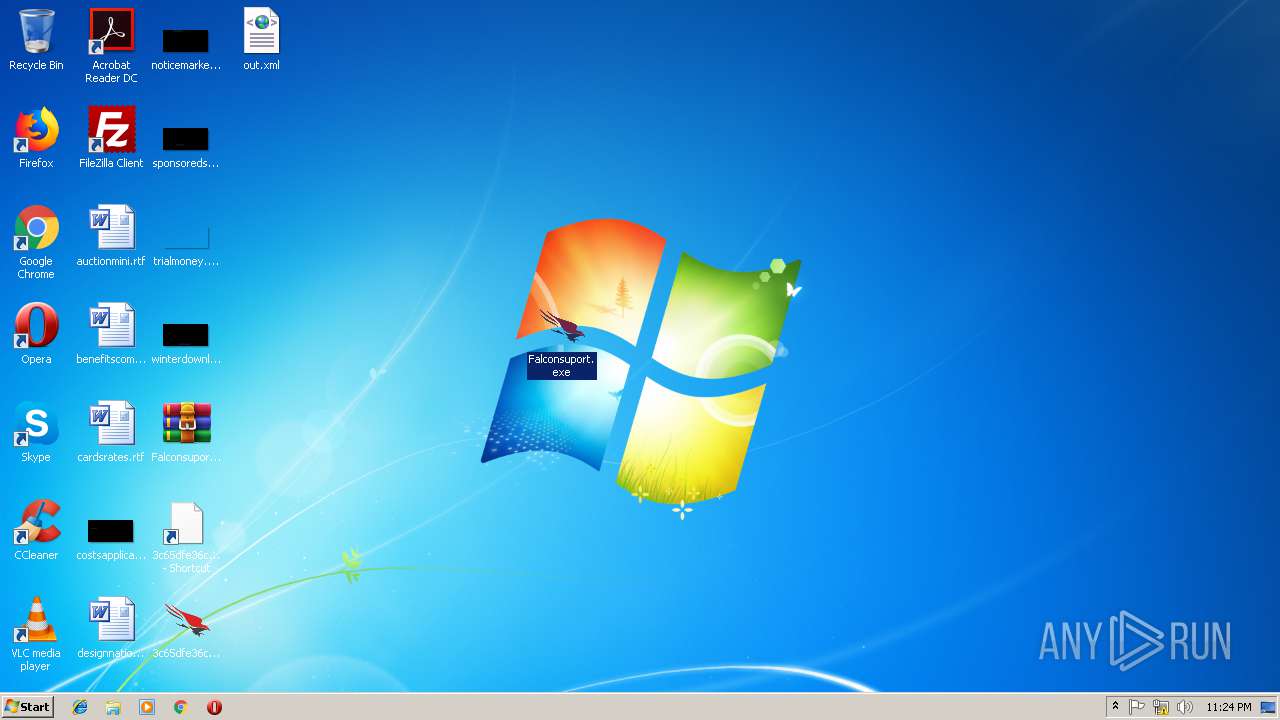
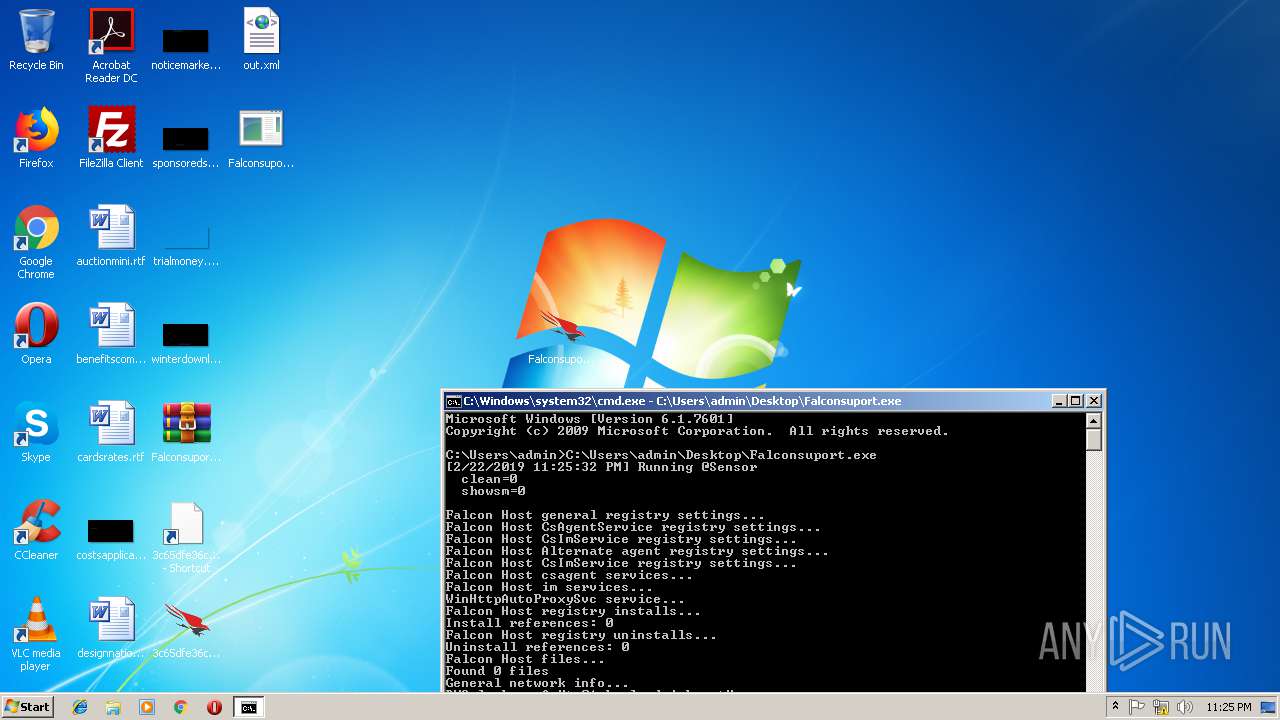
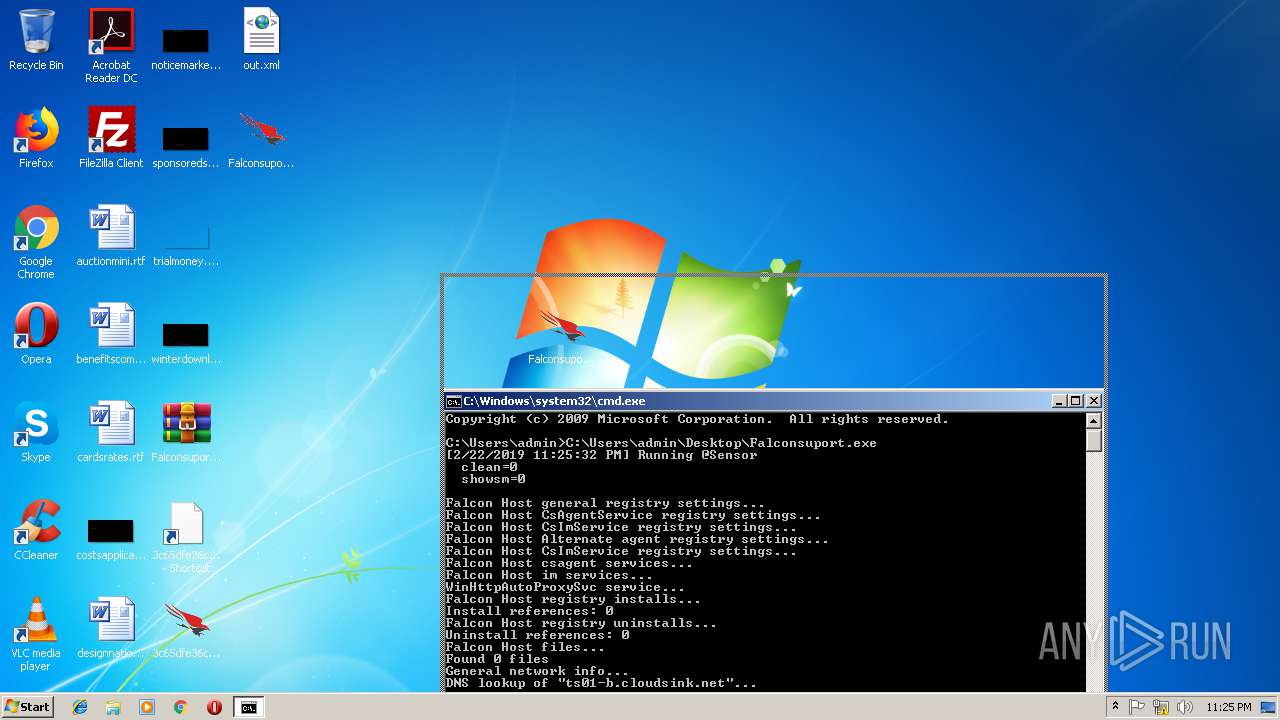
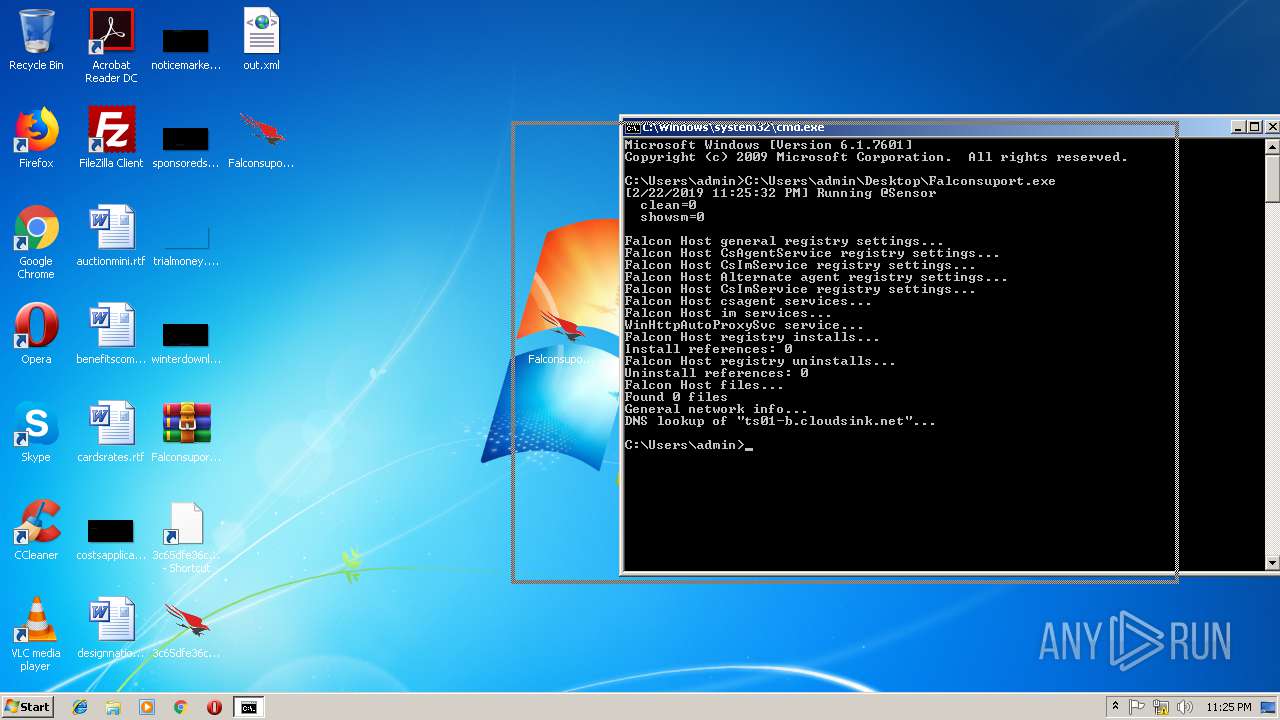
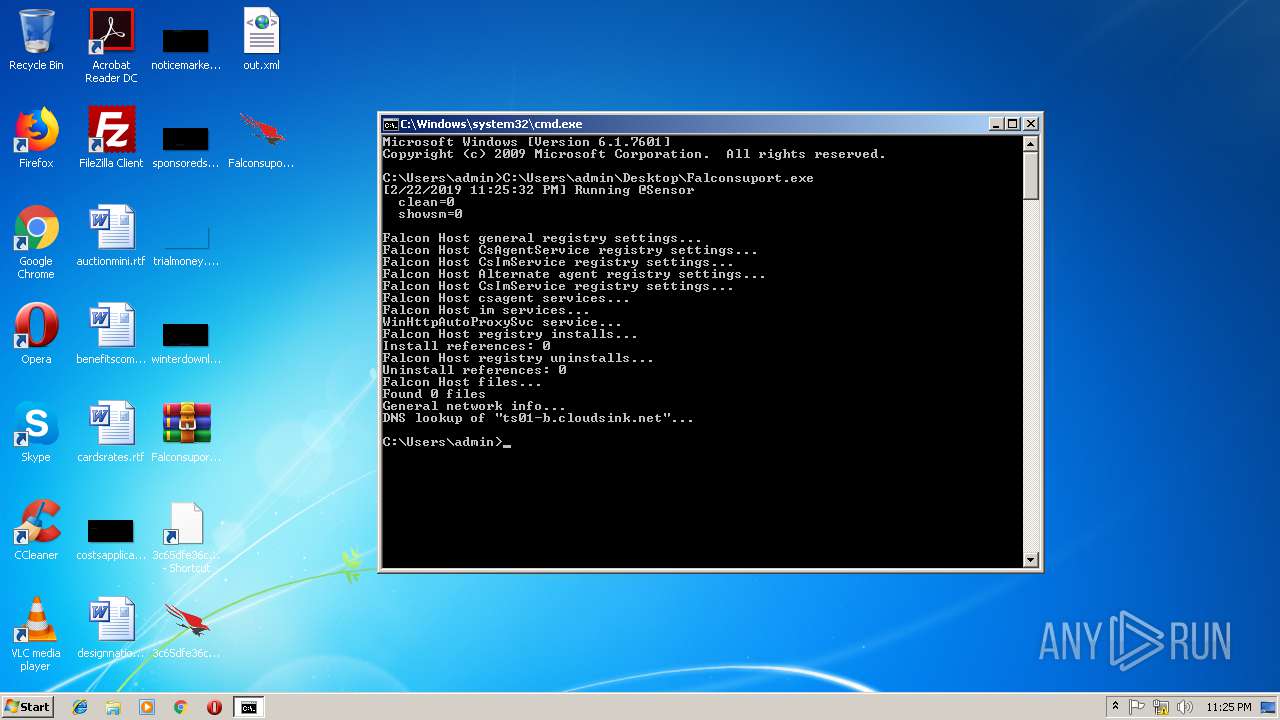
- Falconsuport.exe (PID: 1204)
- Falconsuport32.exe (PID: 3512)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2964)
- 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe (PID: 3024)
- Falconsuport.exe (PID: 1204)
Reads CPU info
- 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe (PID: 3024)
- 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe (PID: 1016)
- Falconsuport.exe (PID: 1204)
- Falconsuport32.exe (PID: 3512)
Reads the date of Windows installation
- 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe (PID: 1016)
- Falconsuport32.exe (PID: 3512)
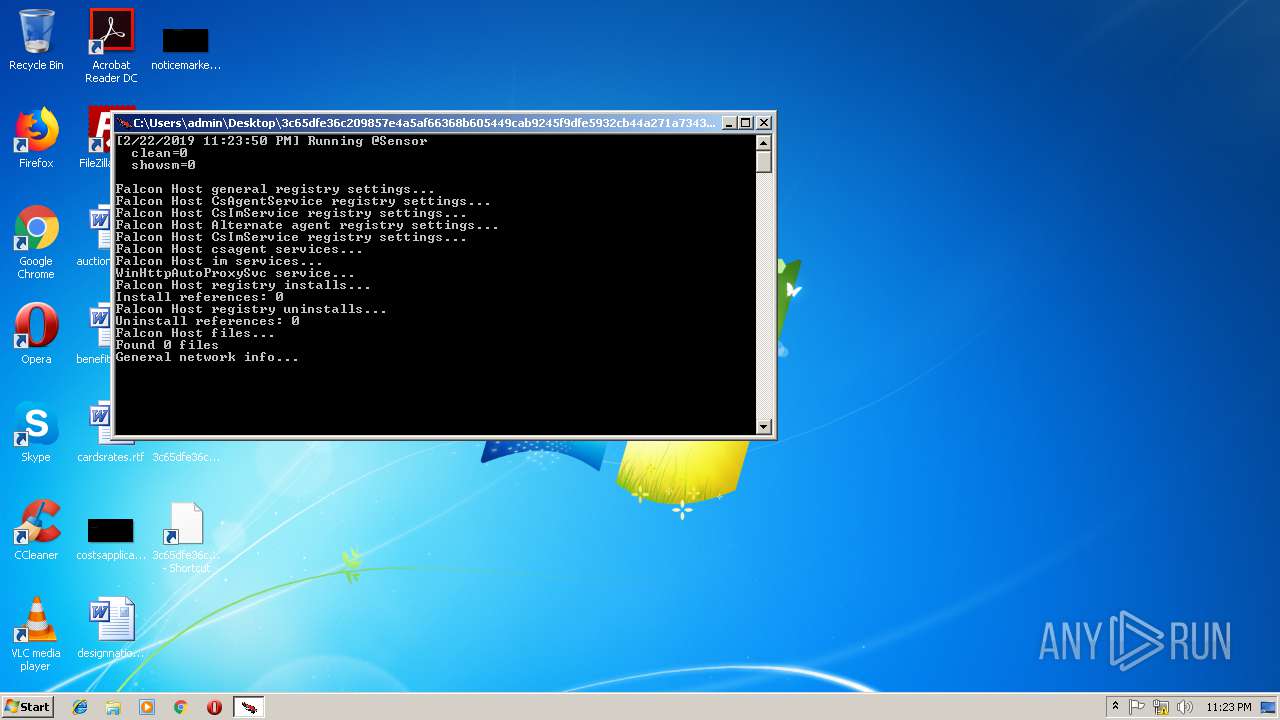
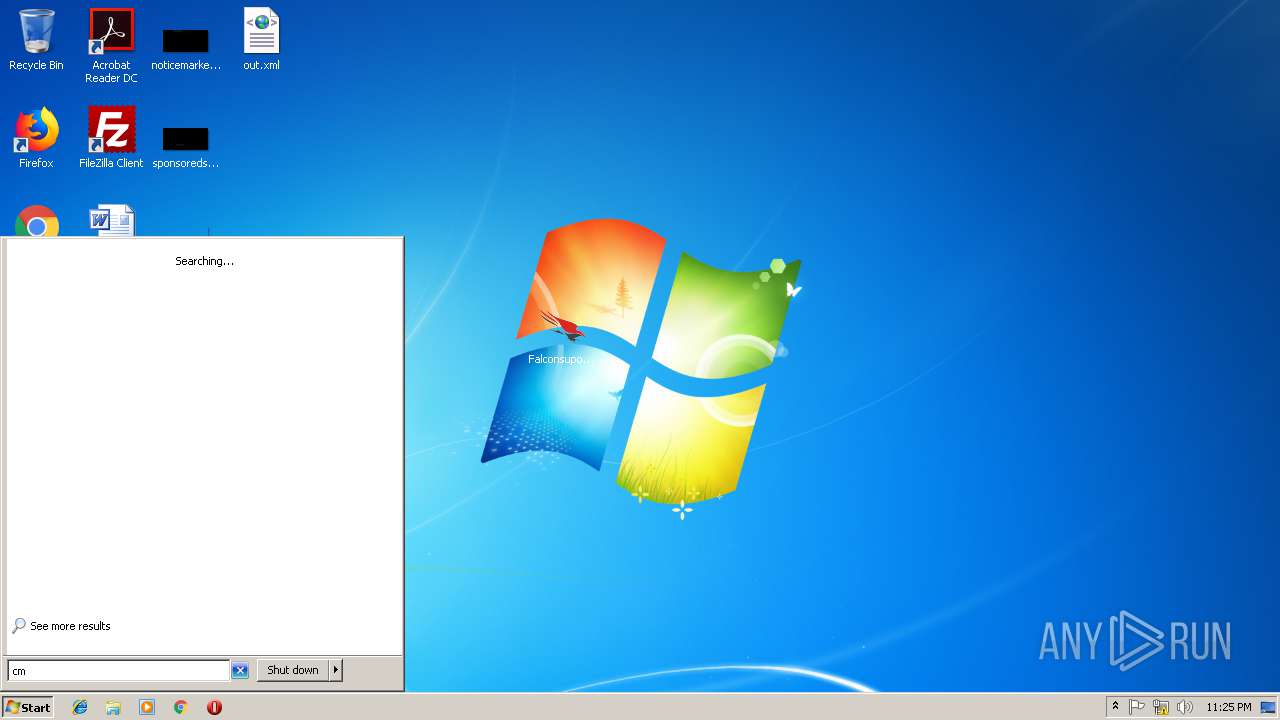
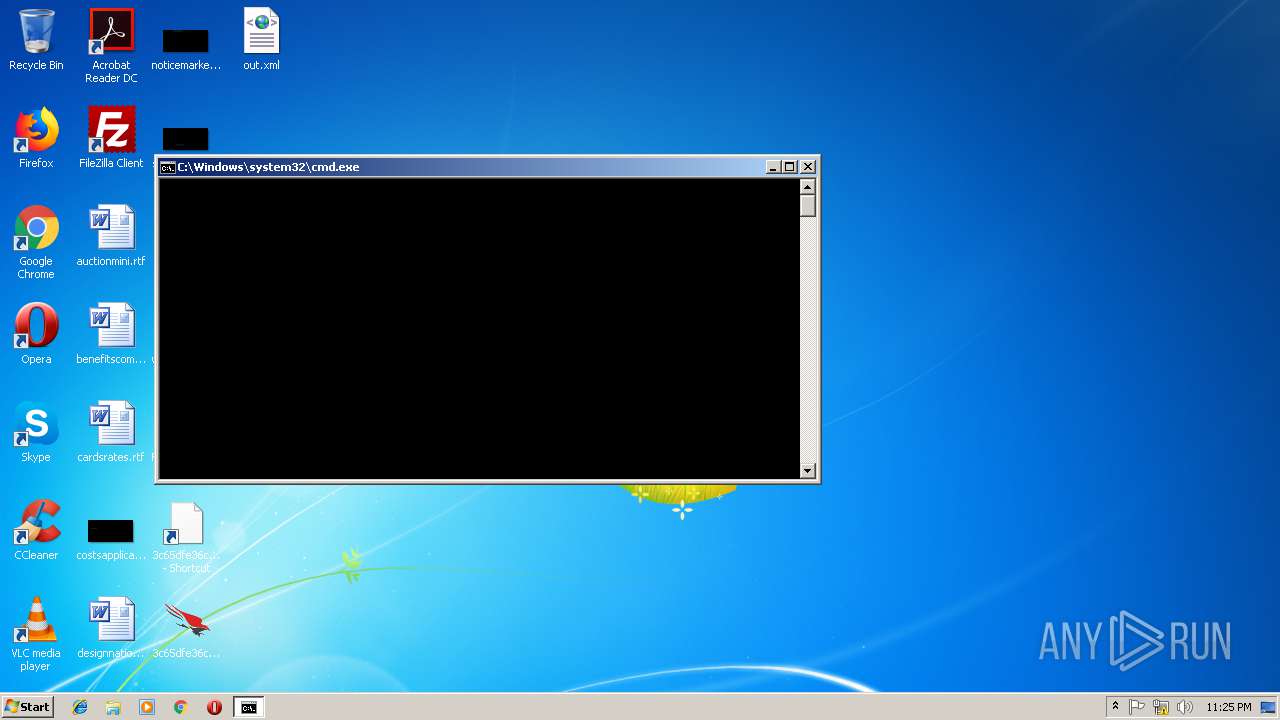
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 2948)
- cmd.exe (PID: 2708)
Starts CMD.EXE for commands execution
- 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe (PID: 1016)
- Falconsuport32.exe (PID: 3512)
INFO
Dropped object may contain Bitcoin addresses
- 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe (PID: 3024)
- Falconsuport.exe (PID: 1204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | (none) |
| ModifyDate: | 0000:00:00 00:00:00 |
| ExtraFlags: | Maximum Compression |
| OperatingSystem: | Unix |
Total processes
52
Monitored processes
15
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | "C:\Users\admin\Desktop\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe" -# "C:\Users\admin\Desktop\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe" -i "C:\Users\admin\AppData\Local\Temp\cs58E300C464DD2949BFC234E193BA03DD.txt" | C:\Users\admin\Desktop\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe | — | 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe | |||||||||||
User: admin Company: CrowdStrike, Inc. Integrity Level: MEDIUM Description: CrowdStrike Static Host Data Collection Tool Exit code: 0 Version: 1.0.5.43 Modules
| |||||||||||||||
| 1204 | C:\Users\admin\Desktop\Falconsuport.exe | C:\Users\admin\Desktop\Falconsuport.exe | cmd.exe | ||||||||||||
User: admin Company: CrowdStrike, Inc. Integrity Level: MEDIUM Description: CrowdStrike Static Host Data Collection Tool Exit code: 0 Version: 1.0.5.43 Modules
| |||||||||||||||
| 2444 | C:\Windows\system32\cmd.exe /c route print | C:\Windows\system32\cmd.exe | — | Falconsuport32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2708 | C:\Windows\system32\cmd.exe /c ipconfig /displaydns | C:\Windows\system32\cmd.exe | — | Falconsuport32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
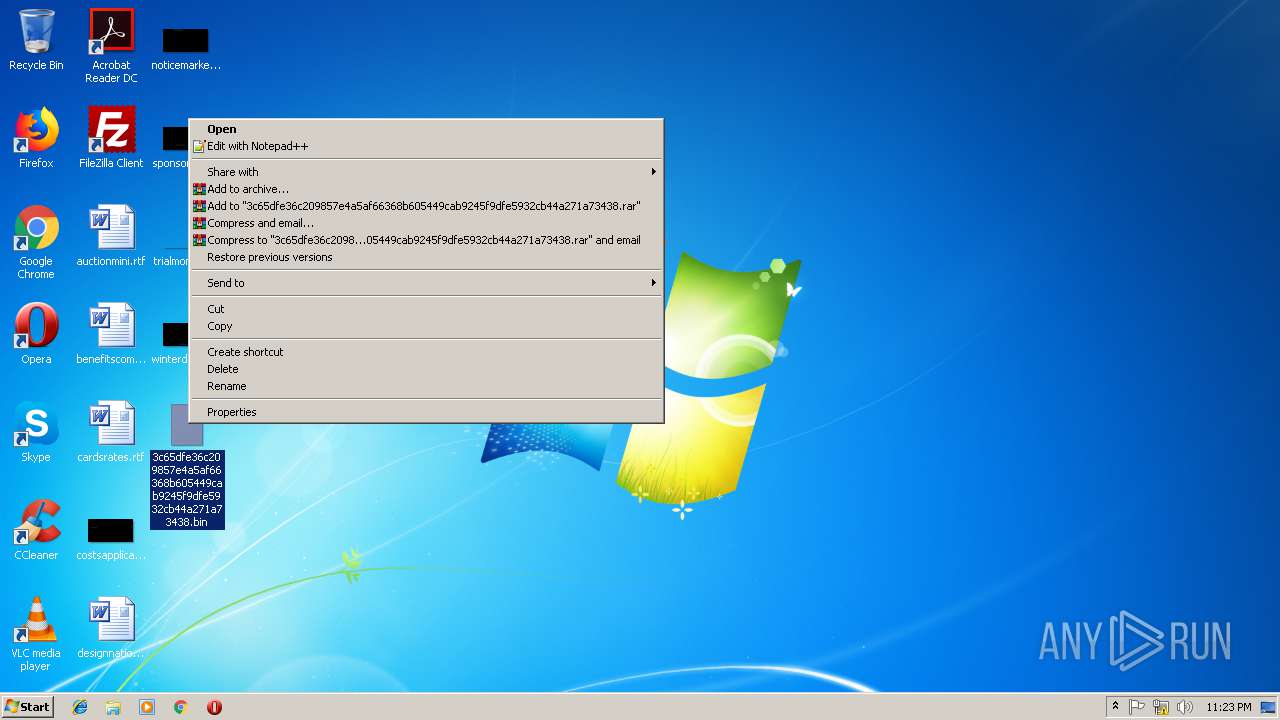
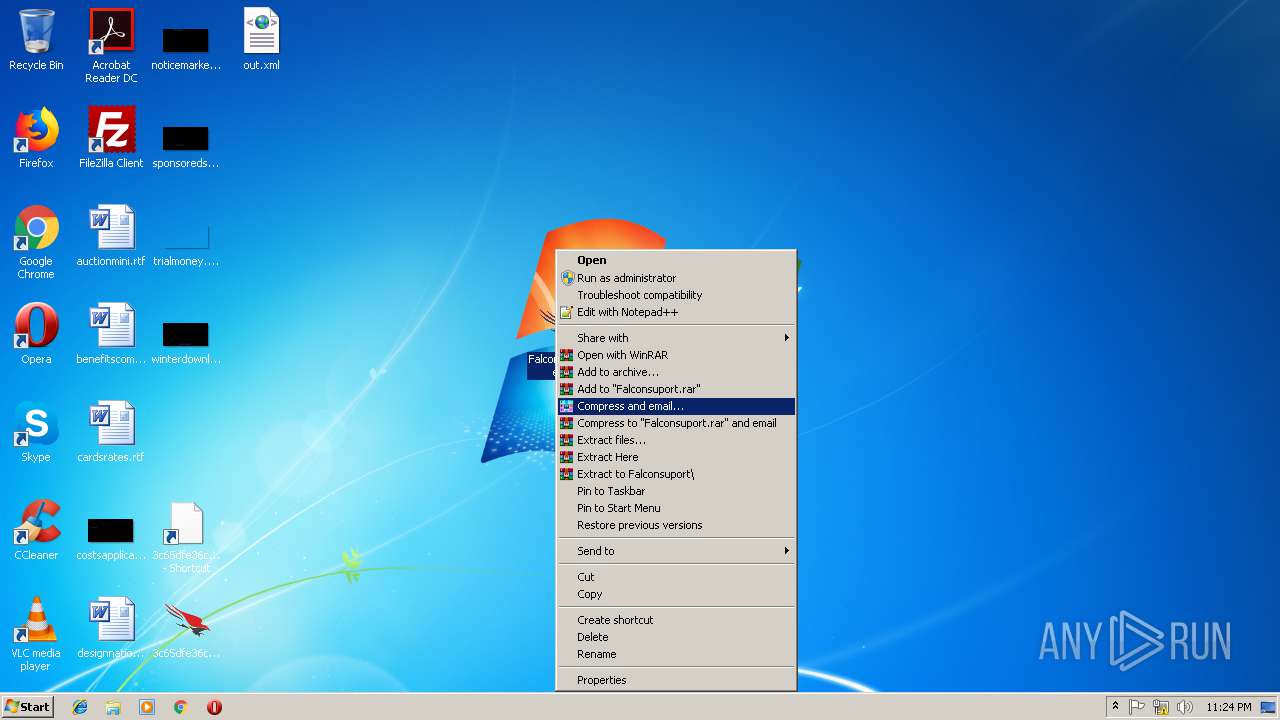
| 2872 | "C:\Program Files\WinRAR\WinRAR.exe" a -ep1 -scul -r0 -iext -- Falconsuport.rar C:\Users\admin\Desktop\Falconsuport.exe | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2896 | ipconfig /displaydns | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | C:\Windows\system32\cmd.exe /c ipconfig /displaydns | C:\Windows\system32\cmd.exe | — | 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
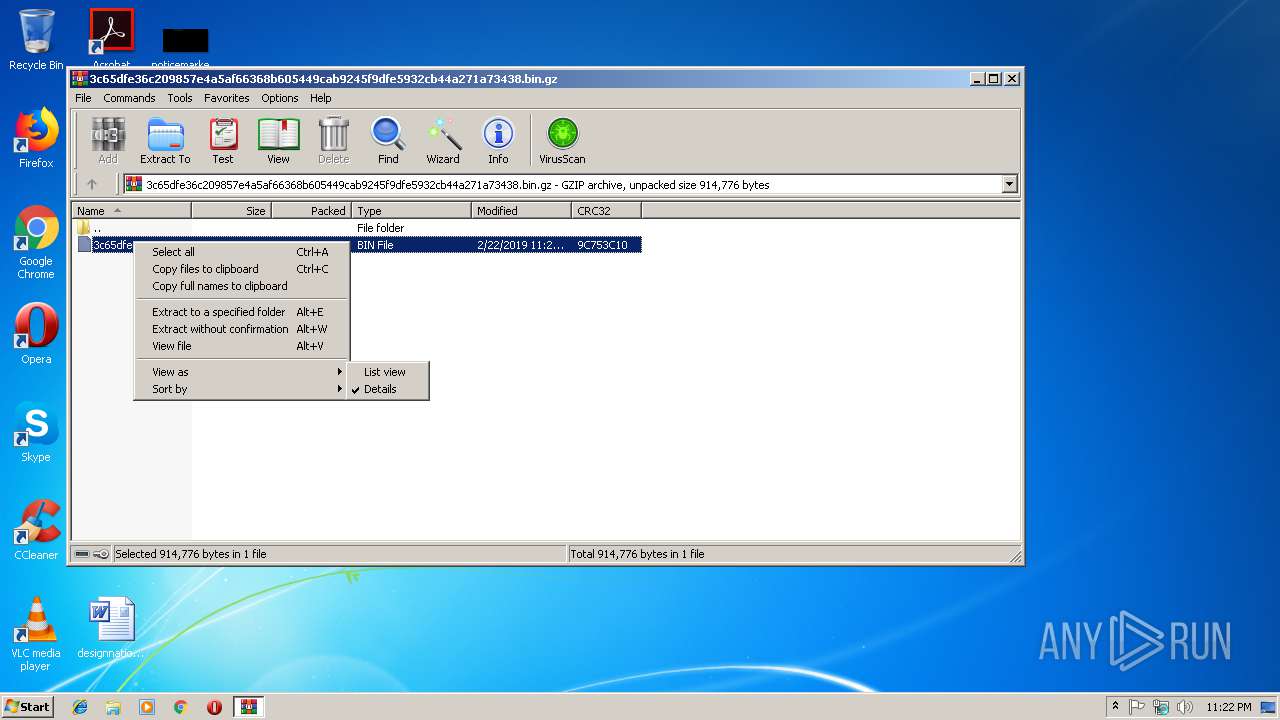
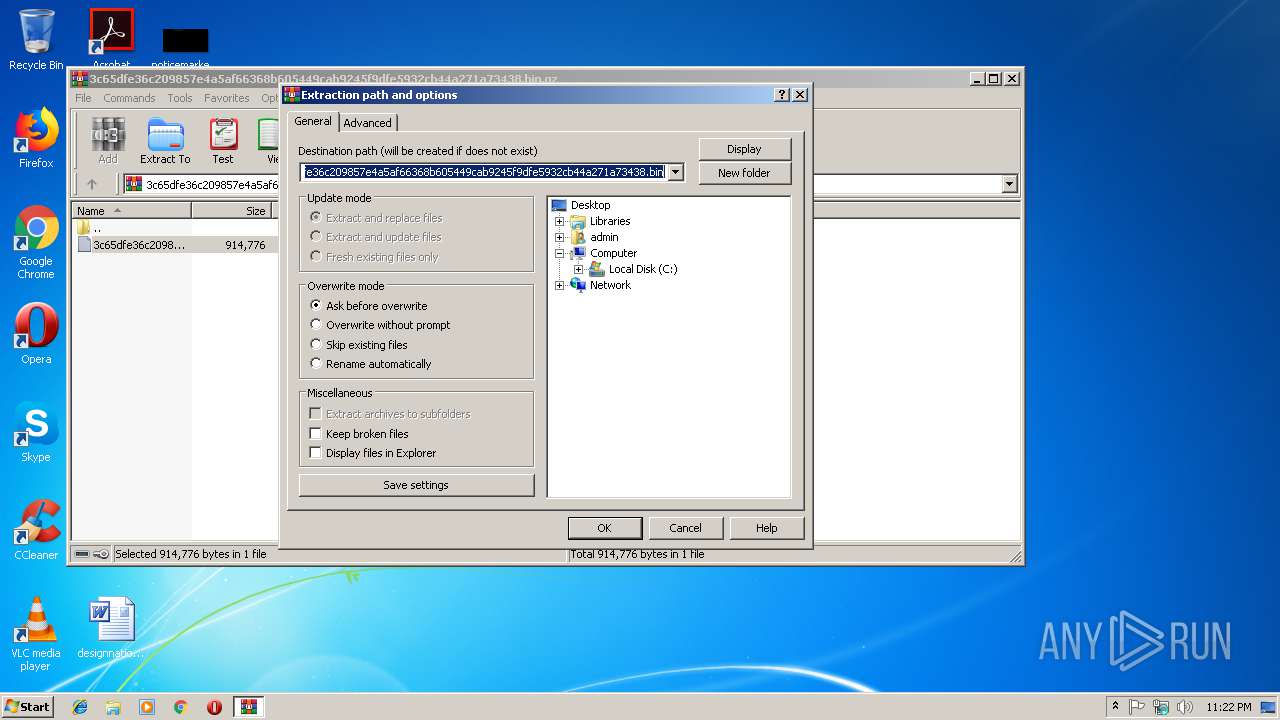
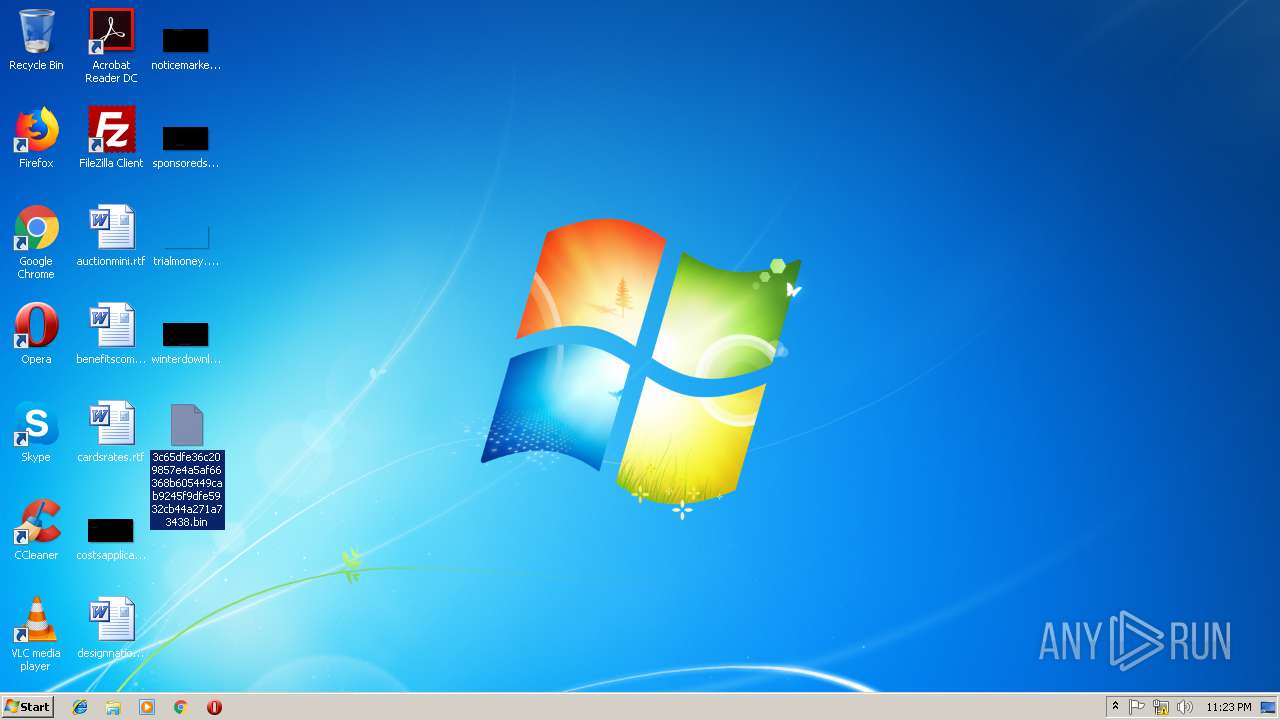
| 2964 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.bin.gz" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\Desktop\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe" | C:\Users\admin\Desktop\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe | explorer.exe | ||||||||||||
User: admin Company: CrowdStrike, Inc. Integrity Level: MEDIUM Description: CrowdStrike Static Host Data Collection Tool Exit code: 0 Version: 1.0.5.43 Modules
| |||||||||||||||
| 3180 | ipconfig /displaydns | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
642
Read events
591
Write events
51
Delete events
0
Modification events
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.bin.gz | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
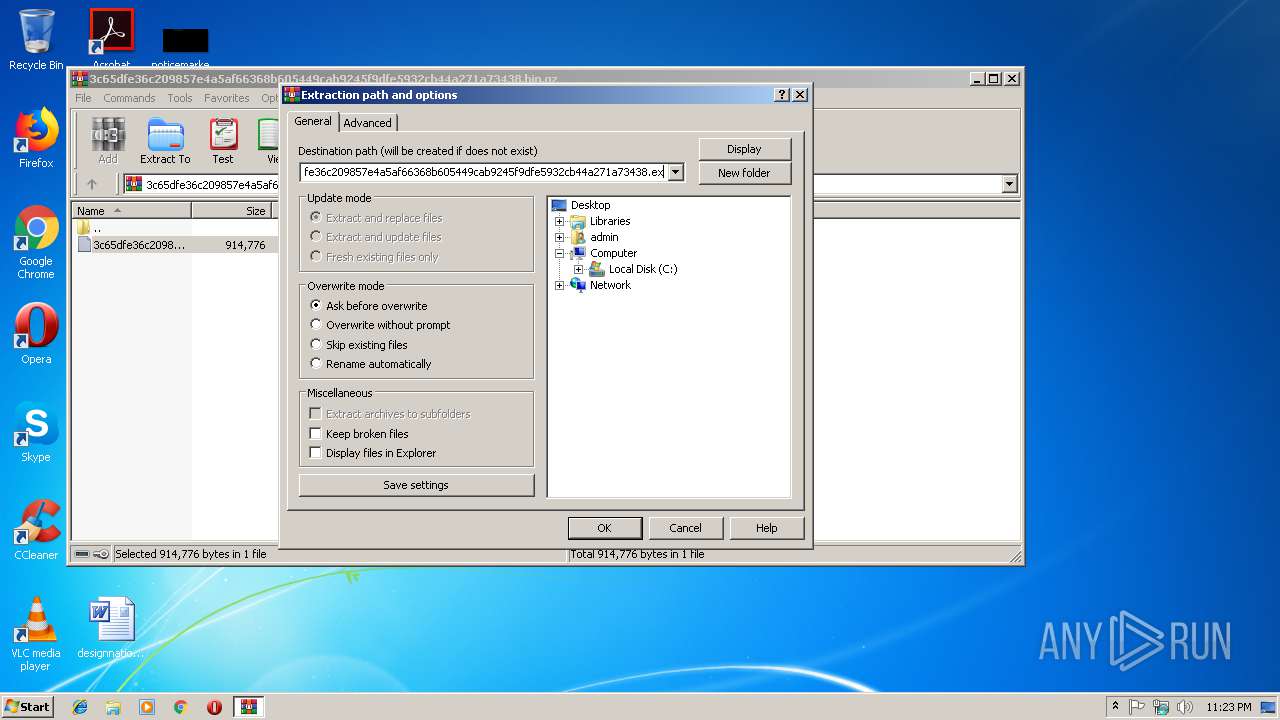
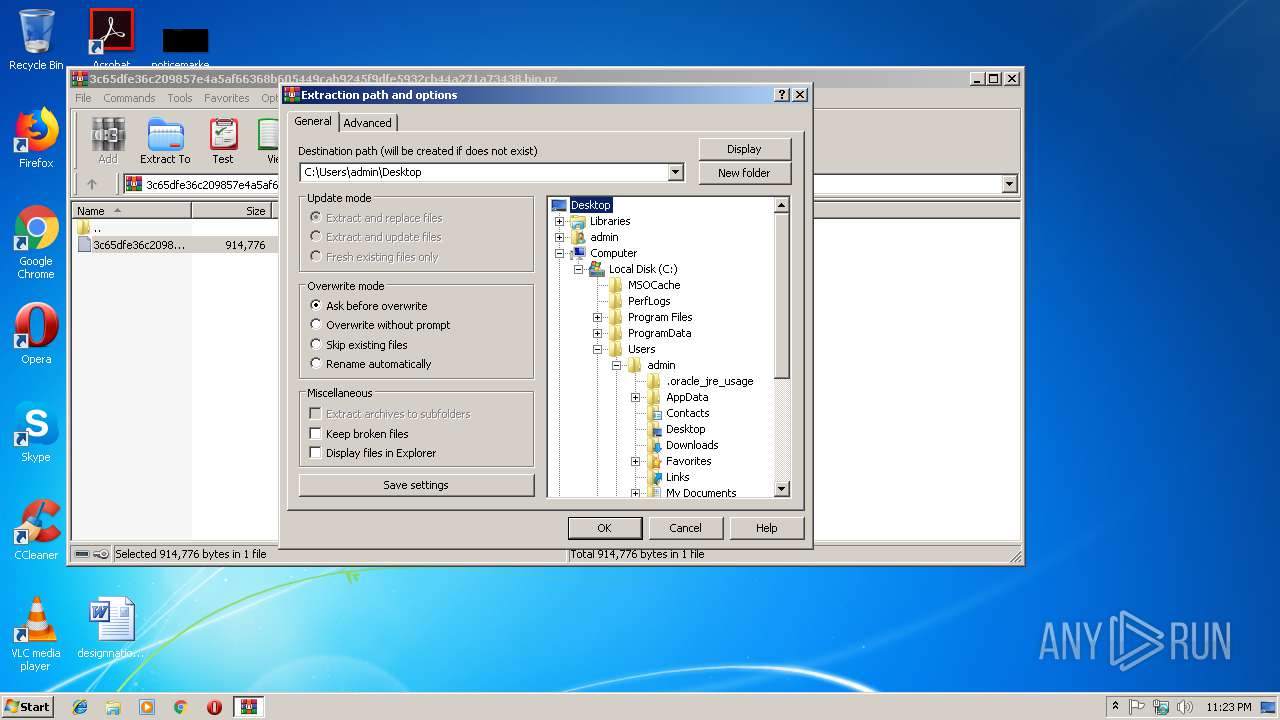
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
3
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe | C:\Users\admin\AppData\Local\Temp\csF3F25EB4E9E9B840A8C4A30A52F5B112.tmp | — | |
MD5:— | SHA256:— | |||
| 1204 | Falconsuport.exe | C:\Users\admin\AppData\Local\Temp\csE85F68C6C833CA49835C54BDCB82F391.tmp | — | |
MD5:— | SHA256:— | |||
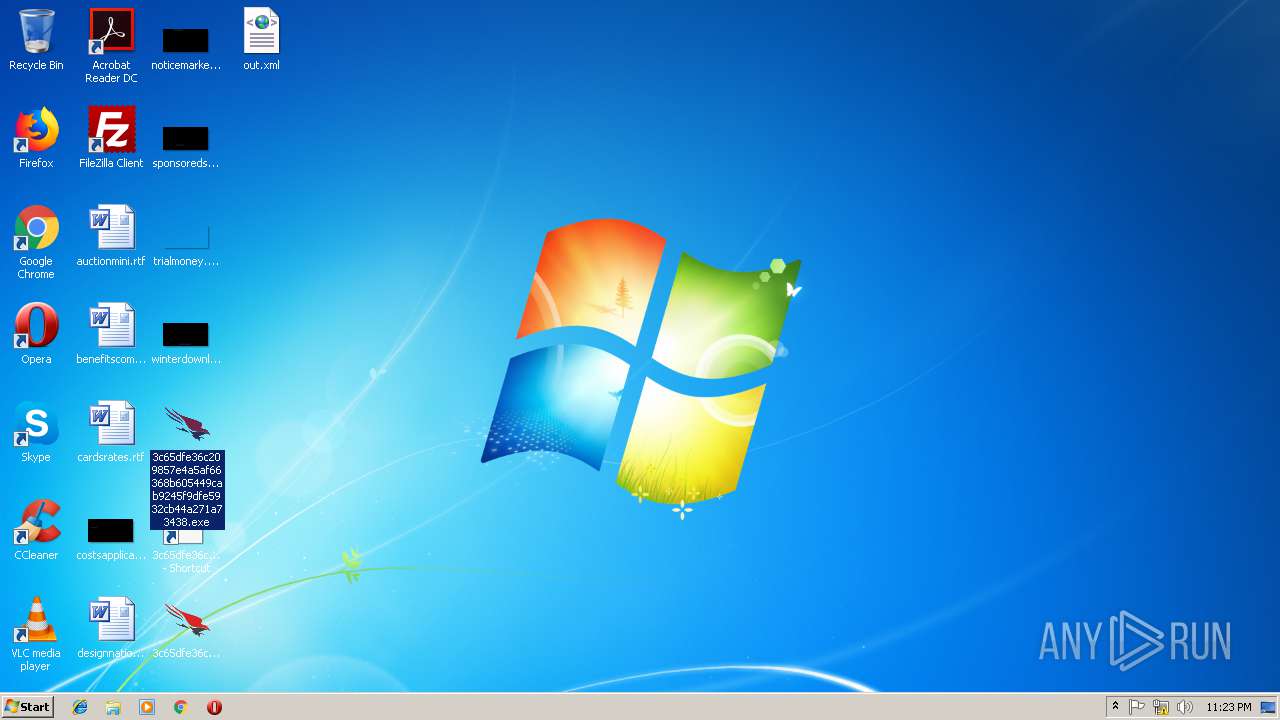
| 3512 | Falconsuport32.exe | C:\Users\admin\out.xml | xml | |
MD5:— | SHA256:— | |||
| 1016 | 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe | C:\Users\admin\Desktop\out.xml | xml | |
MD5:— | SHA256:— | |||
| 2964 | WinRAR.exe | C:\Users\admin\Desktop\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.bin | executable | |
MD5:— | SHA256:— | |||
| 3024 | 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe | C:\Users\admin\AppData\Local\Temp\cs58E300C464DD2949BFC234E193BA03DD.txt | text | |
MD5:— | SHA256:— | |||
| 2872 | WinRAR.exe | C:\Users\admin\Desktop\Falconsuport.rar | compressed | |
MD5:— | SHA256:— | |||
| 1204 | Falconsuport.exe | C:\Users\admin\AppData\Local\Temp\csD9C6D270C38C8248A46B5C63866B7E55.txt | text | |
MD5:— | SHA256:— | |||
| 1204 | Falconsuport.exe | C:\Users\admin\Desktop\Falconsuport32.exe | executable | |
MD5:— | SHA256:— | |||
| 3024 | 3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a73438.exe | C:\Users\admin\Desktop\3c65dfe36c209857e4a5af66368b605449cab9245f9dfe5932cb44a271a7343832.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
ts01-b.cloudsink.net |
| unknown |