| URL: | https://covid19.auth-verify.com/XQjgvWU9MTTJHem1pSnhoTFEzVVhaczc1d2txd1Q0bkt1WmJlNys0NWgzK2wwU0hJRzlsbDBDQ0tNbFlJSXNzRHNoTkJXWXlBM2xmWnZKMDJMOWFqTnE2MjA0dVRjUFRLNXlxQ29hLzVrcXUvejdlOXpHOXl1RmhmMDBWd25lYTlQYTVrZ2VDeDhRQ2tia0VhdVA2US9zTFR0NUllQ2NzRmhuQ2h4am81VFROTXp4N2xJNFlIdkFFNTFzaG5GQStaUmZYZWYxRT0tLTFPZzZRc1ViYUVJWjJ0amUtLXFzVlh0cWEycGZ0QWJrTy9Fa3R2RlE9PQ==?cid=347115901 |
| Full analysis: | https://app.any.run/tasks/588aa31b-9aee-4cc3-9ad2-dcc768196713 |
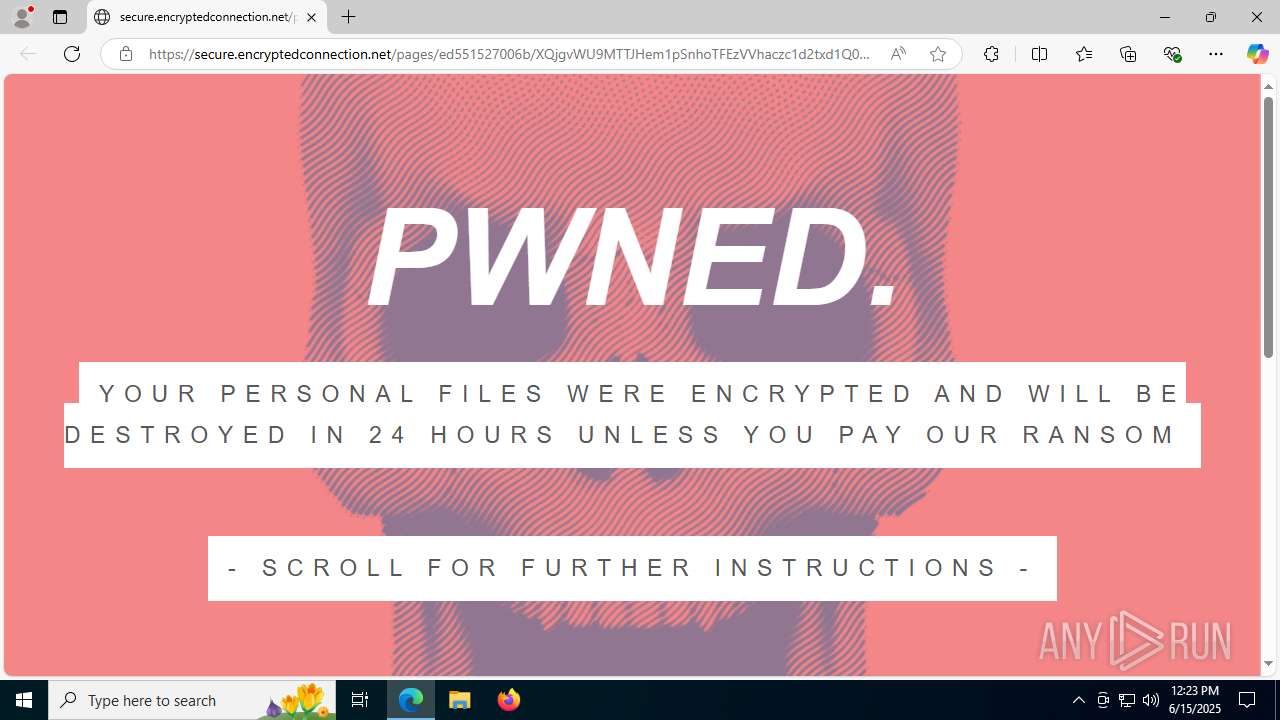
| Verdict: | Malicious activity |
| Analysis date: | June 15, 2025, 12:23:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C60BF87BE803DADE0E57ABD8E307E5F3 |
| SHA1: | 90DBB0C116C507DB5DC631D1679FF1F7B6B6AD01 |
| SHA256: | A121B4D52748343EF1690AB381ECF7C0D63AA7194CADBB16B856CBD99DB2ADC8 |
| SSDEEP: | 6:2UTHd37Imn5JDgRDMoBNLF2OqGa6FkzutG2AVh7RNchjWAWVETyyJtjxh2A49U:2CN7IAoAoBxqukuRExc8g7x89U |
MALICIOUS
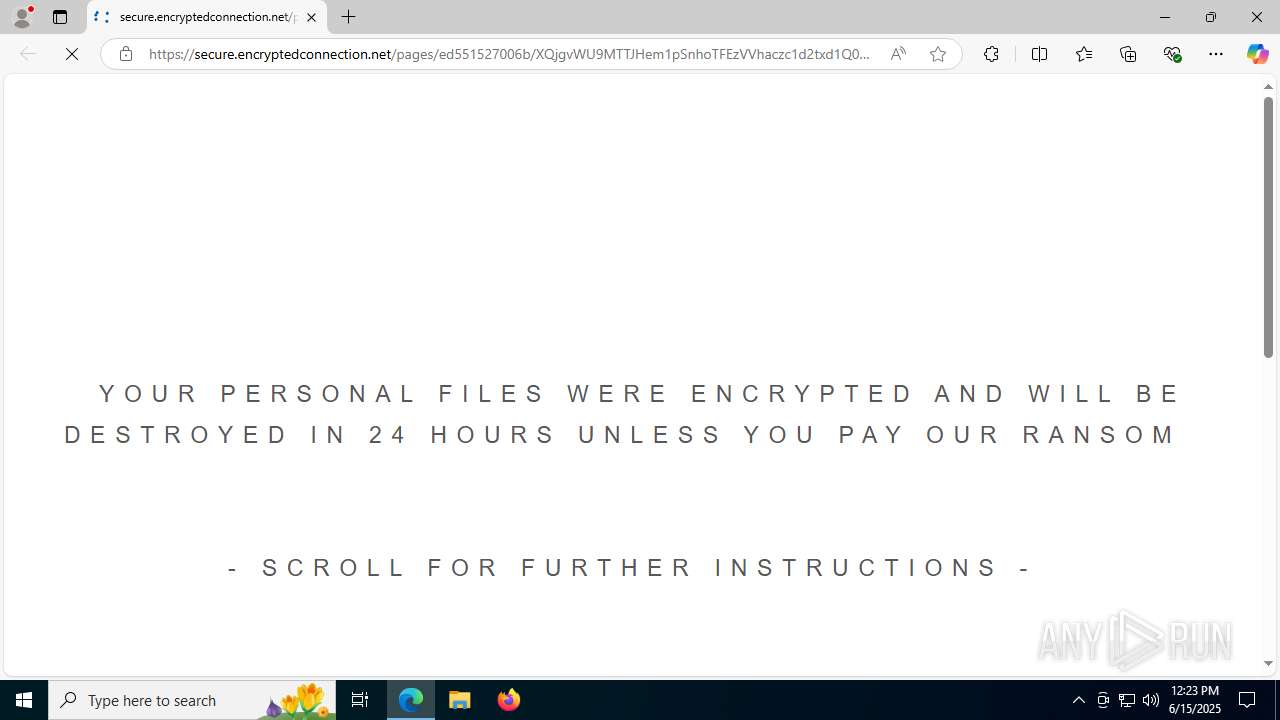
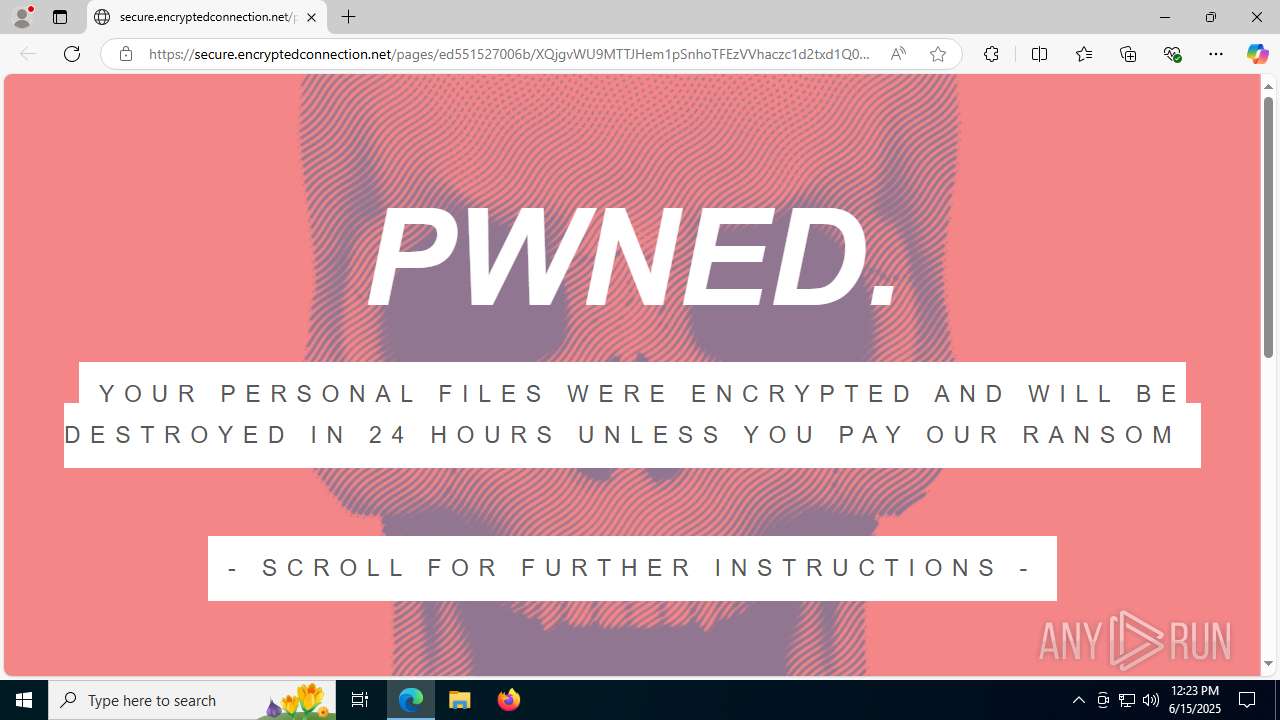
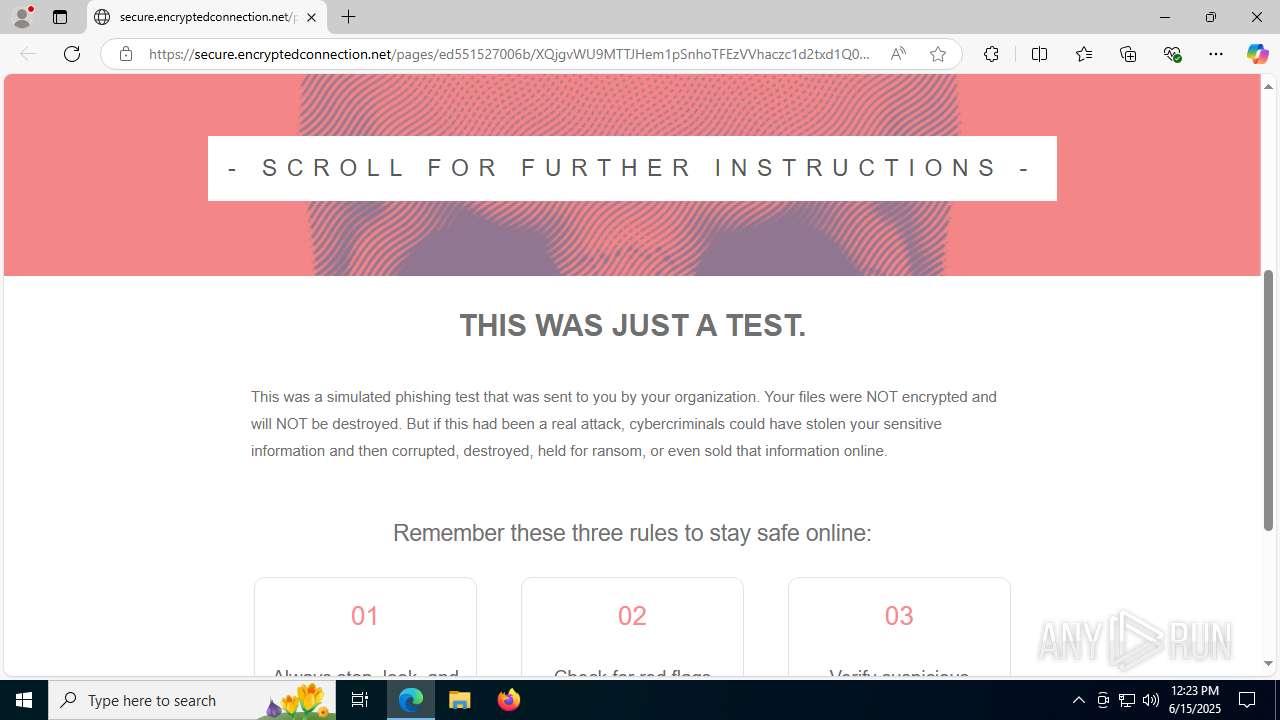
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 1216)
SUSPICIOUS
The process executes via Task Scheduler
- updater.exe (PID: 7156)
Application launched itself
- updater.exe (PID: 7156)
INFO
Drops a (possible) Coronavirus decoy
- iexplore.exe (PID: 6096)
Reads the computer name
- identity_helper.exe (PID: 7712)
- updater.exe (PID: 7156)
Application launched itself
- msedge.exe (PID: 1328)
Checks supported languages
- identity_helper.exe (PID: 7712)
- updater.exe (PID: 6892)
- updater.exe (PID: 7156)
Reads Environment values
- identity_helper.exe (PID: 7712)
Reads the software policy settings
- slui.exe (PID: 1132)
Process checks whether UAC notifications are on
- updater.exe (PID: 7156)
Checks proxy server information
- slui.exe (PID: 1132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
172
Monitored processes
33
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1452,i,3250212381814202376,10826260983513115544,262144 --variations-seed-version --mojo-platform-channel-handle=6400 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2300,i,3250212381814202376,10826260983513115544,262144 --variations-seed-version --mojo-platform-channel-handle=2528 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 -- "https://covid19.auth-verify.com/XQjgvWU9MTTJHem1pSnhoTFEzVVhaczc1d2txd1Q0bkt1WmJlNys0NWgzK2wwU0hJRzlsbDBDQ0tNbFlJSXNzRHNoTkJXWXlBM2xmWnZKMDJMOWFqTnE2MjA0dVRjUFRLNXlxQ29hLzVrcXUvejdlOXpHOXl1RmhmMDBWd25lYTlQYTVrZ2VDeDhRQ2tia0VhdVA2US9zTFR0NUllQ2NzRmhuQ2h4am81VFROTXp4N2xJNFlIdkFFNTFzaG5GQStaUmZYZWYxRT0tLTFPZzZRc1ViYUVJWjJ0amUtLXFzVlh0cWEycGZ0QWJrTy9Fa3R2RlE9PQ==?cid=347115901" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6396,i,3250212381814202376,10826260983513115544,262144 --variations-seed-version --mojo-platform-channel-handle=1704 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3604,i,3250212381814202376,10826260983513115544,262144 --variations-seed-version --mojo-platform-channel-handle=3616 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5628,i,3250212381814202376,10826260983513115544,262144 --variations-seed-version --mojo-platform-channel-handle=6484 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2076 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2380,i,3250212381814202376,10826260983513115544,262144 --variations-seed-version --mojo-platform-channel-handle=2356 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3588 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffc43a6f208,0x7ffc43a6f214,0x7ffc43a6f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4112 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3620,i,3250212381814202376,10826260983513115544,262144 --variations-seed-version --mojo-platform-channel-handle=3672 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
6 468
Read events
6 421
Write events
43
Delete events
4
Modification events
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31186416 | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6096) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
10
Suspicious files
259
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1772fd.TMP | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17731c.TMP | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17731c.TMP | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17732c.TMP | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17733c.TMP | — | |
MD5:— | SHA256:— | |||
| 1328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
65
DNS requests
67
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7708 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750195136&P2=404&P3=2&P4=T9n1G%2b0WR2qUxiPR0DwwwEN2aj9wSQiq4mcsni57W9OdBa%2b1AOnejuMUJab9FupumL8DR6C9D%2bjjtPgJxIkd8g%3d%3d | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750195136&P2=404&P3=2&P4=T9n1G%2b0WR2qUxiPR0DwwwEN2aj9wSQiq4mcsni57W9OdBa%2b1AOnejuMUJab9FupumL8DR6C9D%2bjjtPgJxIkd8g%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.19.105.127:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1750195138&P2=404&P3=2&P4=Fdv1pd4b9pR1iFQDjA1GcpGwnl0RpMnATe%2baI4nEOzShihtNAJakPdsWWwfPsgpaQu%2fJQD2pXKBmL%2fkJGV6V6A%3d%3d | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750195135&P2=404&P3=2&P4=FaEA58CZyLLyLFHiuHWxdlz%2b3eJ8C3pqNXyIWAp8xKdjFWc5nmORLN%2fQoTyRcMRc9VujFlJPmI%2b2y3VsA0QjKg%3d%3d | unknown | — | — | whitelisted |
7708 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1750195138&P2=404&P3=2&P4=Fdv1pd4b9pR1iFQDjA1GcpGwnl0RpMnATe%2baI4nEOzShihtNAJakPdsWWwfPsgpaQu%2fJQD2pXKBmL%2fkJGV6V6A%3d%3d | unknown | — | — | whitelisted |
7708 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1750195136&P2=404&P3=2&P4=cnpP4jNJyTrkYNSdd1HSpzBUnkRBZJ%2bQEPWPBx1Nx3mwvtIRSiUK4jCv274QbBBWe9G9AS06F%2bripWNNUconww%3d%3d | unknown | — | — | whitelisted |
7708 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/46df2db5-82ac-46a7-9d9e-cf1580d73a96?P1=1750195137&P2=404&P3=2&P4=gQC%2foT5QIdtLR%2flXyEOKcqq0tsnQTRPJxG7lX%2fj2QGcr62QXDuMhc6JZDq8Vr6mdADml2MbMl%2fEuRICDaeSB1w%3d%3d | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1750195136&P2=404&P3=2&P4=cnpP4jNJyTrkYNSdd1HSpzBUnkRBZJ%2bQEPWPBx1Nx3mwvtIRSiUK4jCv274QbBBWe9G9AS06F%2bripWNNUconww%3d%3d | unknown | — | — | whitelisted |
7708 | svchost.exe | GET | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/46df2db5-82ac-46a7-9d9e-cf1580d73a96?P1=1750195137&P2=404&P3=2&P4=gQC%2foT5QIdtLR%2flXyEOKcqq0tsnQTRPJxG7lX%2fj2QGcr62QXDuMhc6JZDq8Vr6mdADml2MbMl%2fEuRICDaeSB1w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5476 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1216 | msedge.exe | 34.255.94.28:443 | covid19.auth-verify.com | AMAZON-02 | IE | whitelisted |
1216 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1216 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1216 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1216 | msedge.exe | 2.16.204.141:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
covid19.auth-verify.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
secure.encryptedconnection.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1216 | msedge.exe | Potentially Bad Traffic | ET HUNTING Suspicious TLS SNI Request for Possible COVID-19 Domain M1 |
1216 | msedge.exe | Potentially Bad Traffic | ET HUNTING Suspicious TLS SNI Request for Possible COVID-19 Domain M1 |
1216 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Microsoft Phishing (secure .encryptedconnection .net) |
1216 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Microsoft Phishing (secure .encryptedconnection .net) |
1216 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Microsoft Phishing (secure .encryptedconnection .net) |
1216 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Microsoft Phishing (secure .encryptedconnection .net) |